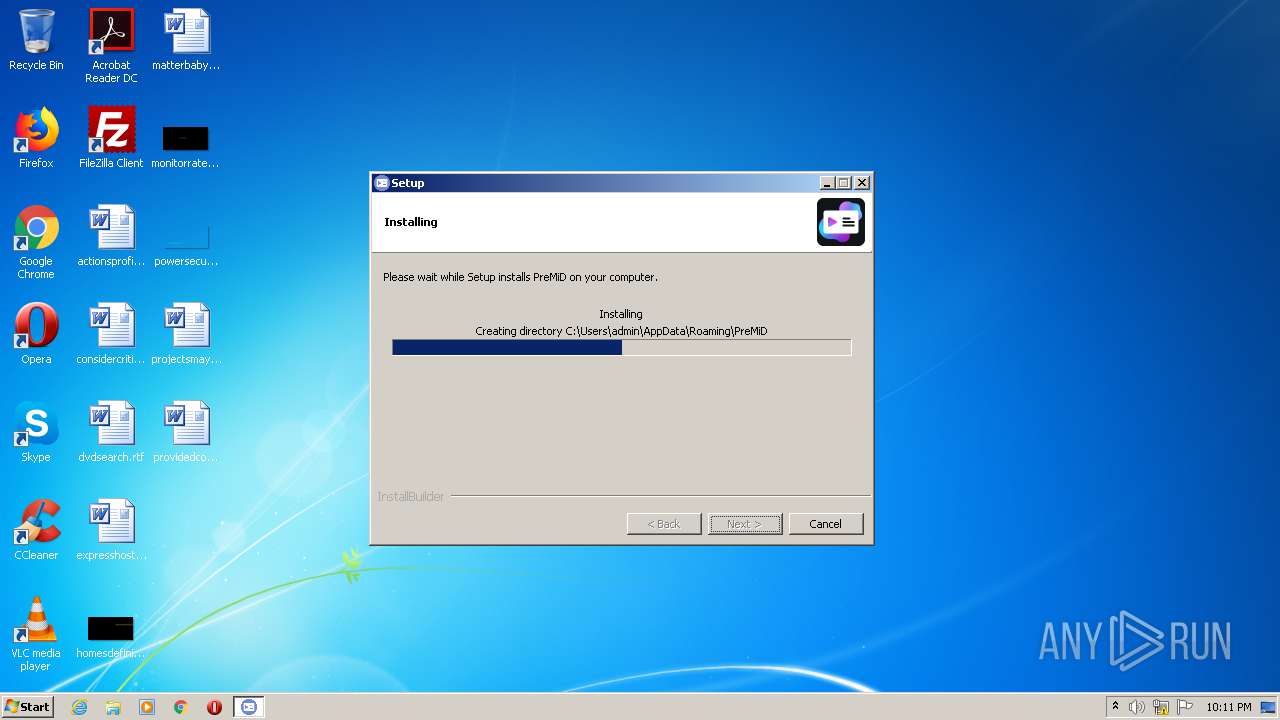
| File name: | PreMiD-installer.exe |
| Full analysis: | https://app.any.run/tasks/2a07d8bd-7cd1-4298-a3c1-9c946a56727c |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2021, 21:10:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 6AC694AD2F3D2CA003102F6E842B2EAF |
| SHA1: | 1AEFDDC5E887434AB99057AE2C12CBF17BF3CE04 |
| SHA256: | 8244204C1226A24D2842412CE429A09659AB66BCD7C4CB4F072A786B878ECBC4 |
| SSDEEP: | 98304:h4pLgrb08V6O1wwFAyj4uUU3OzWCqsGqcM2vCPBWisuY+KEJ7ubLjO/atIxaKQLr:WpkU+LCC4kQcrviWPuYDy/atCat7Hn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops a file with too old compile date
- PreMiD-installer.exe (PID: 1920)
Executable content was dropped or overwritten
- PreMiD-installer.exe (PID: 1920)
Drops a file that was compiled in debug mode
- PreMiD-installer.exe (PID: 1920)
Creates files in the user directory
- PreMiD-installer.exe (PID: 1920)
INFO
Dropped object may contain Bitcoin addresses
- PreMiD-installer.exe (PID: 1920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (48.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (34.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.3) |
| .exe | | | Win32 Executable (generic) (5) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| ProductVersion: | latest |
|---|---|
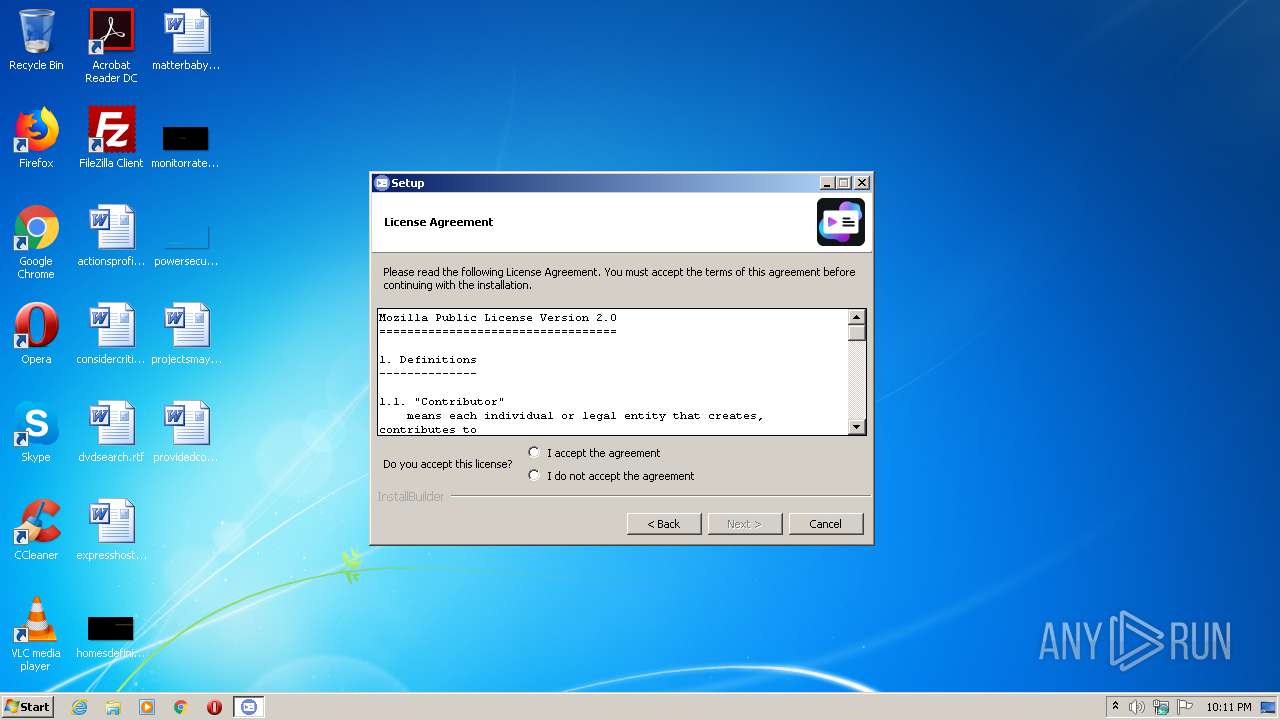
| ProductName: | PreMiD |
| FileVersion: | latest |
| LegalCopyright: | Copyright Timeraa |
| CompanyName: | Timeraa |
| OriginalFileName: | setup.exe |
| FileDescription: | Rich Presence for web services. |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x12a0 |
| UninitializedDataSize: | 7168 |
| InitializedDataSize: | 2926592 |
| CodeSize: | 1972224 |
| LinkerVersion: | 2.22 |
| PEType: | PE32 |
| TimeStamp: | 2019:10:10 19:24:39+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Oct-2019 17:24:39 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 10-Oct-2019 17:24:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001E1704 | 0x001E1800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.14841 |
.data | 0x001E3000 | 0x0001478C | 0x00014800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.62072 |
.rdata | 0x001F8000 | 0x00042B00 | 0x00042C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.83748 |
.eh_framl\xf0\x04 | 0x0023B000 | 0x0004F06C | 0x0004F200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.06303 |
.bss | 0x0028B000 | 0x00001BC8 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.edata | 0x0028D000 | 0x0000006E | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.36248 |
.idata | 0x0028E000 | 0x00003C30 | 0x00003E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.55047 |
.CRT | 0x00292000 | 0x00000018 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.114463 |
.tls | 0x00293000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.231158 |
.rsrc | 0x00294000 | 0x0002AA90 | 0x0002AC00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.80783 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07511 | 1904 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.37331 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3 | 2.11743 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.11093 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 1.57307 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.29164 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.17695 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.18099 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.15567 | 308 | UNKNOWN | English - United States | RT_CURSOR |
10 | 1.88729 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.dll |
IMM32.DLL |
KERNEL32.dll |
OLE32.dll |
OLEAUT32.DLL |
SHELL32.DLL |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TclKit_AppInit | 1 | 0x00002BD4 |
TclKit_SetKitPath | 2 | 0x00002FD4 |
Total processes
32
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1920 | "C:\Users\admin\AppData\Local\Temp\PreMiD-installer.exe" | C:\Users\admin\AppData\Local\Temp\PreMiD-installer.exe | explorer.exe | ||||||||||||
User: admin Company: Timeraa Integrity Level: MEDIUM Description: Rich Presence for web services. Exit code: 0 Version: latest Modules
| |||||||||||||||
Total events
386
Read events
386
Write events
0
Delete events
0
Modification events
Executable files
15
Suspicious files
1
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1920 | PreMiD-installer.exe | C:\Users\admin\AppData\Local\Temp\PreMiD-release.zip | — | |
MD5:— | SHA256:— | |||
| 1920 | PreMiD-installer.exe | C:\Users\admin\AppData\Roaming\PreMiD\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 1920 | PreMiD-installer.exe | C:\Users\admin\AppData\Local\Temp\BR4699.tmp | executable | |
MD5:10BF1C1948B47C944C055F9EF828207A | SHA256:436517B8C463AE164325F0C0B7EB61CFD26CDDA690AA9CDF92C97079736B7CDF | |||
| 1920 | PreMiD-installer.exe | C:\Users\admin\AppData\Local\Temp\BR4871.tmp | executable | |
MD5:08AD4CD2A940379F1DCDBDB9884A1375 | SHA256:78827E2B1EF0AAD4F8B1B42D0964064819AA22BFCD537EBAACB30D817EDC06D8 | |||
| 1920 | PreMiD-installer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\PreMiD\Uninstall PreMiD.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1920 | PreMiD-installer.exe | C:\Users\admin\AppData\Local\Temp\BR4892.tmp | executable | |
MD5:027491B39A7B16B116E780F55ABC288E | SHA256:EEF69D005BF1C0B715C8D6205400D4755C261DD38DDFBBFE918E6EE91F21F1F0 | |||
| 1920 | PreMiD-installer.exe | C:\Users\admin\AppData\Local\Temp\BR4DC7.tmp | executable | |
MD5:C030205EEB88AB26D1DAF9DB946943CF | SHA256:749EF6F9AF090FEBCAA42E6A1AE29BAF3E719273C520F585D4187C68221AD94A | |||
| 1920 | PreMiD-installer.exe | C:\Users\admin\AppData\Local\Temp\BR4DA6.tmp | executable | |
MD5:0700F3DBE367287CE10472CFFBD3D7D1 | SHA256:77E46A6A8FBC079CDB1D3EE299AF36C3D1881D38D93C4E0551F114965CDAF10F | |||
| 1920 | PreMiD-installer.exe | C:\Users\admin\AppData\Local\Temp\BR4E39.tmp | executable | |
MD5:145D5C49FE34A44662BEAFFE641D58C7 | SHA256:59182F092B59A3005ADA6B2F2855C7E860E53E8ADF6E41CD8CD515578AE7815A | |||
| 1920 | PreMiD-installer.exe | C:\Users\admin\AppData\Local\Temp\BR4E38.tmp | executable | |
MD5:606F13D4D580B1F322B3F3D3DF423BBA | SHA256:C71A16B1056E522CD0365449448116D06F37A3273D77694D170340064511DD25 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1920 | PreMiD-installer.exe | 185.199.108.154:443 | github-releases.githubusercontent.com | GitHub, Inc. | NL | suspicious |
1920 | PreMiD-installer.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
github-releases.githubusercontent.com |
| whitelisted |