| File name: | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw |
| Full analysis: | https://app.any.run/tasks/55eead9d-dab1-43fc-9e95-13b74c604dbb |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 06:20:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9E3CE08750B875EAC894F245B0271FDC |
| SHA1: | C29E78099CDF3A3A8C2E23FE75F38BBABC631D92 |
| SHA256: | 825A5E768DF385AD651B16256755A63D91FB710E46296D3B0D05E9DF7EEEDAFF |
| SSDEEP: | 49152:wy+Sh4r+VNPvJ3x19XX3QZcBJwHjniXZsILcKvQ1aB:B+Sh4revJB/XX3QZkqDiXWXKI1a |
MALICIOUS
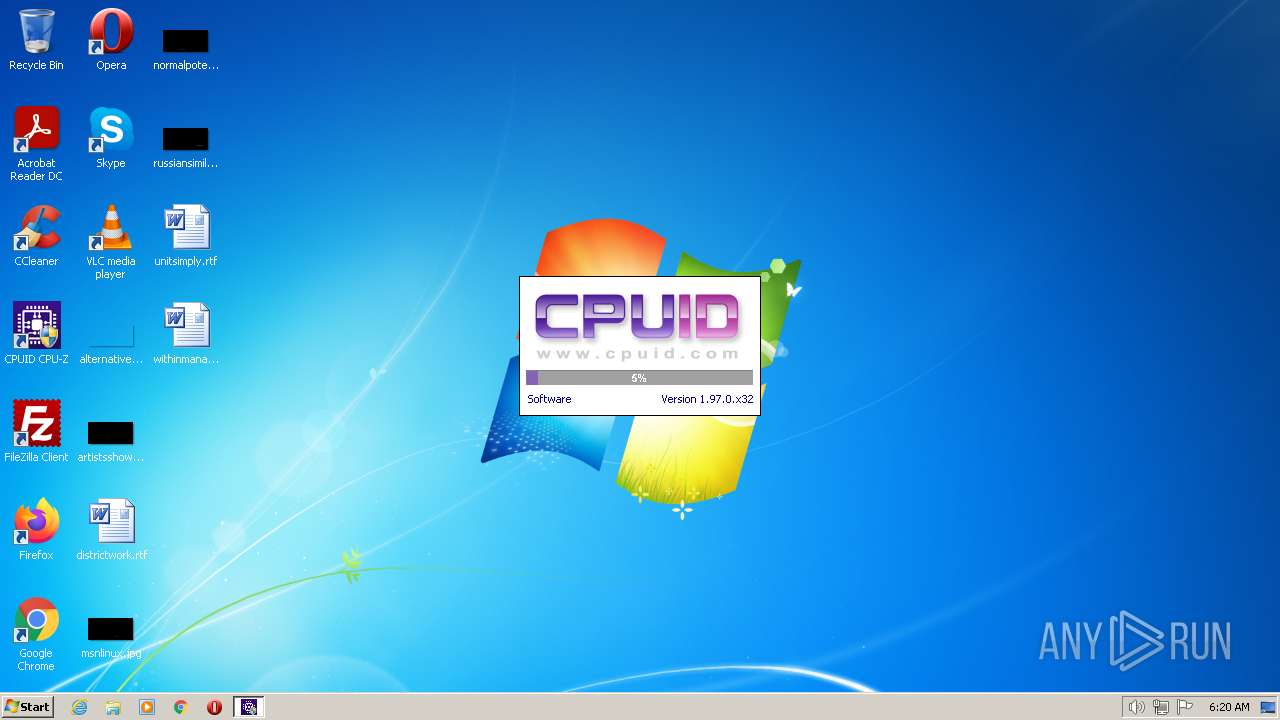
Drops the executable file immediately after the start
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 3608)
- cpuz.exe (PID: 3096)
Application was dropped or rewritten from another process
- cpuz.exe (PID: 3096)
- cpuz.exe (PID: 2656)
SUSPICIOUS
Reads the Windows owner or organization settings
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 3608)
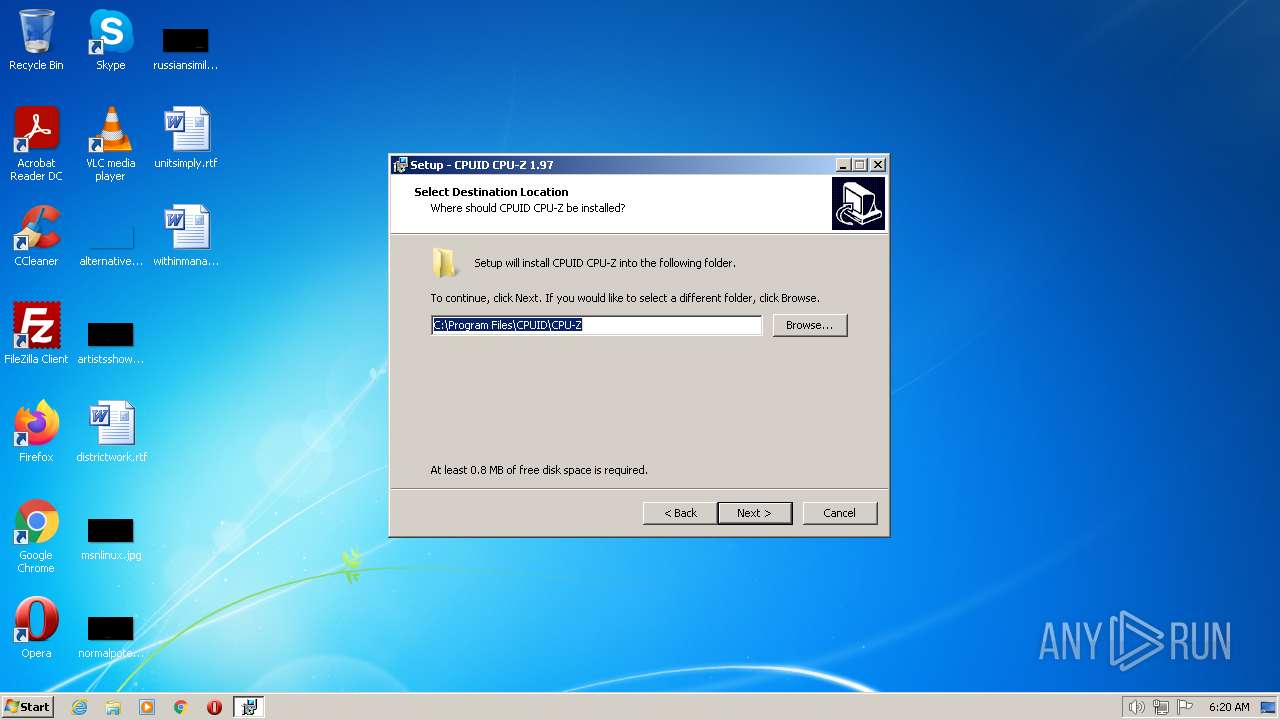
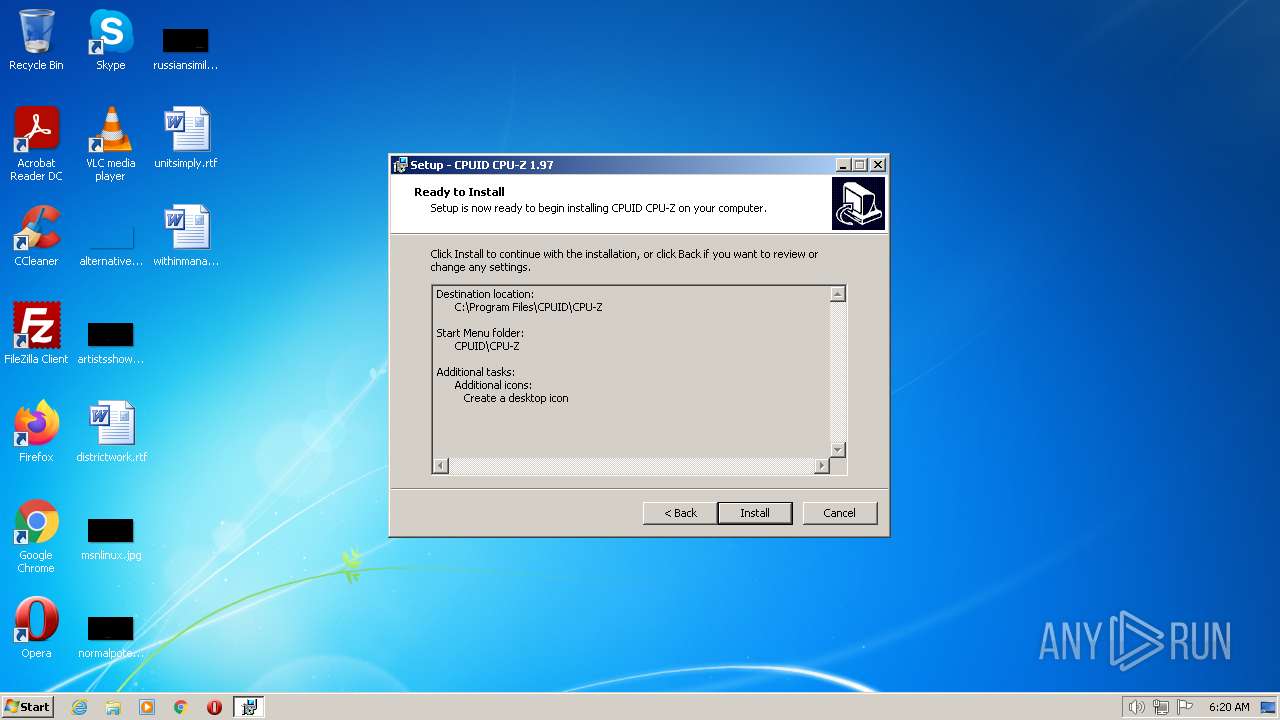
Creates a directory in Program Files
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 3608)
Drops a file with too old compile date
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 3608)
Executable content was dropped or overwritten
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 3608)
- cpuz.exe (PID: 3096)
Checks Windows Trust Settings
- cpuz.exe (PID: 3096)
Reads the Internet Settings
- cpuz.exe (PID: 3096)
Reads security settings of Internet Explorer
- cpuz.exe (PID: 3096)
Adds/modifies Windows certificates
- cpuz.exe (PID: 3096)
Reads settings of System Certificates
- cpuz.exe (PID: 3096)
INFO
Checks supported languages
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 2284)
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 3608)
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe (PID: 3336)
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe (PID: 2056)
- cpuz.exe (PID: 3096)
Reads the computer name
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 2284)
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 3608)
- cpuz.exe (PID: 3096)
Application was dropped or rewritten from another process
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 2284)
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 3608)
Creates files in the program directory
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 3608)
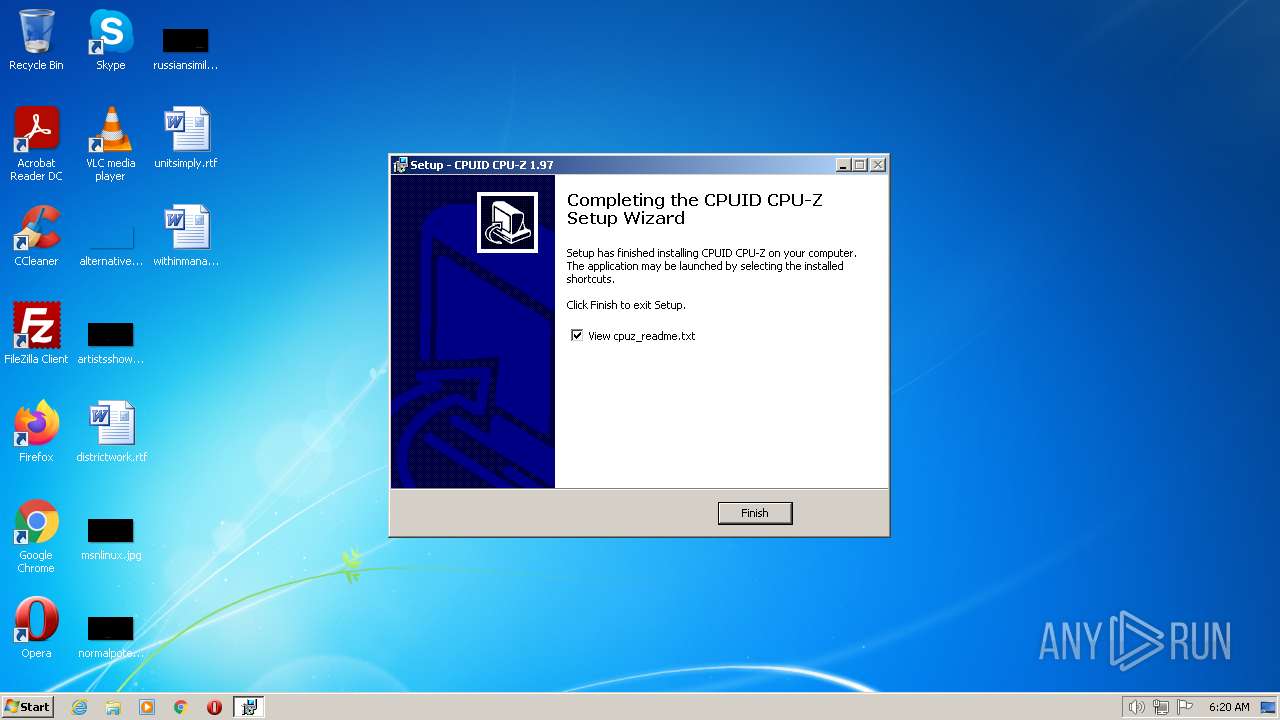
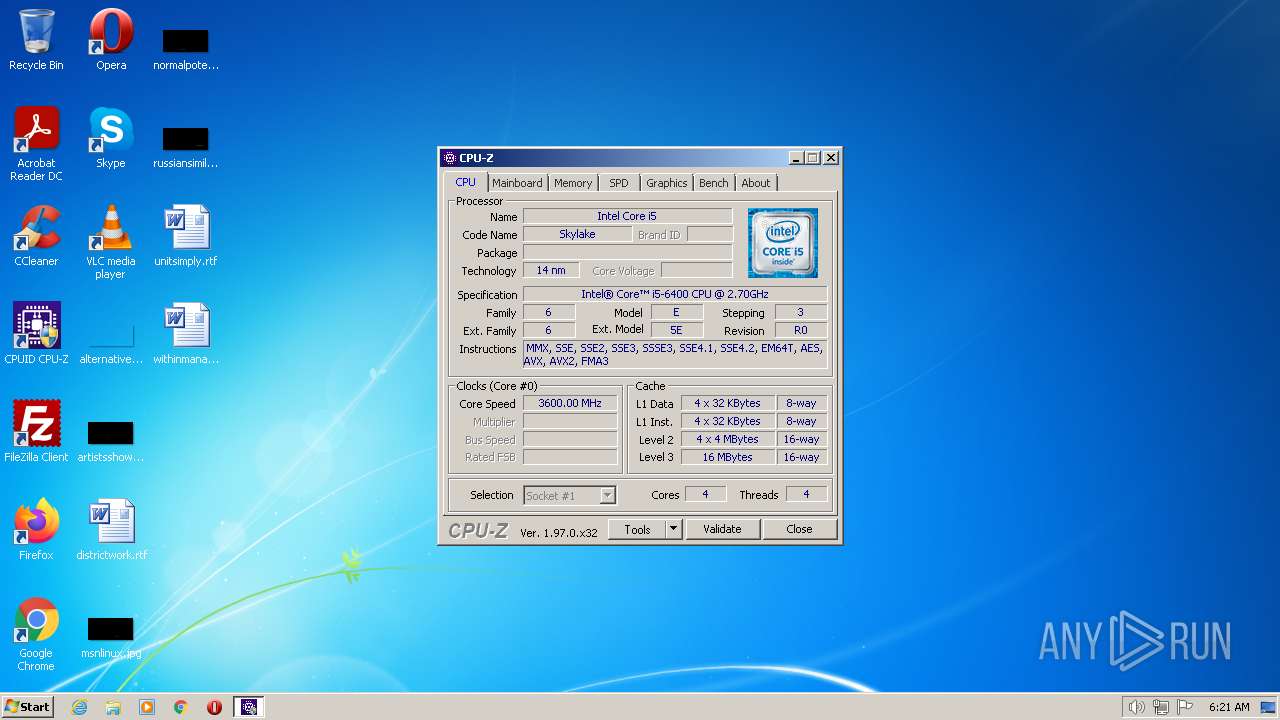
Manual execution by a user
- cpuz.exe (PID: 2656)
- cpuz.exe (PID: 3096)
Creates a software uninstall entry
- MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp (PID: 3608)
Drops a file that was compiled in debug mode
- cpuz.exe (PID: 3096)
Reads Environment values
- cpuz.exe (PID: 3096)
Checks proxy server information
- cpuz.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 1992-Jun-19 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
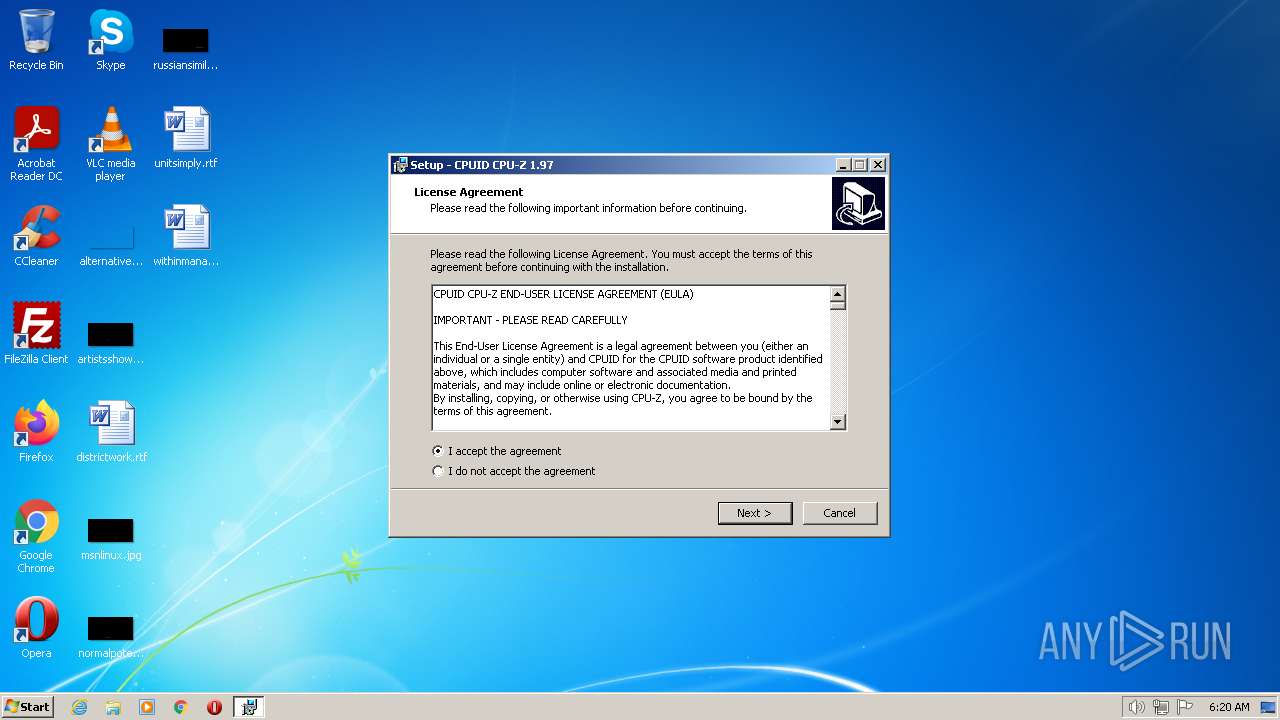
| CompanyName: | CPUID, Inc. |
| FileDescription: | CPUID CPU-Z Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | CPUID CPU-Z |
| ProductVersion: | 1.97 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 80 |
| e_cp: | 2 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | 15 |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | 26 |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 256 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 8 |
| TimeDateStamp: | 1992-Jun-19 22:22:17 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 4096 | 41480 | 41984 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60167 |
DATA | 49152 | 592 | 1024 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.77135 |
BSS | 53248 | 3732 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.idata | 57344 | 2428 | 2560 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 61440 | 8 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.rdata | 65536 | 24 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 69632 | 2336 | 0 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | |
.rsrc | 73728 | 11264 | 11264 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.58902 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.25755 | 296 | UNKNOWN | Dutch - Netherlands | RT_ICON |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
advapi32.dll (#2) |
comctl32.dll |
kernel32.dll |
kernel32.dll (#2) |
oleaut32.dll |
user32.dll |
user32.dll (#2) |
Total processes
48
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2056 | "C:\Users\admin\AppData\Local\Temp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe" | C:\Users\admin\AppData\Local\Temp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe | — | Explorer.EXE | |||||||||||
User: admin Company: CPUID, Inc. Integrity Level: MEDIUM Description: CPUID CPU-Z Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Local\Temp\is-NQG7P.tmp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp" /SL5="$50198,1823662,58368,C:\Users\admin\AppData\Local\Temp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe" | C:\Users\admin\AppData\Local\Temp\is-NQG7P.tmp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | — | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\CPUID\CPU-Z\cpuz.exe" | C:\Program Files\CPUID\CPU-Z\cpuz.exe | — | Explorer.EXE | |||||||||||
User: admin Company: CPUID Integrity Level: MEDIUM Description: CPU-Z Application Exit code: 3221226540 Version: 1, 9, 7, 0 Modules
| |||||||||||||||
| 3096 | "C:\Program Files\CPUID\CPU-Z\cpuz.exe" | C:\Program Files\CPUID\CPU-Z\cpuz.exe | Explorer.EXE | ||||||||||||
User: admin Company: CPUID Integrity Level: HIGH Description: CPU-Z Application Exit code: 0 Version: 1, 9, 7, 0 Modules
| |||||||||||||||
| 3336 | "C:\Users\admin\AppData\Local\Temp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe" /SPAWNWND=$601B0 /NOTIFYWND=$50198 | C:\Users\admin\AppData\Local\Temp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | ||||||||||||
User: admin Company: CPUID, Inc. Integrity Level: HIGH Description: CPUID CPU-Z Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3608 | "C:\Users\admin\AppData\Local\Temp\is-AHPCJ.tmp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp" /SL5="$601C8,1823662,58368,C:\Users\admin\AppData\Local\Temp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe" /SPAWNWND=$601B0 /NOTIFYWND=$50198 | C:\Users\admin\AppData\Local\Temp\is-AHPCJ.tmp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
7 028
Read events
6 936
Write events
86
Delete events
6
Modification events
| (PID) Process: | (3608) MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 180E000072F566DB3A09D901 | |||
| (PID) Process: | (3608) MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 8C0347F38C93799CC79A4E945B54D88728B6F980EE923F99E7DF4A8C1BD835CA | |||
| (PID) Process: | (3608) MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3608) MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\CPUID\CPU-Z\cpuz.exe | |||
| (PID) Process: | (3608) MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 4BA3D99E853550BBF76FBF9BC645FCD54CF9138E767748C6CF4869FC292CDCEE | |||
| (PID) Process: | (3608) MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\CPUID\CPU-Z |
| Operation: | write | Name: | PATH |
Value: C:\Program Files\CPUID\CPU-Z | |||
| (PID) Process: | (3608) MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\CPUID\CPU-Z |
| Operation: | write | Name: | PRODUCT_NAME |
Value: CPUID CPU-Z | |||
| (PID) Process: | (3608) MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\CPUID\CPU-Z |
| Operation: | write | Name: | VERSION |
Value: 1.97 | |||
| (PID) Process: | (3608) MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CPUID CPU-Z_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (a) | |||
| (PID) Process: | (3608) MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CPUID CPU-Z_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\CPUID\CPU-Z | |||
Executable files
7
Suspicious files
7
Text files
8
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3608 | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CPUID\CPU-Z\CPU-Z.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3608 | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | C:\Users\Public\Desktop\CPUID CPU-Z.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3608 | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CPUID\CPU-Z\Uninstall CPU-Z.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3608 | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | C:\Program Files\CPUID\CPU-Z\unins000.dat | dat | |
MD5:— | SHA256:— | |||
| 3608 | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CPUID\CPU-Z\Edit CPU-Z Config File.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3096 | cpuz.exe | C:\Windows\temp\cpuz_driver_3096.log | text | |
MD5:— | SHA256:— | |||
| 3096 | cpuz.exe | C:\Windows\temp\cpuz152\cpuz152_x32.sys | executable | |
MD5:— | SHA256:— | |||
| 2056 | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.exe | C:\Users\admin\AppData\Local\Temp\is-NQG7P.tmp\MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | executable | |
MD5:1AFBD25DB5C9A90FE05309F7C4FBCF09 | SHA256:3BB0EE5569FE5453C6B3FA25AA517B925D4F8D1F7BA3475E58FA09C46290658C | |||
| 3608 | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | C:\Program Files\CPUID\CPU-Z\cpuz_eula.txt | text | |
MD5:E44F547A3378E46171D56A8A80CE9A40 | SHA256:AB086F912FF00C8C3AB42B8CA6D01395A96ECA253FAE4B186A3CA72C230B66B0 | |||
| 3608 | MDNEqUr9u_ZHKnPDHwXzdOnYA0bl-4NkZFadCa3TnQM_CLBkWRXwfsrlu_bNhfddmvan-lE-1QHDPOGQfA6_2tCD6C1YAUbCnCtdCjsdEOw.tmp | C:\Program Files\CPUID\CPU-Z\is-VSR7O.tmp | text | |
MD5:E44F547A3378E46171D56A8A80CE9A40 | SHA256:AB086F912FF00C8C3AB42B8CA6D01395A96ECA253FAE4B186A3CA72C230B66B0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3096 | cpuz.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d7d733ce0b900b66 | US | compressed | 61.4 Kb | whitelisted |
3096 | cpuz.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d3e03ff165925991 | US | compressed | 4.70 Kb | whitelisted |
3096 | cpuz.exe | GET | 200 | 184.24.9.54:80 | http://x1.c.lencr.org/ | DE | der | 717 b | whitelisted |
3096 | cpuz.exe | GET | 200 | 23.2.13.26:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMx09HkWS07es1rXypVKP5qnA%3D%3D | US | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3096 | cpuz.exe | 195.154.81.43:443 | download.cpuid.com | Online S.a.s. | FR | suspicious |
3096 | cpuz.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3096 | cpuz.exe | 23.2.13.26:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
3096 | cpuz.exe | 184.24.9.54:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.cpuid.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |