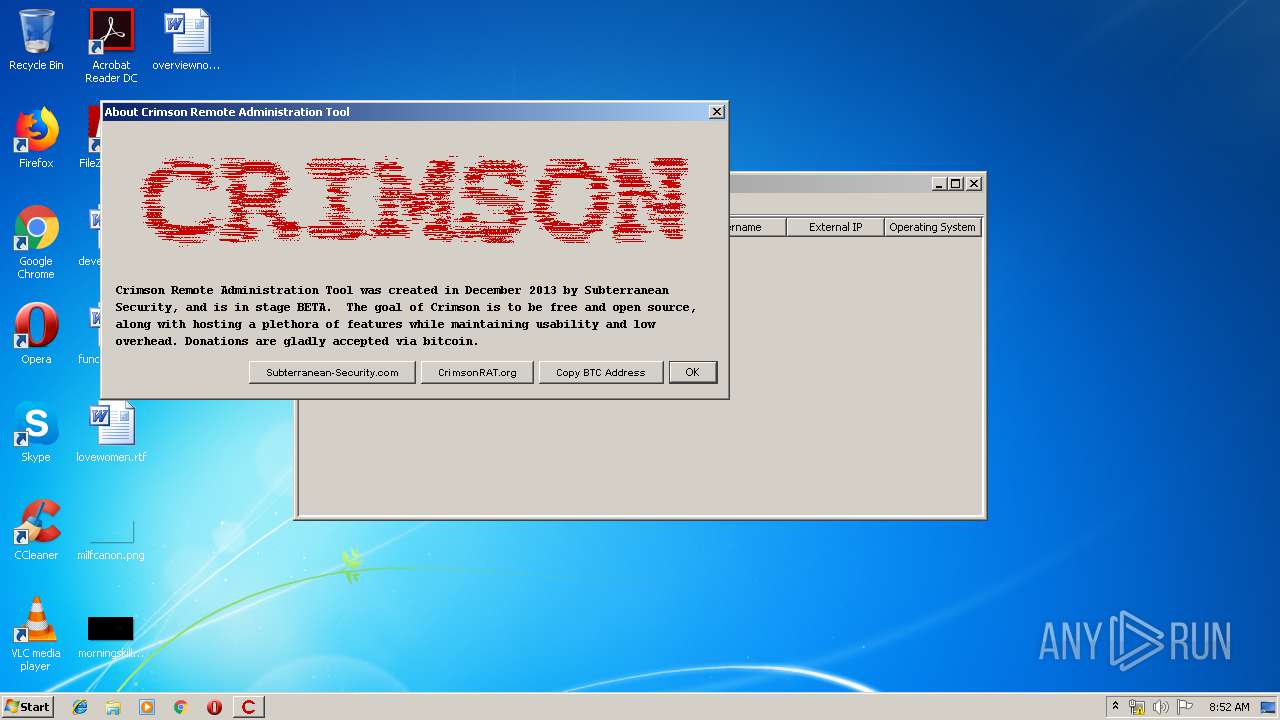
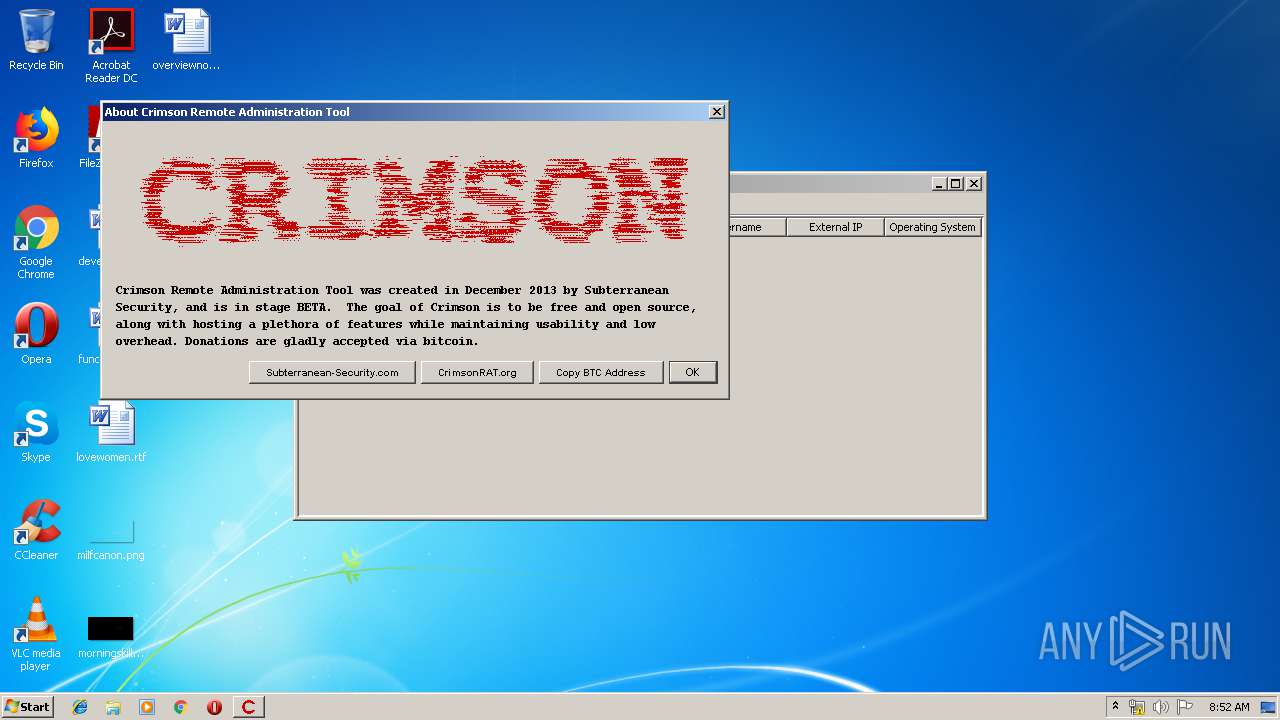
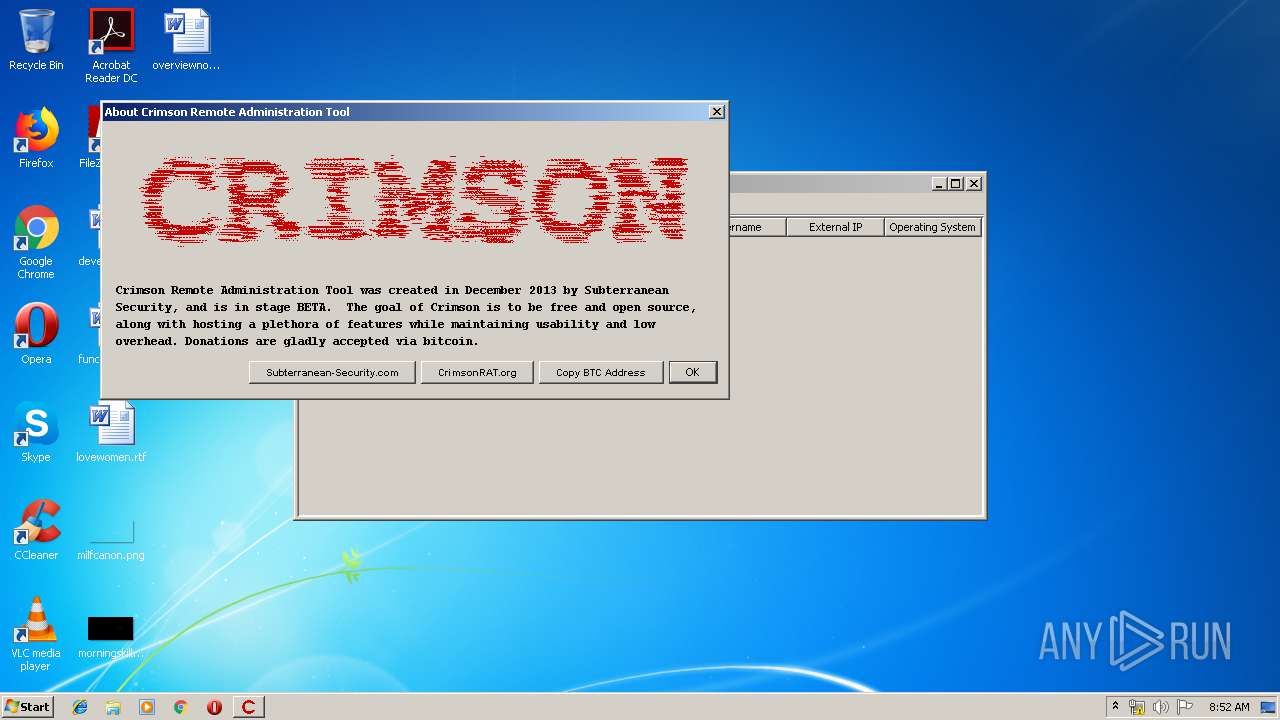
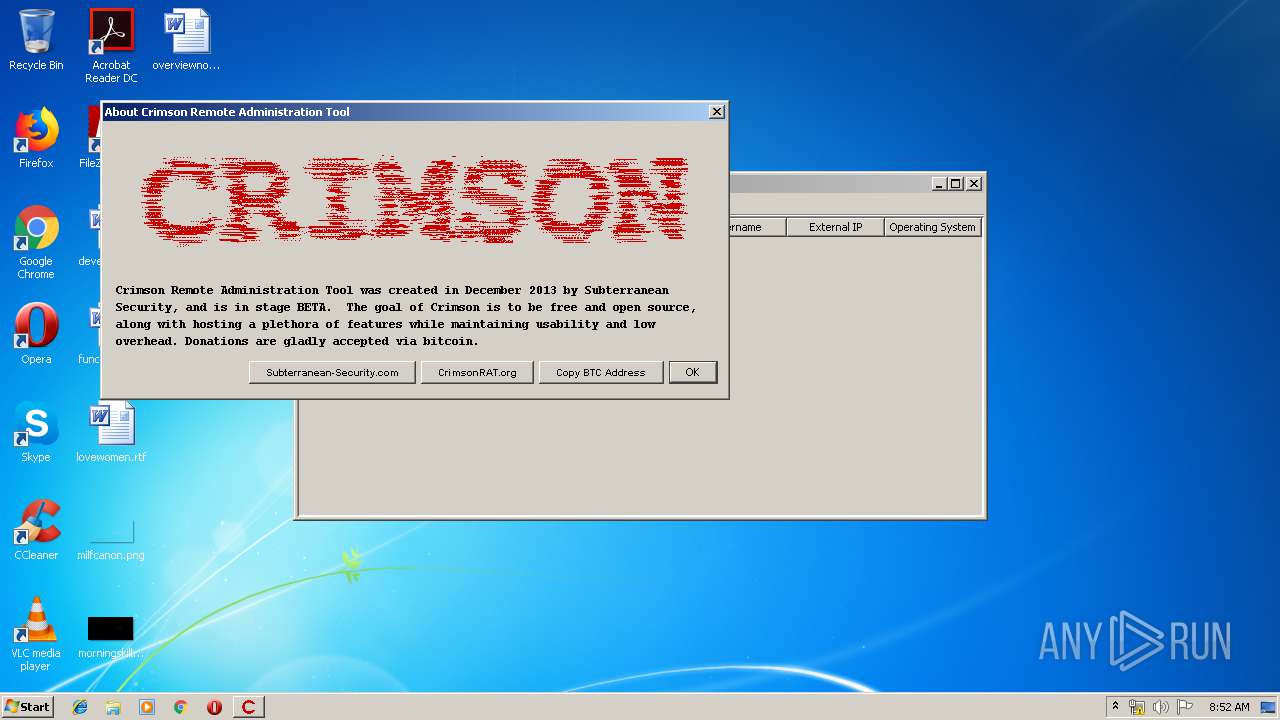
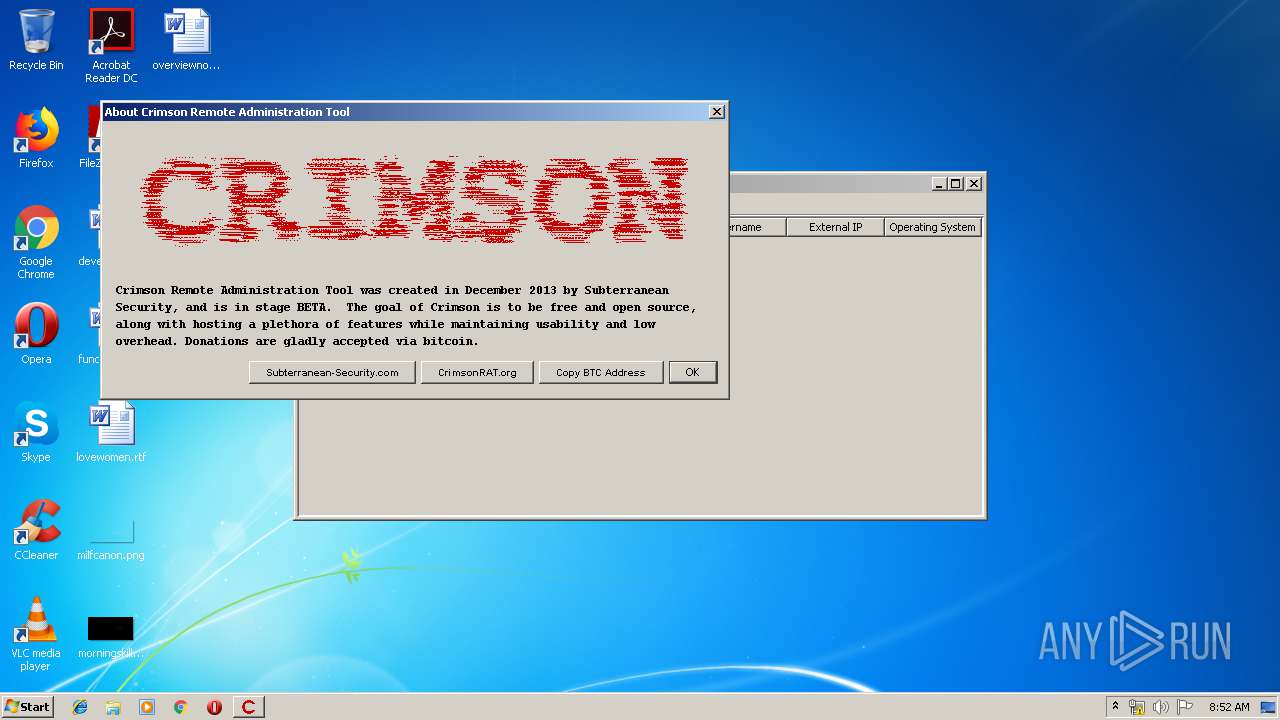
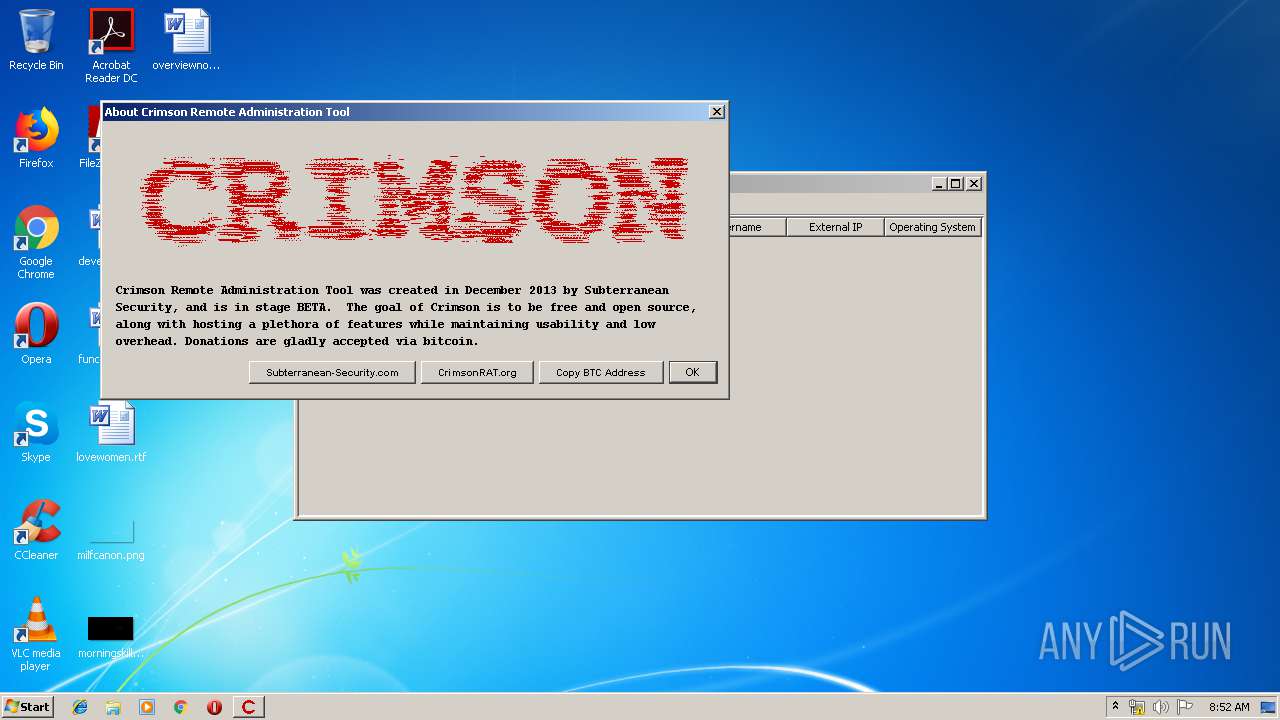
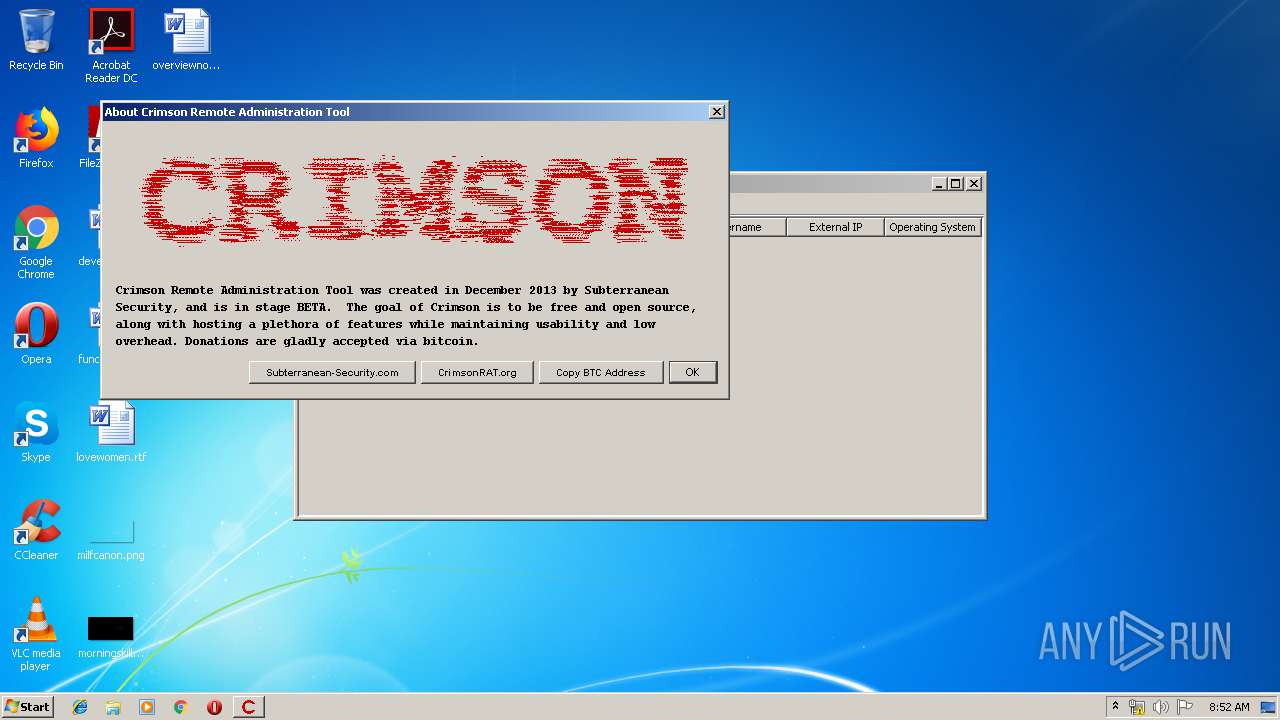
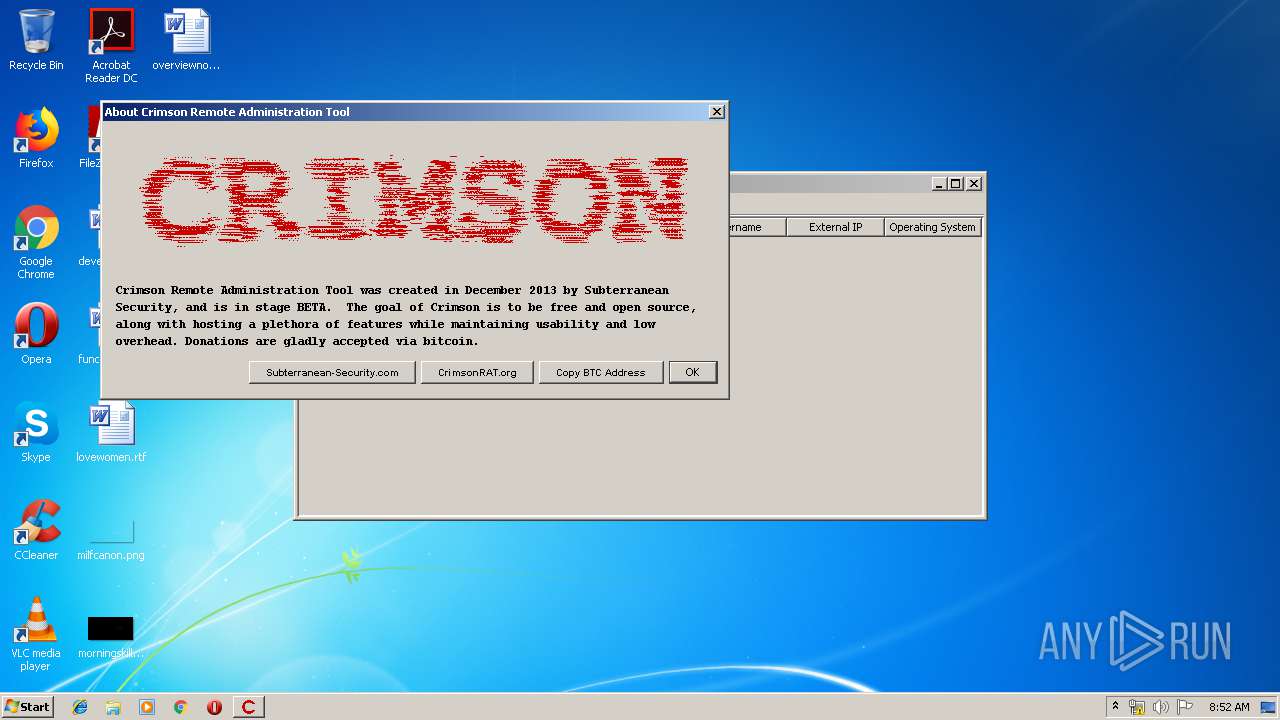
