| File name: | 829bd472dddfec080fa4ca9481610bff90a116af3d4c8e7b3c78a1d22c89eb8c |
| Full analysis: | https://app.any.run/tasks/1337543d-cc06-49c5-98bf-07a796790622 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 13:54:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B0BFDC4760ABDB351A1F192AE3C627B0 |
| SHA1: | 0904B4FF63E9F82E1FB2DFC4AF832FDB914D39D3 |
| SHA256: | 829BD472DDDFEC080FA4CA9481610BFF90A116AF3D4C8E7B3C78A1D22C89EB8C |
| SSDEEP: | 768:ZH7FJl5/ija+1I21wB3Ehri99Mm4laPeDO:ZbFJiw5EM99DPeDO |
MALICIOUS
No malicious indicators.SUSPICIOUS
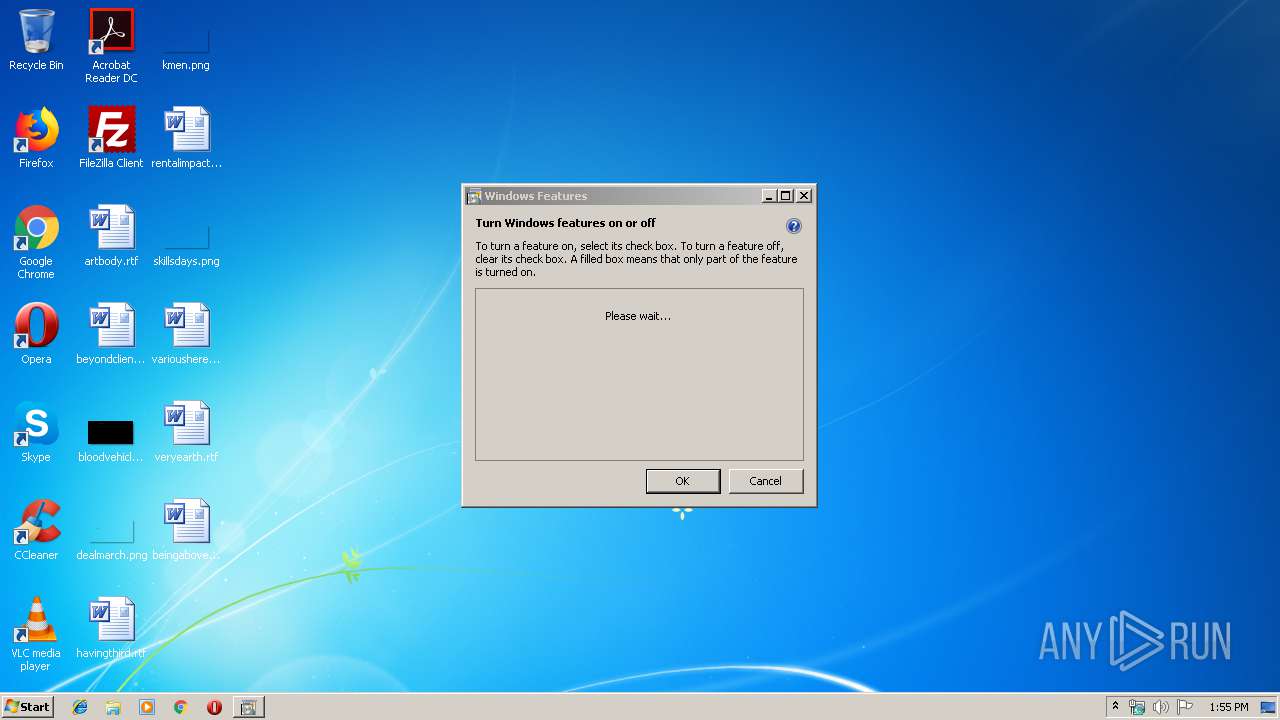
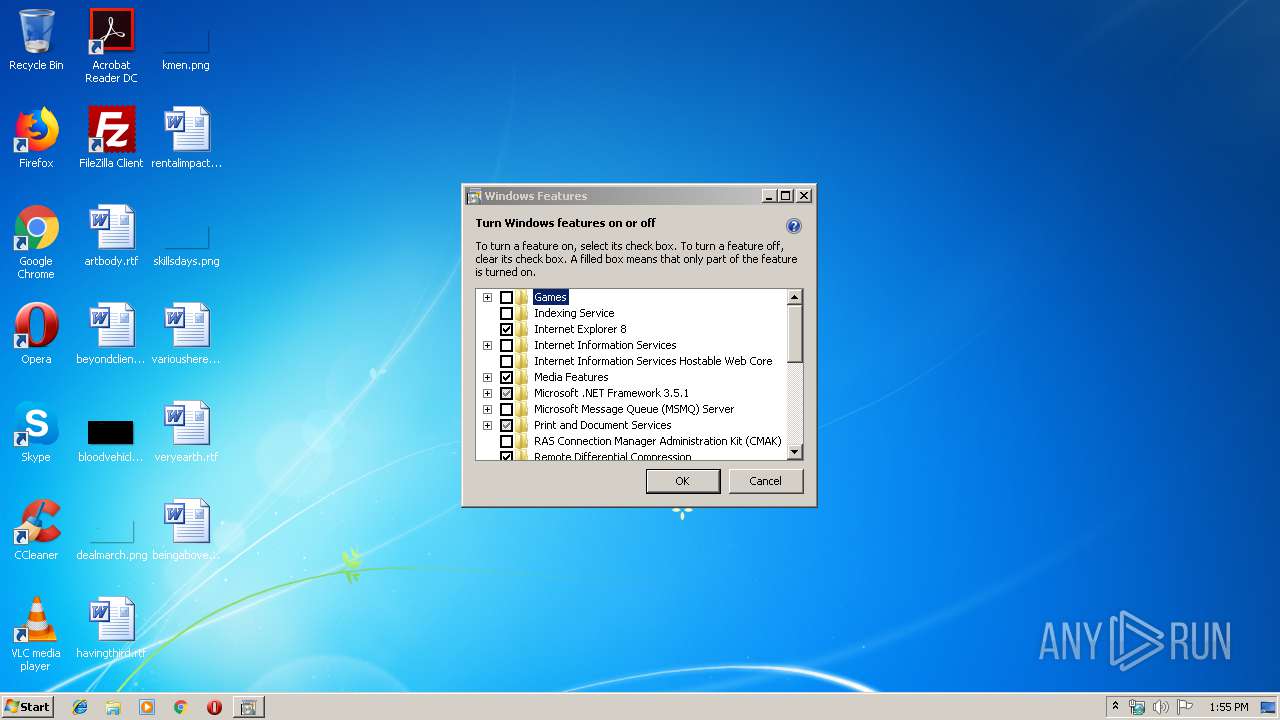
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 2116)
Starts CMD.EXE for commands execution
- 829bd472dddfec080fa4ca9481610bff90a116af3d4c8e7b3c78a1d22c89eb8c.exe (PID: 1712)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2116)
Executed as Windows Service
- vssvc.exe (PID: 3476)
INFO
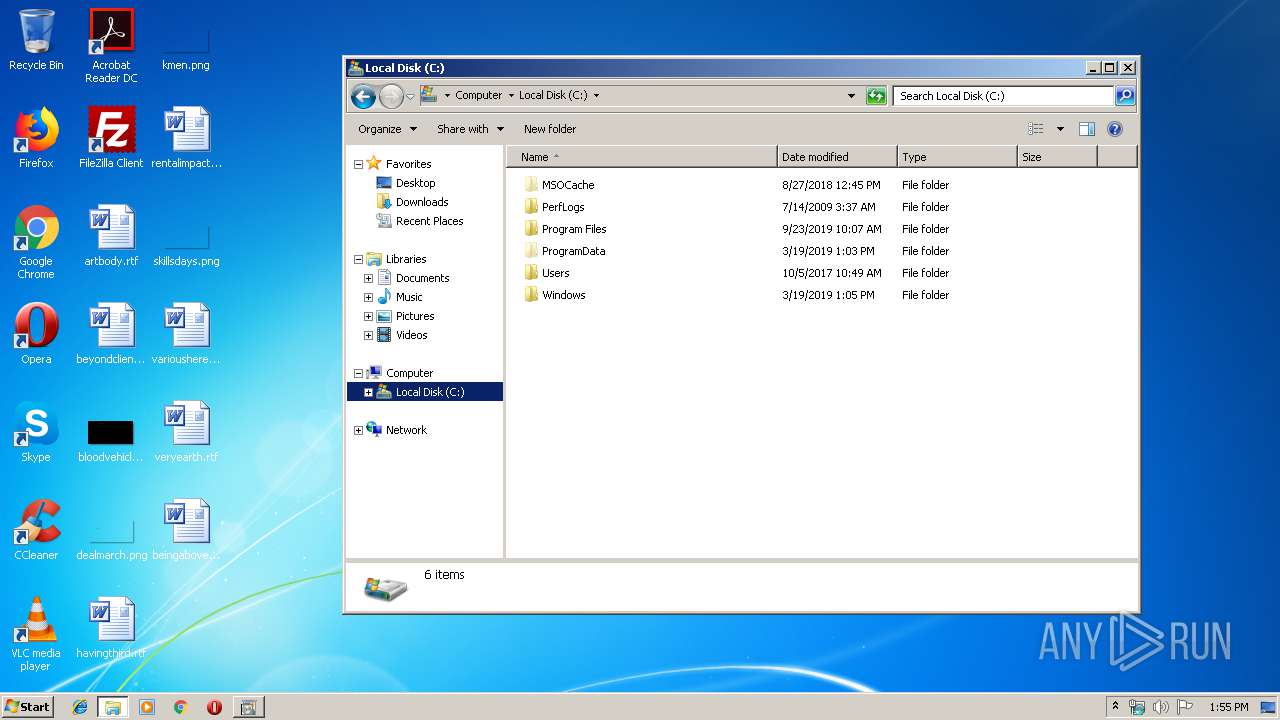
