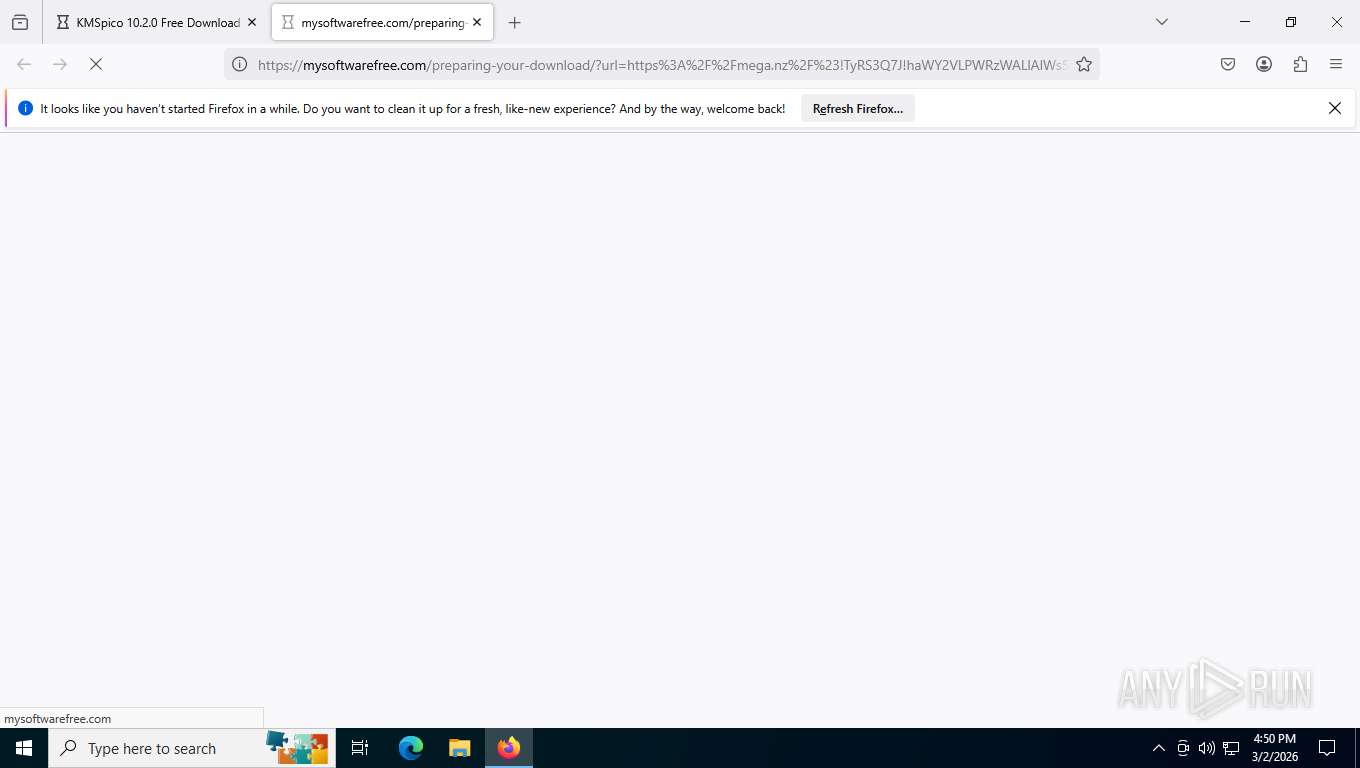
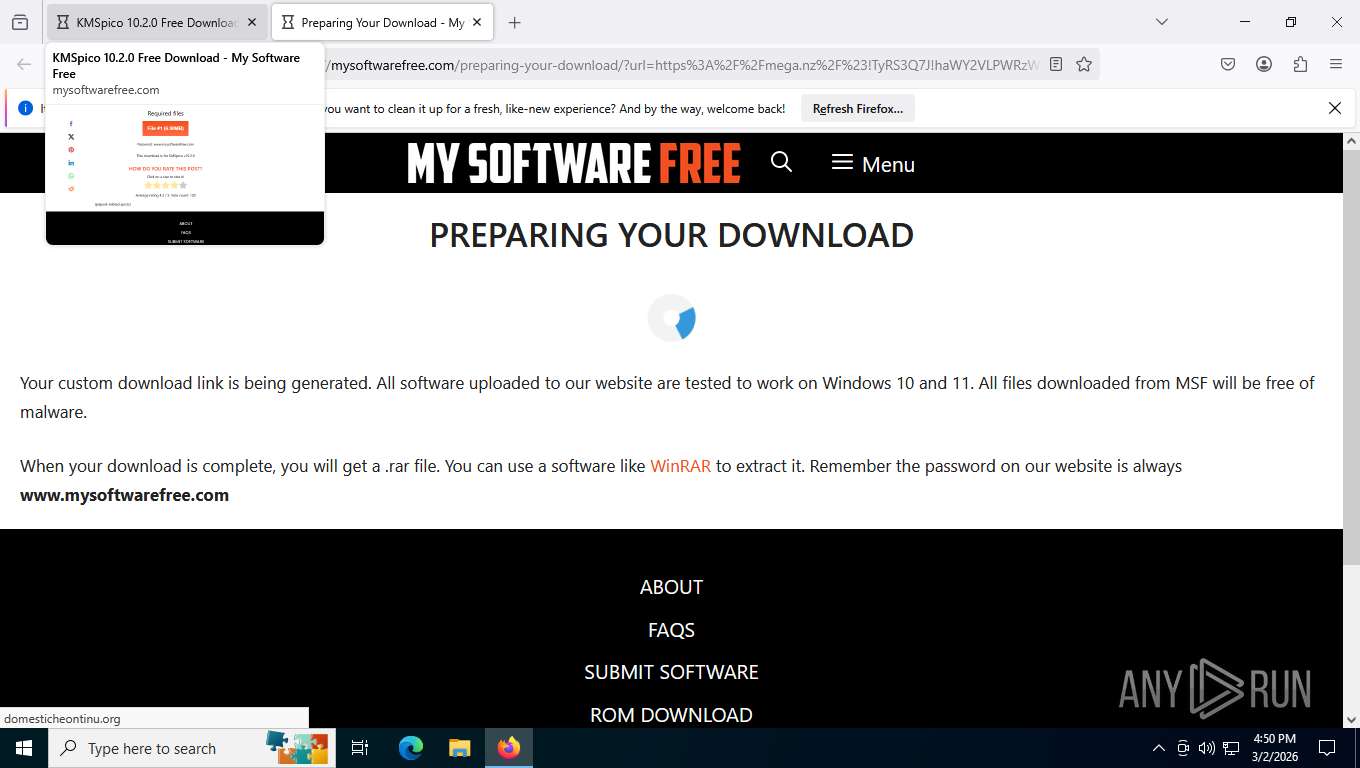
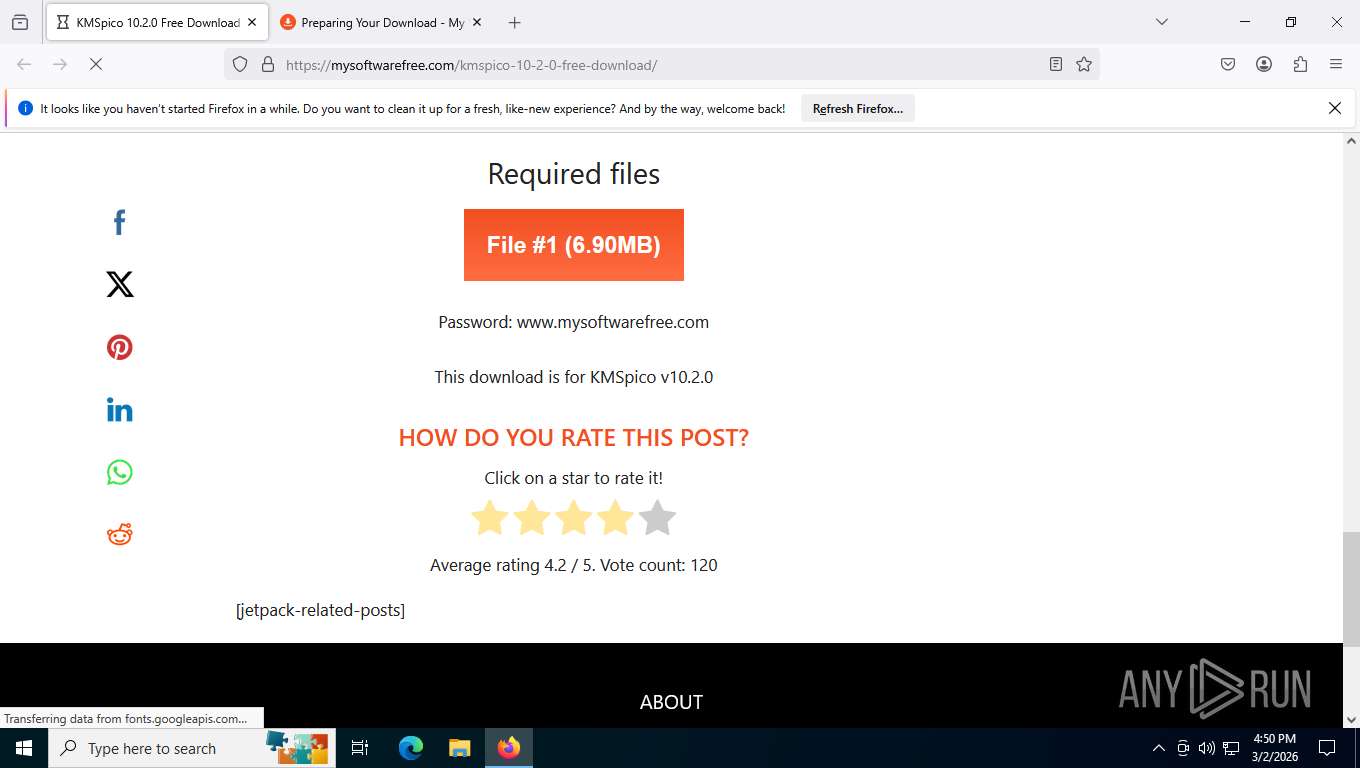
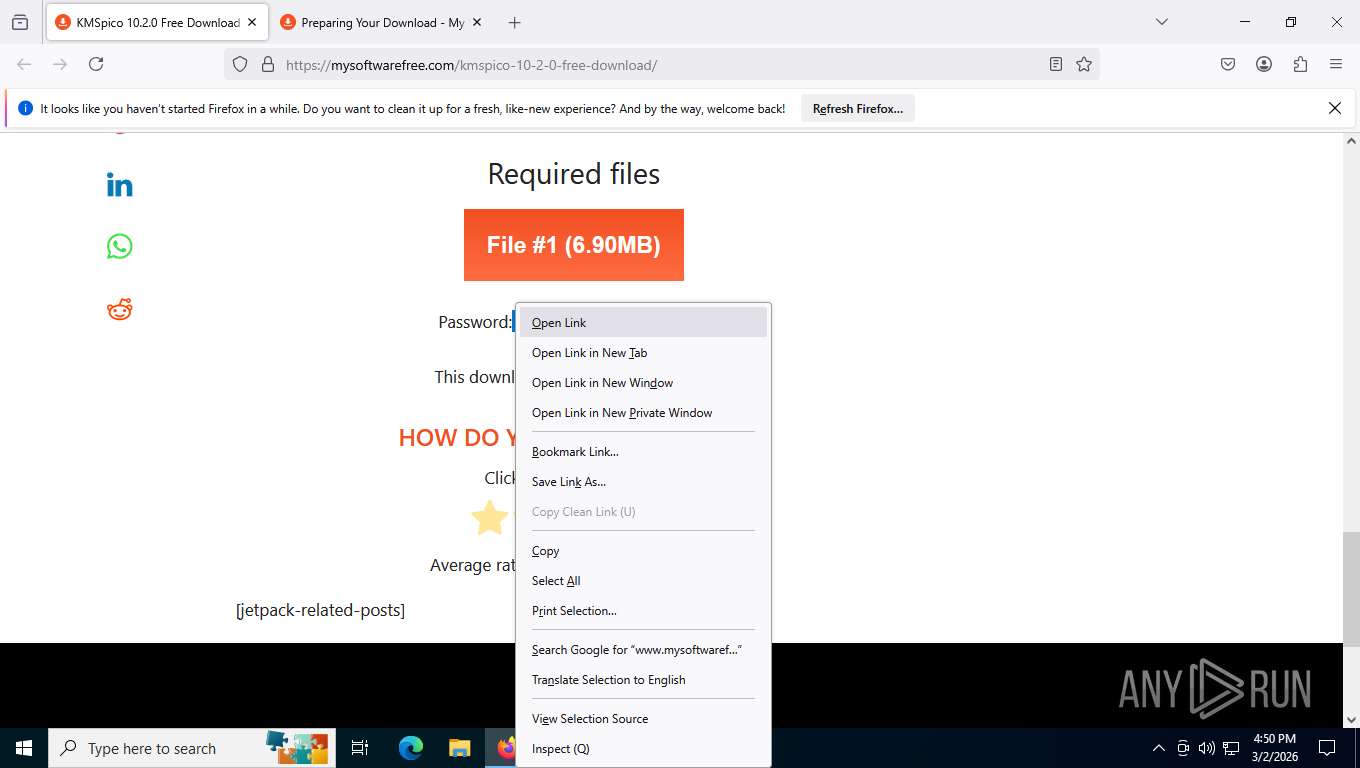
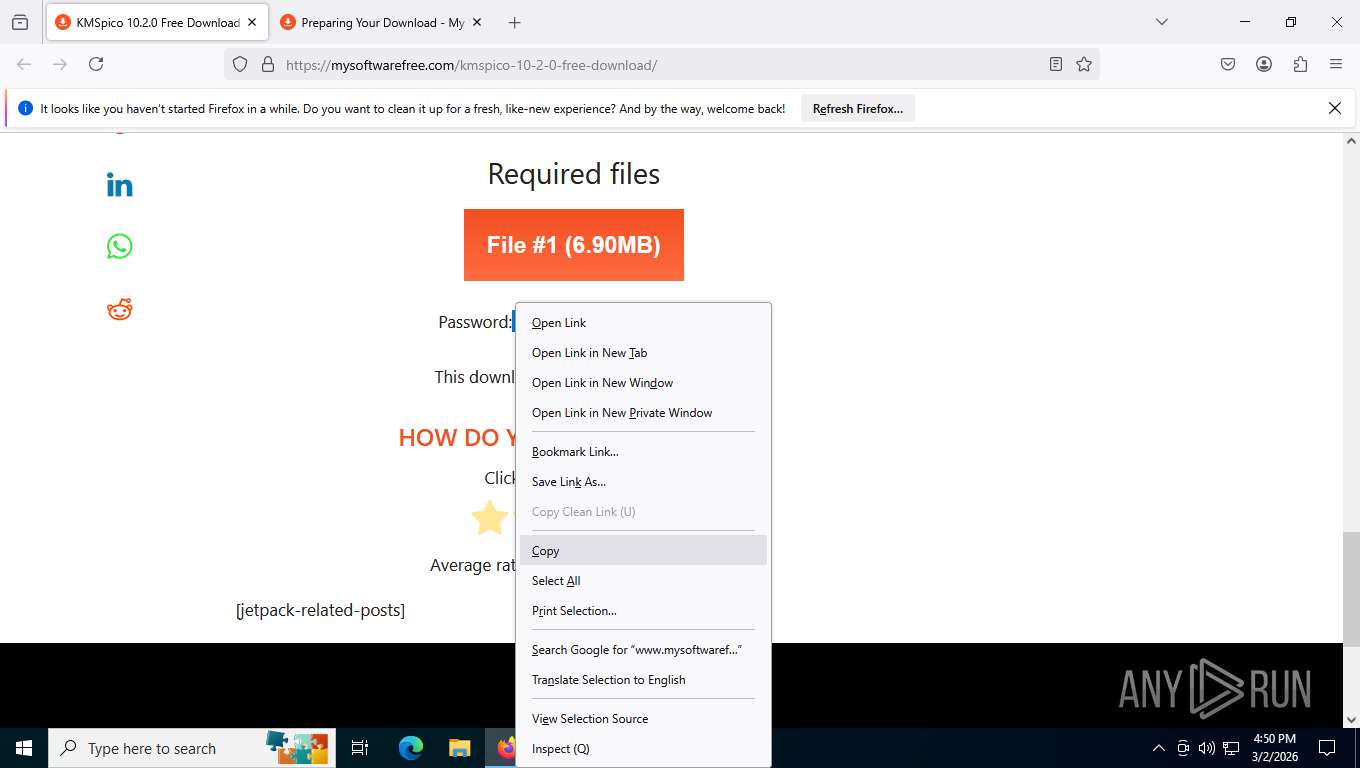
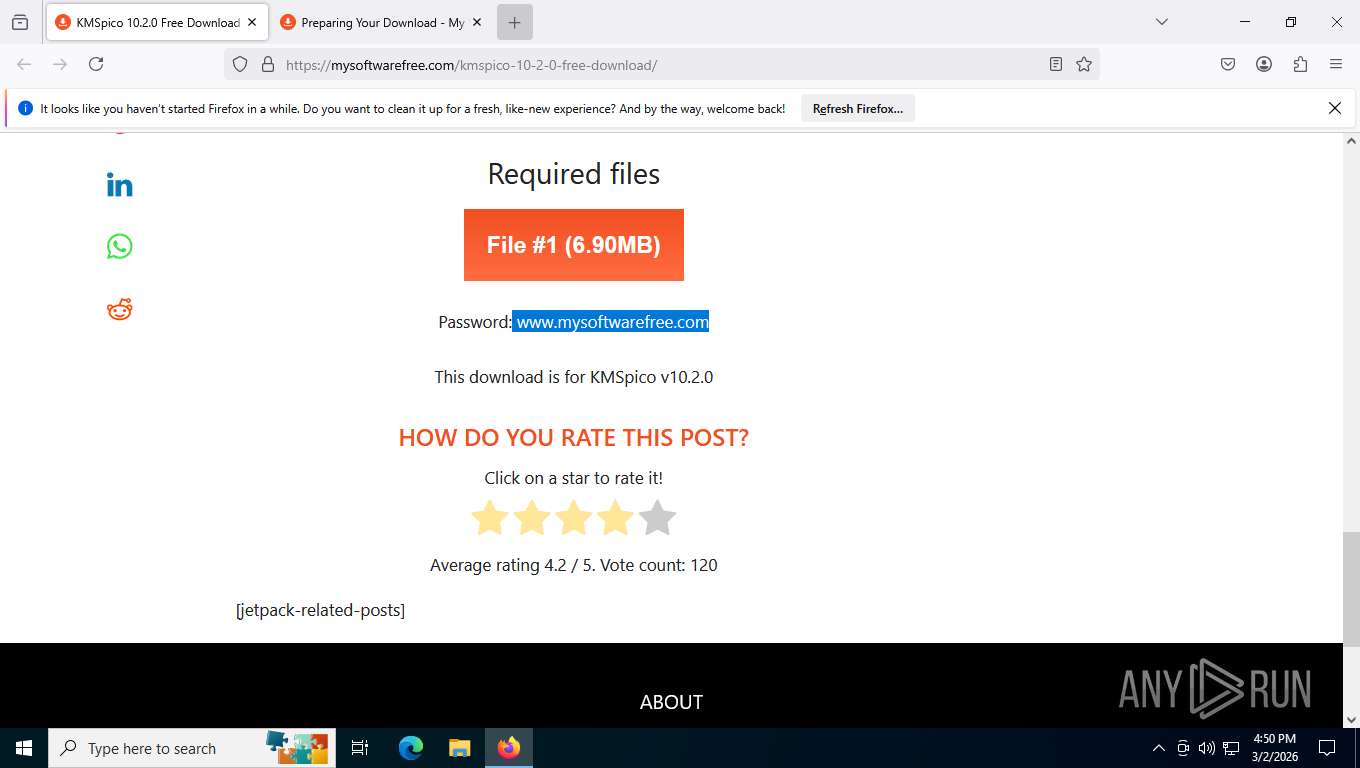
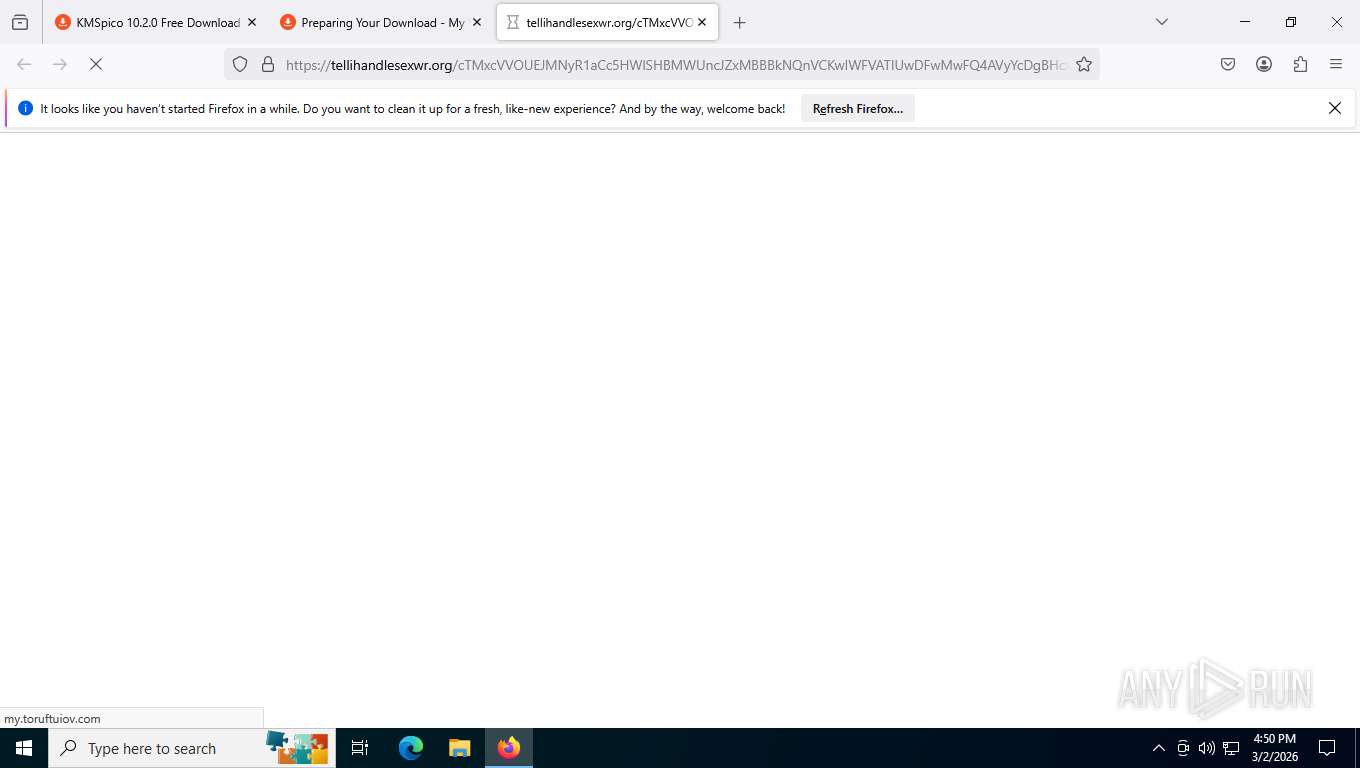
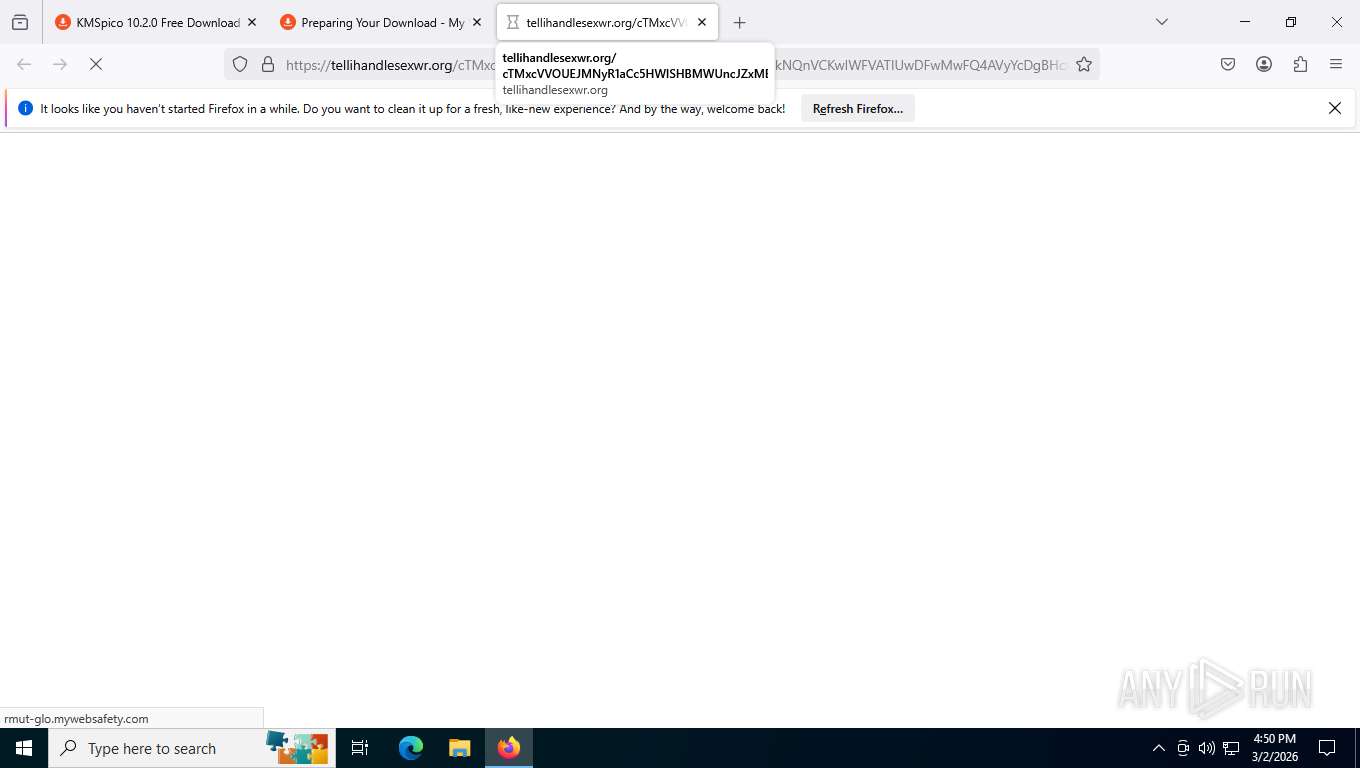
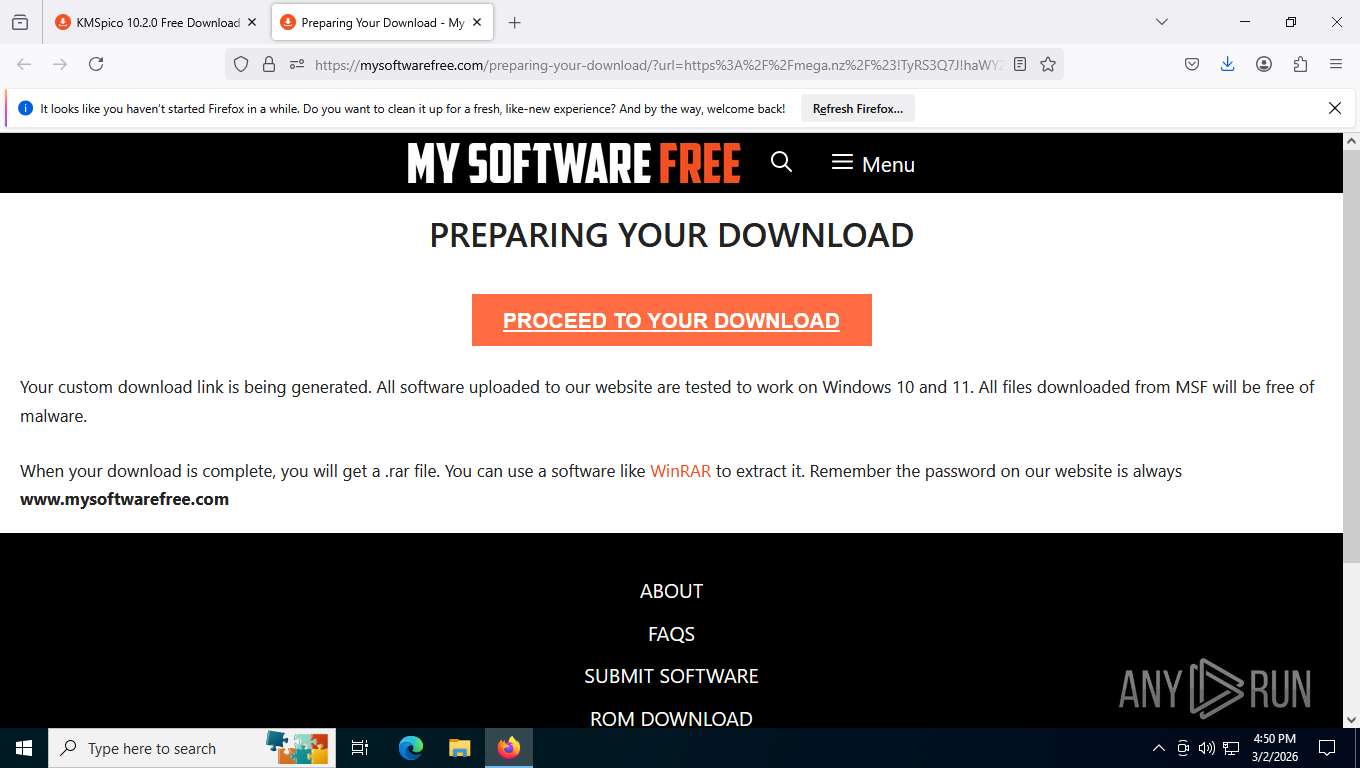
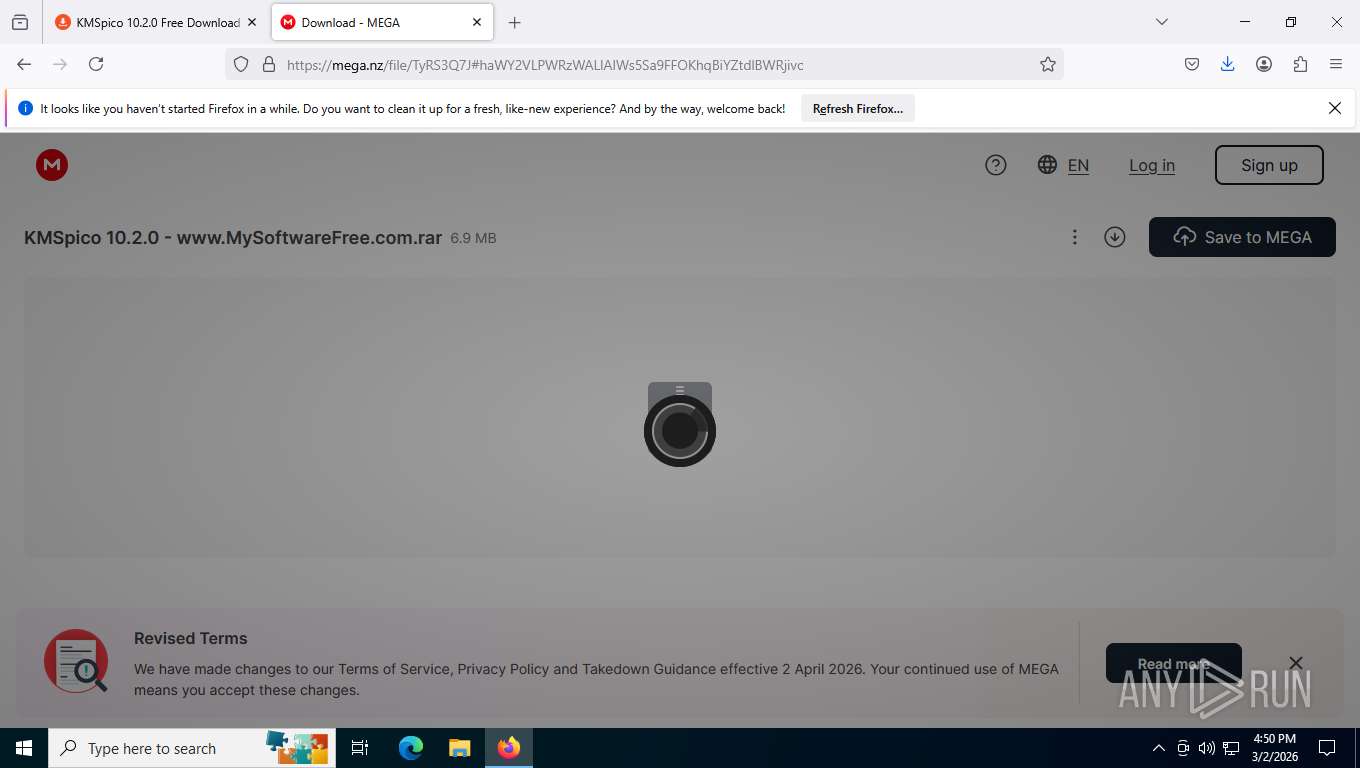
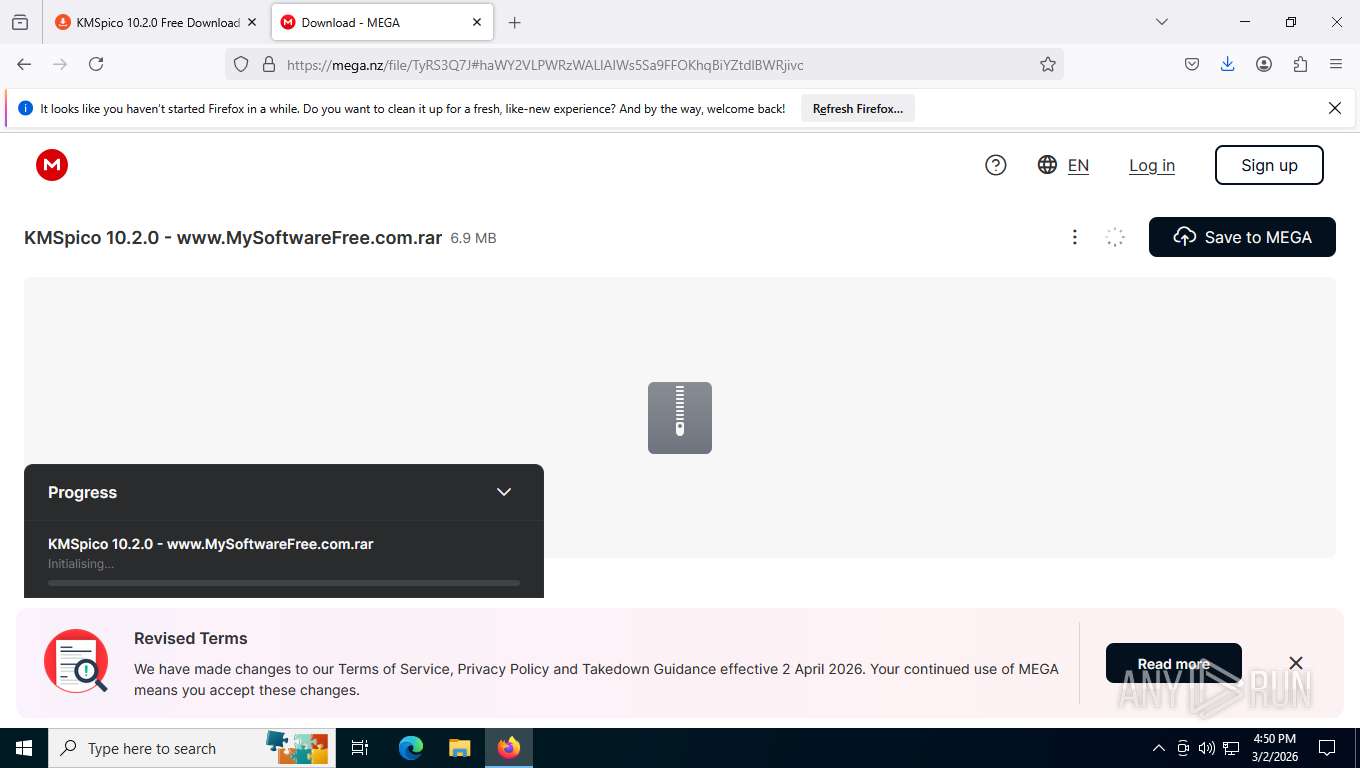
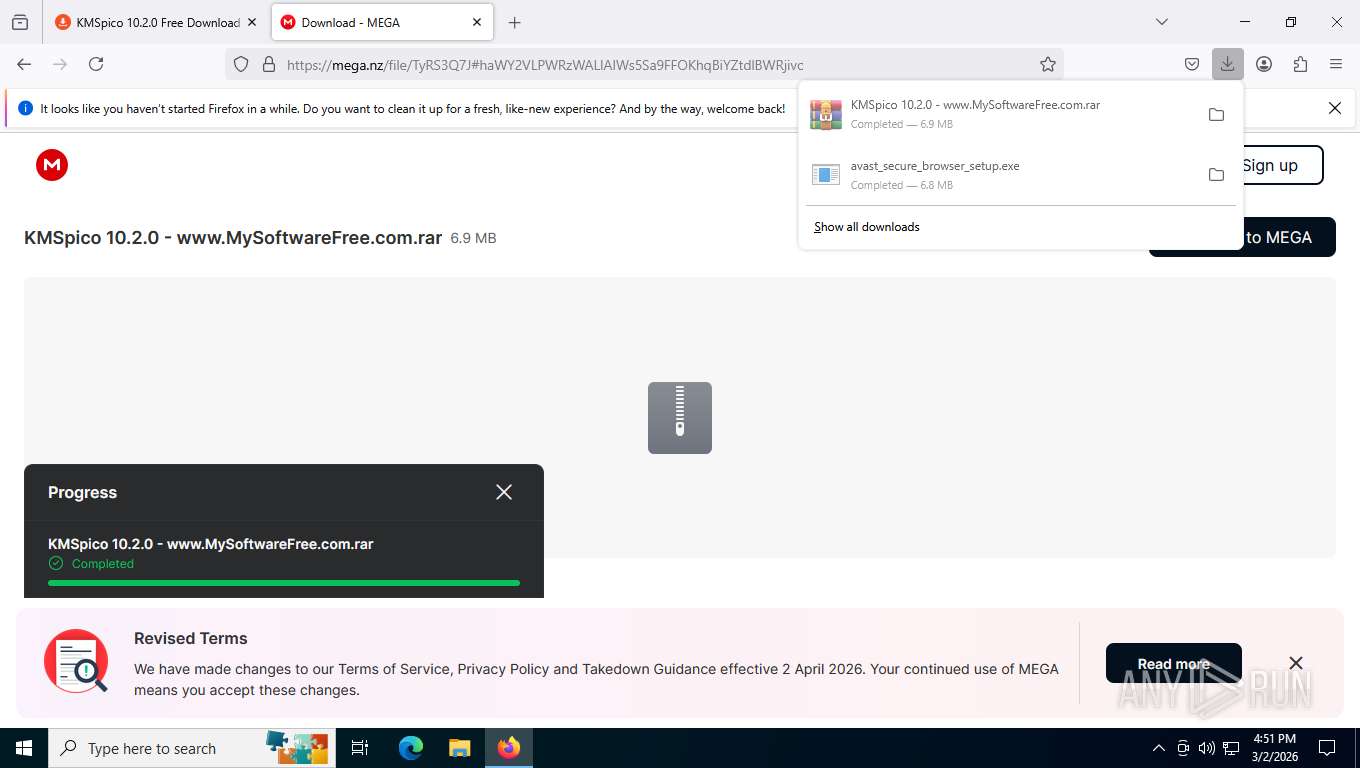
| URL: | https://mysoftwarefree.com/kmspico-10-2-0-free-download/ |
| Full analysis: | https://app.any.run/tasks/271cd294-1e4f-4cbd-80bb-dfc1b34981c5 |
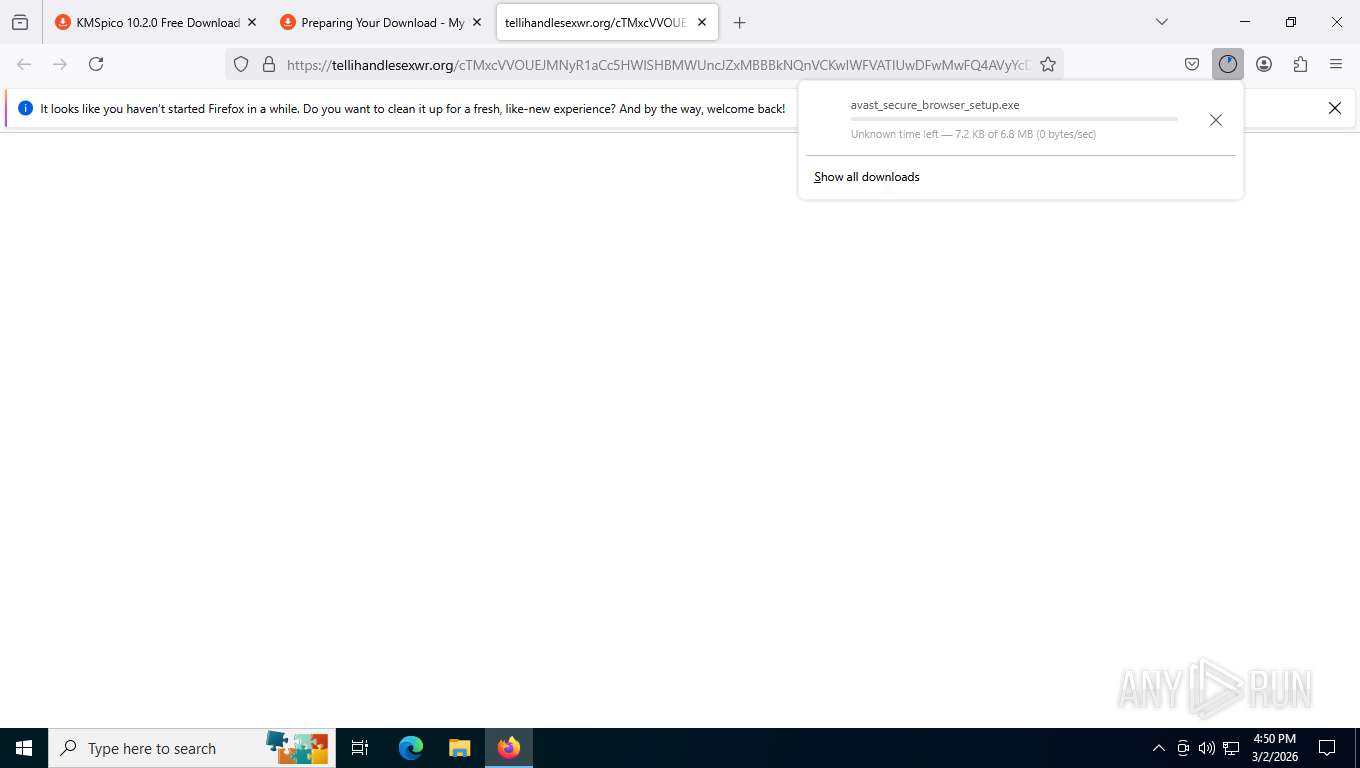
| Verdict: | Malicious activity |
| Analysis date: | March 02, 2026, 21:49:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DEBE912BBED1F435493C4CE36D123AC5 |
| SHA1: | 609F5F1D2DBFE2B65EE12578F18C17280592927B |
| SHA256: | 825C349FB2211DC561B36979F53D4DC8AB0EE9BC58921CC7A94793DD2156F889 |
| SSDEEP: | 3:N8pJKIVIn0V58Fmn:2pEIVu0Vd |
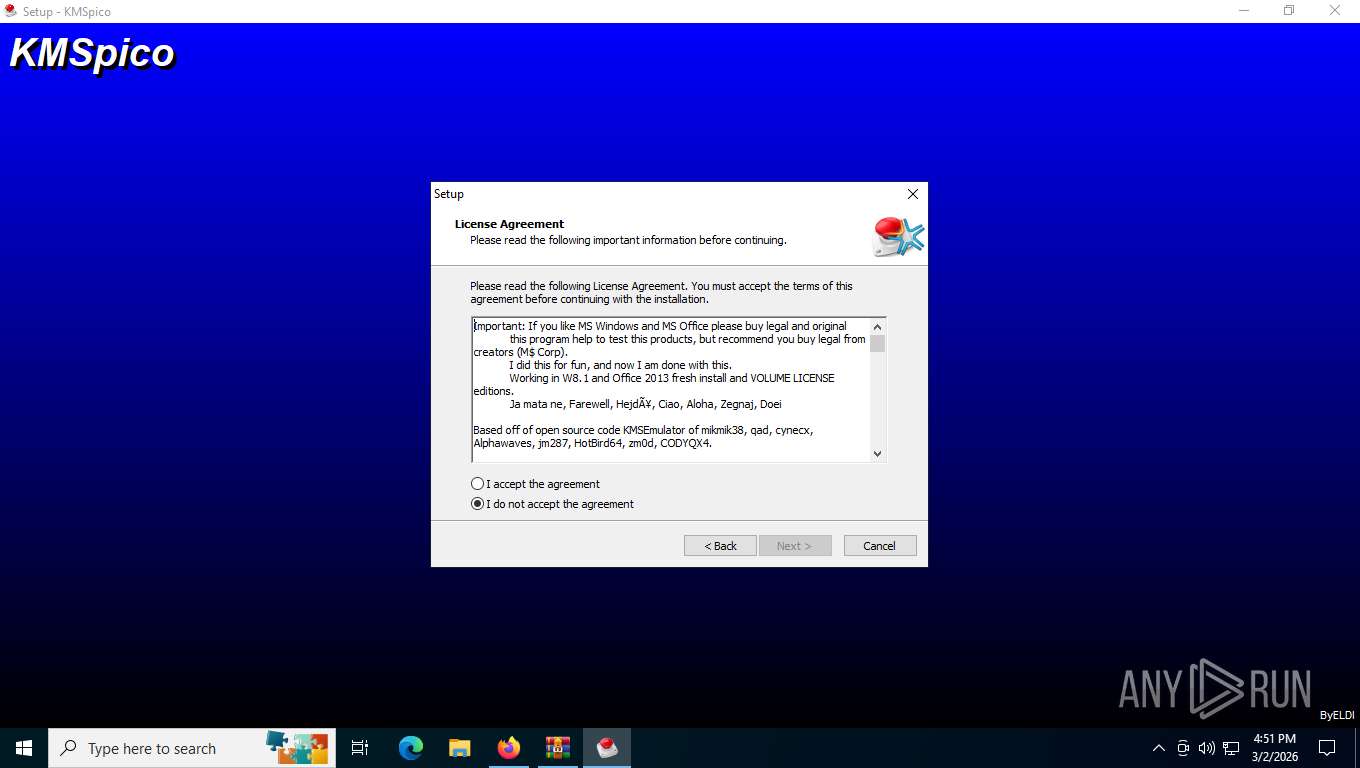
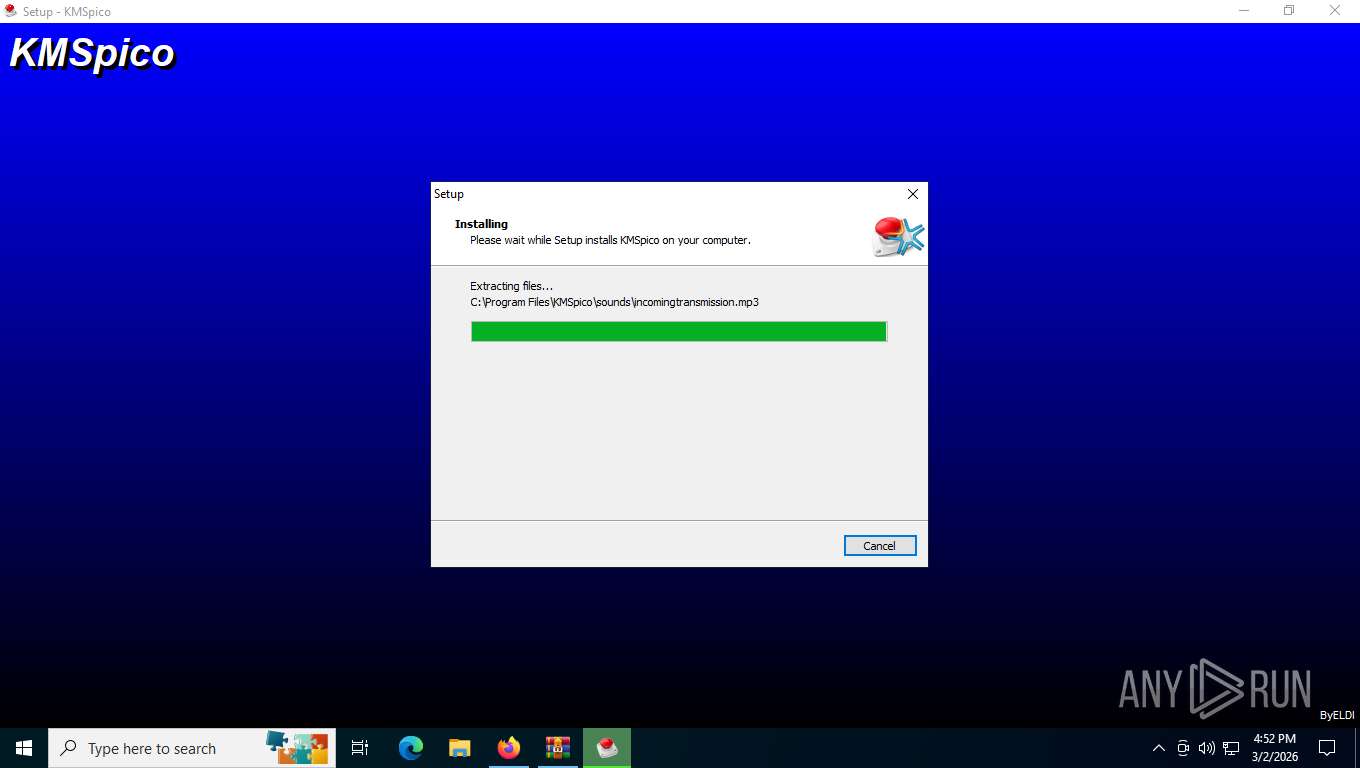
MALICIOUS
GENERIC has been found (auto)
- WinRAR.exe (PID: 7244)
Executing a file with an untrusted certificate
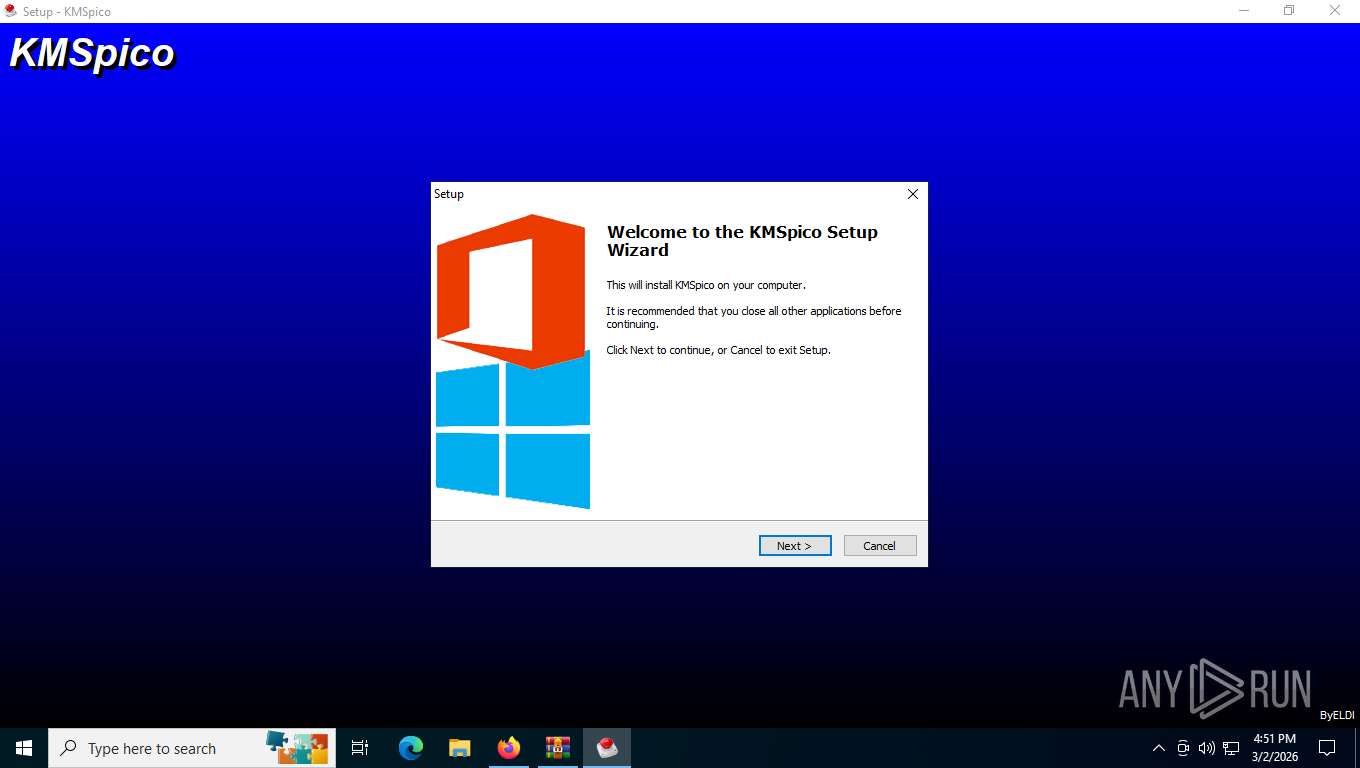
- KMSpico_setup.exe (PID: 8288)
- KMSpico_setup.exe (PID: 5140)
- KMSELDI.exe (PID: 8004)
- AutoPico.exe (PID: 3112)
Disables Windows Smartscreen
- KMSpico_setup.tmp (PID: 8076)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5988)
Changes image file execution options
- KMSELDI.exe (PID: 8004)
- AutoPico.exe (PID: 3112)
SUSPICIOUS
