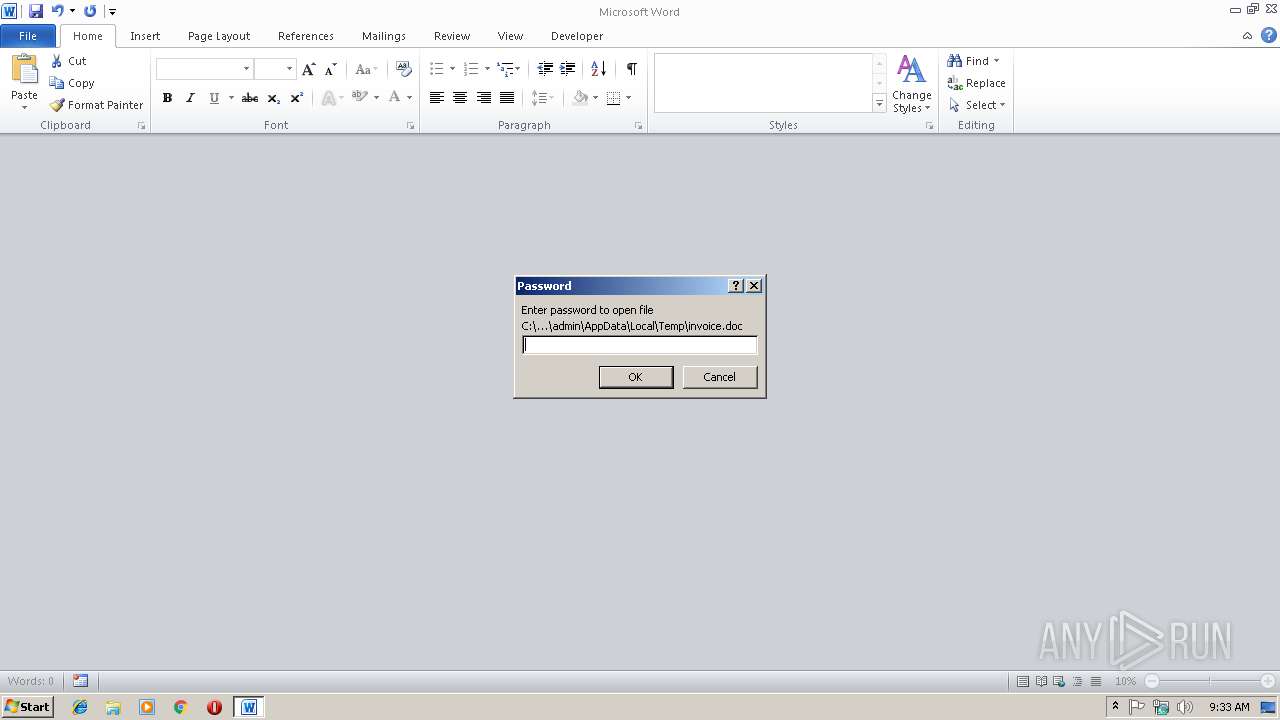
| File name: | invoice.doc |
| Full analysis: | https://app.any.run/tasks/acf9b8aa-880f-46a8-b2a6-592b3003a9af |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 09:33:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Locale ID: 1033, Author: cwtoi, Subject: aievstrm |
| MD5: | 85A3898F88235B2887D73E7C2DEF5FAE |
| SHA1: | 17642E30256E968315C82B357101CA649731C221 |
| SHA256: | 826C8DA48360599B6E13DF5212EF855B28E814BA46A23068664DD7A1A425326E |
| SSDEEP: | 768:K7ACy1kz5f6e3uqdPJrGf4eIq9XeyuZRft/59:kA1UDu+hGf4eISXsF |
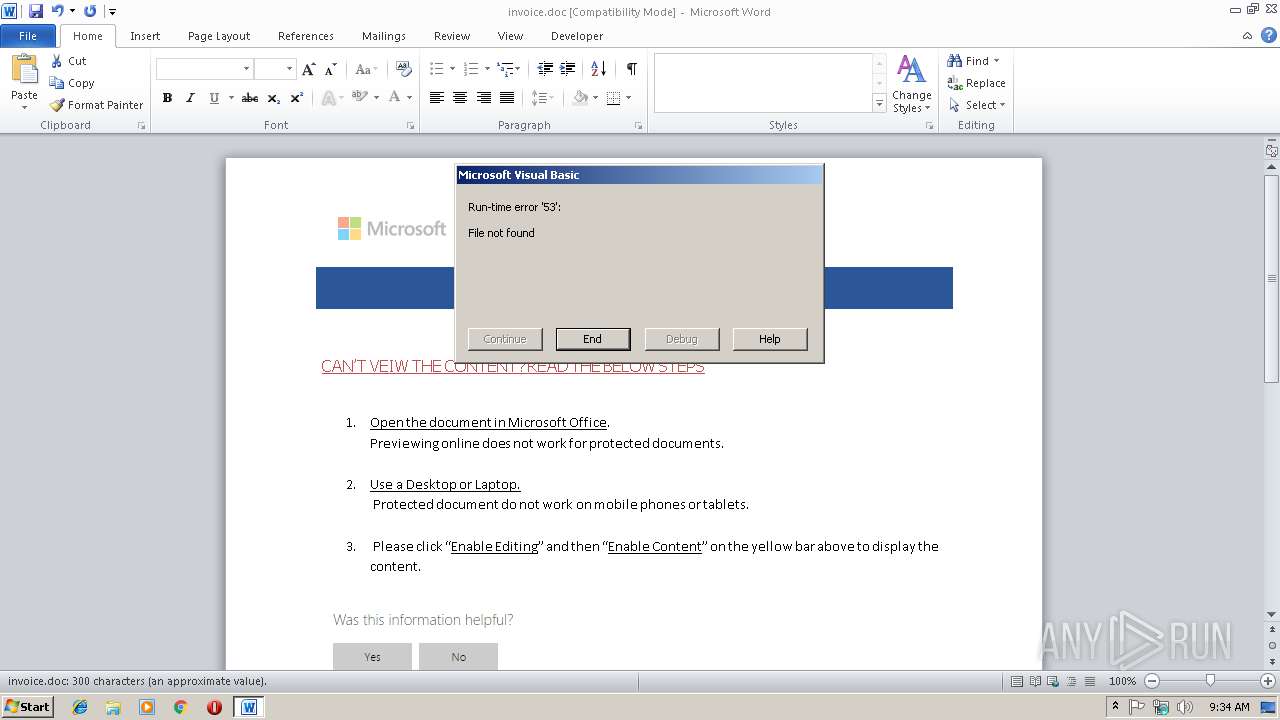
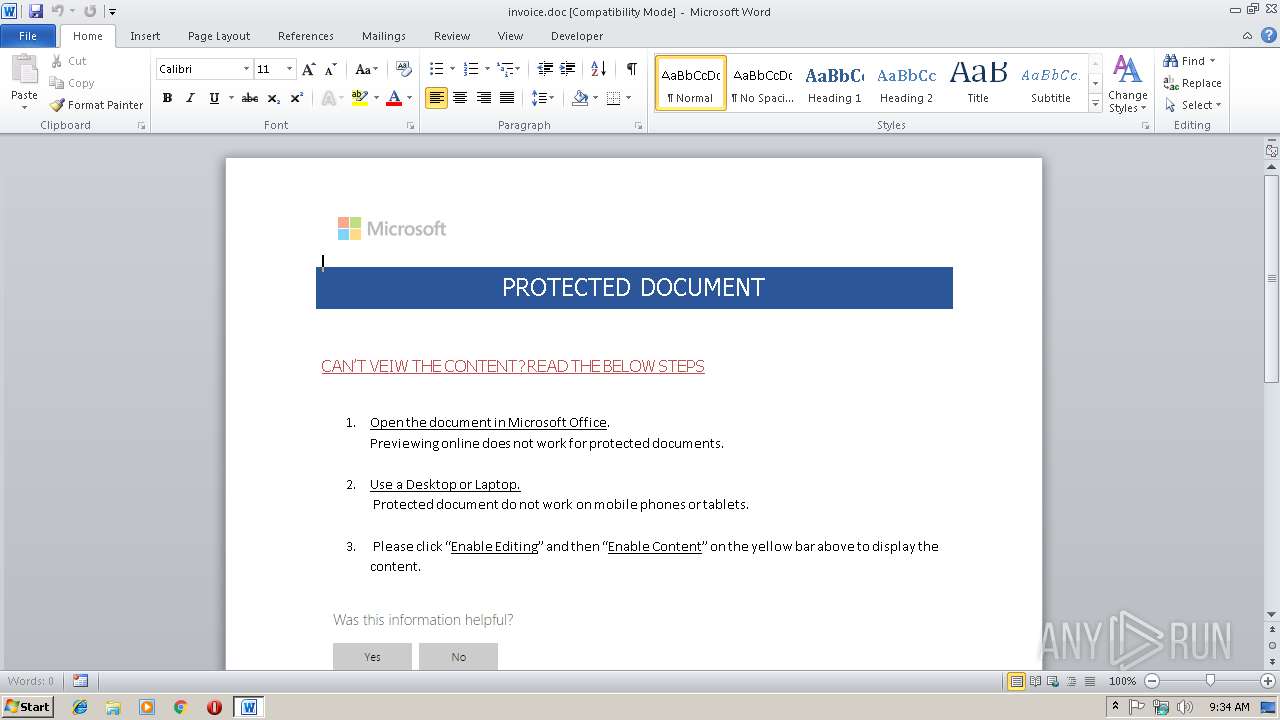
MALICIOUS
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 2812)
SUSPICIOUS
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 2812)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2812)
Creates files in the user directory
- WINWORD.EXE (PID: 2812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| LocaleIndicator: | 1033 |
| Author: | cwtoi |
| Subject: | aievstrm |
Total processes
30
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2812 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\invoice.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 215
Read events
815
Write events
395
Delete events
5
Modification events
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }8$ |
Value: 7D382400FC0A0000010000000000000000000000 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1301151774 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301151888 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301151889 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: FC0A0000681606229093D40100000000 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | #:$ |
Value: 233A2400FC0A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | #:$ |
Value: 233A2400FC0A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR987D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFDDEB7AB1908D5087.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFCA0E5098618344D8.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF5FE57FE63F7D1318.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF68EEBB6FA4EC6B49.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\msoAFB0.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC9FA1E344C02E698.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFCEB1BD31DDF06865.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F6EFD27D.png | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A6407E5A.png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2812 | WINWORD.EXE | GET | 404 | 209.141.61.249:80 | http://209.141.61.249/516.exe | US | html | 205 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2812 | WINWORD.EXE | 209.141.61.249:80 | — | FranTech Solutions | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2812 | WINWORD.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2812 | WINWORD.EXE | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious downloader - 404 Not Found for .exe |