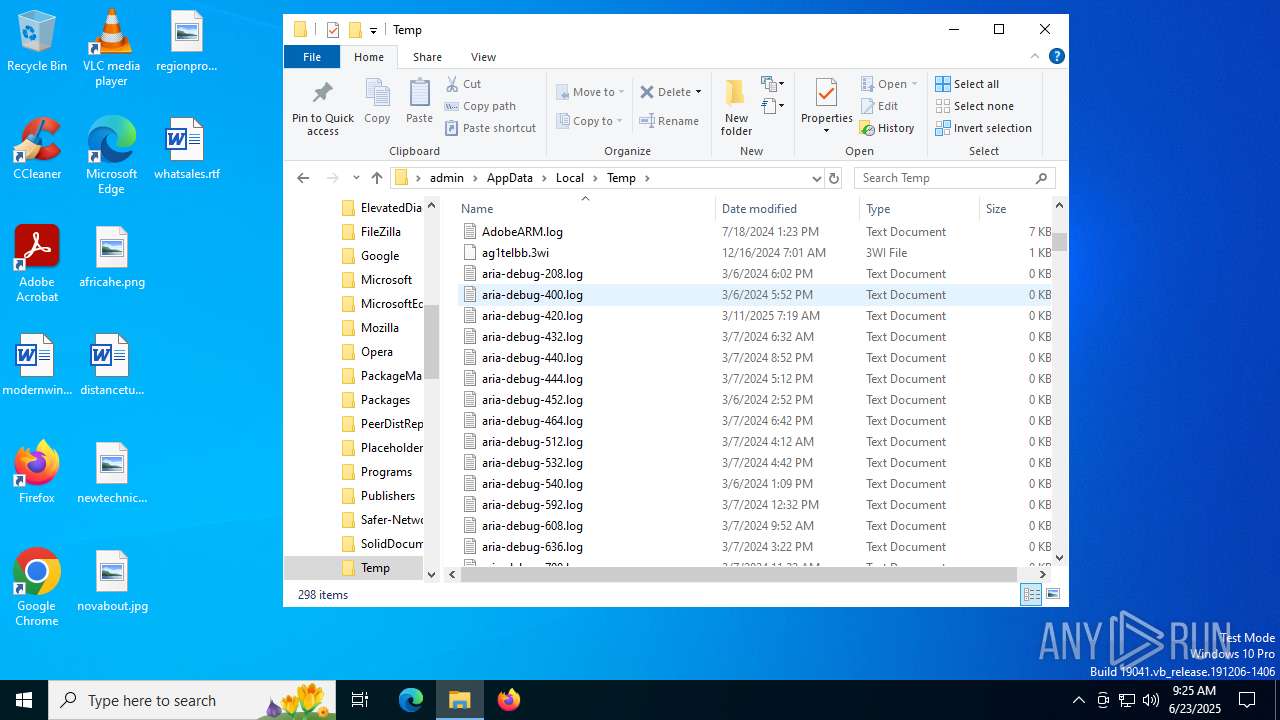
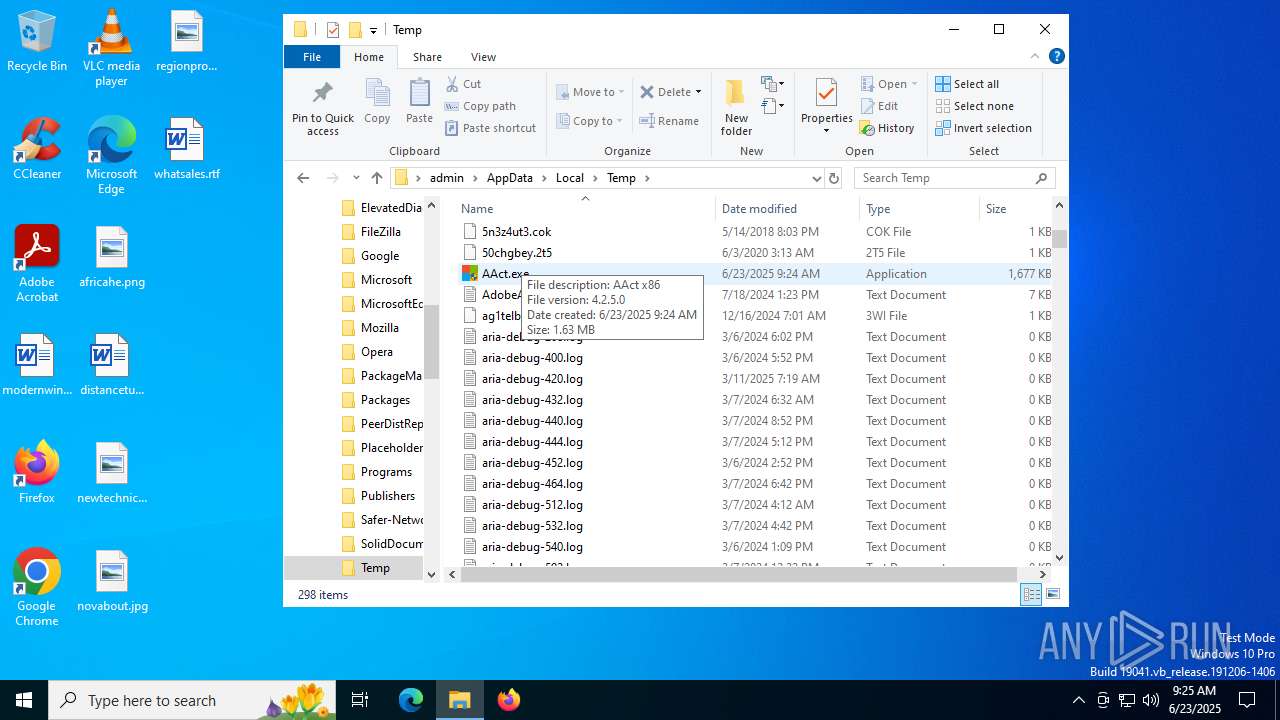
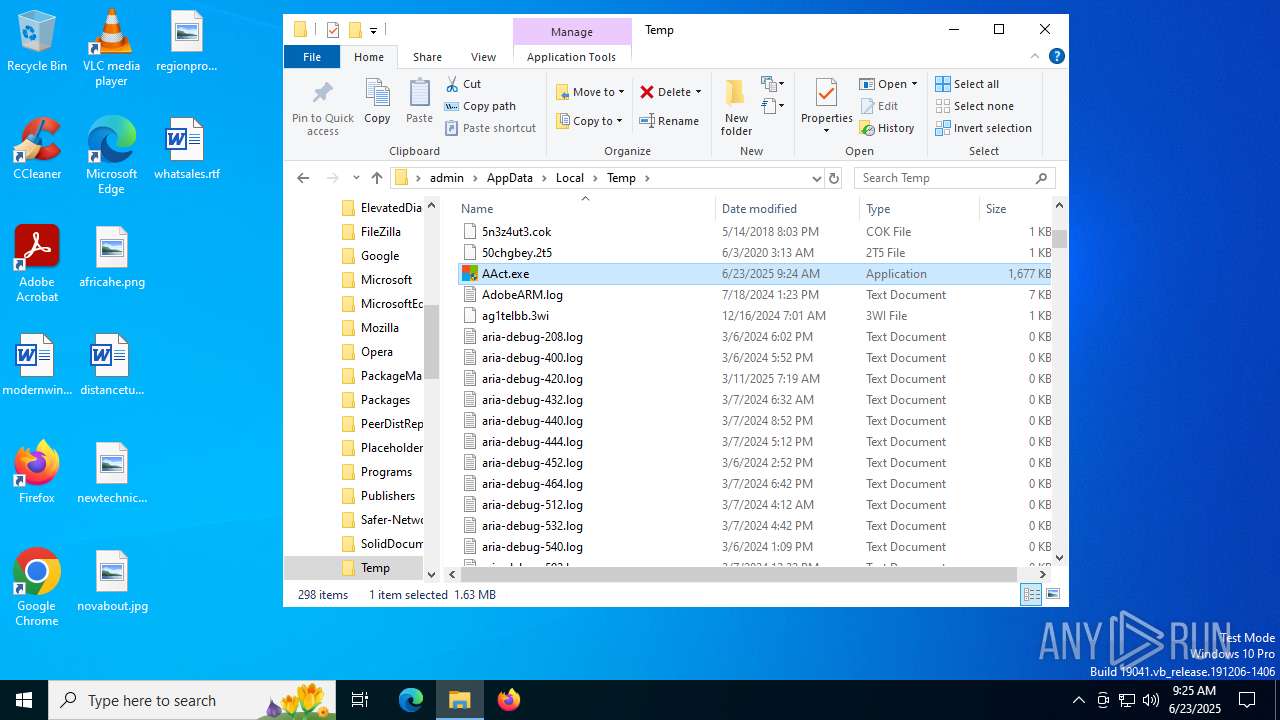
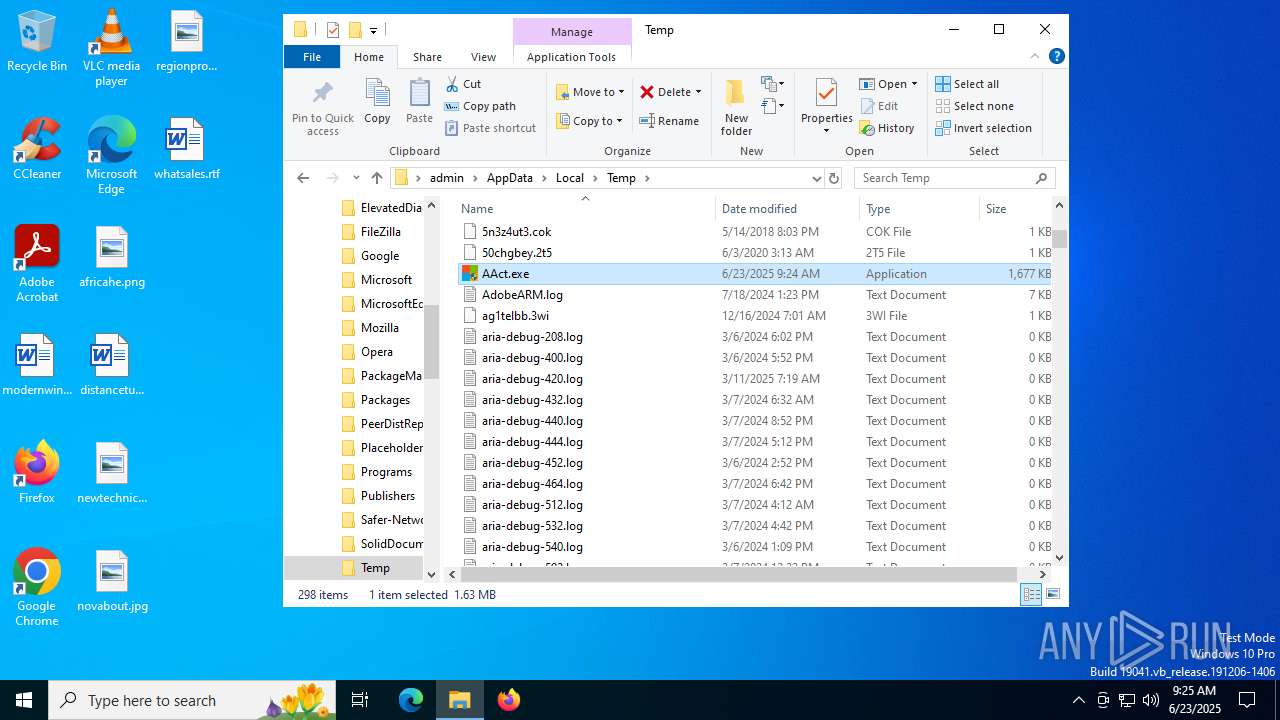
| File name: | AAct.exe |
| Full analysis: | https://app.any.run/tasks/acb33c18-d6e2-48f3-98a0-40ff89c9f7d2 |
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2025, 09:24:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 0012A31A595AE876B7D3CC8917CE592B |
| SHA1: | 6D3D4EDC330AEFB324F200F981DEB1AFC327A65C |
| SHA256: | 82A277A54A5F519C2B06C55D73D900ED49969673AD62E3D056BA520F09B2EC09 |
| SSDEEP: | 49152:f5hmZ4bcNXMi0eTWWJHXQ7wzgDnAHDbXT8:RhmTqiTnJHXKwzgDnAjbXT8 |
MALICIOUS
Executing a file with an untrusted certificate
