| URL: | https://www.driverscape.com |
| Full analysis: | https://app.any.run/tasks/54a5bb5a-e1da-4d77-b949-6d6c8fd8cfa0 |
| Verdict: | Suspicious activity |
| Analysis date: | December 08, 2020, 13:40:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3F9AE79B11CEFC8A690C8D5E3205D069 |
| SHA1: | ED09699592D1378A8761ED40455AB6E228E35C58 |
| SHA256: | 8273DD86DDBFFDDAA6A1AEEF8A4998AAEA7186D8D6B34FAB64E461AB0B47C57C |
| SSDEEP: | 3:N8DSLaWGA2:2OLch |
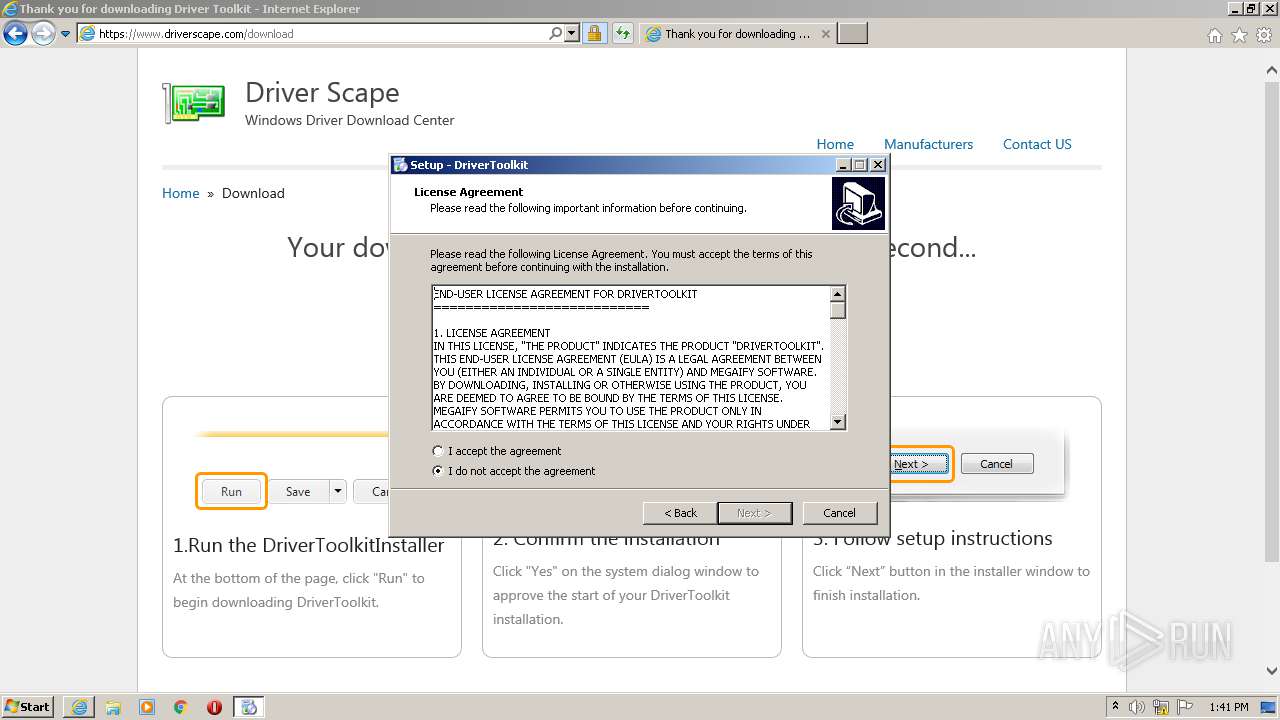
MALICIOUS
Drops executable file immediately after starts
- DriverToolkitInstaller.exe (PID: 2196)
- DriverToolkitInstaller.exe (PID: 3864)
- DriverToolkitInstaller.tmp (PID: 312)
Application was dropped or rewritten from another process
- DriverToolkitInstaller.exe (PID: 2196)
- DriverToolkitInstaller.exe (PID: 3864)
- DriverToolkit.exe (PID: 2280)
Changes settings of System certificates
- DriverToolkit.exe (PID: 2280)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 1932)
- DriverToolkitInstaller.exe (PID: 3864)
- iexplore.exe (PID: 960)
- DriverToolkitInstaller.exe (PID: 2196)
- DriverToolkitInstaller.tmp (PID: 312)
Reads Windows owner or organization settings
- DriverToolkitInstaller.tmp (PID: 312)
Reads the Windows organization settings
- DriverToolkitInstaller.tmp (PID: 312)
Drops a file with too old compile date
- DriverToolkitInstaller.tmp (PID: 312)
Drops a file that was compiled in debug mode
- DriverToolkitInstaller.tmp (PID: 312)
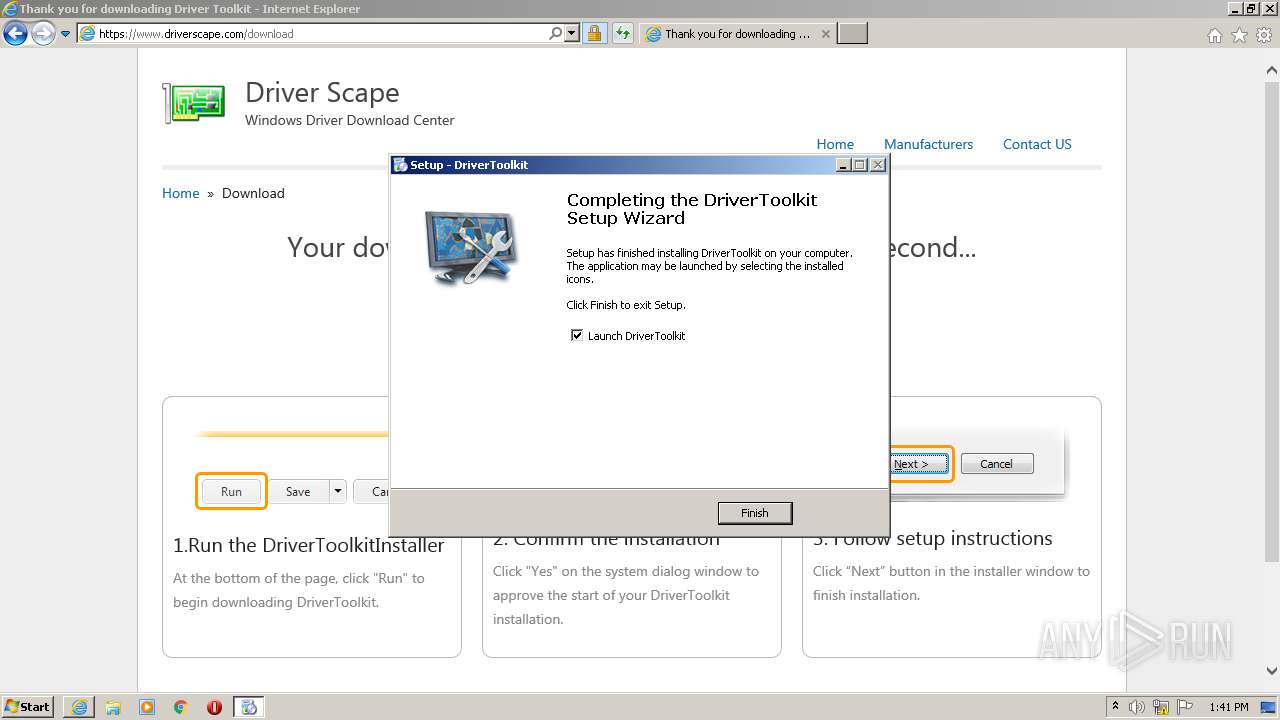
Creates a directory in Program Files
- DriverToolkitInstaller.tmp (PID: 312)
- DriverToolkit.exe (PID: 2280)
Adds / modifies Windows certificates
- DriverToolkit.exe (PID: 2280)
INFO
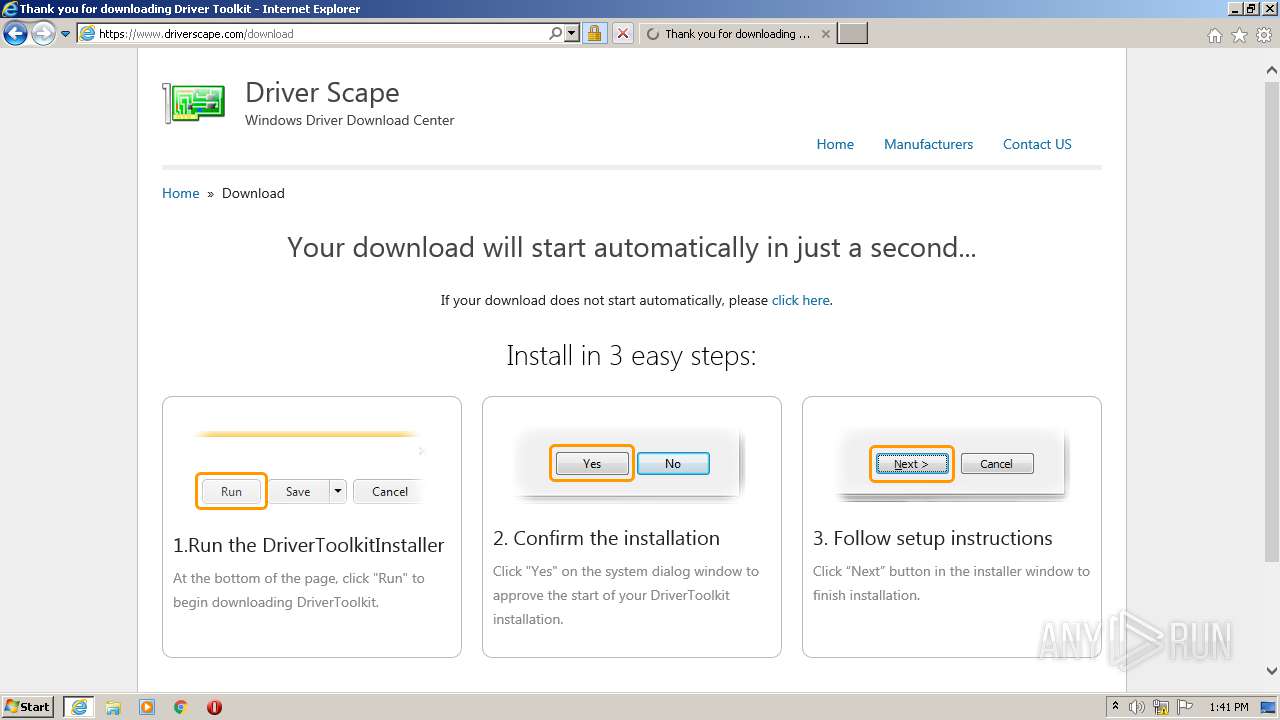
Application launched itself
- iexplore.exe (PID: 960)
Changes internet zones settings
- iexplore.exe (PID: 960)
Creates files in the user directory
- iexplore.exe (PID: 1932)
Changes settings of System certificates
- iexplore.exe (PID: 960)
Application was dropped or rewritten from another process
- DriverToolkitInstaller.tmp (PID: 3080)
- DriverToolkitInstaller.tmp (PID: 312)
Reads settings of System Certificates
- iexplore.exe (PID: 1932)
- iexplore.exe (PID: 960)
- DriverToolkit.exe (PID: 2280)
Reads internet explorer settings
- iexplore.exe (PID: 1932)
Modifies the phishing filter of IE
- iexplore.exe (PID: 960)
Adds / modifies Windows certificates
- iexplore.exe (PID: 960)
Loads dropped or rewritten executable
- DriverToolkitInstaller.tmp (PID: 312)
Creates a software uninstall entry
- DriverToolkitInstaller.tmp (PID: 312)
Creates files in the program directory
- DriverToolkitInstaller.tmp (PID: 312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
8
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Users\admin\AppData\Local\Temp\is-MGBSK.tmp\DriverToolkitInstaller.tmp" /SL5="$201DA,2034942,134144,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\DriverToolkitInstaller.exe" /SPAWNWND=$101D8 /NOTIFYWND=$401AC | C:\Users\admin\AppData\Local\Temp\is-MGBSK.tmp\DriverToolkitInstaller.tmp | DriverToolkitInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.driverscape.com | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:960 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
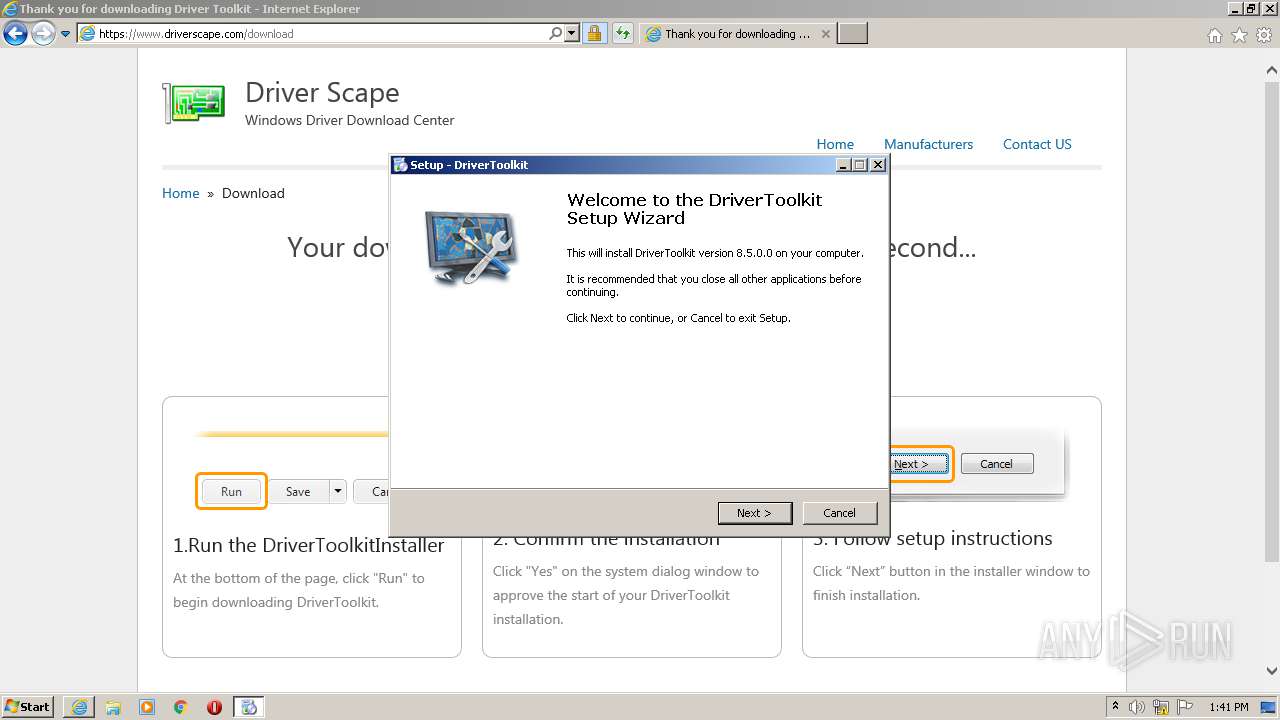
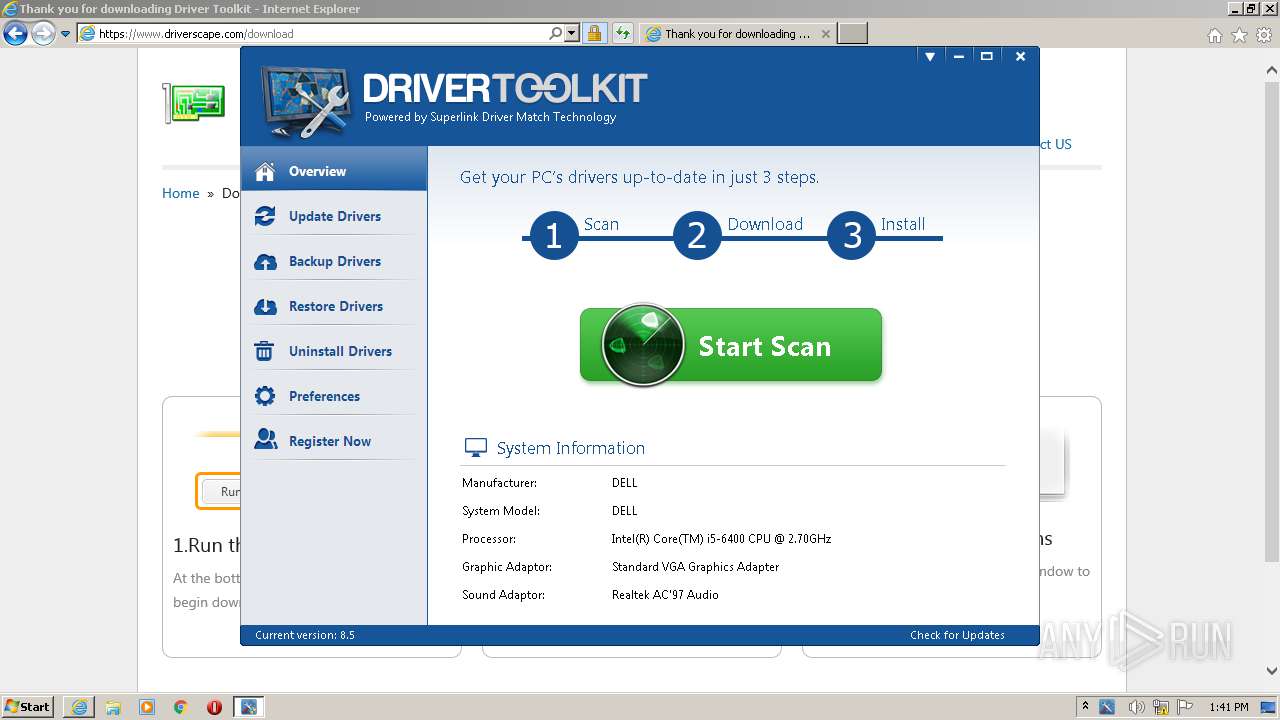
| 2196 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\DriverToolkitInstaller.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\DriverToolkitInstaller.exe | iexplore.exe | ||||||||||||
User: admin Company: Megaify Software Integrity Level: MEDIUM Description: DriverToolkit Setup Exit code: 0 Version: 8.5 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\DriverToolkit\DriverToolkit.exe" | C:\Program Files\DriverToolkit\DriverToolkit.exe | DriverToolkitInstaller.tmp | ||||||||||||
User: admin Company: Megaify Software Co., Ltd. Integrity Level: HIGH Description: DriverToolkit Exit code: 0 Version: 8.5.0.0 Modules
| |||||||||||||||
| 3080 | "C:\Users\admin\AppData\Local\Temp\is-4426P.tmp\DriverToolkitInstaller.tmp" /SL5="$401AC,2034942,134144,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\DriverToolkitInstaller.exe" | C:\Users\admin\AppData\Local\Temp\is-4426P.tmp\DriverToolkitInstaller.tmp | — | DriverToolkitInstaller.