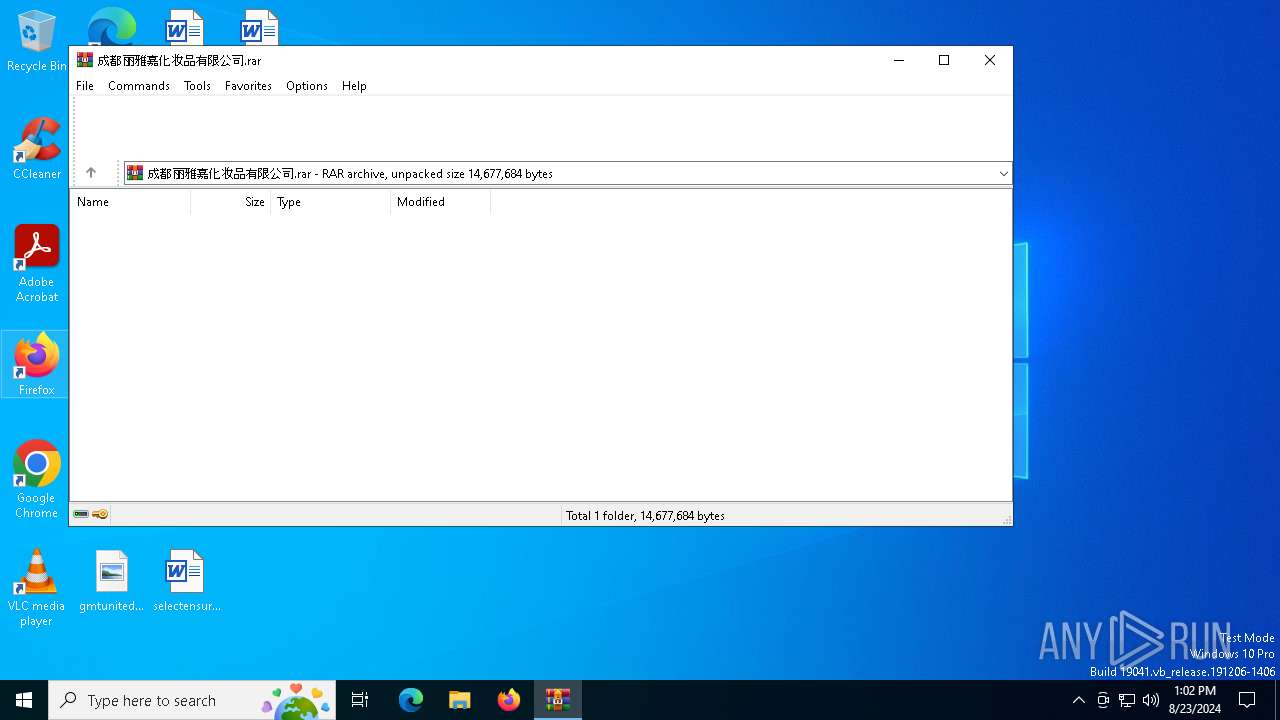
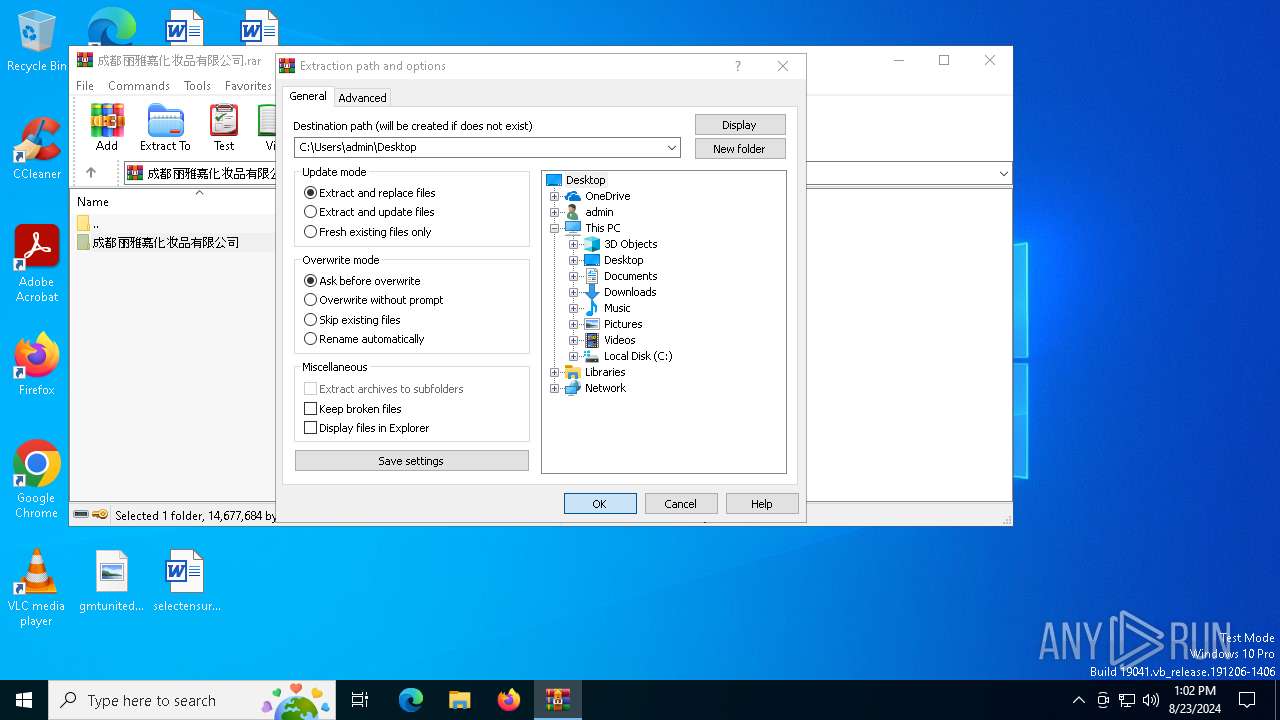
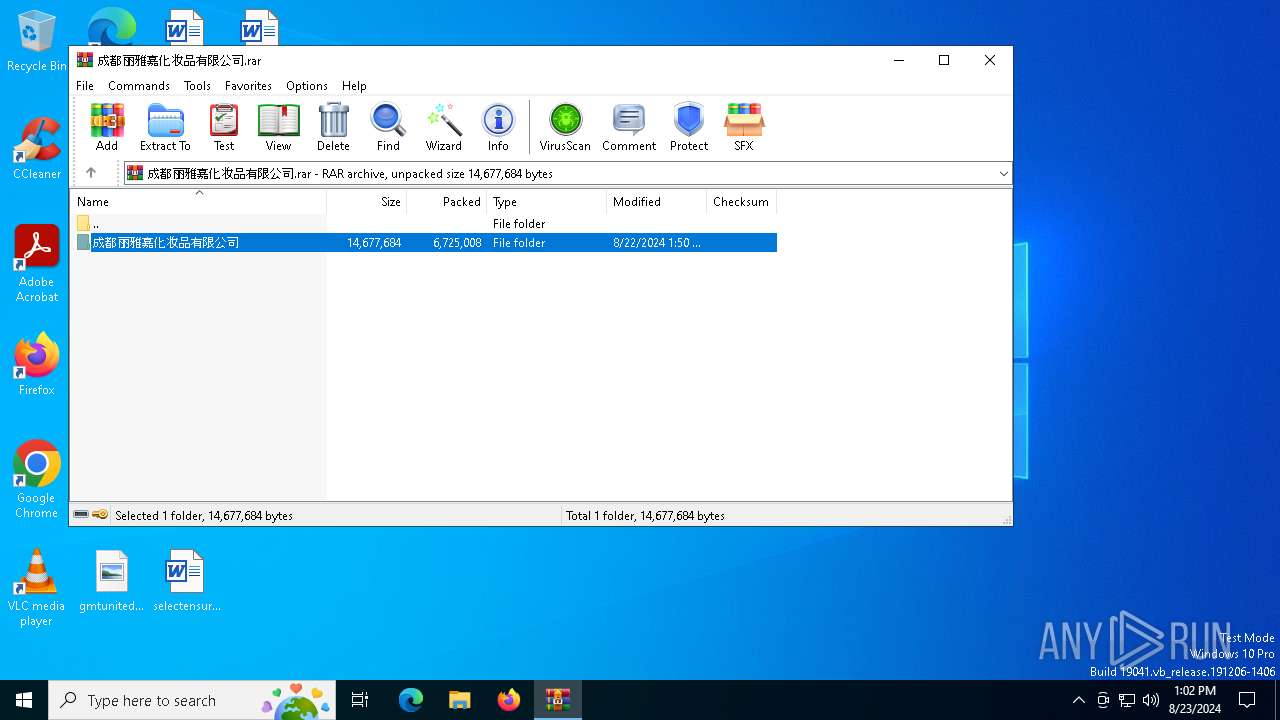
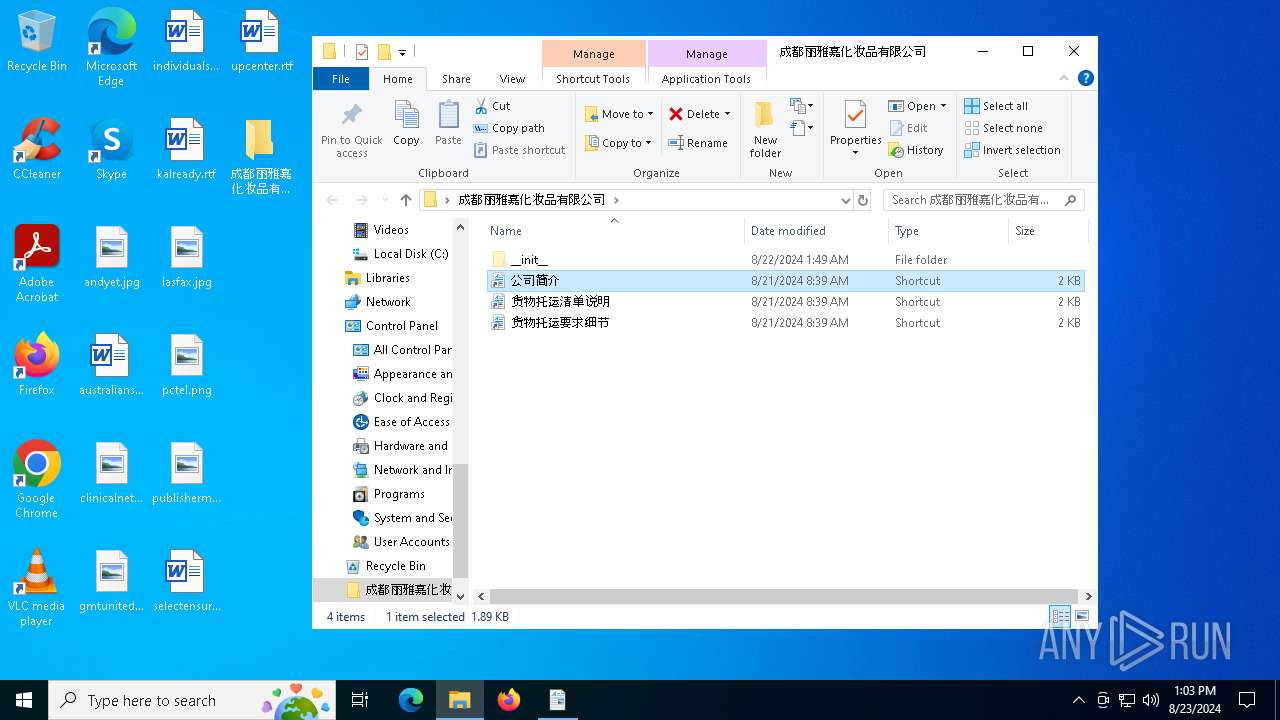
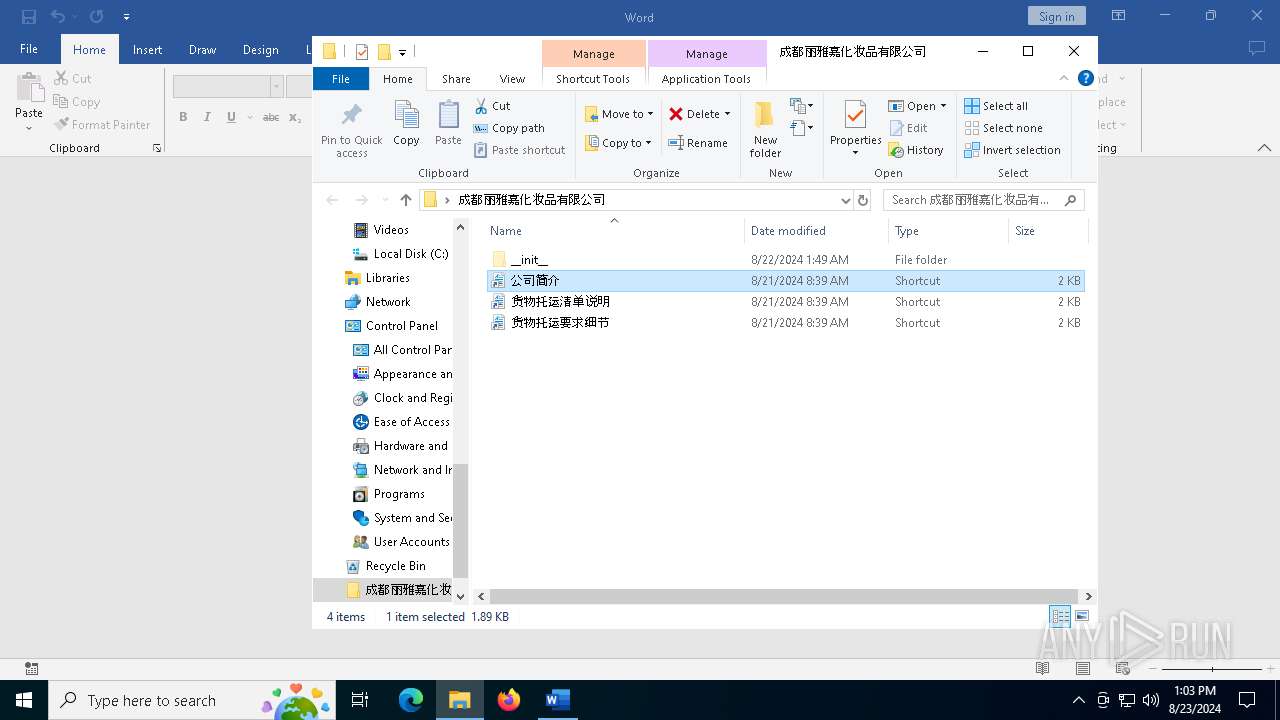
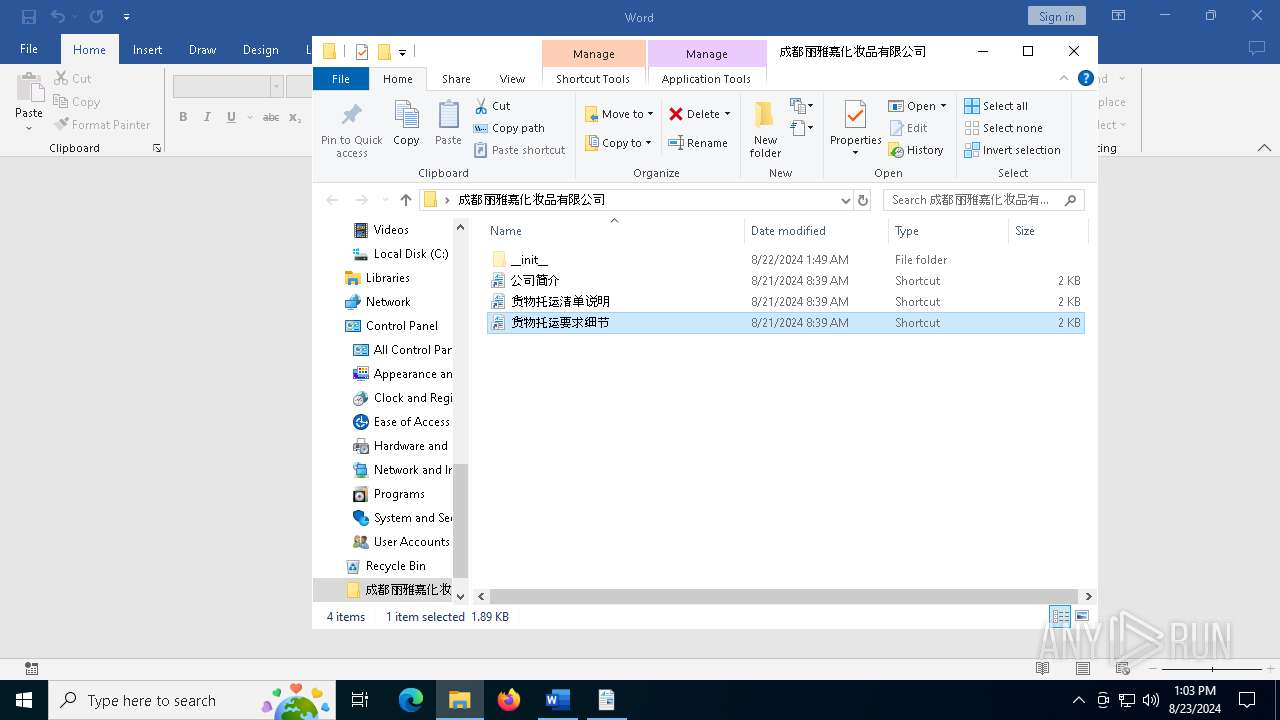
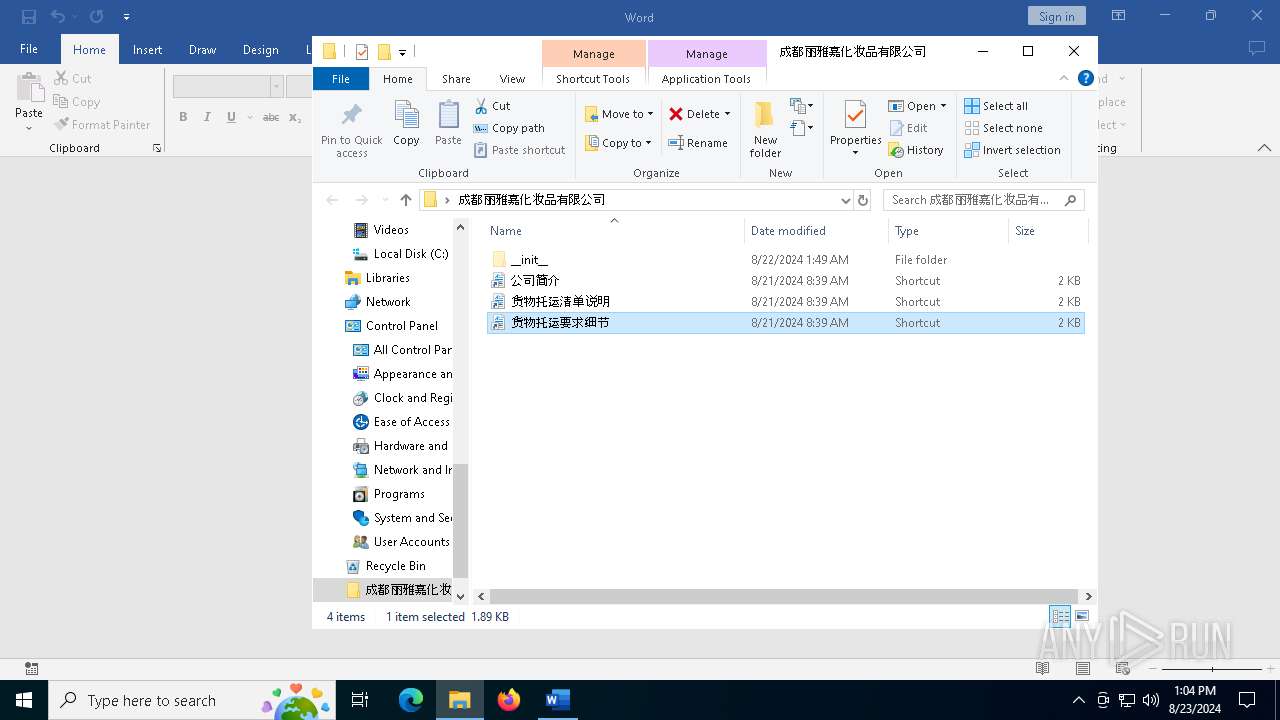
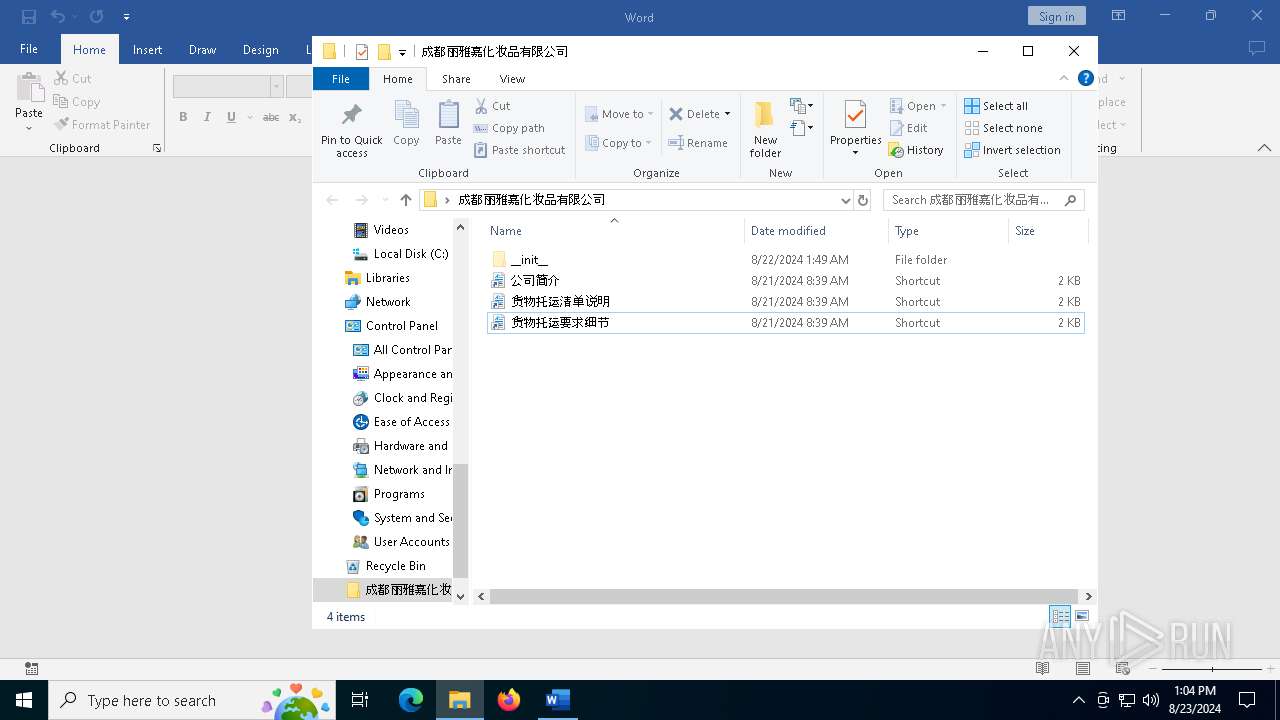
| File name: | 成都丽雅嘉化妆品有限公司.rar |
| Full analysis: | https://app.any.run/tasks/464852d2-0a32-41d4-9b45-9ea4e997bcd6 |
| Verdict: | Malicious activity |
| Analysis date: | August 23, 2024, 13:02:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 3AA9CD29645180518F66B7D1034A7B35 |
| SHA1: | 385737988D83A5A73D4CE551F834FB393B512264 |
| SHA256: | 82856572C1DE0CE98791F66F4D35FBC5A54A6D1BD520DC56F22DFE8CA7E7D919 |
| SSDEEP: | 98304:p8RA8yg+4ZG2fQkiB6rARdpb8mzOaVaiKPyXE0ukUScN8p3z1z8yRUFh2pjNFzFp:S9a9jFAb8FS1eHc6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
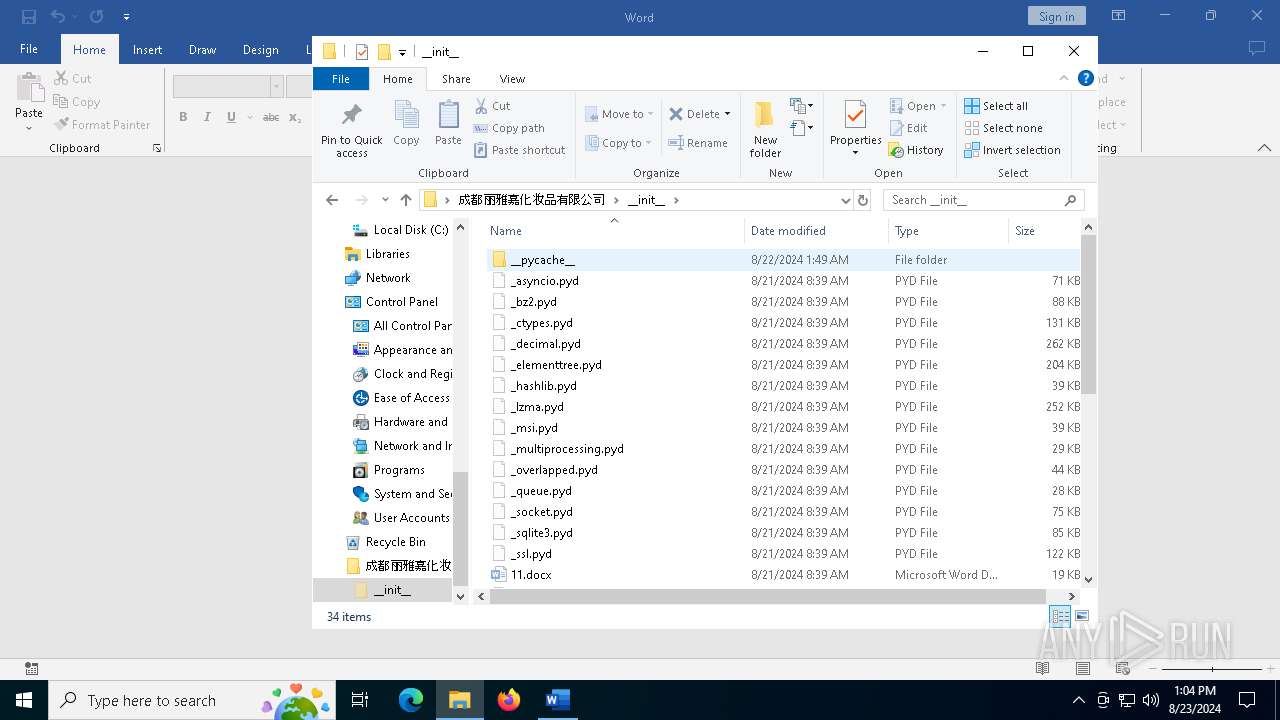
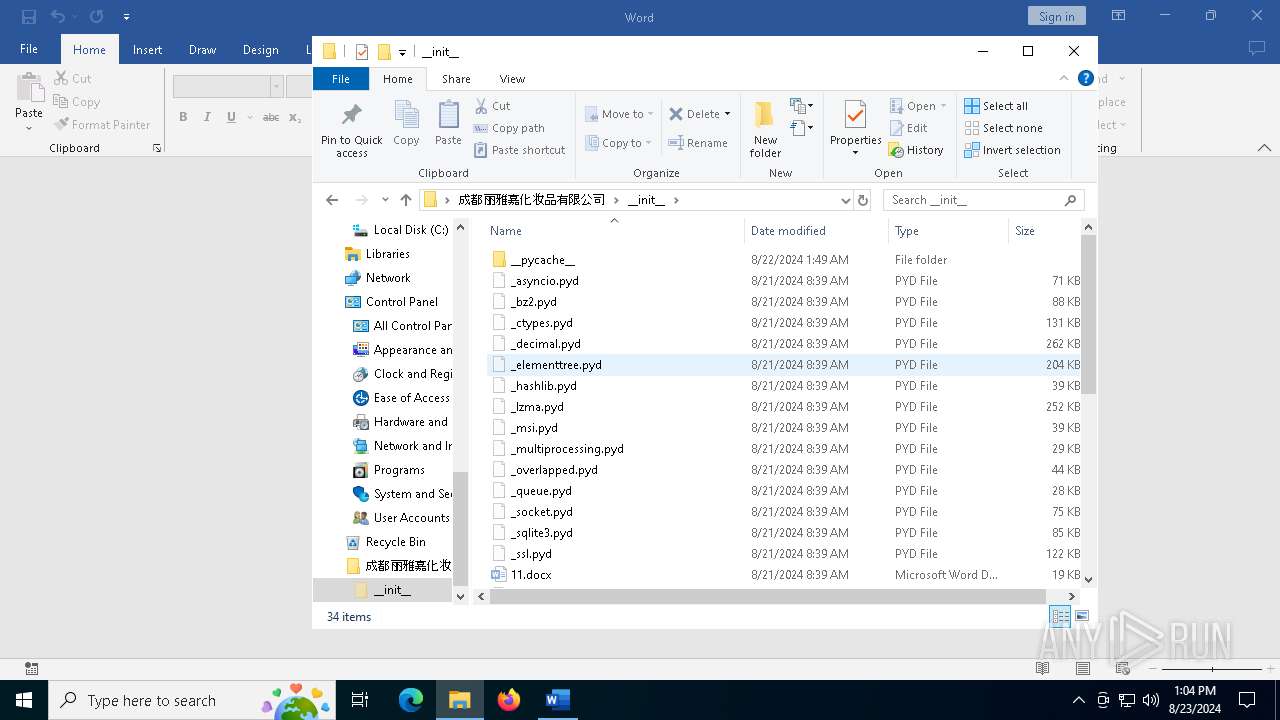
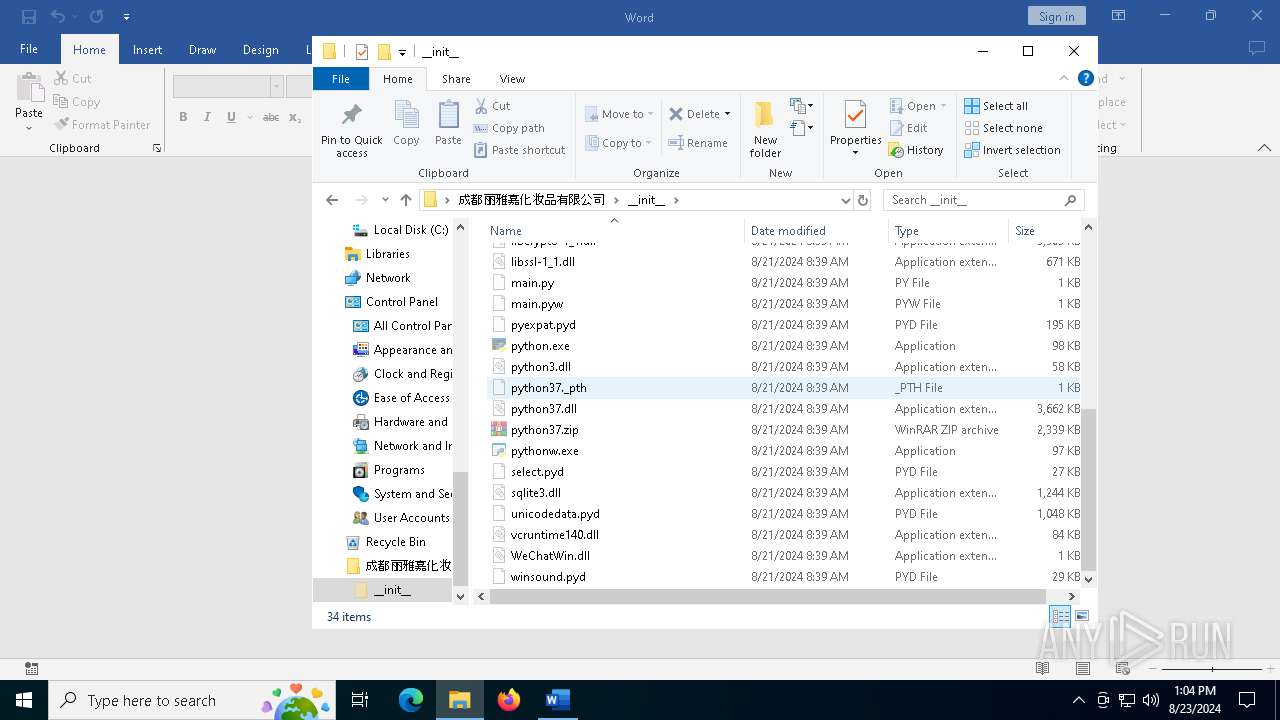
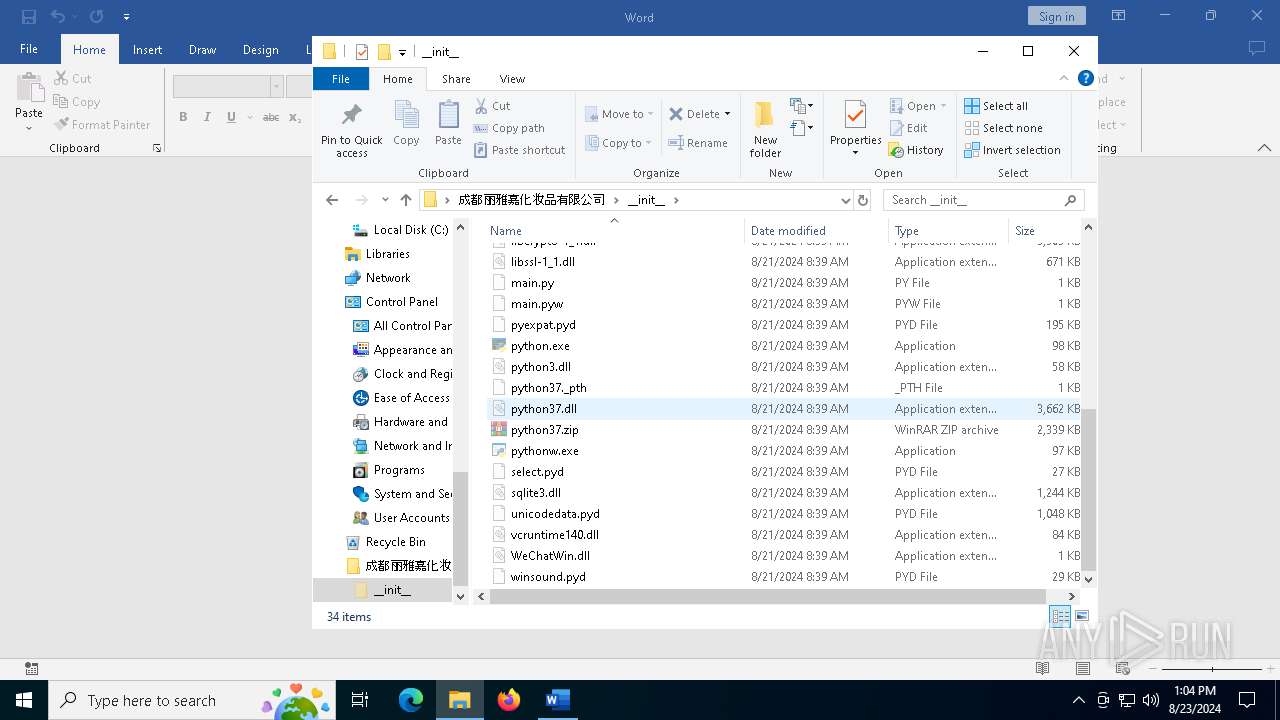
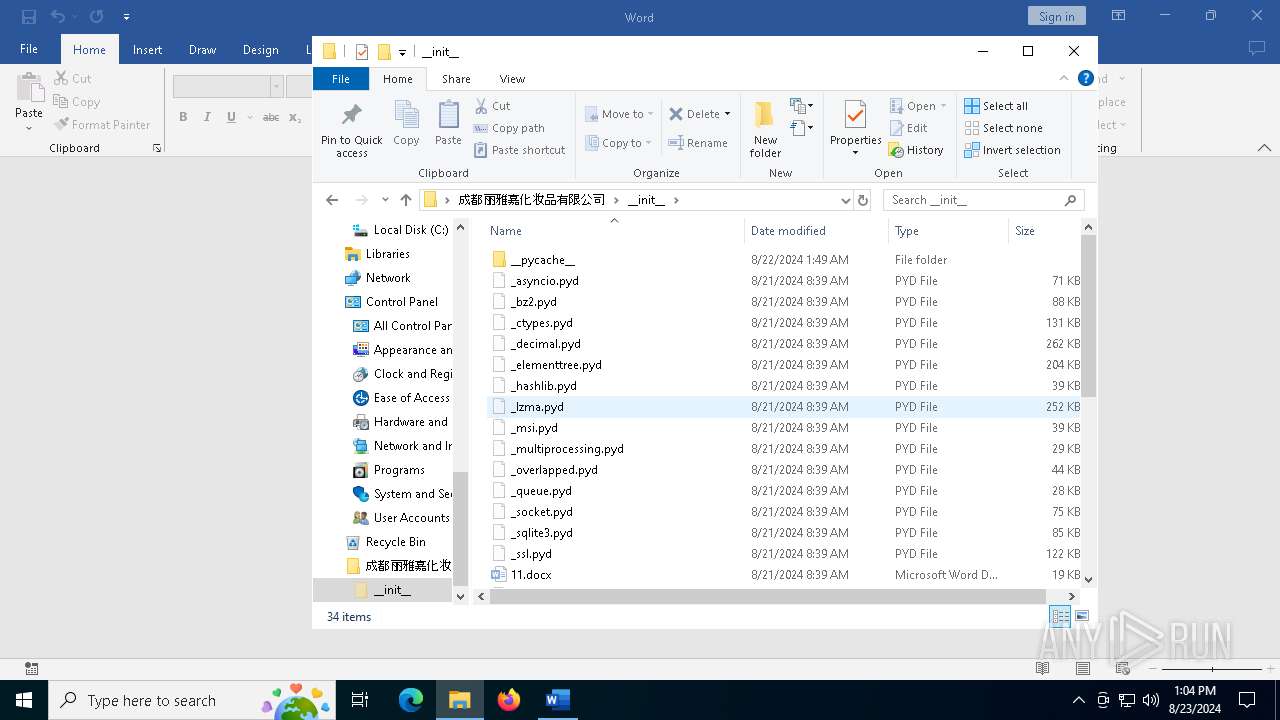
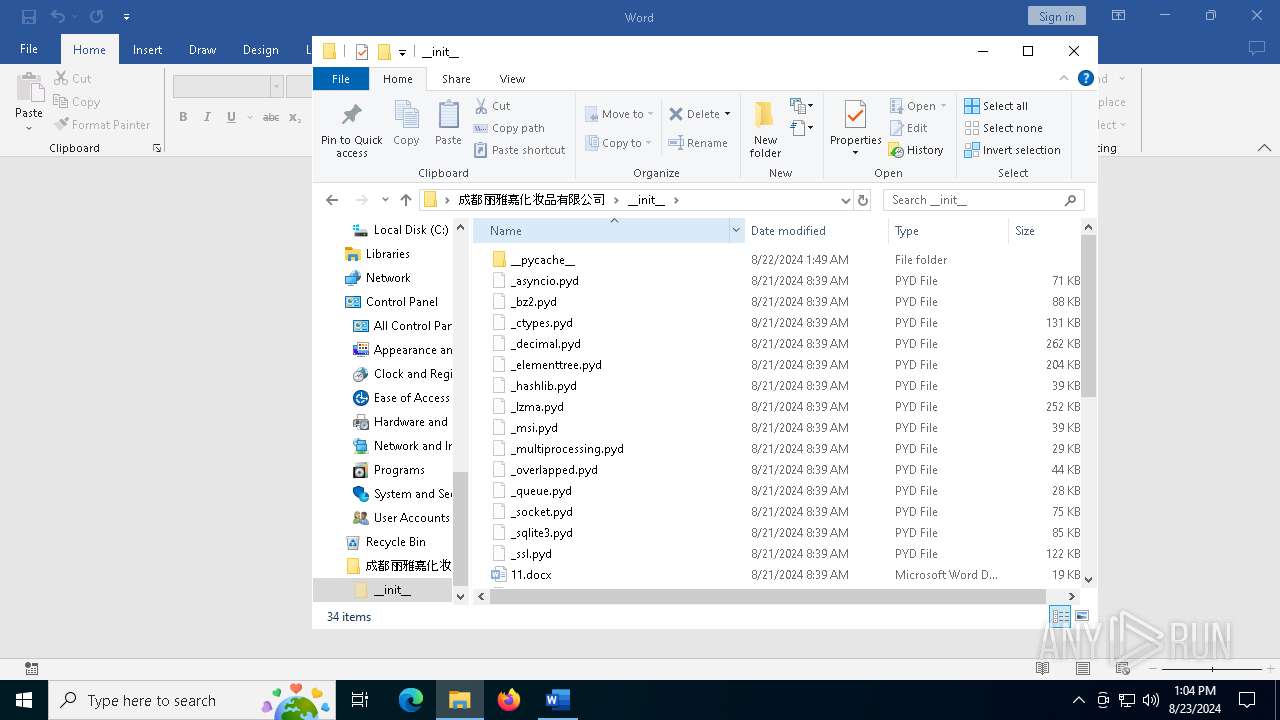
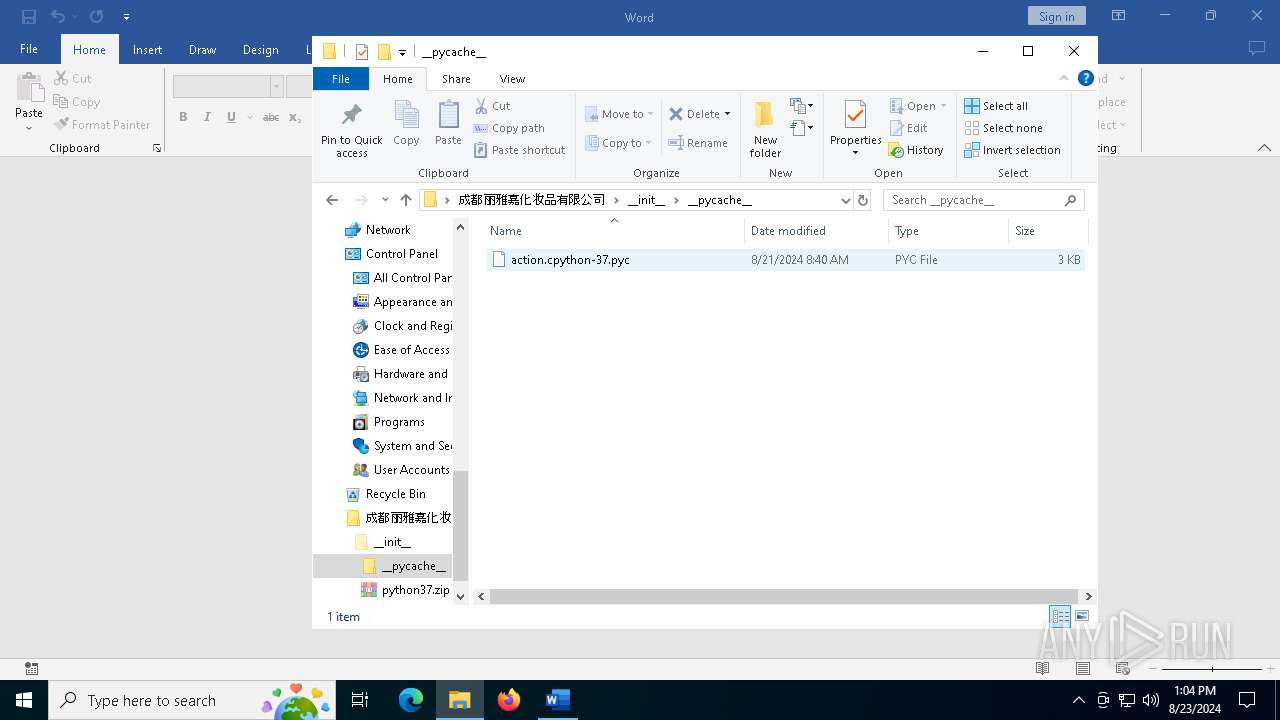
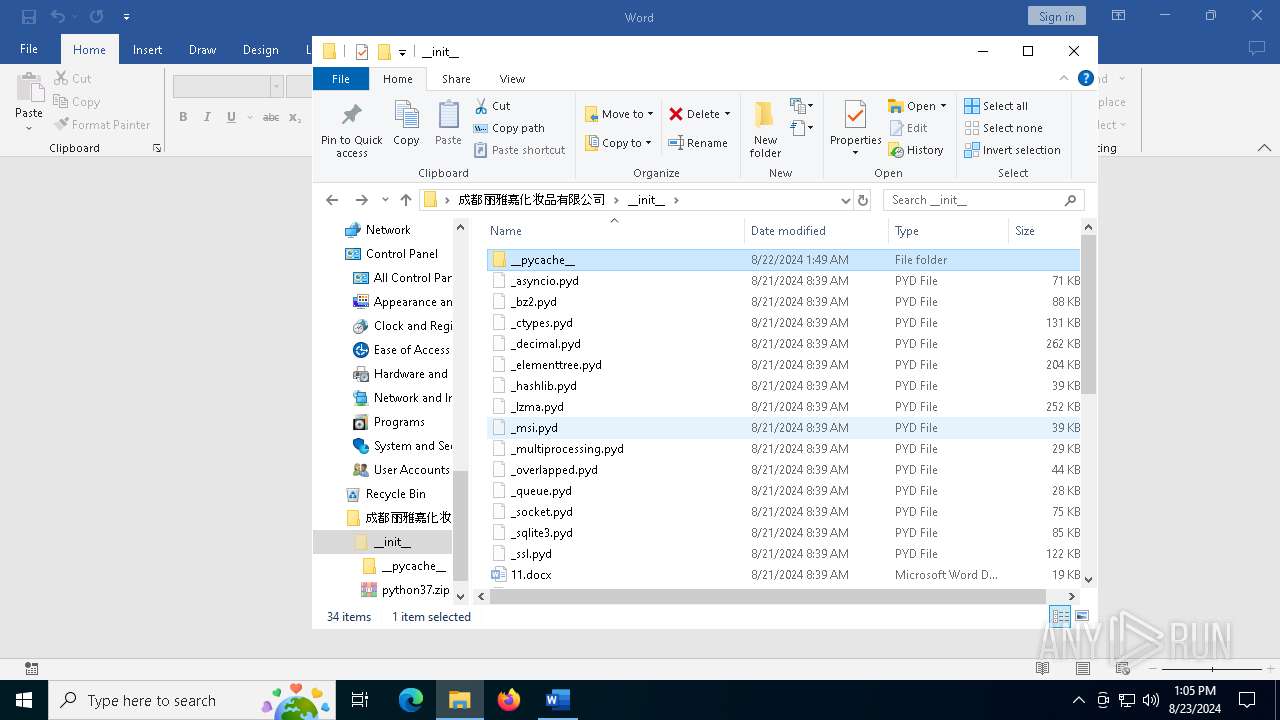
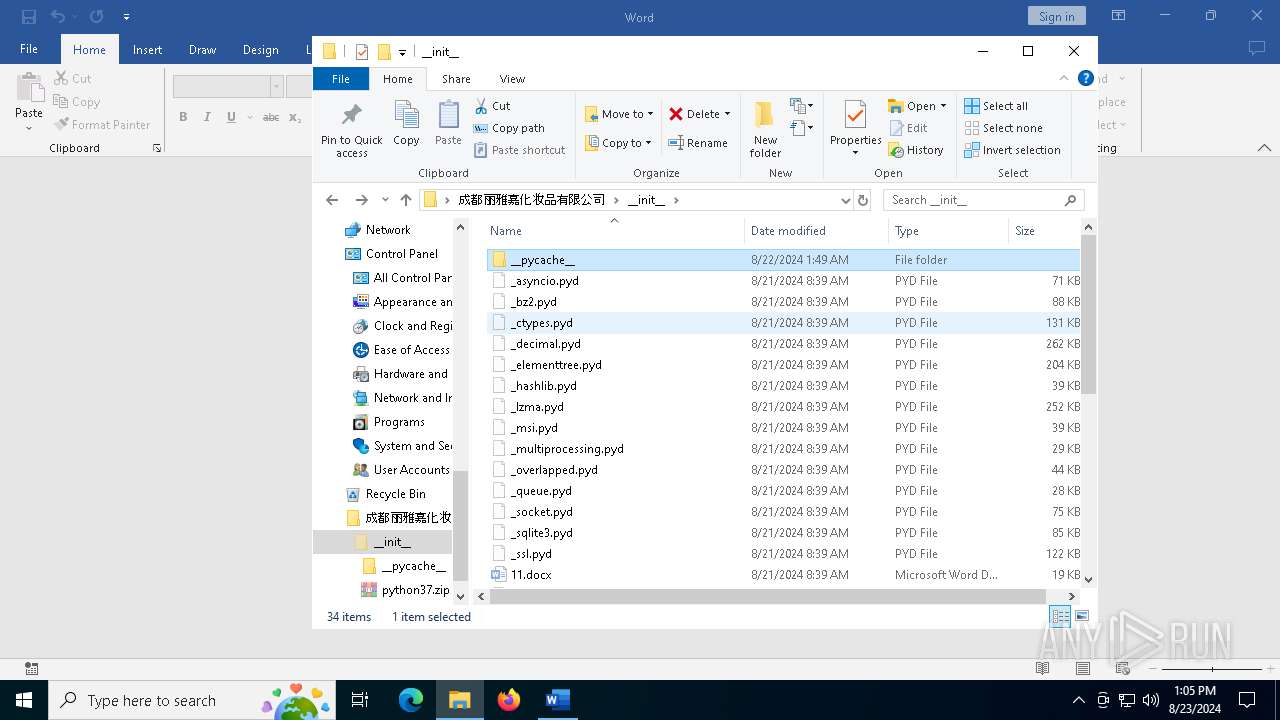
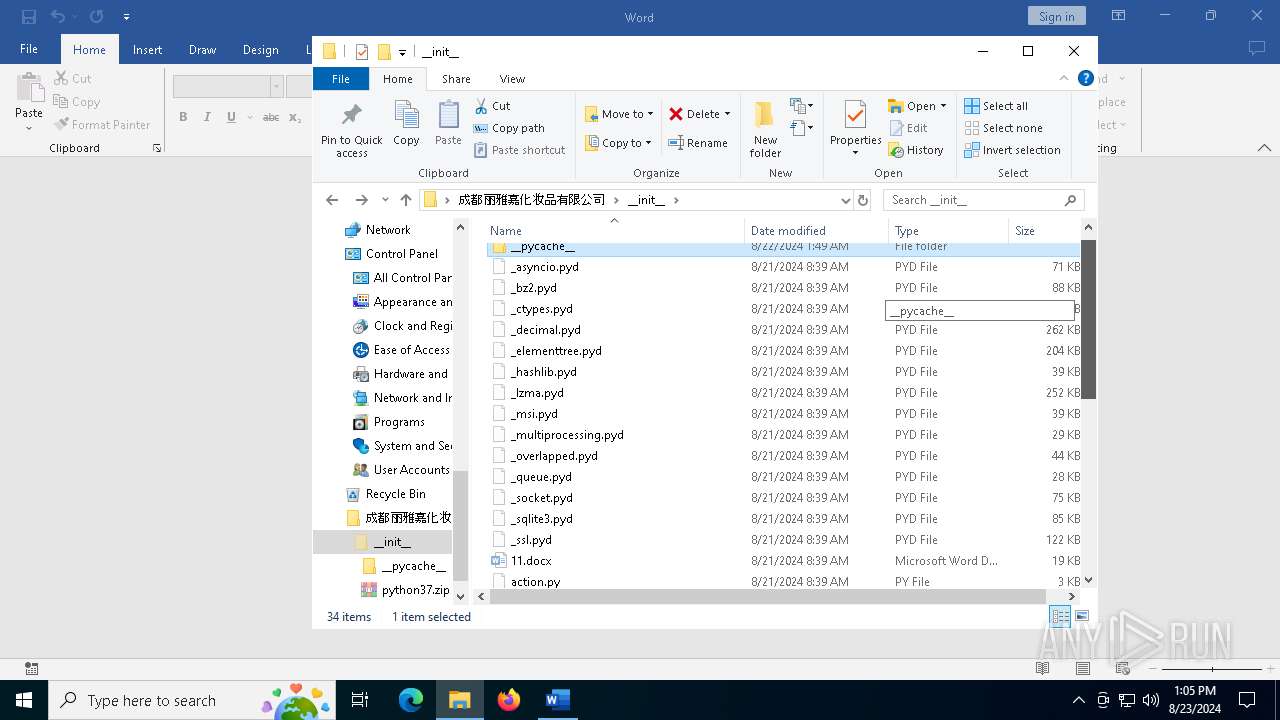
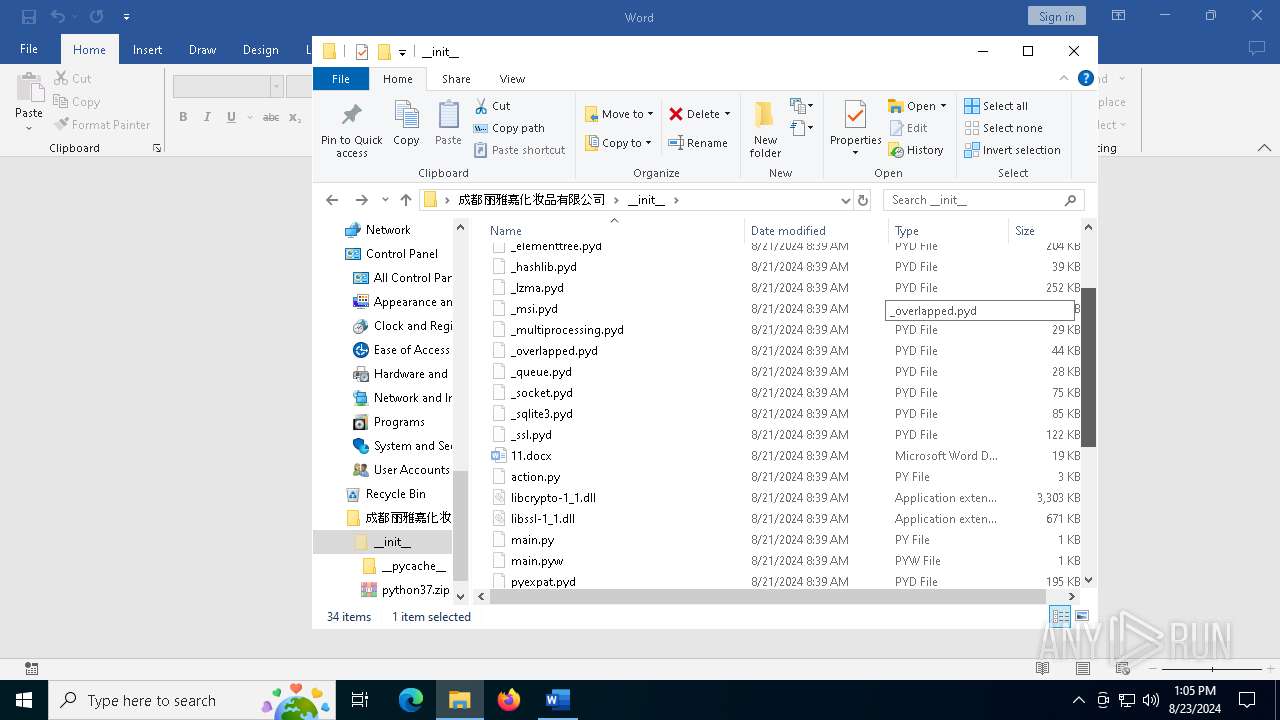
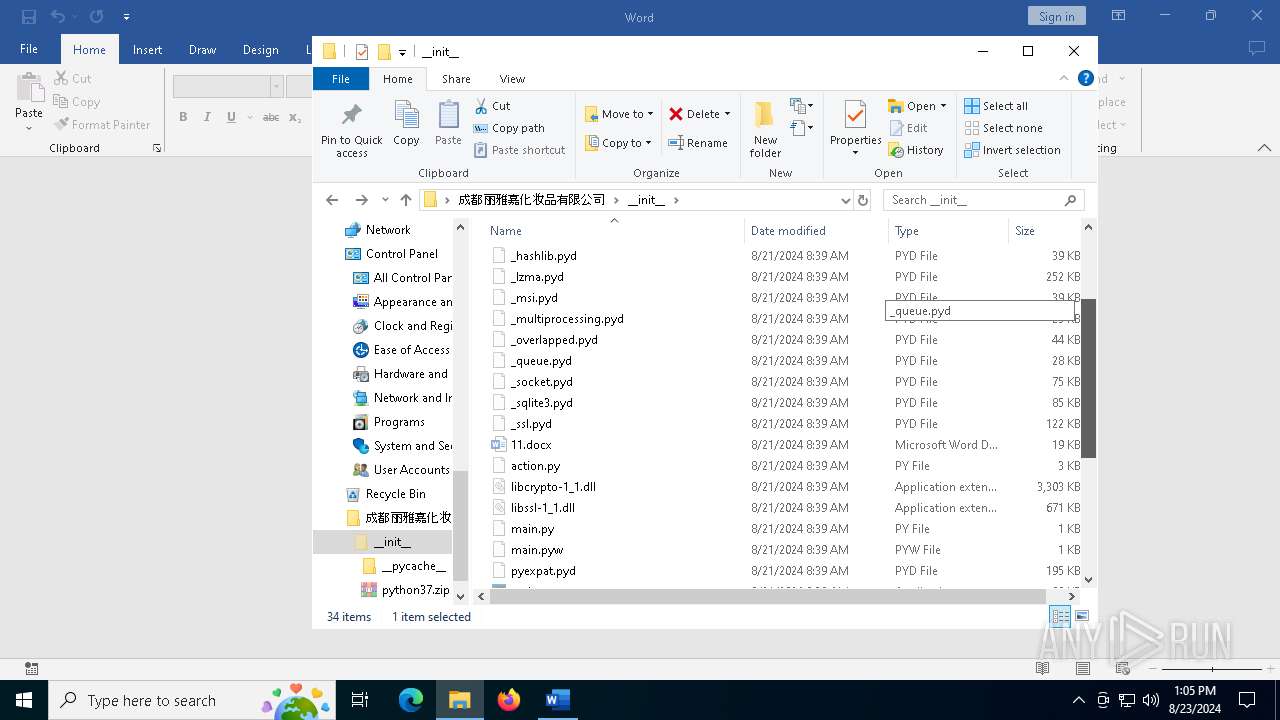
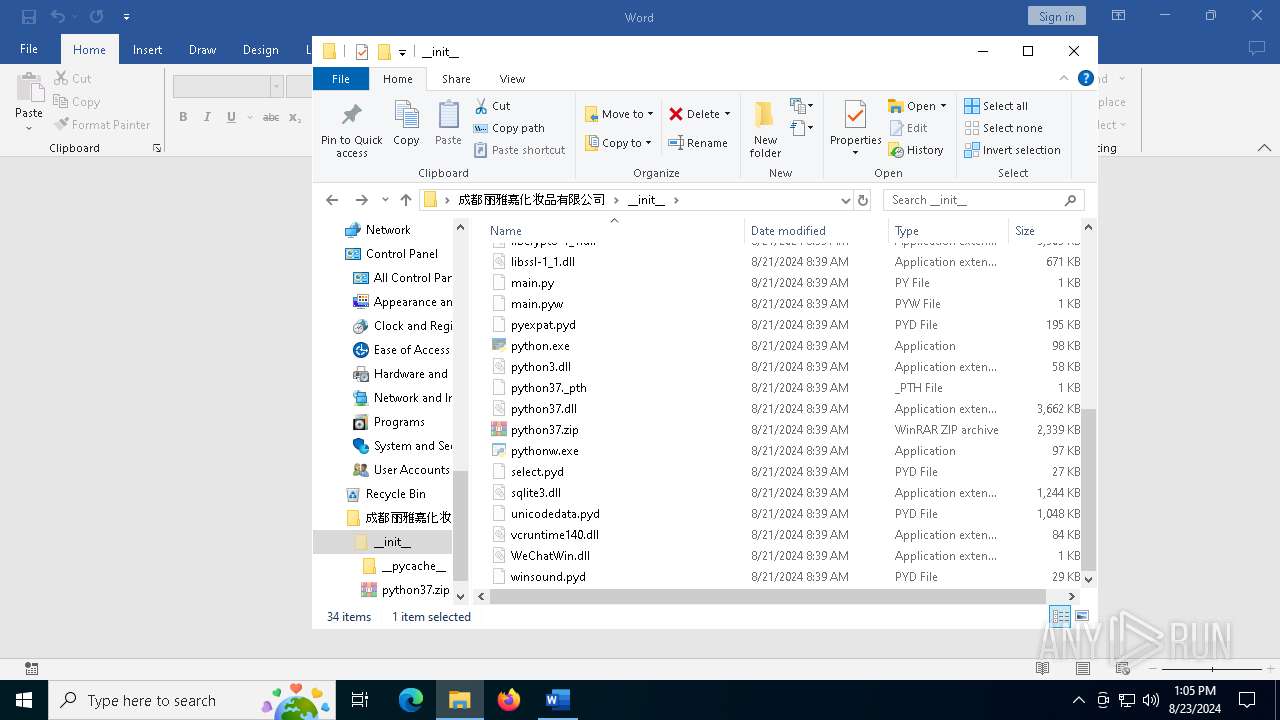
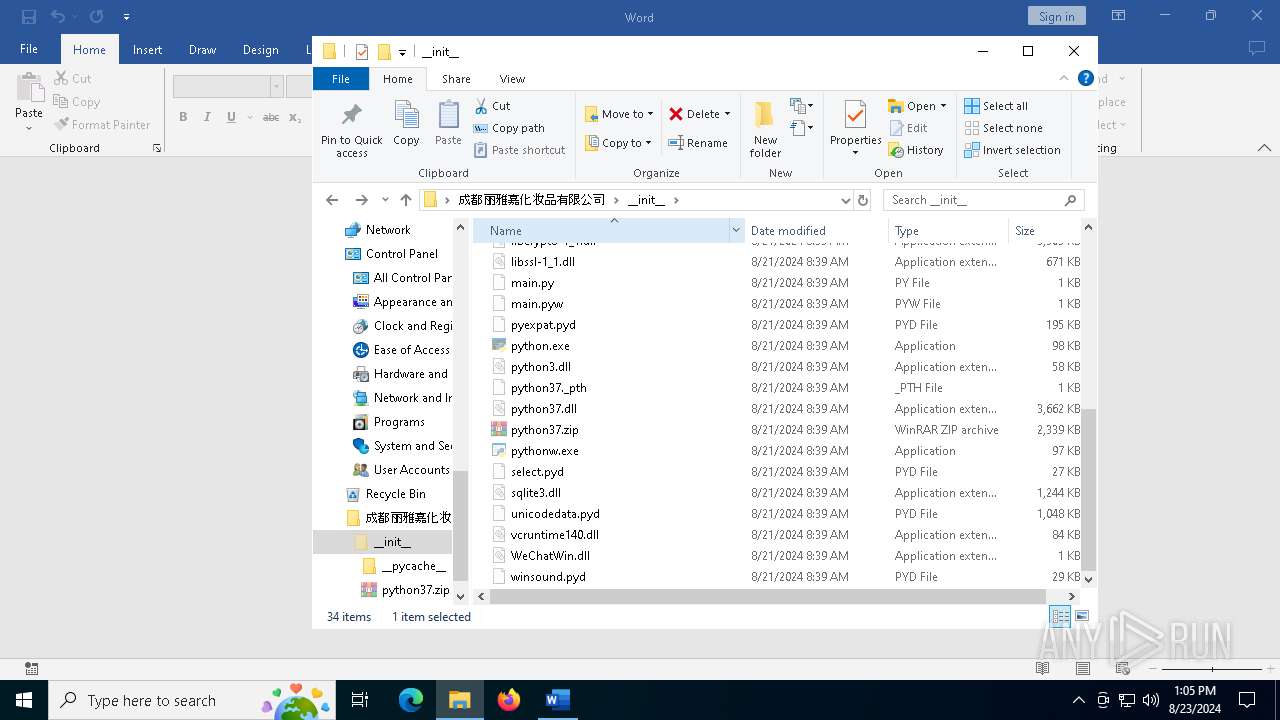
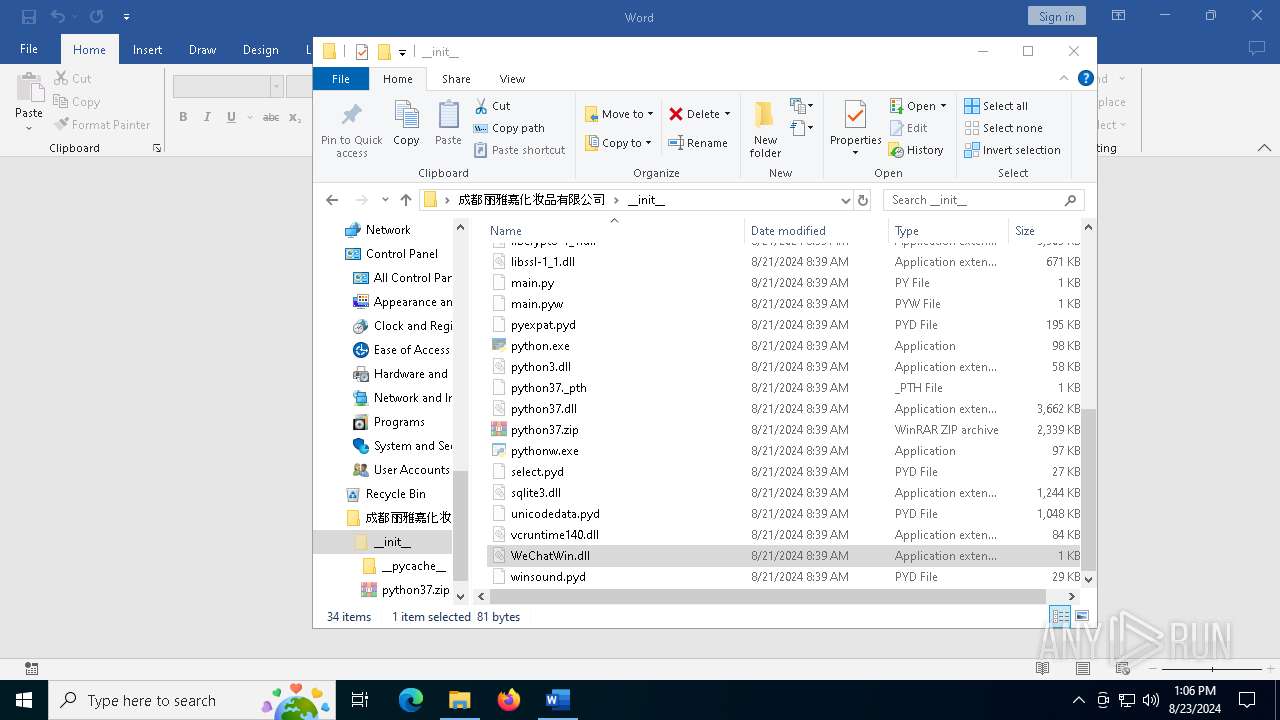
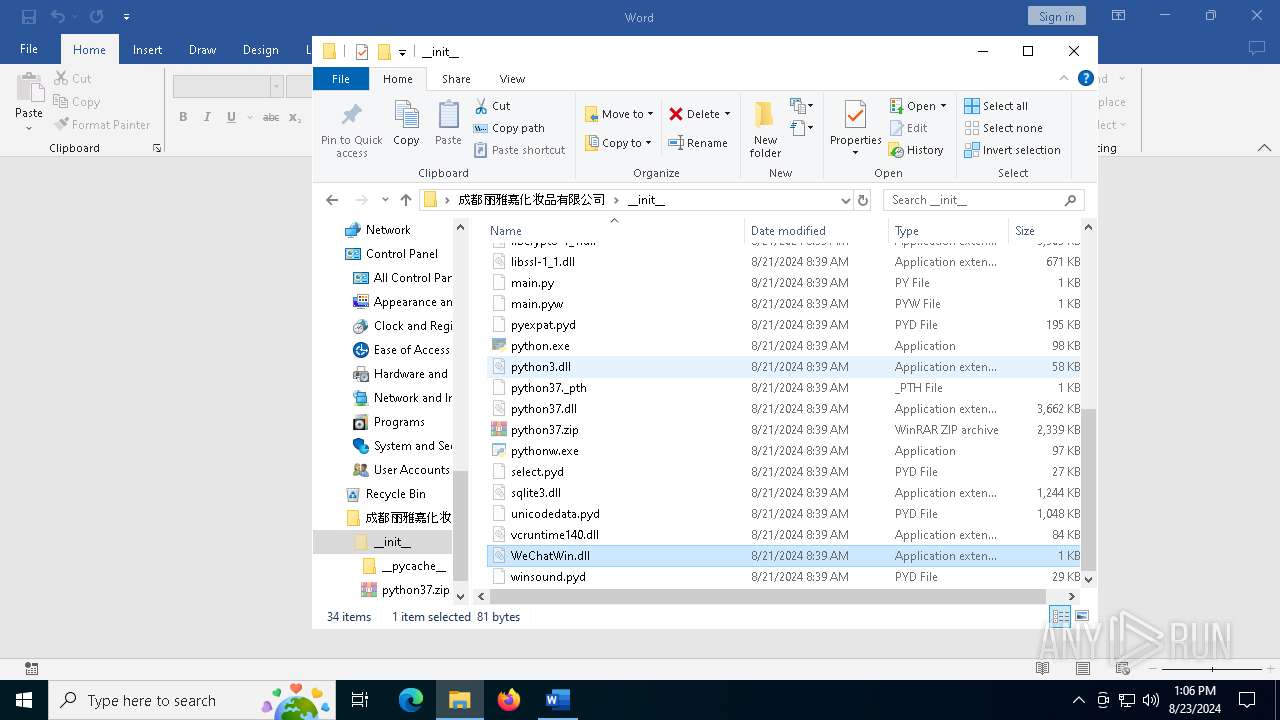
Process drops python dynamic module
- WinRAR.exe (PID: 7132)
Starts CMD.EXE for commands execution
- ftp.exe (PID: 6640)
- ftp.exe (PID: 752)
Executes an FTP script from a file
- ftp.exe (PID: 6640)
- ftp.exe (PID: 752)
Loads Python modules
- pythonw.exe (PID: 6316)
- pythonw.exe (PID: 6936)
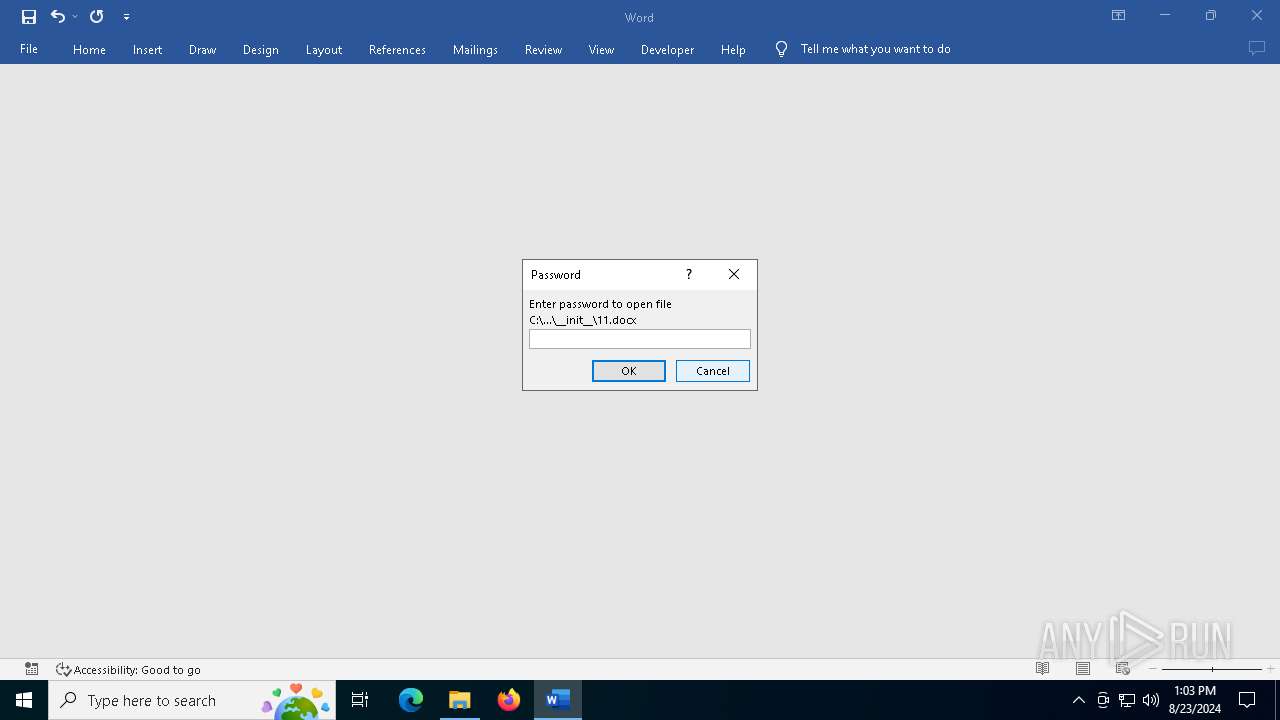
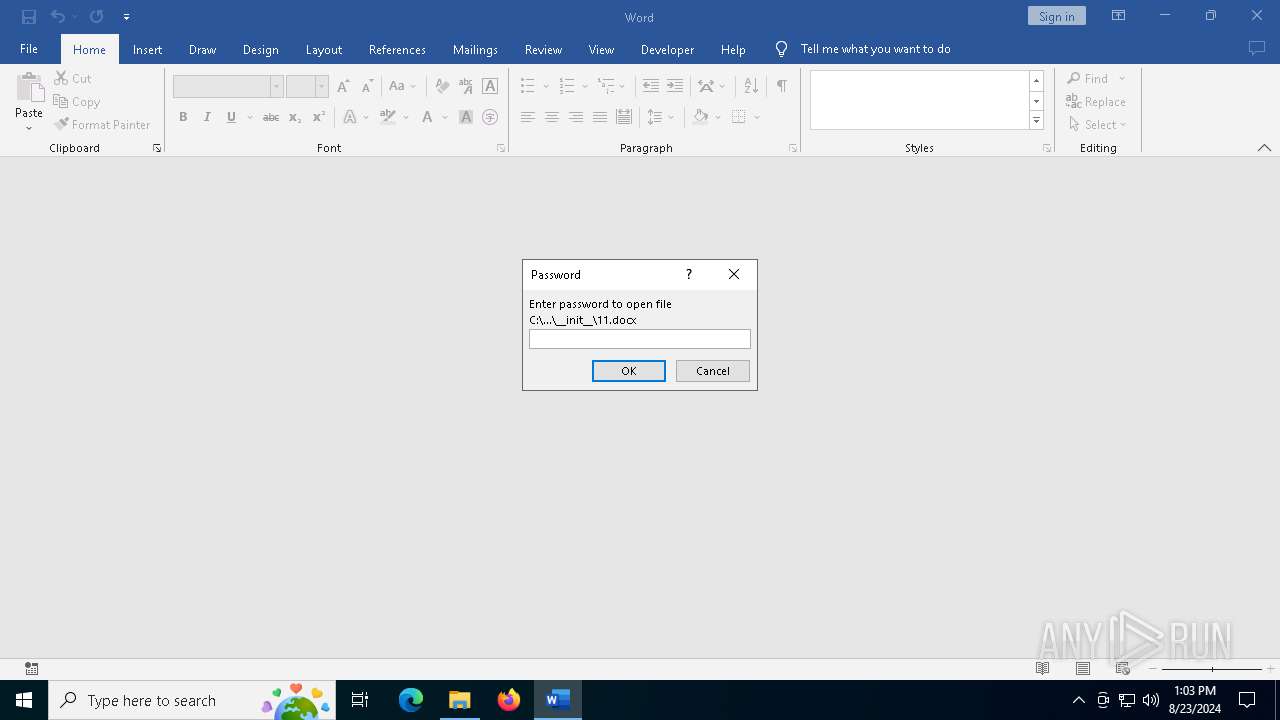
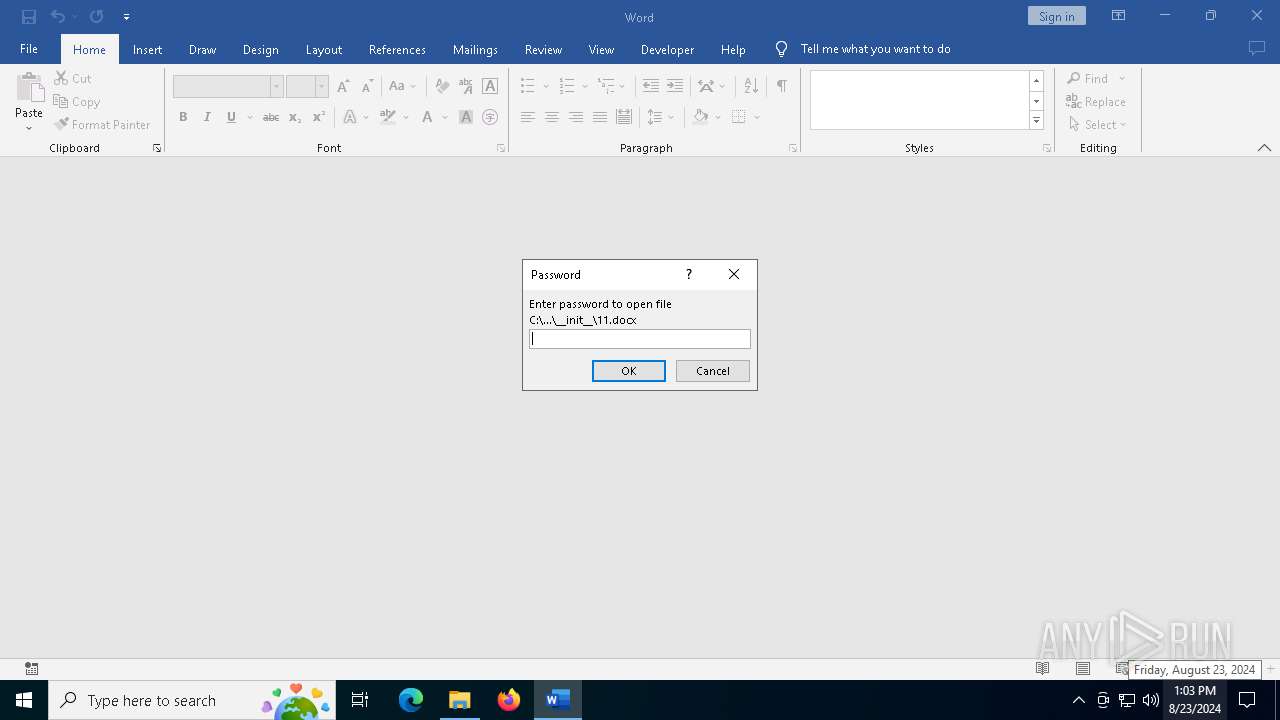
Suspicious WINWORD start
- WINWORD.EXE (PID: 6368)
- WINWORD.EXE (PID: 4708)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7132)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7132)
Reads the machine GUID from the registry
- pythonw.exe (PID: 6316)
