| File name: | Launch.exe |
| Full analysis: | https://app.any.run/tasks/da6ea653-c6f4-4bf6-be4b-b441eab41415 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 03:03:30 |
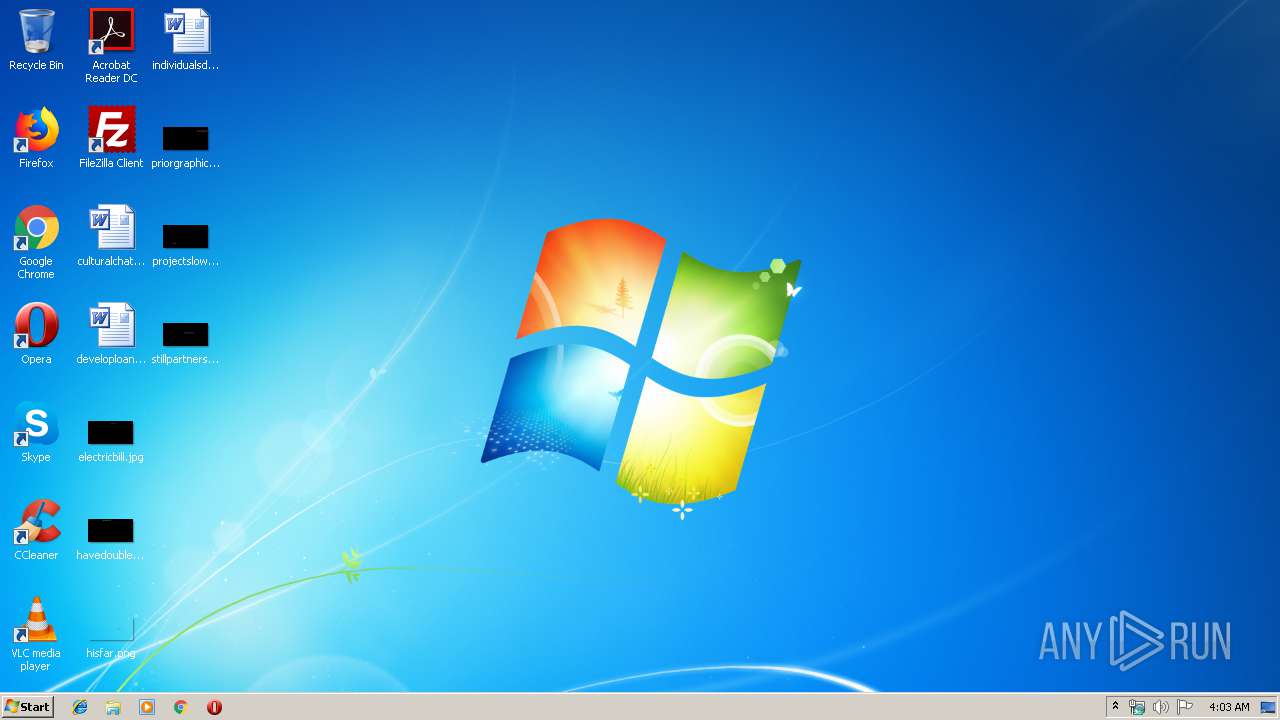
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 742F0422CE1FAB03D0291B331BB6F12D |
| SHA1: | CD17423DBC01AC2887FEAA6B69F7A5AB68983AB4 |
| SHA256: | 8218E396A8856FB873127450941FCDBB811039FACF668420A6B2D765395A5ACF |
| SSDEEP: | 98304:66slLTzcfujzFn05Ricx4PHzLbQvnfs4P0QkCNCXkiCl3CNaQfQo6iS/VBzrXQjy:ODcfujP2oJCp29oiqBcjytFx |
MALICIOUS
No malicious indicators.SUSPICIOUS
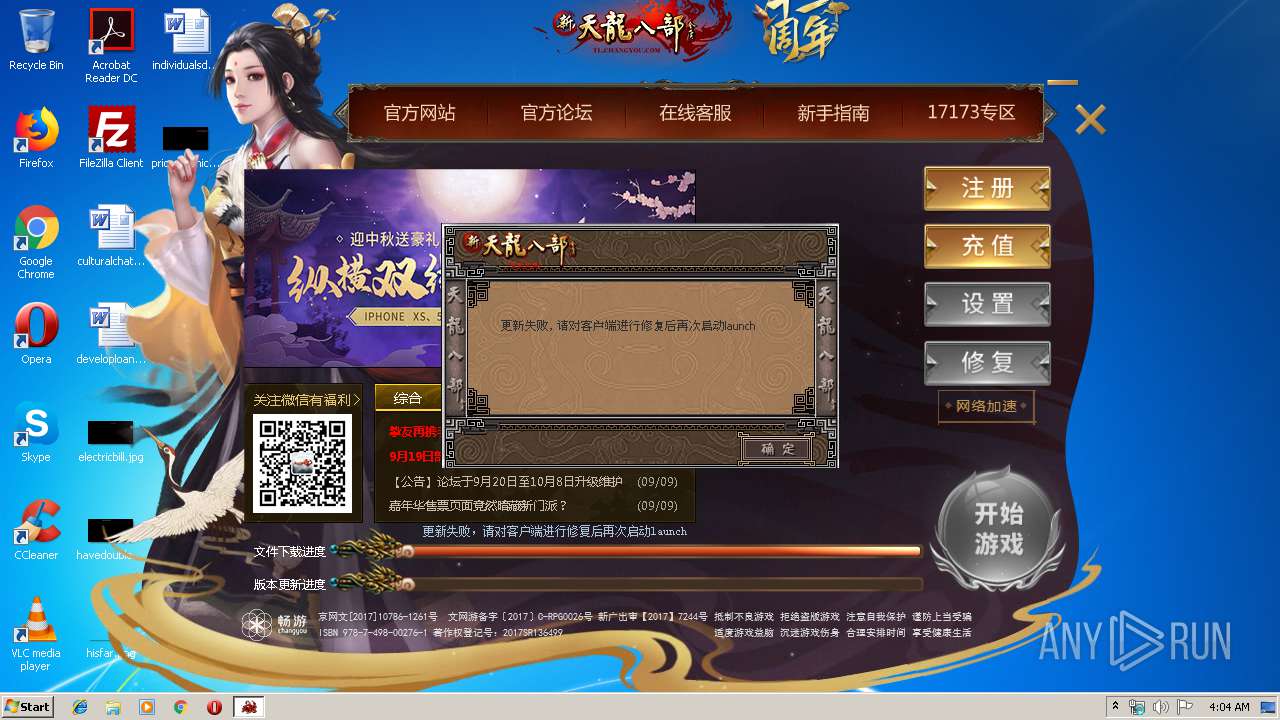
Starts itself from another location
- Launch.exe (PID: 3732)
Creates files in the user directory
- Launch.bin (PID: 2788)
Starts application with an unusual extension
- Launch.exe (PID: 3732)
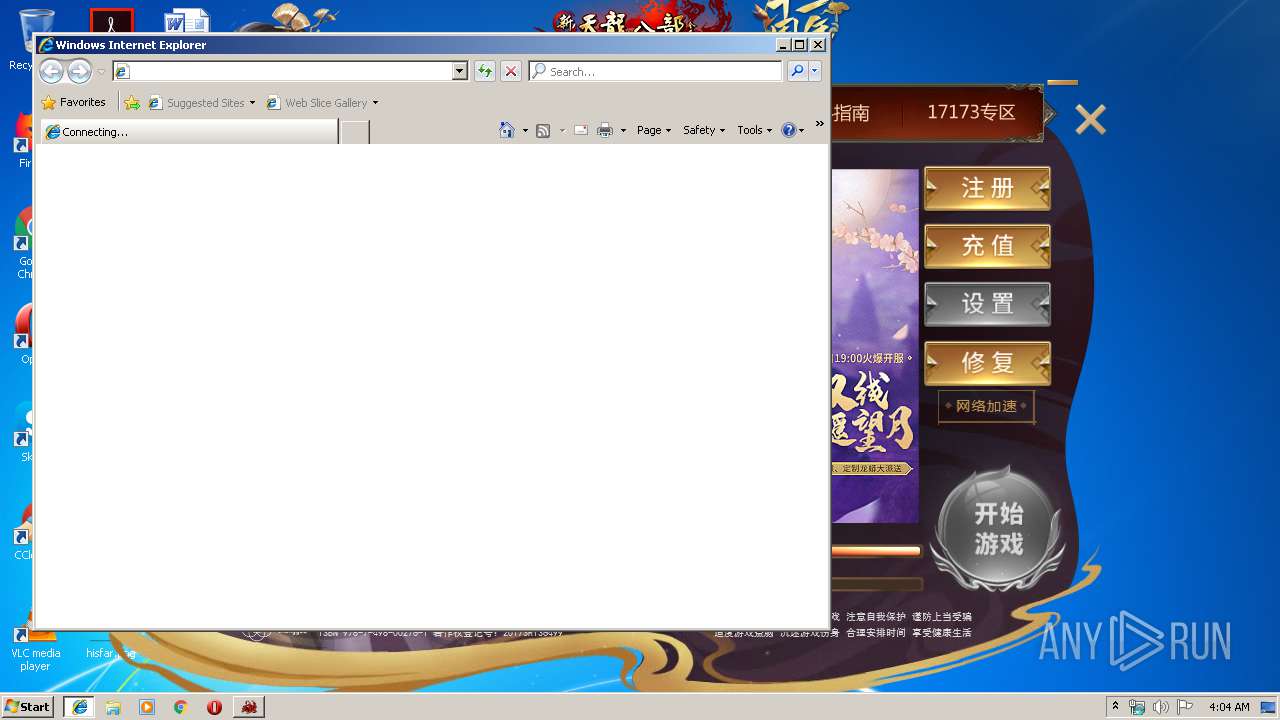
Starts Internet Explorer
- Launch.bin (PID: 2788)
Reads Internet Cache Settings
- Launch.bin (PID: 2788)
Reads internet explorer settings
- Launch.bin (PID: 2788)
Executable content was dropped or overwritten
- Launch.exe (PID: 3732)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3460)
Reads settings of System Certificates
- Launch.bin (PID: 2788)
Application launched itself
- iexplore.exe (PID: 3460)
Reads Internet Cache Settings
- iexplore.exe (PID: 4008)
Reads internet explorer settings
- iexplore.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:19 14:40:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 1105920 |
| InitializedDataSize: | 5603328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xdf6e6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.7.157 |
| ProductVersionNumber: | 1.0.7.157 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| Comments: | XTLBB Launch for JD |
| CompanyName: | Changyou.com Limited |
| FileDescription: | Launch_1.0.7.157 |
| FileVersion: | 1.0.7.157 |
| InternalName: | Launch.exe |
| LegalCopyright: | (C) 2008-2019 Changyou.com Limited. All Rights Reserved. |
| OriginalFileName: | Launch.exe |
| ProductName: | XTLBB Launch |
| ProductVersion: | 1.0.7.157 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jul-2019 12:40:18 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | XTLBB Launch for JD |
| CompanyName: | Changyou.com Limited |
| FileDescription: | Launch_1.0.7.157 |
| FileVersion: | 1.0.7.157 |
| InternalName: | Launch.exe |
| LegalCopyright: | (C) 2008-2019 Changyou.com Limited. All Rights Reserved. |
| OriginalFilename: | Launch.exe |
| ProductName: | XTLBB Launch |
| ProductVersion: | 1.0.7.157 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 19-Jul-2019 12:40:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0010D1B4 | 0x0010E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51605 |
.rdata | 0x0010F000 | 0x0002AA66 | 0x0002B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.44533 |
.data | 0x0013A000 | 0x00016220 | 0x0000D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.20934 |
.tls | 0x00151000 | 0x00005299 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00157000 | 0x0050F098 | 0x00510000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.99481 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.4902 | 876 | UNKNOWN | Chinese - PRC | RT_VERSION |
2 | 3.42575 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 3.21971 | 488 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 3.34697 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 4.98446 | 3752 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 5.60786 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 2.74563 | 124 | UNKNOWN | Chinese - PRC | RT_STRING |
8 | 4.9694 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 3.10014 | 270376 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 3.30459 | 67624 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WININET.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
CreateSoDATask | 1 | 0x000B4ED9 |
DestroySoDATask | 2 | 0x000B4DFD |