- AAct.exe (PID: 3864)
- AAct.exe (PID: 7152)
- AAct.exe (PID: 4512)
- AAct.exe (PID: 7056)
- AAct.exe (PID: 4312)
SUSPICIOUS
Starts CMD.EXE for commands execution
- AAct.exe (PID: 7152)
- AAct.exe (PID: 4512)
- AAct.exe (PID: 4312)
Found strings related to reading or modifying Windows Defender settings
- AAct.exe (PID: 7152)
- AAct.exe (PID: 4512)
- AAct.exe (PID: 4312)
The process executes via Task Scheduler
- updater.exe (PID: 3572)
Application launched itself
- updater.exe (PID: 3572)
INFO
Reads product name
- AAct.exe (PID: 7152)
- AAct.exe (PID: 4512)
- AAct.exe (PID: 4312)
Checks supported languages
- AAct.exe (PID: 7152)
- AAct.exe (PID: 4512)
- AAct.exe (PID: 4312)
- updater.exe (PID: 3572)
- updater.exe (PID: 1296)
Reads Environment values
- AAct.exe (PID: 7152)
- AAct.exe (PID: 4512)
- AAct.exe (PID: 4312)
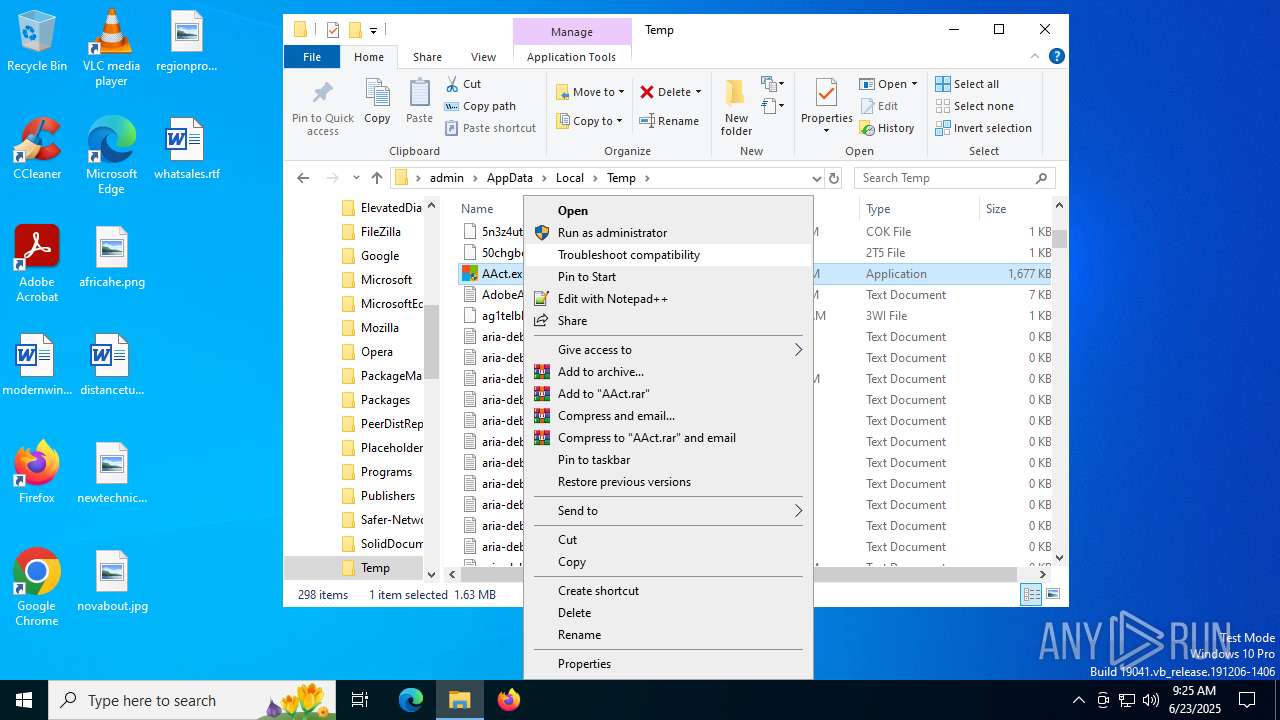
Manual execution by a user
- AAct.exe (PID: 7056)
- AAct.exe (PID: 4512)
- AAct.exe (PID: 4312)
Reads the computer name
- updater.exe (PID: 3572)
Process checks whether UAC notifications are on
- updater.exe (PID: 3572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:12:01 08:41:49+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 1634304 |
| InitializedDataSize: | 73728 |
| UninitializedDataSize: | 1392640 |
| EntryPoint: | 0x2e3b90 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.2.5.0 |
| ProductVersionNumber: | 4.2.5.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | AAct x86 |
Total processes
151
Monitored processes
12
Malicious processes
3
Suspicious processes
2
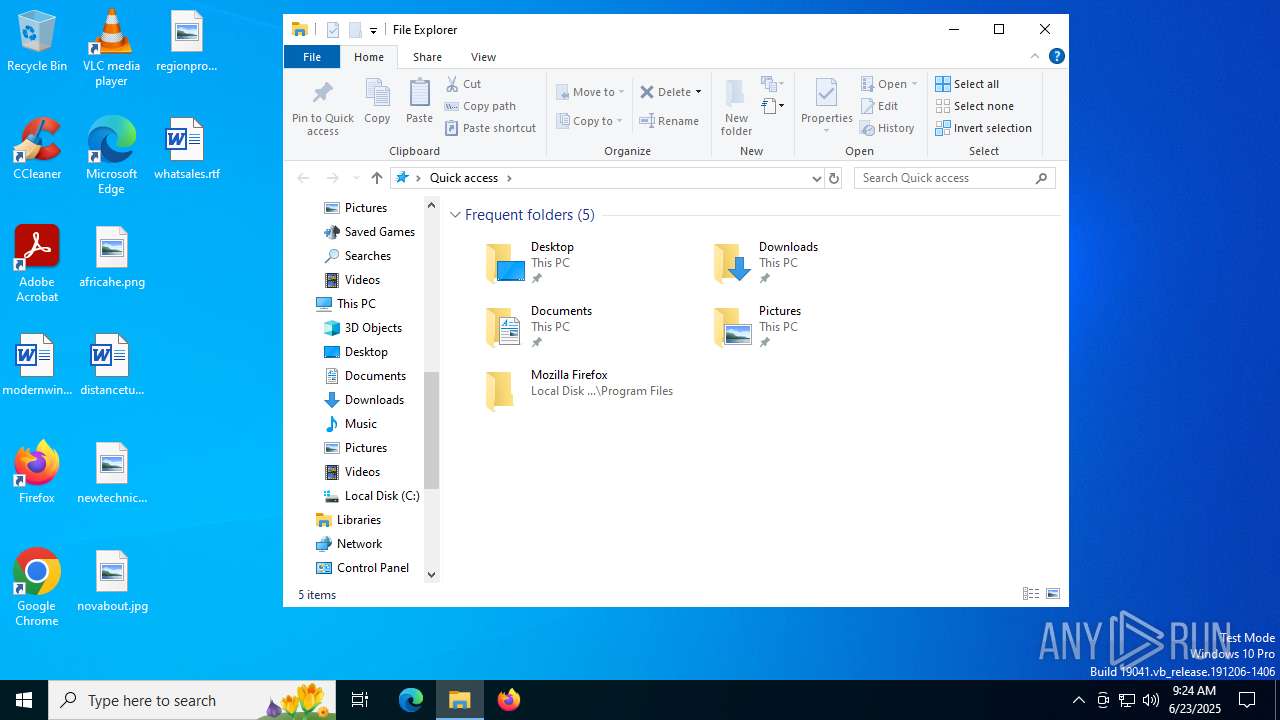
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x298,0x29c,0x2a0,0x274,0x2a4,0x111c460,0x111c46c,0x111c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
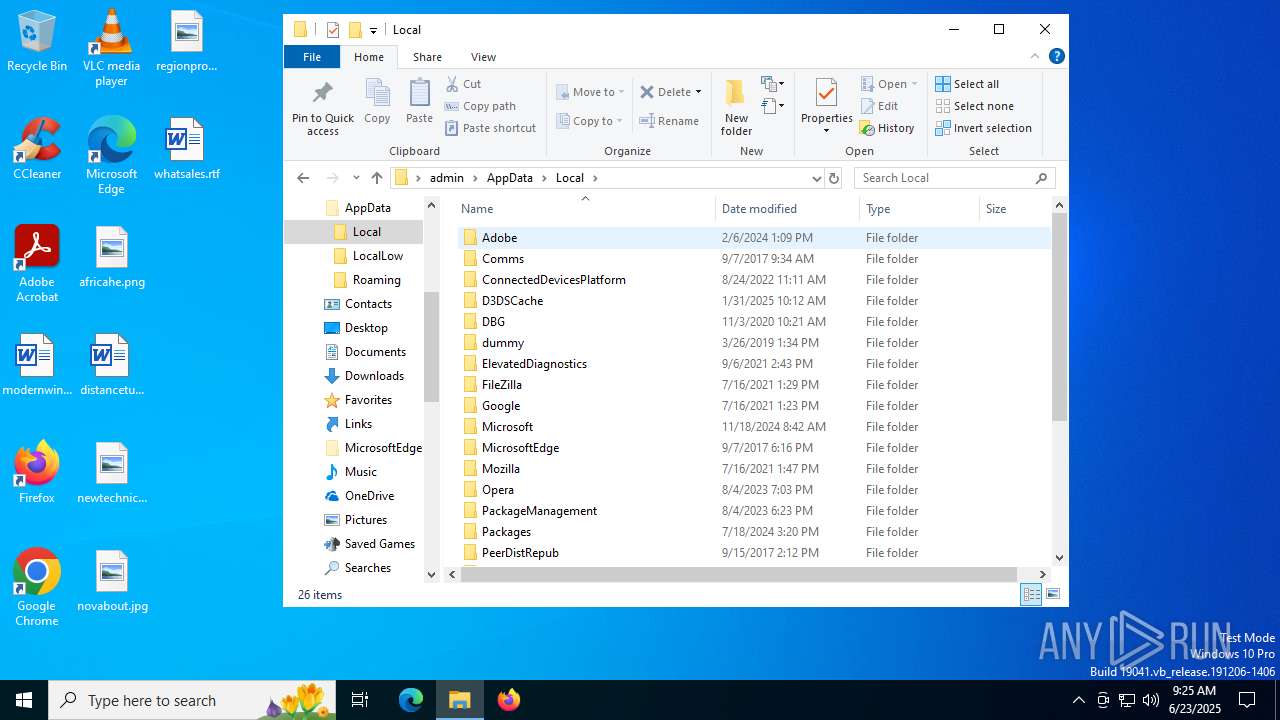
| 3556 | "C:\WINDOWS\Sysnative\cmd.exe" /c WMIC /NAMESPACE:\\root\Microsoft\Windows\Defender PATH MSFT_MpPreference call Add ExclusionPath="C:\Users\admin\AppData\Local\Temp\AAct.exe" | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225738 