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3848 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:960 CREDAT:4003088 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | |||||||||||||||
| 3864 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\DriverToolkitInstaller.exe" /SPAWNWND=$101D8 /NOTIFYWND=$401AC | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\DriverToolkitInstaller.exe | DriverToolkitInstaller.tmp | ||||||||||||
User: admin Company: Megaify Software Integrity Level: HIGH Description: DriverToolkit Setup Exit code: 0 Version: 8.5 Modules
| |||||||||||||||
Total events
1 471
Read events
1 277
Write events
185
Delete events
9
Modification events
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3695543612 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30854503 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
16
Suspicious files
29
Text files
224
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1932 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab470A.tmp | — | |
MD5:— | SHA256:— | |||
| 1932 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar470B.tmp | — | |
MD5:— | SHA256:— | |||
| 1932 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2BPD6S3F.txt | — | |
MD5:— | SHA256:— | |||
| 1932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 1932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
| 1932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A6C0FDC2F20EB02B7673AFFC7682CCF7 | binary | |
MD5:— | SHA256:— | |||
| 1932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\2M30CH3H.htm | html | |
MD5:— | SHA256:— | |||
| 1932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_7C1C45A209E1552633930171FD75B297 | der | |
MD5:— | SHA256:— | |||
| 1932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_7C1C45A209E1552633930171FD75B297 | binary | |
MD5:— | SHA256:— | |||
| 1932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
42
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1932 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBj7MZ1CMRFmCAAAAABi2Ko%3D | US | der | 471 b | whitelisted |
1932 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | der | 472 b | whitelisted |
1932 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | der | 472 b | whitelisted |
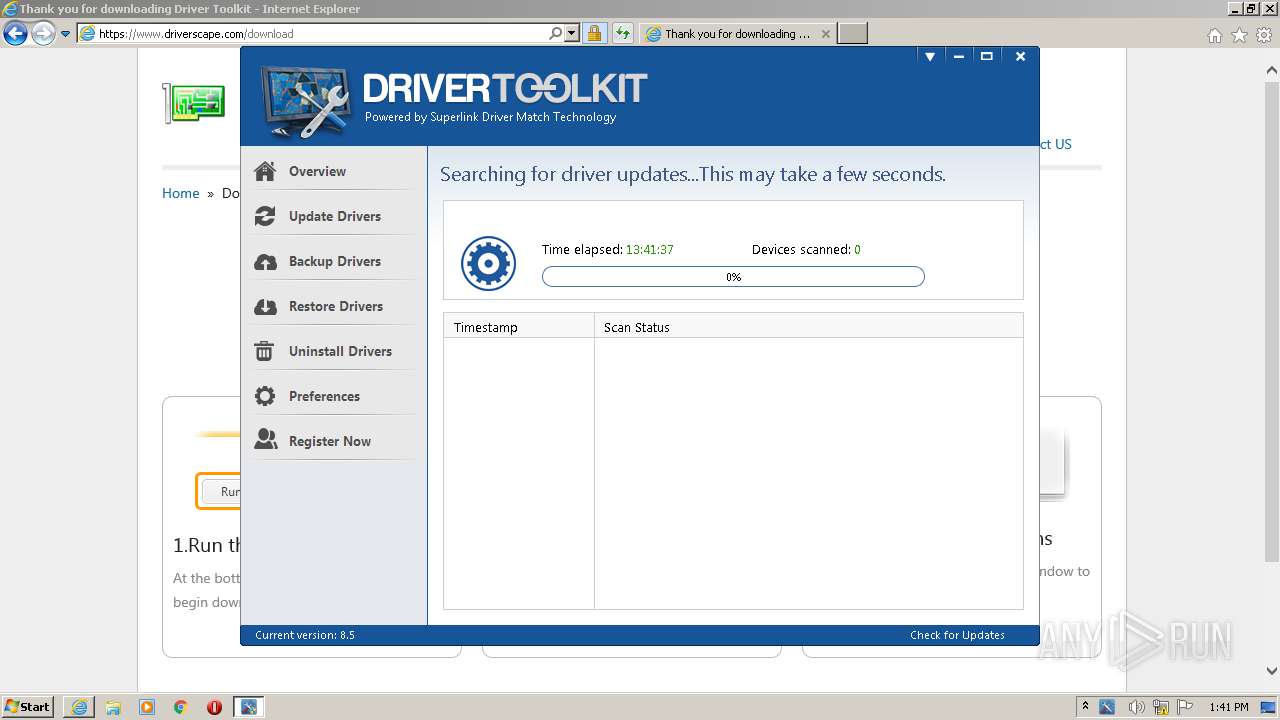
2280 | DriverToolkit.exe | POST | 200 | 159.69.65.4:80 | http://debug.drivertoolkit.com/service/debug.php | US | — | — | suspicious |
1932 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBj7MZ1CMRFmCAAAAABi2Ko%3D | US | der | 471 b | whitelisted |
1932 | iexplore.exe | GET | 200 | 23.55.163.68:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgSmZRcB5V9dz6Nvm4sU3T3xnA%3D%3D | US | der | 527 b | whitelisted |
1932 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1932 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDliVAU%2F6ZWzwIAAAAAgFX%2B | US | der | 472 b | whitelisted |
960 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1932 | iexplore.exe | 104.75.88.112:443 | s7.addthis.com | Akamai Technologies, Inc. | NL | suspicious |
1932 | iexplore.exe | 23.55.163.68:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | US | suspicious |
1932 | iexplore.exe | 216.58.212.164:443 | www.google.com | Google Inc. | US | whitelisted |
1932 | iexplore.exe | 172.217.23.142:443 | apis.google.com | Google Inc. | US | whitelisted |
1932 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1932 | iexplore.exe | 23.55.163.61:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | US | unknown |
1932 | iexplore.exe | 192.99.170.88:443 | www.driverscape.com | OVH SAS | US | unknown |
1932 | iexplore.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1932 | iexplore.exe | 116.202.213.150:443 | ga.megaify.com | 334,Udyog Vihar | IN | unknown |
1932 | iexplore.exe | 142.250.74.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.driverscape.com |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.google.com |
| malicious |
apis.google.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
platform.twitter.com |
| whitelisted |
ga.megaify.com |
| unknown |
ocsp.pki.goog |
| whitelisted |