SoDACancelDownload | 3 | 0x000B4DBE |
SoDACancelDownloadUrllist | 4 | 0x000B4DF4 |
SoDACommitFile | 5 | 0x000B4E39 |
SoDADownloadUrl | 6 | 0x000B4D83 |
SoDADownloadUrllist | 7 | 0x000B4DD5 |
SoDAGetPort | 8 | 0x000B4D27 |
SoDAGetStatusInfo | 9 | 0x000B4DC7 |
SoDAInitLibrary | 10 | 0x000B4CF9 |
Total processes
36
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2788 | Launch.bin -defskin | C:\Users\admin\AppData\Local\Temp\Launch.bin | Launch.exe | ||||||||||||
User: admin Company: Changyou.com Limited Integrity Level: MEDIUM Description: Launch_1.0.7.157 Exit code: 0 Version: 1.0.7.157 Modules
| |||||||||||||||
| 3460 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Launch.bin | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3732 | "C:\Users\admin\AppData\Local\Temp\Launch.exe" | C:\Users\admin\AppData\Local\Temp\Launch.exe | explorer.exe | ||||||||||||
User: admin Company: Changyou.com Limited Integrity Level: MEDIUM Description: Launch_1.0.7.157 Exit code: 0 Version: 1.0.7.157 Modules
| |||||||||||||||
| 4008 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3460 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
526
Read events
446
Write events
79
Delete events
1
Modification events
| (PID) Process: | (2788) Launch.bin | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2788) Launch.bin | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2788) Launch.bin | Key: | HKEY_CURRENT_USER\Software\SOHU\FireFox\TLBB |
| Operation: | write | Name: | cus2 |
Value: 2f9e5ae66f32413ba3fa768b6a2d9e25 | |||
| (PID) Process: | (2788) Launch.bin | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Launch_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2788) Launch.bin | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Launch_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2788) Launch.bin | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Launch_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2788) Launch.bin | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Launch_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2788) Launch.bin | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Launch_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2788) Launch.bin | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Launch_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2788) Launch.bin | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Launch_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
6
Text files
53
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2788 | Launch.bin | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 2788 | Launch.bin | C:\Users\admin\AppData\Local\Temp\TLBA78F.tmp | — | |
MD5:— | SHA256:— | |||
| 2788 | Launch.bin | C:\Users\admin\AppData\Local\Temp\TLBA790.tmp | — | |
MD5:— | SHA256:— | |||
| 2788 | Launch.bin | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\bkg[1] | — | |
MD5:— | SHA256:— | |||
| 2788 | Launch.bin | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\tlbb-launch[1] | html | |
MD5:— | SHA256:— | |||
| 3732 | Launch.exe | C:\Users\admin\AppData\Local\Temp\Launch.bin | executable | |
MD5:— | SHA256:— | |||
| 2788 | Launch.bin | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sol | sol | |
MD5:— | SHA256:— | |||
| 2788 | Launch.bin | C:\Users\admin\AppData\Local\Temp\~TLBBDownload.zip | compressed | |
MD5:— | SHA256:— | |||
| 2788 | Launch.bin | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\bkg[1] | image | |
MD5:— | SHA256:— | |||
| 2788 | Launch.bin | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\left[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
26
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2788 | Launch.bin | GET | 200 | 163.171.132.119:80 | http://update.tl.sohu.com/xtlbb-jd/loginserver.txt?rnd=132723 | US | text | 210 Kb | malicious |
2788 | Launch.bin | GET | 200 | 163.171.132.119:80 | http://update.tl.sohu.com/xtlbb-jd/patchinfo.txt?rnd=132726 | US | ini | 262 Kb | malicious |
2788 | Launch.bin | GET | 200 | 163.171.132.119:80 | http://i1.cy.com/xtl/pic/2019/09/05/launch.jpg | US | image | 52.1 Kb | malicious |
2788 | Launch.bin | GET | 200 | 163.171.132.119:80 | http://i0.cy.com/xtl/launcher/20160928/er_code.jpg | US | image | 2.73 Kb | malicious |
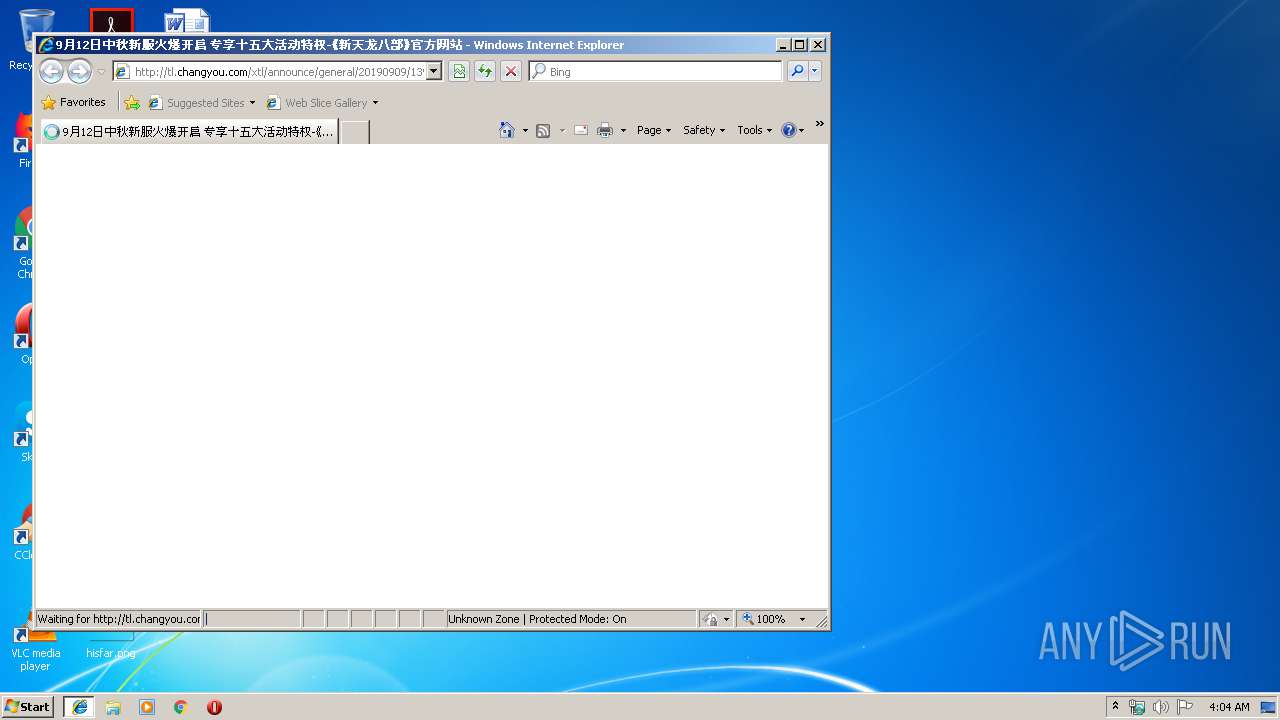
2788 | Launch.bin | GET | 200 | 163.171.132.119:80 | http://tl.changyou.com/content/launcher/1510/right2.shtml | US | html | 1.22 Kb | malicious |
2788 | Launch.bin | GET | 200 | 163.171.132.119:80 | http://tl.changyou.com/content/launcher/1510/left.shtml | US | html | 5.23 Kb | malicious |
2788 | Launch.bin | GET | 200 | 163.171.132.119:80 | http://i1.cy.com/xtl/pic/2019/08/02/launch_a1.png | US | image | 183 Kb | malicious |
2788 | Launch.bin | GET | 200 | 163.171.132.119:80 | http://i0.cy.com/xtl/launcher/20161111/news.jpg | US | image | 8.31 Kb | malicious |
2788 | Launch.bin | GET | 200 | 163.171.132.119:80 | http://i1.cy.com/xtl/pic/2019/09/09/xf/main_a1.jpg | US | image | 110 Kb | malicious |
2788 | Launch.bin | GET | 200 | 163.171.132.119:80 | http://i1.cy.com/xtl/pic/2019/09/09/jng/launch.jpg | US | image | 114 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2788 | Launch.bin | 163.171.132.119:80 | tl.changyou.com | — | US | malicious |
2788 | Launch.bin | 140.143.111.230:80 | mon.changyou.com | Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
4008 | iexplore.exe | 163.171.132.119:80 | tl.changyou.com | — | US | malicious |
3460 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2788 | Launch.bin | 103.235.46.191:443 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
2788 | Launch.bin | 211.159.180.107:80 | activity.changyou.com | Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tl.changyou.com |
| malicious |
update.tl.sohu.com |
| malicious |
i1.cy.com |
| malicious |
activity.changyou.com |
| unknown |
i0.cy.com |
| malicious |
mon.changyou.com |
| unknown |
hm.baidu.com |
| whitelisted |
www.bing.com |
| whitelisted |