Executing commands from ".cmd" file
- KMSpico_setup.tmp (PID: 8076)
Starts CMD.EXE for commands execution
- KMSpico_setup.tmp (PID: 8076)
Creates scheduled task with highest privileges
- schtasks.exe (PID: 4684)
Reads the Windows owner or organization settings
- KMSpico_setup.tmp (PID: 8076)
Modifies the phishing filter of IE
- KMSpico_setup.tmp (PID: 8076)
Starts SC.EXE for service management
- cmd.exe (PID: 2000)
Creates a new Windows service
- sc.exe (PID: 4956)
INFO
Application launched itself
- firefox.exe (PID: 3016)
- firefox.exe (PID: 4504)
Drops script file
- firefox.exe (PID: 4840)
- WinRAR.exe (PID: 7244)
- firefox.exe (PID: 4504)
- KMSpico_setup.tmp (PID: 8076)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 2000)
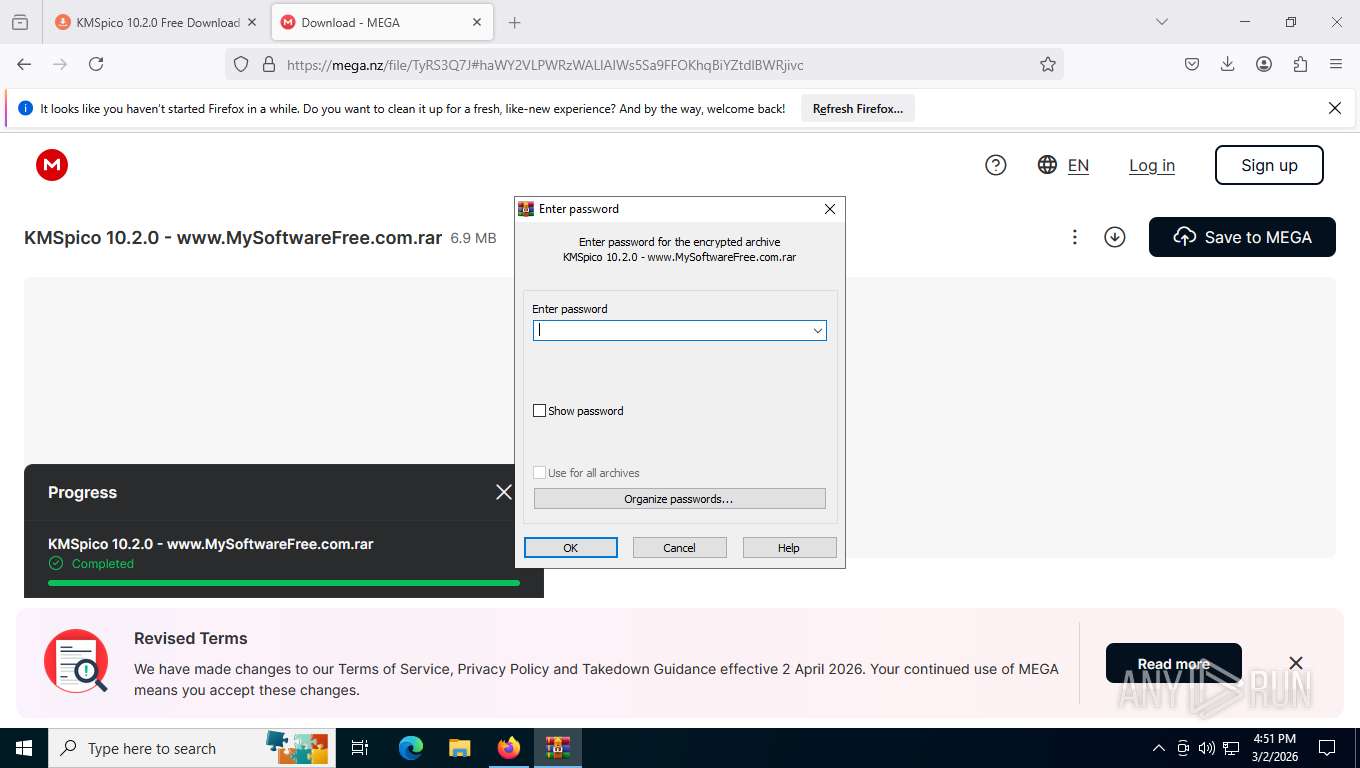
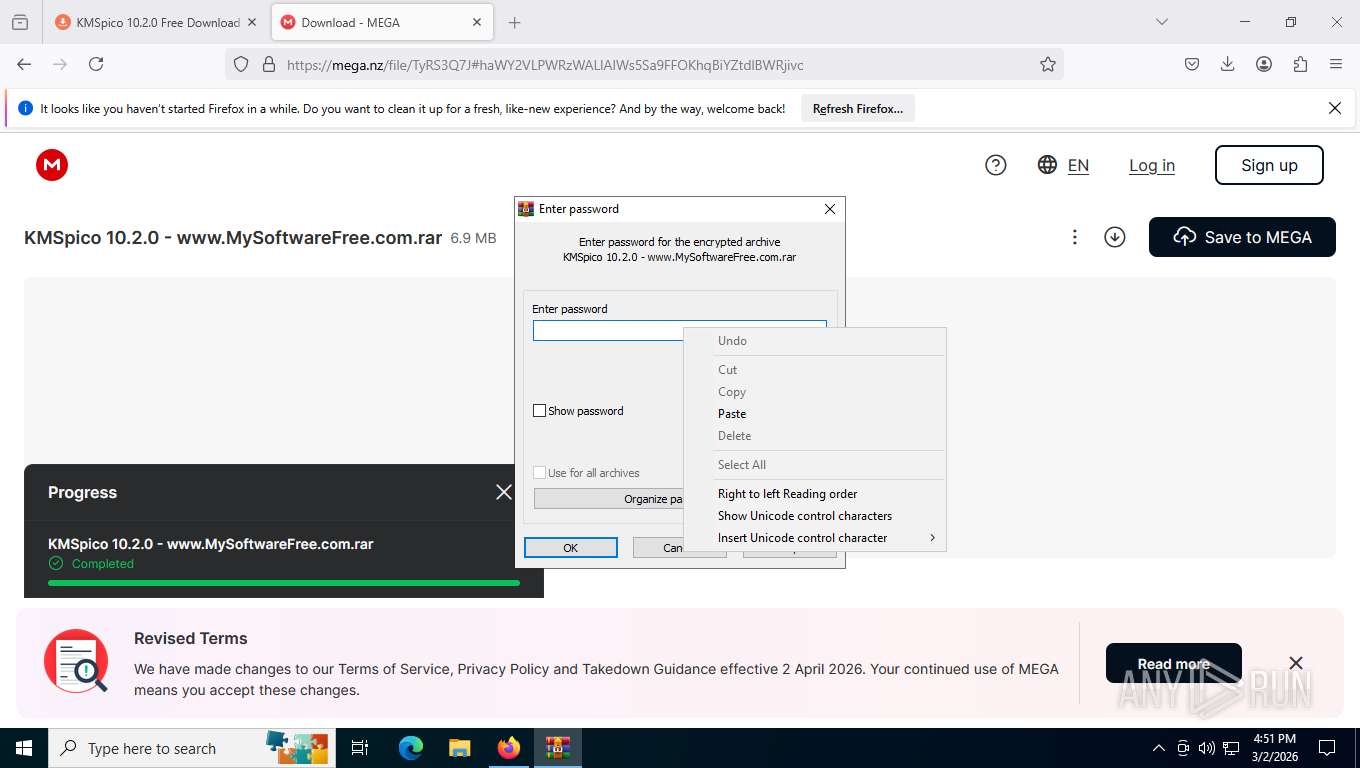
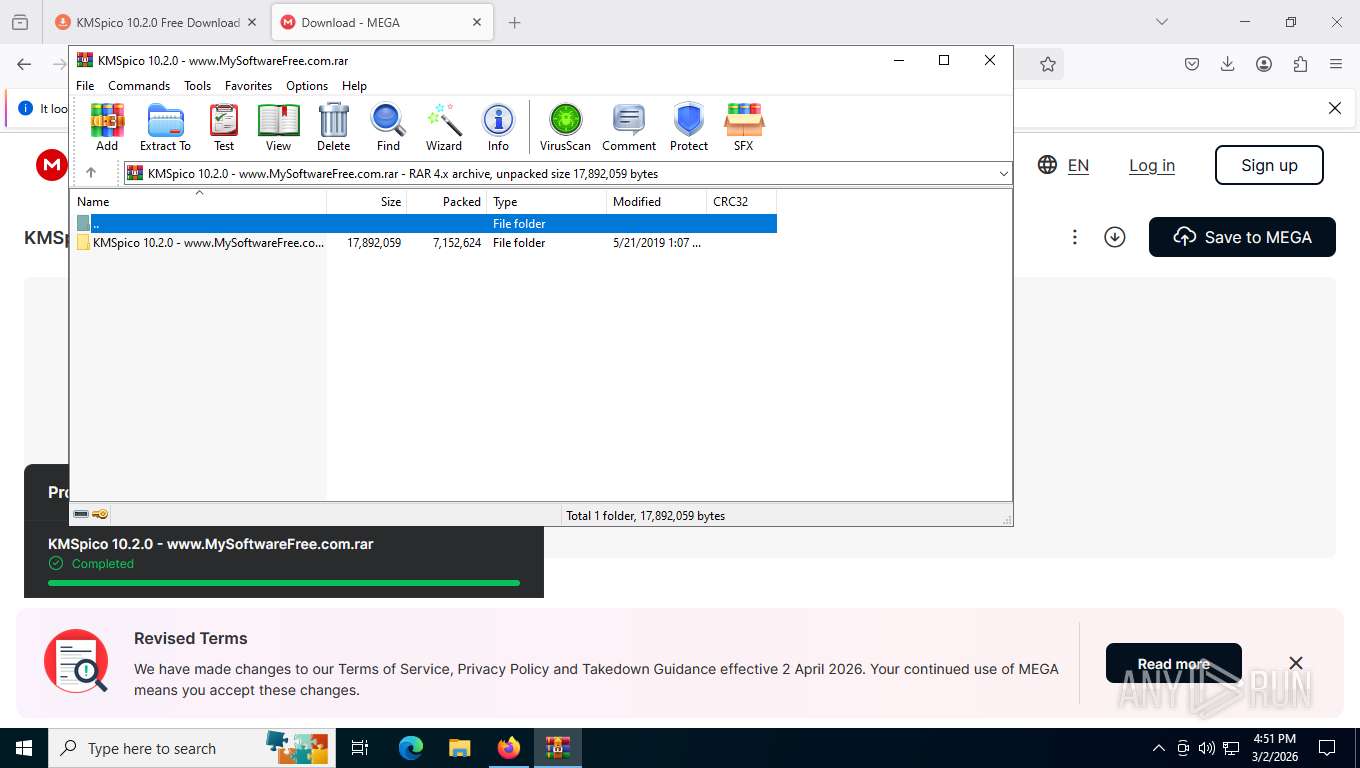
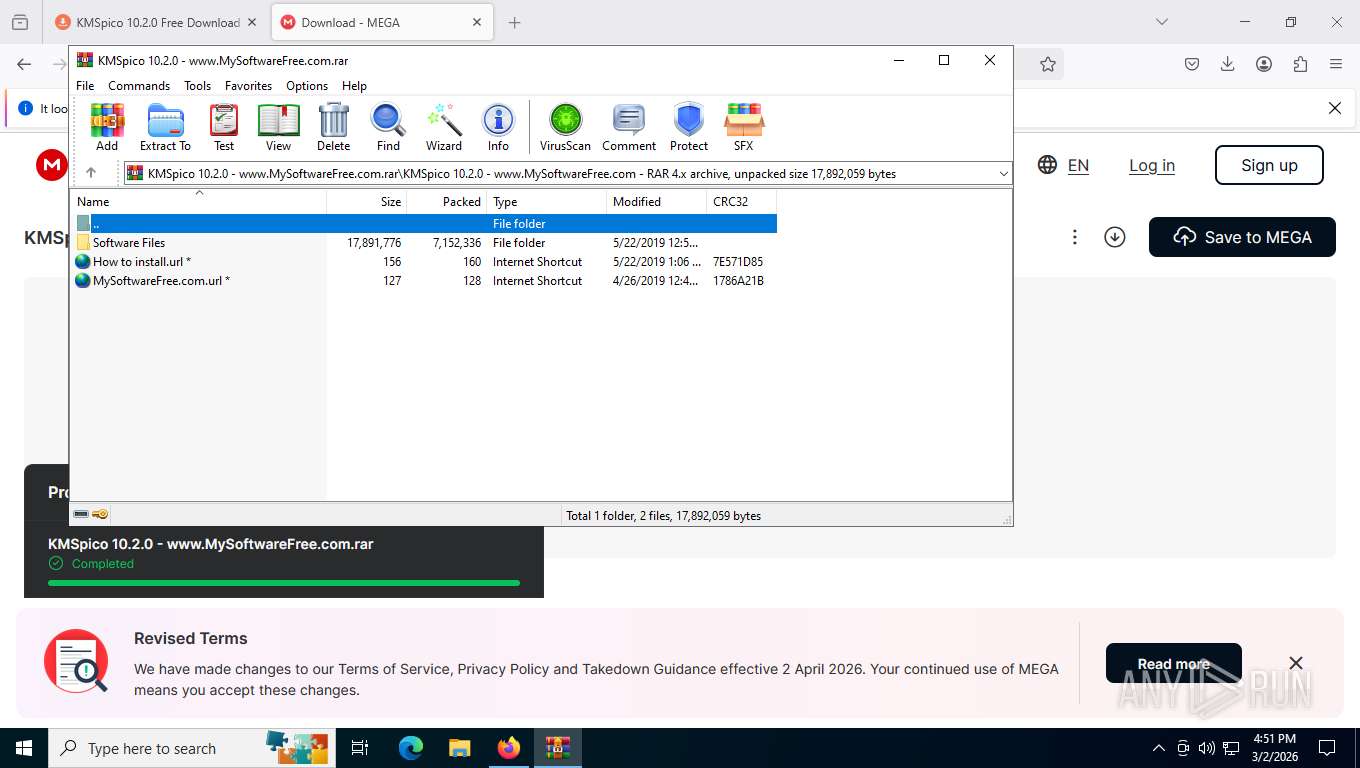
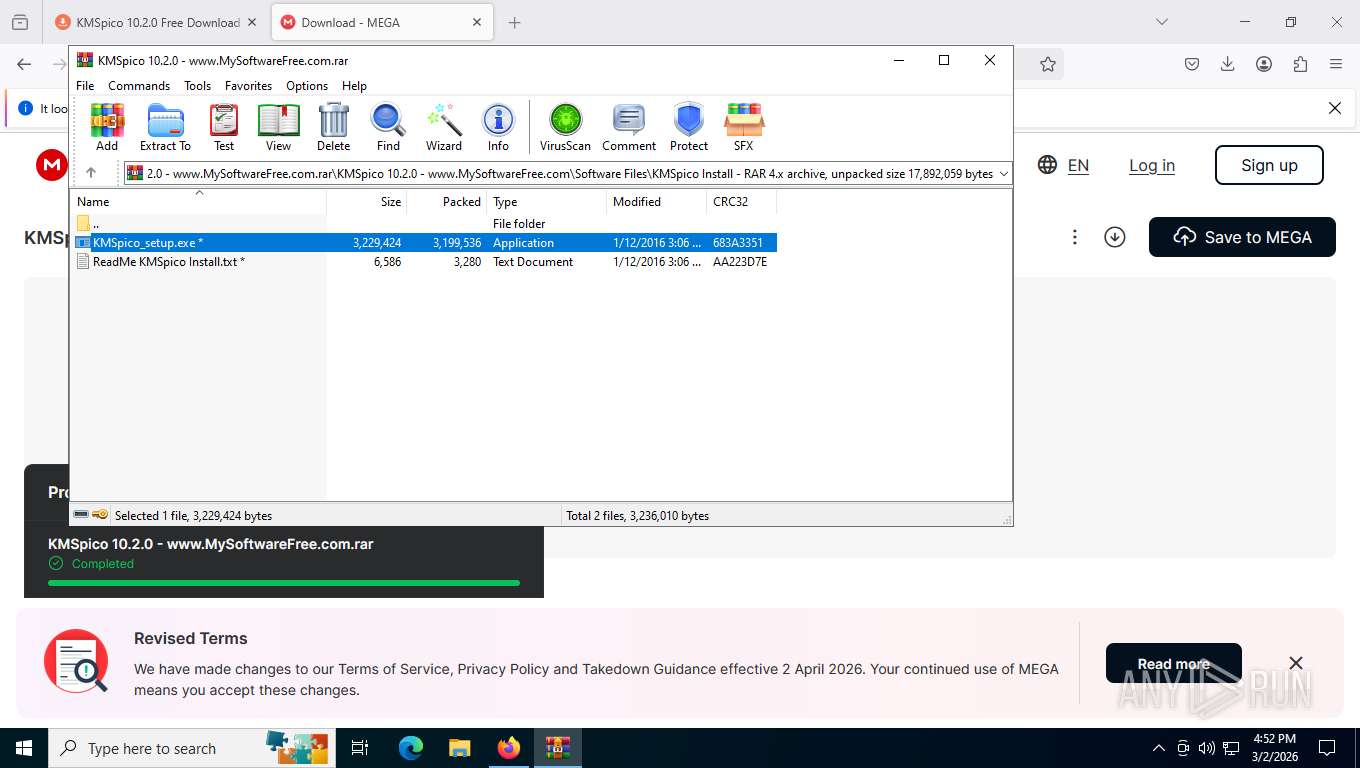
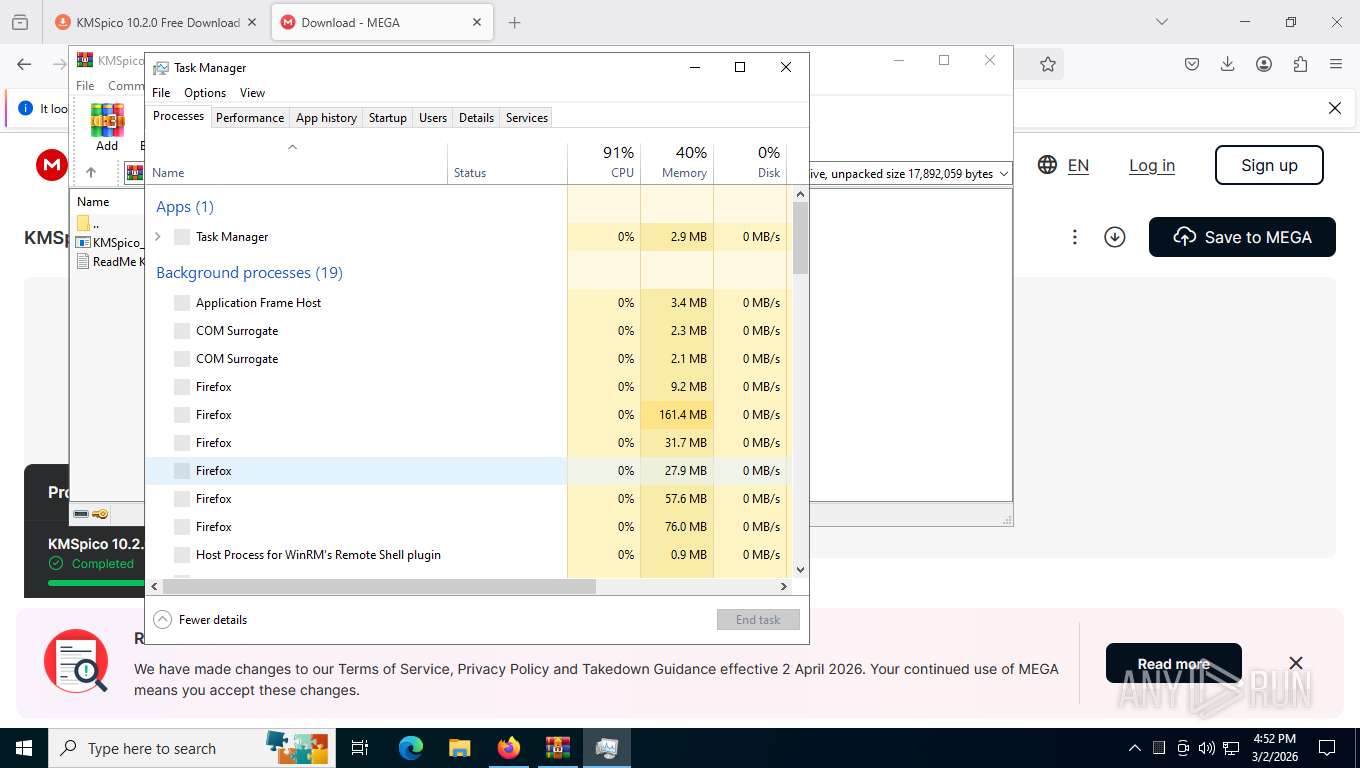
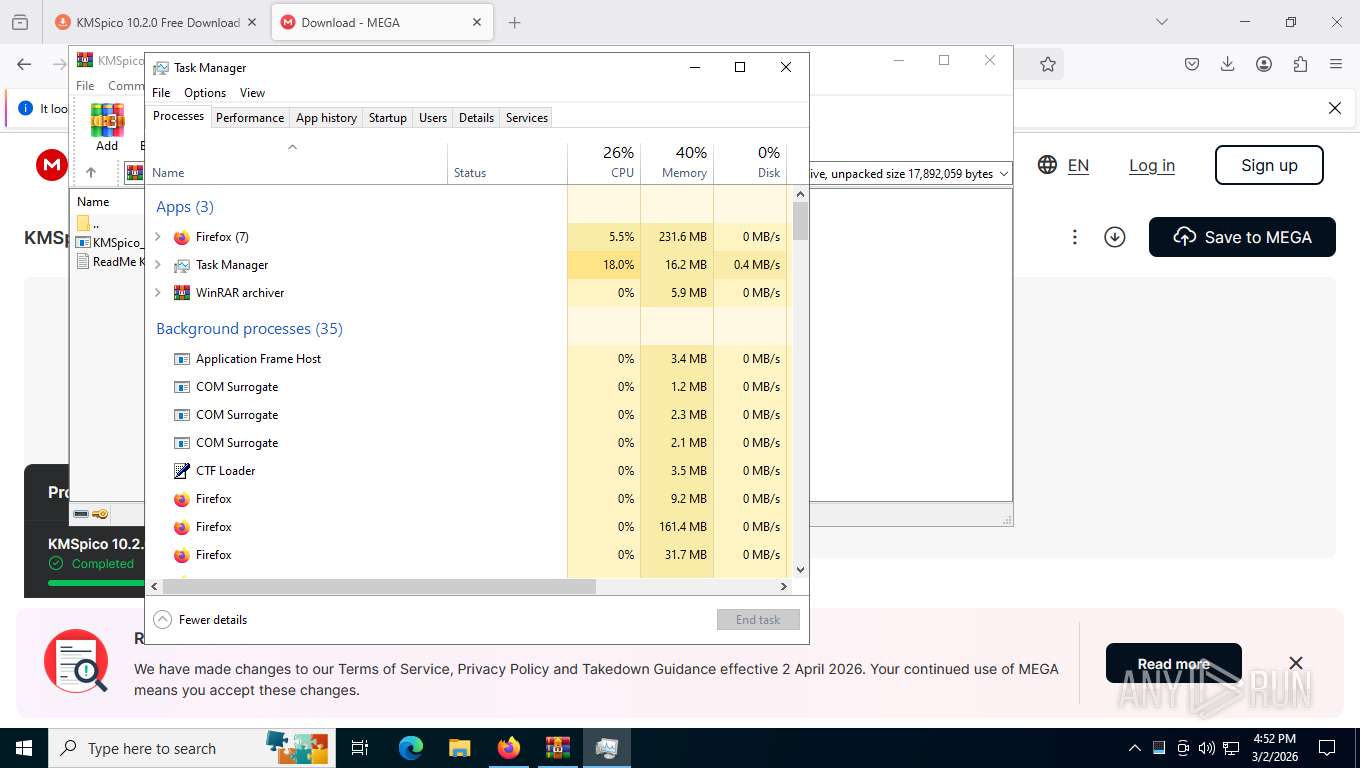
Manual execution by a user
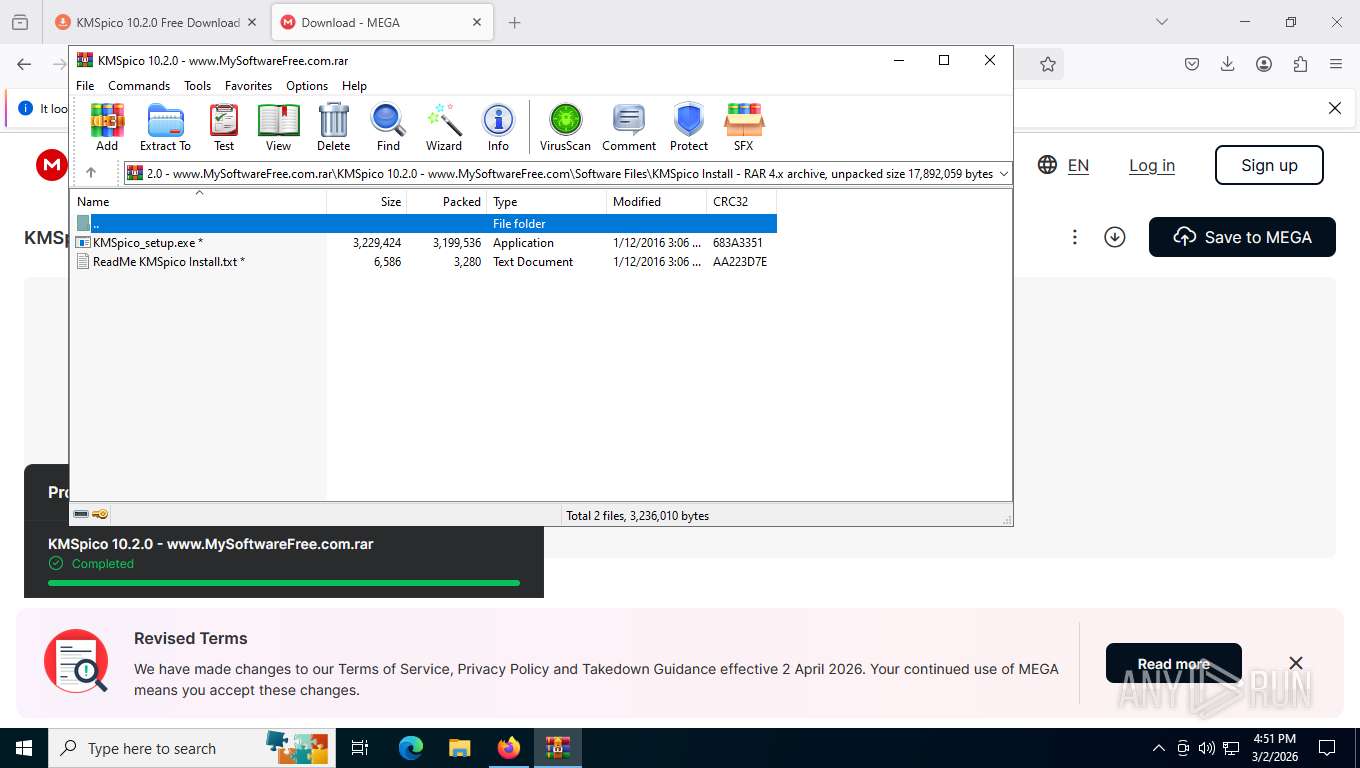
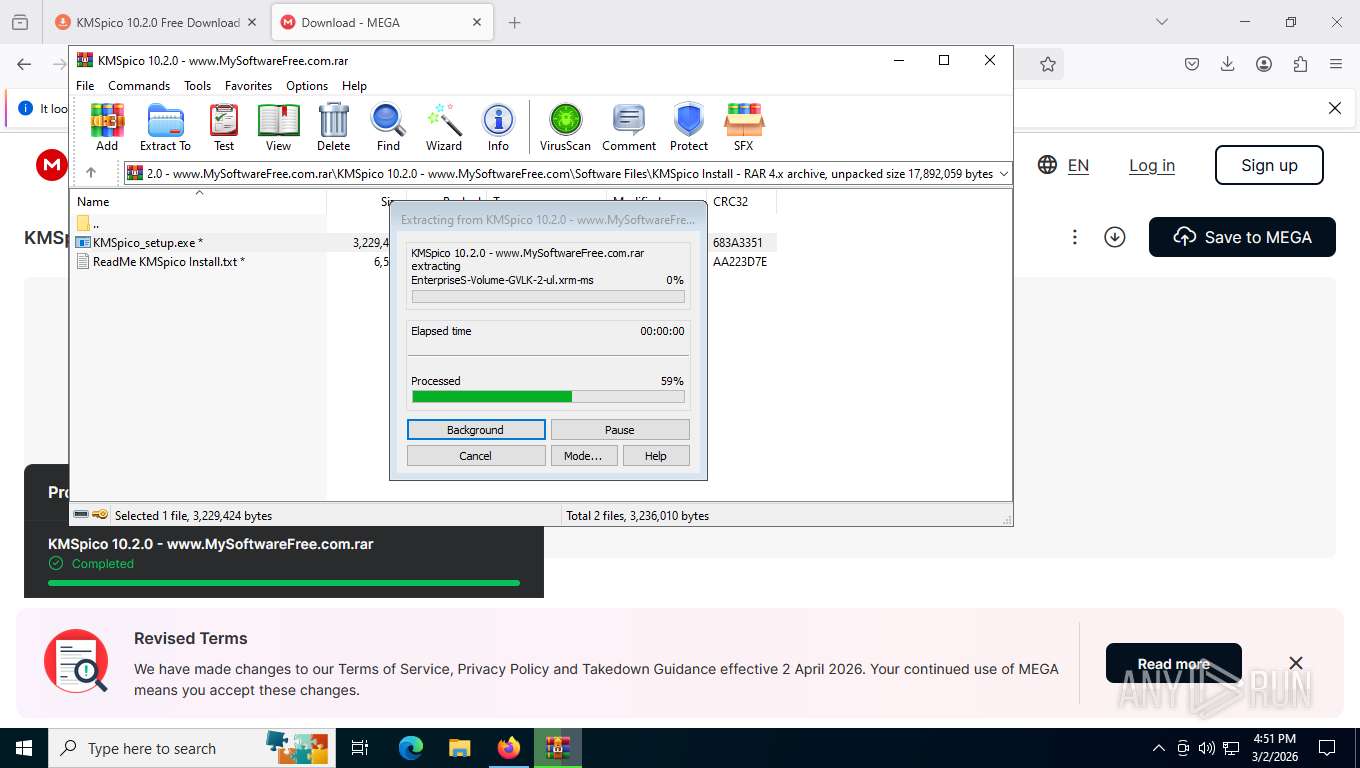
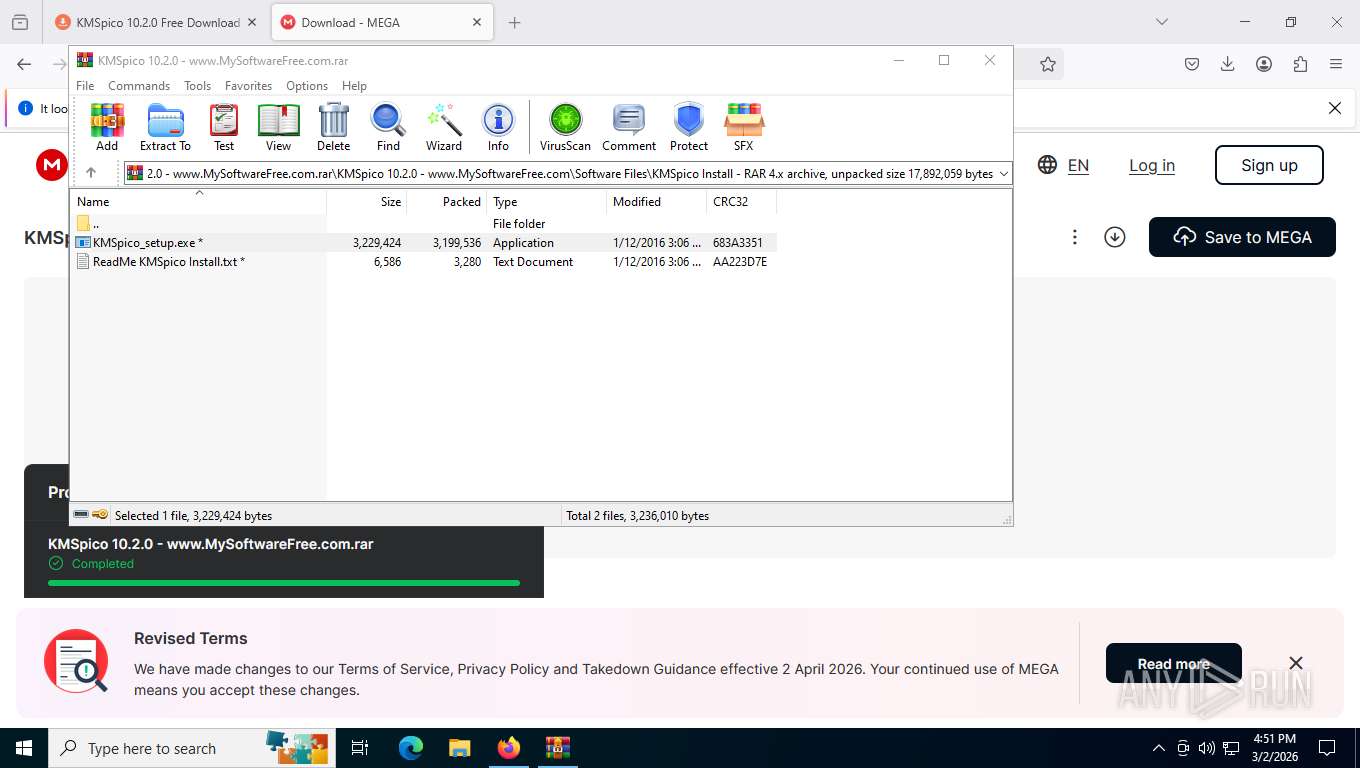
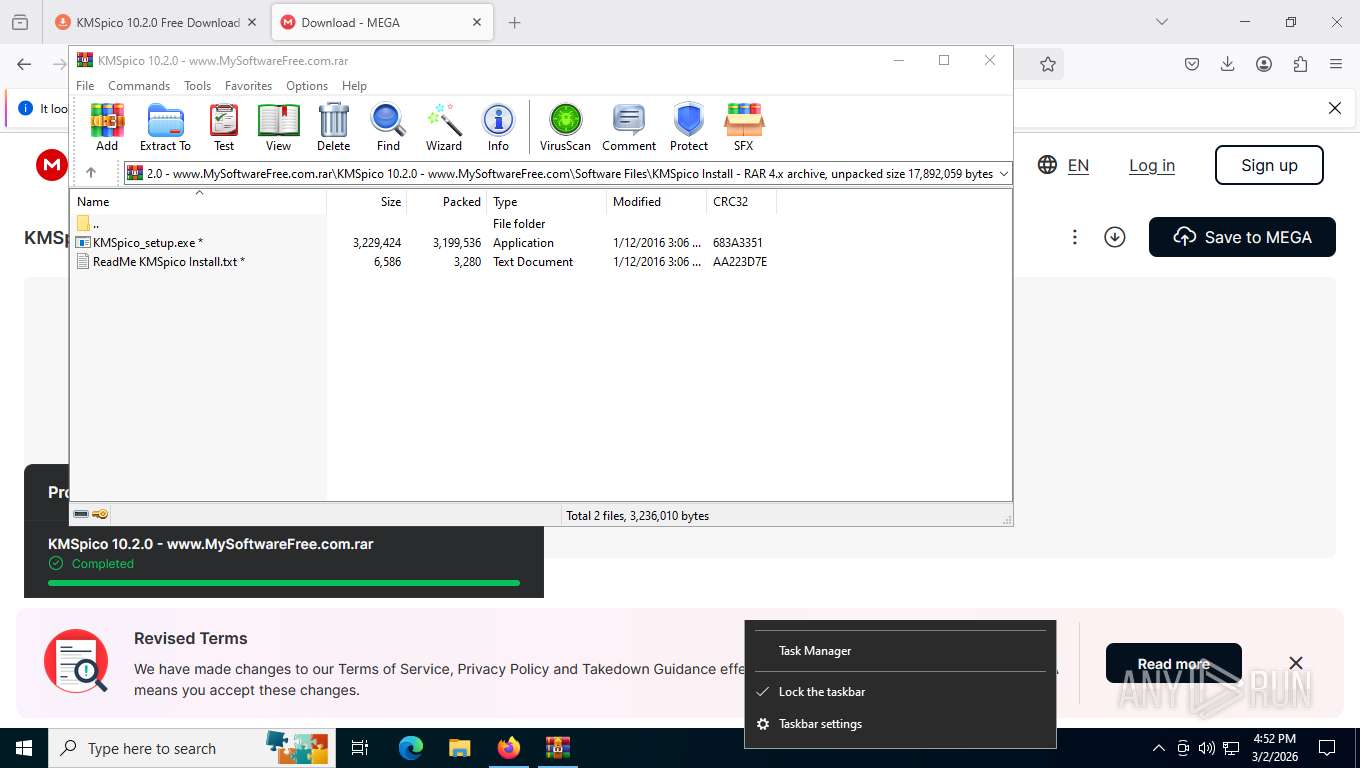
- WinRAR.exe (PID: 7244)
- Taskmgr.exe (PID: 8608)
- Taskmgr.exe (PID: 9164)
Checks supported languages
- KMSpico_setup.exe (PID: 8288)
- KMSpico_setup.tmp (PID: 6044)
- KMSpico_setup.exe (PID: 5140)
- KMSpico_setup.tmp (PID: 8076)
- KMSELDI.exe (PID: 8004)
- UninsHs.exe (PID: 2328)
- SECOH-QAD.exe (PID: 8284)
- AutoPico.exe (PID: 3112)
Reads the computer name
- KMSpico_setup.tmp (PID: 6044)
- KMSpico_setup.tmp (PID: 8076)
- KMSELDI.exe (PID: 8004)
- AutoPico.exe (PID: 3112)
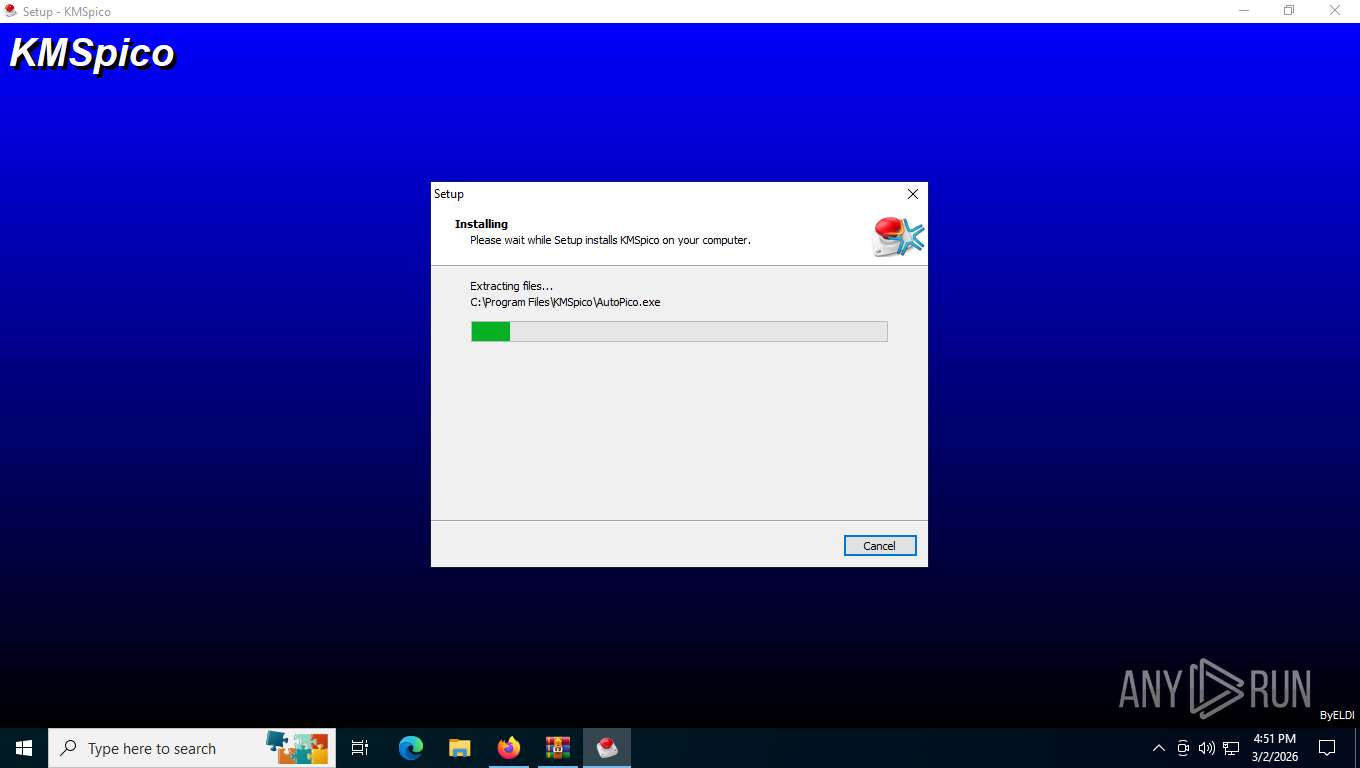
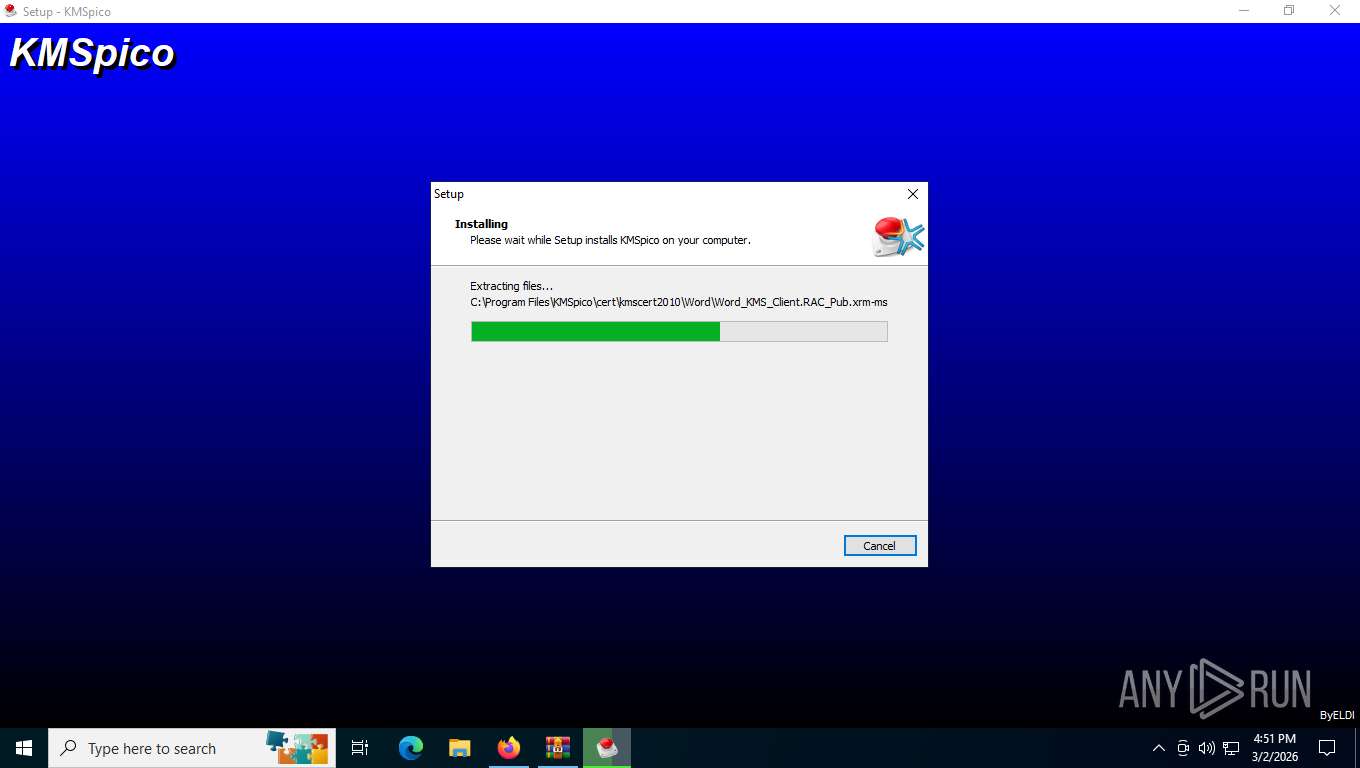
Create files in a temporary directory
- KMSpico_setup.exe (PID: 8288)
- KMSpico_setup.exe (PID: 5140)
- KMSpico_setup.tmp (PID: 8076)
Launching a file from the Downloads directory
- firefox.exe (PID: 4504)
Reads security settings of Internet Explorer
- KMSpico_setup.tmp (PID: 6044)
- WinRAR.exe (PID: 7244)
- Taskmgr.exe (PID: 9164)
Process checks computer location settings
- KMSpico_setup.tmp (PID: 6044)
Detects InnoSetup installer (YARA)
- KMSpico_setup.exe (PID: 8288)
- KMSpico_setup.tmp (PID: 6044)
- KMSpico_setup.tmp (PID: 8076)
- KMSpico_setup.exe (PID: 5140)
Creates a software uninstall entry
- KMSpico_setup.tmp (PID: 8076)
Compiled with Borland Delphi (YARA)
- KMSpico_setup.tmp (PID: 8076)
- KMSpico_setup.tmp (PID: 6044)
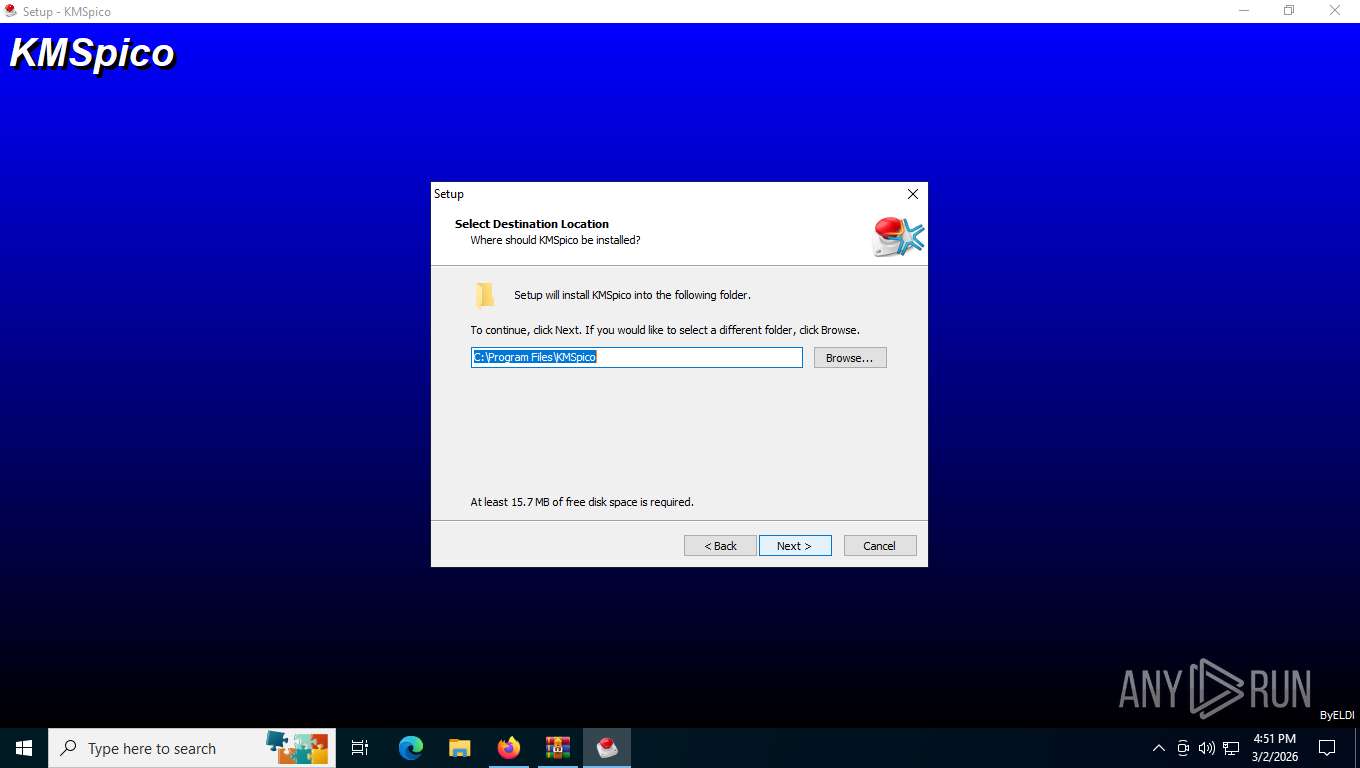
Creates files in the program directory
- KMSpico_setup.tmp (PID: 8076)
- KMSELDI.exe (PID: 8004)
- AutoPico.exe (PID: 3112)
Launching a file from Task Scheduler
- cmd.exe (PID: 5988)
Reads Environment values
- KMSELDI.exe (PID: 8004)
- AutoPico.exe (PID: 3112)
Reads the machine GUID from the registry
- KMSELDI.exe (PID: 8004)
- AutoPico.exe (PID: 3112)
Reads product name
- KMSELDI.exe (PID: 8004)
- AutoPico.exe (PID: 3112)
Reads Microsoft Office registry keys
- KMSELDI.exe (PID: 8004)
- AutoPico.exe (PID: 3112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
184
Monitored processes
38
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2000 | "C:\WINDOWS\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Service.cmd"" | C:\Windows\System32\cmd.exe | — | KMSpico_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
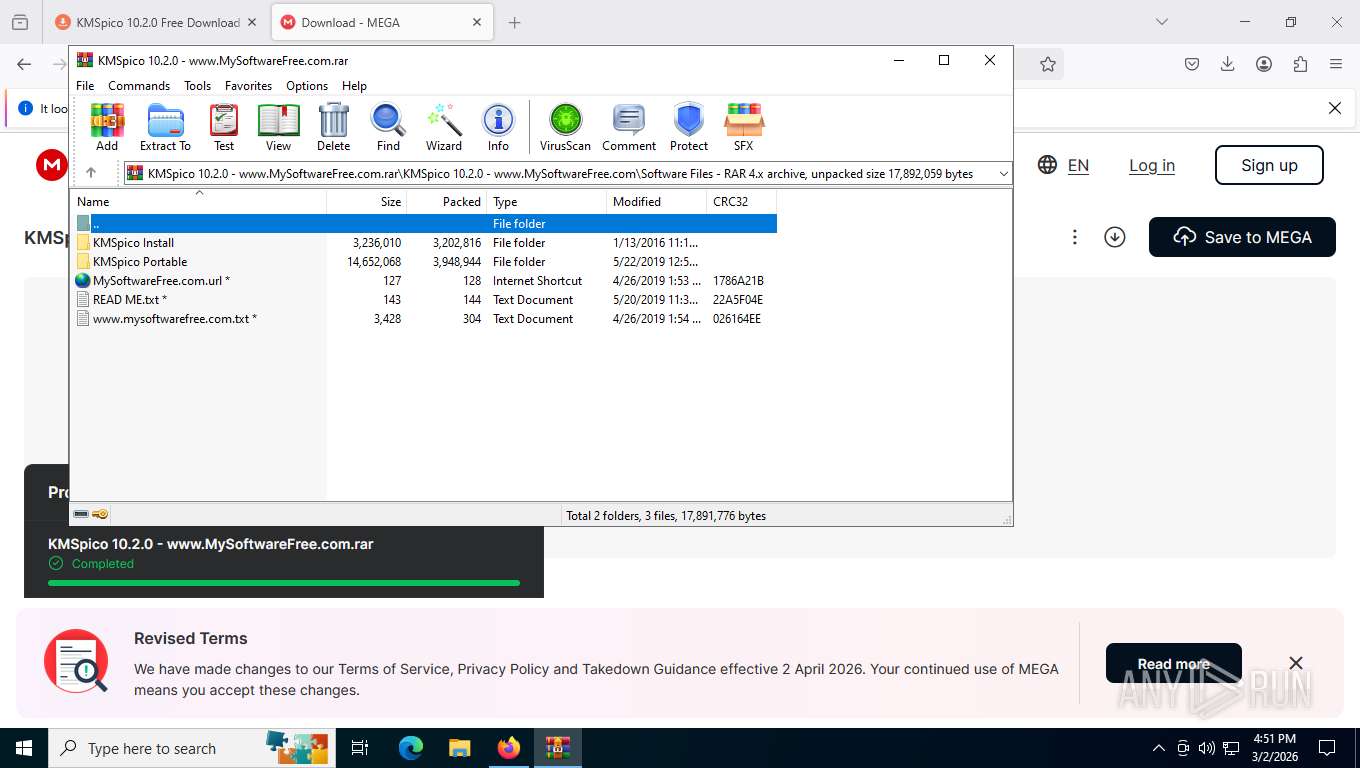
| 2328 | "C:\Program Files\KMSpico\UninsHs.exe" /r0=KMSpico,default,C:\Users\admin\AppData\Local\Temp\Rar$EXb7244.42671\KMSpico 10.2.0 - www.MySoftwareFree.com\Software Files\KMSpico Install\KMSpico_setup.exe | C:\Program Files\KMSpico\UninsHs.exe | — | KMSpico_setup.tmp | |||||||||||
User: admin Company: Han-soft Integrity Level: HIGH Description: Uninstall for InnoSetup by Han-soft Exit code: 0 Version: 2.1.0.283 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://mysoftwarefree.com/kmspico-10-2-0-free-download/ | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 3112 | "C:\Program Files\KMSpico\AutoPico.exe" /silent | C:\Program Files\KMSpico\AutoPico.exe | KMSpico_setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: AutoPico Exit code: 0 Version: 16.1.0.0 Modules
| |||||||||||||||
| 4504 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://mysoftwarefree.com/kmspico-10-2-0-free-download/ | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 4684 | SCHTASKS /Create /TN "AutoPico Daily Restart" /TR "'C:\Program Files\KMSpico\AutoPico.exe' /silent" /SC DAILY /ST 23:59:59 /RU "NT AUTHORITY\SYSTEM" /RL Highest /F | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4840 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4000 -prefsLen 45170 -prefMapHandle 4004 -prefMapSize 273045 -jsInitHandle 4008 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3976 -initialChannelId {a6fda88b-e015-4fd0-aeb5-1065ee4f0aef} -parentPid 4504 -crashReporter "\\.