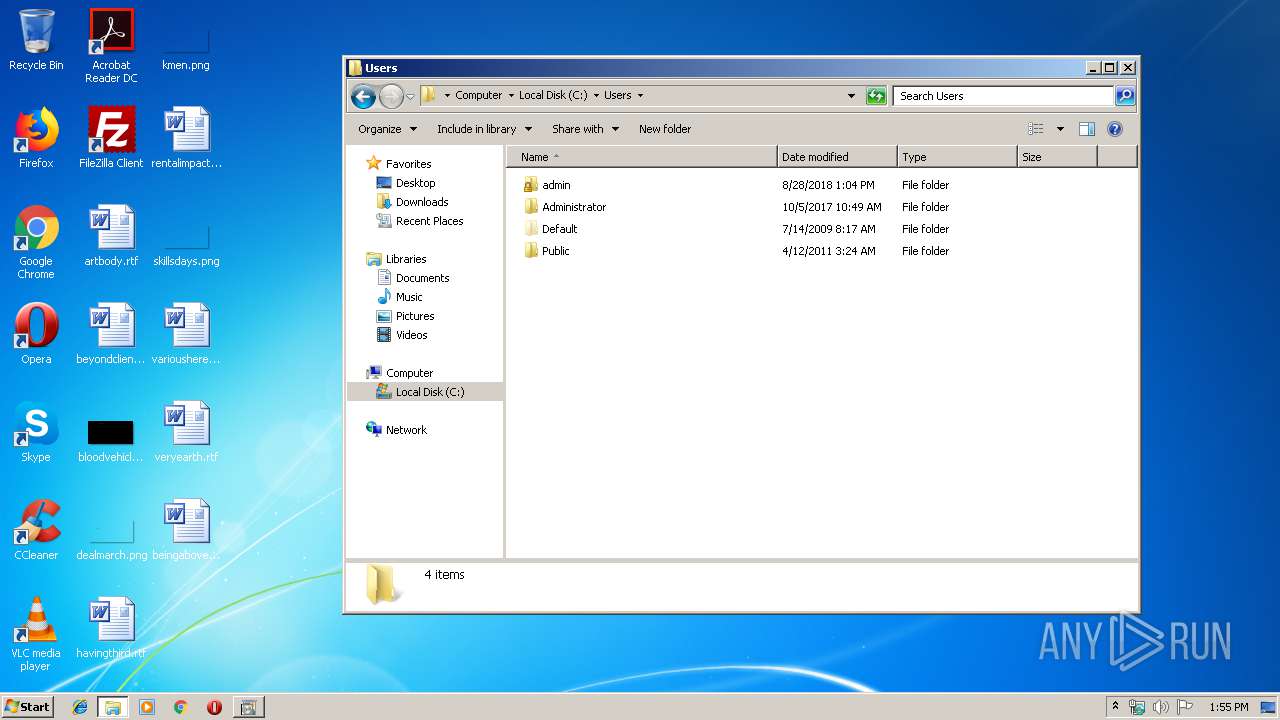
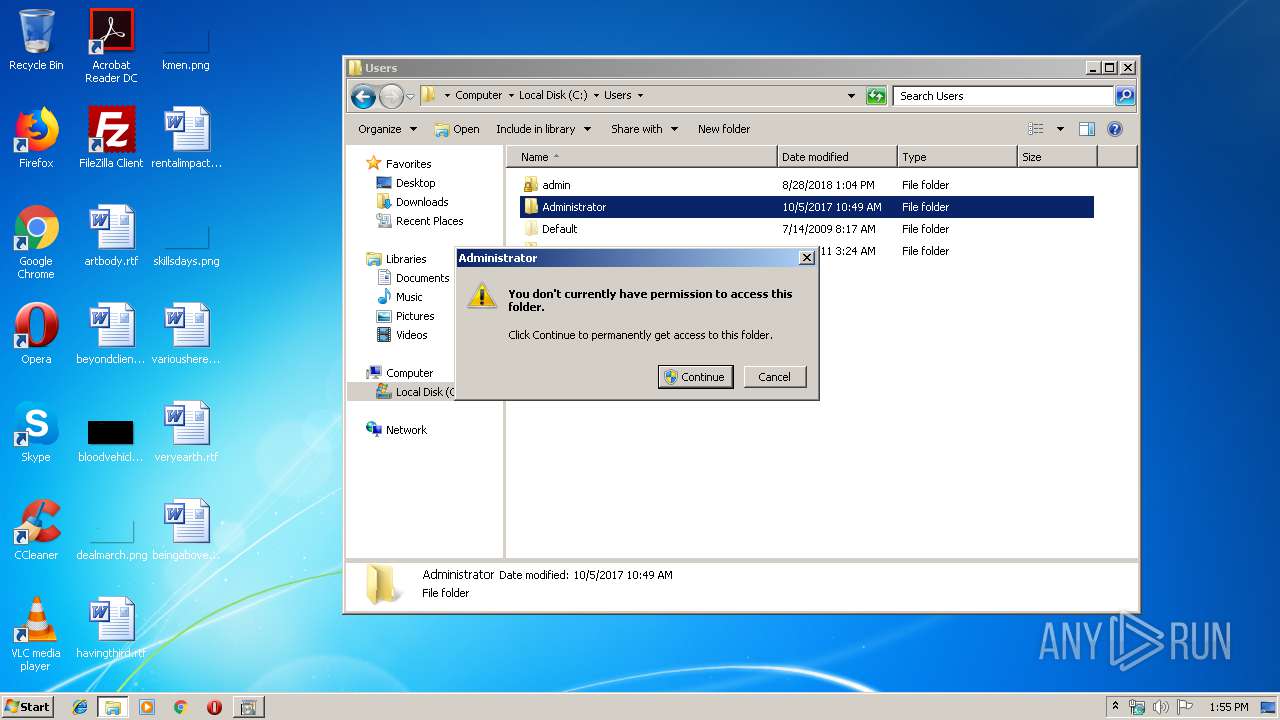
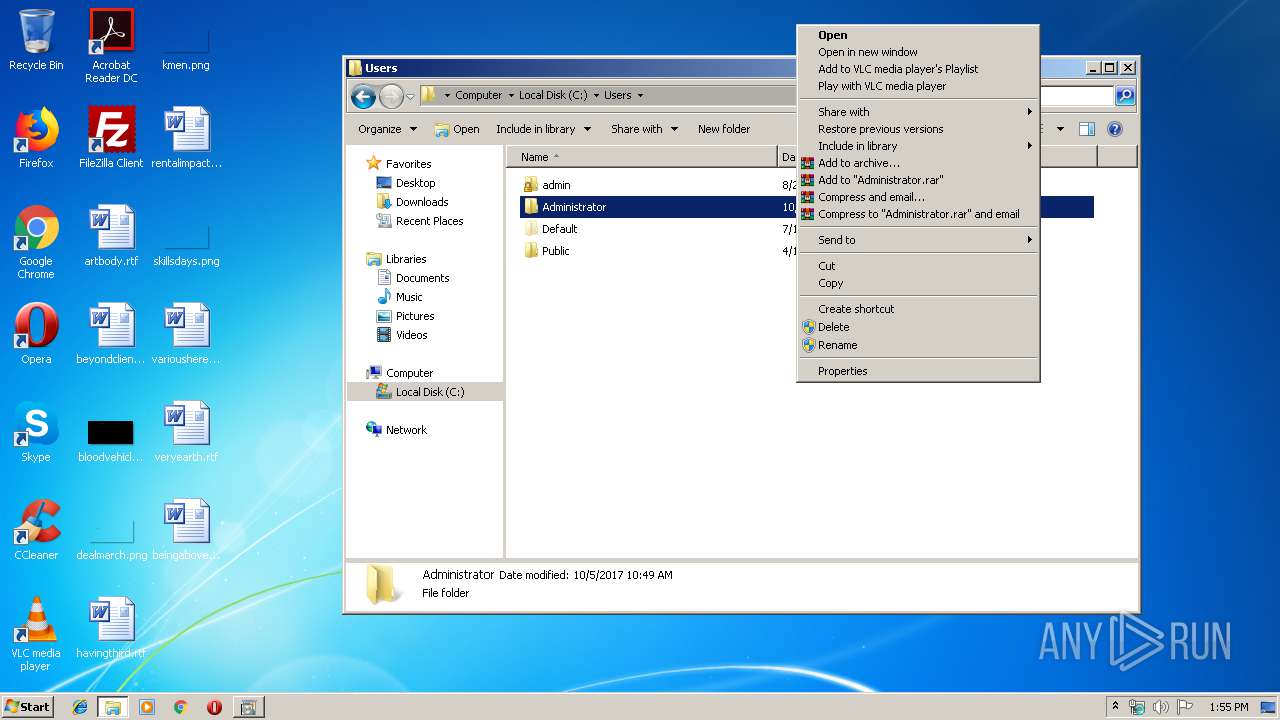
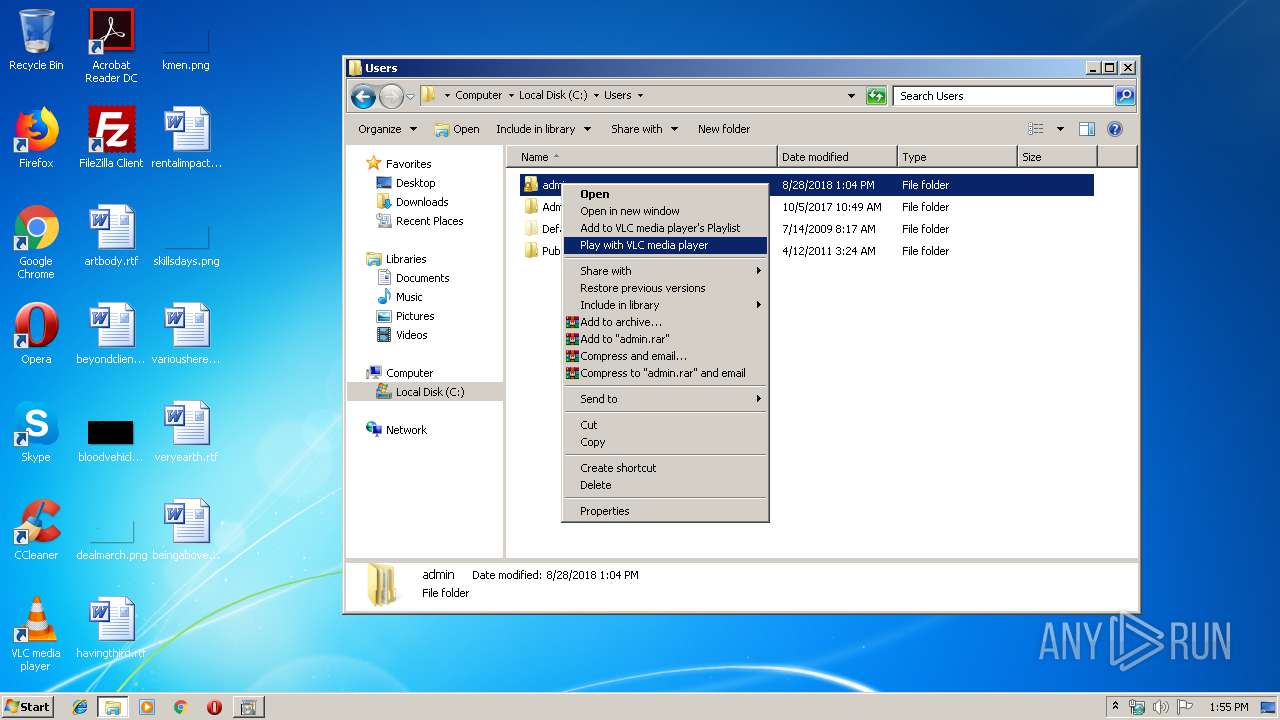
Manual execution by user
- explorer.exe (PID: 1792)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:05:11 00:18:21+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 18432 |
| InitializedDataSize: | 9216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x60b4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-May-2016 22:18:21 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 10-May-2016 22:18:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004060 | 0x00004200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55333 |
.itext | 0x00006000 | 0x000005BC | 0x00000600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.79903 |
.data | 0x00007000 | 0x000007AC | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.25346 |
.bss | 0x00008000 | 0x00002928 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000B000 | 0x00000746 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.30607 |
.tls | 0x0000C000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000D000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.reloc | 0x0000E000 | 0x00000490 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.62945 |
.rsrc | 0x0000F000 | 0x00000B4C | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.19159 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
99 | 2.75 | 8 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
4096 | 3.32582 | 1236 | Latin 1 / Western European | UNKNOWN | RT_STRING |
SCRIPT | 7.78829 | 1296 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
SETT | 5.4183 | 48 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
kernel32.dll |
user32.dll |
Total processes
56
Monitored processes
12
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | timeout /t 2 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
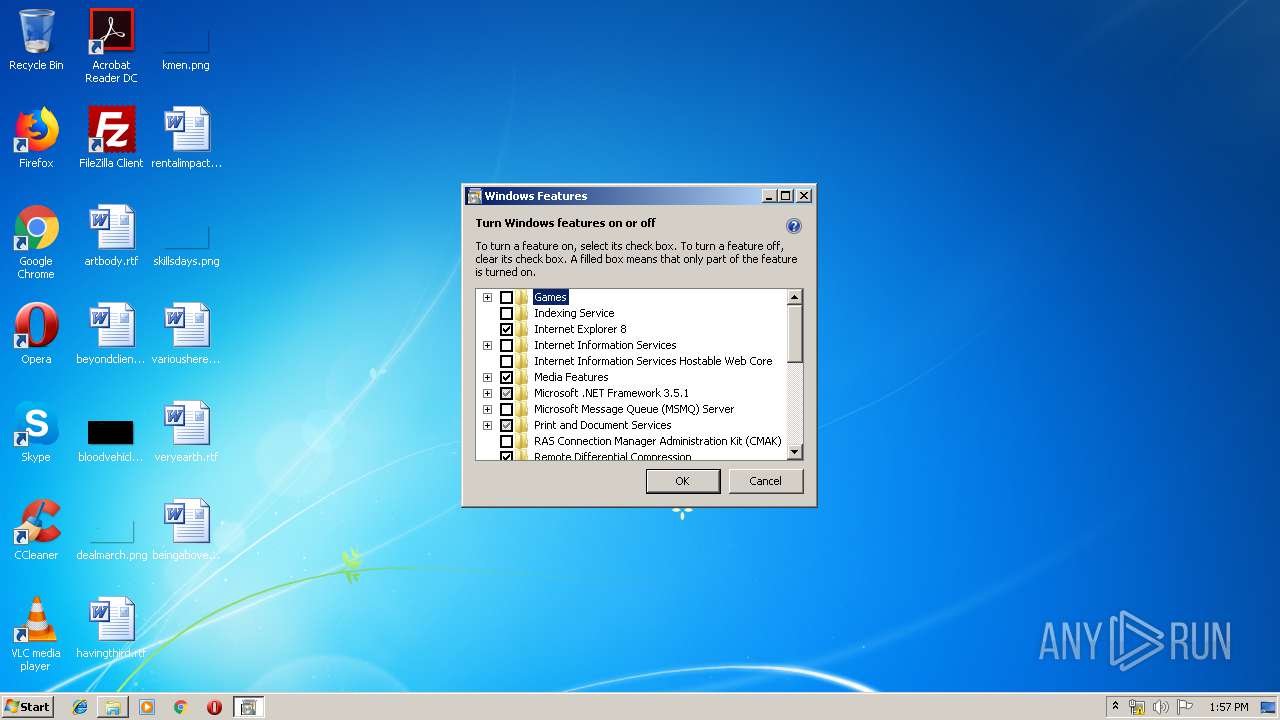
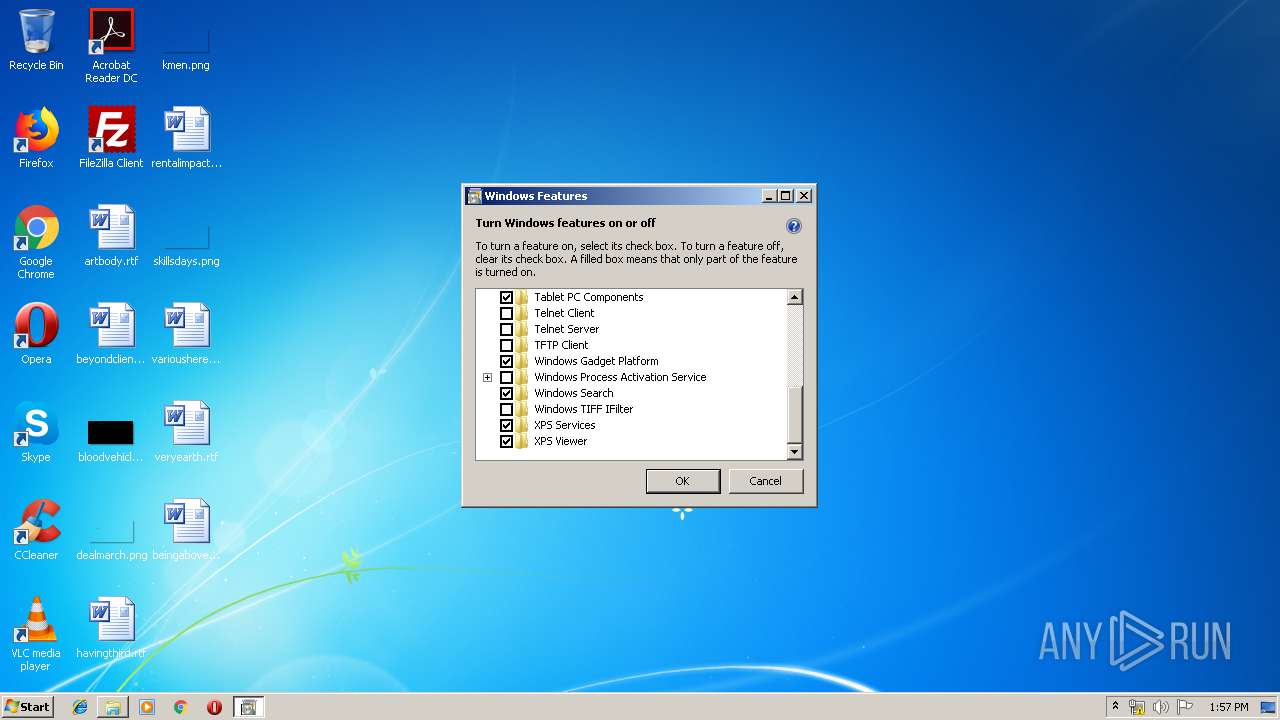
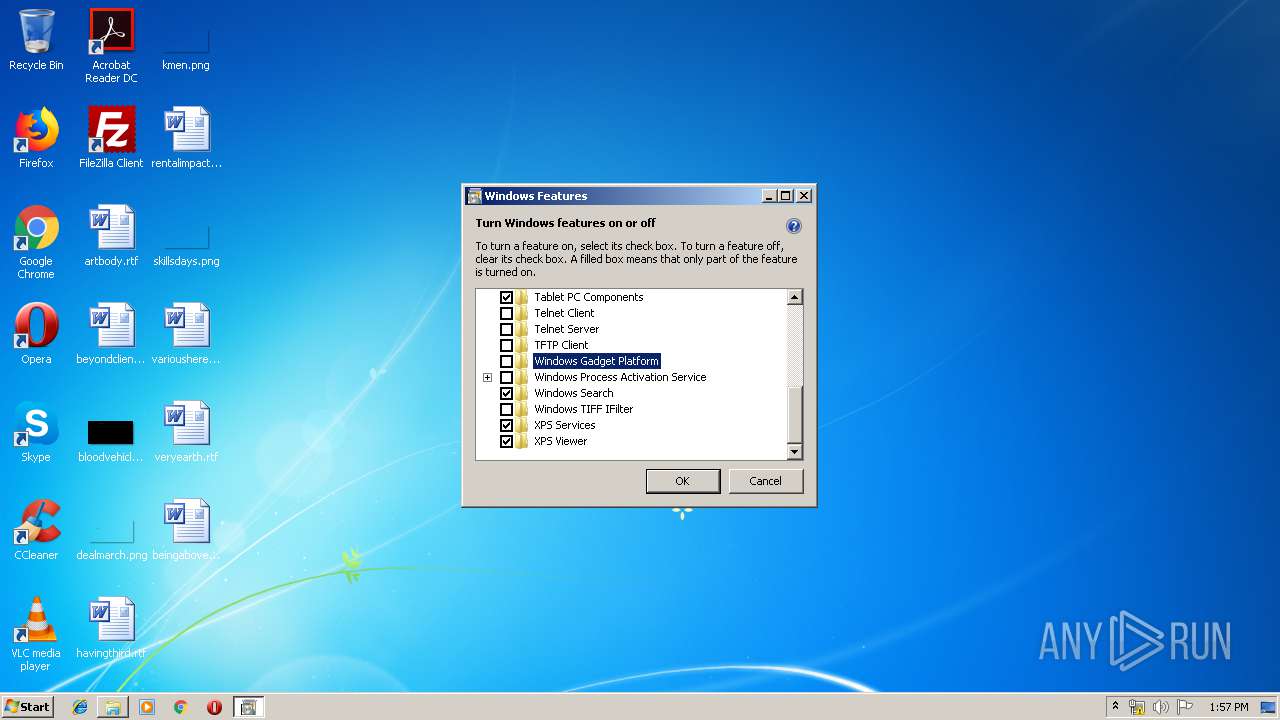
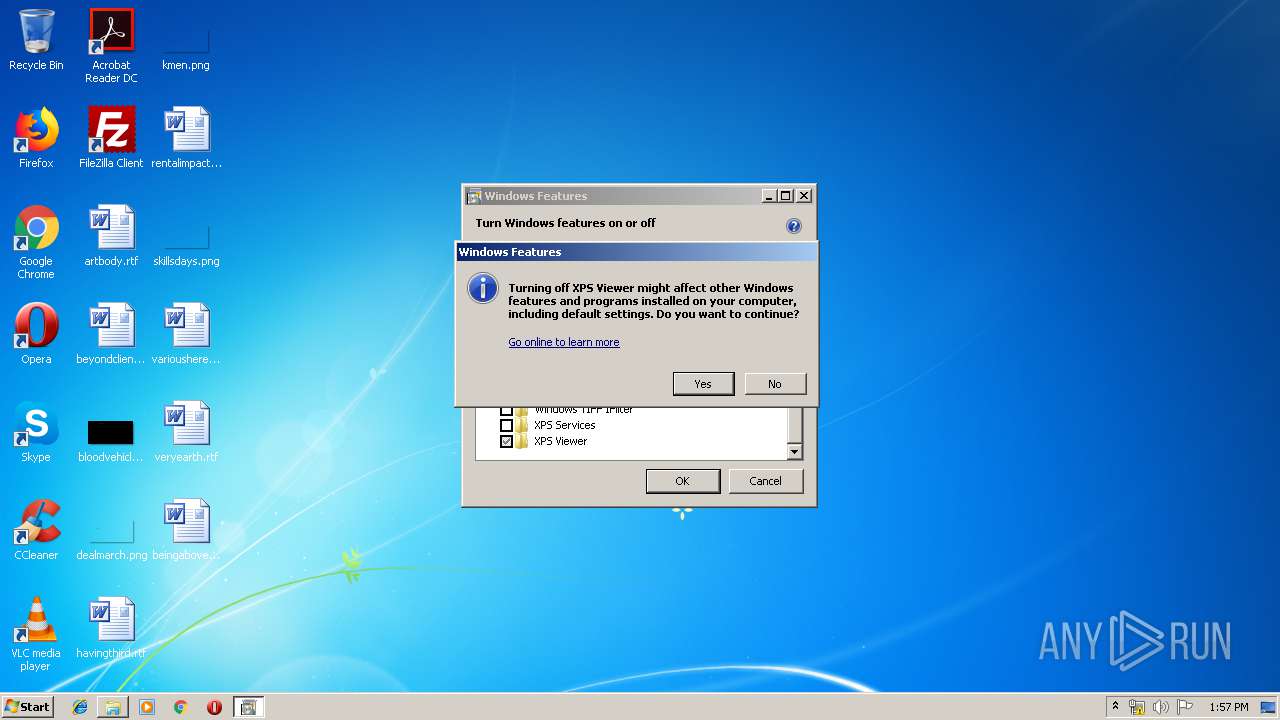
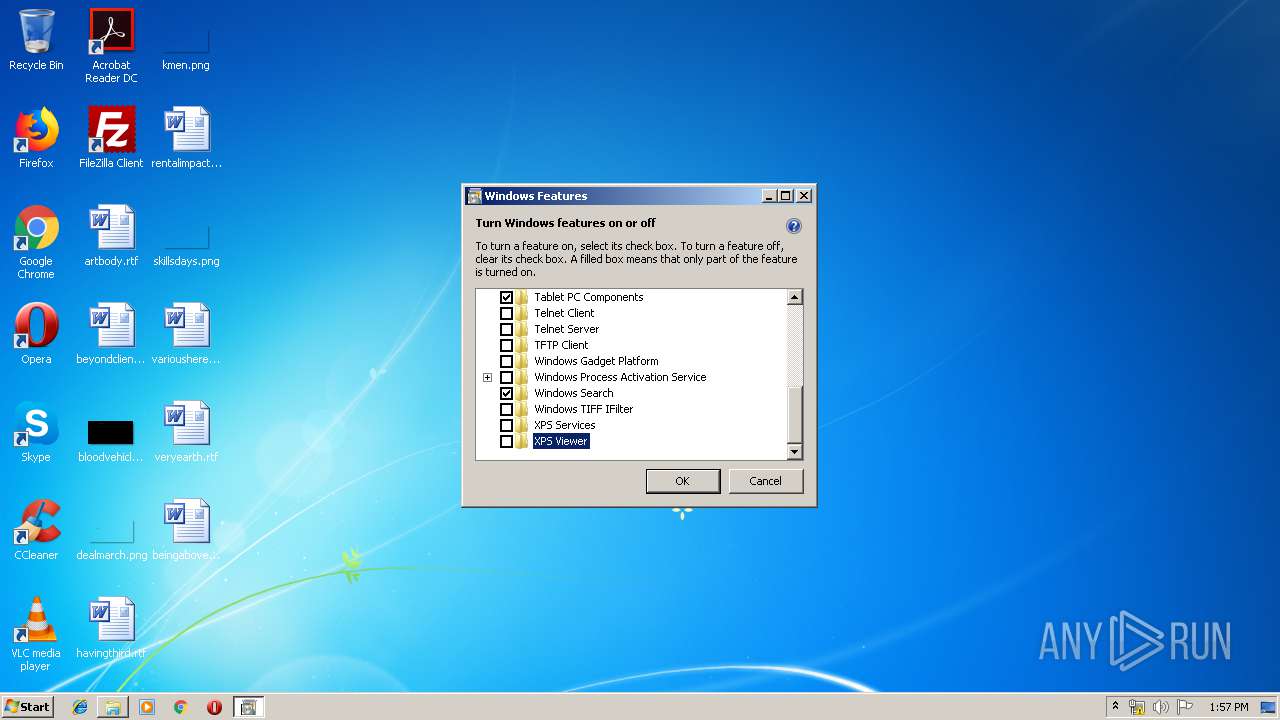
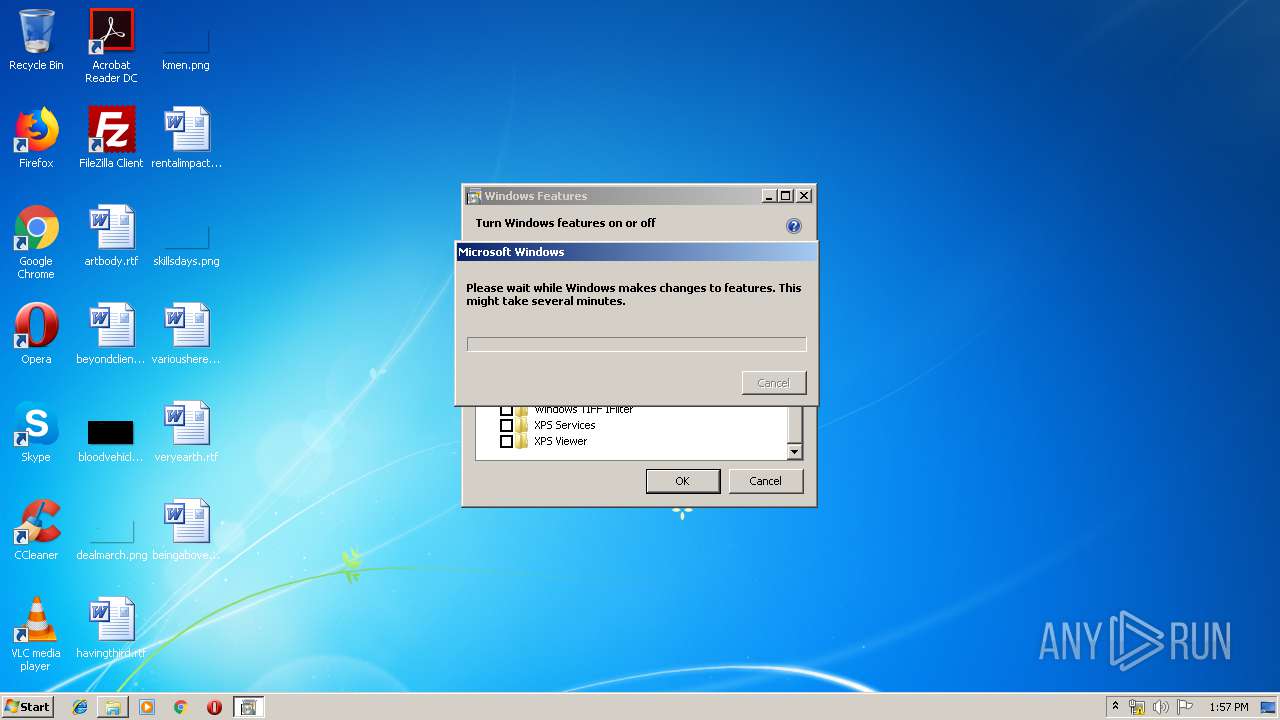
| 1516 | "C:\Windows\System32\OptionalFeatures.exe" | C:\Windows\System32\OptionalFeatures.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Features Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
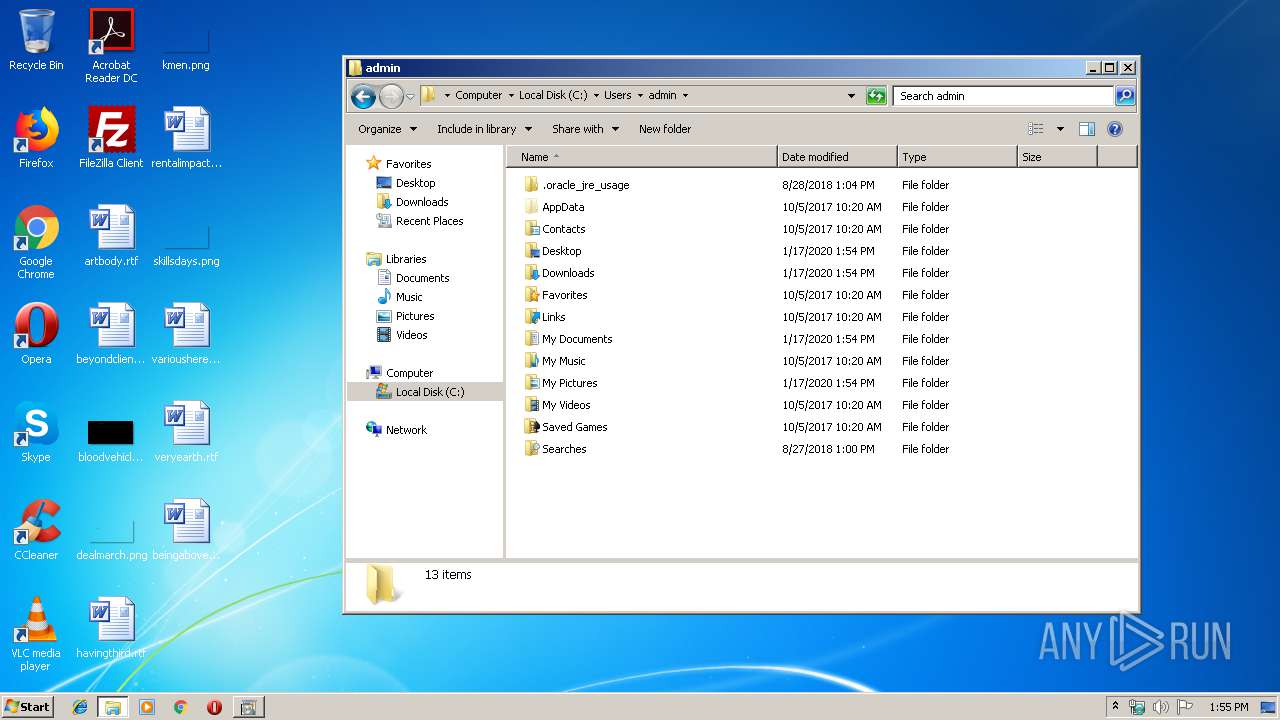
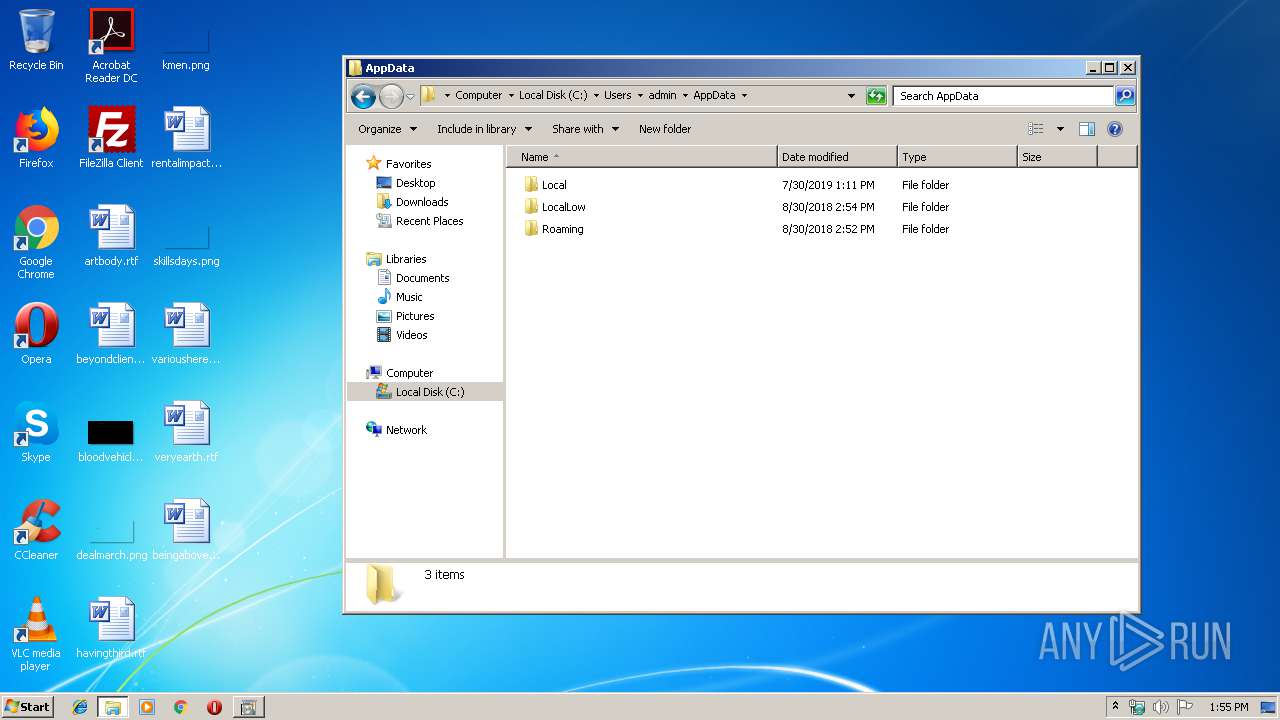
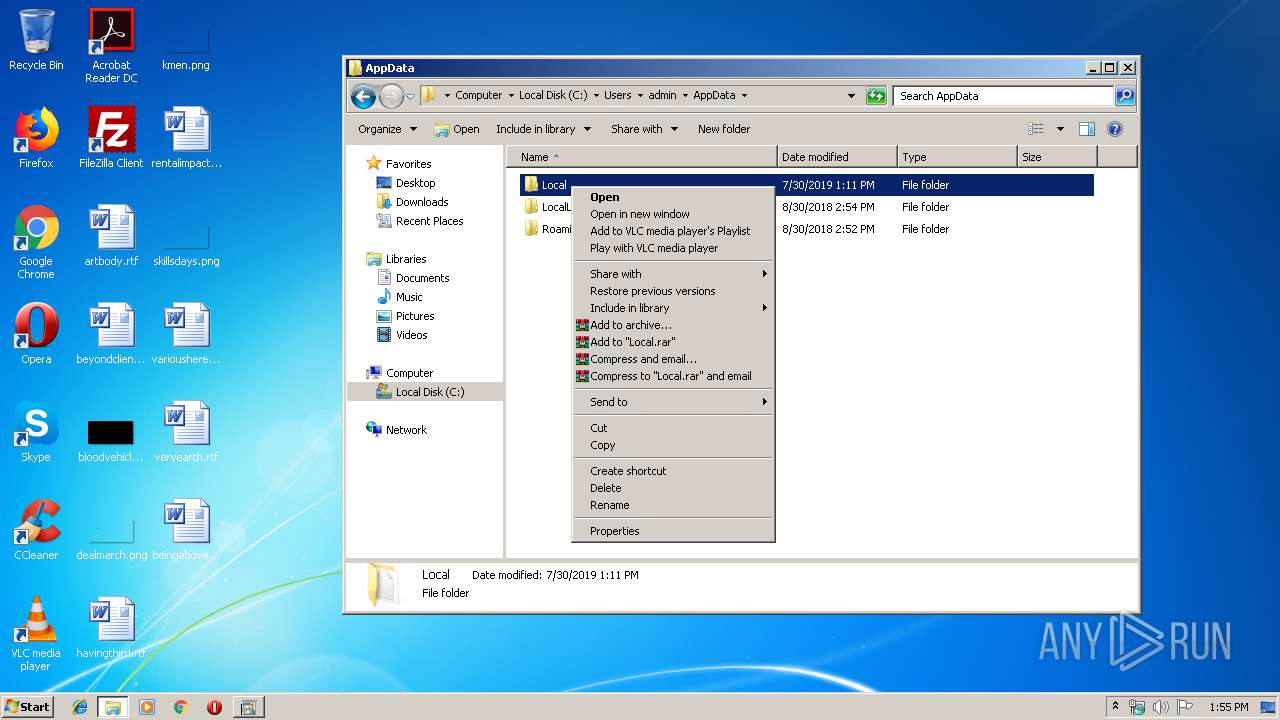
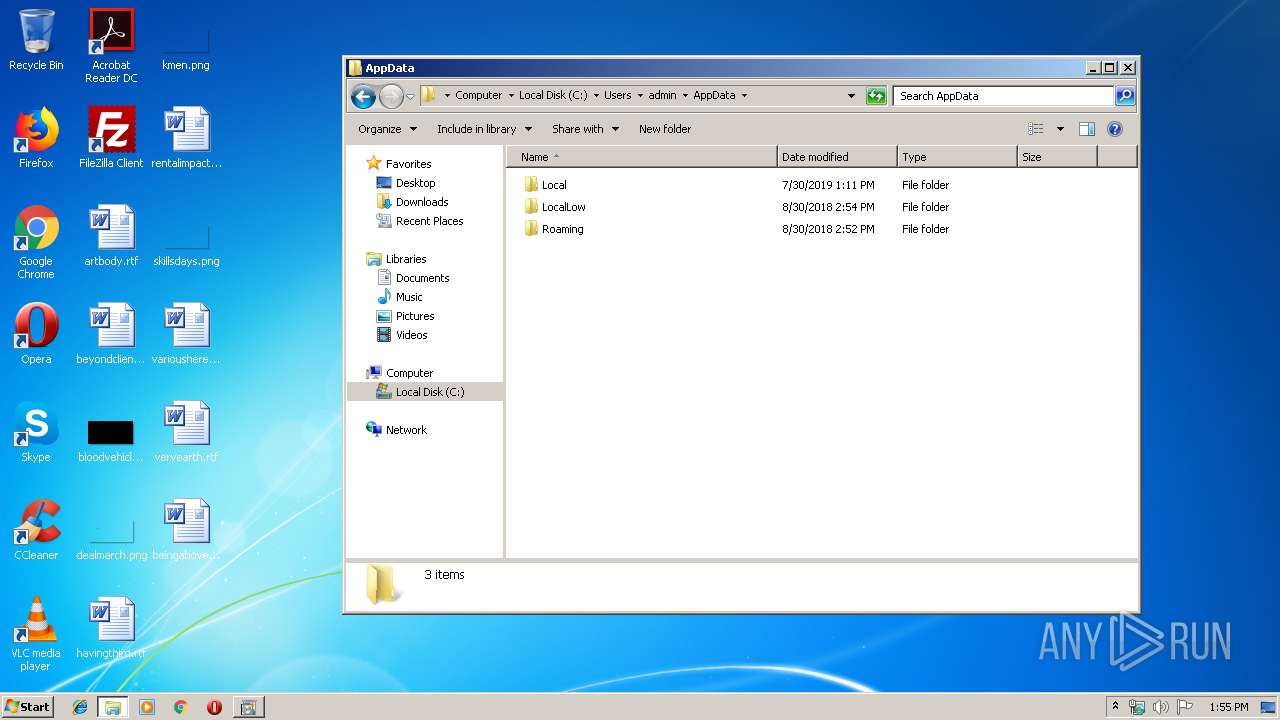
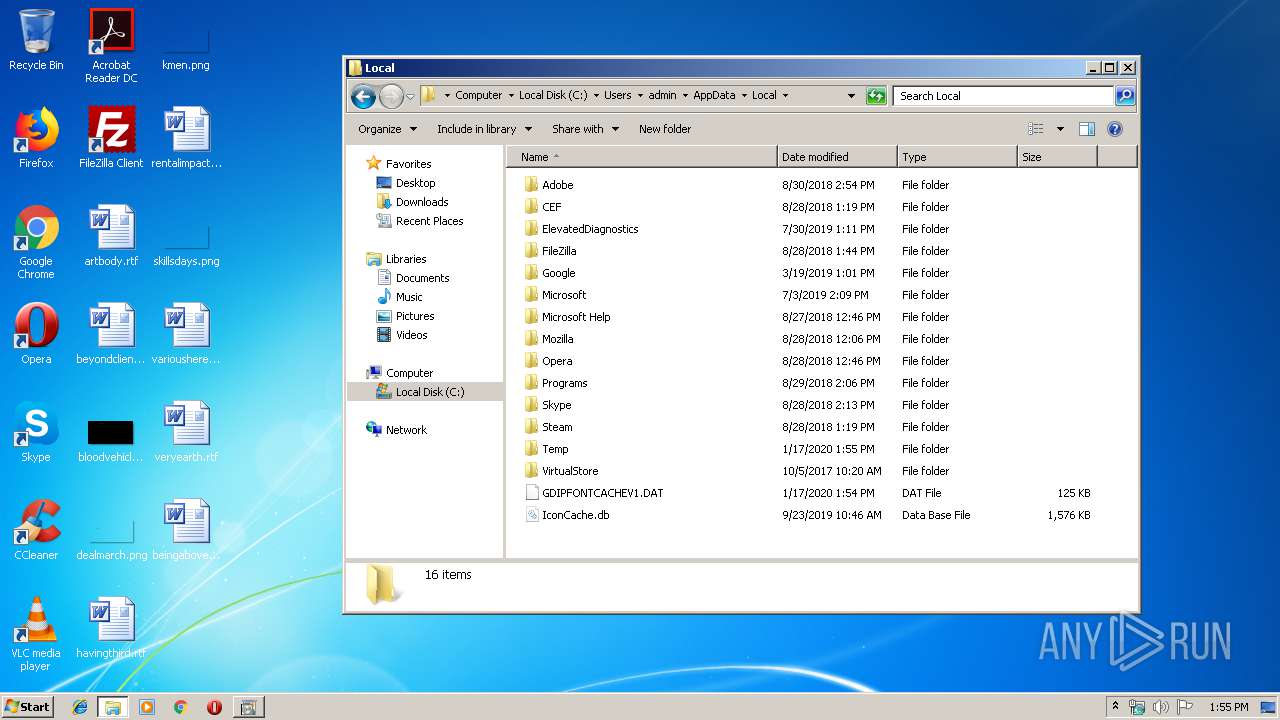
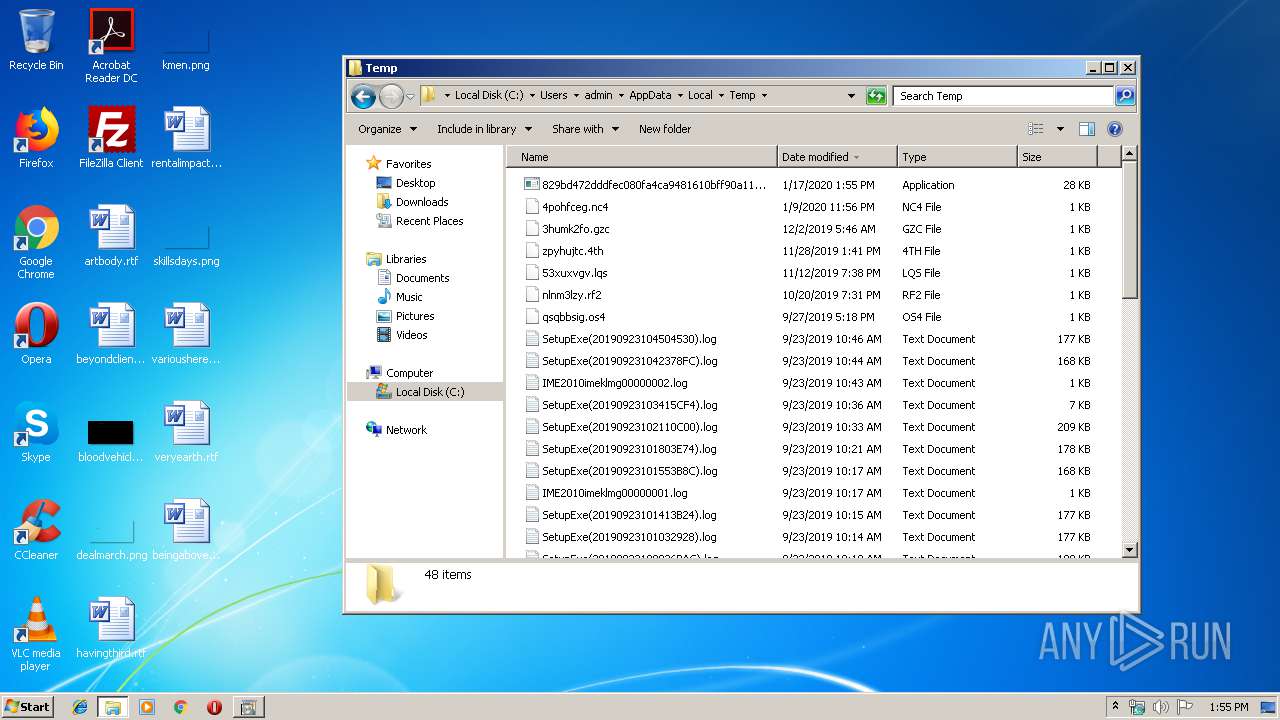
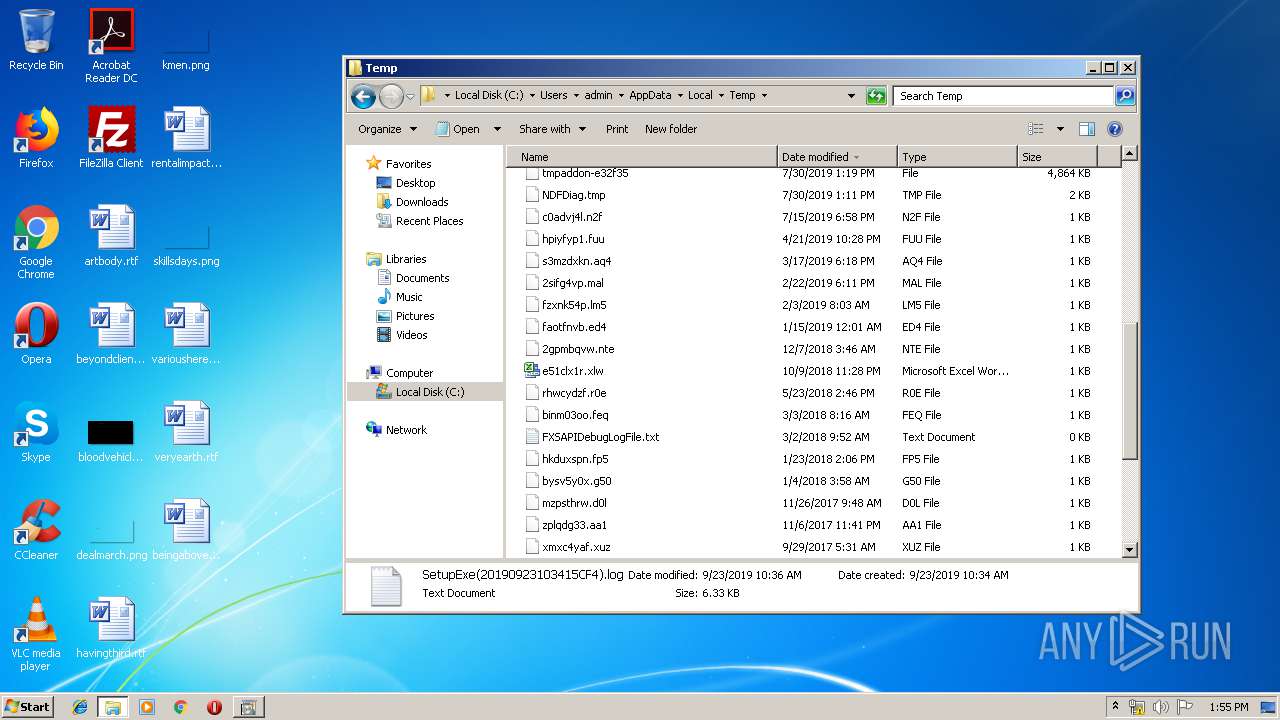
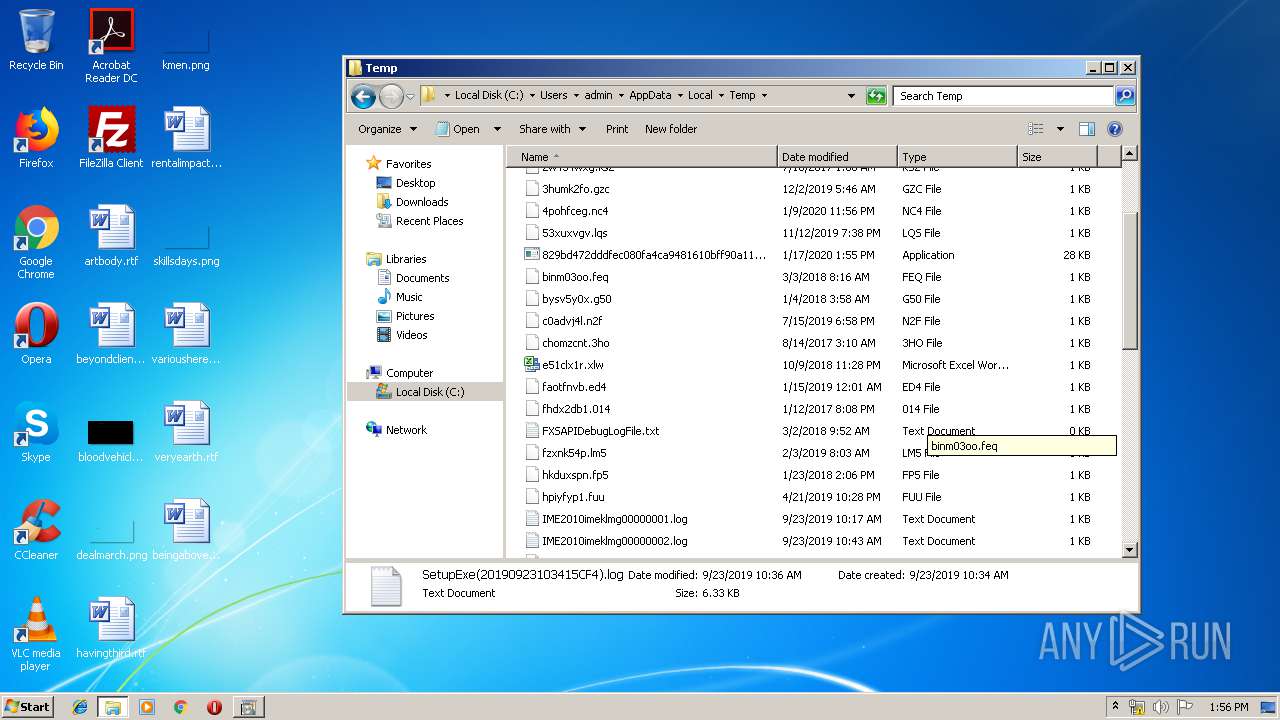
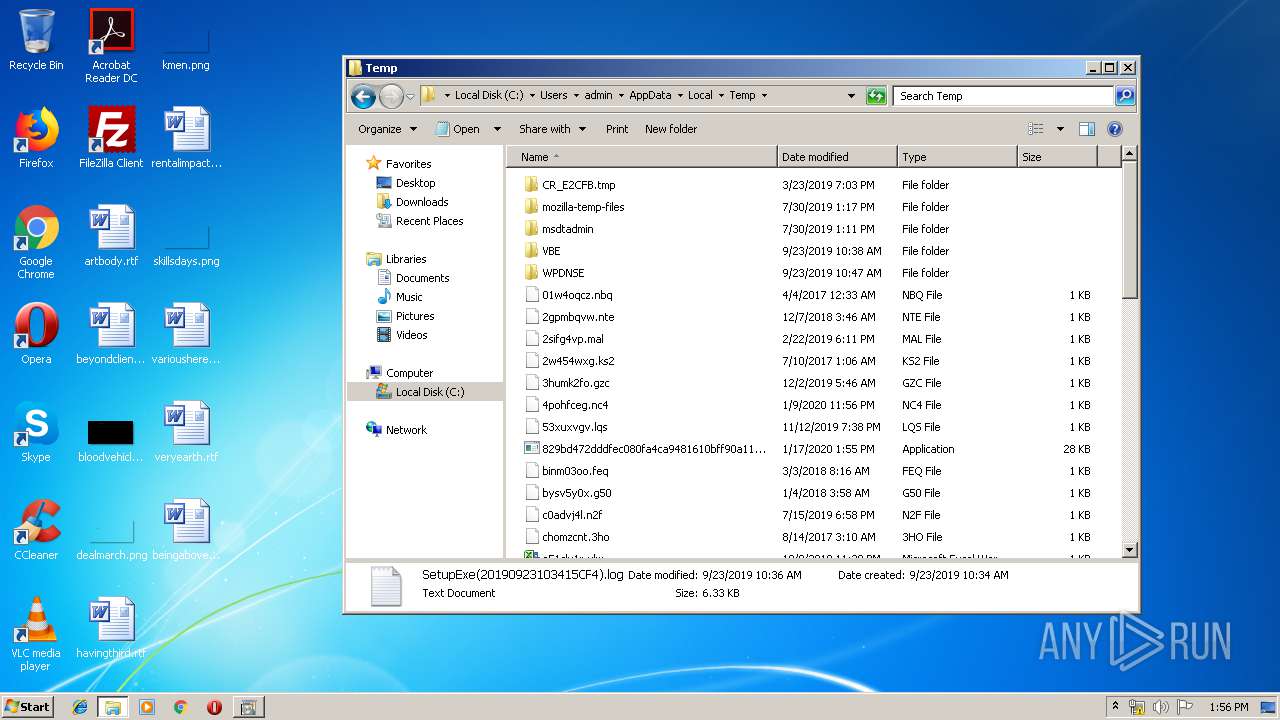
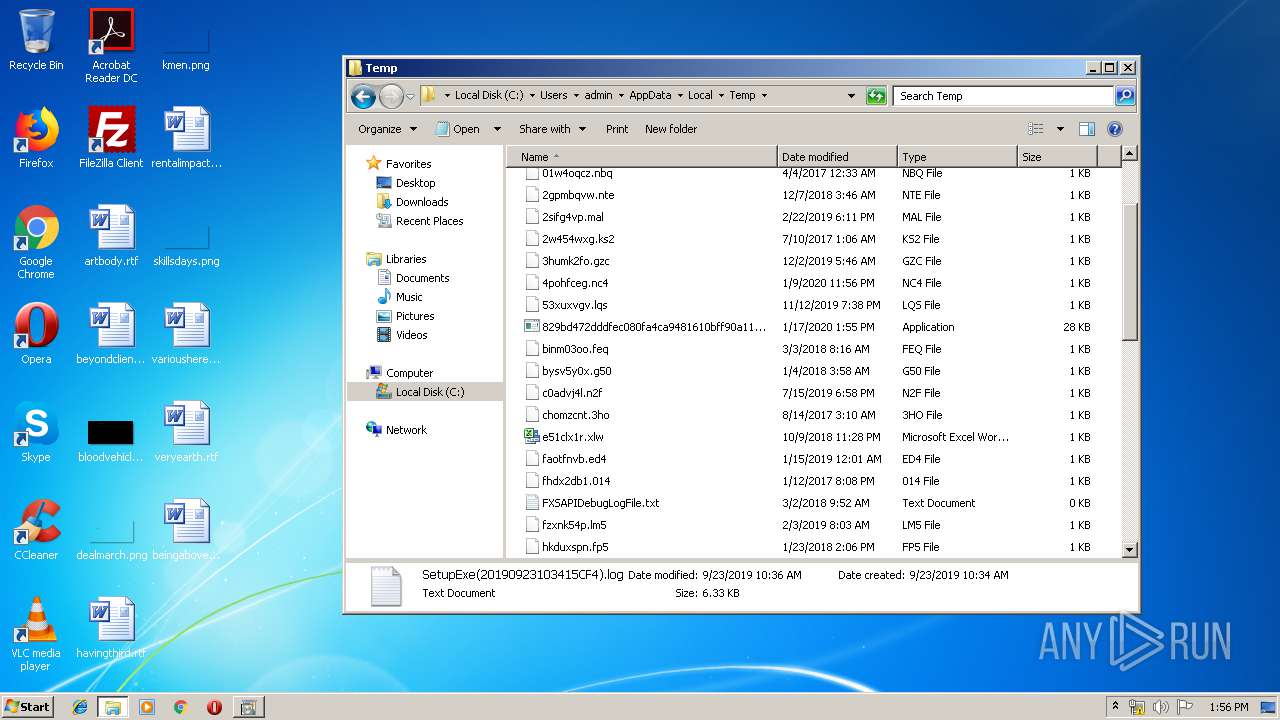
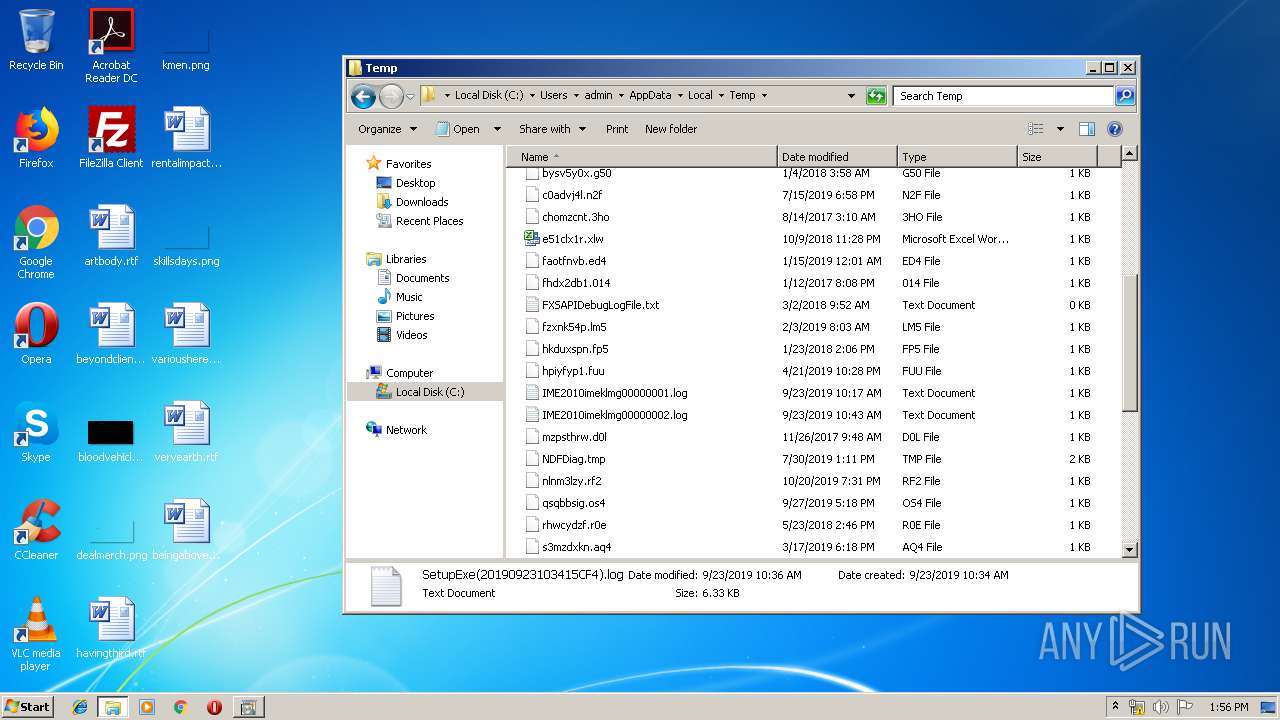
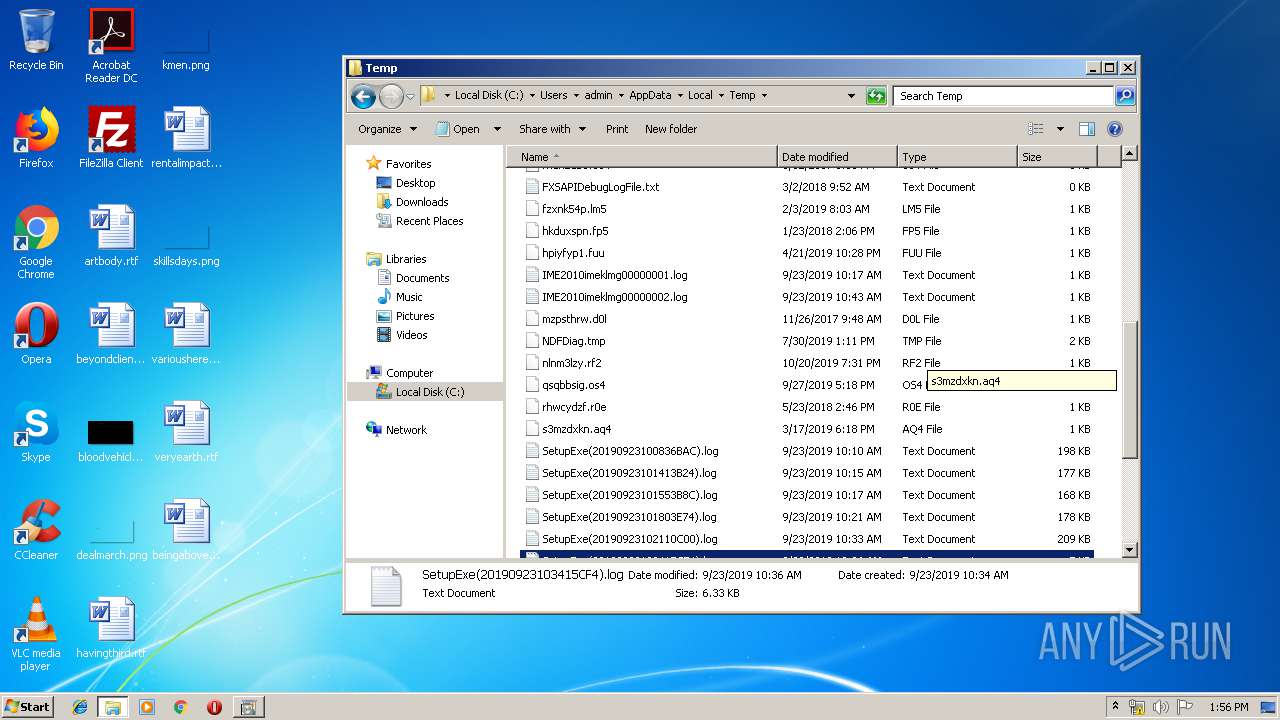
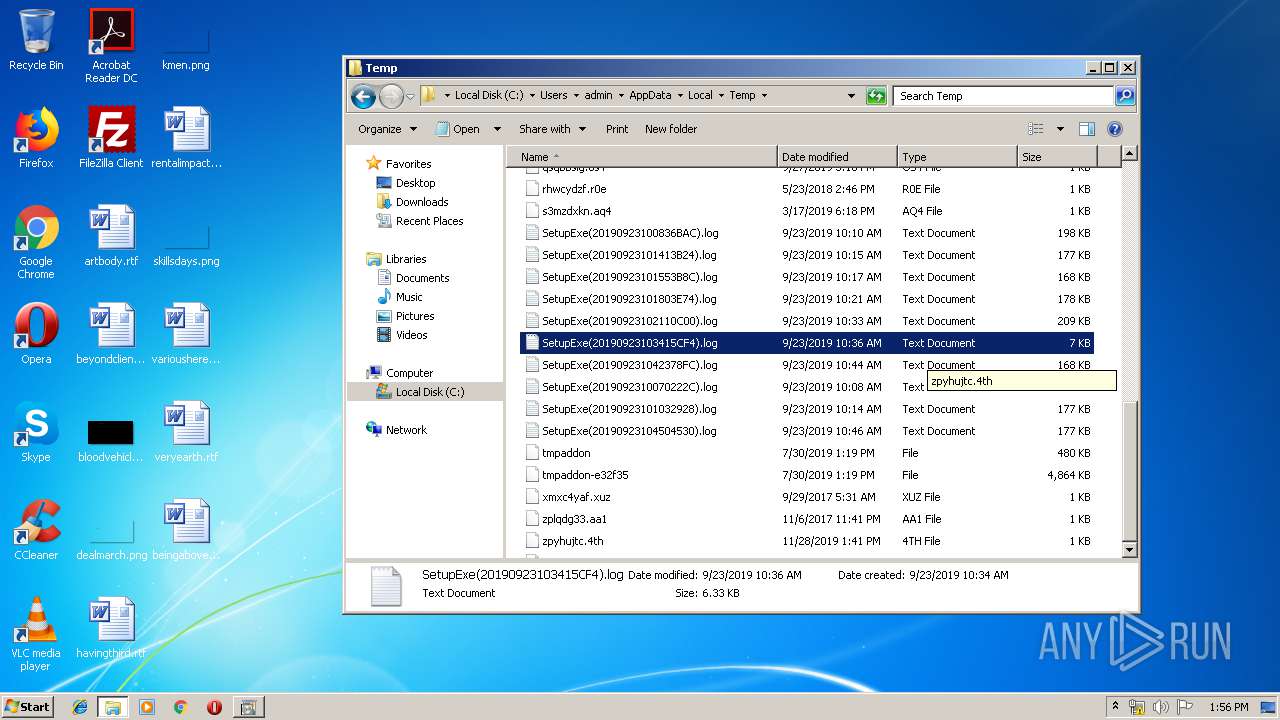
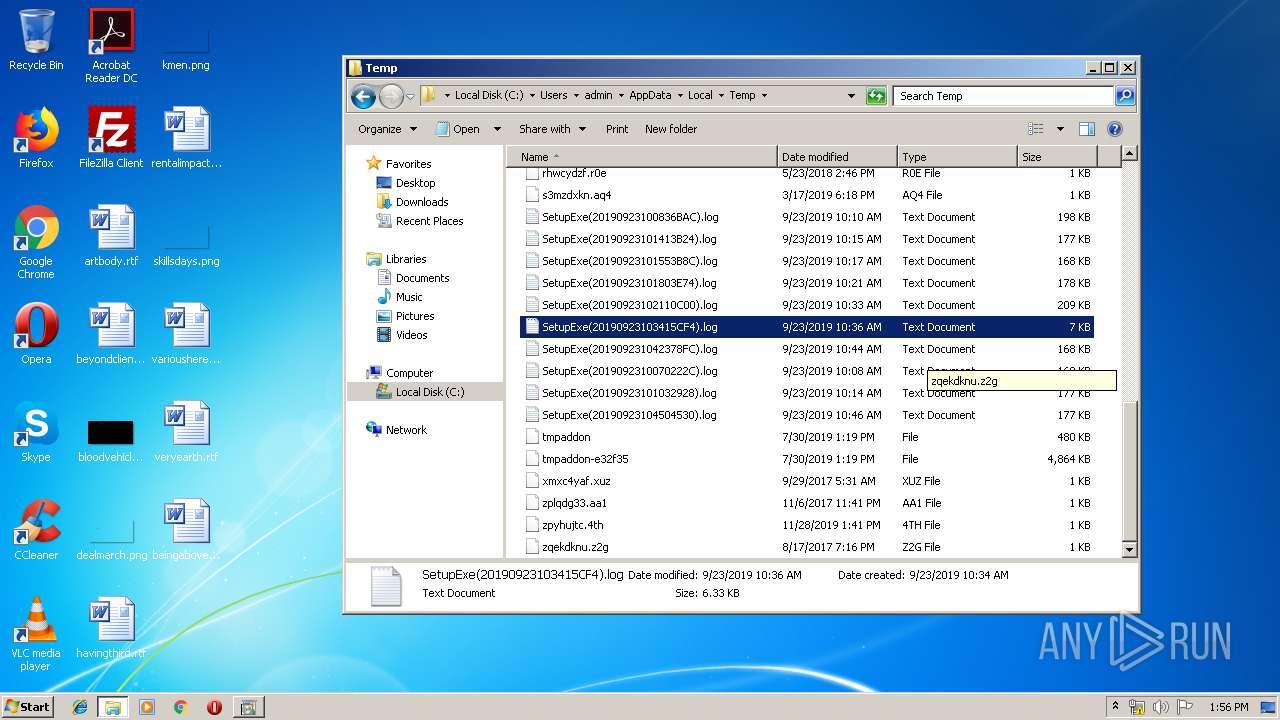
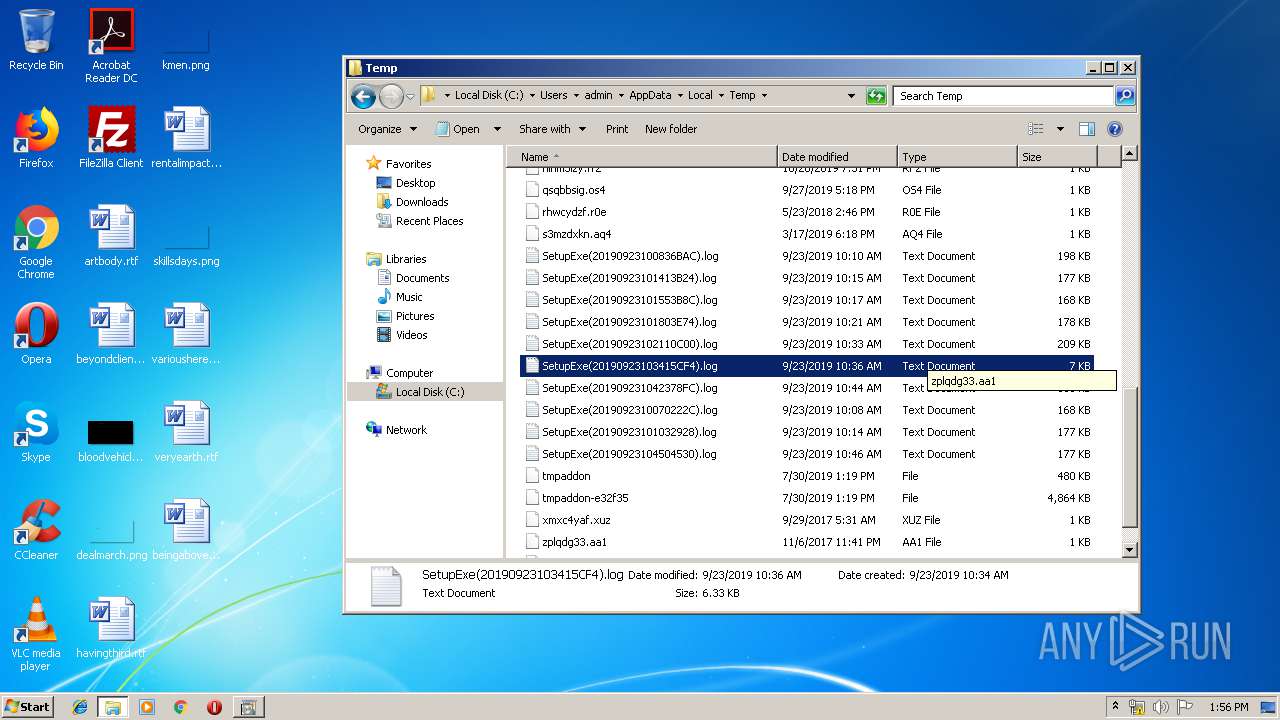
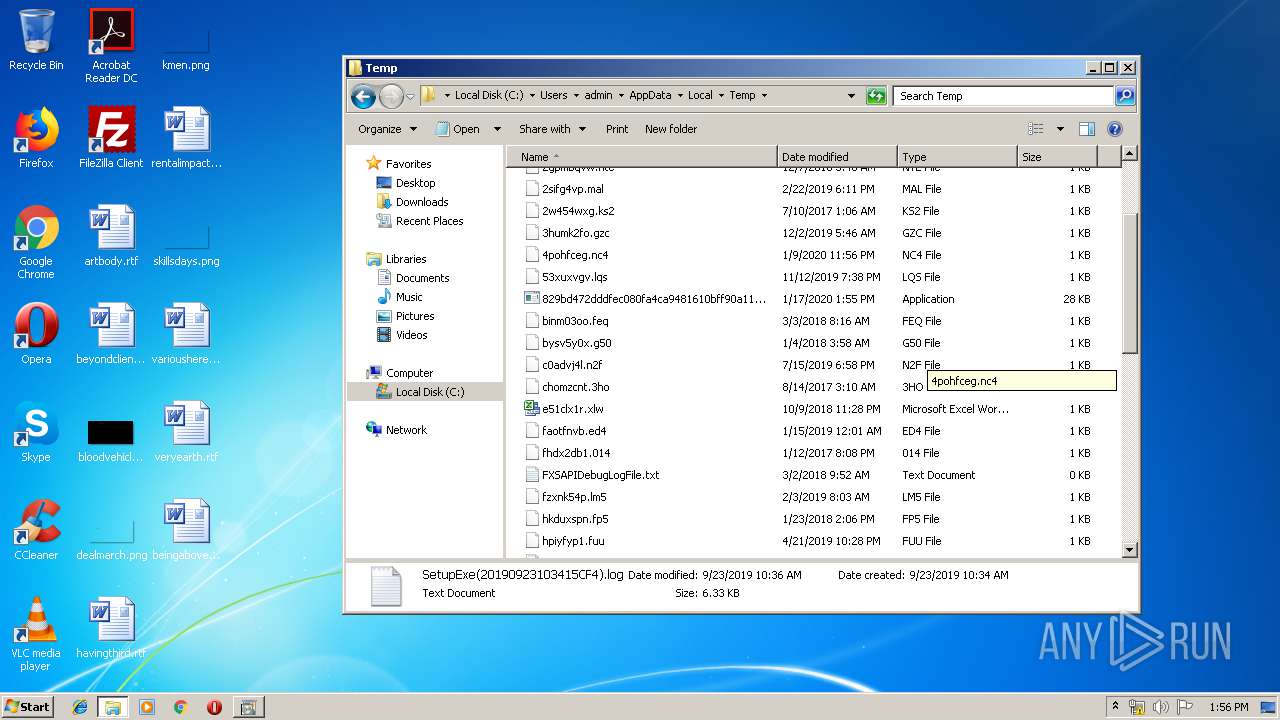
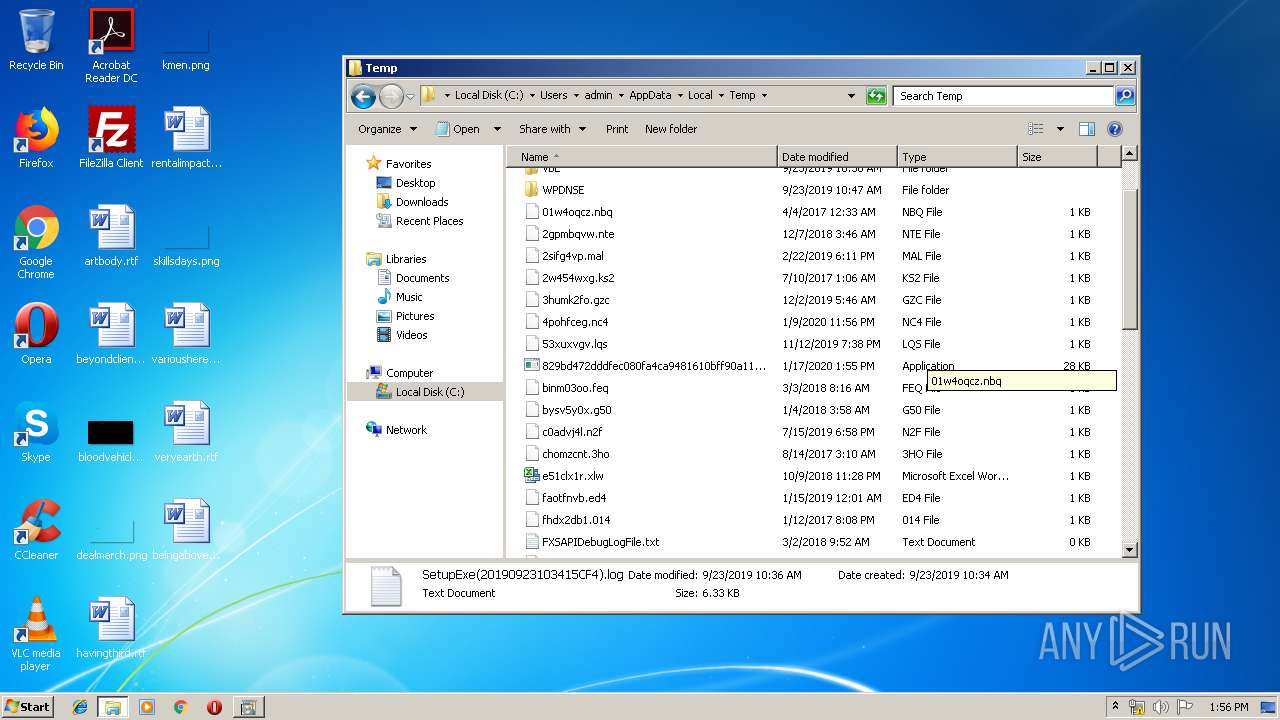
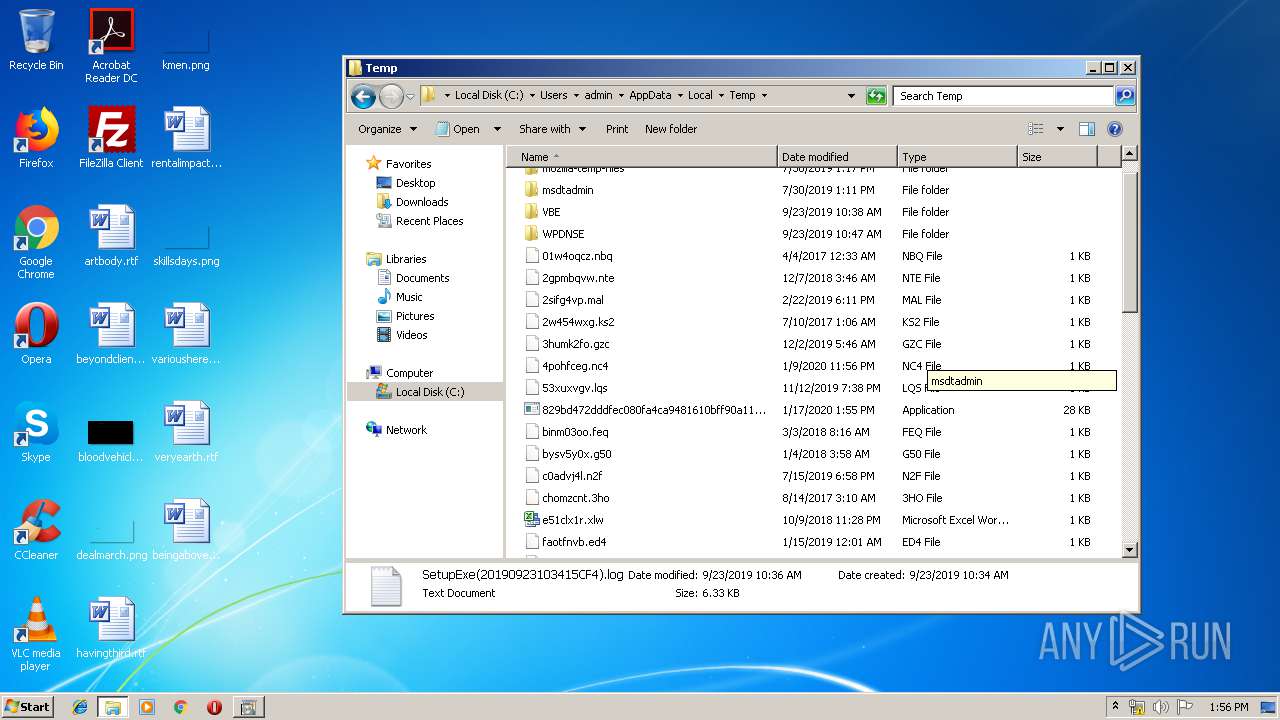
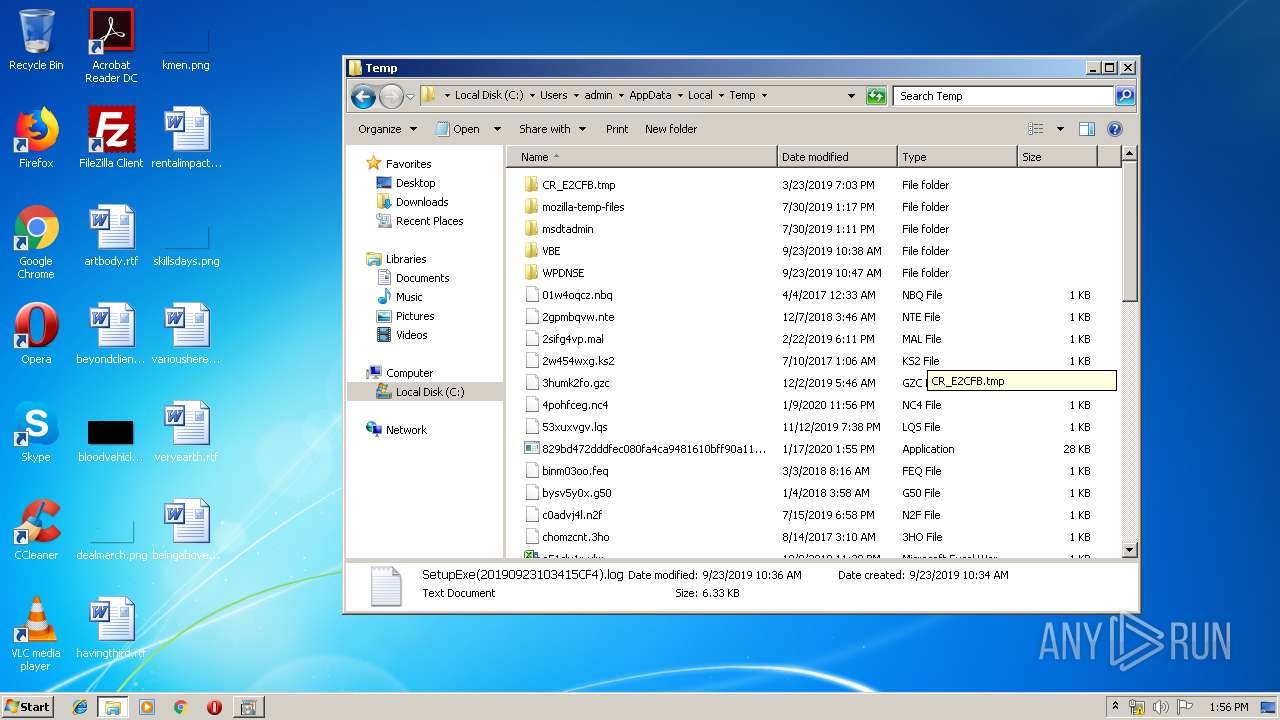
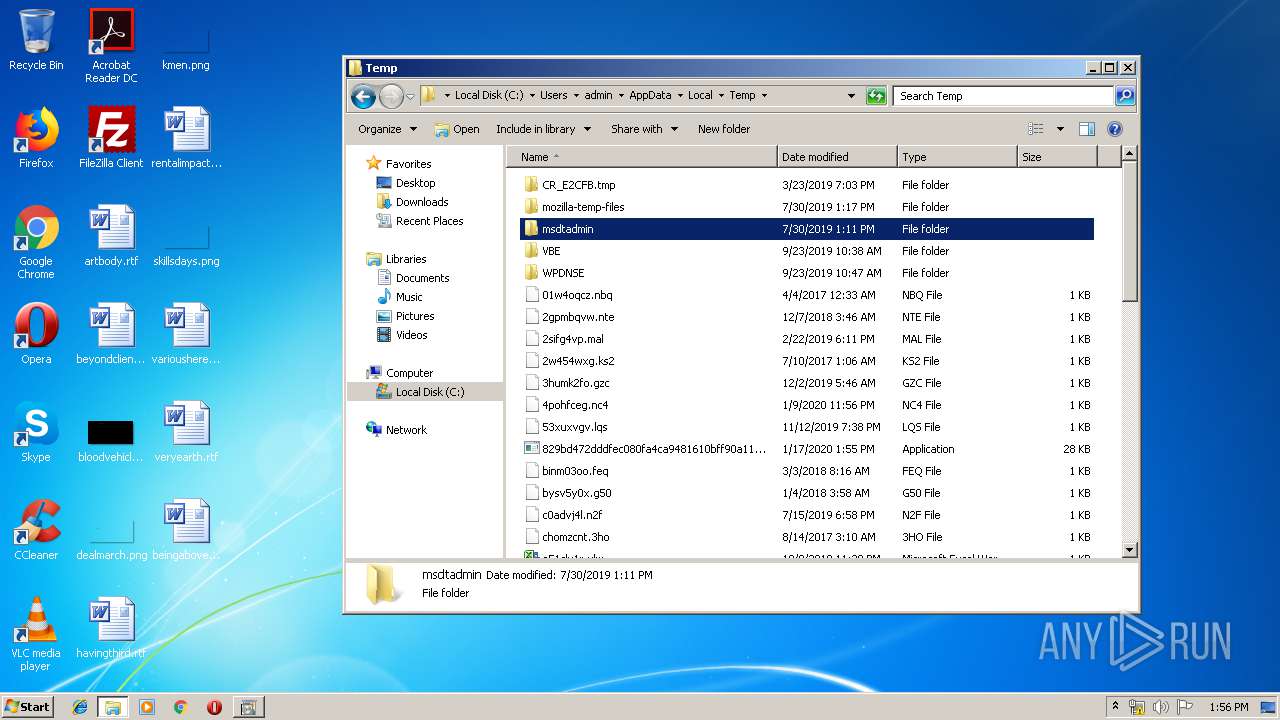
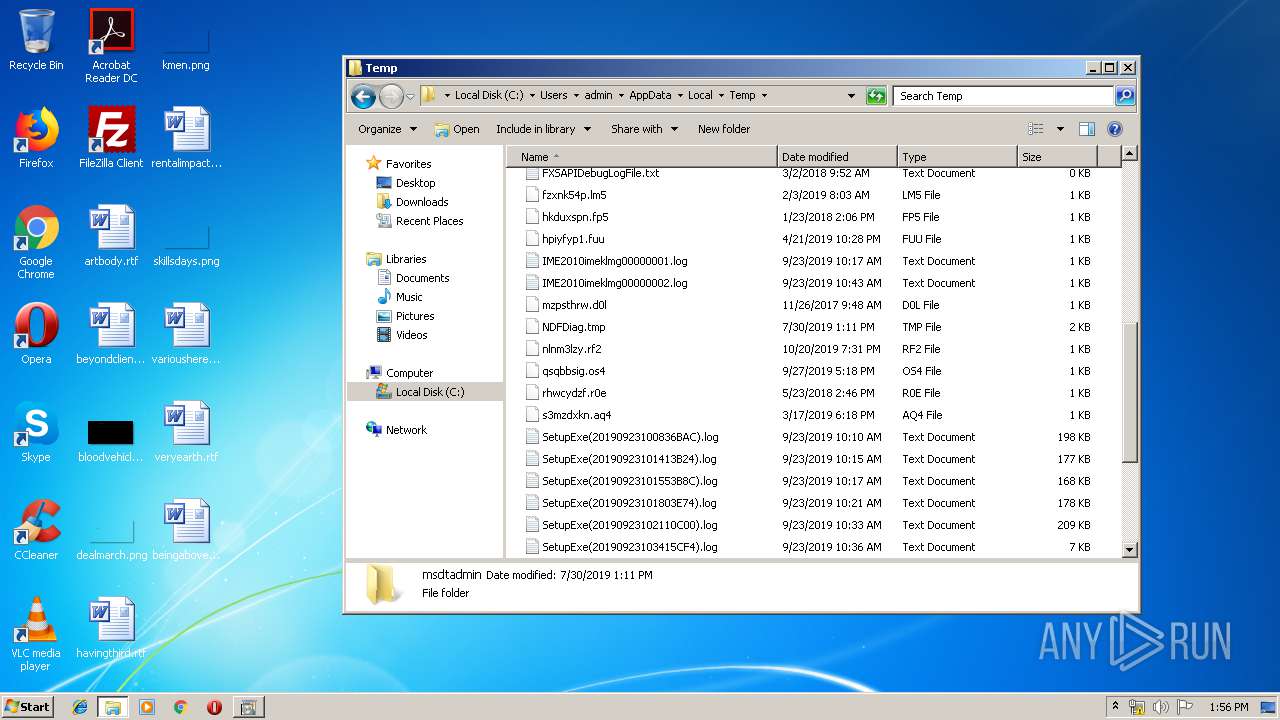
| 1712 | "C:\Users\admin\AppData\Local\Temp\829bd472dddfec080fa4ca9481610bff90a116af3d4c8e7b3c78a1d22c89eb8c.exe" | C:\Users\admin\AppData\Local\Temp\829bd472dddfec080fa4ca9481610bff90a116af3d4c8e7b3c78a1d22c89eb8c.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1792 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | reg add "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing\PackageDetect\Microsoft-Windows-Foundation-Package~31bf3856ad364e35~amd64~~0.0.0.0" /v "Microsoft-Windows-HVSI-Package~31bf3856ad364e35~amd64~~10.0.19041.1" /t REG_DWORD /d "3" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1908 | reg add "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing\PackageDetect\Microsoft-Windows-Foundation-Package~31bf3856ad364e35~amd64~~0.0.0.0" /v "Microsoft-Hyper-V-ClientEdition-Package~31bf3856ad364e35~amd64~~10.0.19041.1" /t REG_DWORD /d "3" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
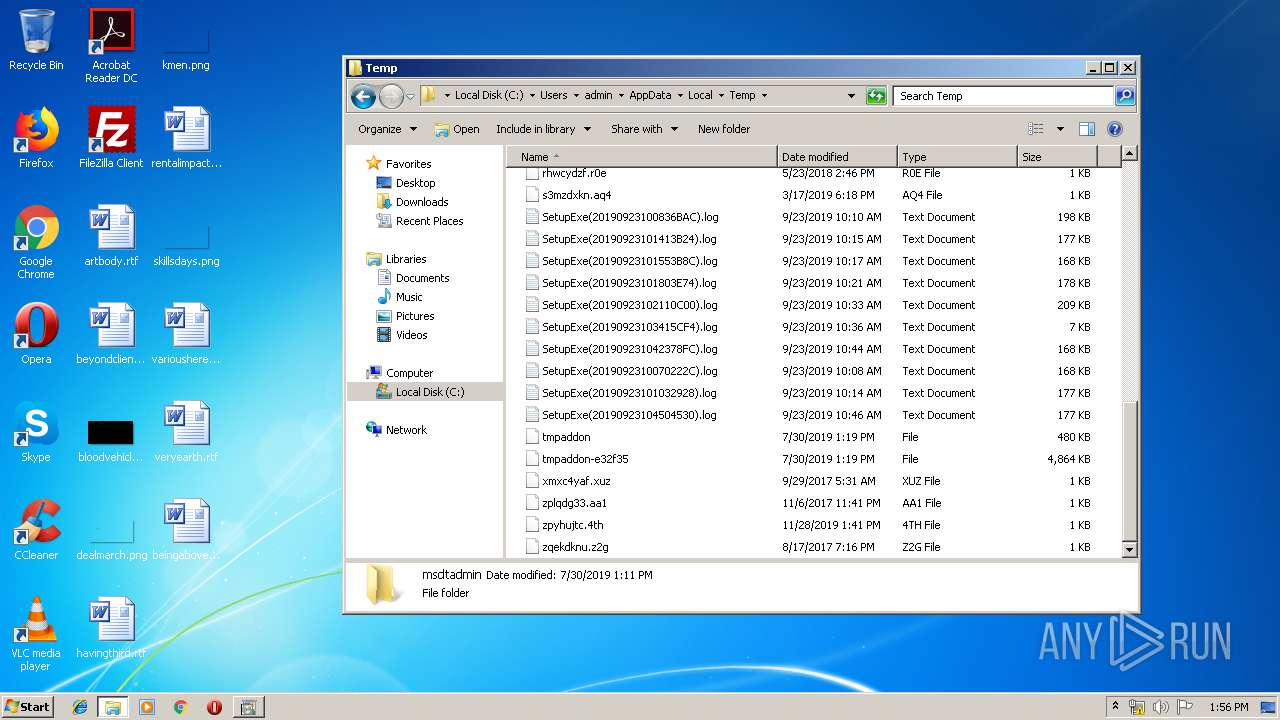
| 2116 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\0YQK7DR1.cmd" "C:\Users\admin\AppData\Local\Temp\829bd472dddfec080fa4ca9481610bff90a116af3d4c8e7b3c78a1d22c89eb8c.exe" " | C:\Windows\system32\cmd.exe | — | 829bd472dddfec080fa4ca9481610bff90a116af3d4c8e7b3c78a1d22c89eb8c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2288 | rundll32.exe shell32.dll, Control_RunDLL appwiz.cpl,,2 | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2732 | "C:\Windows\System32\OptionalFeatures.exe" | C:\Windows\System32\OptionalFeatures.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Features Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3420 | reg add "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing\PackageDetect\Microsoft-Windows-Foundation-Package~31bf3856ad364e35~amd64~~0.0.0.0" /v "Microsoft-Windows-HyperV-OptionalFeature-HypervisorPlatform-Disabled-Package~31bf3856ad364e35~amd64~~10.0.19041.1" /t REG_DWORD /d "3" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
166
Read events
154
Write events
12
Delete events
0
Modification events
| (PID) Process: | (2288) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2288) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EDE5291B3ECDD501940D000034090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EDE5291B3ECDD501940D0000240B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EDE5291B3ECDD501940D0000240F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EDE5291B3ECDD501940D00006C0D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000AFD1351B3ECDD501940D000034090000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000AFD1351B3ECDD501940D00006C0D0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000000934381B3ECDD501940D0000240F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3476) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 400000000000000063963A1B3ECDD501940D0000240B0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
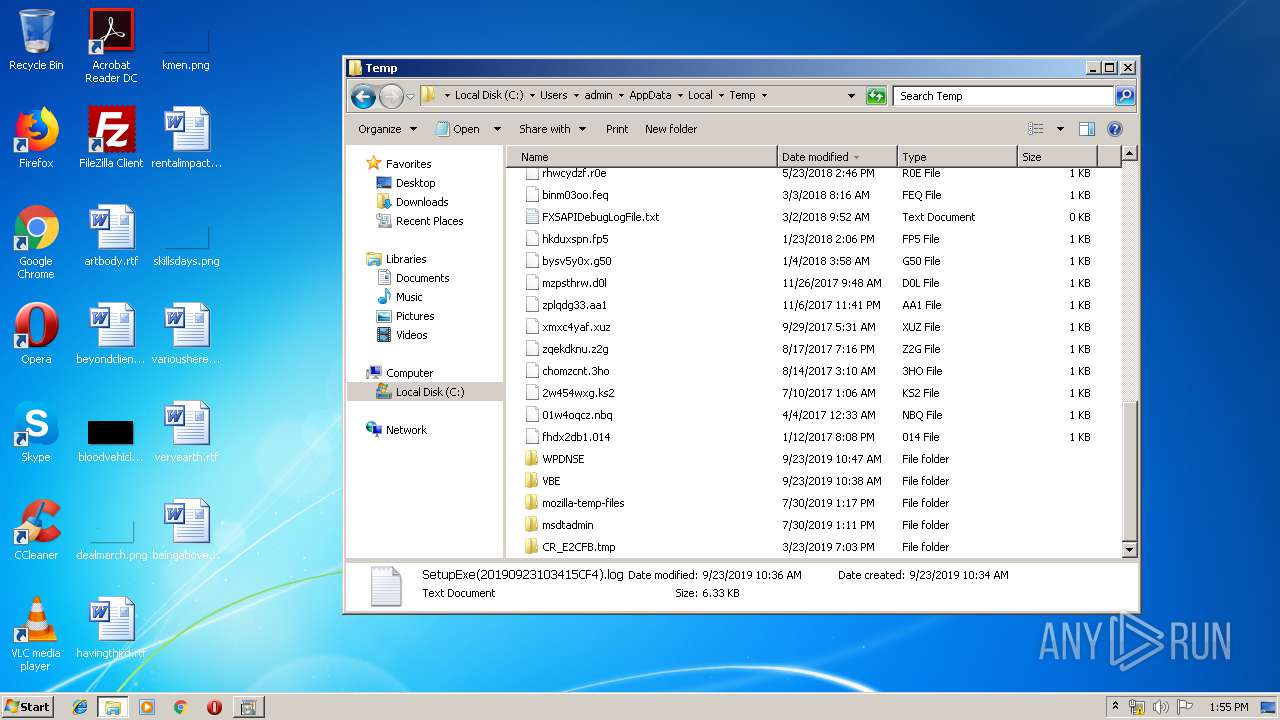
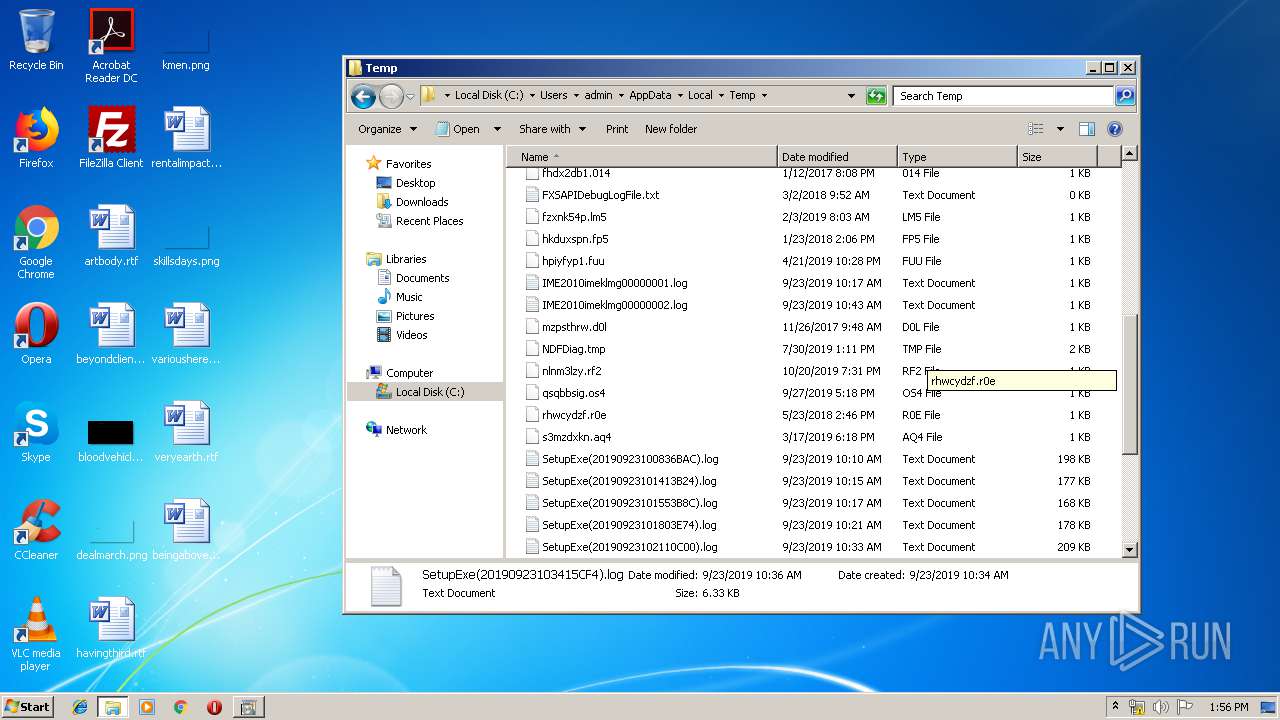
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
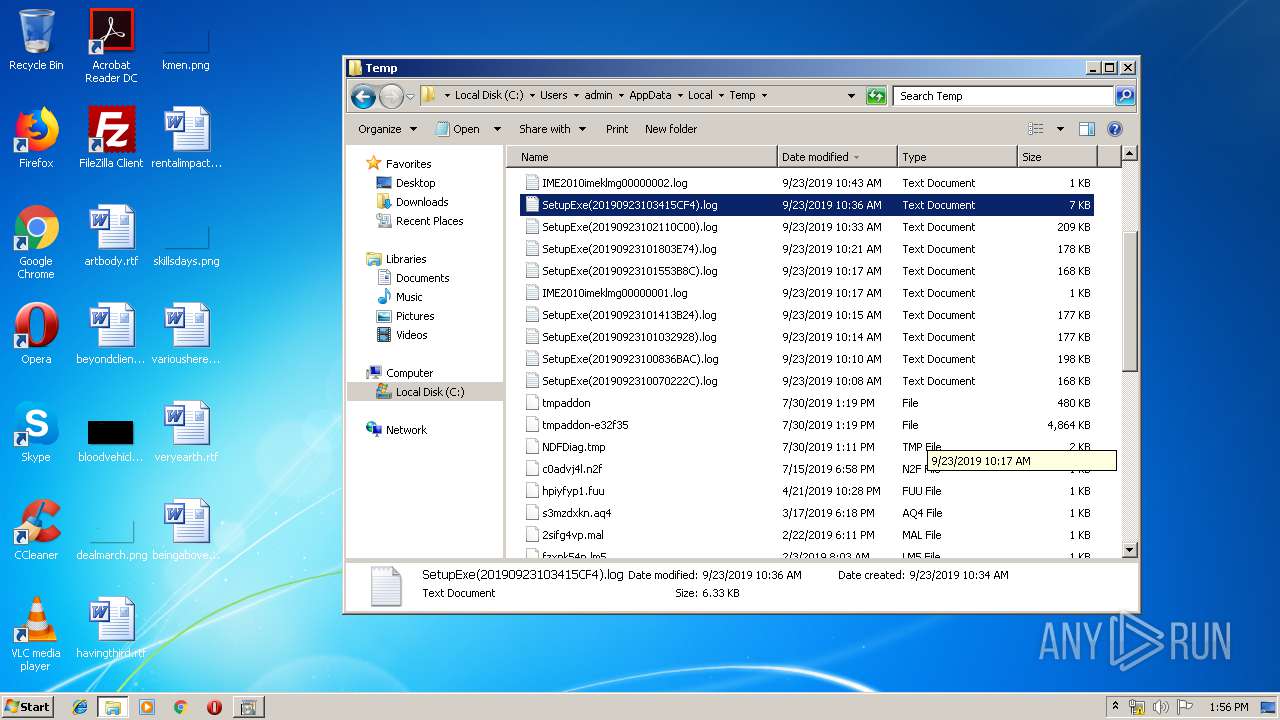
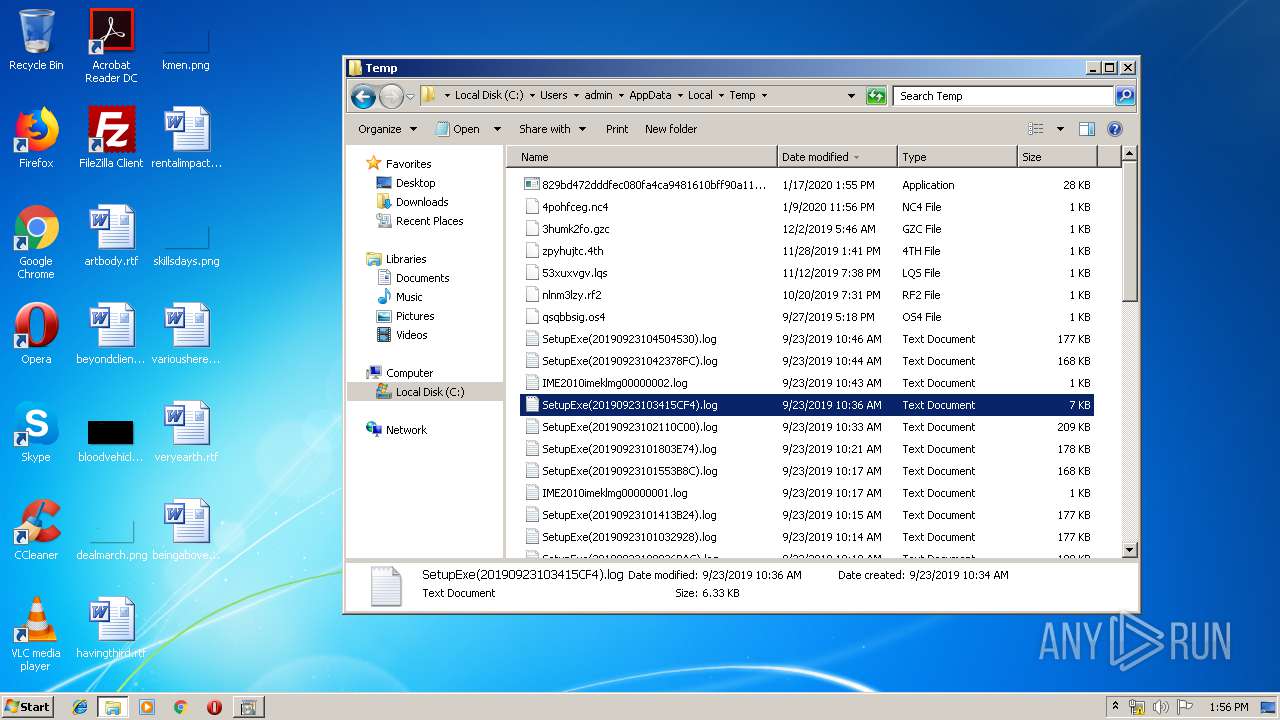
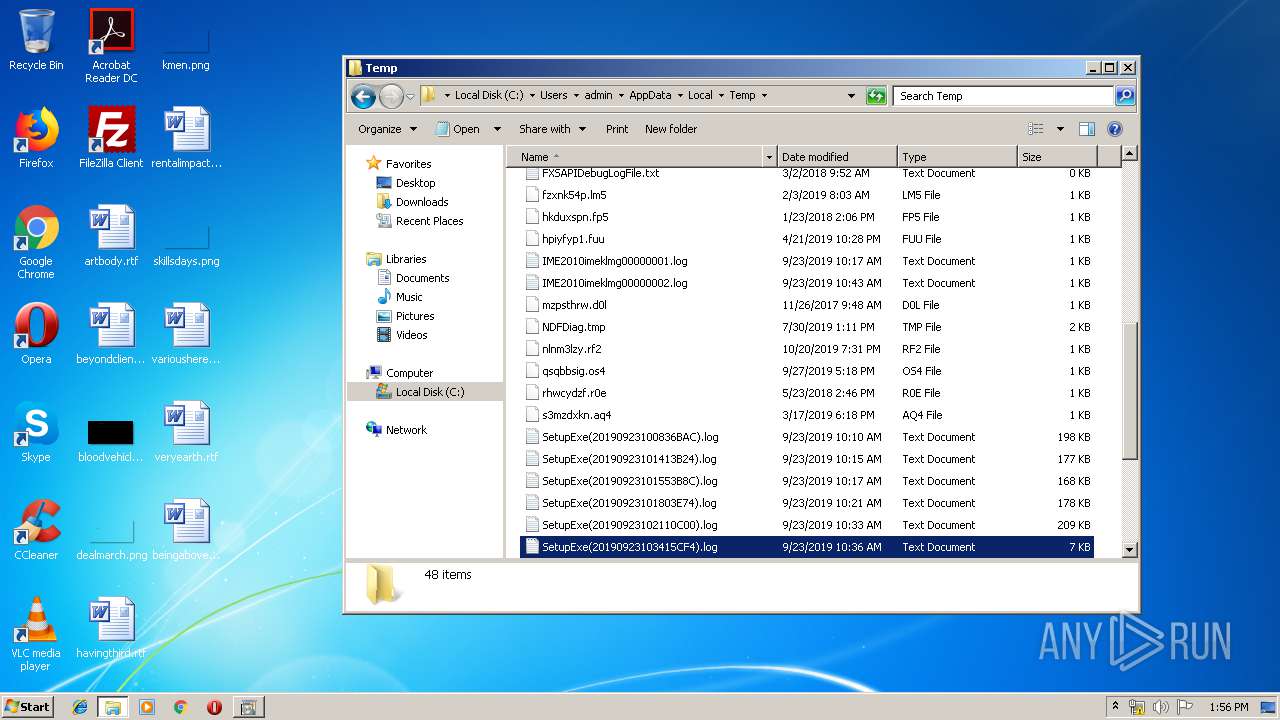
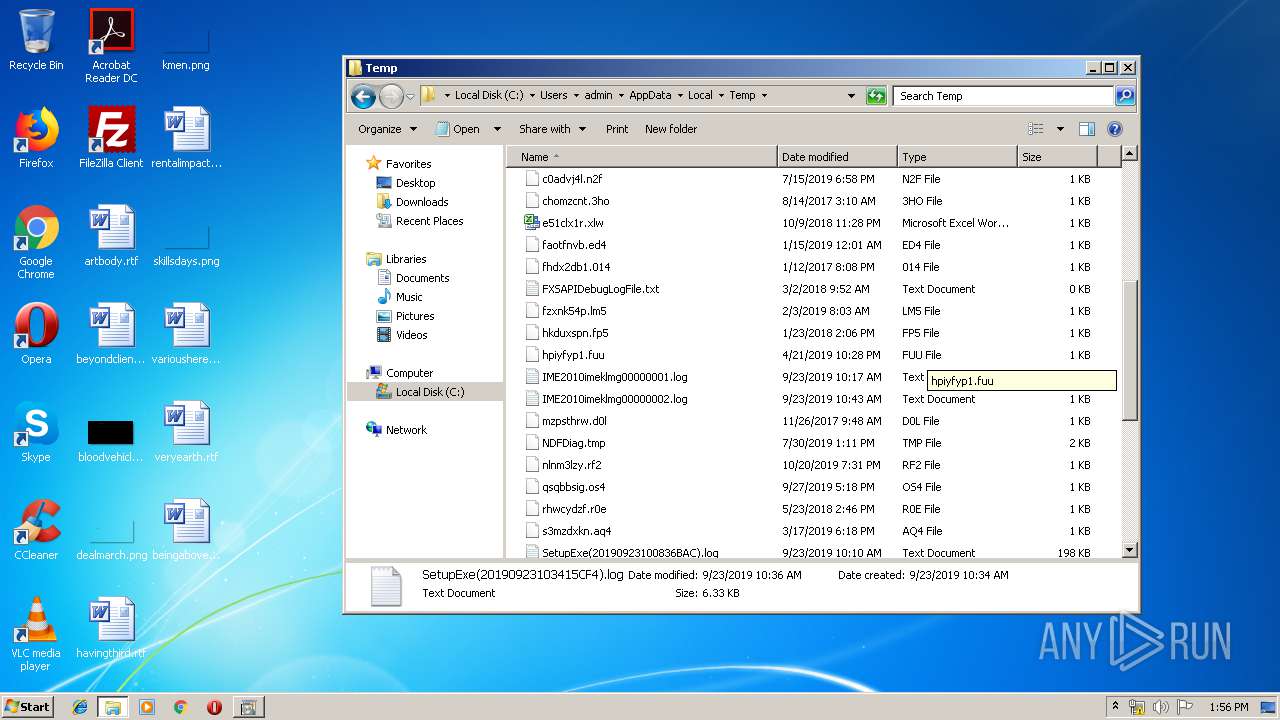
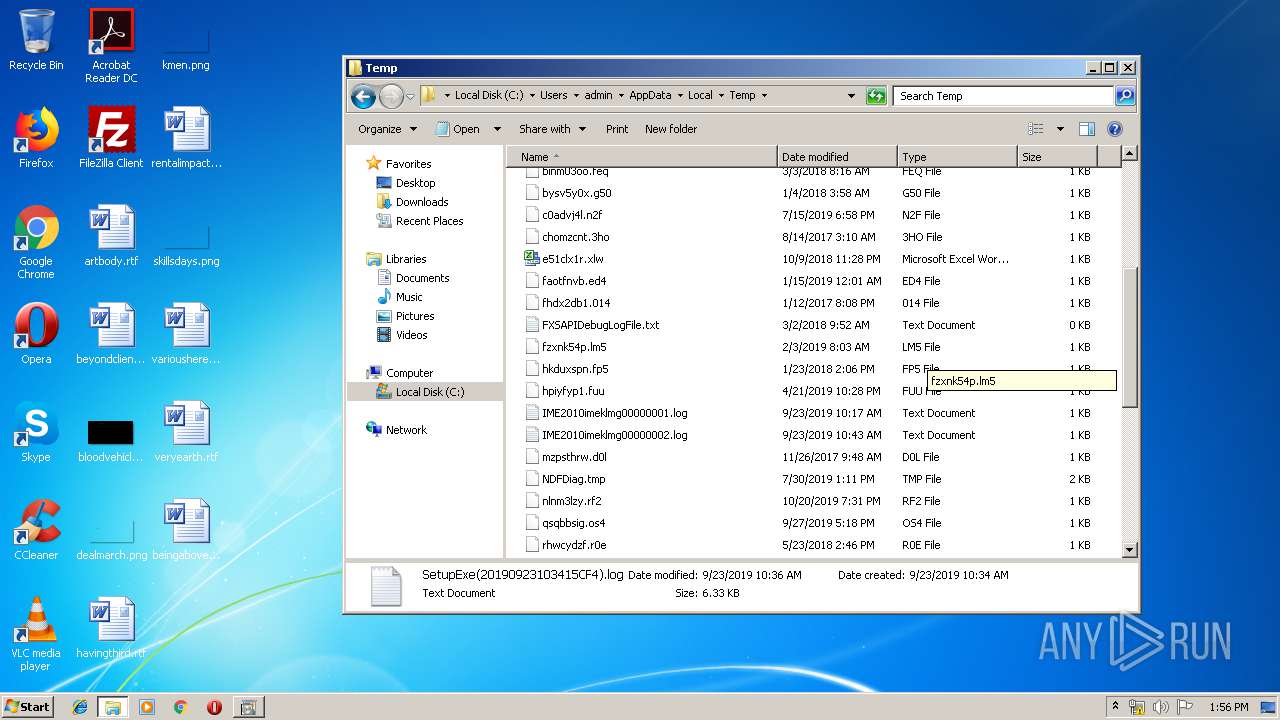
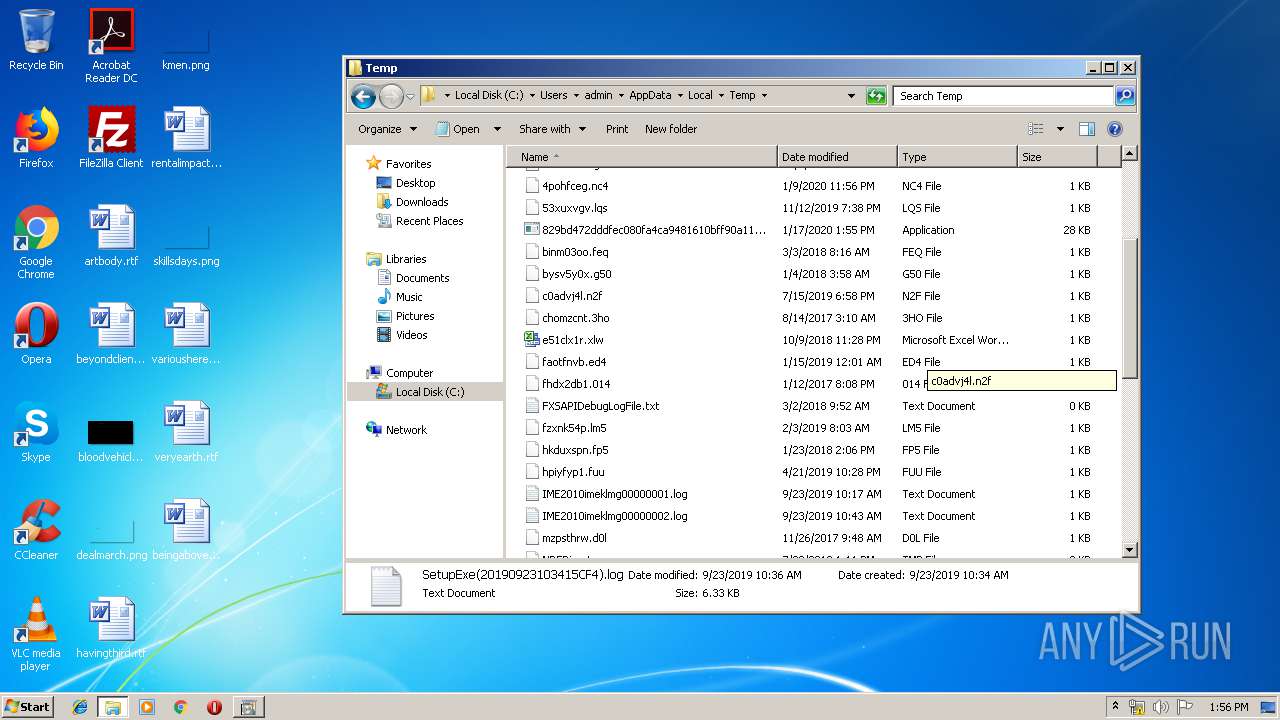
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1712 | 829bd472dddfec080fa4ca9481610bff90a116af3d4c8e7b3c78a1d22c89eb8c.exe | C:\Users\admin\AppData\Local\Temp\0YQK7DR1.cmd | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report