- pythonw.exe (PID: 6936)
Manual execution by a user
- ftp.exe (PID: 6640)
- ftp.exe (PID: 752)
- notepad++.exe (PID: 2024)
Checks supported languages
- pythonw.exe (PID: 6316)
- pythonw.exe (PID: 6936)
Checks proxy server information
- pythonw.exe (PID: 6316)
- pythonw.exe (PID: 6936)
Reads the computer name
- pythonw.exe (PID: 6316)
- pythonw.exe (PID: 6936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
137
Monitored processes
16
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
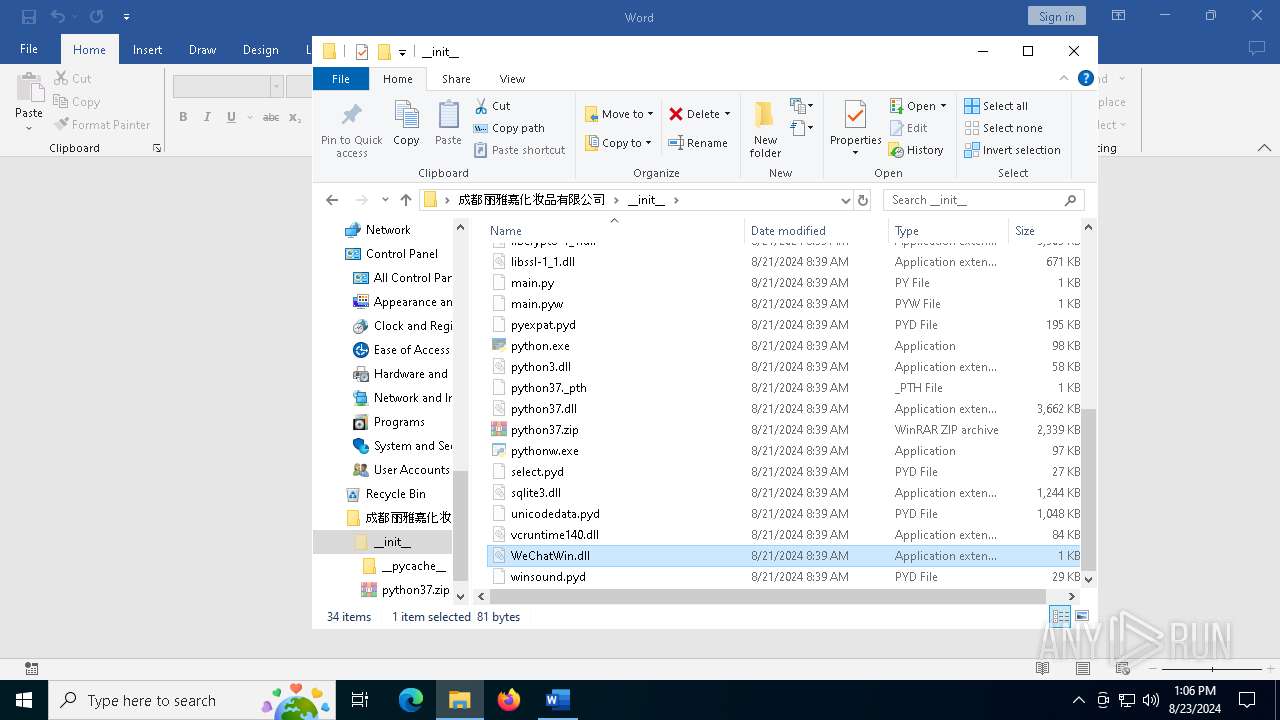
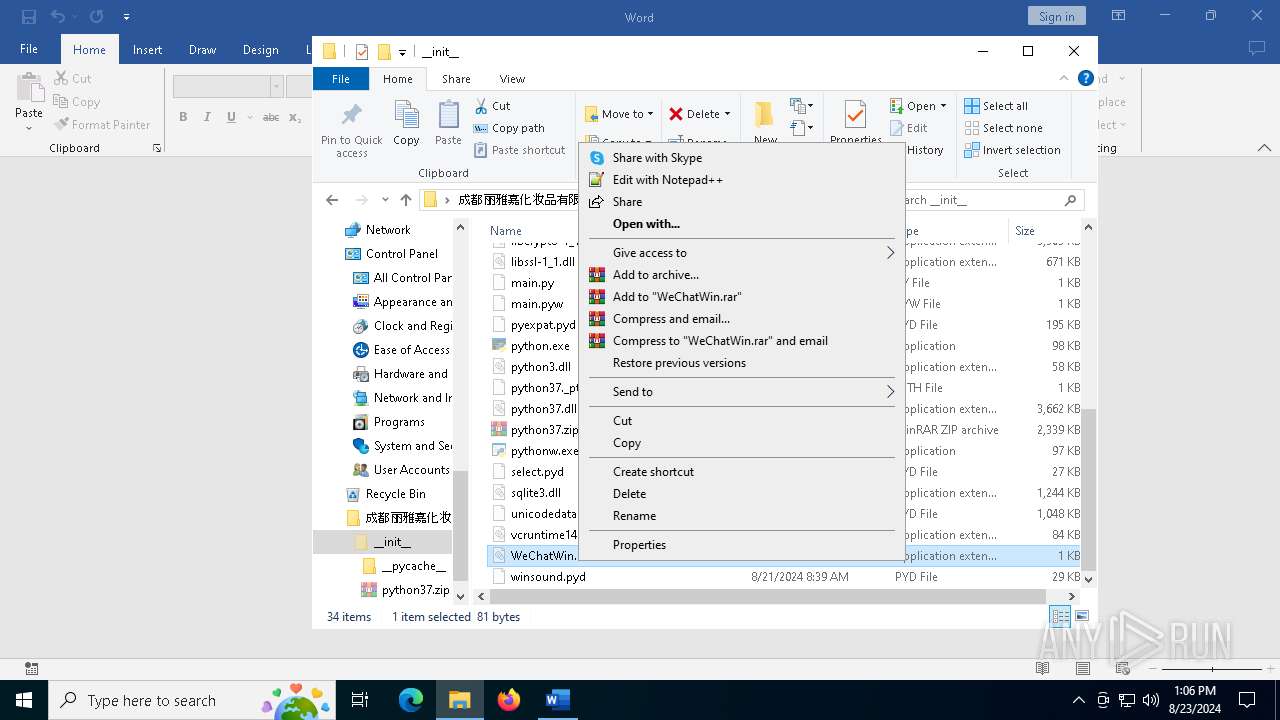
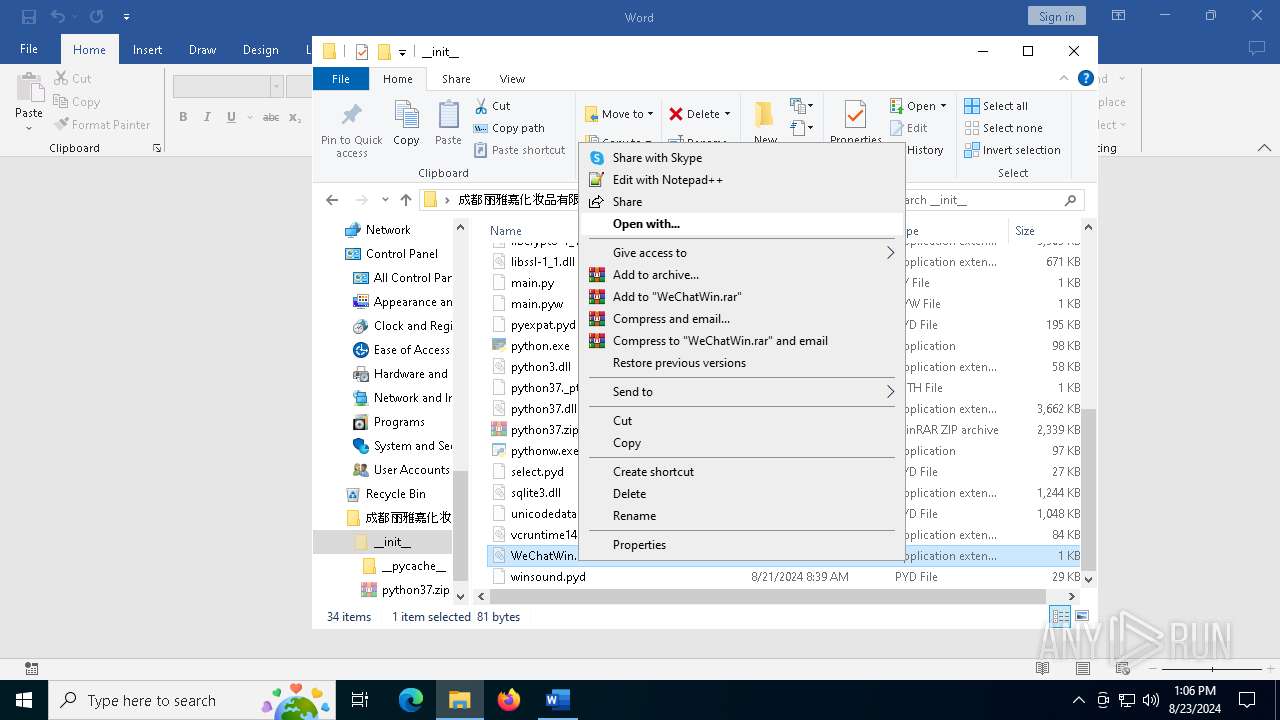
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
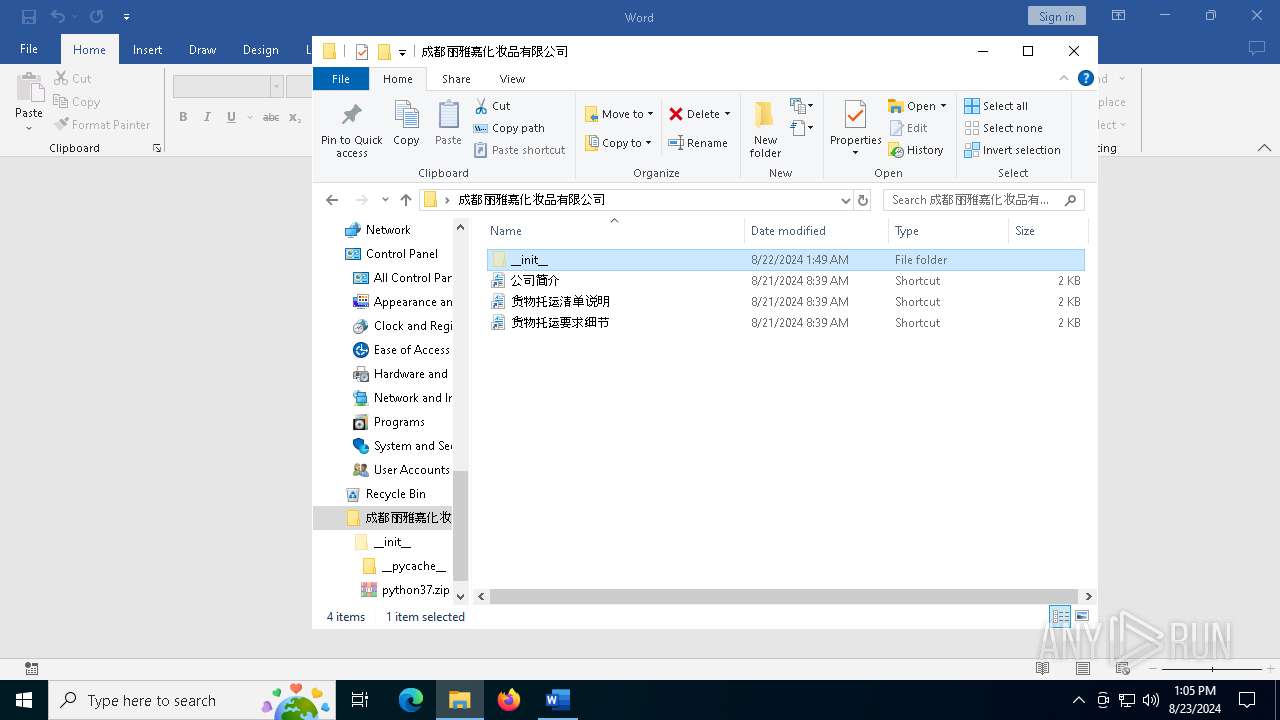
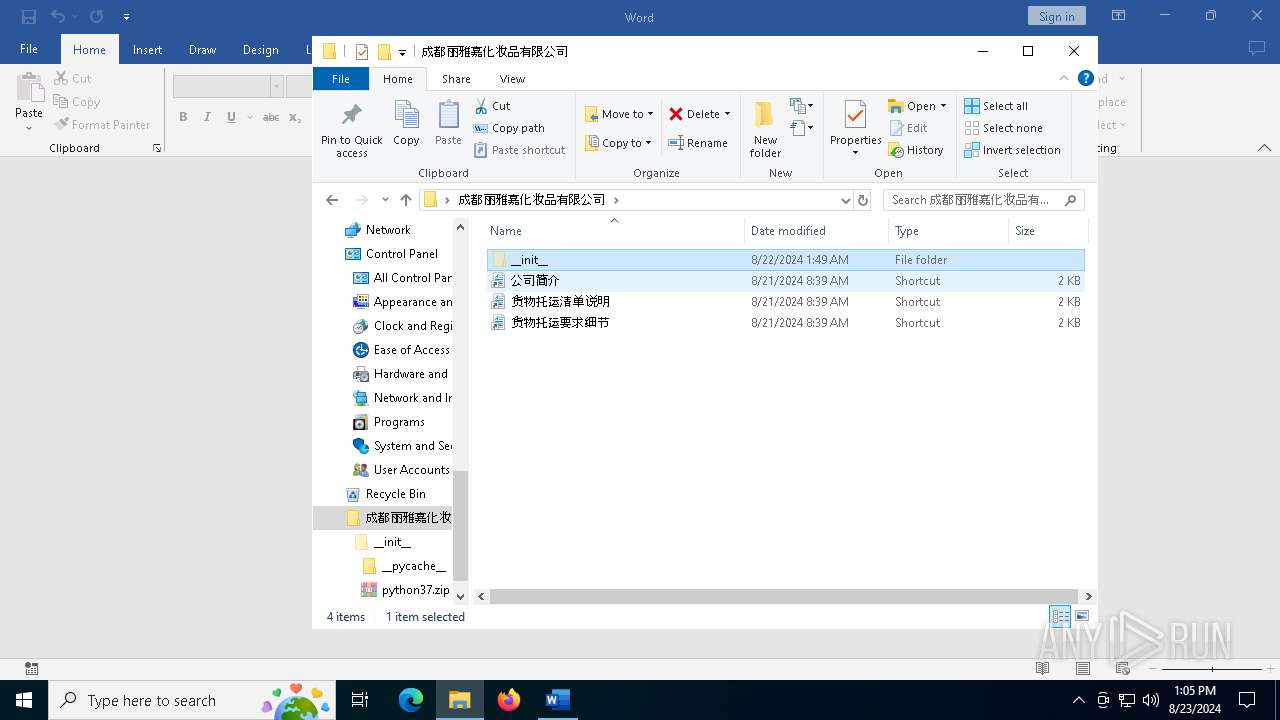
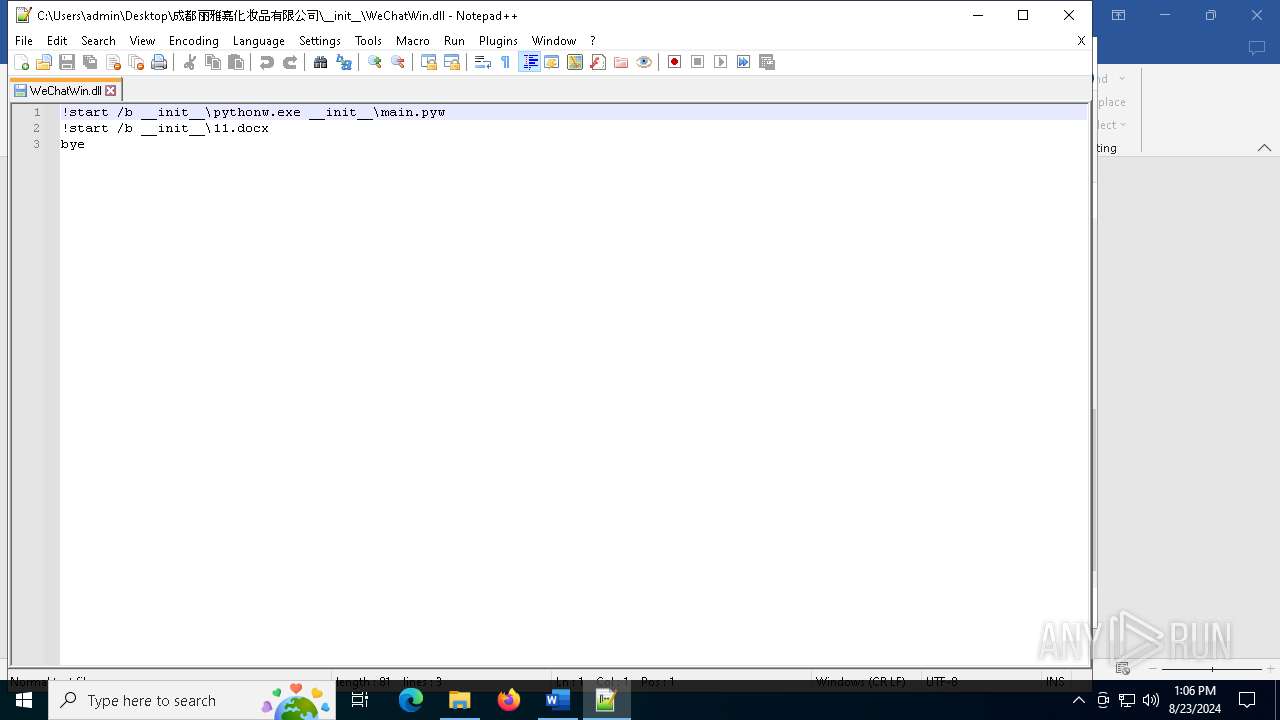
| 752 | "C:\Windows\System32\ftp.exe" -""s:__init__\WeChatWin.dll | C:\Windows\System32\ftp.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Transfer Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ftp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2024 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\WeChatWin.dll" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
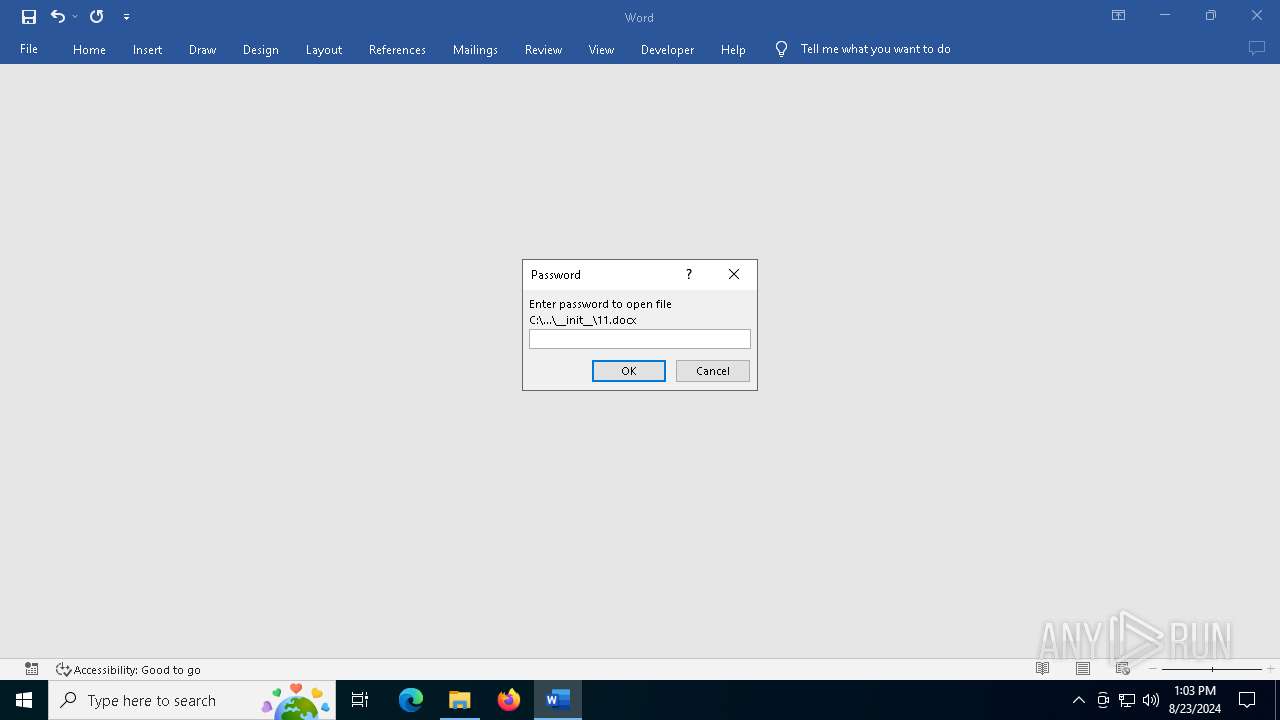
| 3844 | C:\WINDOWS\system32\cmd.exe /C start /b __init__\11.docx | C:\Windows\System32\cmd.exe | — | ftp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4132 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "5DFCD35D-A02C-454B-94E2-A75AFA8FDDA9" "4F154B49-140D-4A6C-A1F0-614E5DFD9487" "6368" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 4708 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\11.docx" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 5740 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ftp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6240 | C:\WINDOWS\system32\cmd.exe /C start /b __init__\11.docx | C:\Windows\System32\cmd.exe | — | ftp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6260 | C:\WINDOWS\system32\cmd.exe /C start /b __init__\pythonw.exe __init__\main.pyw | C:\Windows\System32\cmd.exe | — | ftp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 523
Read events
22 284
Write events
199
Delete events
40
Modification events
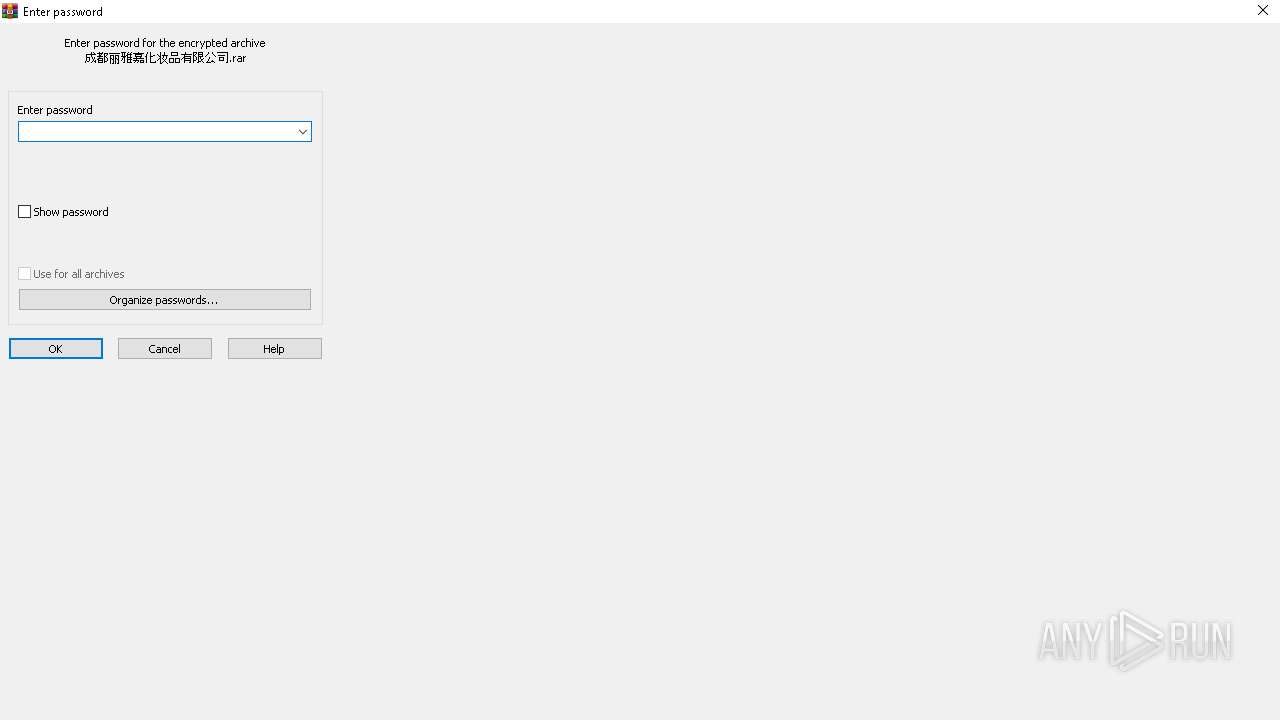
| (PID) Process: | (7132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
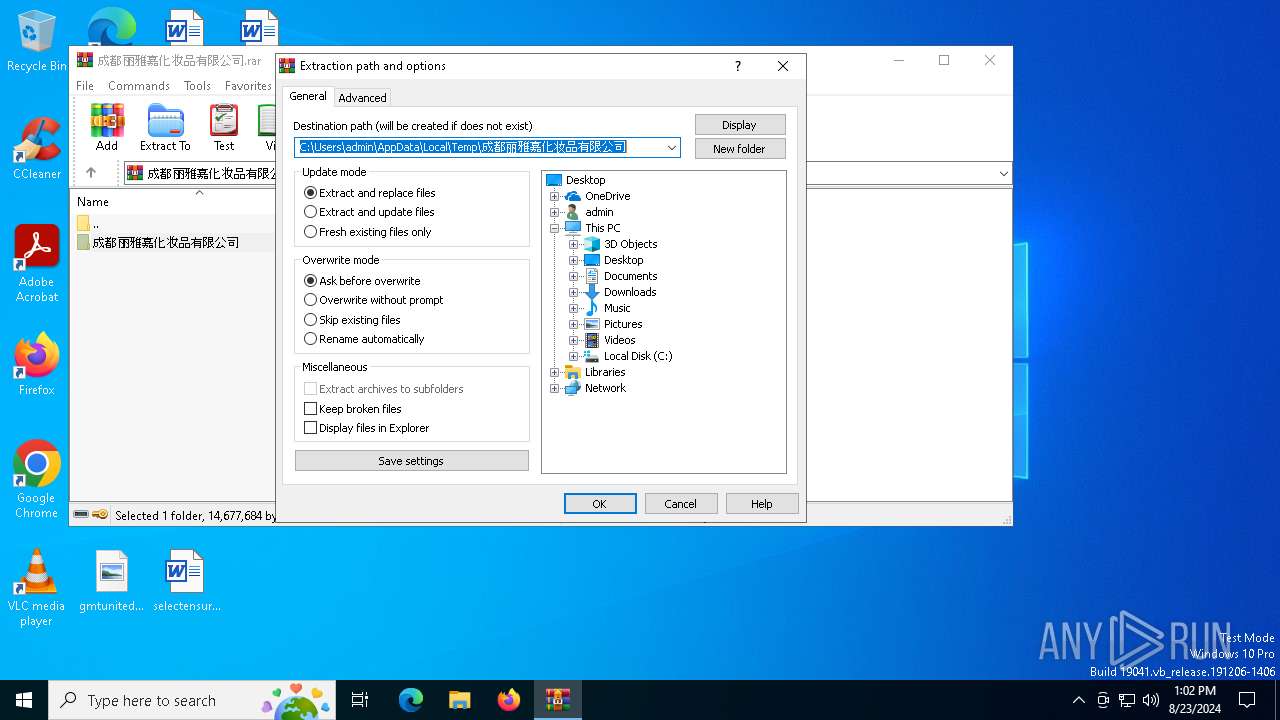
| (PID) Process: | (7132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (7132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\成都丽雅嘉化妆品有限公司.rar | |||
| (PID) Process: | (7132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
26
Suspicious files
12
Text files
12
Unknown types
0
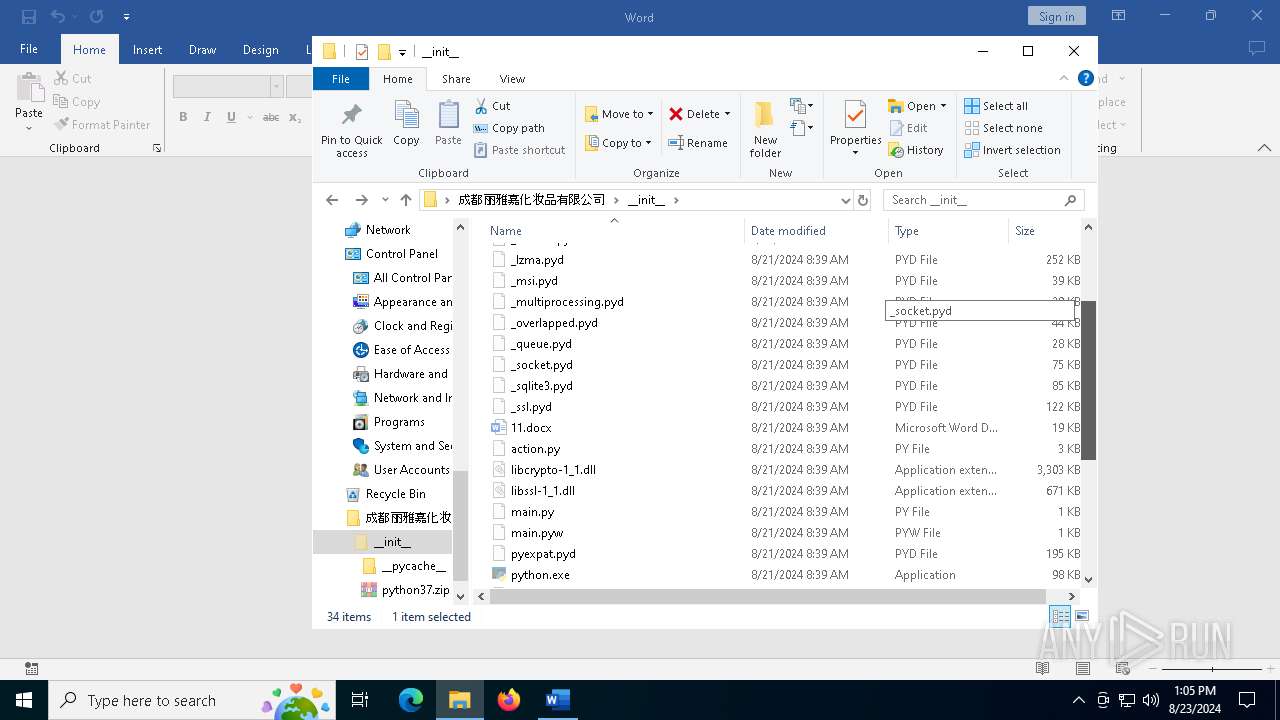
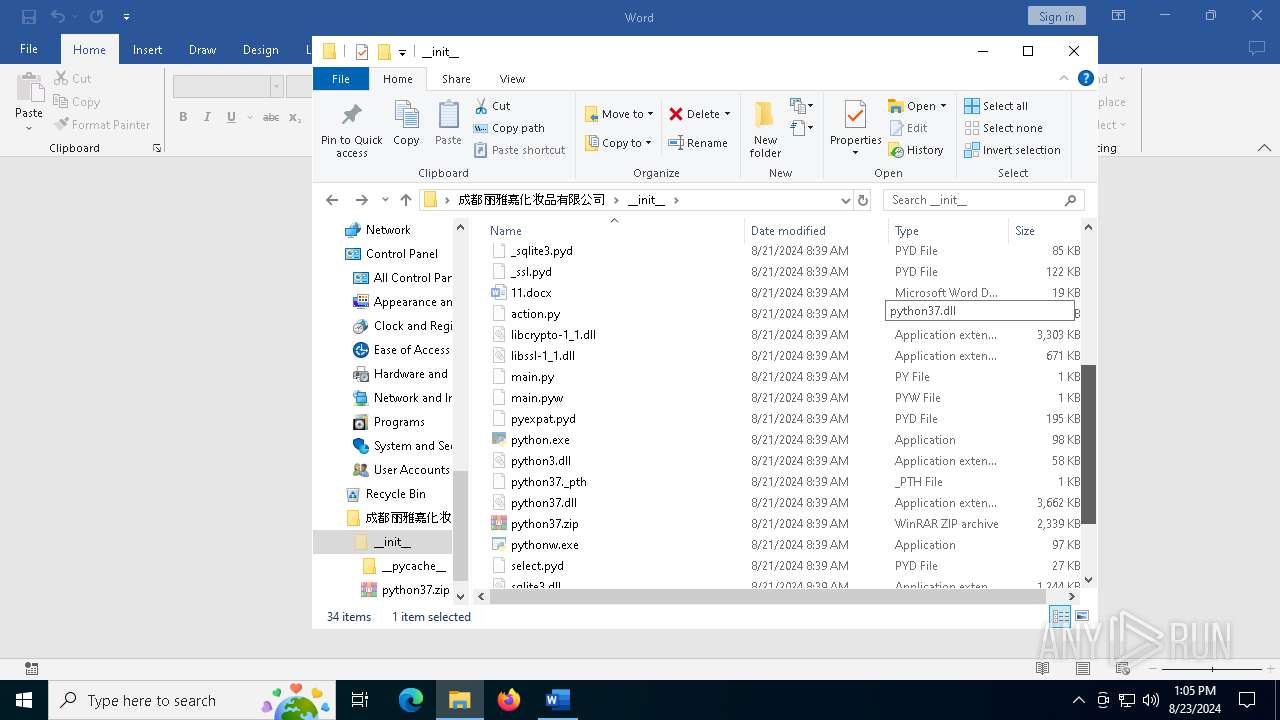
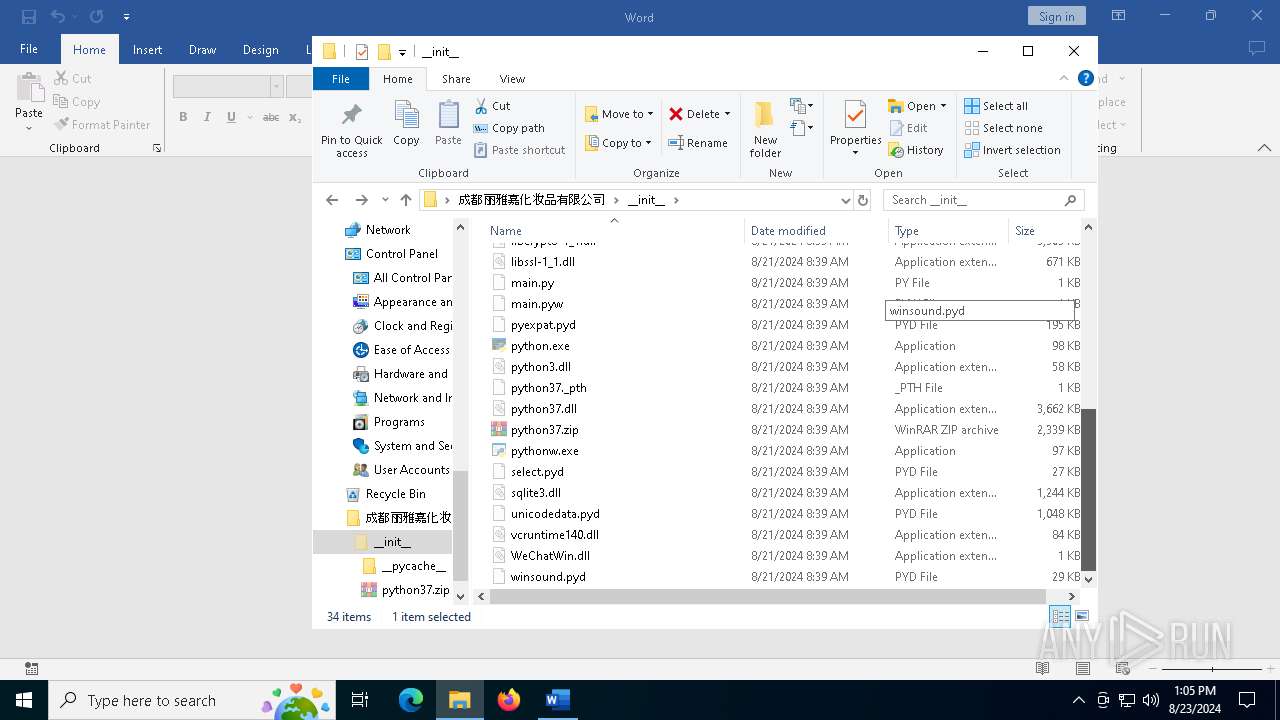
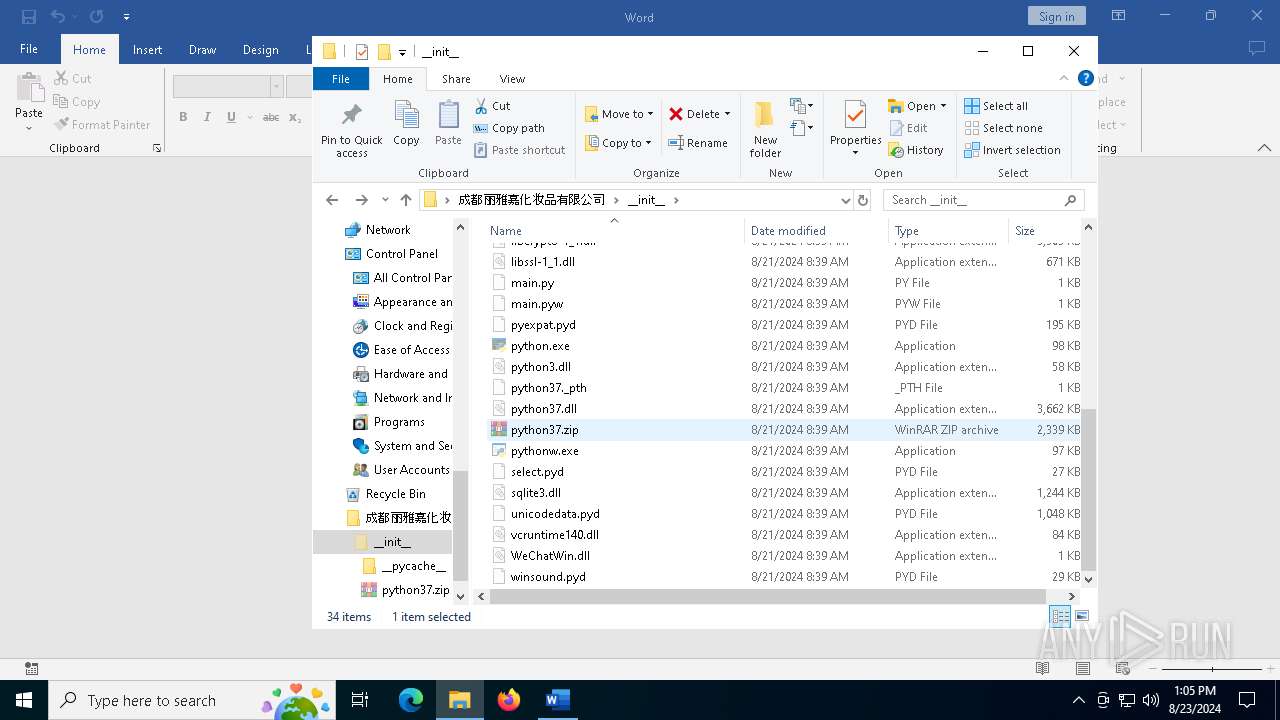
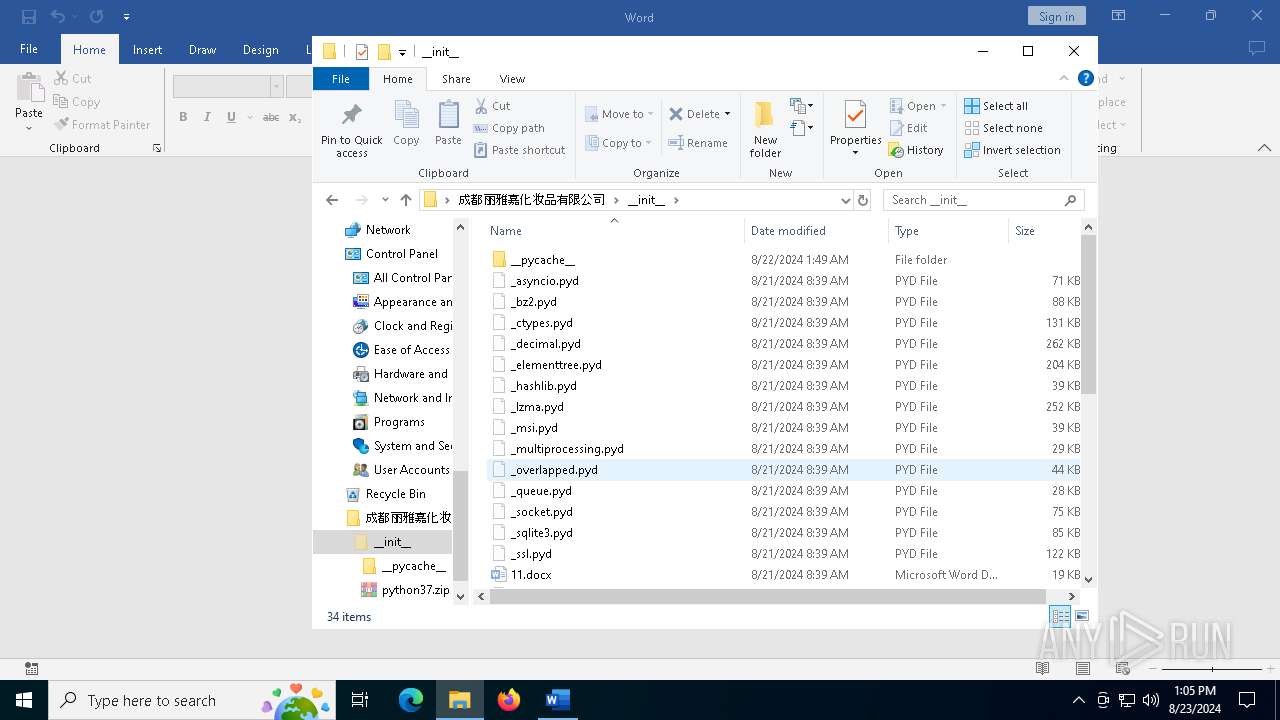
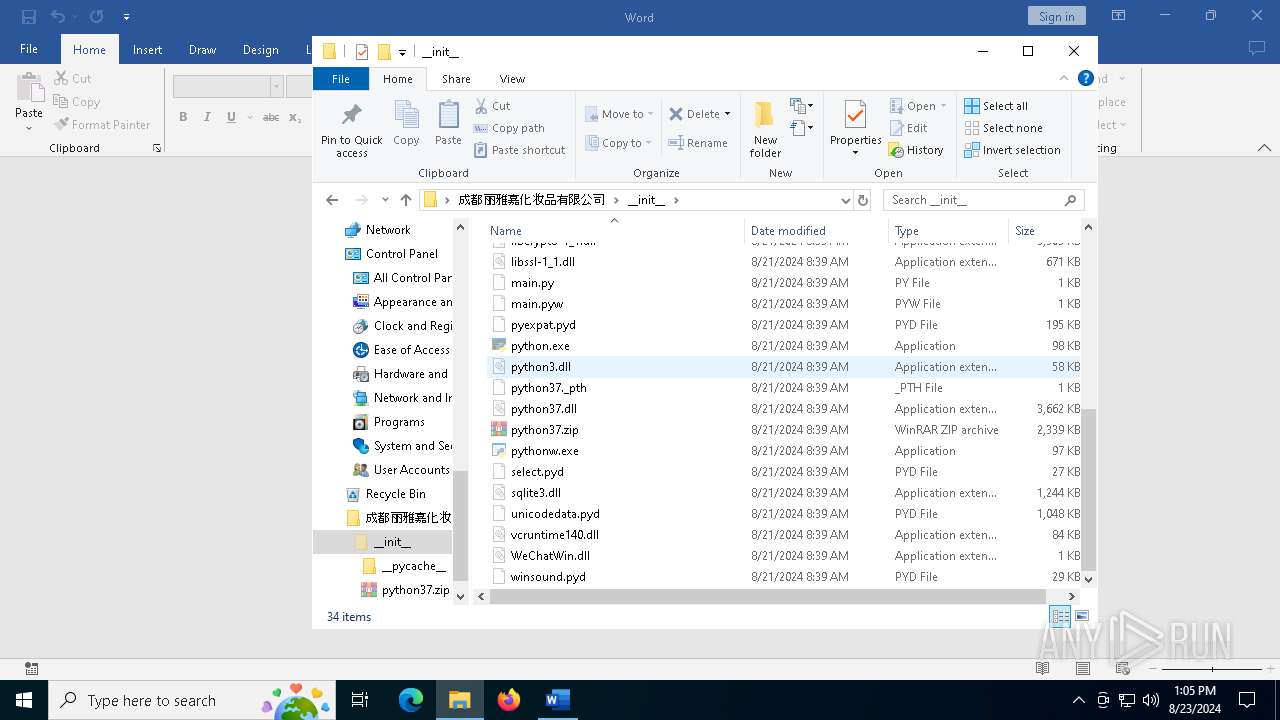
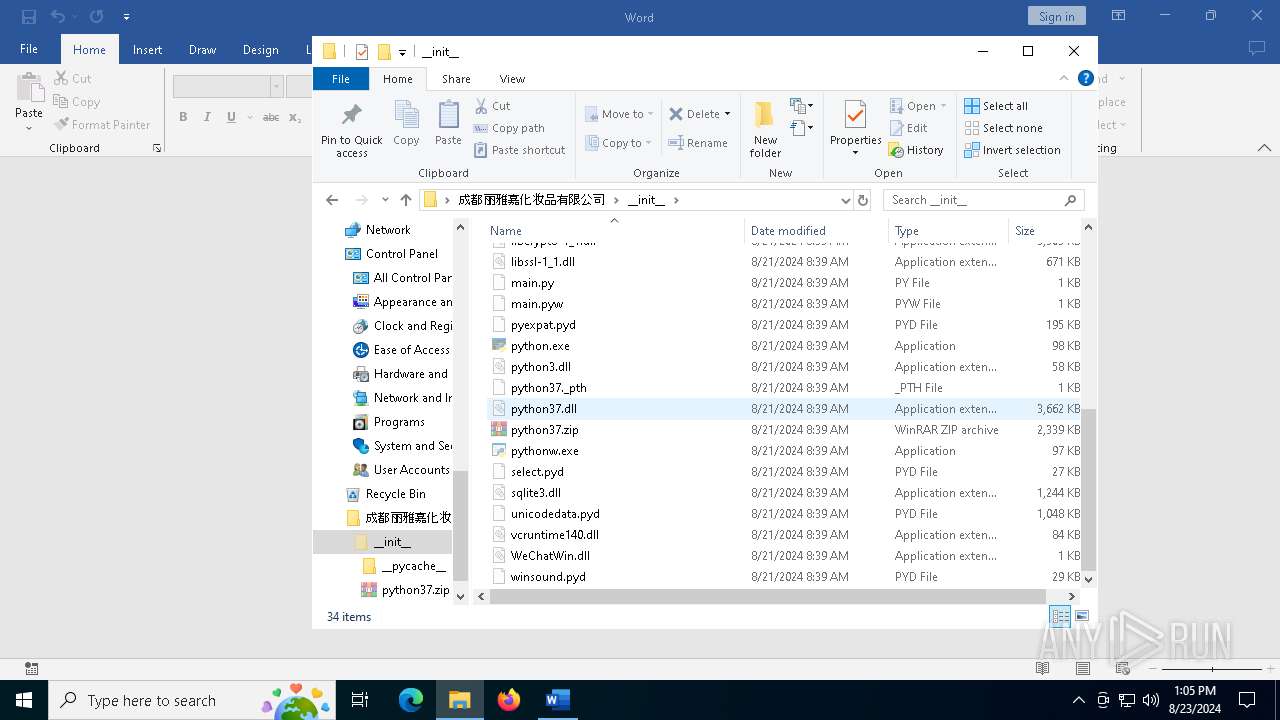
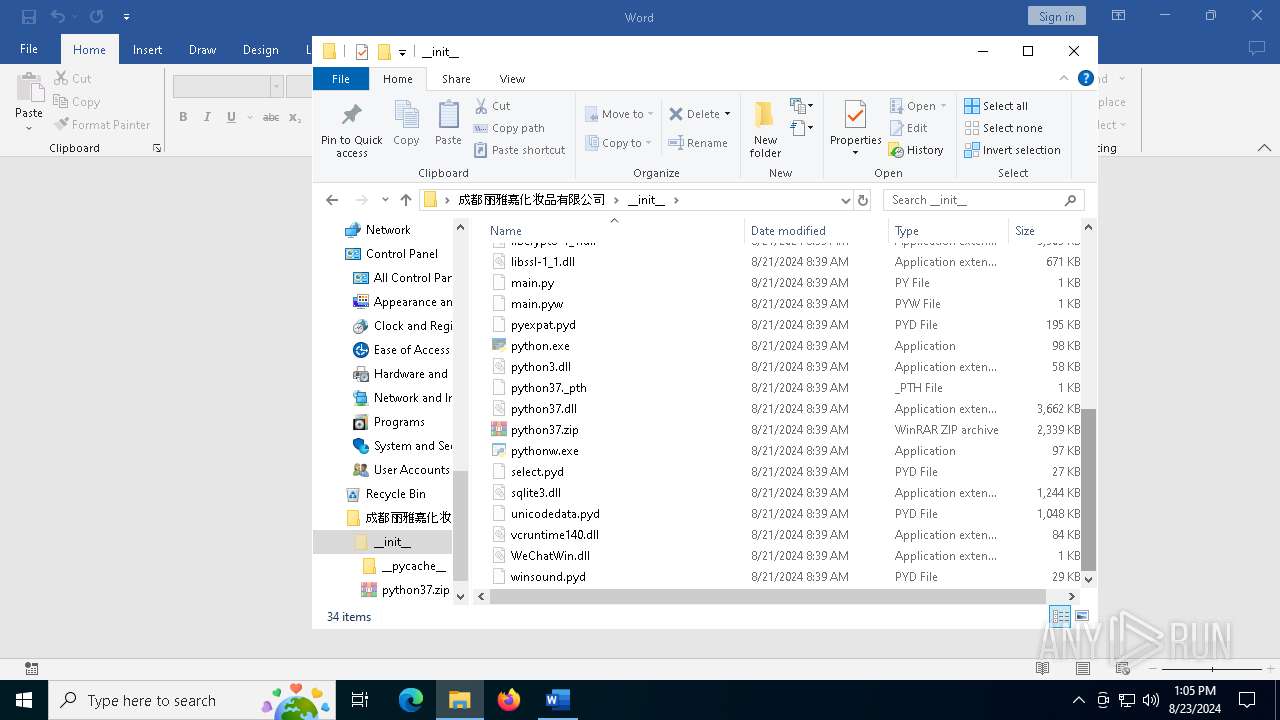
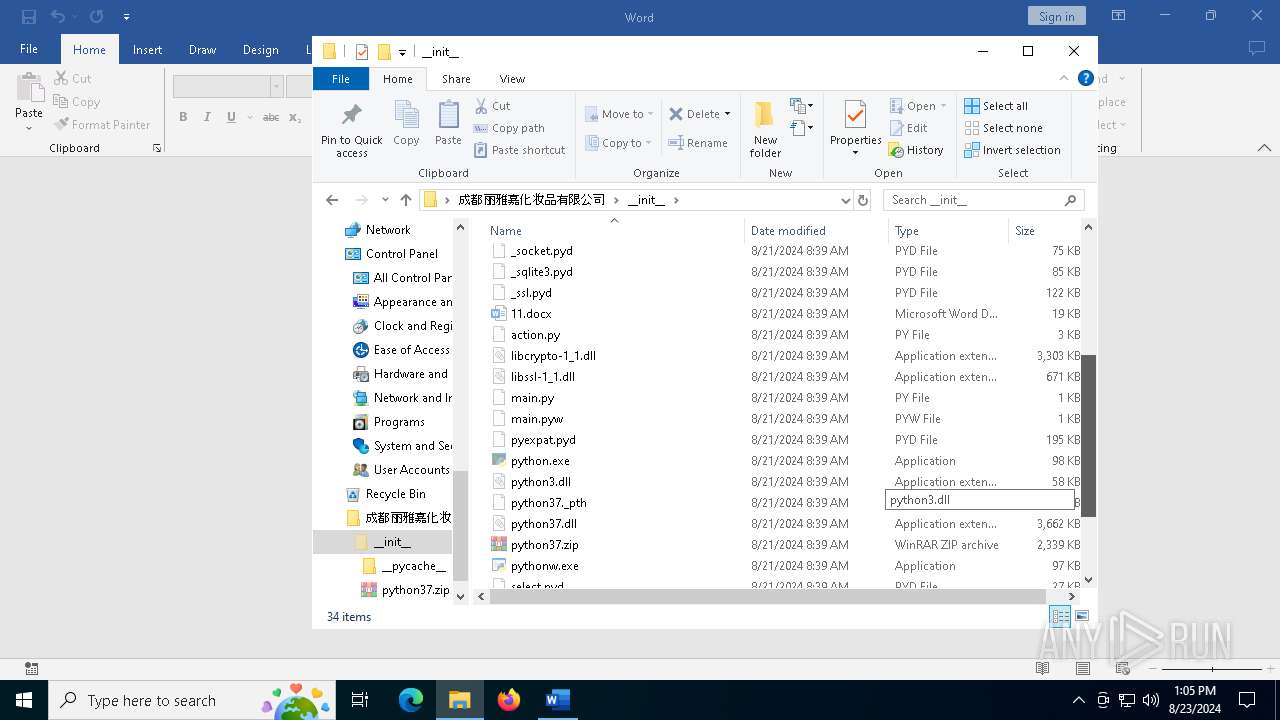
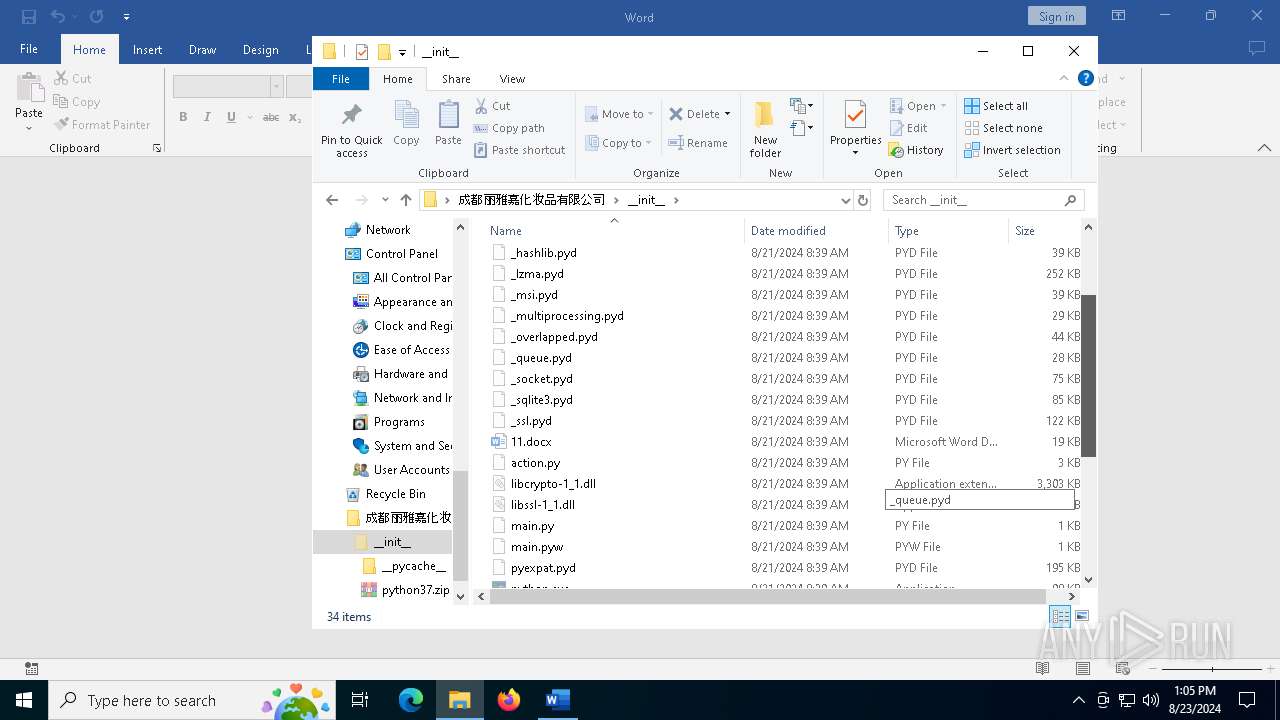
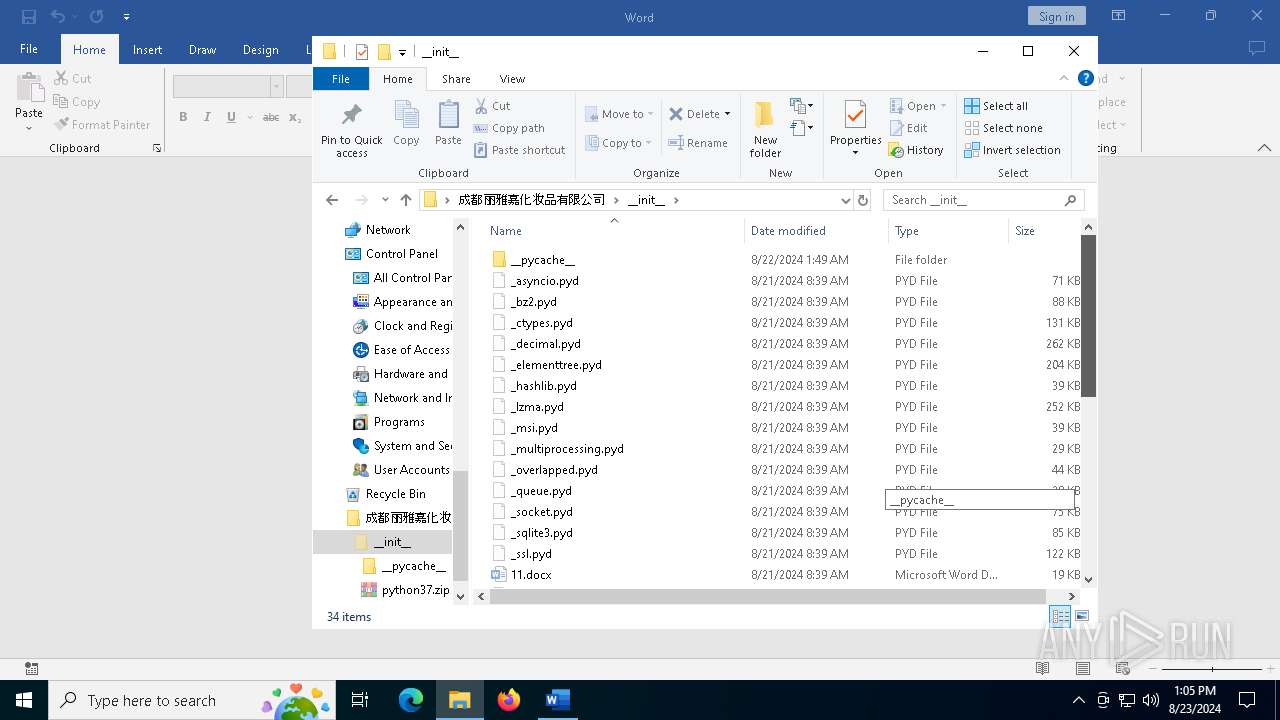
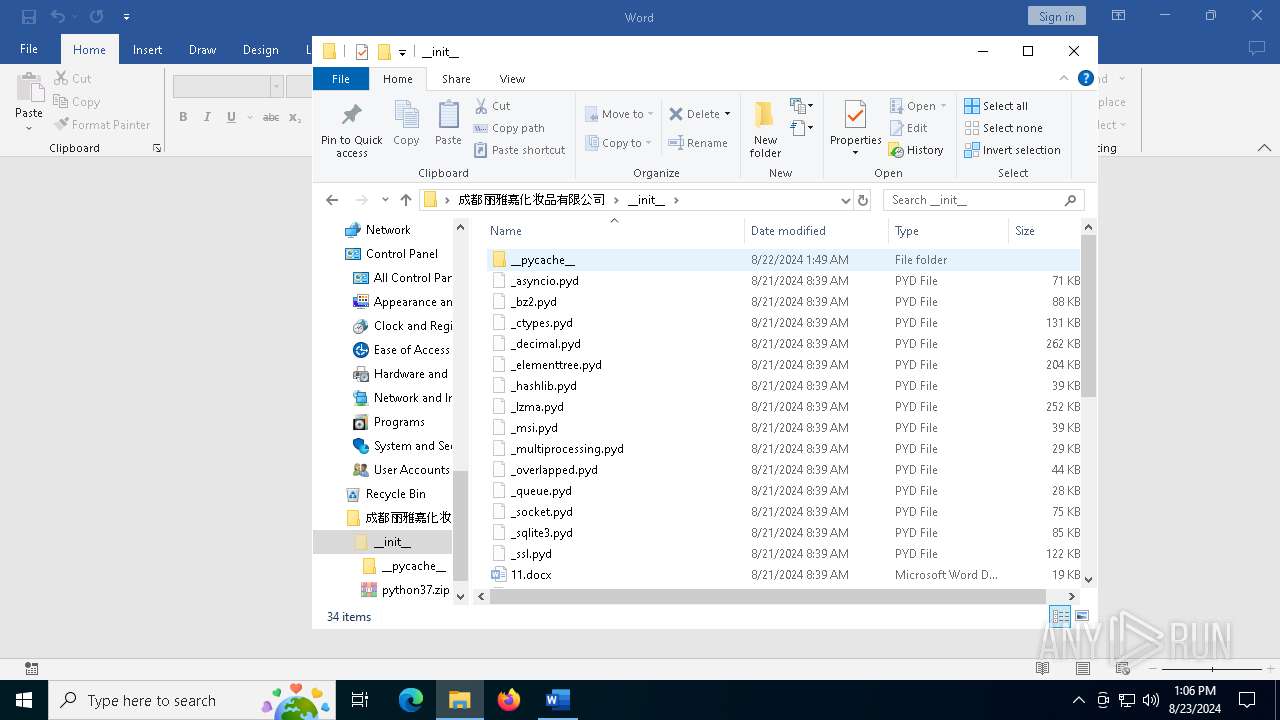
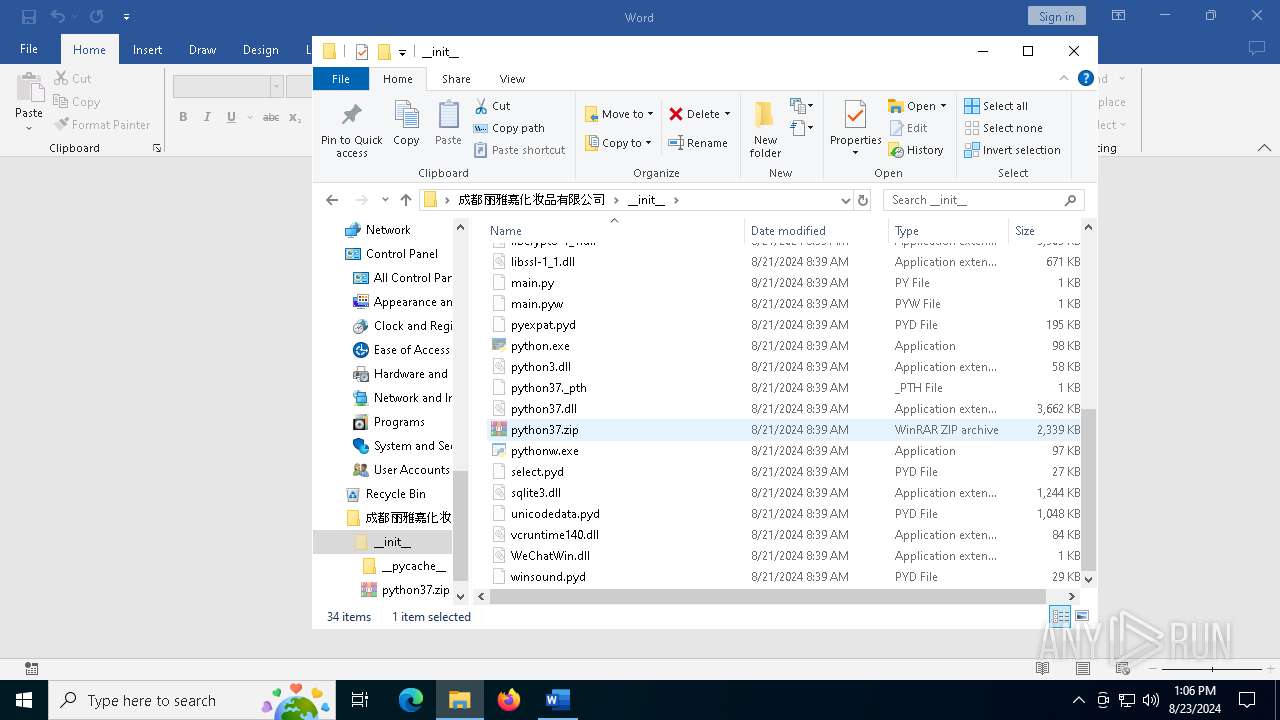
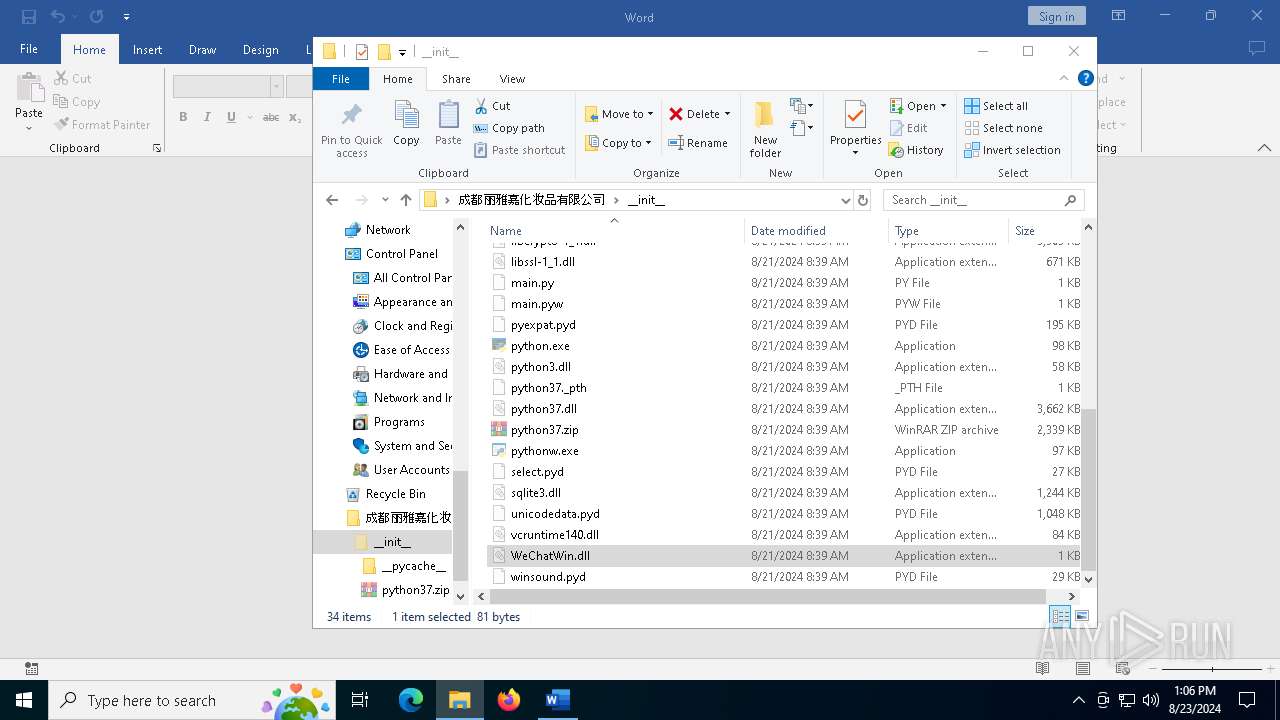
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
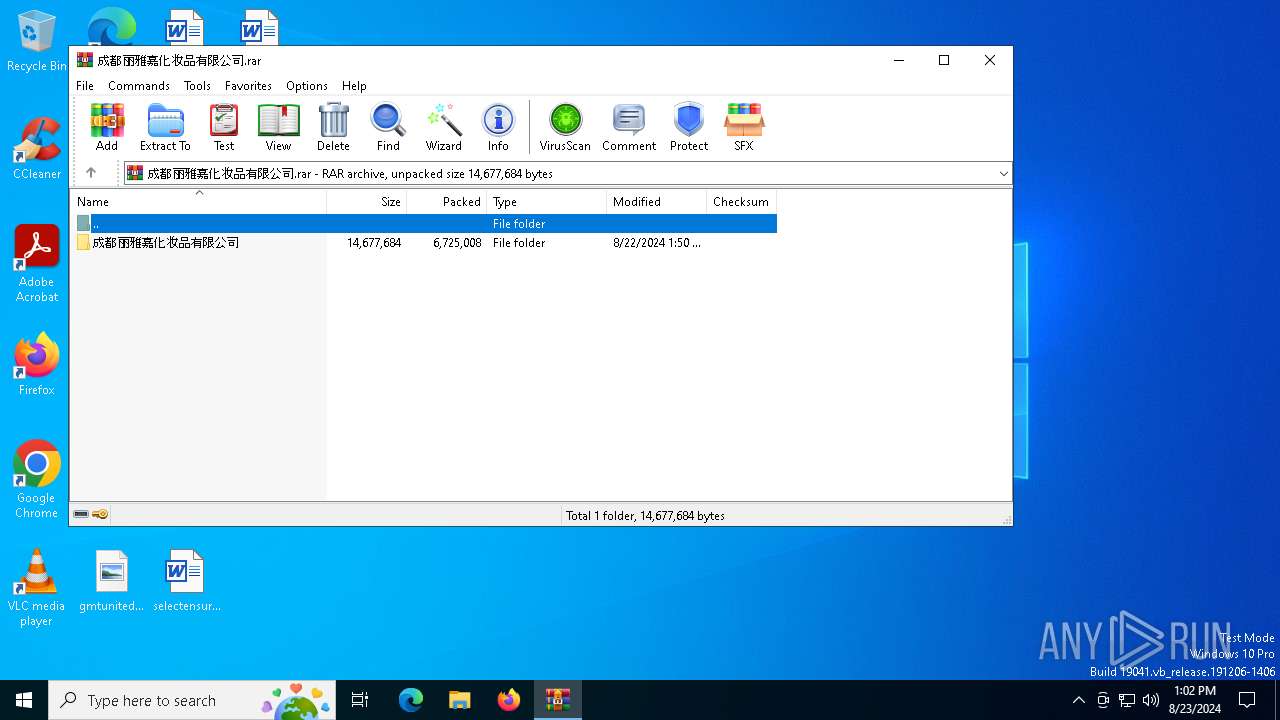
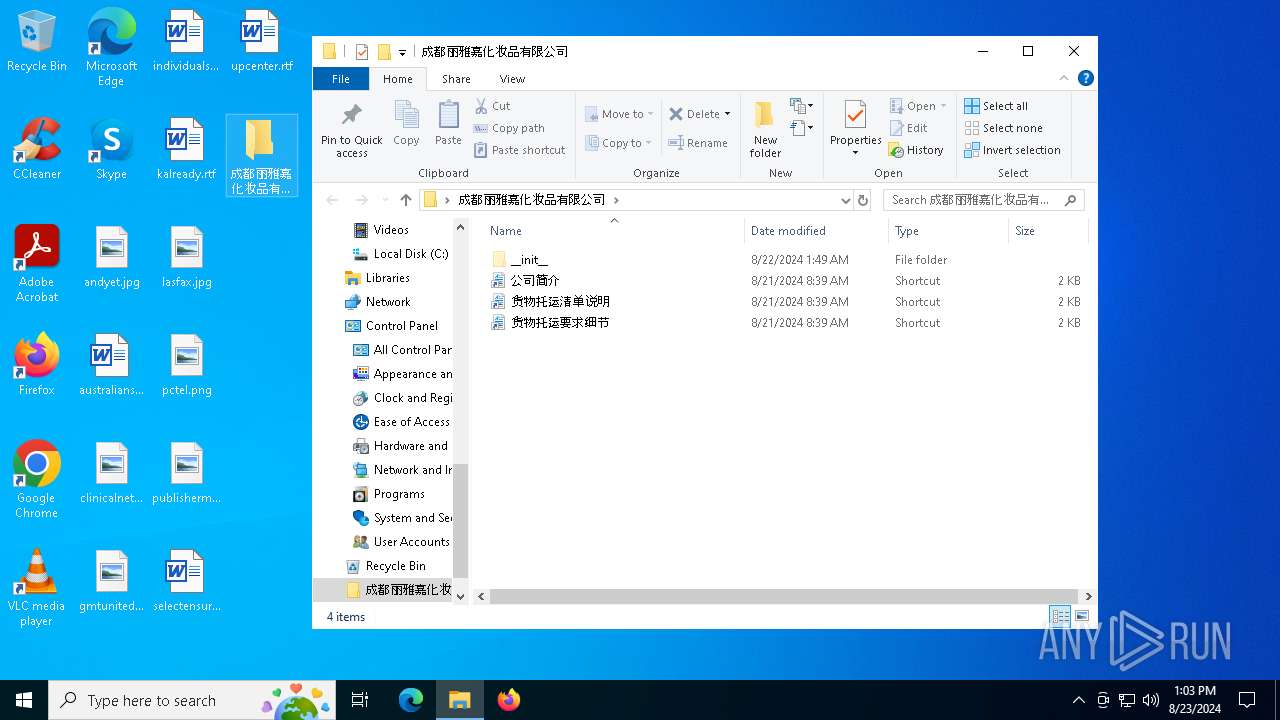
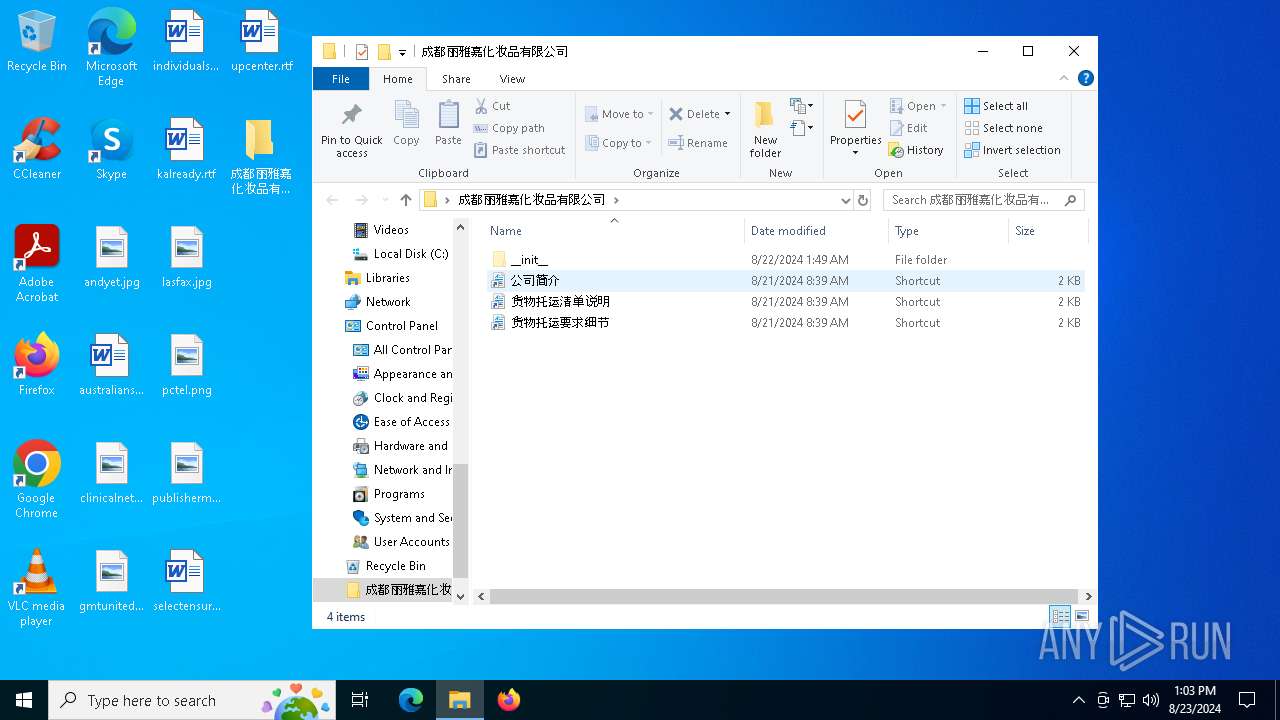
| 7132 | WinRAR.exe | C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\python.exe | executable | |
MD5:F30BD5457F7712CF98DEF1B1BBE60443 | SHA256:8442582AF22F767E491E01F539115F9D8FBAB6E86121C743FBCFAFEA70CFB681 | |||
| 7132 | WinRAR.exe | C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\action.py | text | |
MD5:2ED92EC59C4636E9E444FF7282838186 | SHA256:C80AB5F755B2E866E014A2A21F075B312360A311D0E8821EB60907592C88E04E | |||
| 7132 | WinRAR.exe | C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\pyexpat.pyd | executable | |
MD5:33B1AB9A8D925F41F409233499BBBAF7 | SHA256:946F8E40FD4A8AF4F2758AB599703D8659FFB049F7F631B9C8CA95625F1F7785 | |||
| 7132 | WinRAR.exe | C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\python3.dll | executable | |
MD5:D86BB6AC638B6D964435ABDF63D20A92 | SHA256:7ACFDB2A6338B8758E17F1F8D705C286ABC60554527A18E2954B5EB5C2EFBA72 | |||
| 7132 | WinRAR.exe | C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\main.py | text | |
MD5:3DDA327D22AFC76A74B1EF93C553596B | SHA256:318166BD6F42CD542DD9FD5357A2C767CA695A8BBF944BA3851B1D1D95D6B3ED | |||
| 7132 | WinRAR.exe | C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\python37.dll | executable | |
MD5:C863D0071DE96CE5F4753CFF419AE9E8 | SHA256:A760E7CCB856F7A5F6484C2B6B042344F5C55CB77BA778FF7682324E7851C628 | |||
| 7132 | WinRAR.exe | C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\libssl-1_1.dll | executable | |
MD5:FE1F3632AF98E7B7A2799E3973BA03CF | SHA256:1CE7BA99E817C1C2D71BC88A1BDD6FCAD82AA5C3E519B91EBD56C96F22E3543B | |||
| 7132 | WinRAR.exe | C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\11.docx | binary | |
MD5:B93AAA92DFEE1E8C7083AE7EBF3E69BA | SHA256:EE336B4F788842D2E7F922D64D8CF5E36A35C8B3BF053FD5542493E8F15AFCCC | |||
| 7132 | WinRAR.exe | C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\sqlite3.dll | executable | |
MD5:07984F7FD0567F810FF69D09FDE2F3E9 | SHA256:E9DF541FB8263E5FBE88860E051789EA5A4FC2A7E4820E128019A8A35B625E92 | |||
| 7132 | WinRAR.exe | C:\Users\admin\Desktop\成都丽雅嘉化妆品有限公司\__init__\_asyncio.pyd | executable | |
MD5:1E91EEDFAA8F43E106DB442596FE4B6A | SHA256:B27D96CF29C0D38AC26E81462D6EE8DF87771FFFA2FFACD66583F673DDBCE1D2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
37
DNS requests
17
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3304 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3304 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6316 | pythonw.exe | 39.104.9.76:443 | wvpibcb5y8c773.oss-cn-huhehaote.aliyuncs.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
6368 | WINWORD.EXE | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
6368 | WINWORD.EXE | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6368 | WINWORD.EXE | 23.48.23.62:443 | omex.cdn.office.net | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
wvpibcb5y8c773.oss-cn-huhehaote.aliyuncs.com |
| unknown |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
metadata.templates.cdn.office.net |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6316 | pythonw.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
2256 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6936 | pythonw.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|