| File name: | 5ze7vs_tgt6e3k-5 |
| Full analysis: | https://app.any.run/tasks/160d8836-cbf2-49f7-990c-c3ae9ad2aeeb |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 21:27:48 |
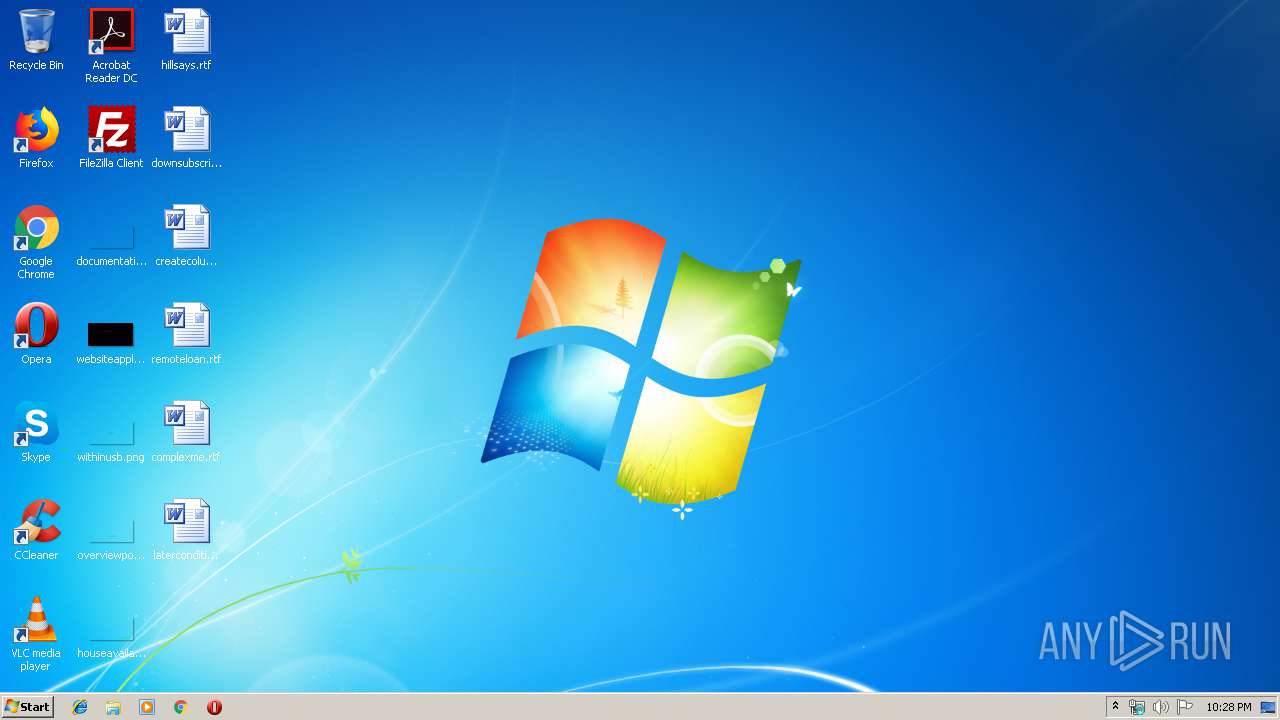
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 9725D9368E642E74586456BBAD9F37B5 |
| SHA1: | 917323050EB10993D13039E5F0A32F5FF97684C1 |
| SHA256: | 8274749A1F4910E88944BC47D74AA0760CF6EB24712FCAFBC0D744047A9839E9 |
| SSDEEP: | 1536:9cIywQo98sJoWA+fYlbrsKEj05c9W0u/irsBM3PfO5iuNUW:9cs8sCgmrzEvwZesBePfMXUW |
MALICIOUS
EMOTET was detected
- soundser.exe (PID: 3516)
Emotet process was detected
- soundser.exe (PID: 2916)
Connects to CnC server
- soundser.exe (PID: 3516)
SUSPICIOUS
Starts itself from another location
- 5ze7vs_tgt6e3k-5.exe (PID: 3648)
Executable content was dropped or overwritten
- 5ze7vs_tgt6e3k-5.exe (PID: 3648)
Connects to server without host name
- soundser.exe (PID: 3516)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
| .vxd | | | VXD Driver (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:11:12 12:08:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 4608 |
| InitializedDataSize: | 70656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1769 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Nov-2015 11:08:00 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 12-Nov-2015 11:08:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000011EA | 0x00001200 | IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.37562 |
.data | 0x00003000 | 0x000113F0 | 0x00011400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9082 |
Imports
advapi32.dll |
authz.dll |
cryptdll.dll |
kernel32.dll |
shlwapi.dll |
Total processes
37
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2916 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 5ze7vs_tgt6e3k-5.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3060 | "C:\Users\admin\AppData\Local\Temp\5ze7vs_tgt6e3k-5.exe" | C:\Users\admin\AppData\Local\Temp\5ze7vs_tgt6e3k-5.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3516 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3648 | --23b82f89 | C:\Users\admin\AppData\Local\Temp\5ze7vs_tgt6e3k-5.exe | 5ze7vs_tgt6e3k-5.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
118
Read events
104
Write events
14
Delete events
0
Modification events
| (PID) Process: | (3516) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3516) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3516) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3516) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3516) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3516) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3516) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3516) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3516) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3516) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3648 | 5ze7vs_tgt6e3k-5.exe | C:\Users\admin\AppData\Local\soundser\soundser.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
55
DNS requests
0
Threats
223
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3516 | soundser.exe | POST | — | 74.207.227.96:443 | http://74.207.227.96:443/acquire/ | US | — | — | malicious |
3516 | soundser.exe | POST | — | 98.142.208.27:443 | http://98.142.208.27:443/pnp/ | US | — | — | malicious |
3516 | soundser.exe | POST | — | 186.4.234.27:443 | http://186.4.234.27:443/site/ | EC | — | — | malicious |
3516 | soundser.exe | POST | — | 178.62.37.188:443 | http://178.62.37.188:443/arizona/ | GB | — | — | malicious |
3516 | soundser.exe | POST | 404 | 45.55.201.204:7080 | http://45.55.201.204:7080/odbc/enable/ringin/ | US | xml | 345 b | malicious |
3516 | soundser.exe | POST | 404 | 177.242.202.30:8080 | http://177.242.202.30:8080/jit/ | MX | xml | 345 b | malicious |
3516 | soundser.exe | POST | 404 | 189.154.42.168:80 | http://189.154.42.168/jit/ | MX | xml | 345 b | malicious |
3516 | soundser.exe | POST | 404 | 190.145.67.134:8090 | http://190.145.67.134:8090/arizona/ | CO | xml | 345 b | malicious |
3516 | soundser.exe | POST | 404 | 98.144.73.193:80 | http://98.144.73.193/jit/ | US | xml | 345 b | malicious |
3516 | soundser.exe | POST | 404 | 104.236.206.44:8080 | http://104.236.206.44:8080/bml/vermont/ringin/merge/ | US | xml | 345 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3516 | soundser.exe | 74.207.227.96:443 | — | Linode, LLC | US | malicious |
3516 | soundser.exe | 174.136.14.100:8080 | — | Colo4, LLC | US | malicious |
3516 | soundser.exe | 177.242.202.30:8080 | — | SERVICIO Y EQUIPO EN TELEFONÍA INTERNET Y TV S.A. DE C.V. | MX | malicious |
3516 | soundser.exe | 190.145.67.134:8090 | — | Telmex Colombia S.A. | CO | malicious |
3516 | soundser.exe | 98.142.208.27:443 | — | Total Server Solutions L.L.C. | US | malicious |
— | — | 183.82.110.170:53 | — | Atria Convergence Technologies pvt ltd | IN | malicious |
— | — | 189.154.42.168:80 | — | Uninet S.A. de C.V. | MX | malicious |
3516 | soundser.exe | 77.56.253.112:80 | — | Liberty Global Operations B.V. | CH | malicious |
3516 | soundser.exe | 94.76.200.114:8080 | — | Simply Transit Ltd | GB | malicious |
3516 | soundser.exe | 98.144.73.193:80 | — | Time Warner Cable Internet LLC | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3516 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3516 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3516 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3516 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3516 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3516 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 4 |
3516 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3516 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 5 |
3516 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3516 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 11 |
141 ETPRO signatures available at the full report