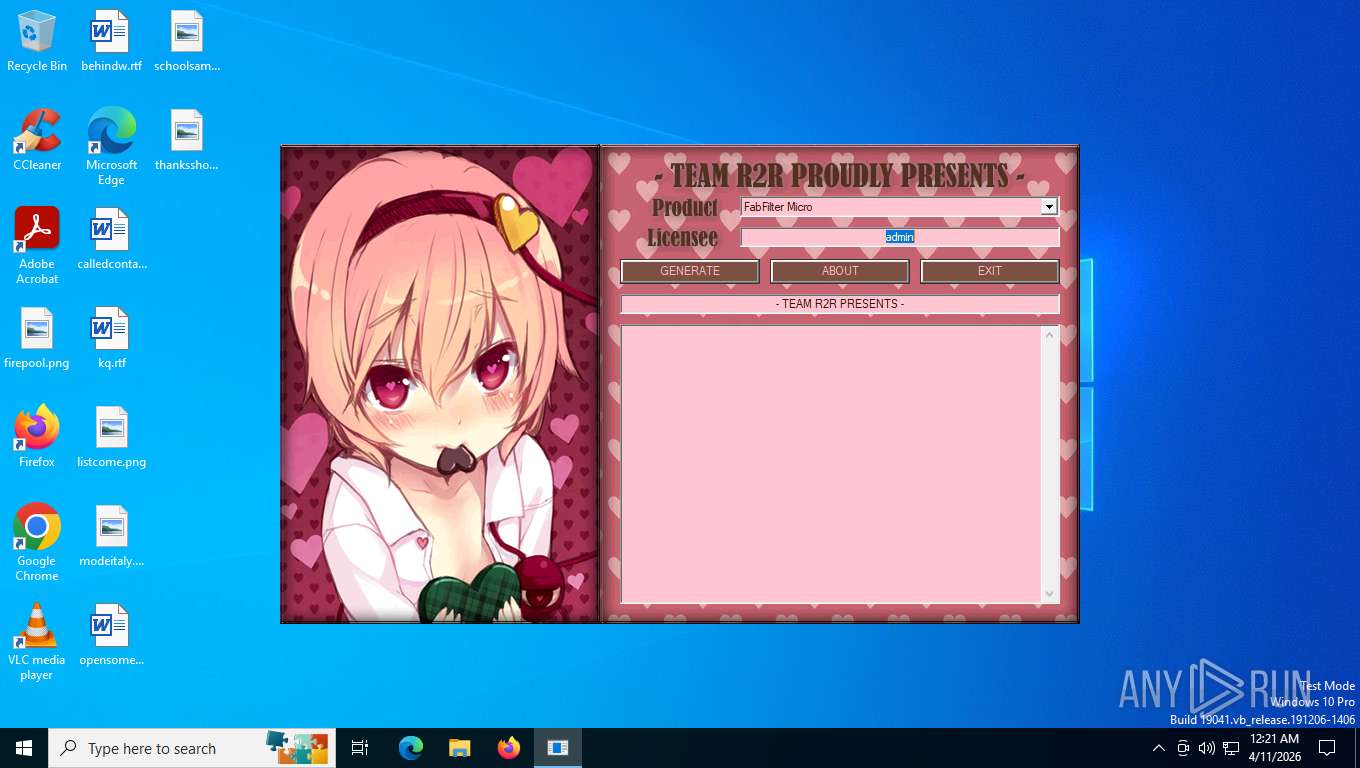
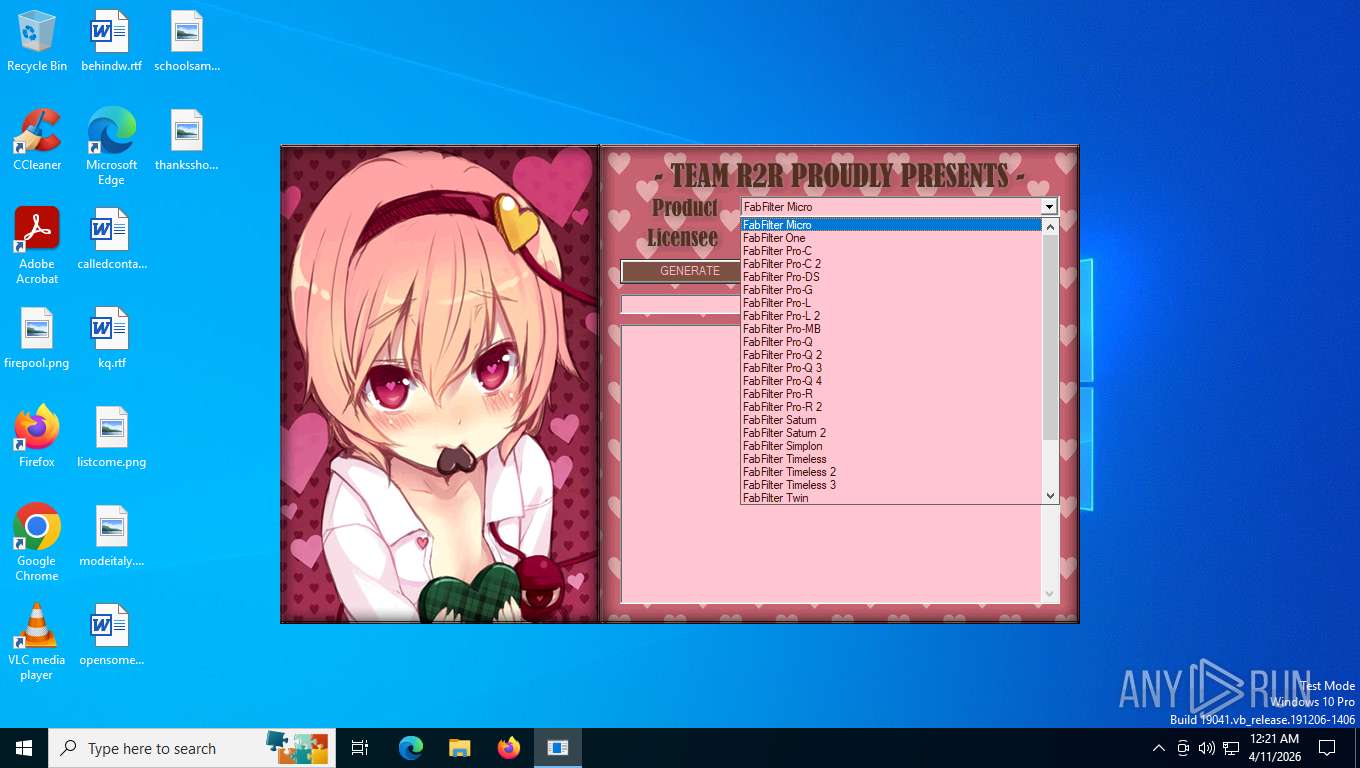
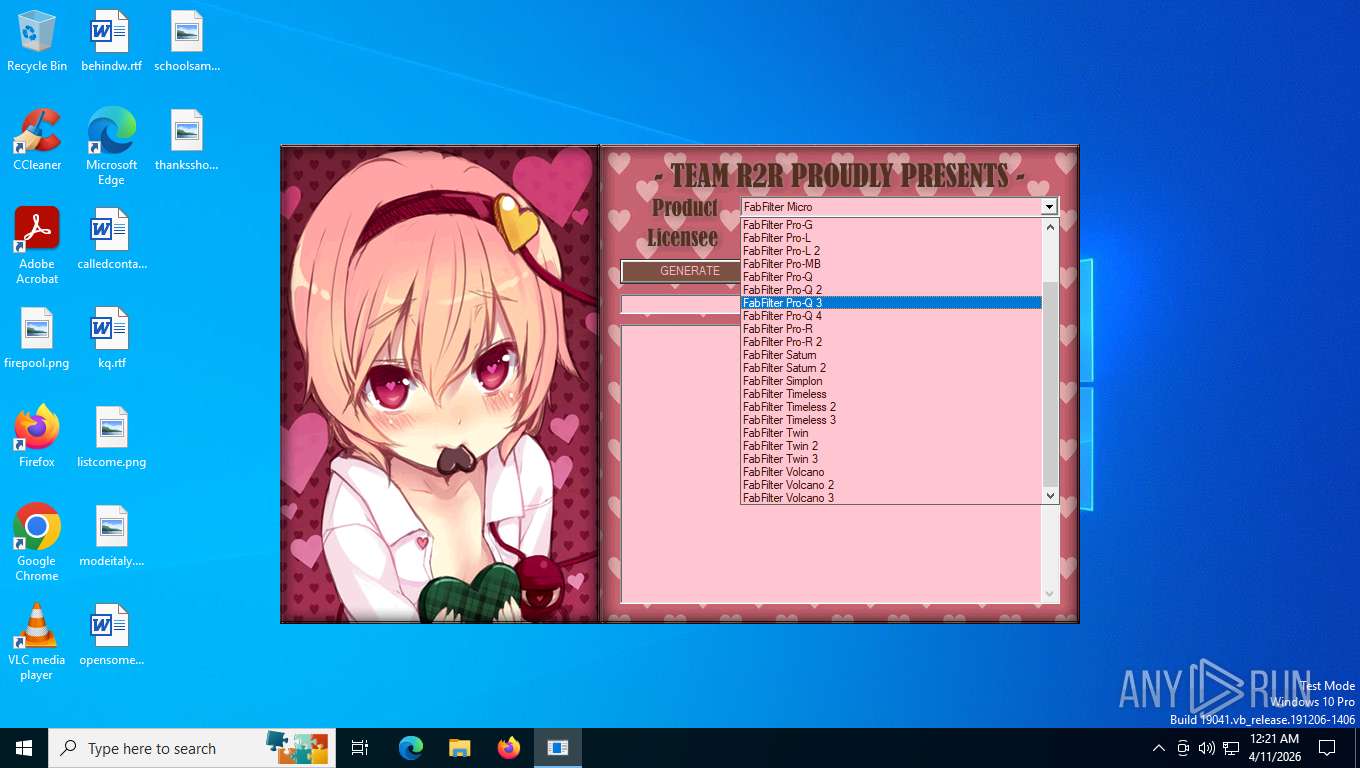
| File name: | FabFilter_KeyGen.exe |
| Full analysis: | https://app.any.run/tasks/9d0ea7af-9dc4-46f4-92ed-2d4f61618549 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2026, 04:21:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 2BBD096A02E68977B40F50DE0C243D76 |
| SHA1: | 90B1814D8226C52A784EE10EC0DDA55FD4358AF1 |
| SHA256: | 82B38456CF80306542FDBB9229A1FCD41A6BE6E801836236C737AD327FA9E163 |
| SSDEEP: | 24576:K3sUkCN2U+zqhkrPyk4K00JsRHeDSix1hHX:K3sUkCN2U+zqh6Pyk4t0Js9eDSix1hHX |
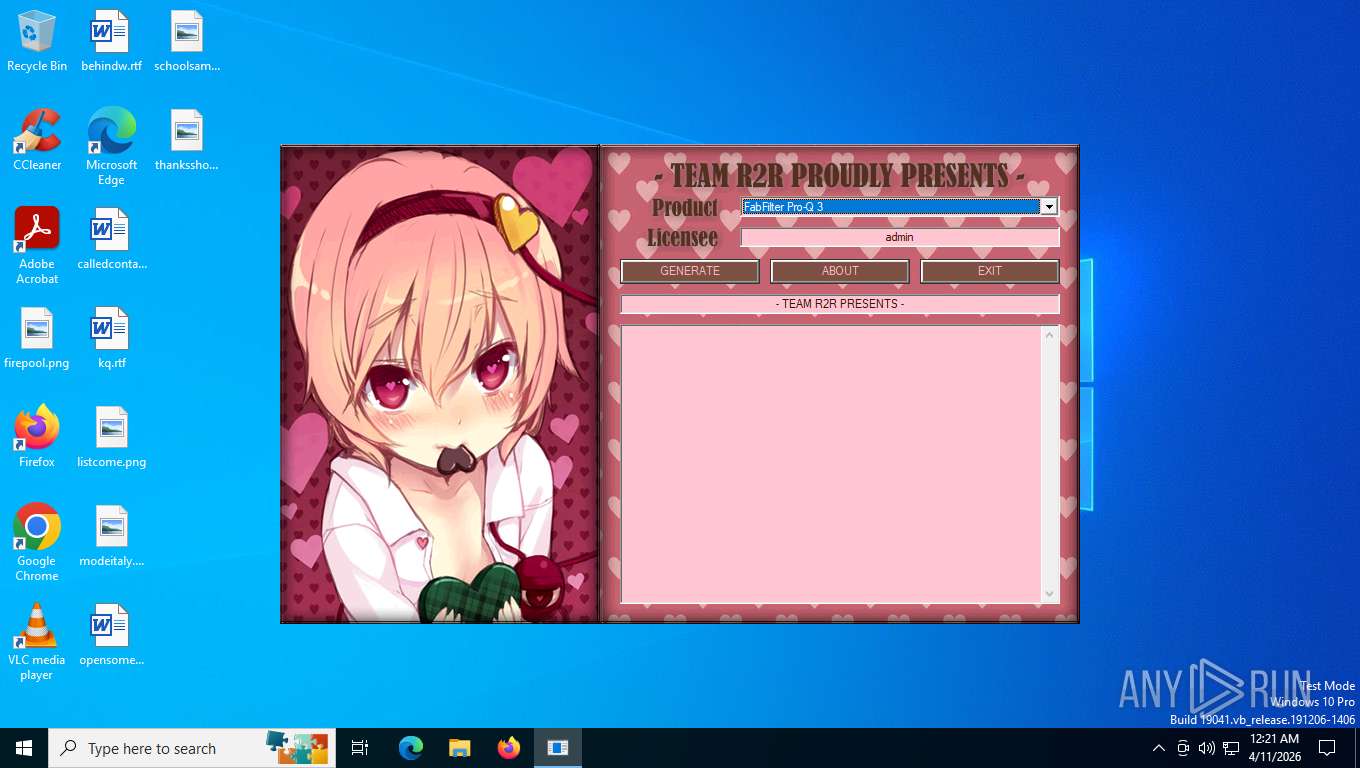
MALICIOUS
R2RKEYGEN has been detected
- FabFilter_KeyGen.exe (PID: 6412)
SUSPICIOUS
Executable content was dropped or overwritten
- FabFilter_KeyGen.exe (PID: 6412)
INFO
Checks supported languages
- FabFilter_KeyGen.exe (PID: 6412)
- keygen.exe (PID: 4328)
Create files in a temporary directory
- FabFilter_KeyGen.exe (PID: 6412)
- keygen.exe (PID: 4328)
Reads the computer name
- keygen.exe (PID: 4328)
There is functionality for taking screenshot (YARA)
- FabFilter_KeyGen.exe (PID: 6412)
- keygen.exe (PID: 4328)
Reads the machine GUID from the registry
- keygen.exe (PID: 4328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 22:50:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
128
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4328 | C:\Users\admin\AppData\Local\Temp\keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | — | FabFilter_KeyGen.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6412 | "C:\Users\admin\AppData\Local\Temp\FabFilter_KeyGen.exe" | C:\Users\admin\AppData\Local\Temp\FabFilter_KeyGen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6988 | "C:\Users\admin\AppData\Local\Temp\FabFilter_KeyGen.exe" | C:\Users\admin\AppData\Local\Temp\FabFilter_KeyGen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
348
Read events
348
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4328 | keygen.exe | C:\Users\admin\AppData\Local\Temp\~DF6078B24F9F22FF2E.TMP | binary | |
MD5:4BC6F7D5EDBD026CC863BB5A038354F7 | SHA256:D0AF7484C3D1459EB6160D13430BB2202B6A7AEAAF077243E59E47ABB86D5885 | |||
| 6412 | FabFilter_KeyGen.exe | C:\Users\admin\AppData\Local\Temp\bgm.it | binary | |
MD5:5E3C083251880C635F5EA6A0A6ED8E76 | SHA256:9D460A48D7F7F461967C9065182456871606EEF1C27F21767335B7D81384E141 | |||
| 6412 | FabFilter_KeyGen.exe | C:\Users\admin\AppData\Local\Temp\BASSMOD.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 6412 | FabFilter_KeyGen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | executable | |
MD5:D1DFFD39A24E6DBB3900009CA1CE9138 | SHA256:F6445A70DACB174D81CB012315C03C4D529FBD5FC514E072708684D3B7E095F4 | |||
| 6412 | FabFilter_KeyGen.exe | C:\Users\admin\AppData\Local\Temp\R2RFBFKG.dll | executable | |
MD5:D9E603D8B6056C2E73C6AFAEE27E826F | SHA256:3245C4C10193826BDD307AF6F8208C4D7C8E3C8D41D31EAA0F7EEB34F3D339DC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
18
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
3280 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
3280 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | US | binary | 400 b | whitelisted |
3280 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 400 b | whitelisted |
3280 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | US | binary | 813 b | whitelisted |
6076 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
3280 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
3280 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | NL | binary | 824 b | whitelisted |
3280 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6076 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3280 | svchost.exe | 72.246.29.11:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3280 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |