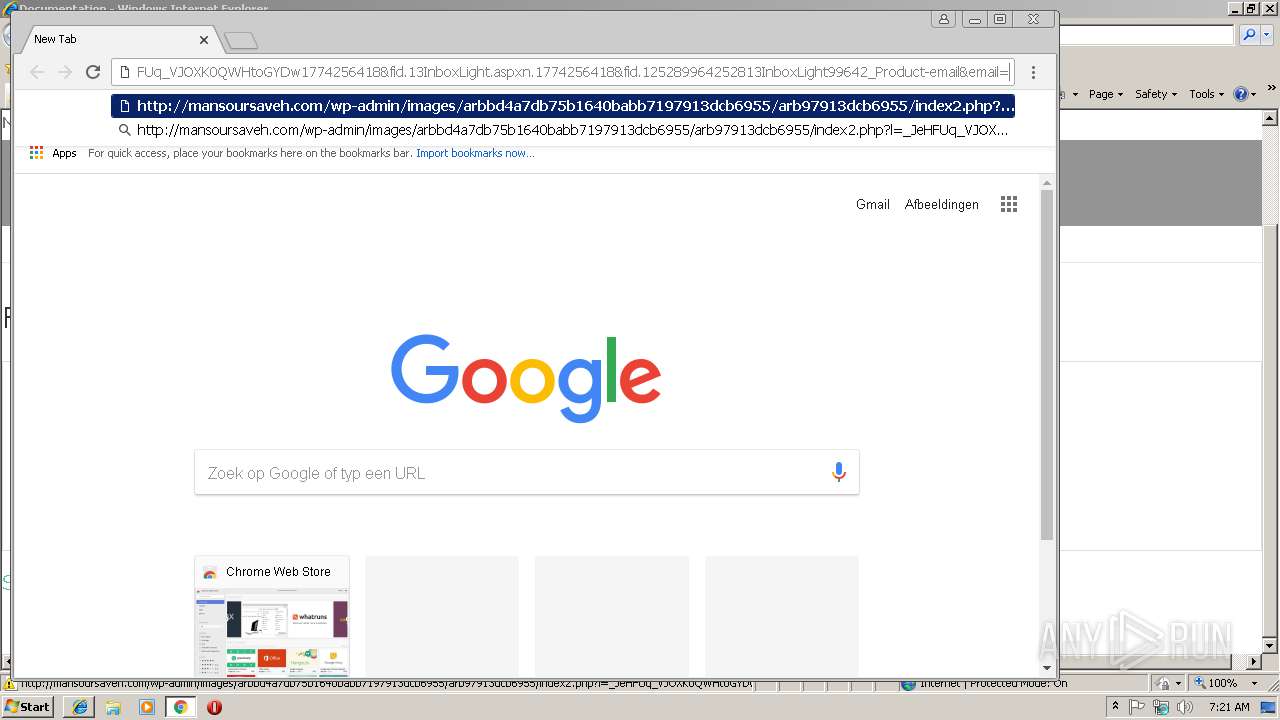
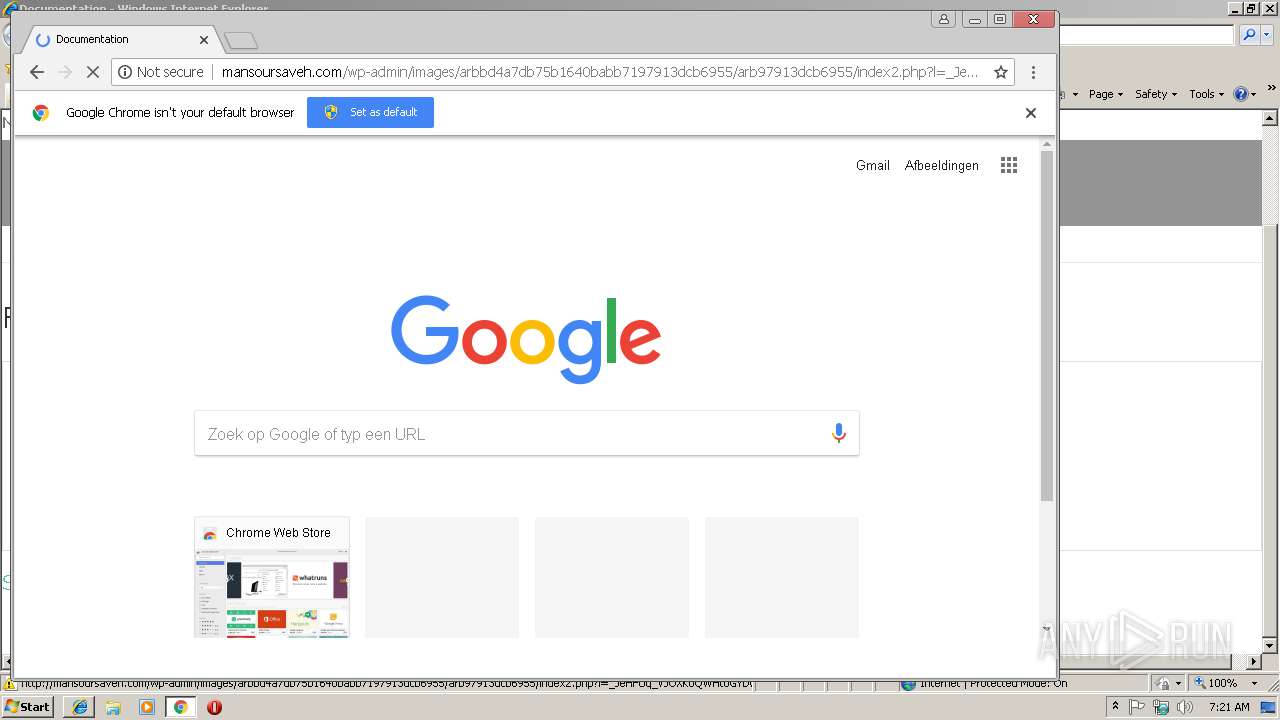
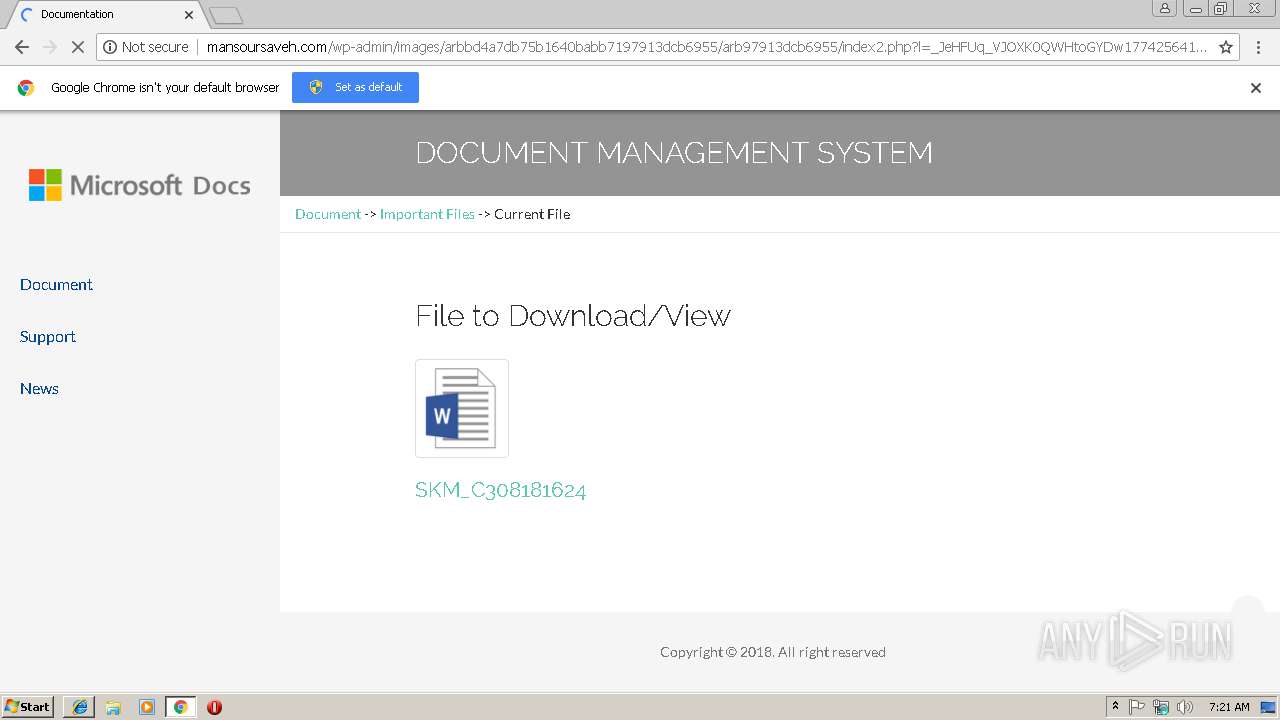
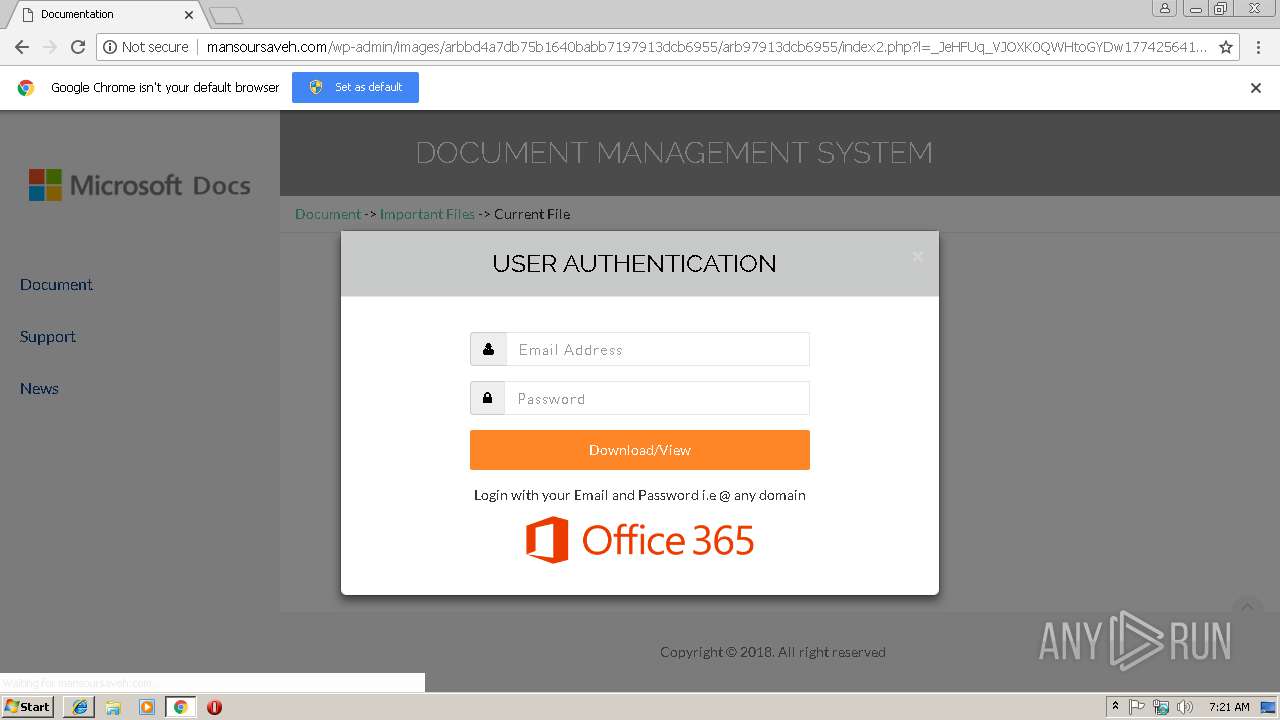
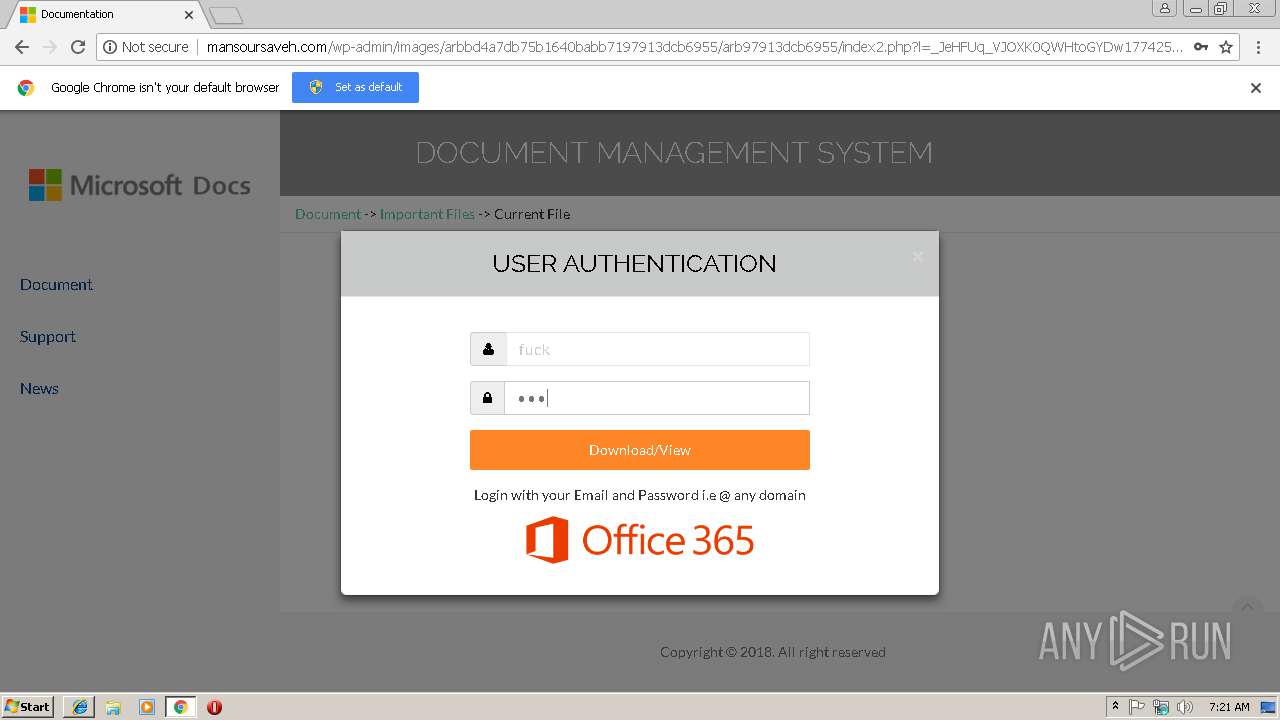
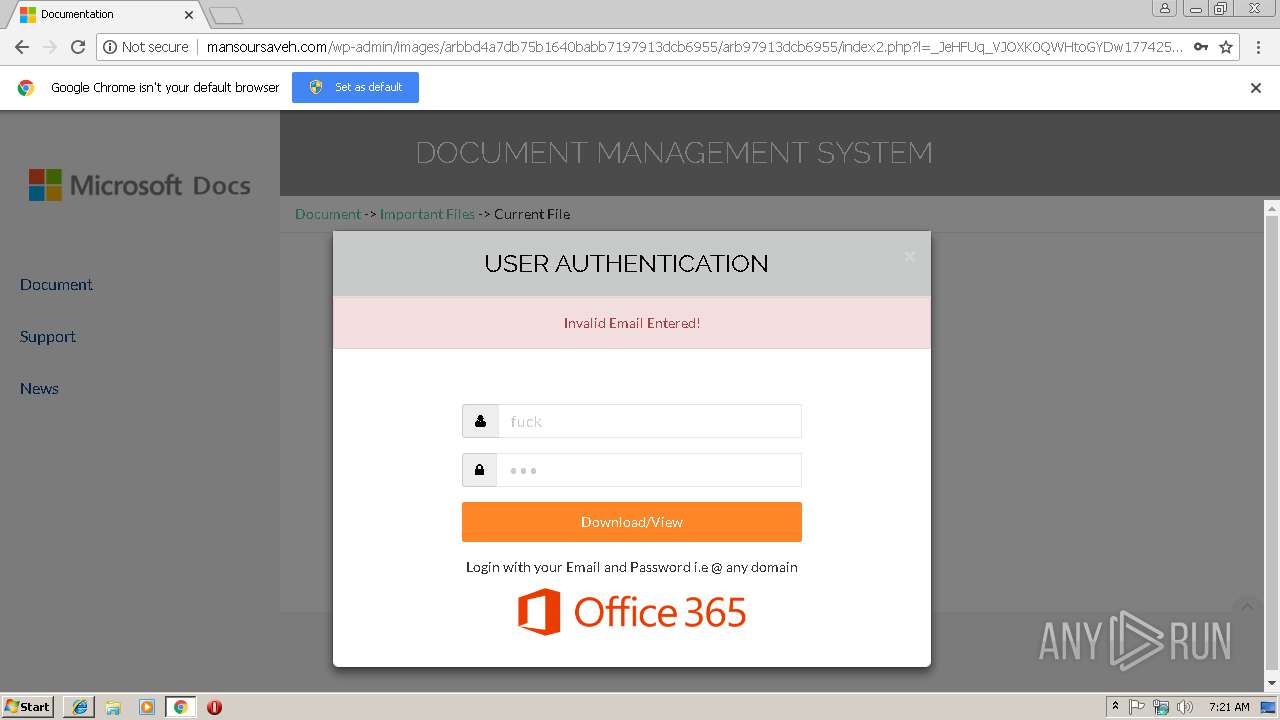
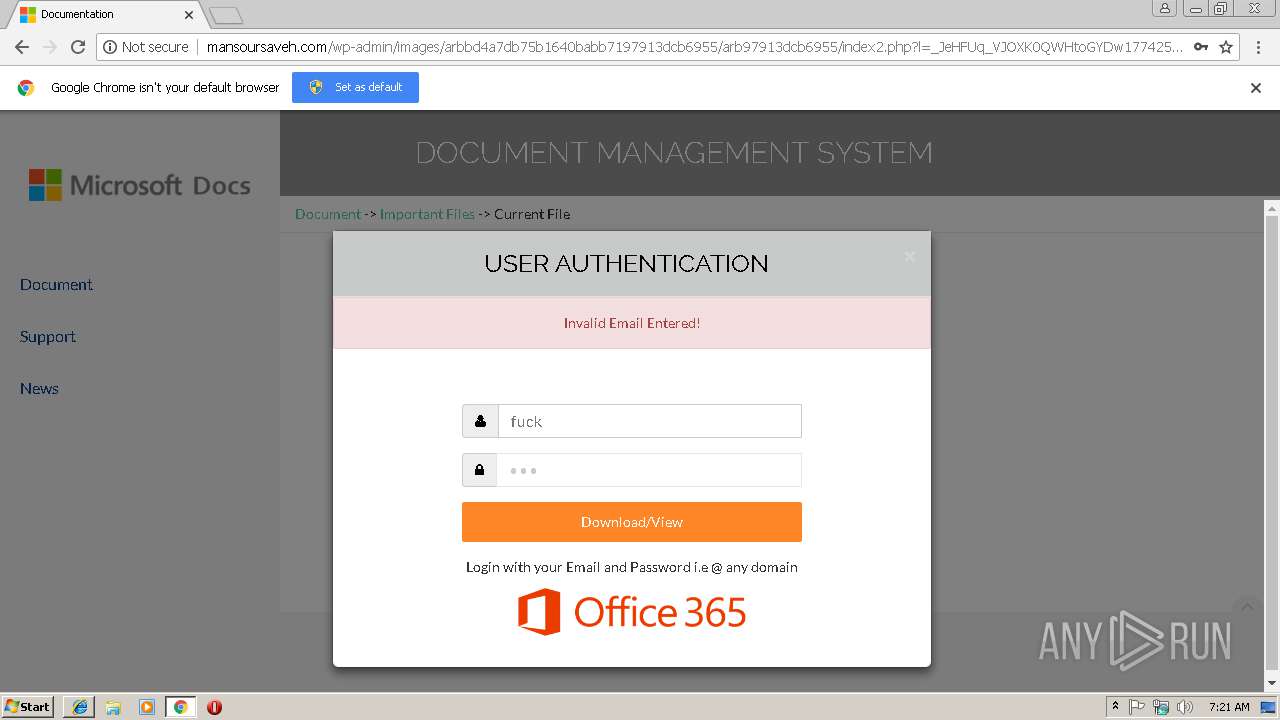
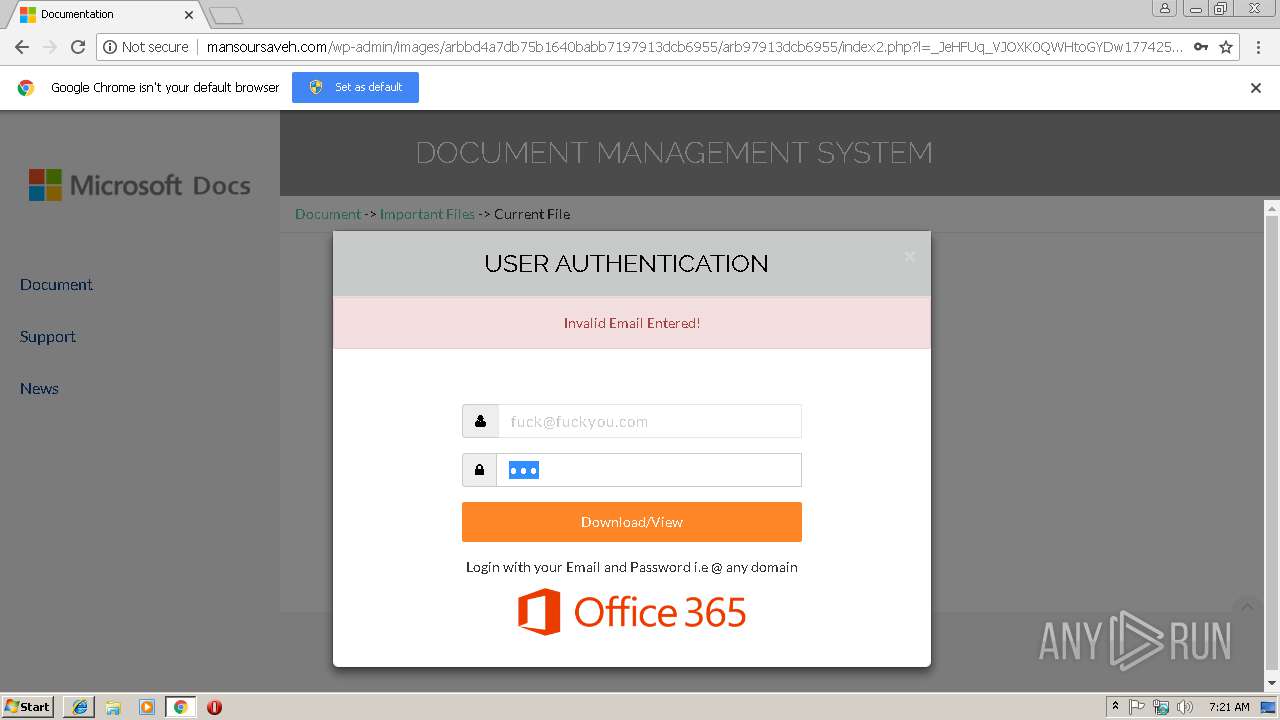
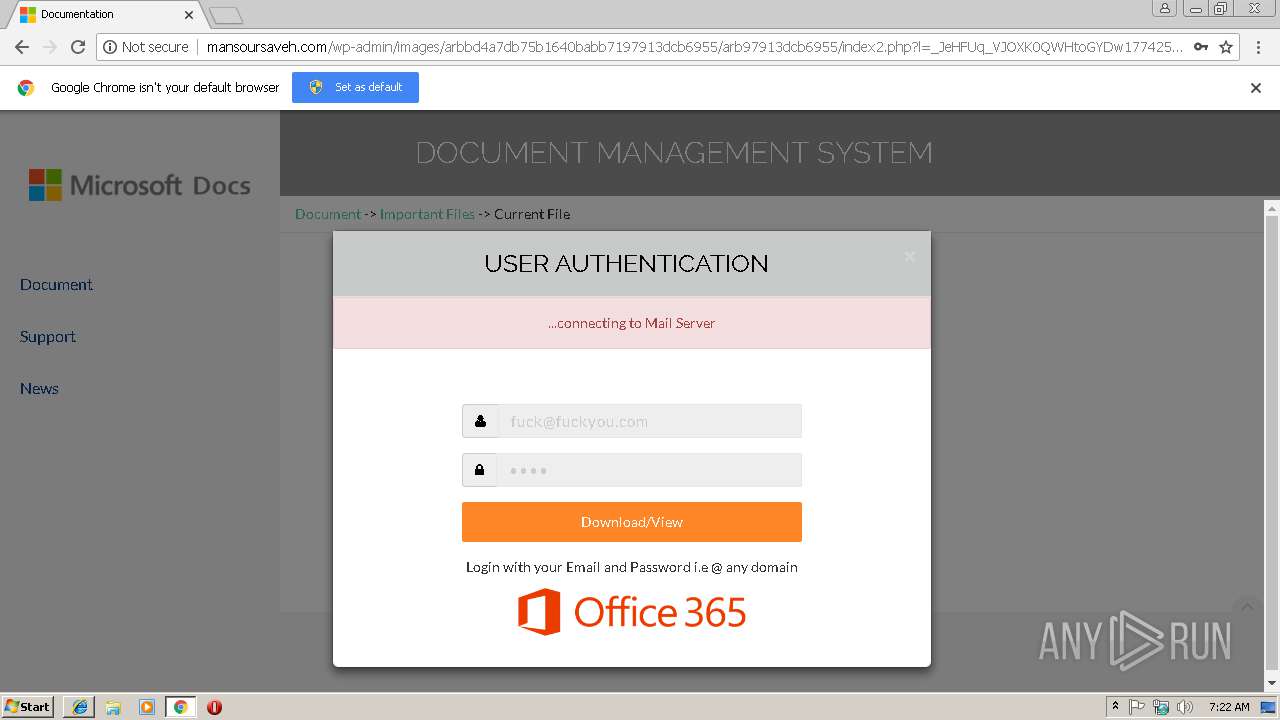
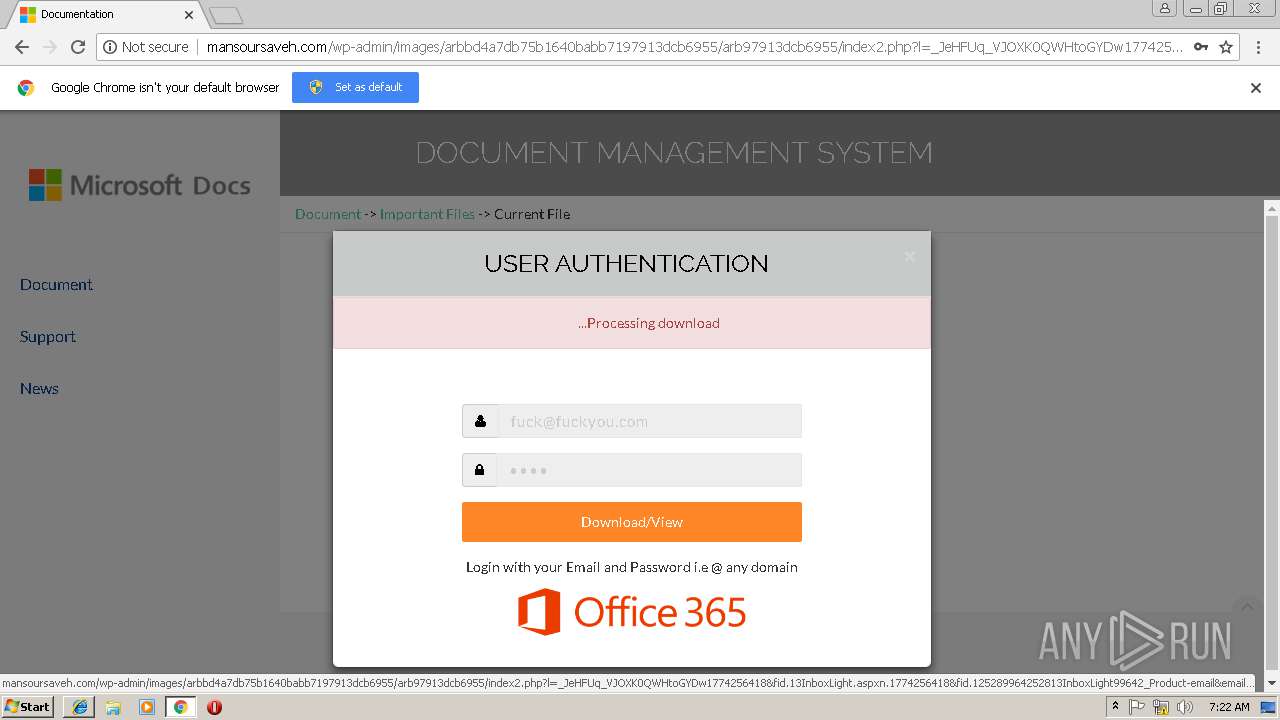
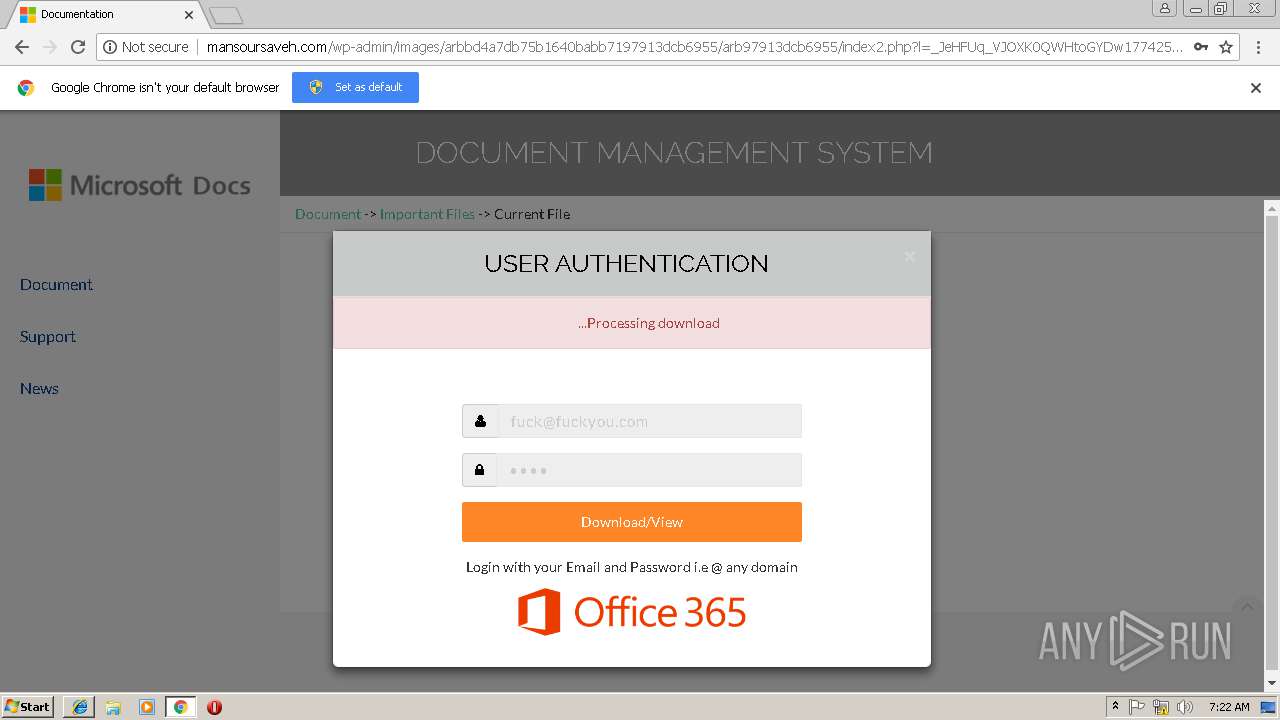
| URL: | http://mansoursaveh.com/wp-admin/images/arbbd4a7db75b1640babb7197913dcb6955/arb97913dcb6955/ |
| Full analysis: | https://app.any.run/tasks/f0d8a886-e3d1-47c9-b358-45aa8486d10d |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 07:21:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DBE956E34DB7BFF4F1DC41EA3FEE959C |
| SHA1: | 84CE2E74FF09061F10C2B2EB07D0A34EFECB41E2 |
| SHA256: | 81FDBBF96656021592D8B4BCC27ACD3E116D7189E4428482925872483F79D345 |
| SSDEEP: | 3:N1KT1jDMZGK2gzndUTrQM5wEXown:Cxj4ZGvgj7MwEXown |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2240)
- iexplore.exe (PID: 2972)
Changes internet zones settings
- iexplore.exe (PID: 2972)
Reads internet explorer settings
- iexplore.exe (PID: 3252)
Reads Internet Cache Settings
- iexplore.exe (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2244 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,11058385979517158040,16612007867782564671,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1E3C16D6F73A723156601F8529A63544 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1E3C16D6F73A723156601F8529A63544 --renderer-client-id=6 --mojo-platform-channel-handle=3556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,11058385979517158040,16612007867782564671,131072 --enable-features=PasswordImport --service-pipe-token=D05F08E3A1BEE635FE6B80DB37E0F161 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D05F08E3A1BEE635FE6B80DB37E0F161 --renderer-client-id=5 --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6dfa00b0,0x6dfa00c0,0x6dfa00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3252 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2972 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=888,11058385979517158040,16612007867782564671,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=0AD97E09712B56CD783CD62B20E82CCD --mojo-platform-channel-handle=3796 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=888,11058385979517158040,16612007867782564671,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=9A795364401DA20DA21B13F13263A16E --mojo-platform-channel-handle=940 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,11058385979517158040,16612007867782564671,131072 --enable-features=PasswordImport --service-pipe-token=6CC86184E5214E2ADC00058624483600 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6CC86184E5214E2ADC00058624483600 --renderer-client-id=3 --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
914
Read events
807
Write events
101
Delete events
6
Modification events
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {A5995243-1AF1-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307010005001200070015001300DC00 | |||
Executable files
0
Suspicious files
36
Text files
67
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\index2[1].php | — | |
MD5:— | SHA256:— | |||
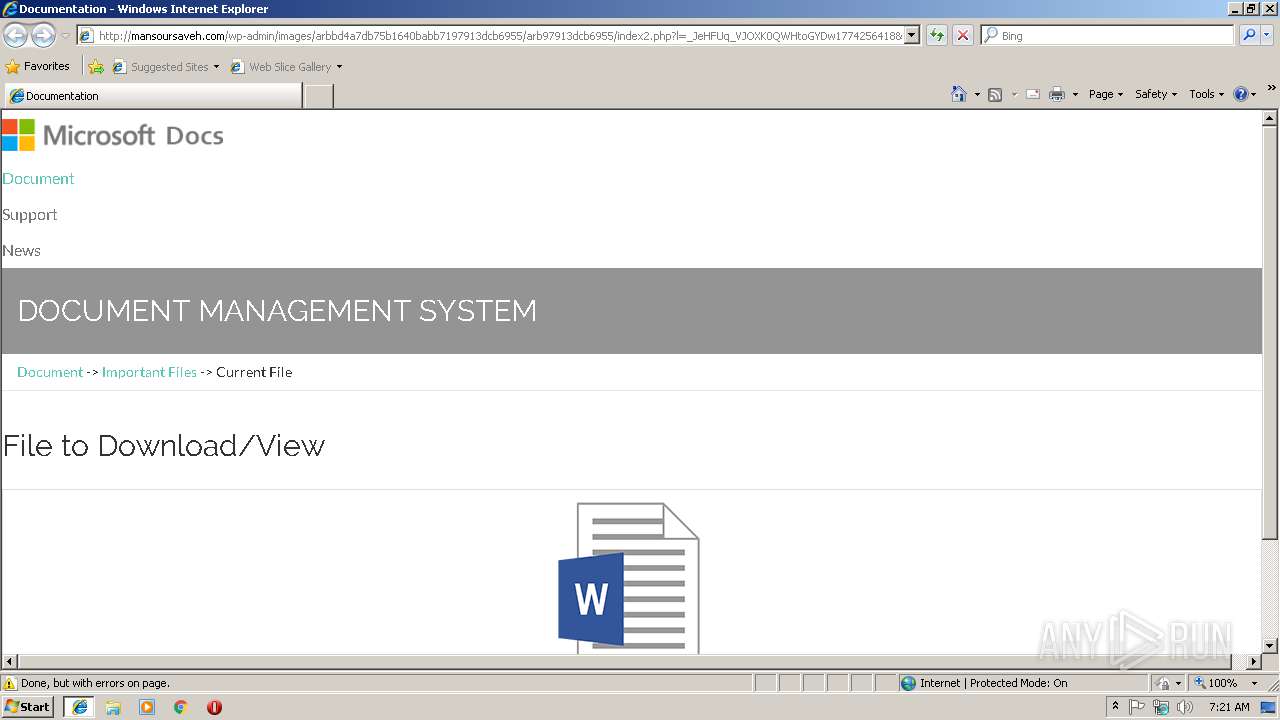
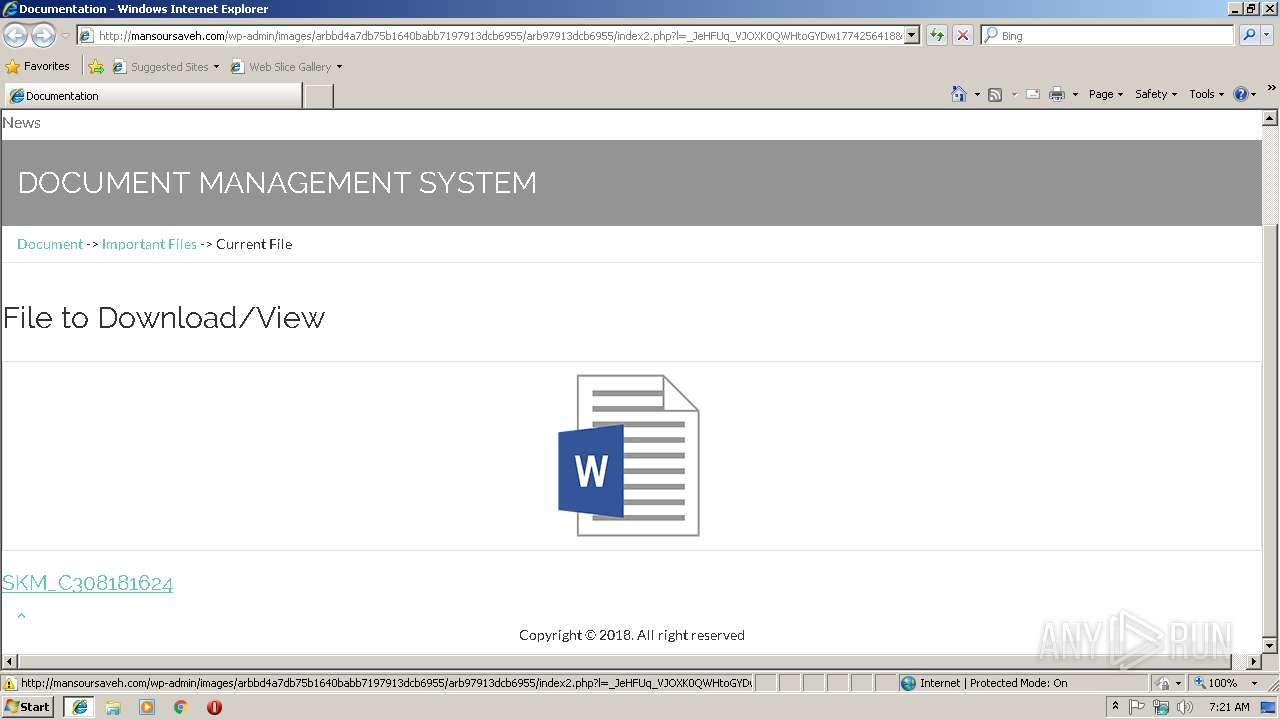
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\word[1].png | image | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\index2[1].htm | html | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\Office_365_logo[1].png | image | |
MD5:95E1D221F4F2F485C900D7C69D5F8049 | SHA256:8AE79A4D18EEA420AF0FD562D43879B569BBD2C622DA6DEBA79F6C202E385361 | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019011820190119\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\setup-config[1].htm | html | |
MD5:— | SHA256:— | |||
| 2240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
35
DNS requests
17
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3252 | iexplore.exe | GET | 302 | 164.138.20.168:80 | http://mansoursaveh.com/wp-admin/images/arbbd4a7db75b1640babb7197913dcb6955/arb97913dcb6955/ | IR | — | — | suspicious |
2972 | iexplore.exe | GET | 302 | 164.138.20.168:80 | http://mansoursaveh.com/favicon.ico | IR | — | — | suspicious |
3252 | iexplore.exe | GET | 200 | 164.138.20.168:80 | http://mansoursaveh.com/wp-admin/images/arbbd4a7db75b1640babb7197913dcb6955/arb97913dcb6955/assets/img/word.png | IR | image | 7.09 Kb | suspicious |
3252 | iexplore.exe | GET | 200 | 164.138.20.168:80 | http://mansoursaveh.com/wp-admin/images/arbbd4a7db75b1640babb7197913dcb6955/arb97913dcb6955/index2.php?l=_JeHFUq_VJOXK0QWHtoGYDw1774256418&fid.13InboxLight.aspxn.1774256418&fid.125289964252813InboxLight99642_Product-email&email= | IR | html | 5.16 Kb | suspicious |
3252 | iexplore.exe | GET | 200 | 216.58.206.10:80 | http://fonts.googleapis.com/css?family=Raleway:100,300,400,500%7CLato:300,400 | US | text | 197 b | whitelisted |
2972 | iexplore.exe | GET | 200 | 164.138.20.168:80 | http://mansoursaveh.com/wp-admin/setup-config.php | IR | html | 13.4 Kb | suspicious |
2240 | chrome.exe | GET | 200 | 164.138.20.168:80 | http://mansoursaveh.com/wp-admin/images/arbbd4a7db75b1640babb7197913dcb6955/arb97913dcb6955/index2.php?l=_JeHFUq_VJOXK0QWHtoGYDw1774256418&fid.13InboxLight.aspxn.1774256418&fid.125289964252813InboxLight99642_Product-email&email= | IR | html | 5.16 Kb | suspicious |
3252 | iexplore.exe | GET | 200 | 164.138.20.168:80 | http://mansoursaveh.com/wp-admin/images/arbbd4a7db75b1640babb7197913dcb6955/arb97913dcb6955/assets/css/theDocs.all.min.css | IR | text | 202 Kb | suspicious |
3252 | iexplore.exe | GET | 200 | 164.138.20.168:80 | http://mansoursaveh.com/wp-admin/images/arbbd4a7db75b1640babb7197913dcb6955/arb97913dcb6955/assets/css/custom.css | IR | text | 1.72 Kb | suspicious |
3252 | iexplore.exe | GET | 200 | 164.138.20.168:80 | http://mansoursaveh.com/wp-admin/images/arbbd4a7db75b1640babb7197913dcb6955/arb97913dcb6955/assets/js/theDocs.all.min.js | IR | text | 221 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2240 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2240 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2972 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3252 | iexplore.exe | 164.138.20.168:80 | mansoursaveh.com | Ravand Tazeh Co,.PJS. | IR | suspicious |
3252 | iexplore.exe | 216.58.206.10:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3252 | iexplore.exe | 91.198.174.208:443 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
2240 | chrome.exe | 172.217.23.142:443 | apis.google.com | Google Inc. | US | whitelisted |
2240 | chrome.exe | 216.58.206.10:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2240 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2240 | chrome.exe | 164.138.20.168:80 | mansoursaveh.com | Ravand Tazeh Co,.PJS. | IR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
mansoursaveh.com |
| suspicious |
fonts.googleapis.com |
| whitelisted |
upload.wikimedia.org |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
4 ETPRO signatures available at the full report