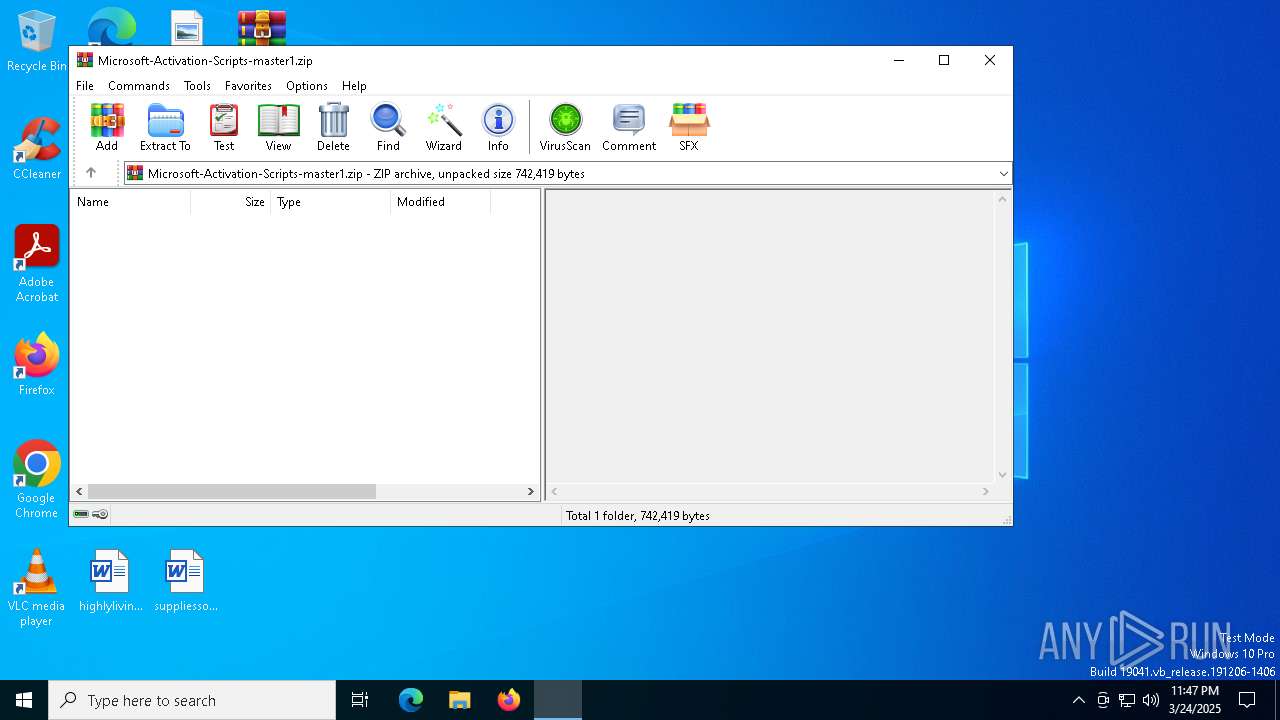
| File name: | Microsoft-Activation-Scripts-master1.zip |
| Full analysis: | https://app.any.run/tasks/2dfa9cf1-1132-4fec-ab7c-c495c83ca261 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 23:47:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | AE21D617B9C6EDDC114B4F920BAC2DA6 |
| SHA1: | 70BDE0557835F951FF9D198FAF9A079B709A2116 |
| SHA256: | 8262AF9A9FC0345CA8405251B1354A679C8E768BB87FC89E177D9A04859E8A1E |
| SSDEEP: | 6144:E+xs+Jb1dqZxK1N3FyI5Ox8Fca/rxwDk0dFT+2eif/6:Qub1gKz3wKa4qQAR+n2/6 |
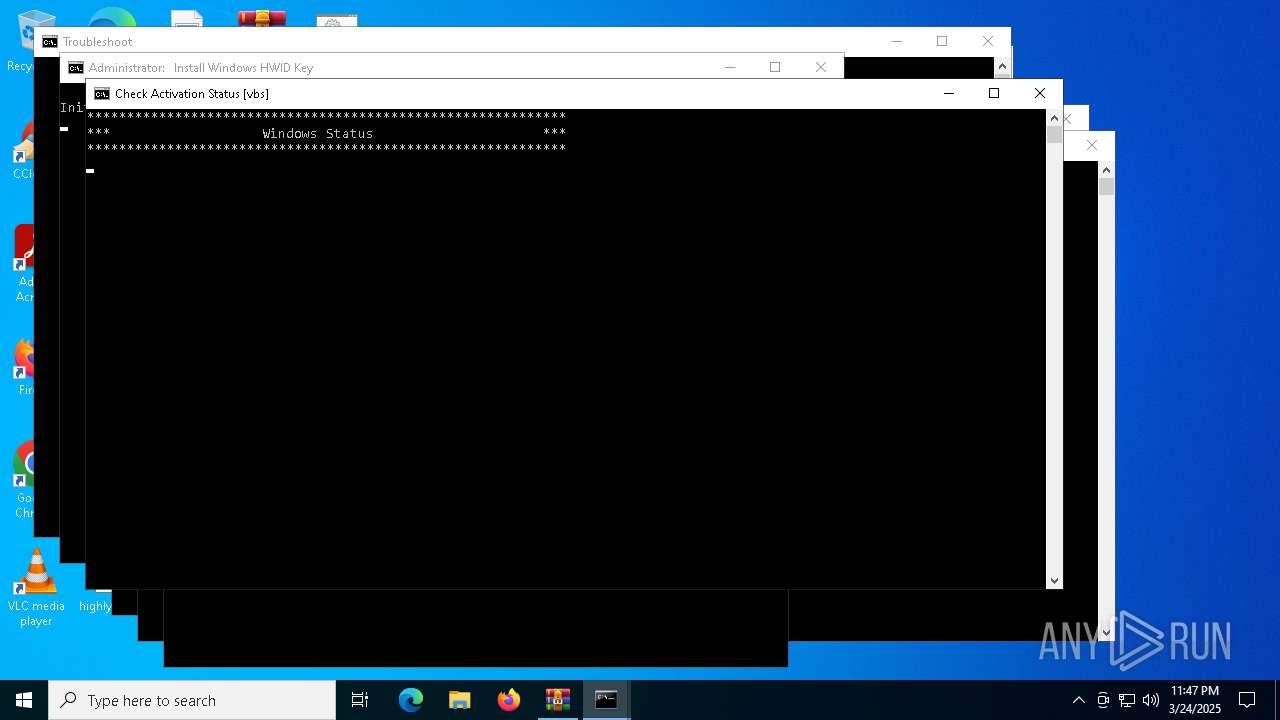
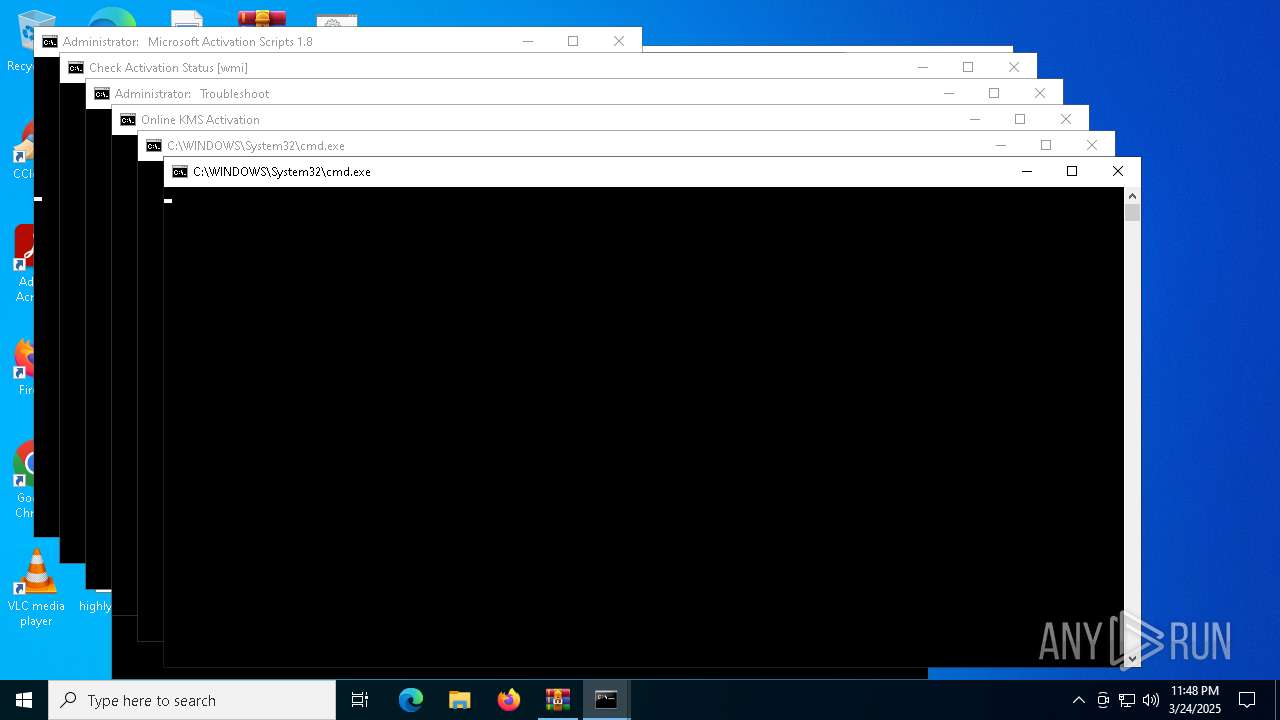
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7340)
Starts NET.EXE for service management
- cmd.exe (PID: 8084)
- net.exe (PID: 7520)
- cmd.exe (PID: 4188)
- net.exe (PID: 7788)
- net.exe (PID: 8136)
- cmd.exe (PID: 5380)
- net.exe (PID: 7808)
- net.exe (PID: 2136)
- net.exe (PID: 4220)
- net.exe (PID: 900)
- net.exe (PID: 1676)
- net.exe (PID: 7684)
- net.exe (PID: 5360)
- net.exe (PID: 7808)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7992)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 2320)
- powershell.exe (PID: 8112)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 1052)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 7608)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 7928)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 5380)
- powershell.exe (PID: 6132)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 1164)
- powershell.exe (PID: 4220)
- cmd.exe (PID: 4980)
- powershell.exe (PID: 7528)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 5984)
- powershell.exe (PID: 7820)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 6372)
Application launched itself
- cmd.exe (PID: 7992)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 1052)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 4980)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 6372)
- ClipUp.exe (PID: 5576)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7864)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 7572)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 7980)
Executing commands from ".cmd" file
- cmd.exe (PID: 7864)
- cmd.exe (PID: 6048)
- powershell.exe (PID: 8112)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 7544)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 6132)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 7800)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7528)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 1804)
- powershell.exe (PID: 7820)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 4740)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6048)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 2852)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 968)
- cmd.exe (PID: 8148)
The process executes VB scripts
- cmd.exe (PID: 8084)
- cmd.exe (PID: 5380)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 7460)
- cscript.exe (PID: 7880)
- cscript.exe (PID: 684)
- cscript.exe (PID: 7632)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 7460)
- cscript.exe (PID: 7880)
- cscript.exe (PID: 920)
- cscript.exe (PID: 684)
- cscript.exe (PID: 7632)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 4188)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 2616)
Hides command output
- cmd.exe (PID: 6644)
- cmd.exe (PID: 7796)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 5124)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 900)
- cmd.exe (PID: 2284)
- cmd.exe (PID: 4776)
- cmd.exe (PID: 7724)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 5008)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 4452)
- cmd.exe (PID: 864)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7592)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 6728)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6644)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 4980)
- cmd.exe (PID: 2852)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 7248)
Starts SC.EXE for service management
- cmd.exe (PID: 4188)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 2616)
Windows service management via SC.EXE
- sc.exe (PID: 7300)
- sc.exe (PID: 668)
- sc.exe (PID: 7612)
- sc.exe (PID: 8040)
- sc.exe (PID: 900)
- sc.exe (PID: 6752)
- sc.exe (PID: 7964)
- sc.exe (PID: 7880)
- sc.exe (PID: 8120)
- sc.exe (PID: 6872)
- sc.exe (PID: 5416)
- sc.exe (PID: 8164)
- sc.exe (PID: 7880)
- sc.exe (PID: 6728)
- sc.exe (PID: 8056)
- sc.exe (PID: 7988)
- sc.exe (PID: 2284)
- sc.exe (PID: 5416)
- sc.exe (PID: 900)
- sc.exe (PID: 6724)
- sc.exe (PID: 2392)
- sc.exe (PID: 6028)
- sc.exe (PID: 5416)
- sc.exe (PID: 7616)
- sc.exe (PID: 4408)
- sc.exe (PID: 5508)
- sc.exe (PID: 6132)
- sc.exe (PID: 6620)
- sc.exe (PID: 8124)
- sc.exe (PID: 6028)
- sc.exe (PID: 7512)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 2096)
- cmd.exe (PID: 4776)
- cmd.exe (PID: 7676)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4740)
- cmd.exe (PID: 5380)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 920)
Accesses computer name via WMI (SCRIPT)
- cscript.exe (PID: 920)
Gets a collection of all available drive names (SCRIPT)
- cscript.exe (PID: 920)
Gets the drive type (SCRIPT)
- cscript.exe (PID: 920)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- cscript.exe (PID: 920)
Executable content was dropped or overwritten
- Dism.exe (PID: 660)
- Dism.exe (PID: 7852)
- Dism.exe (PID: 1012)
The process creates files with name similar to system file names
- Dism.exe (PID: 660)
- Dism.exe (PID: 7852)
- WerFault.exe (PID: 7496)
- Dism.exe (PID: 1012)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 7908)
- DismHost.exe (PID: 4620)
- DismHost.exe (PID: 5376)
Executes application which crashes
- cscript.exe (PID: 920)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 684)
- cscript.exe (PID: 7632)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8148)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2240)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 5380)
INFO
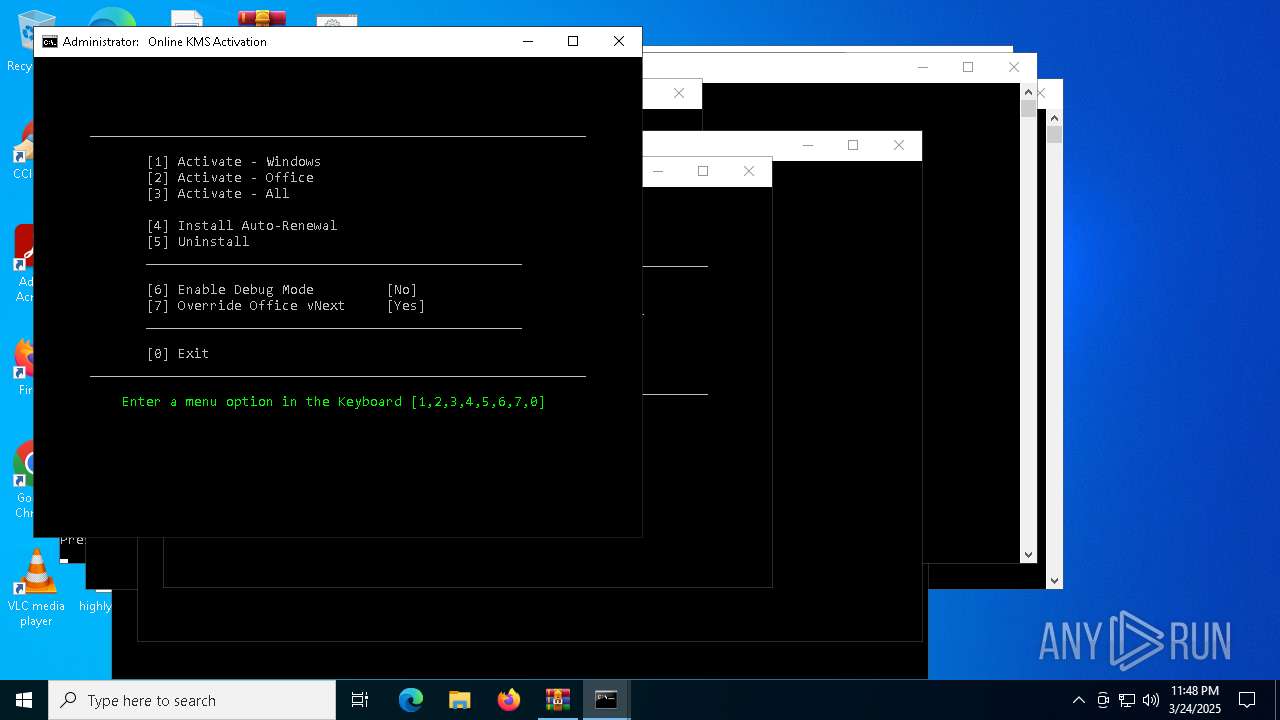
Manual execution by a user
- cmd.exe (PID: 7464)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 7800)
Checks operating system version
- cmd.exe (PID: 7864)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 4740)
Checks supported languages
- mode.com (PID: 7260)
- mode.com (PID: 7492)
- mode.com (PID: 8160)
- mode.com (PID: 1228)
- mode.com (PID: 7496)
- mode.com (PID: 5416)
- DismHost.exe (PID: 7908)
- mode.com (PID: 7728)
- DismHost.exe (PID: 4620)
- DismHost.exe (PID: 5376)
- mode.com (PID: 6828)
Starts MODE.COM to configure console settings
- mode.com (PID: 7260)
- mode.com (PID: 7492)
- mode.com (PID: 8160)
- mode.com (PID: 1228)
- mode.com (PID: 7496)
- mode.com (PID: 5416)
- mode.com (PID: 7728)
- mode.com (PID: 6828)
Reads security settings of Internet Explorer
- cscript.exe (PID: 7460)
- WMIC.exe (PID: 8136)
- WMIC.exe (PID: 7928)
- WMIC.exe (PID: 7768)
- WMIC.exe (PID: 1324)
- WMIC.exe (PID: 7780)
- WMIC.exe (PID: 1764)
- cscript.exe (PID: 7880)
- WMIC.exe (PID: 6800)
- WMIC.exe (PID: 6148)
- WMIC.exe (PID: 736)
- WMIC.exe (PID: 1132)
- cscript.exe (PID: 920)
- WMIC.exe (PID: 7868)
- WMIC.exe (PID: 7568)
- WMIC.exe (PID: 7924)
- WMIC.exe (PID: 8040)
- WMIC.exe (PID: 4920)
- WMIC.exe (PID: 8036)
- WMIC.exe (PID: 4776)
- WMIC.exe (PID: 5772)
- cscript.exe (PID: 684)
- WMIC.exe (PID: 2140)
- WMIC.exe (PID: 7548)
- WMIC.exe (PID: 8060)
- WMIC.exe (PID: 8028)
- WMIC.exe (PID: 3996)
- cscript.exe (PID: 7632)
Reads Microsoft Office registry keys
- reg.exe (PID: 8004)
- reg.exe (PID: 7832)
- reg.exe (PID: 5728)
- reg.exe (PID: 8028)
- reg.exe (PID: 8044)
- reg.exe (PID: 736)
- reg.exe (PID: 7724)
- reg.exe (PID: 7020)
- reg.exe (PID: 7600)
- reg.exe (PID: 8032)
- reg.exe (PID: 5772)
Reads the software policy settings
- cscript.exe (PID: 920)
Checks proxy server information
- cscript.exe (PID: 920)
Creates files or folders in the user directory
- cscript.exe (PID: 920)
- WerFault.exe (PID: 7496)
Create files in a temporary directory
- Dism.exe (PID: 660)
- Dism.exe (PID: 7852)
- Dism.exe (PID: 1012)
- ClipUp.exe (PID: 920)
Reads the computer name
- DismHost.exe (PID: 7908)
- DismHost.exe (PID: 4620)
- DismHost.exe (PID: 5376)
The sample compiled with english language support
- Dism.exe (PID: 660)
- Dism.exe (PID: 7852)
- Dism.exe (PID: 1012)
Reads Environment values
- DismHost.exe (PID: 7908)
- DismHost.exe (PID: 4620)
- DismHost.exe (PID: 5376)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7924)
Creates files in the program directory
- ClipUp.exe (PID: 920)
- cmd.exe (PID: 5380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:03:21 13:46:58 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Microsoft-Activation-Scripts-master/ |
Total processes
718
Monitored processes
560
Malicious processes
24
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | reg query "HKCU\Console" /v ForceV2 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | reg query HKLM\SYSTEM\CurrentControlSet\Services\wlidsvc /v ImagePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v ImagePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | findstr /i "ClipSVC-1058 sppsvc-1058" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo "TwBTAE0AYQBqAG8AcgBWAGUAcgBzAGkAbwBuAD0ANQA7AE8AUwBNAGkAbgBvAHIAVgBlAHIAcwBpAG8AbgA9ADEAOwBPAFMAUABsAGEAdABmAG8AcgBtAEkAZAA9ADIAOwBQAFAAPQAwADsAUABmAG4APQBNAGkAYwByAG8AcwBvAGYAdAAuAFcAaQBuAGQAbwB3AHMALgA0ADgALgBYADEAOQAtADkAOAA4ADQAMQBfADgAdwBlAGsAeQBiADMAZAA4AGIAYgB3AGUAOwBEAG8AdwBuAGwAZQB2AGUAbABHAGUAbgB1AGkAbgBlAFMAdABhAHQAZQA9ADEAOwAAAA==" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | cmd /c exit /b -2147023436 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147943860 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | findstr /i ID | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | choice /C:12345670 /N | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | C:\WINDOWS\system32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
101 288
Read events
101 270
Write events
18
Delete events
0
Modification events
| (PID) Process: | (7340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master1.zip | |||
| (PID) Process: | (7340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7444) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31169815 | |||
| (PID) Process: | (7444) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: 830788448 | |||
Executable files
150
Suspicious files
8
Text files
41
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bwltbbv1.h11.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4220 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ptjvwwdl.ncb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mtbjvt5b.5i4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_n2en2zog.z2p.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7528 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_azw0emek.wcg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8084 | cmd.exe | C:\Users\admin\AppData\Local\Temp\slmgr.vbs | text | |
MD5:3903BCAB32A4A853DFA54962112D4D02 | SHA256:95FC646D222D324DB46F603A7F675C329FE59A567ED27FDAED2A572A19206816 | |||
| 4220 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iqse15sr.1f2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wc1diaq2.342.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_djzldobg.ida.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7820 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kptrzxg0.0se.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
20
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
920 | cscript.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
920 | cscript.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_2010-07-06.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
920 | cscript.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
l.root-servers.net |
| unknown |