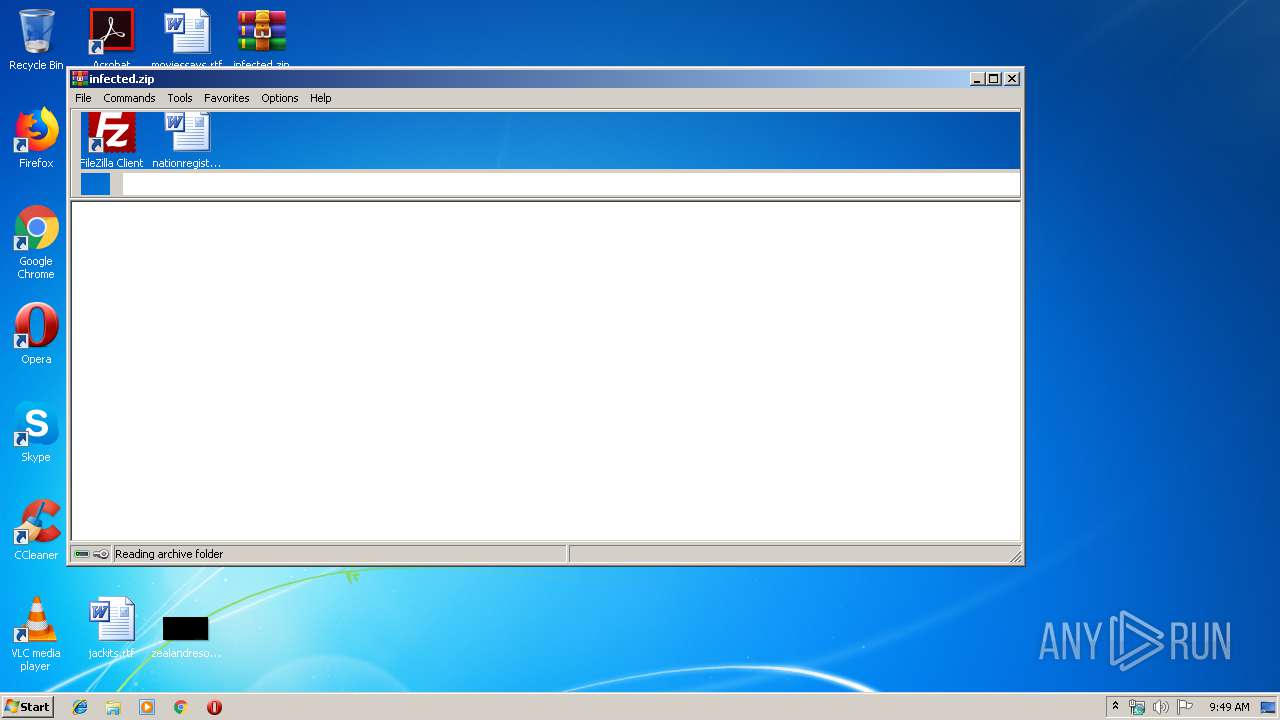
| File name: | infected.zip |
| Full analysis: | https://app.any.run/tasks/51fa9137-db47-478d-b040-e56165fbd415 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 08:49:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 8895CEDAE57C1097BDC50DE7540C994F |
| SHA1: | AE2018863BC29FB1A246CD5797EC6A1B3DBCA6A0 |
| SHA256: | 82C46D9F91E7CA2C0F34FCFE09B2F6273B4A41A3C68107B3445B2F2AD20DF7F1 |
| SSDEEP: | 3072:r2cNU3n9dVi6j3V0RijyXnhyWOdVg5bBI4OPdVh3xxTvaf/kkFtgIz00MekWQN2:r2cUn93zVwDnh5oVg5bBDQVhv1k6eEN2 |
MALICIOUS
Application was injected by another process
- taskeng.exe (PID: 1976)
Loads the Task Scheduler COM API
- svchost.exe (PID: 2192)
Uses SVCHOST.EXE for hidden code execution
- 3ebe8160.exe (PID: 3656)
Changes the autorun value in the registry
- svchost.exe (PID: 2192)
Runs injected code in another process
- svchost.exe (PID: 2192)
Application was dropped or rewritten from another process
- 3ebe8160.exe (PID: 2480)
- 3ebe8160.exe (PID: 3656)
SUSPICIOUS
Application launched itself
- 3ebe8160.exe (PID: 2480)
Creates files in the program directory
- svchost.exe (PID: 2192)
Executable content was dropped or overwritten
- svchost.exe (PID: 2192)
INFO
Manual execution by user
- 3ebe8160.exe (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:05:14 12:10:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
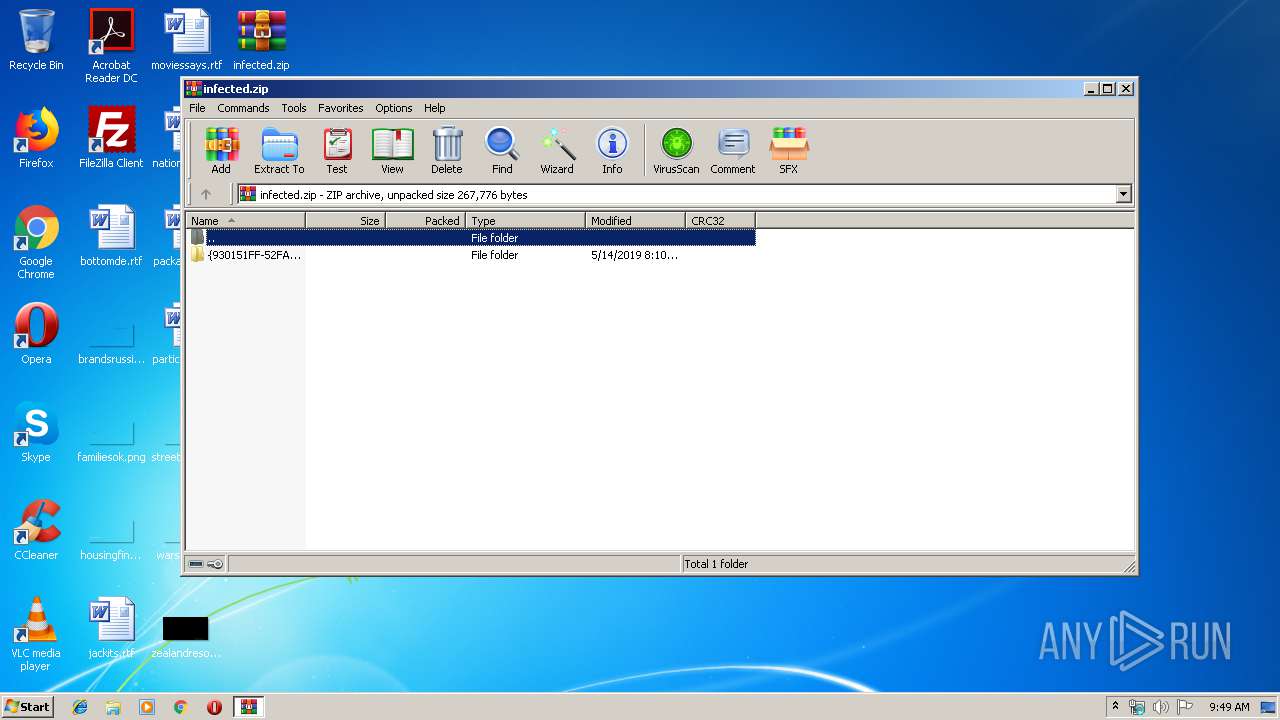
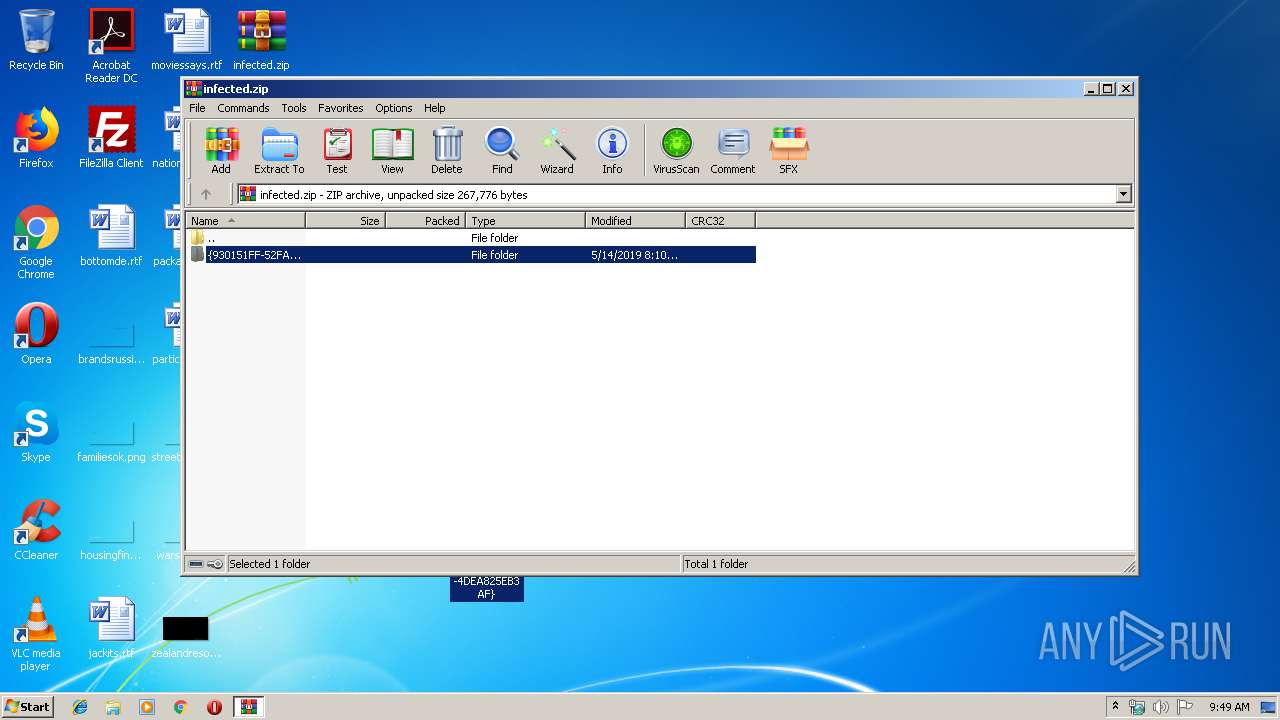
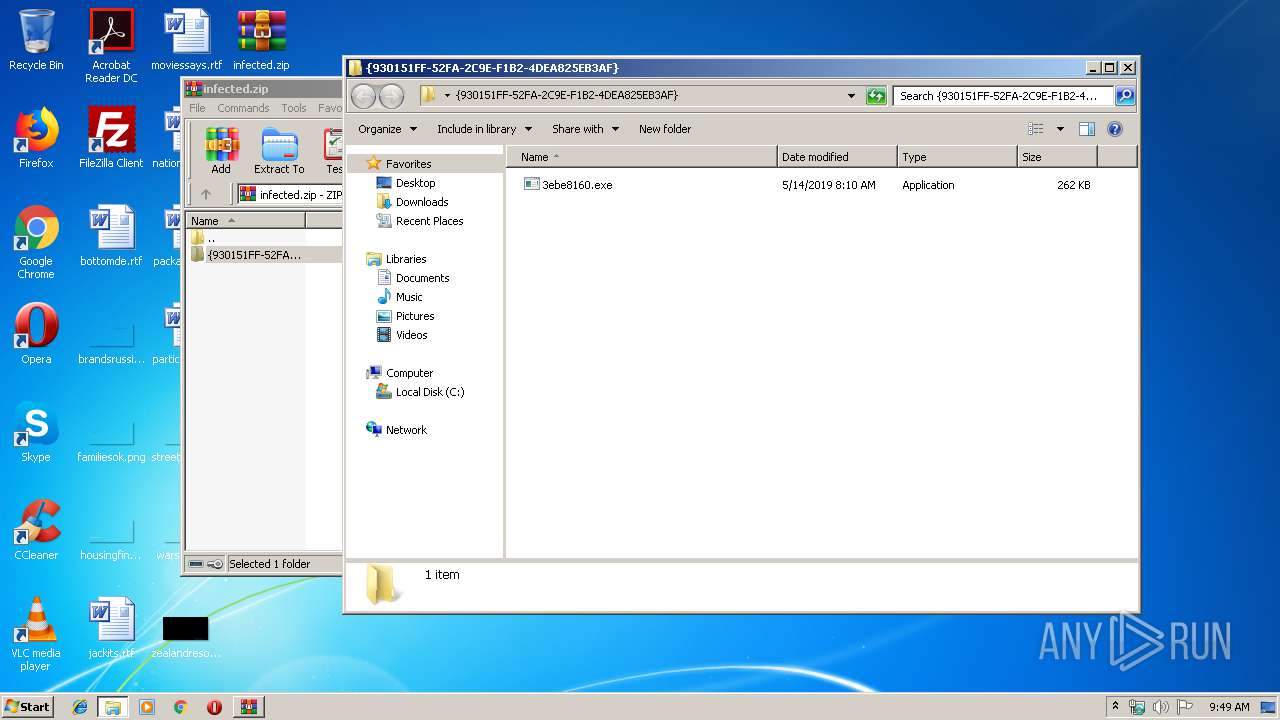
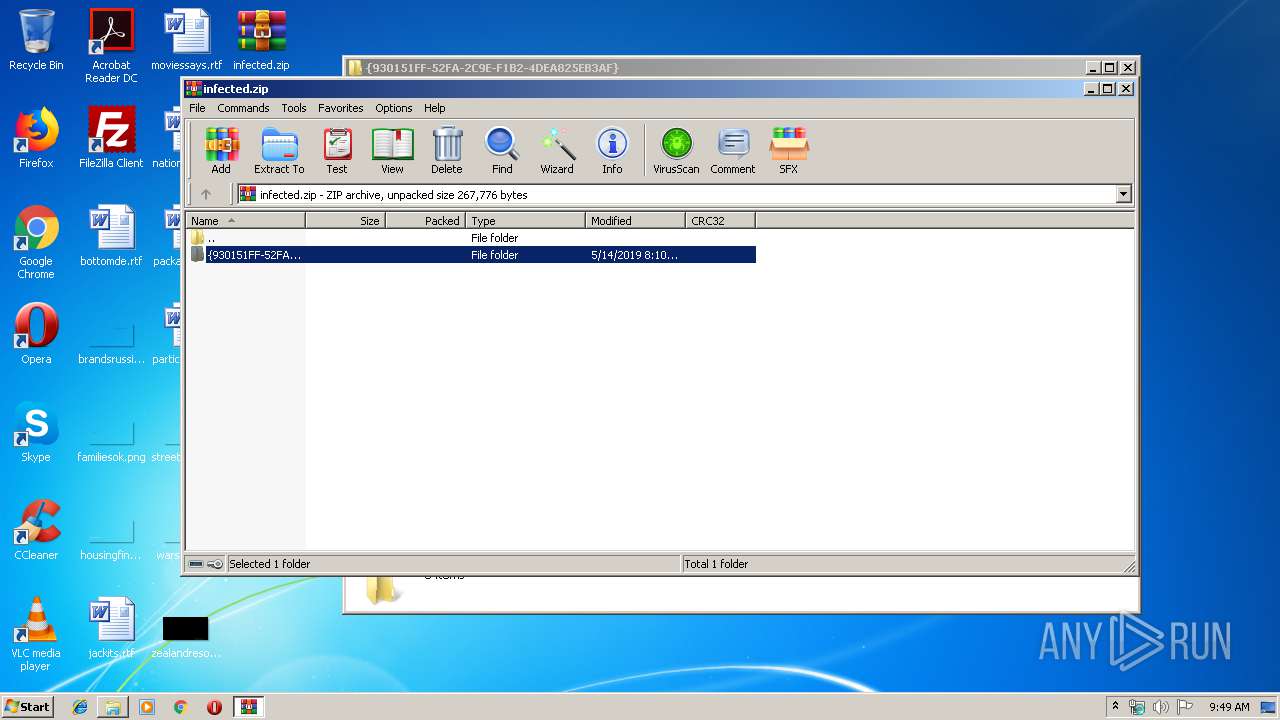
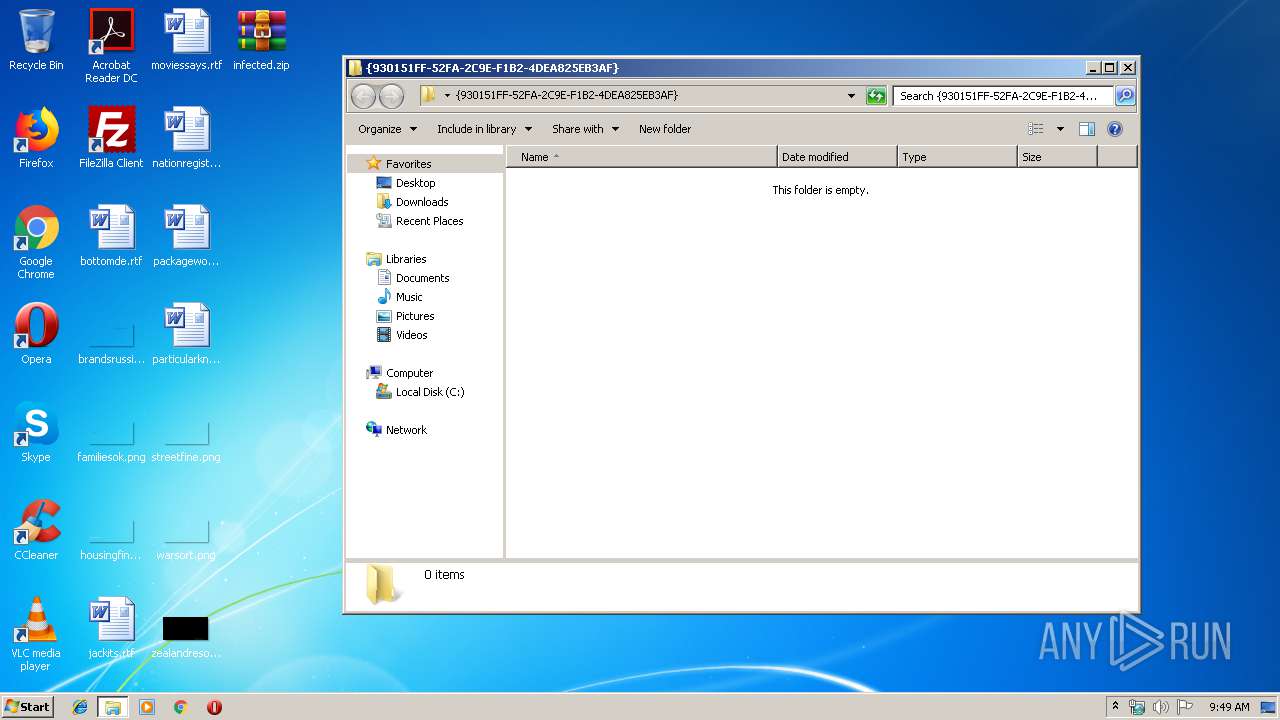
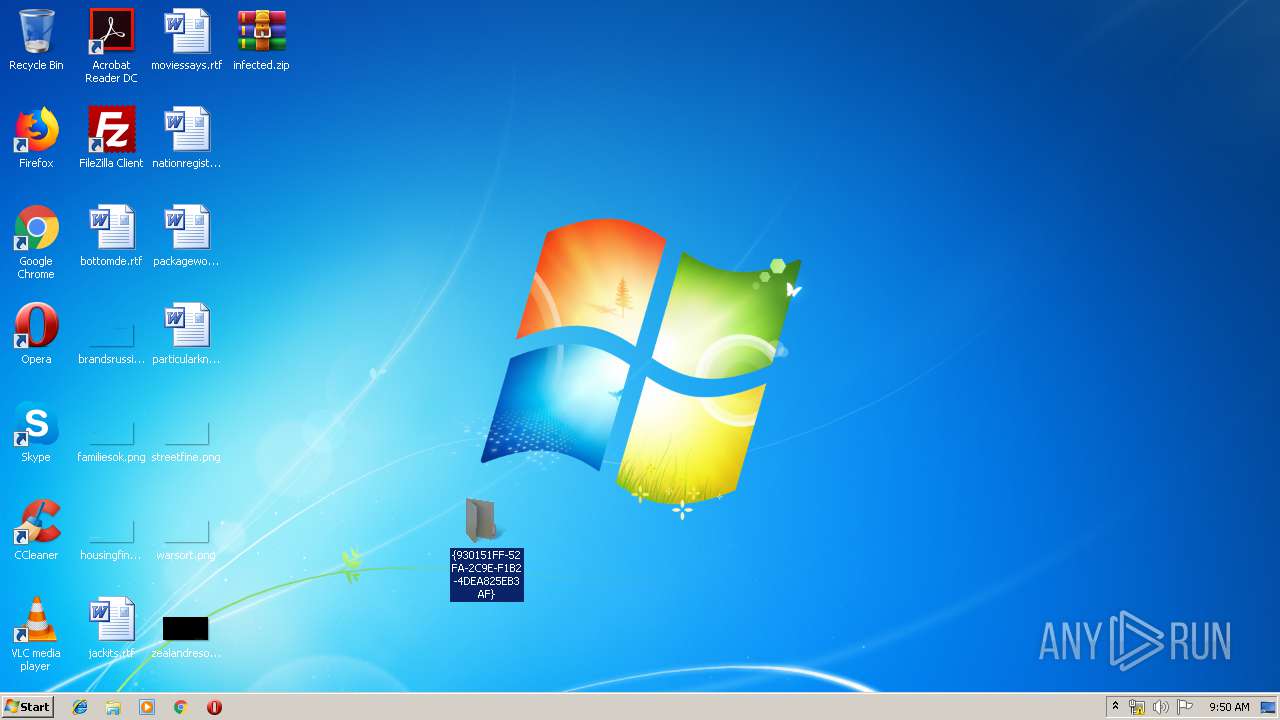
| ZipFileName: | {930151FF-52FA-2C9E-F1B2-4DEA825EB3AF}/ |
Total processes
38
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1976 | taskeng.exe {235AA494-E015-4A32-953D-758354244F92} | C:\Windows\System32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | "C:\Windows\system32\svchost.exe" | C:\Windows\system32\svchost.exe | 3ebe8160.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | "C:\Users\admin\Desktop\{930151FF-52FA-2C9E-F1B2-4DEA825EB3AF}\3ebe8160.exe" | C:\Users\admin\Desktop\{930151FF-52FA-2C9E-F1B2-4DEA825EB3AF}\3ebe8160.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
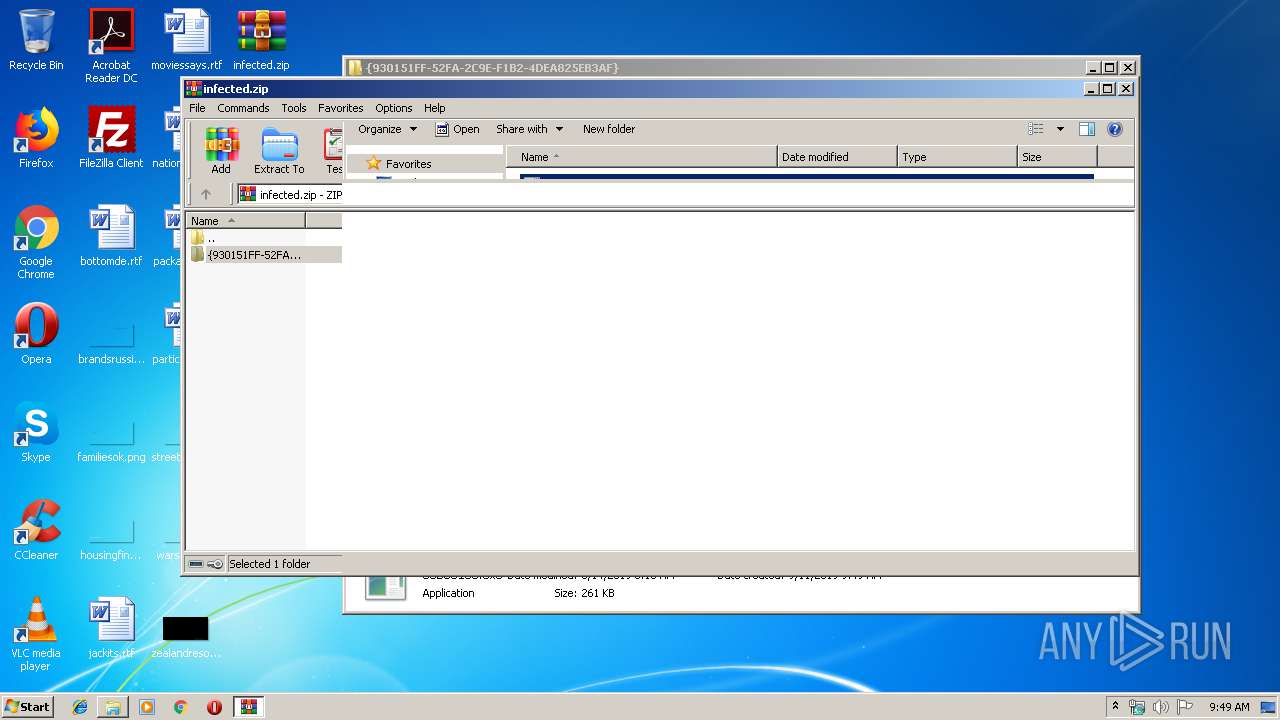
| 3592 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\infected.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3656 | "C:\Users\admin\Desktop\{930151FF-52FA-2C9E-F1B2-4DEA825EB3AF}\3ebe8160.exe" | C:\Users\admin\Desktop\{930151FF-52FA-2C9E-F1B2-4DEA825EB3AF}\3ebe8160.exe | — | 3ebe8160.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
364
Read events
342
Write events
22
Delete events
0
Modification events
| (PID) Process: | (3592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3592) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\infected.zip | |||
| (PID) Process: | (3592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
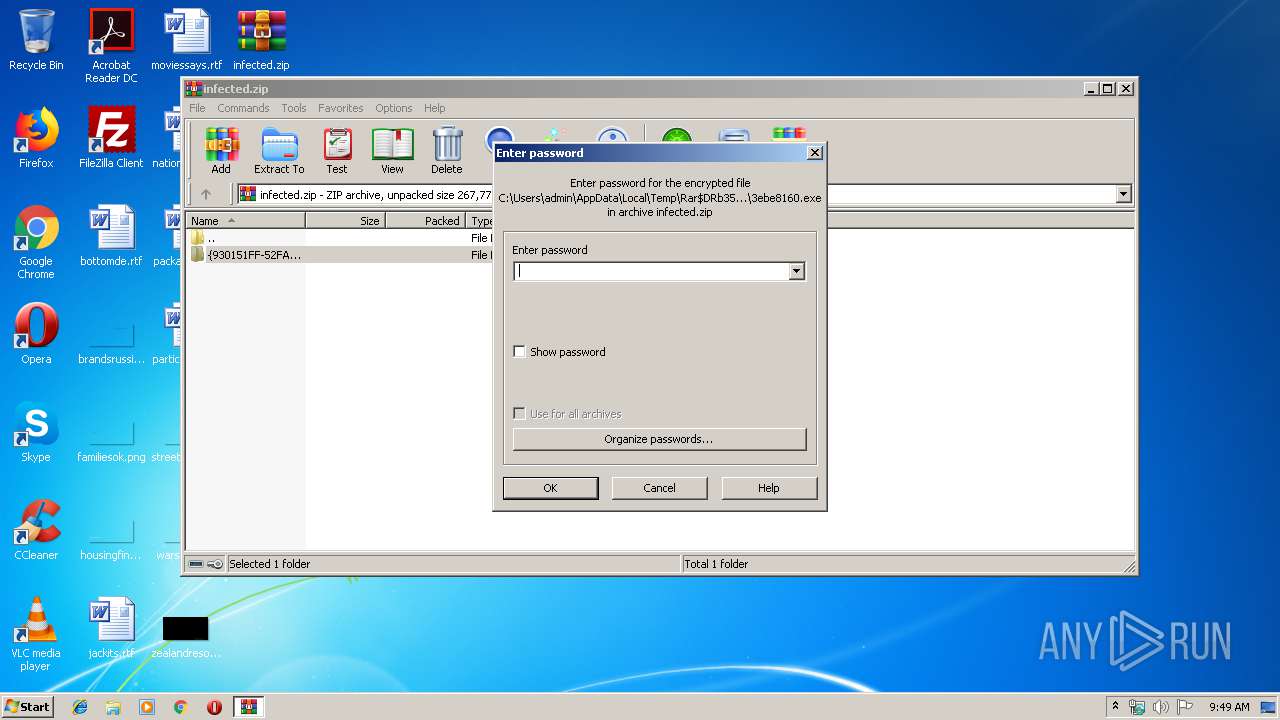
| (PID) Process: | (3592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2192) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | {AB3B8939-E6B9-E5B3-AD18-36842A6DC142} |
Value: c:\programdata\{372BA109-CE89-79A3-AD18-36842A6DC142}\9a947196.exe | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3592 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3592.27184\{930151FF-52FA-2C9E-F1B2-4DEA825EB3AF}\3ebe8160.exe | — | |
MD5:— | SHA256:— | |||
| 2192 | svchost.exe | C:\programdata\{372BA109-CE89-79A3-AD18-36842A6DC142}\9a947196.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report