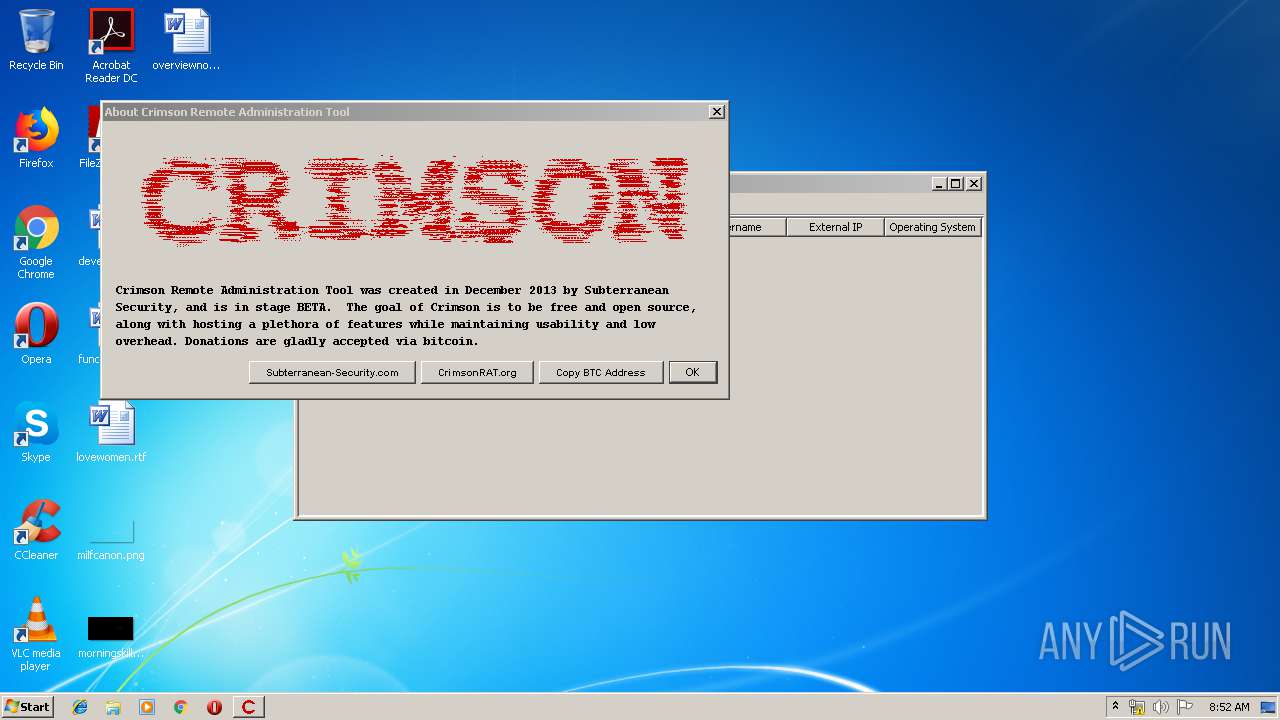
| File name: | CrimsonRAT2.2.2.jar |
| Full analysis: | https://app.any.run/tasks/05072151-20f6-4073-a8c5-4c9ee6da2bb9 |
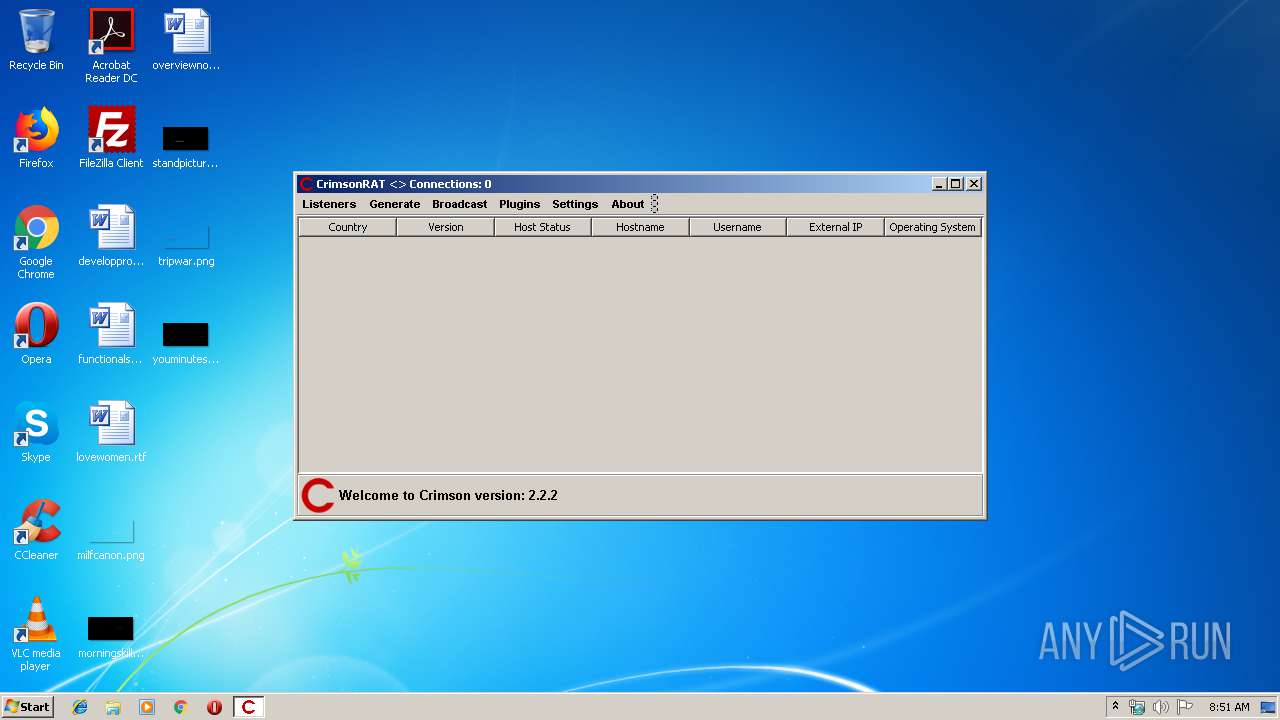
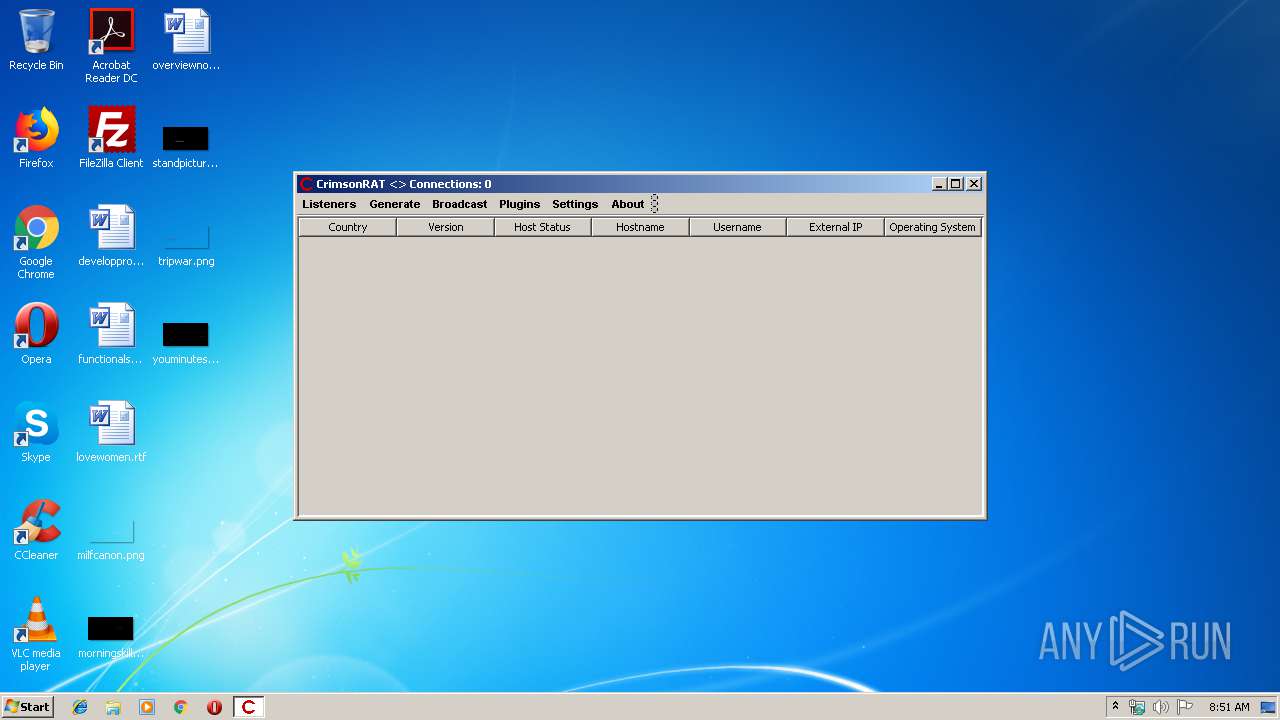
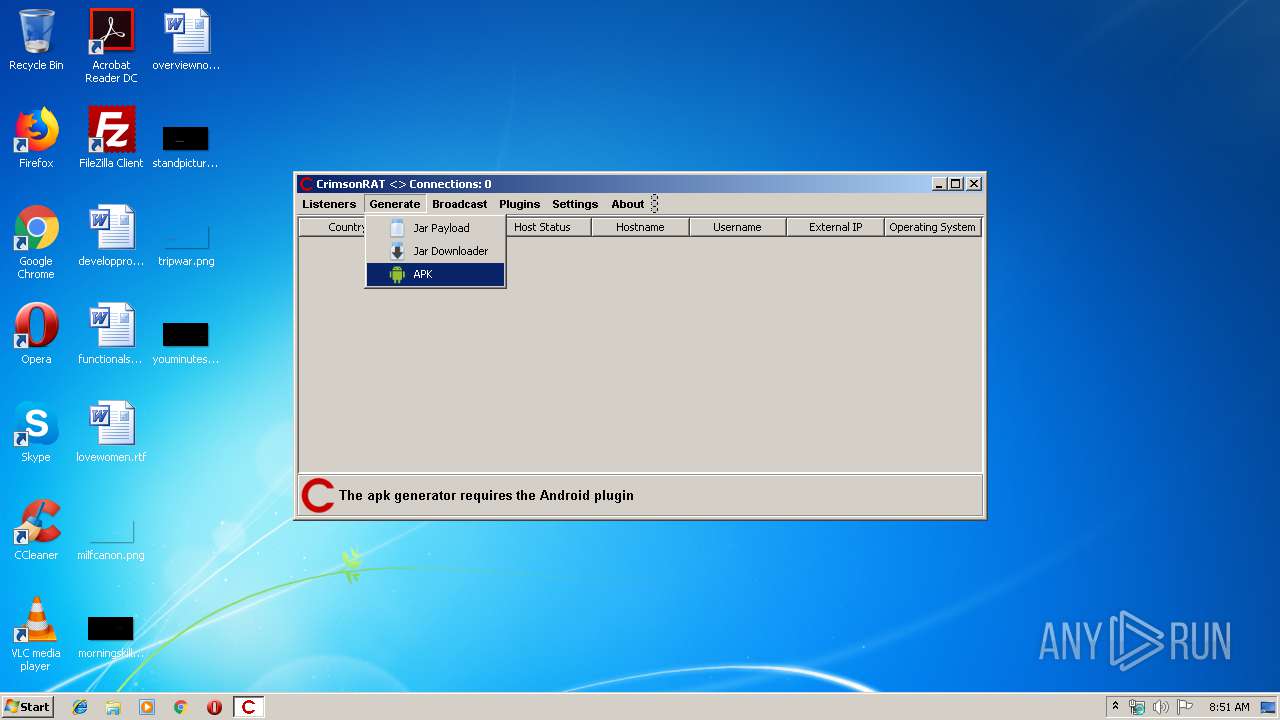
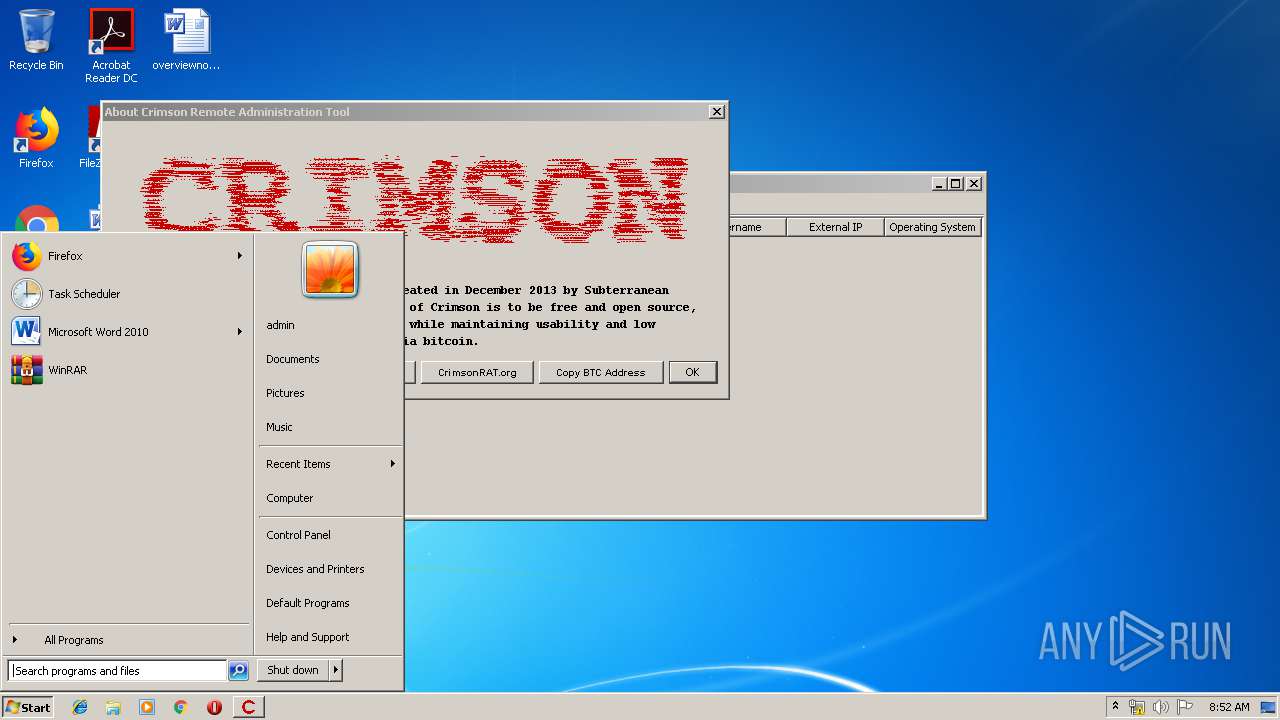
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 08:50:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | FC5CE9BE14A85F0605631100EE97D196 |
| SHA1: | F58AB29876DAD8AF34C65CAB8D5EDF34D26AE98B |
| SHA256: | 821A8664E76FD081E1B8923EC555C8465A926DD3B65E921549CA9A5C059BAE79 |
| SSDEEP: | 98304:3Nlc5H7lmWZc4Nh4nUVPh2QqAGf51nAamGlLHcp1:CH7QCh4SPmDAulbcf |
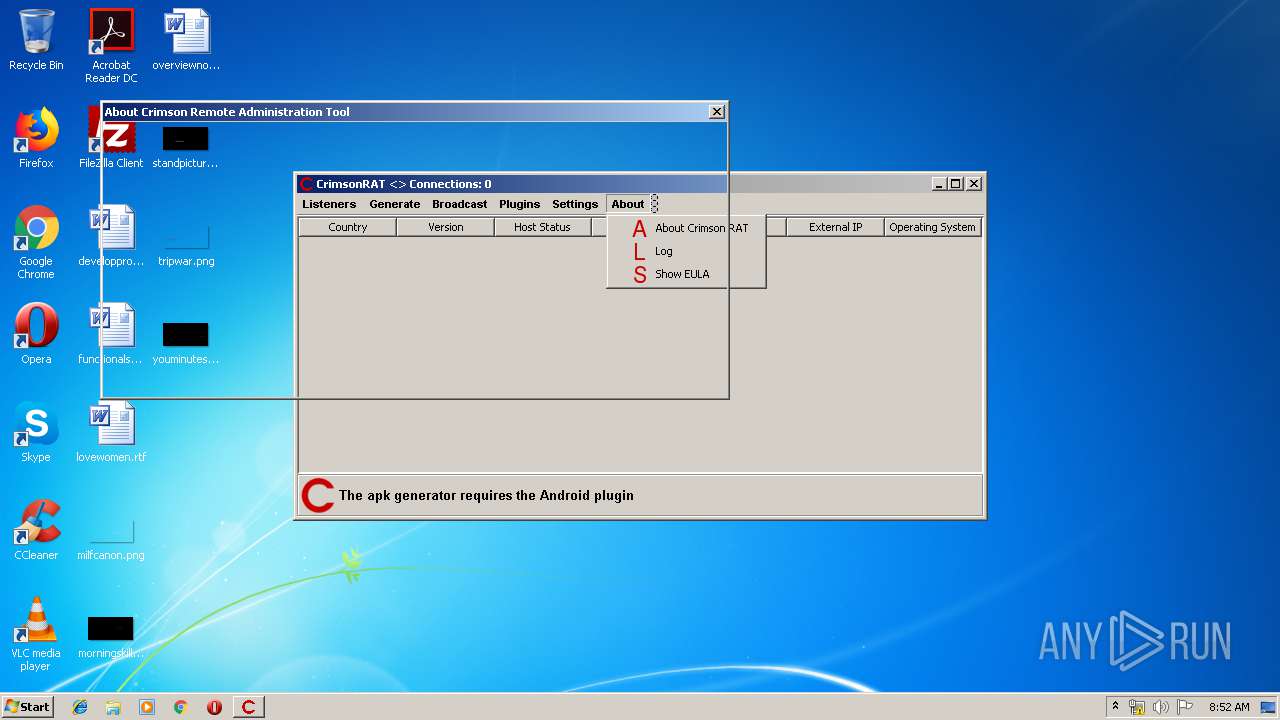
MALICIOUS
Actions looks like stealing of personal data
- javaw.exe (PID: 2588)
SUSPICIOUS
Creates files in the user directory
- javaw.exe (PID: 2588)
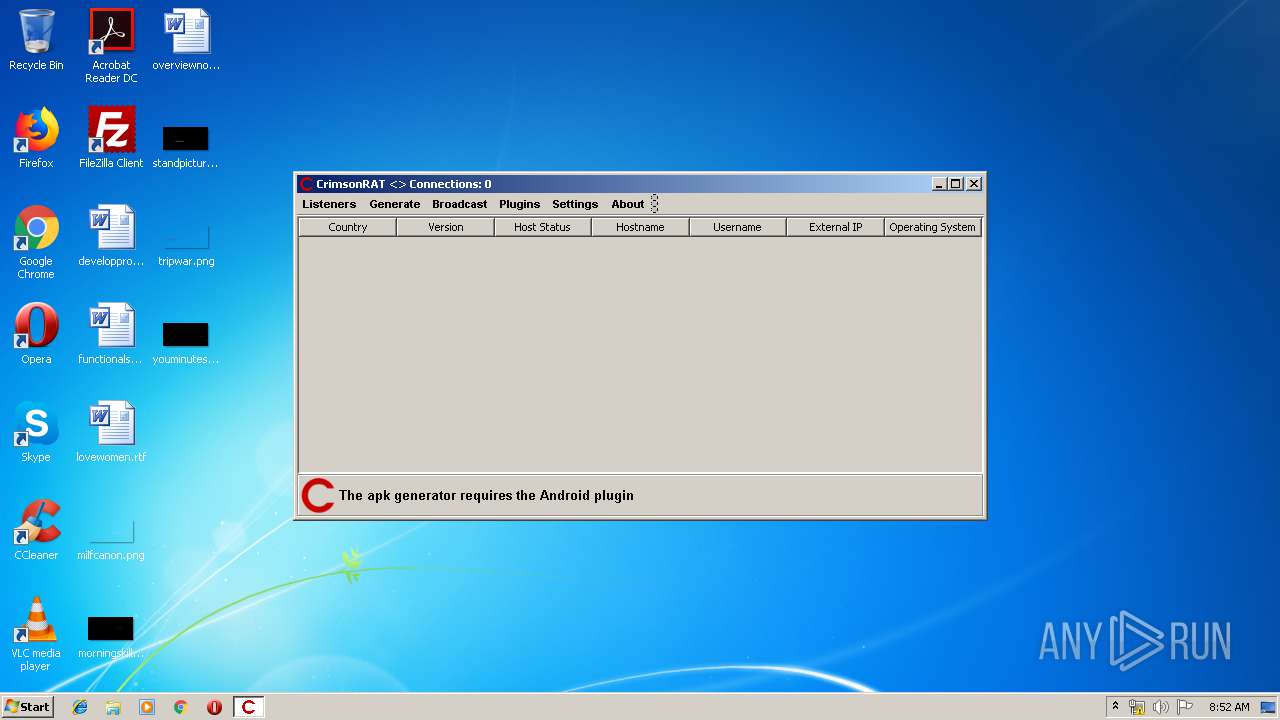
Checks for external IP
- javaw.exe (PID: 2588)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | None |
| ZipModifyDate: | 2014:08:13 19:52:23 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | aurelienribon/ |
Total processes
40
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2588 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\CrimsonRAT2.2.2.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1073807364 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
24
Read events
23
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2588) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2588 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2588 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2588 | javaw.exe | GET | 301 | 104.26.15.73:80 | http://freegeoip.net/xml/85.203.20.11 | US | — | — | malicious |
2588 | javaw.exe | GET | 200 | 52.55.255.113:80 | http://checkip.amazonaws.com/ | US | text | 13 b | malicious |
2588 | javaw.exe | GET | 403 | 104.26.15.73:80 | http://freegeoip.net/shutdown | US | text | 1.51 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | javaw.exe | 52.55.255.113:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
2588 | javaw.exe | 104.26.15.73:80 | freegeoip.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.amazonaws.com |
| malicious |
freegeoip.net |
| malicious |
crimsonrat.org |
| unknown |
Threats
4 ETPRO signatures available at the full report