| File name: | aramaware.exe |
| Full analysis: | https://app.any.run/tasks/e7130127-5e3a-4e19-ab3b-1d8dea06a6fc |
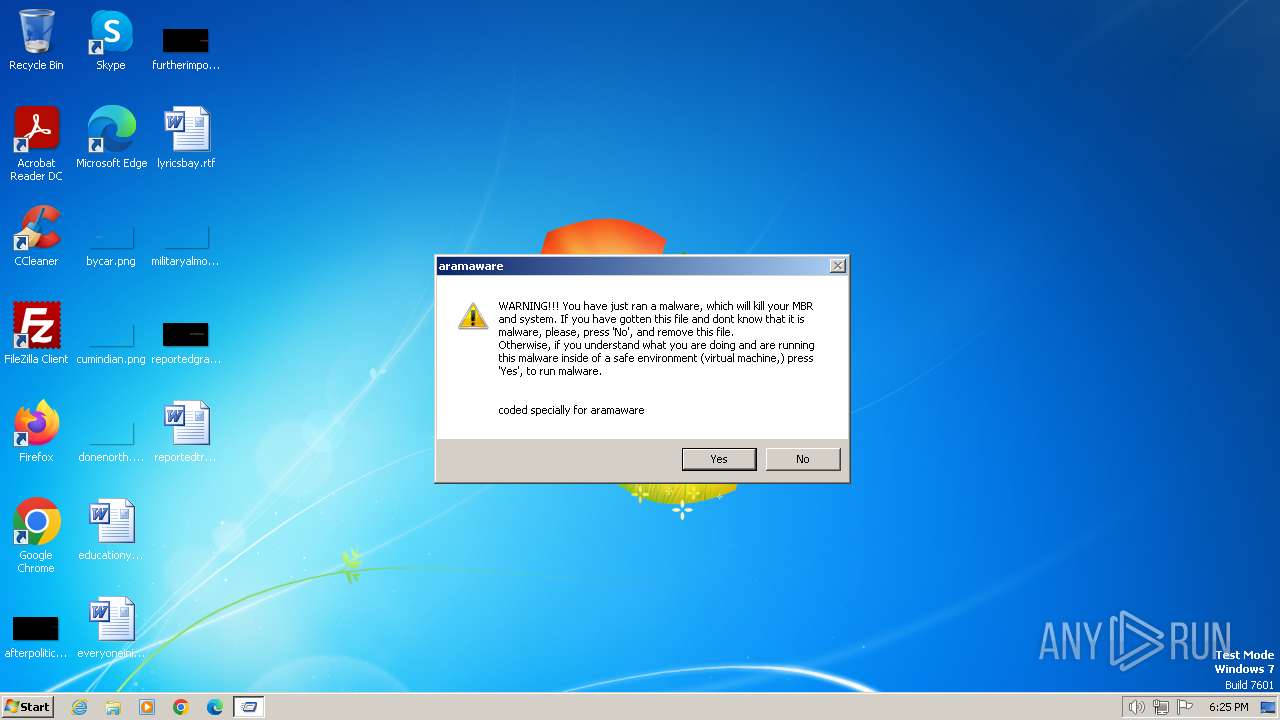
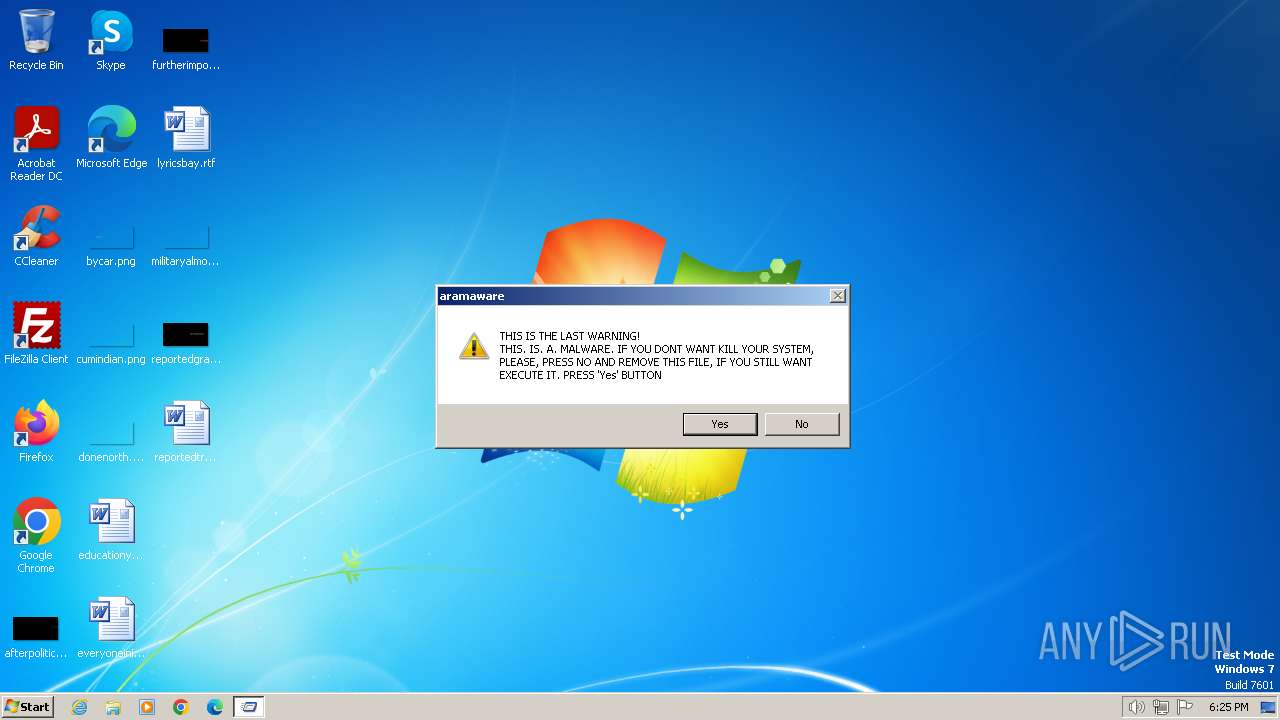
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2024, 18:25:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3ACDCDEE17825753CACC8DFD414E57D3 |
| SHA1: | 269FCB1AE5794190E1CECDF96B1EAA41188DC2A6 |
| SHA256: | 82BB1809904786AFC0C13ABEC22A48B320581EC913BF5BBDDDD02FCE05EF77E8 |
| SSDEEP: | 12288:QNWeKSg6n7ckl86Lamaf/+zDcNzXjSMLMMzfnFvv1xl325LUP:c+M3qzXjSMLMKfH325LUP |
MALICIOUS
Drops the executable file immediately after the start
- aramaware.exe (PID: 2472)
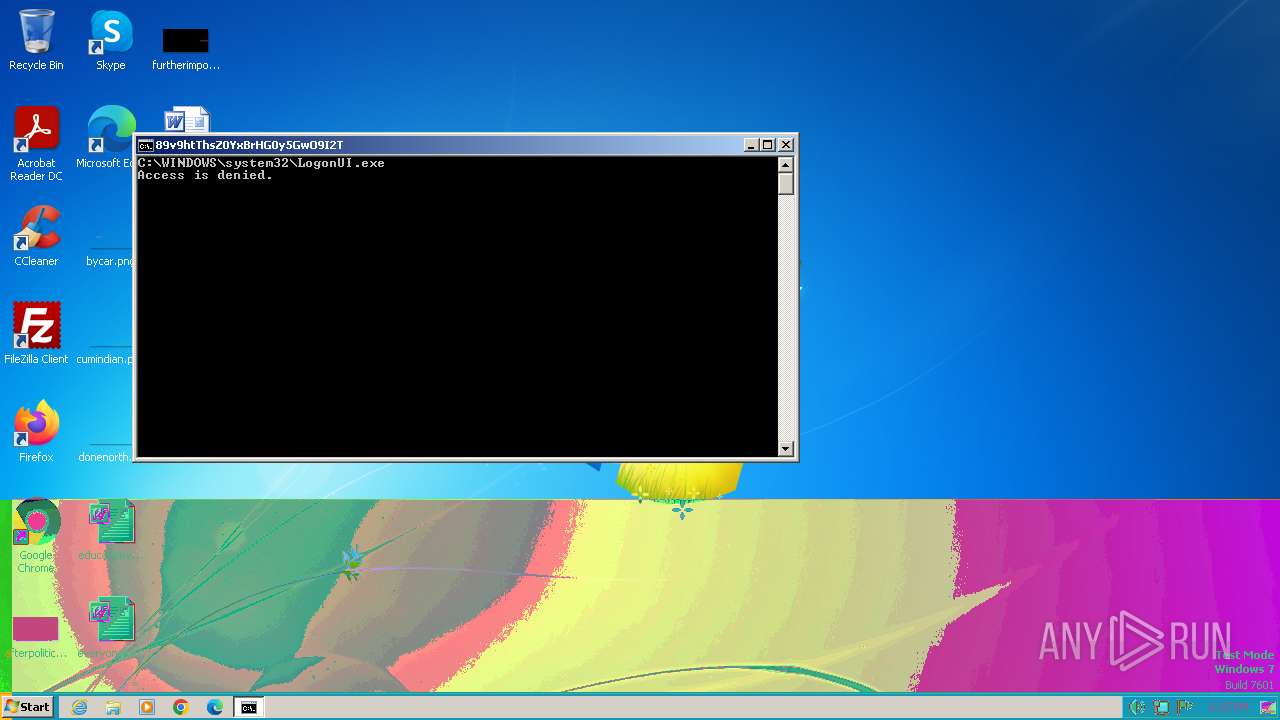
SUSPICIOUS
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3348)
- cmd.exe (PID: 3692)
Starts CMD.EXE for commands execution
- aramaware.exe (PID: 2472)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 2044)
- cmd.exe (PID: 3664)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 1692)
- cmd.exe (PID: 2120)
Executing commands from a ".bat" file
- aramaware.exe (PID: 2472)
The system shut down or reboot
- cmd.exe (PID: 3044)
The process executes via Task Scheduler
- ctfmon.exe (PID: 1632)
- sipnotify.exe (PID: 1440)
Reads the Internet Settings
- sipnotify.exe (PID: 1440)
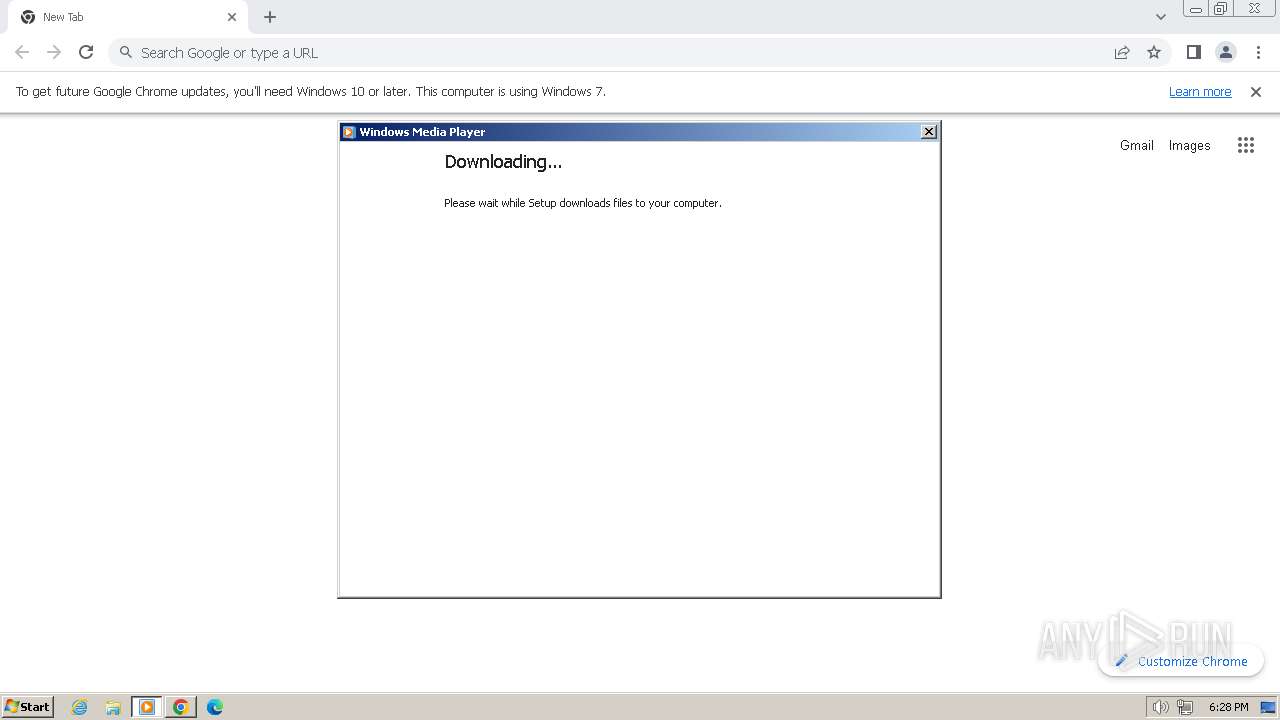
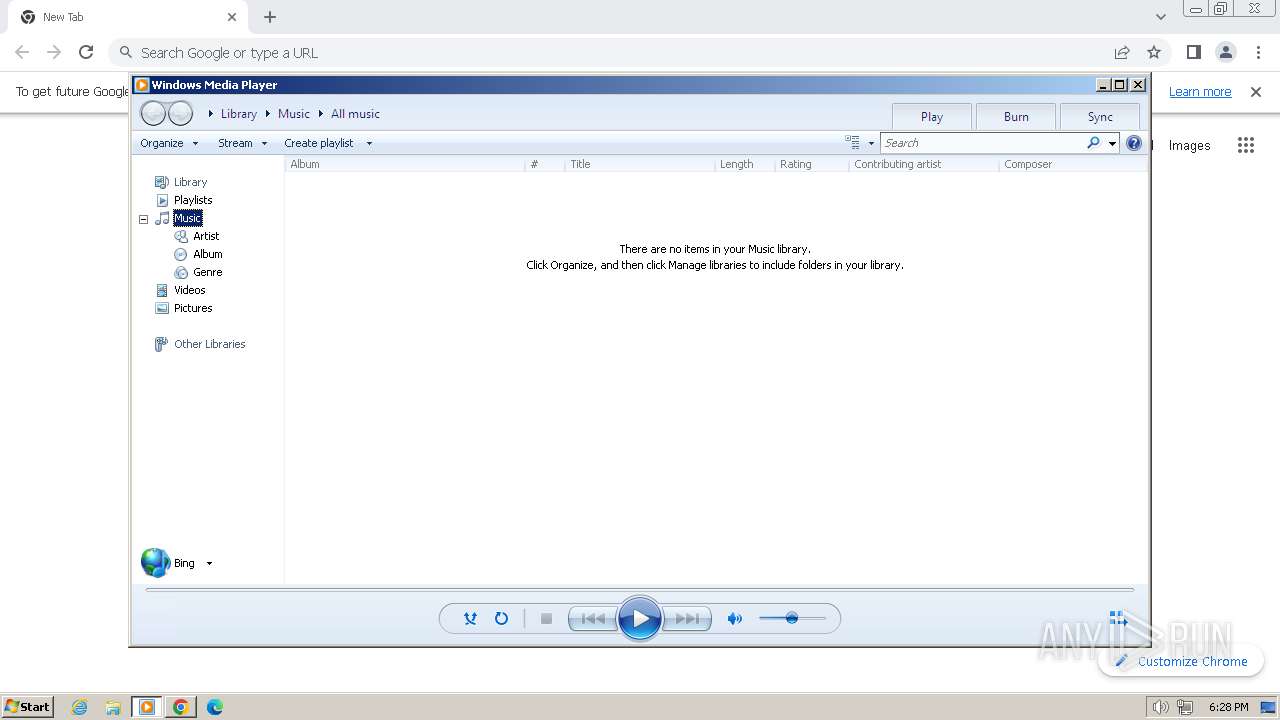
- wmplayer.exe (PID: 2976)
- wmplayer.exe (PID: 3432)
- setup_wm.exe (PID: 2992)
Reads security settings of Internet Explorer
- wmplayer.exe (PID: 2976)
- setup_wm.exe (PID: 2992)
- wmplayer.exe (PID: 3432)
Reads settings of System Certificates
- sipnotify.exe (PID: 1440)
INFO
Checks supported languages
- aramaware.exe (PID: 2472)
- IMEKLMG.EXE (PID: 2076)
- IMEKLMG.EXE (PID: 2084)
- wmpnscfg.exe (PID: 2348)
- setup_wm.exe (PID: 2992)
- wmplayer.exe (PID: 2976)
- wmpnscfg.exe (PID: 2324)
- wmplayer.exe (PID: 3432)
- wmpshare.exe (PID: 3632)
Reads the computer name
- IMEKLMG.EXE (PID: 2076)
- IMEKLMG.EXE (PID: 2084)
- wmpnscfg.exe (PID: 2348)
- wmplayer.exe (PID: 2976)
- setup_wm.exe (PID: 2992)
- wmpnscfg.exe (PID: 2324)
- wmplayer.exe (PID: 3432)
- wmpshare.exe (PID: 3632)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2084)
- IMEKLMG.EXE (PID: 2076)
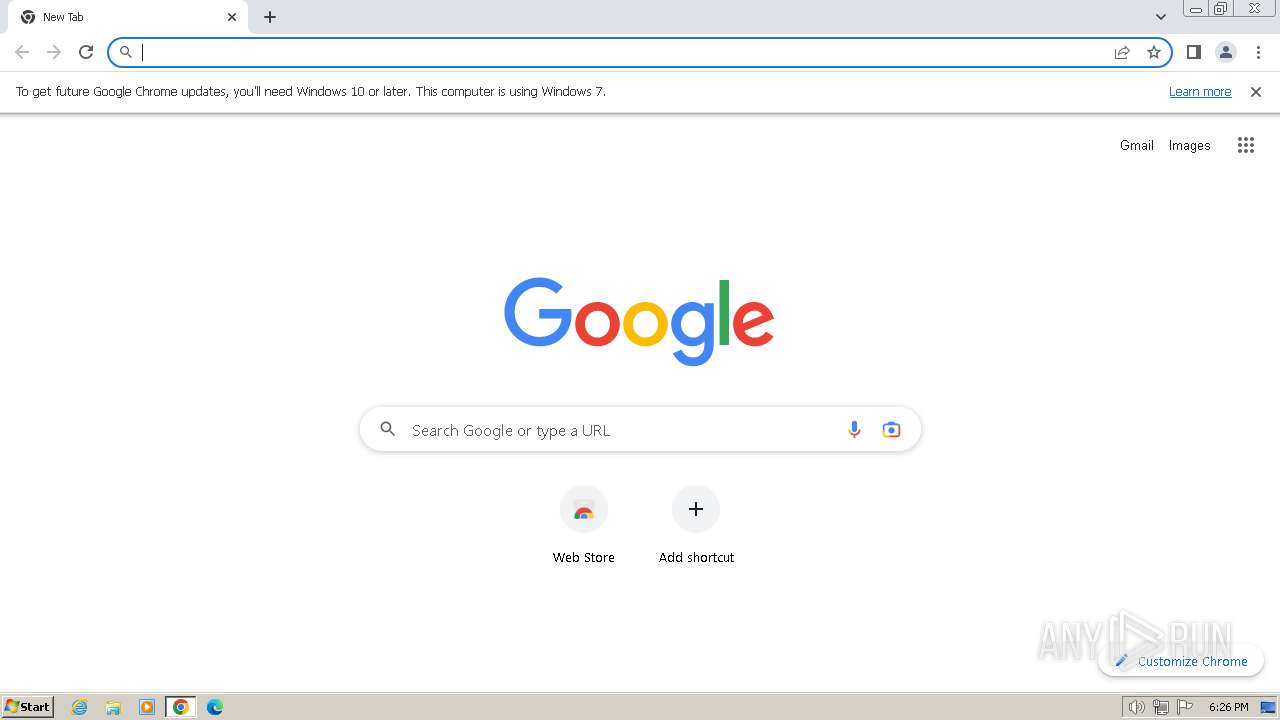
Manual execution by a user
- chrome.exe (PID: 3508)
- IMEKLMG.EXE (PID: 2076)
- IMEKLMG.EXE (PID: 2084)
- wmpnscfg.exe (PID: 2348)
- chrome.exe (PID: 2488)
- wmplayer.exe (PID: 2976)
- wmpnscfg.exe (PID: 2324)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1440)
Application launched itself
- chrome.exe (PID: 3508)
- chrome.exe (PID: 2488)
Create files in a temporary directory
- setup_wm.exe (PID: 2992)
- wmplayer.exe (PID: 3432)
Reads Environment values
- setup_wm.exe (PID: 2992)
- wmplayer.exe (PID: 3432)
Reads the software policy settings
- sipnotify.exe (PID: 1440)
Process checks computer location settings
- setup_wm.exe (PID: 2992)
- wmplayer.exe (PID: 3432)
Checks proxy server information
- setup_wm.exe (PID: 2992)
- wmplayer.exe (PID: 3432)
Reads the machine GUID from the registry
- wmplayer.exe (PID: 3432)
- setup_wm.exe (PID: 2992)
Creates files or folders in the user directory
- wmplayer.exe (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:08:26 14:40:03+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.3 |
| CodeSize: | 135168 |
| InitializedDataSize: | 230400 |
| UninitializedDataSize: | 1536 |
| EntryPoint: | 0x1480 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
151
Monitored processes
56
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2344 --field-trial-handle=1084,i,7149224797200739741,3546269843835871915,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2096 --field-trial-handle=1084,i,7149224797200739741,3546269843835871915,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3376 --field-trial-handle=1084,i,7149224797200739741,3546269843835871915,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1044 --field-trial-handle=1084,i,7149224797200739741,3546269843835871915,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1348 | C:\Windows\system32\cmd.exe /c del C:\WINDOWS\system32\dllcache\logonui.exe /s/q | C:\Windows\System32\cmd.exe | — | aramaware.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1440 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1492 | takeown /F C:\Windows\system32\logonui.exe | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1632 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1692 | C:\Windows\system32\cmd.exe /c icacls %WINDIR%\system32\dllcache\logonui.exe /Grant:r %UserName% :F | C:\Windows\System32\cmd.exe | — | aramaware.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 87 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1824 | C:\Windows\system32\cmd.exe /c assoc .vbs=.html | C:\Windows\System32\cmd.exe | — | aramaware.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
17 038
Read events
16 534
Write events
406
Delete events
98
Modification events
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
44
Text files
75
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF18b07e.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF18b2ef.TMP | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18b224.TMP | text | |
MD5:8593E82FF8753DC10267243C51E8A91B | SHA256:FE9EE2D77D9EB5CBA707EDBCB7F1ABAA83418CDB66D66835B4B9A1B6CC5CC34F | |||
| 3508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF18b2b1.TMP | text | |
MD5:0272AD43ECEA4DC6C694BE6D918B5BA7 | SHA256:530F5A3F46B293038FEBEF2035CFA622F05B202363ABFAF9E40E105BD1472432 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
35
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
1440 | sipnotify.exe | HEAD | 200 | 184.51.236.222:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133523224627810000 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 5.81 Kb | unknown |
2992 | setup_wm.exe | GET | 302 | 2.16.164.64:80 | http://redir.metaservices.microsoft.com/redir/allservices/?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | unknown | — | — | unknown |
2992 | setup_wm.exe | GET | 200 | 2.16.164.88:80 | http://onlinestores.metaservices.microsoft.com/serviceswitching/AllServices.aspx?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | unknown | xml | 546 b | unknown |
3432 | wmplayer.exe | GET | 200 | 72.247.154.56:80 | http://images.windowsmedia.com/svcswitch/media_guide_16x16.png | unknown | image | 897 b | unknown |
3432 | wmplayer.exe | GET | 200 | 2.16.164.88:80 | http://onlinestores.metaservices.microsoft.com/serviceswitching/AllServices.aspx?sv=5&locale=409&geoid=f4&version=12.0.7601.24499&userlocale=409 | unknown | xml | 546 b | unknown |
3432 | wmplayer.exe | GET | 200 | 72.247.154.56:80 | http://images.windowsmedia.com/svcswitch/mg4_wmp12_30x30_2.png | unknown | image | 2.00 Kb | unknown |
3432 | wmplayer.exe | GET | 302 | 2.16.164.64:80 | http://redir.metaservices.microsoft.com/redir/allservices/?sv=5&locale=409&geoid=f4&version=12.0.7601.24499&userlocale=409 | unknown | — | — | unknown |
3432 | wmplayer.exe | GET | 200 | 2.16.164.88:80 | http://onlinestores.metaservices.microsoft.com/bing/bing.xml?locale=409&geoid=f4&version=12.0.7601.24499&userlocale=409 | unknown | text | 523 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3508 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2592 | chrome.exe | 142.250.185.67:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2592 | chrome.exe | 142.250.186.164:443 | www.google.com | GOOGLE | US | whitelisted |
2592 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | unknown |
2592 | chrome.exe | 216.58.206.35:443 | www.gstatic.com | GOOGLE | US | whitelisted |
2592 | chrome.exe | 142.250.185.110:443 | apis.google.com | GOOGLE | US | whitelisted |
2592 | chrome.exe | 142.250.185.195:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
query.prod.cms.rt.microsoft.com |
| whitelisted |
redir.metaservices.microsoft.com |
| whitelisted |