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3572 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
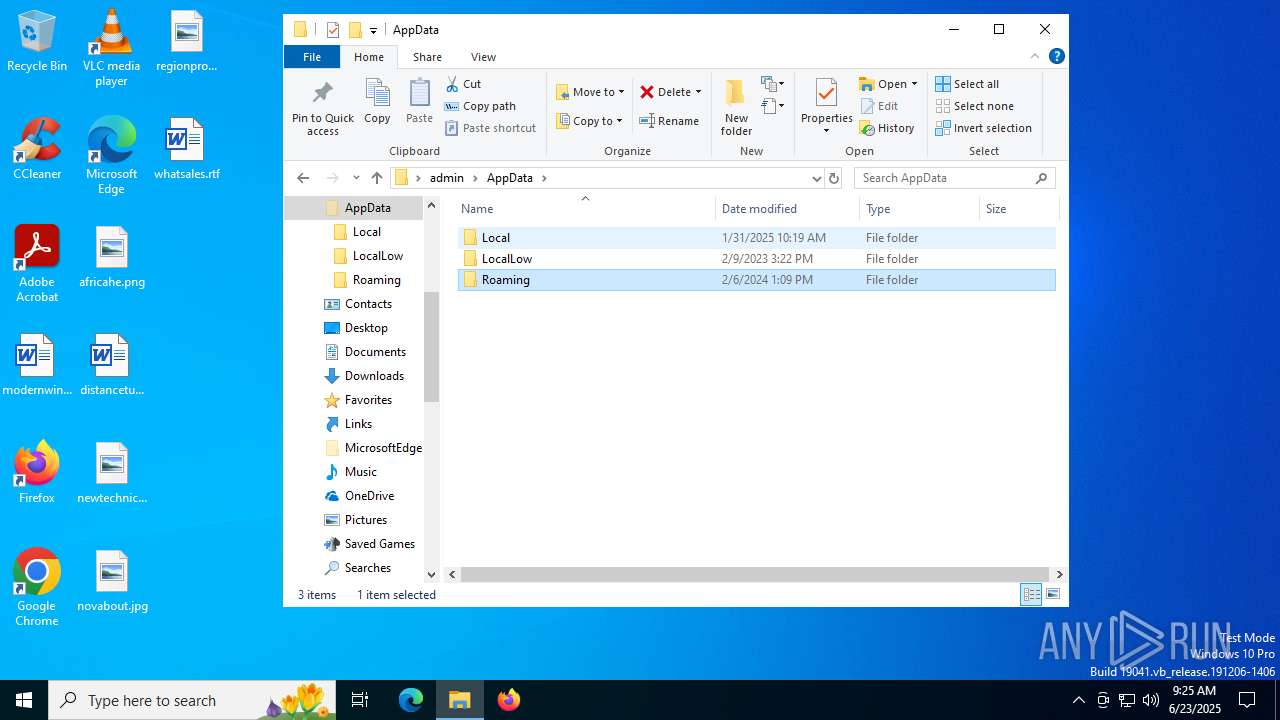
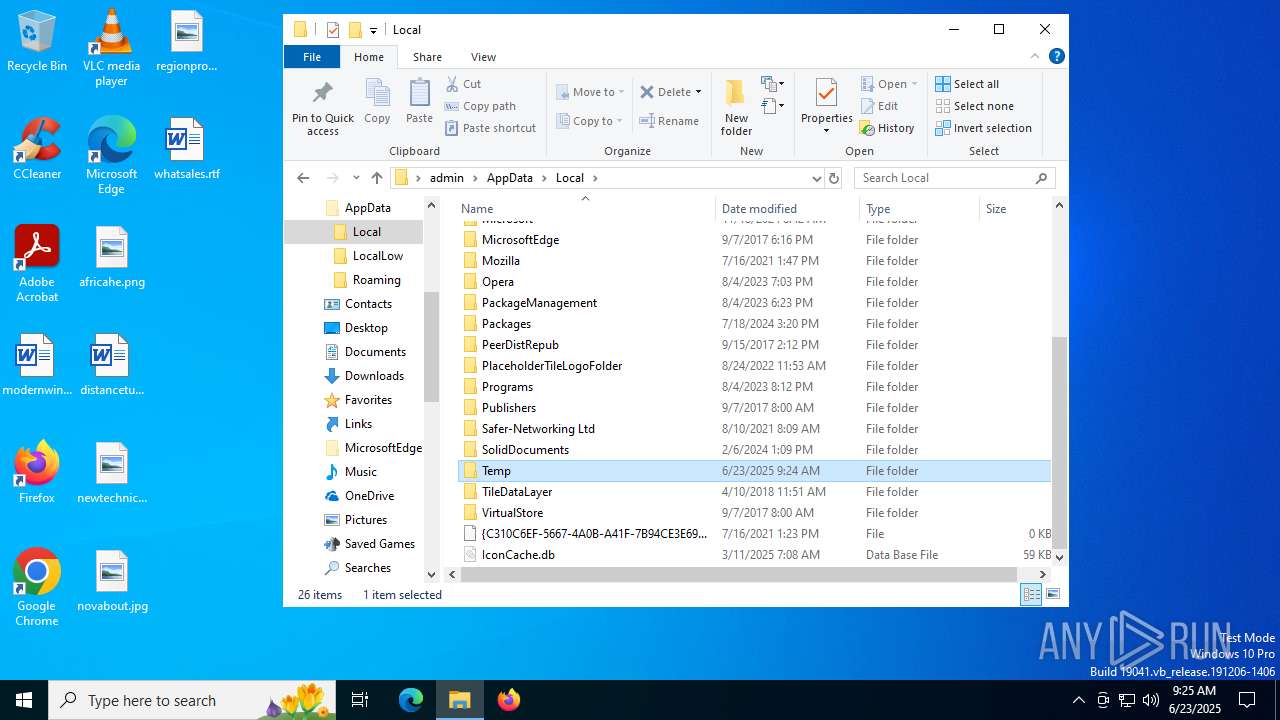
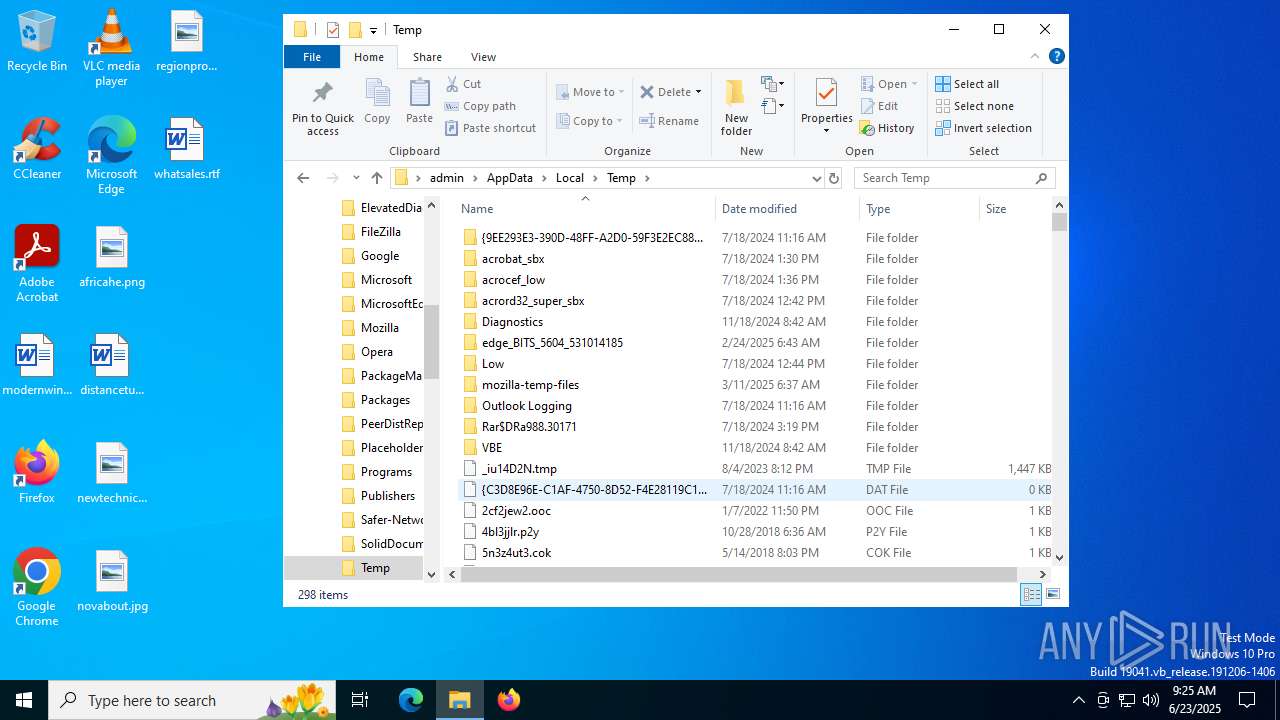
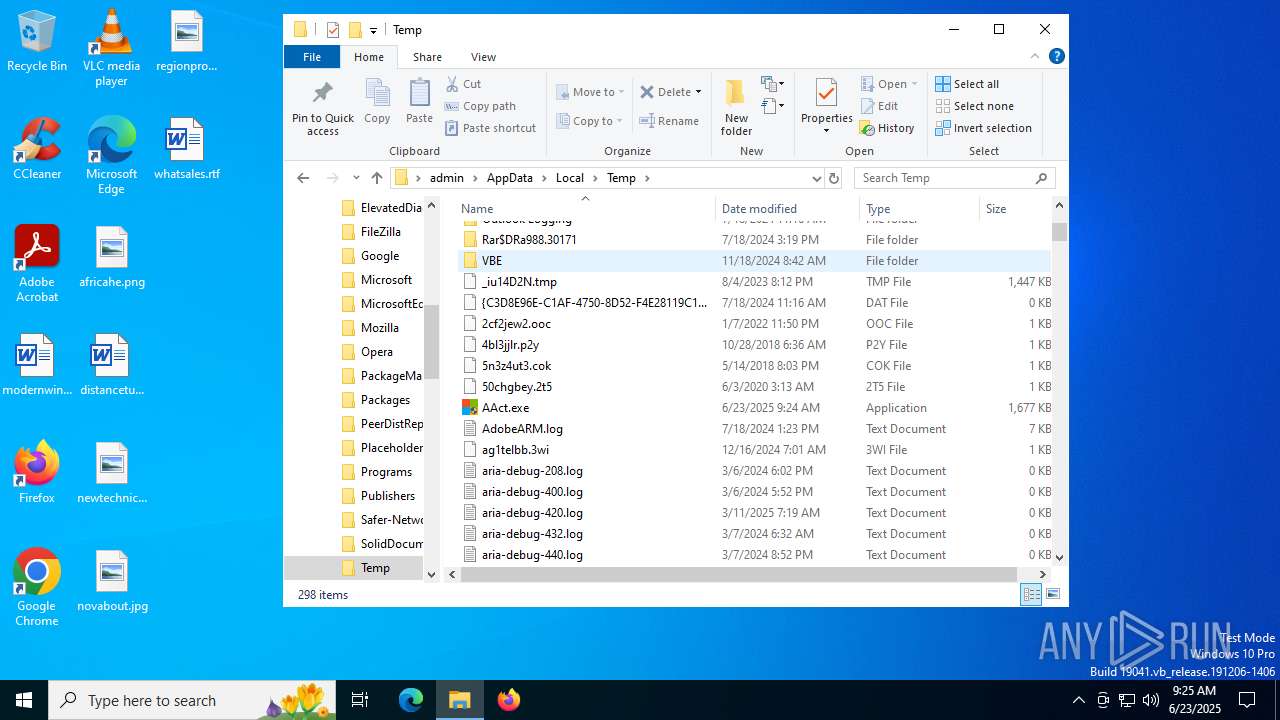
| 3864 | "C:\Users\admin\AppData\Local\Temp\AAct.exe" | C:\Users\admin\AppData\Local\Temp\AAct.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AAct x86 Exit code: 3221226540 Modules
| |||||||||||||||
| 4040 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4236 | "C:\WINDOWS\Sysnative\cmd.exe" /c WMIC /NAMESPACE:\\root\Microsoft\Windows\Defender PATH MSFT_MpPreference call Add ExclusionPath="C:\Users\admin\AppData\Local\Temp\AAct.exe" | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225738 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4312 | "C:\Users\admin\AppData\Local\Temp\AAct.exe" | C:\Users\admin\AppData\Local\Temp\AAct.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AAct x86 Exit code: 0 Modules
| |||||||||||||||
| 4512 | "C:\Users\admin\AppData\Local\Temp\AAct.exe" | C:\Users\admin\AppData\Local\Temp\AAct.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AAct x86 Exit code: 0 Modules
| |||||||||||||||
| 5416 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | "C:\WINDOWS\Sysnative\cmd.exe" /c WMIC /NAMESPACE:\\root\Microsoft\Windows\Defender PATH MSFT_MpPreference call Add ExclusionPath="C:\Users\admin\AppData\Local\Temp\AAct.exe" | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225738 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
385
Read events
384
Write events
1
Delete events
0
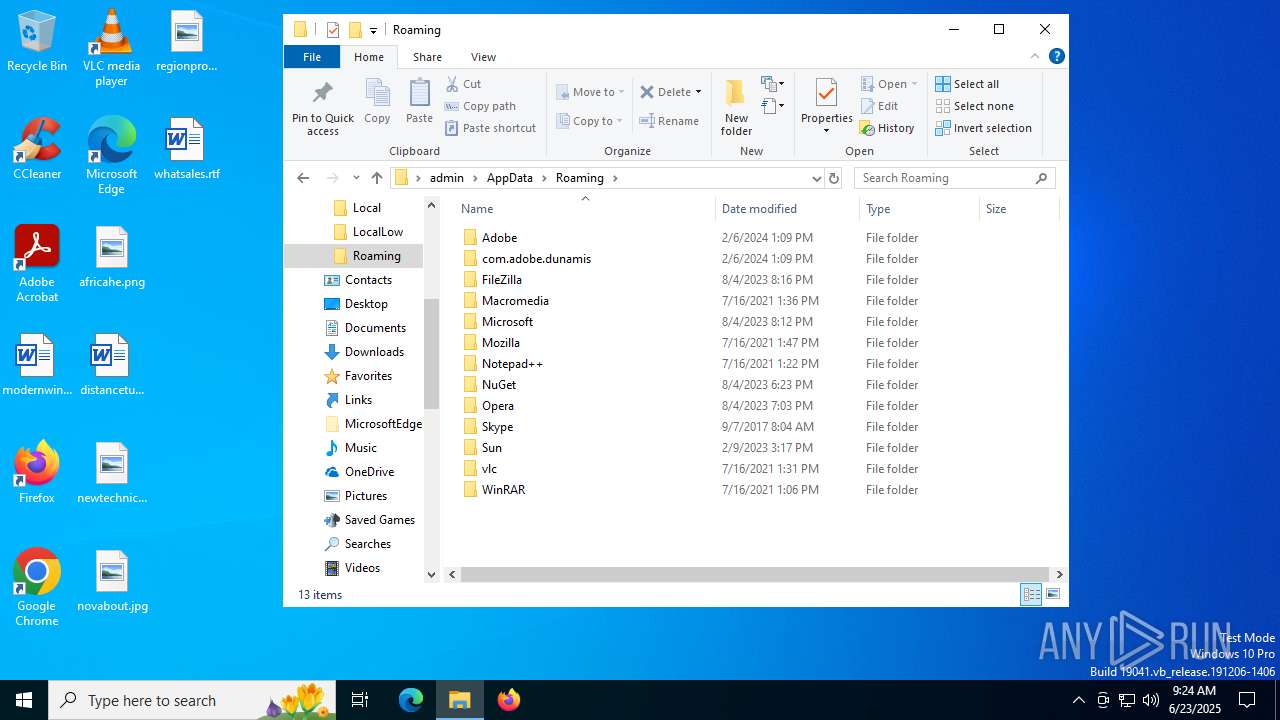
Modification events
| (PID) Process: | (7152) AAct.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
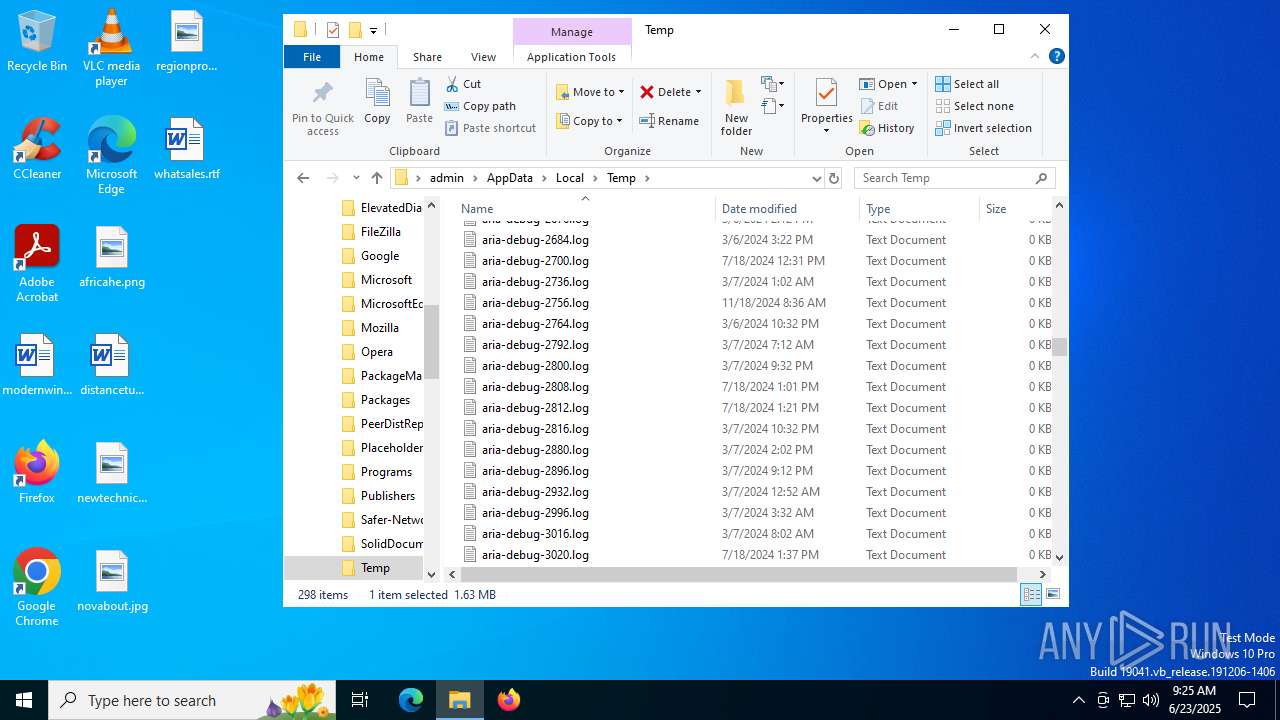
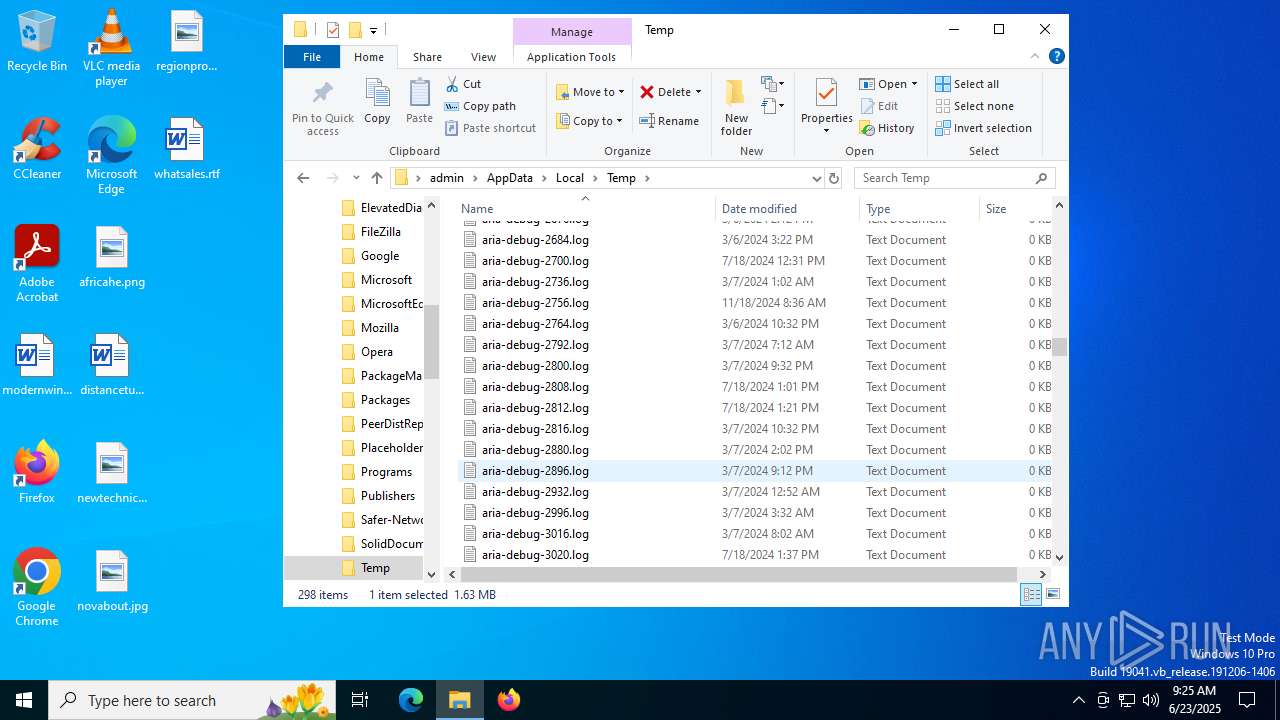
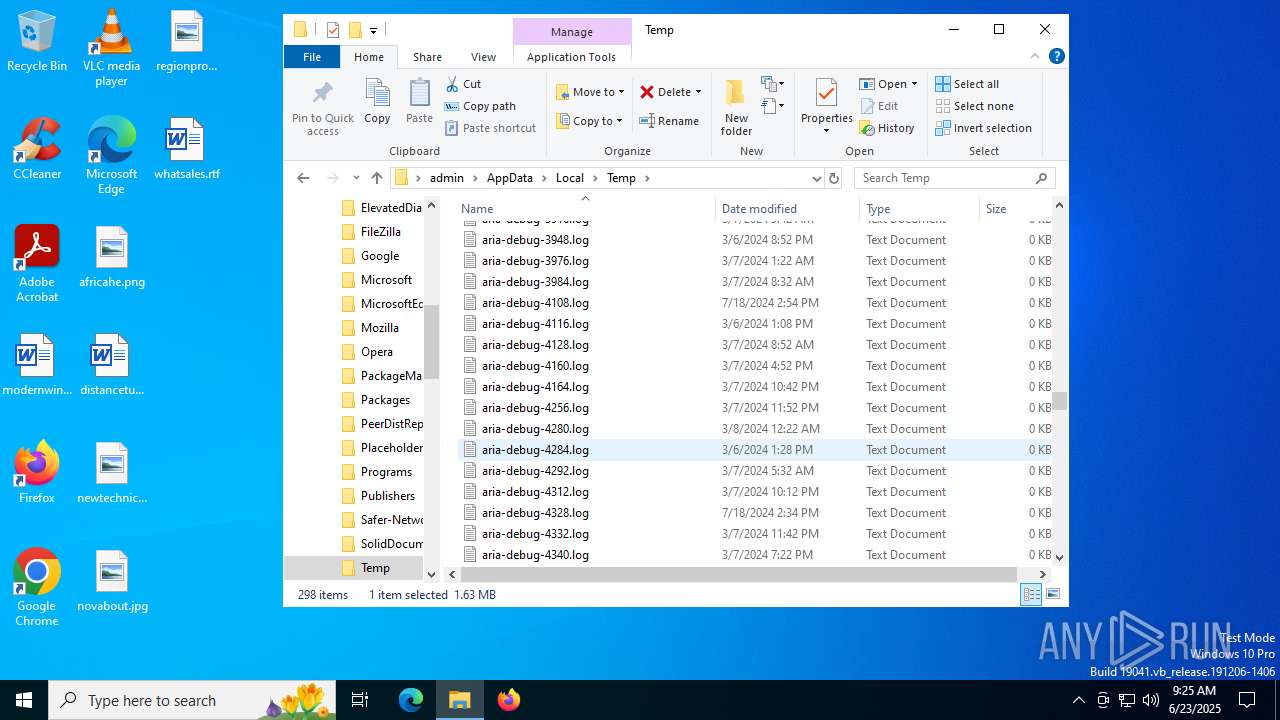
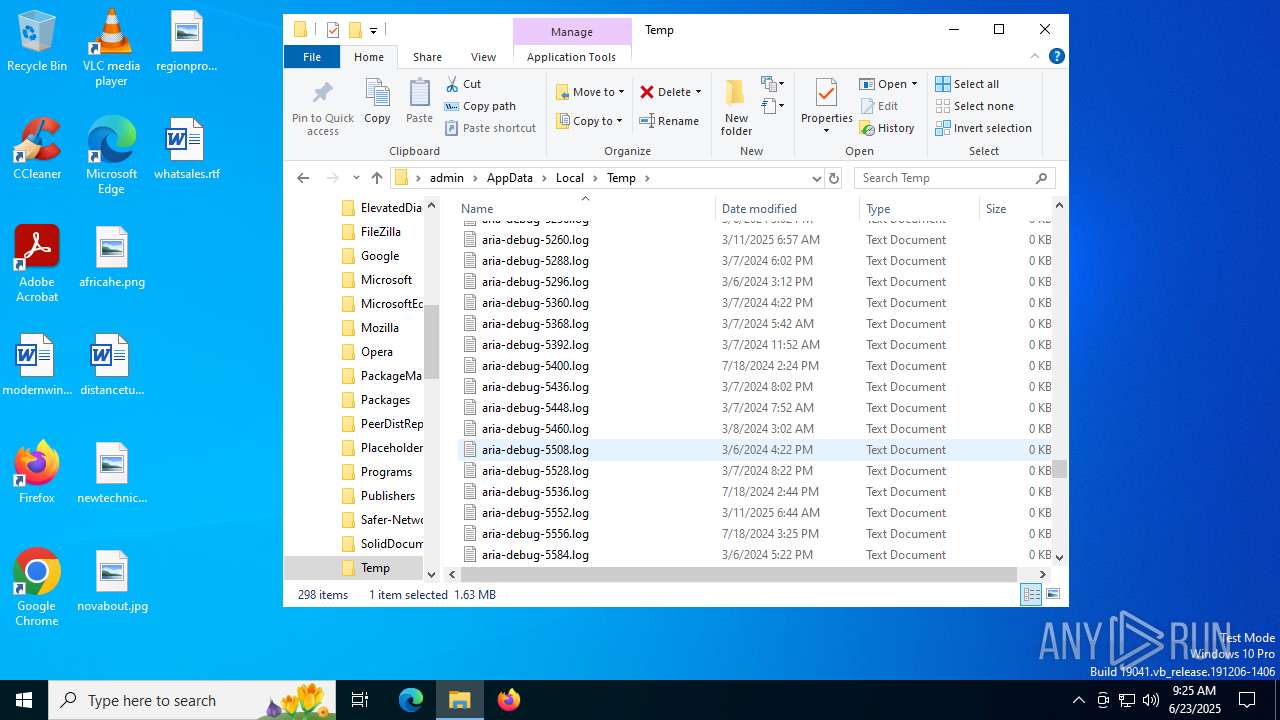
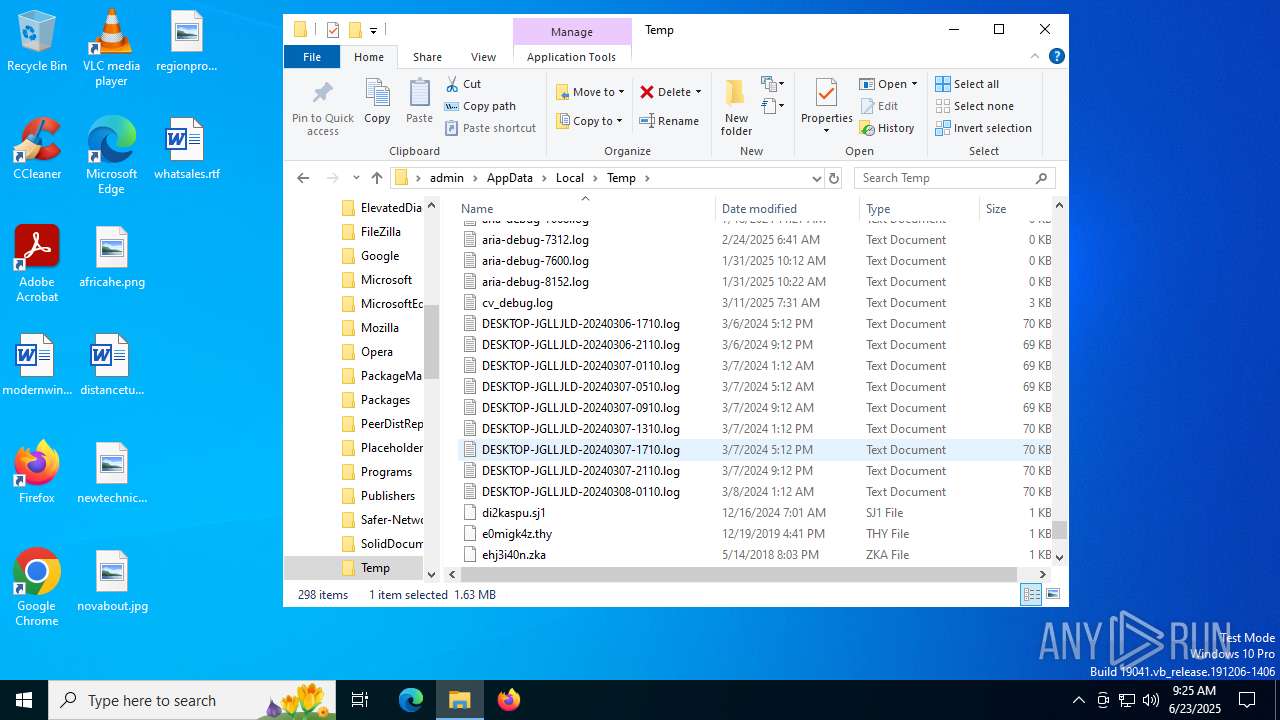
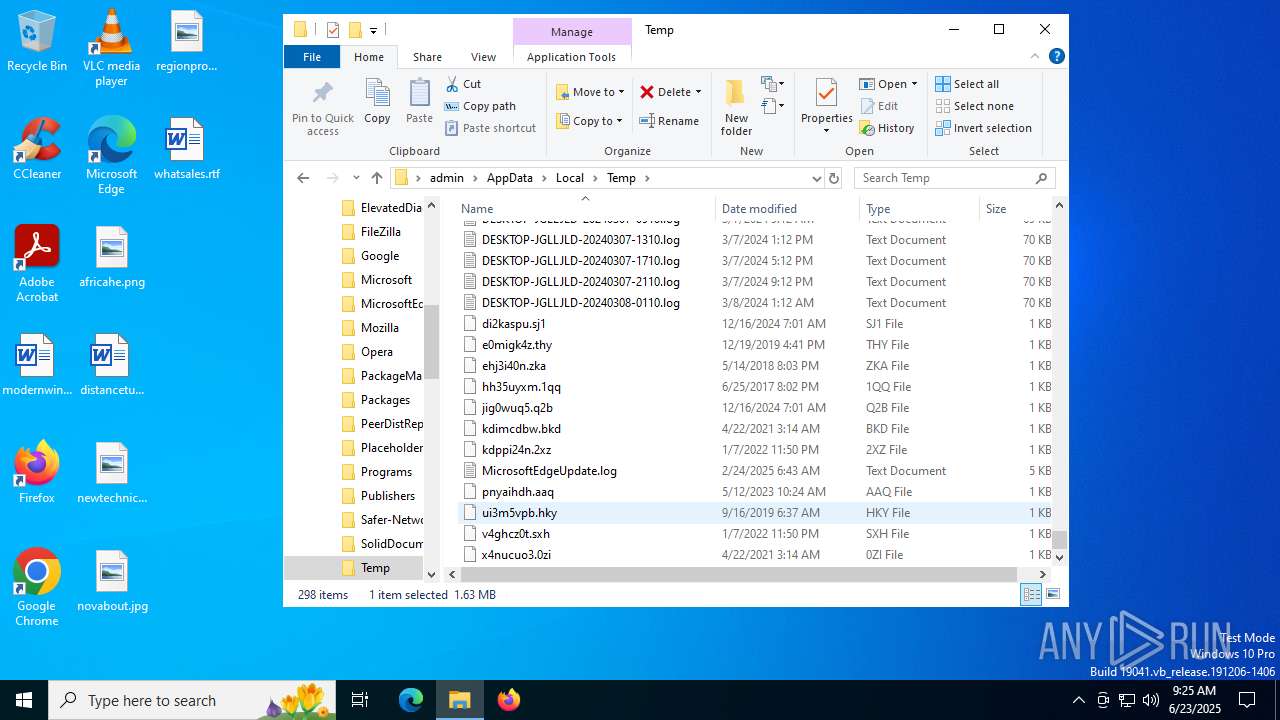
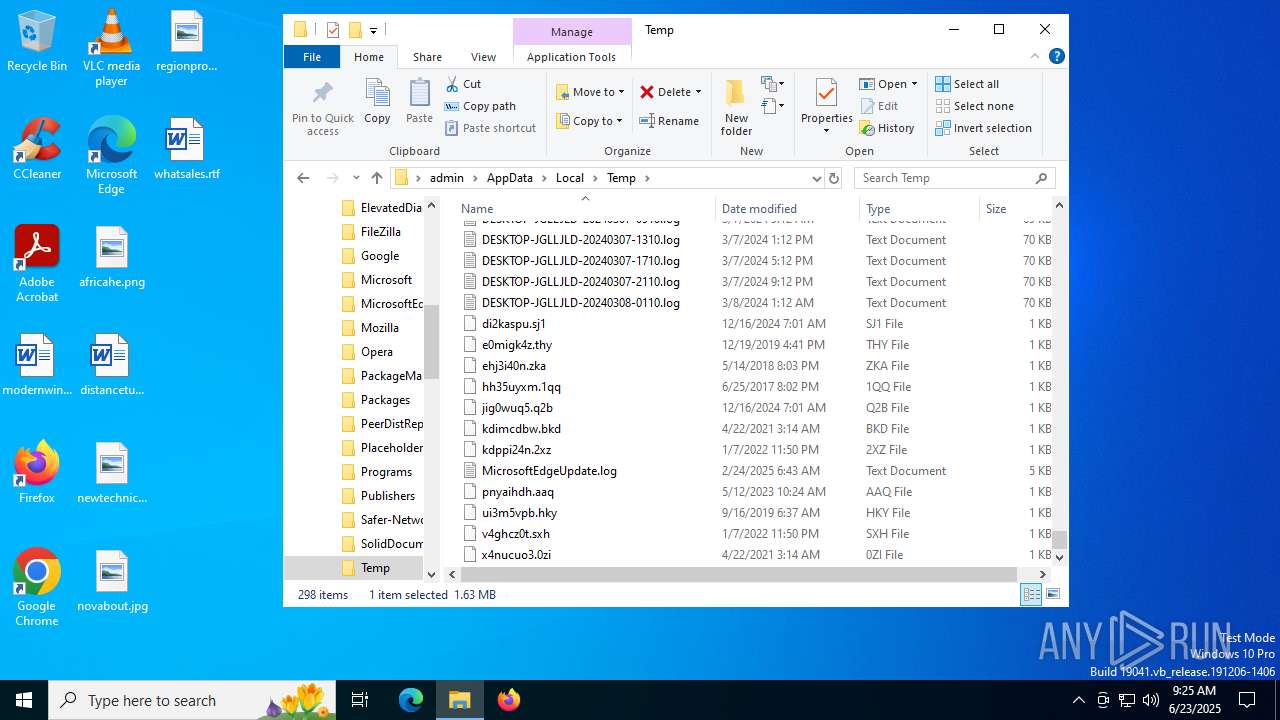