\pipe\gecko-crash-server-pipe.4504" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 5 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 4956 | sc create "Service KMSELDI" binPath= "C:\Program Files\KMSpico\Service_KMS.exe" type= own error= normal start= auto DisplayName= "Service KMSELDI" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5140 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb7244.42671\KMSpico 10.2.0 - www.MySoftwareFree.com\Software Files\KMSpico Install\KMSpico_setup.exe" /SPAWNWND=$60410 /NOTIFYWND=$A02F8 | C:\Users\admin\AppData\Local\Temp\Rar$EXb7244.42671\KMSpico 10.2.0 - www.MySoftwareFree.com\Software Files\KMSpico Install\KMSpico_setup.exe | KMSpico_setup.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: KMSpico Setup Exit code: 0 Version: 10.2.0 Modules
| |||||||||||||||
Total events
13 110
Read events
13 031
Write events
73
Delete events
6
Modification events
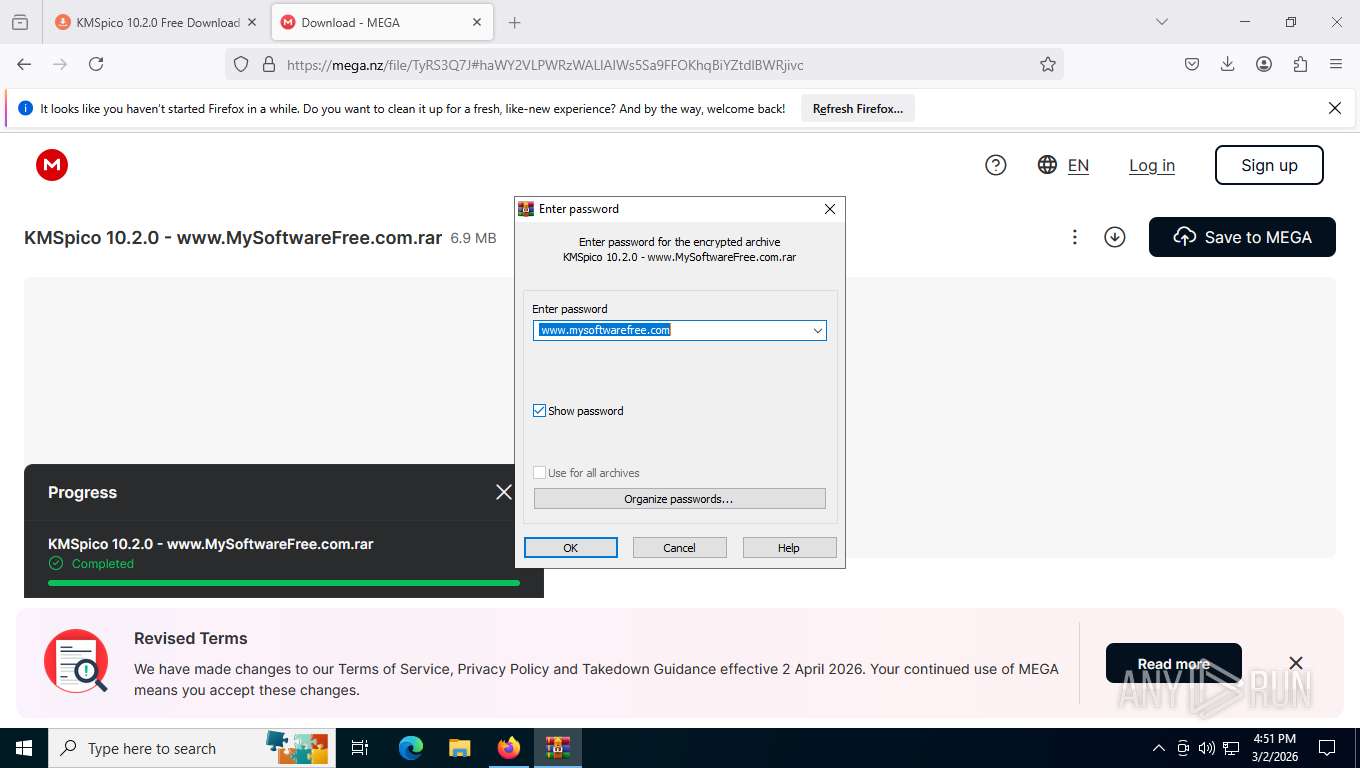
| (PID) Process: | (7244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (7244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (7244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\KMSpico 10.2.0 - www.MySoftwareFree.com.rar | |||
| (PID) Process: | (7244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7244) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-10046 |
Value: Internet Shortcut | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
1 478
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4504 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4504 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:2780183D3F54CEC0A6D7522516D206EA | SHA256:C0BD411E96DD4AA4717850314CAB7B34AD41FA86006F35ECD043365A6AA55C31 | |||
| 4504 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4504 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.contile.json.tmp | binary | |
MD5:A723C5CE8851DCA10919049E11343339 | SHA256:C3D596506EC0AB596116E4AA486A41E33E1DF009599C75E0E96F80BC294EAEA3 | |||
| 4504 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:3134ED3F12E4F4F8643DB90043B0FD7B | SHA256:26E4F122034D7A03F6DA0E707799B09CBEEBDAF8D7A3133A1F7BD894AC72EEA1 | |||
| 4504 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | binary | |
MD5:4C194C56EAB54980F1674D34E9765275 | SHA256:90B5168BC7798FA6B5B259E4CDEC2BF8AE12861E58A2FE47433161EA6F5AA2C3 | |||
| 4504 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 4504 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 4504 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.contile.json | binary | |
MD5:A723C5CE8851DCA10919049E11343339 | SHA256:C3D596506EC0AB596116E4AA486A41E33E1DF009599C75E0E96F80BC294EAEA3 | |||
| 4504 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\protections.sqlite-journal | binary | |
MD5:3C6E9D5FA510DF162D53C954EE559820 | SHA256:2A2FBC945BFF0A4983A8961CBFABEFBE0632397808BE7DD904732E4034FEBE83 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
686
TCP/UDP connections
165
DNS requests
205
Threats
43
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4504 | firefox.exe | GET | 101 | 34.107.243.93:443 | https://push.services.mozilla.com/ | unknown | — | — | unknown |
4504 | firefox.exe | POST | 200 | 142.251.140.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
4504 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2026-03-08-09-54-23.chain | unknown | binary | 5.18 Kb | unknown |
4504 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2026-03-28-10-13-31.chain | unknown | binary | 5.18 Kb | unknown |
4504 | firefox.exe | POST | 200 | 142.251.140.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
4504 | firefox.exe | GET | 200 | 34.160.144.191:443 | https://content-signature-2.cdn.mozilla.net/g/chains/202402/remote-settings.content-signature.mozilla.org-2026-03-28-10-13-31.chain | unknown | binary | 5.18 Kb | unknown |
4504 | firefox.exe | GET | 200 | 142.250.187.202:443 | https://safebrowsing.googleapis.com/v4/threatListUpdates:fetch?$ct=application/x-protobuf&key=AIzaSyC7jsptDS3am4tPx4r3nxis7IMjBc5Dovo&$httpMethod=POST&$req=ChUKE25hdmNsaWVudC1hdXRvLWZmb3gaJwgFEAEaGwoNCAUQBhgBIgMwMDEwARDTgx4aAhgJALrcyCICIAIoARonCAEQARobCg0IARAGGAEiAzAwMTABEL2qExoCGAnDi_-vIgIgAigBGicIAxABGhsKDQgDEAYYASIDMDAxMAEQ4qITGgIYCUbgbD4iAiACKAEaJwgHEAEaGwoNCAcQBhgBIgMwMDEwARCEshMaAhgJ9TW0WSICIAIoARolCAkQARoZCg0ICRAGGAEiAzAwMTABECQaAhgJRoTu3yICIAIoAQ== | unknown | binary | 6.69 Mb | whitelisted |
508 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
508 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4504 | firefox.exe | GET | 200 | 151.101.193.91:443 | https://firefox.settings.services.mozilla.com/v1/buckets/monitor/collections/changes/changeset?collection=url-parser-default-unknown-schemes-interventions&bucket=main&_expected=0 | unknown | binary | 274 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
508 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.138:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4504 | firefox.exe | 151.101.193.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
4504 | firefox.exe | 188.114.96.3:443 | mysoftwarefree.com | CLOUDFLARENET | US | whitelisted |
4504 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
4504 | firefox.exe | 151.101.1.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
mozilla.map.fastly.net |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
mysoftwarefree.com |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2232 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2232 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2232 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
508 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2232 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Domain Associated with Malware Distribution (ukankingwithea .com) |
2232 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Domain Associated with Malware Distribution (ghabovethec .info) |
4504 | firefox.exe | Attempted Information Leak | SUSPICIOUS [ANY.RUN] FingerprintJS Usage Observed in HTTP response |
4504 | firefox.exe | Attempted Information Leak | SUSPICIOUS [ANY.RUN] FingerprintJS Usage Observed in HTTP response |
2232 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2232 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |