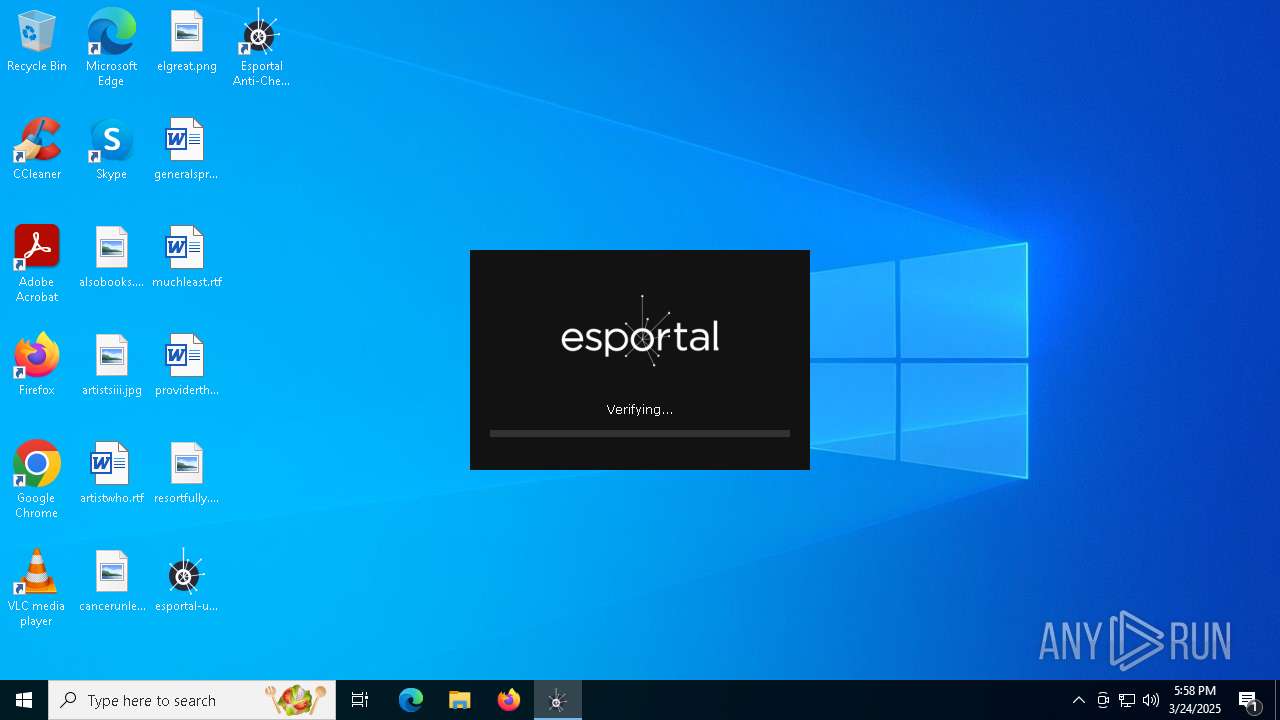
| File name: | esportal-updater.exe |
| Full analysis: | https://app.any.run/tasks/9ce3b840-2b64-45dd-8077-c78ac8aefaff |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 17:55:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 11 sections |
| MD5: | C11515310AF6ABE814E5178D59CE50D5 |
| SHA1: | B307BF10A00B67DFB3C012AF72C190ED250A074B |
| SHA256: | 828BB51DE94936A8D4A592D600C0B47683D73E78A0FC7D9C76BF1E0F67EDBD02 |
| SSDEEP: | 98304:Y11A7qGRplv9red52jILNmH1+miG/3tIWvRSBm3o2kBrMkqmAsK/e7fxdJzpCeGZ:MXUUfdo |
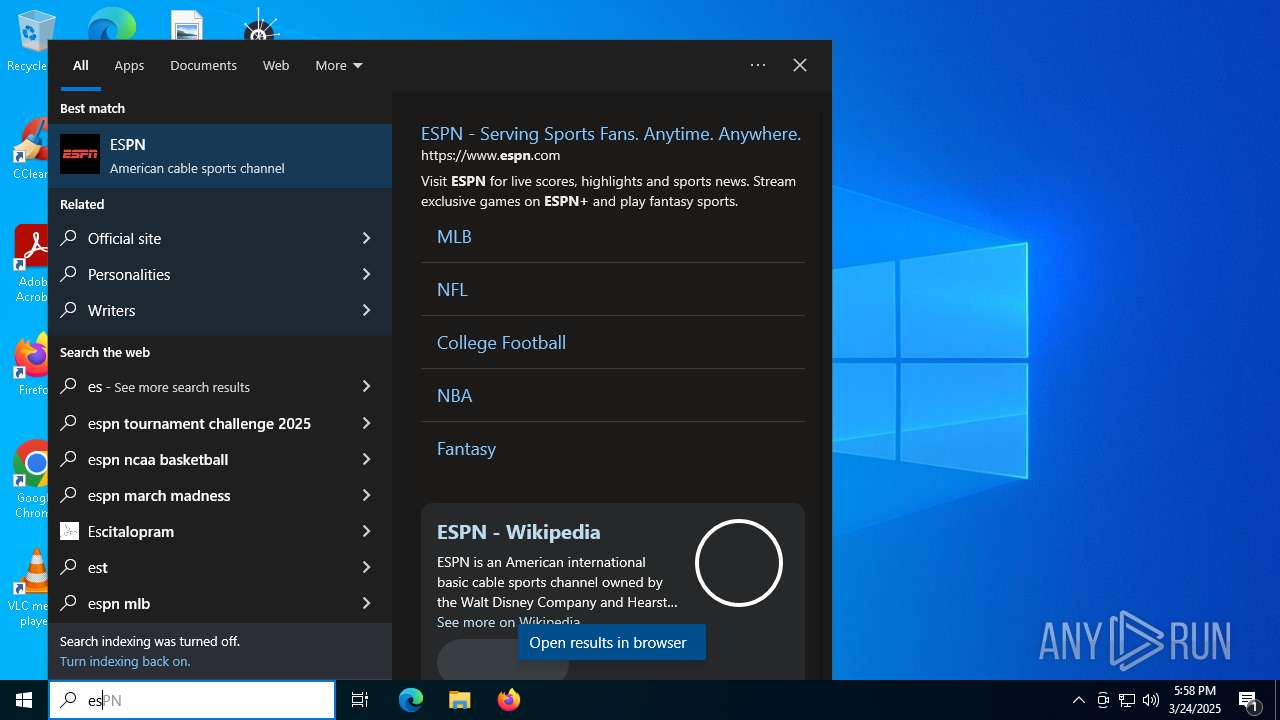
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- esportal-updater.exe (PID: 4988)
Reads security settings of Internet Explorer
- esportal-updater.exe (PID: 4988)
- ShellExperienceHost.exe (PID: 1012)
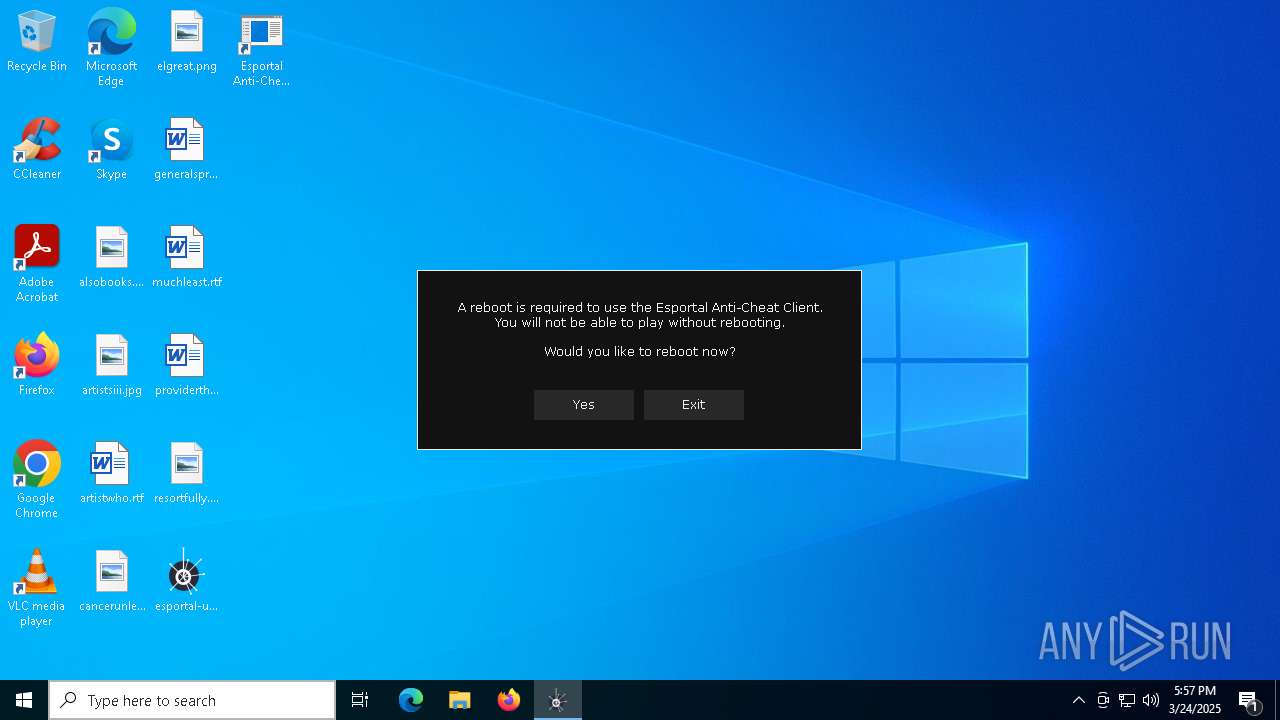
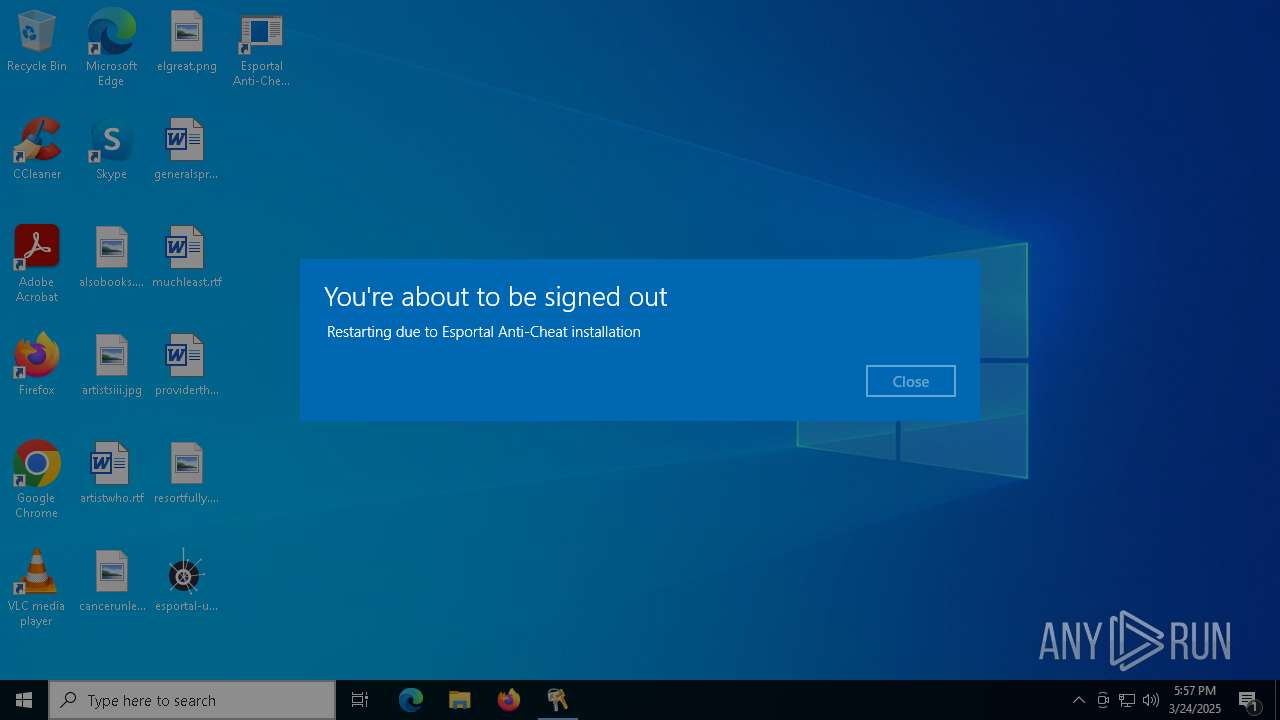
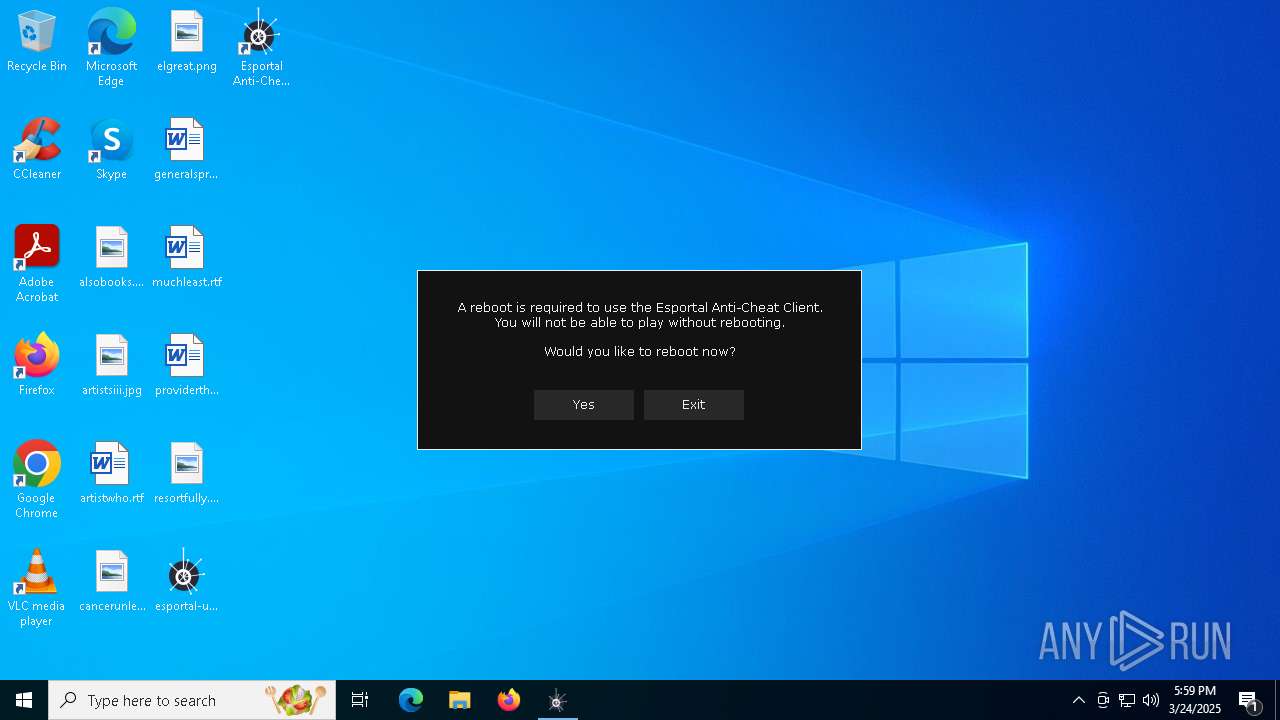
Application launched itself
- esportal-updater.exe (PID: 4988)
Executable content was dropped or overwritten
- esportal-updater.exe (PID: 6592)
- esportal-updater.exe (PID: 4120)
- esportal-updater.exe (PID: 5048)
- esportal-updater.exe (PID: 6776)
Starts CMD.EXE for commands execution
- esportal-updater.exe (PID: 6592)
- esportal-updater.exe (PID: 4120)
- esportal-updater.exe (PID: 6776)
- esportal-updater.exe (PID: 4736)
The executable file from the user directory is run by the CMD process
- esportal-updater.exe (PID: 4120)
- esportal-updater.exe (PID: 4736)
- esportal-updater.exe (PID: 5048)
- esportal-updater.exe (PID: 6864)
Executes application which crashes
- esportal-updater.exe (PID: 4988)
Drops a system driver (possible attempt to evade defenses)
- esportal-updater.exe (PID: 4120)
- esportal-updater.exe (PID: 5048)
Creates a software uninstall entry
- esportal-updater.exe (PID: 4120)
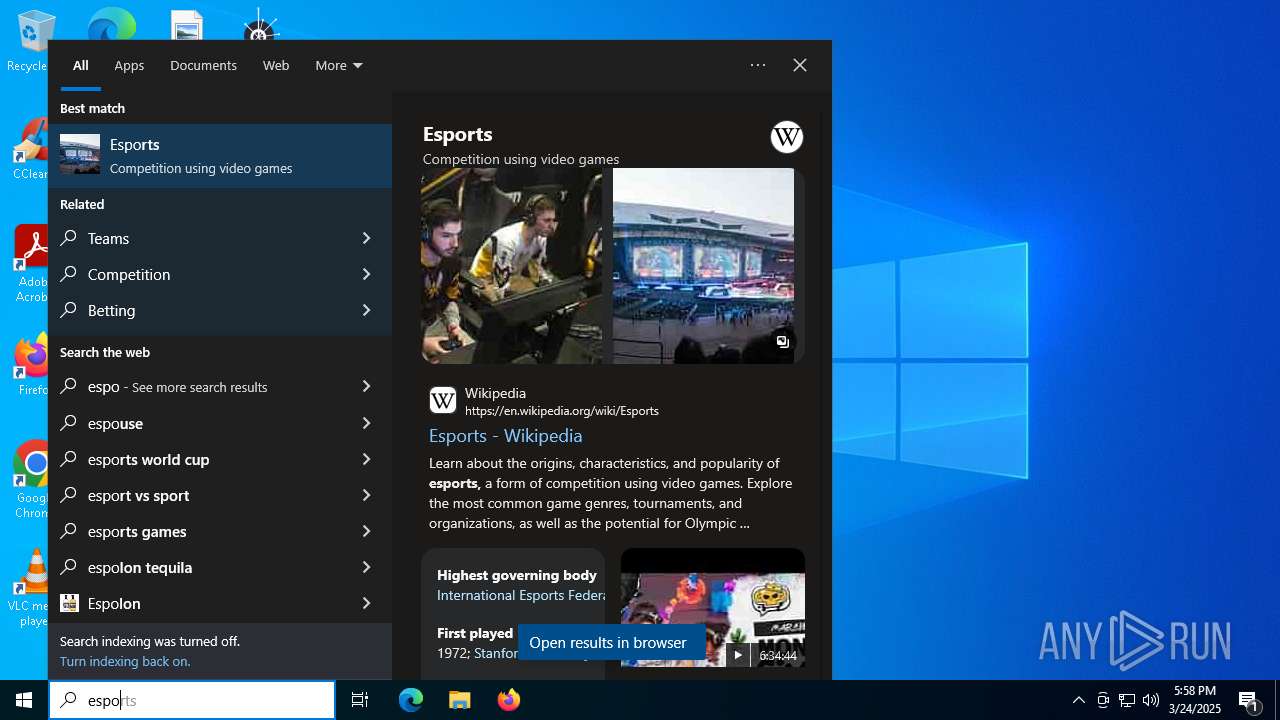
Searches for installed software
- esportal-updater.exe (PID: 5048)
- esportal-updater.exe (PID: 4736)
- esportal-updater.exe (PID: 6776)
Creates files in the driver directory
- esportal-driver-installer.exe (PID: 6944)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4148)
- esportal-updater.exe (PID: 6776)
INFO
Checks supported languages
- esportal-updater.exe (PID: 4988)
- esportal-updater.exe (PID: 6592)
- esportal-updater.exe (PID: 4120)
- ShellExperienceHost.exe (PID: 1012)
- esportal-updater.exe (PID: 5048)
- esportal-driver-installer.exe (PID: 6944)
- SearchApp.exe (PID: 5388)
- esportal-updater.exe (PID: 4736)
The sample compiled with english language support
- esportal-updater.exe (PID: 4988)
- esportal-updater.exe (PID: 6592)
- esportal-updater.exe (PID: 4120)
- esportal-updater.exe (PID: 5048)
- esportal-updater.exe (PID: 6776)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 1040)
- WerFault.exe (PID: 5968)
- esportal-updater.exe (PID: 4120)
- esportal-updater.exe (PID: 5048)
Reads the computer name
- esportal-updater.exe (PID: 4988)
- esportal-updater.exe (PID: 6592)
- esportal-updater.exe (PID: 4120)
- ShellExperienceHost.exe (PID: 1012)
- esportal-updater.exe (PID: 4736)
- esportal-updater.exe (PID: 5048)
- esportal-driver-installer.exe (PID: 6944)
- esportal-updater.exe (PID: 6776)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 1040)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 1676)
- BackgroundTransferHost.exe (PID: 4000)
- BackgroundTransferHost.exe (PID: 1128)
- BackgroundTransferHost.exe (PID: 6964)
- BackgroundTransferHost.exe (PID: 1040)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 1040)
Create files in a temporary directory
- esportal-updater.exe (PID: 4988)
- esportal-updater.exe (PID: 6592)
Process checks computer location settings
- esportal-updater.exe (PID: 4988)
- SearchApp.exe (PID: 5388)
Reads the machine GUID from the registry
- esportal-updater.exe (PID: 4120)
- esportal-updater.exe (PID: 5048)
- esportal-driver-installer.exe (PID: 6944)
- esportal-driver-installer.exe (PID: 7024)
- SearchApp.exe (PID: 5388)
Manual execution by a user
- esportal-updater.exe (PID: 6696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:05 14:08:02+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 5712384 |
| InitializedDataSize: | 2344448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x538e24 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Esportal AB |
| FileDescription: | Esportal Anti-Cheat Client |
| FileVersion: | 1.0.0.0 |
| InternalName: | resources.rc |
| LegalCopyright: | (C) 2023 Esportal AB |
| OriginalFileName: | resources.rc |
| ProductName: | Esportal Anti-Cheat Client |
| ProductVersion: | 1.0.0.0 |
Total processes
294
Monitored processes
30
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | cmd.exe /c start "" "C:\Users\admin\AppData\Local\Temp\esportal-updater.exe" | C:\Windows\System32\cmd.exe | — | esportal-updater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2084 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 1073807364 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4000 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | "C:\Users\admin\AppData\Local\Temp\esportal-updater.exe" | C:\Users\admin\AppData\Local\Temp\esportal-updater.exe | cmd.exe | ||||||||||||
User: admin Company: Esportal AB Integrity Level: HIGH Description: Esportal Anti-Cheat Client Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
20 323
Read events
20 175
Write events
145
Delete events
3
Modification events
| (PID) Process: | (4000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1040) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1040) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1040) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1676) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1676) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1676) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6964) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
20
Suspicious files
145
Text files
165
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1040 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\9285fb84-e823-4f73-a04c-03b97daea3b9.down_data | — | |
MD5:— | SHA256:— | |||
| 5968 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_esportal-updater_14dcb22ee4a494c449f38c86d7bb9414222c277e_06a6358c_68c06771-c04b-4824-b47c-ee121aff79db\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4120 | esportal-updater.exe | C:\Users\admin\AppData\Local\Esportal\esportal-bt.sys | — | |
MD5:— | SHA256:— | |||
| 4120 | esportal-updater.exe | C:\Users\admin\AppData\Local\Esportal\esportal-anti-cheat.exe | — | |
MD5:— | SHA256:— | |||
| 4120 | esportal-updater.exe | C:\Users\admin\AppData\Local\Esportal\esportal-gui.dll | — | |
MD5:— | SHA256:— | |||
| 1040 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:14619FF8E139147ED2832D5A3B9CDFA6 | SHA256:E6FBA5DEDF6DC0B7AAC91368EE05F8638167F8D086D37091879837FEF8FAB963 | |||
| 5048 | esportal-updater.exe | C:\Users\admin\AppData\Local\Esportal\runtime\esportal-anti-cheat.exe | — | |
MD5:— | SHA256:— | |||
| 5048 | esportal-updater.exe | C:\Users\admin\AppData\Local\Esportal\runtime\esportal-bt.sys | — | |
MD5:— | SHA256:— | |||
| 1040 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\9285fb84-e823-4f73-a04c-03b97daea3b9.48d39b71-802f-4bea-8513-42ccfa2aa501.down_meta | binary | |
MD5:D4DB4F03A99A851E1F812BE4AABA9CE9 | SHA256:2D1E937E109A7D96362FC454DC246C61394A32AAEE68C4A2D30BED477E2819DA | |||
| 1040 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
57
DNS requests
36
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6476 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1040 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5388 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5388 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5388 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6476 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6476 | backgroundTaskHost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
cloudflare-dns.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4120 | esportal-updater.exe | Misc activity | ET INFO Observed Cloudflare DNS over HTTPS Domain (cloudflare-dns .com in TLS SNI) |