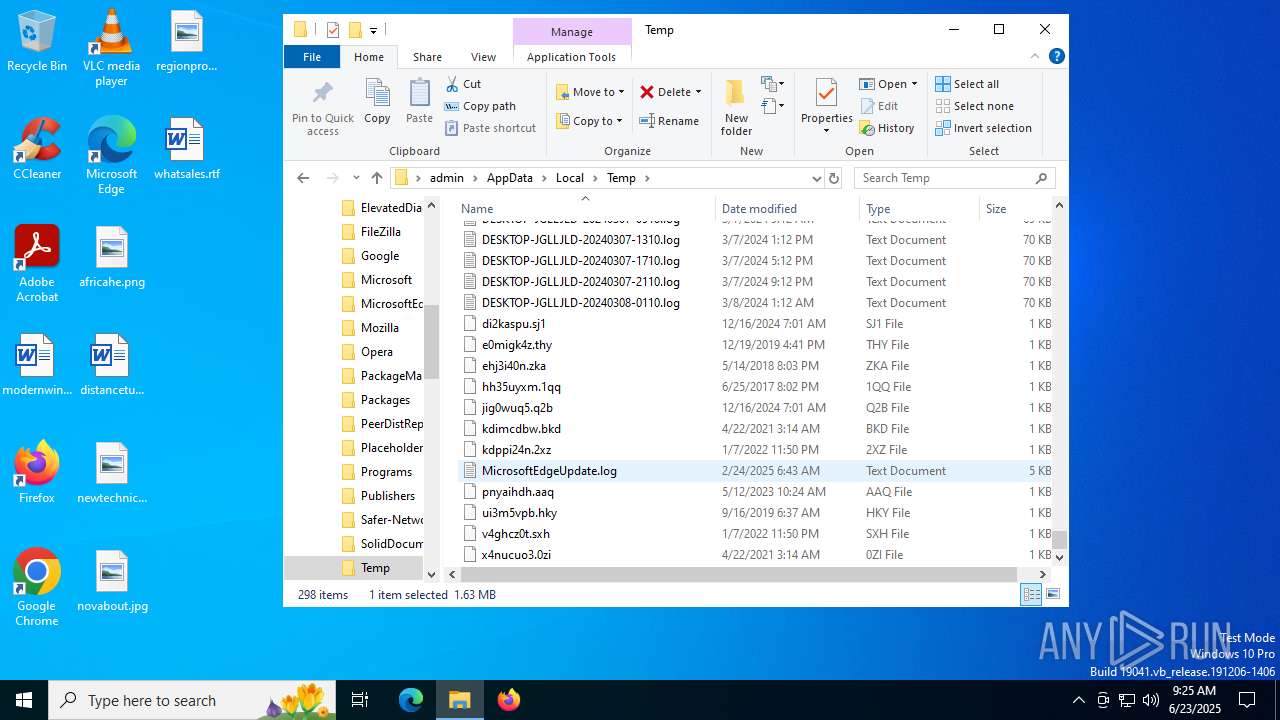
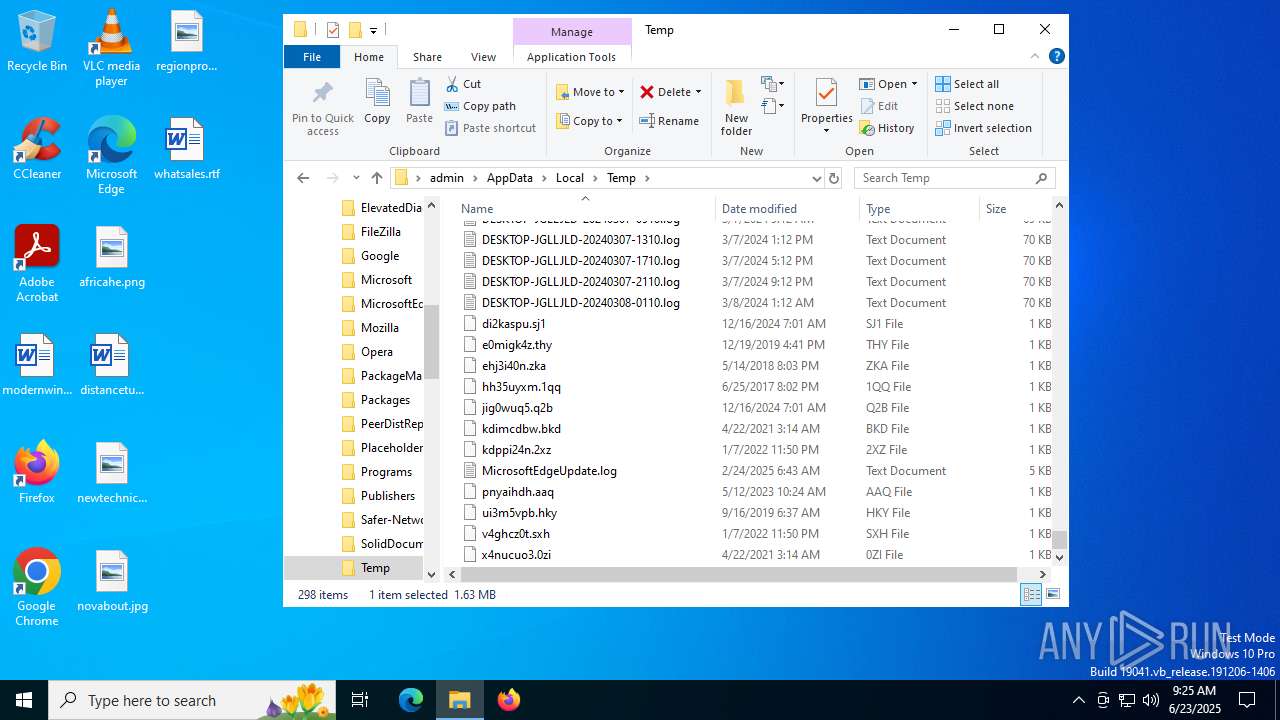
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\updater.log | text | |
MD5:F401297EE0E72856565C127EE72C1D60 | SHA256:CF9FECB5919D776E6B092D007973C166A976CB495DF7DF37BB877126BCFF0E93 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5012 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3608 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
3608 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7052 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.55.104.172:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5012 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |