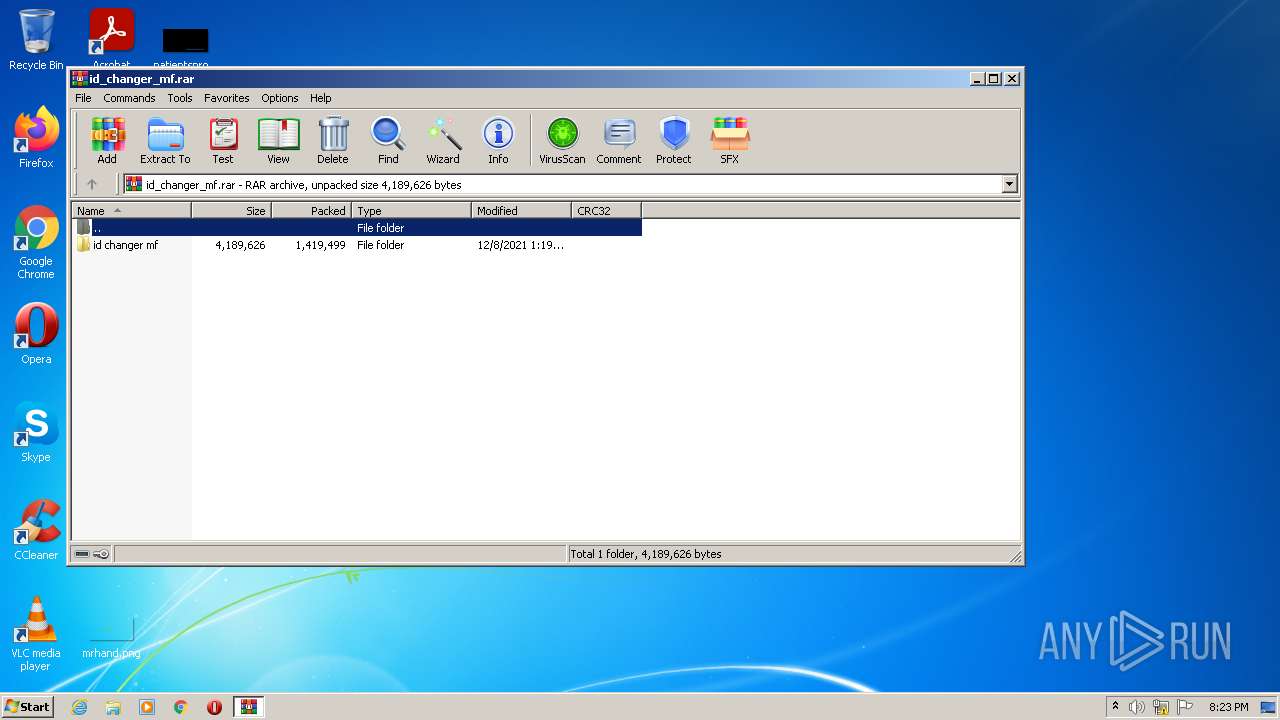
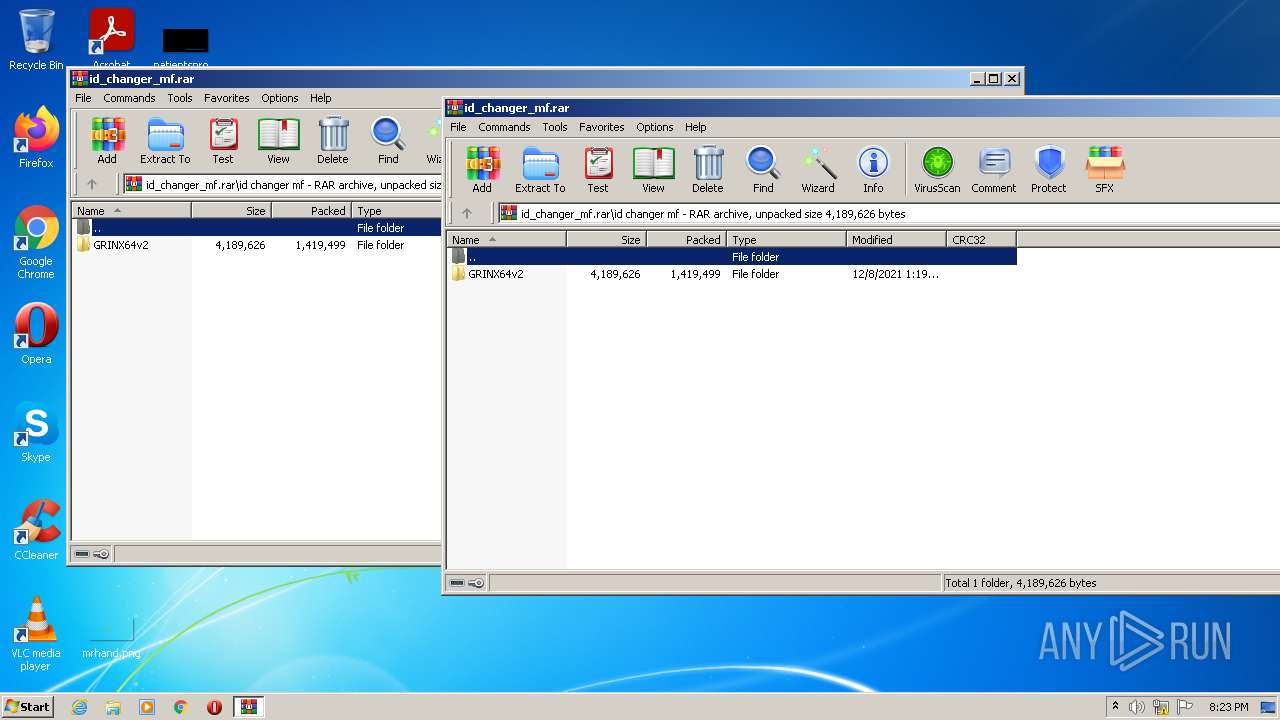
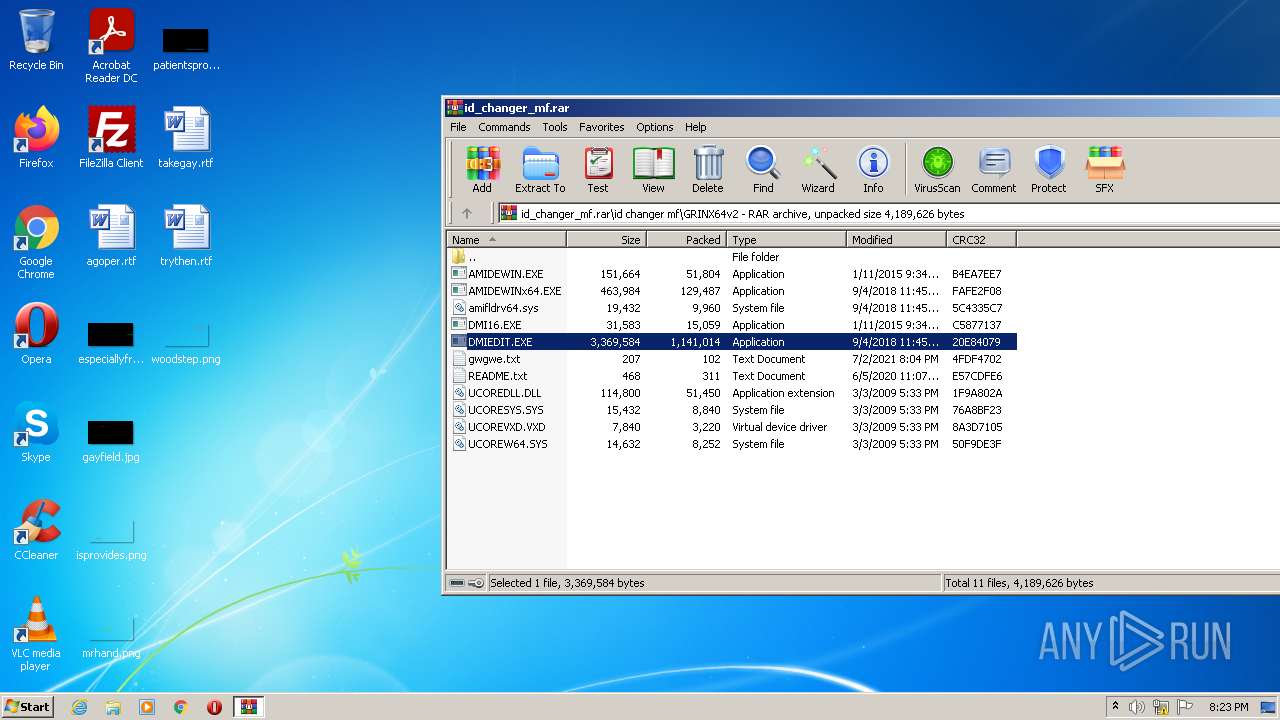
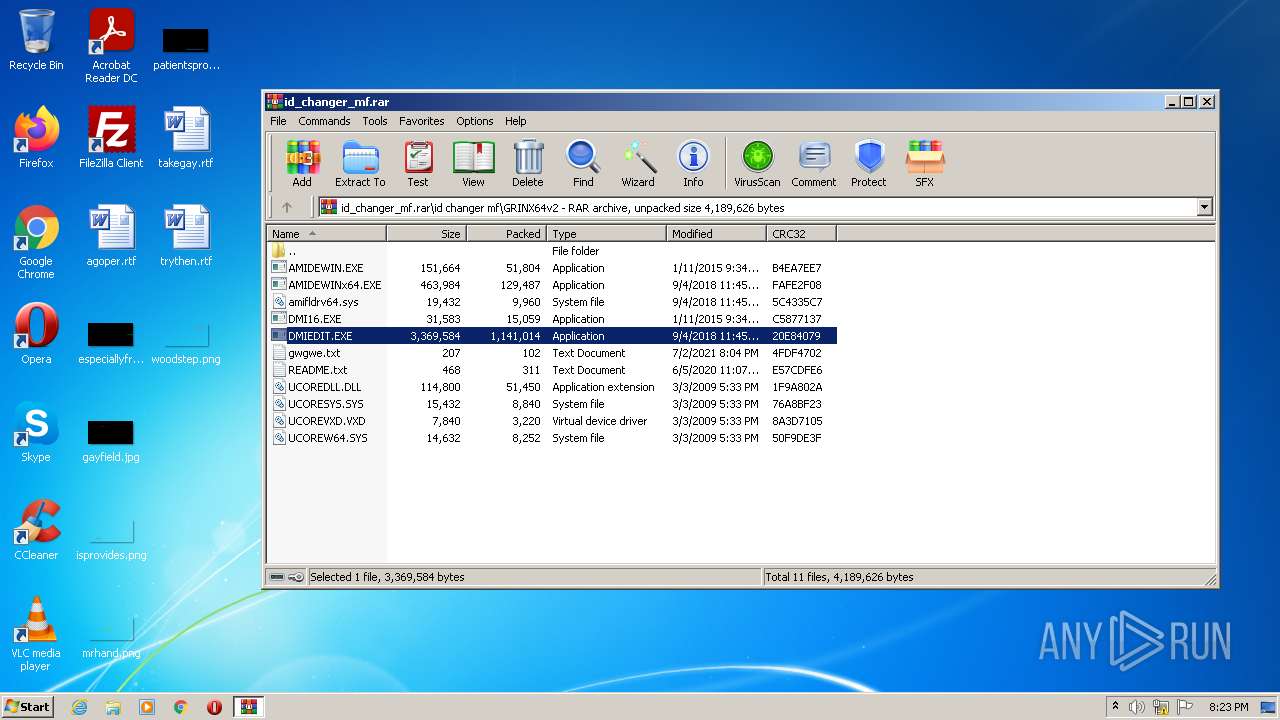
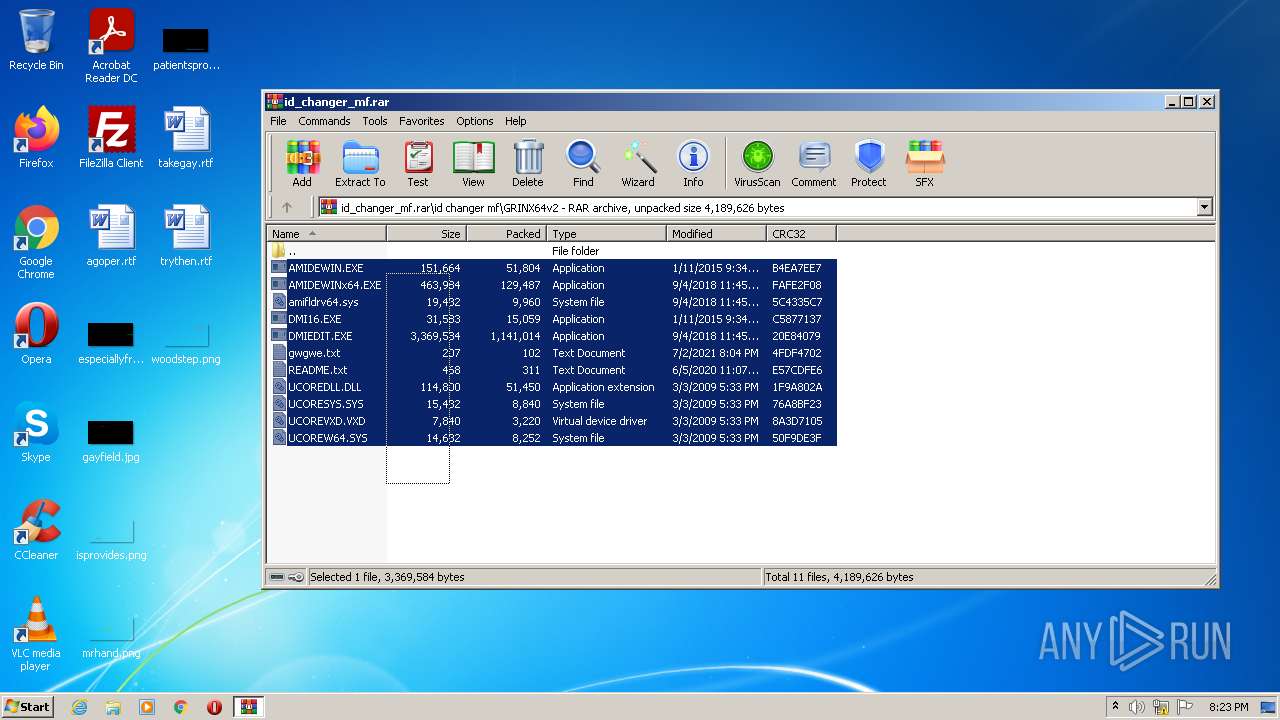
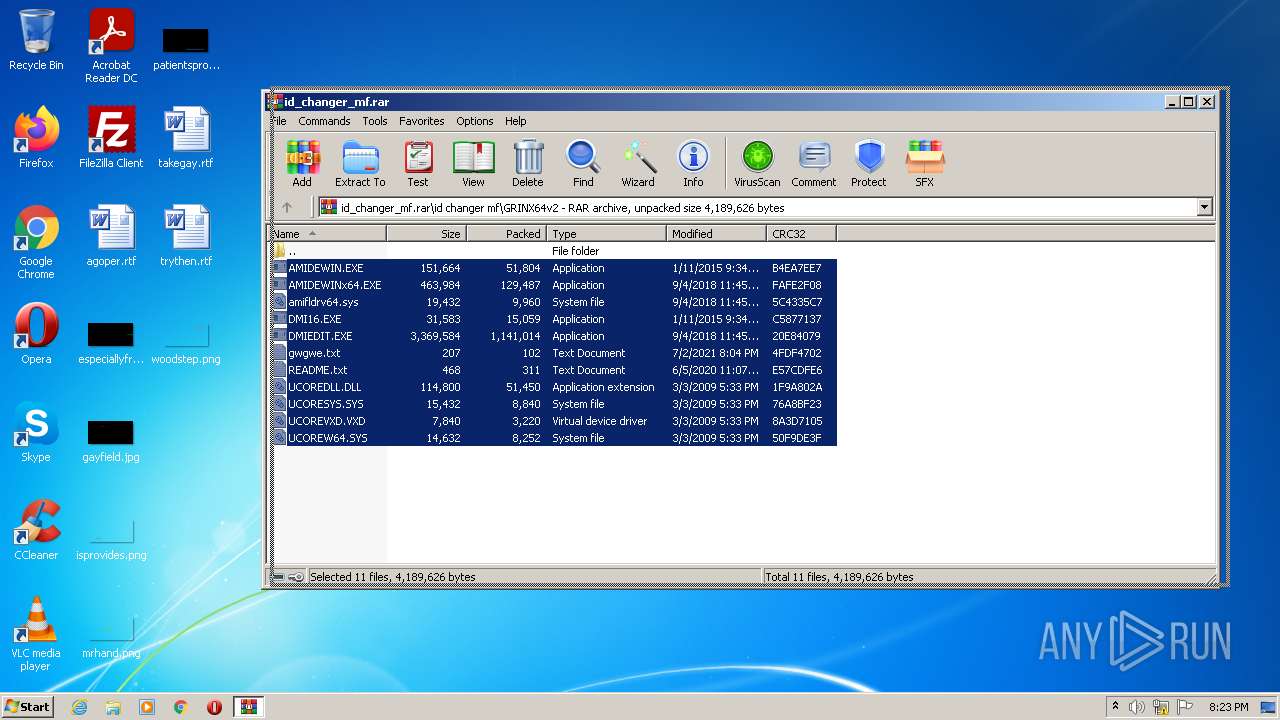
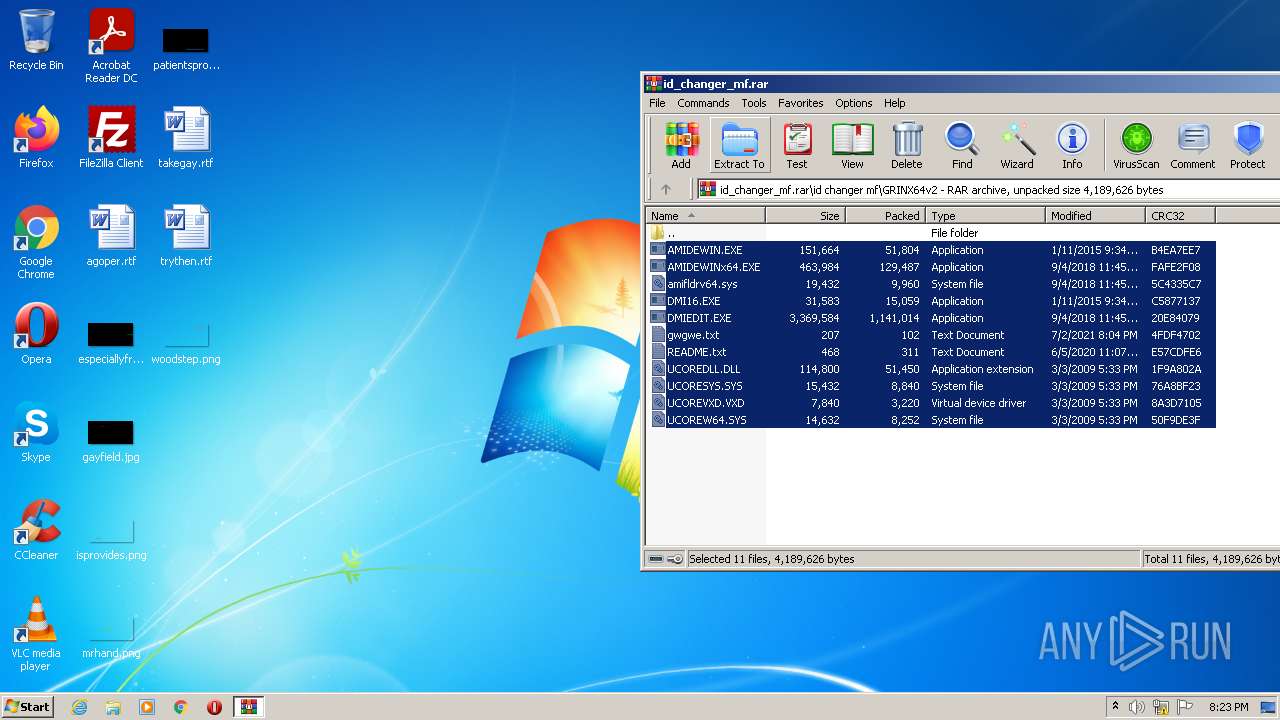
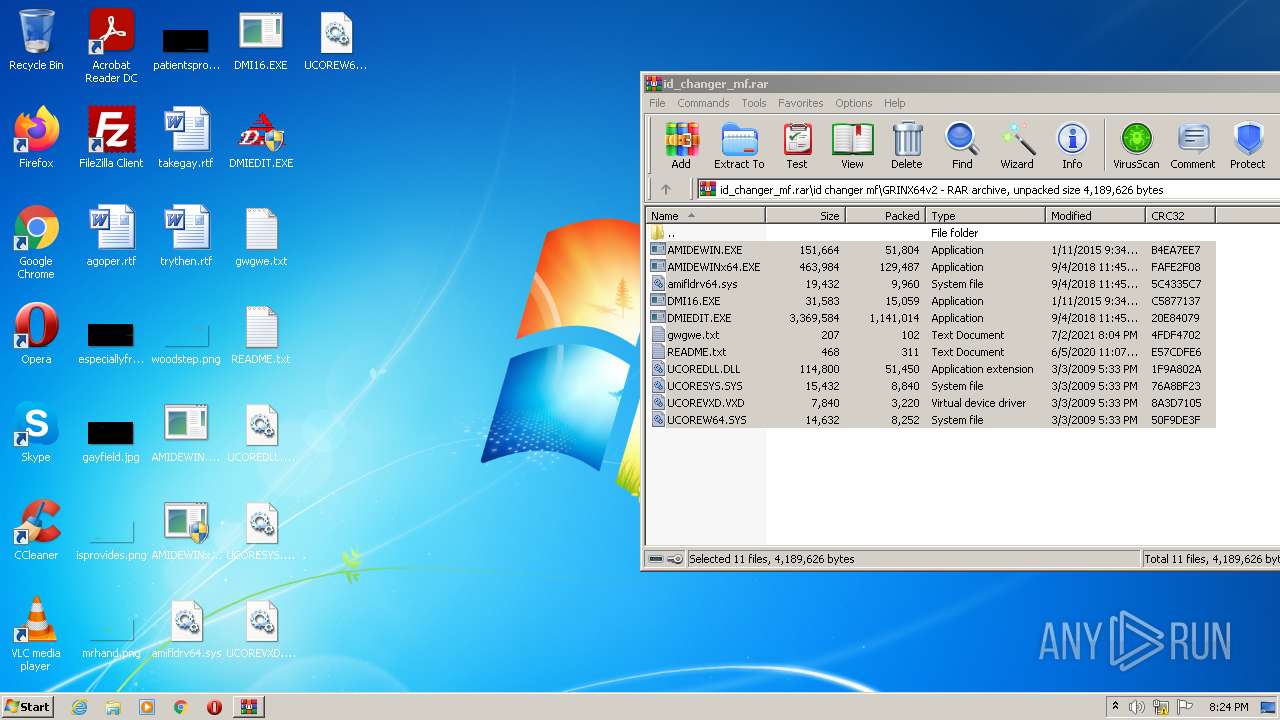
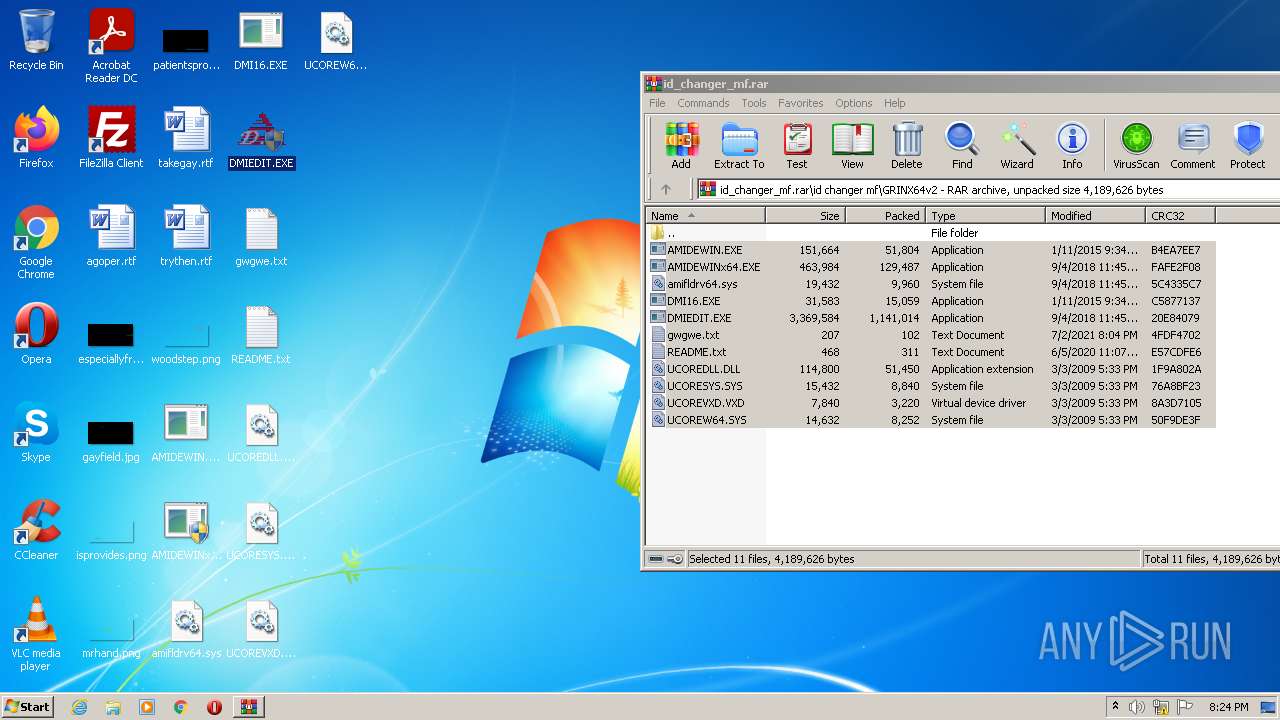
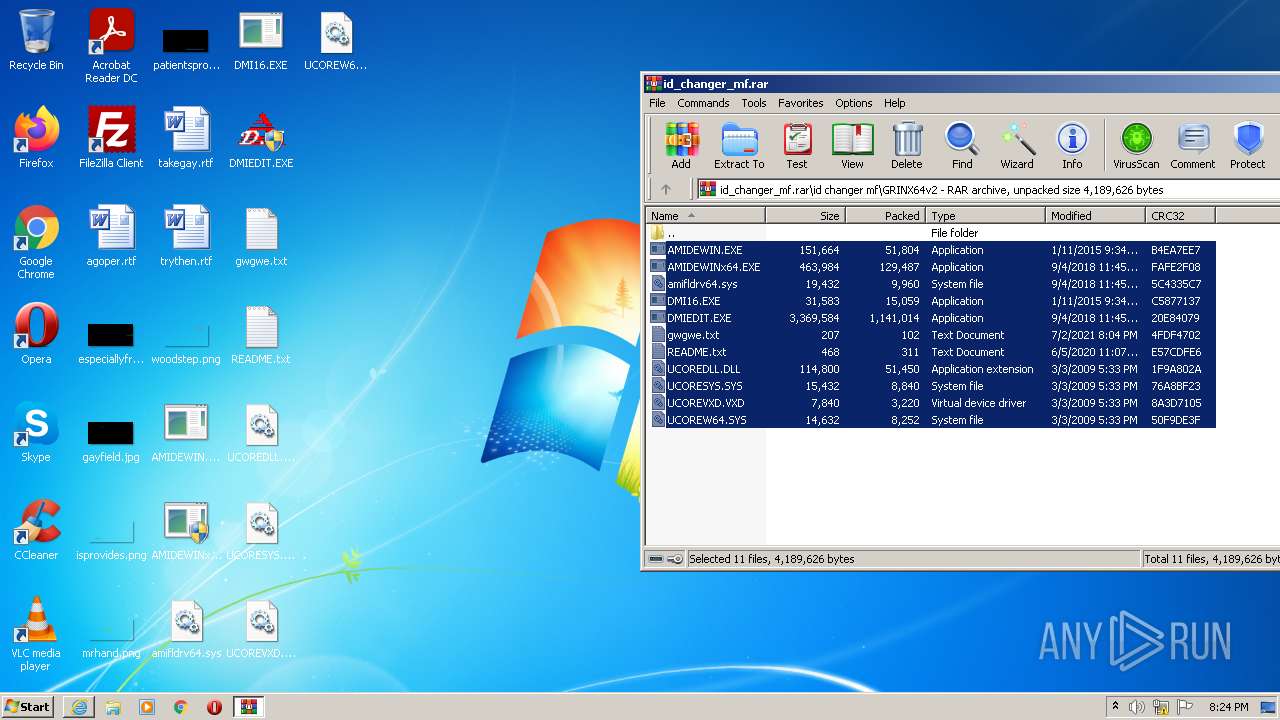
| File name: | id_changer_mf.rar |
| Full analysis: | https://app.any.run/tasks/977fee01-4ea1-40b2-a9c1-251ea40a682c |
| Verdict: | Malicious activity |
| Analysis date: | December 29, 2021, 20:23:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | ABE2DA8539C6BD2765D55AA9943171E5 |
| SHA1: | 242D30872631FA0C0343D5C7CF0169B3700575BB |
| SHA256: | 81F79360944F715CB909574CBBAB77E395287C933D13FF6AC8D9632EDE62769E |
| SSDEEP: | 24576:A7xzUO5m+yKlyt7qtod13mlEUPIgBe5B1EB2TsTx3RKEeSb6s2Fv87L/wpOBL:A7xzUezyKly4udGHPlBeNBYTqEeW6s24 |
MALICIOUS
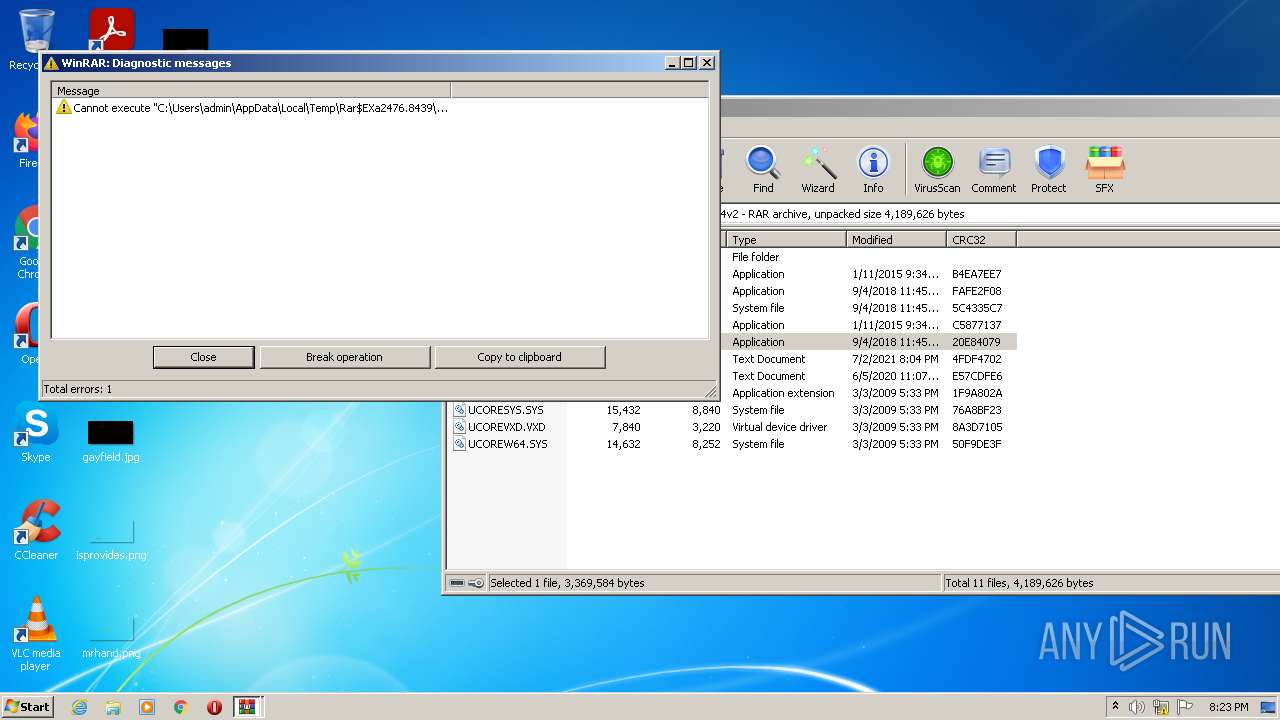
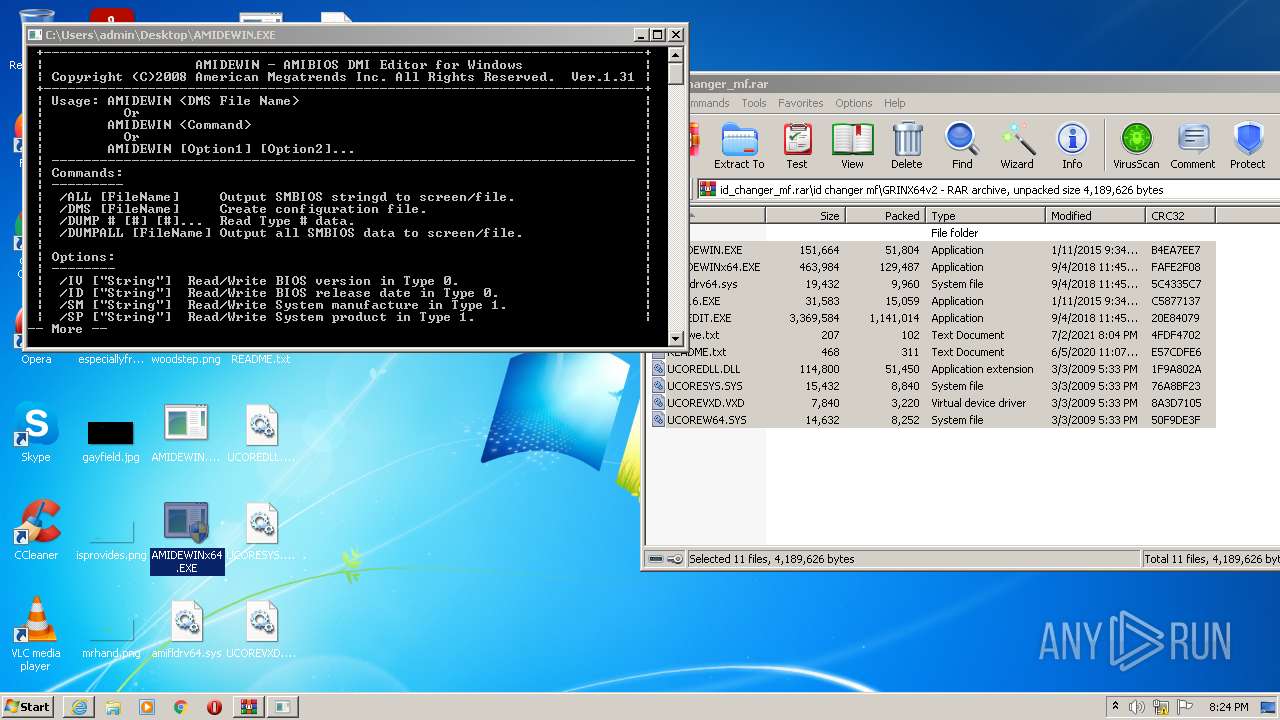
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3400)
Application was dropped or rewritten from another process
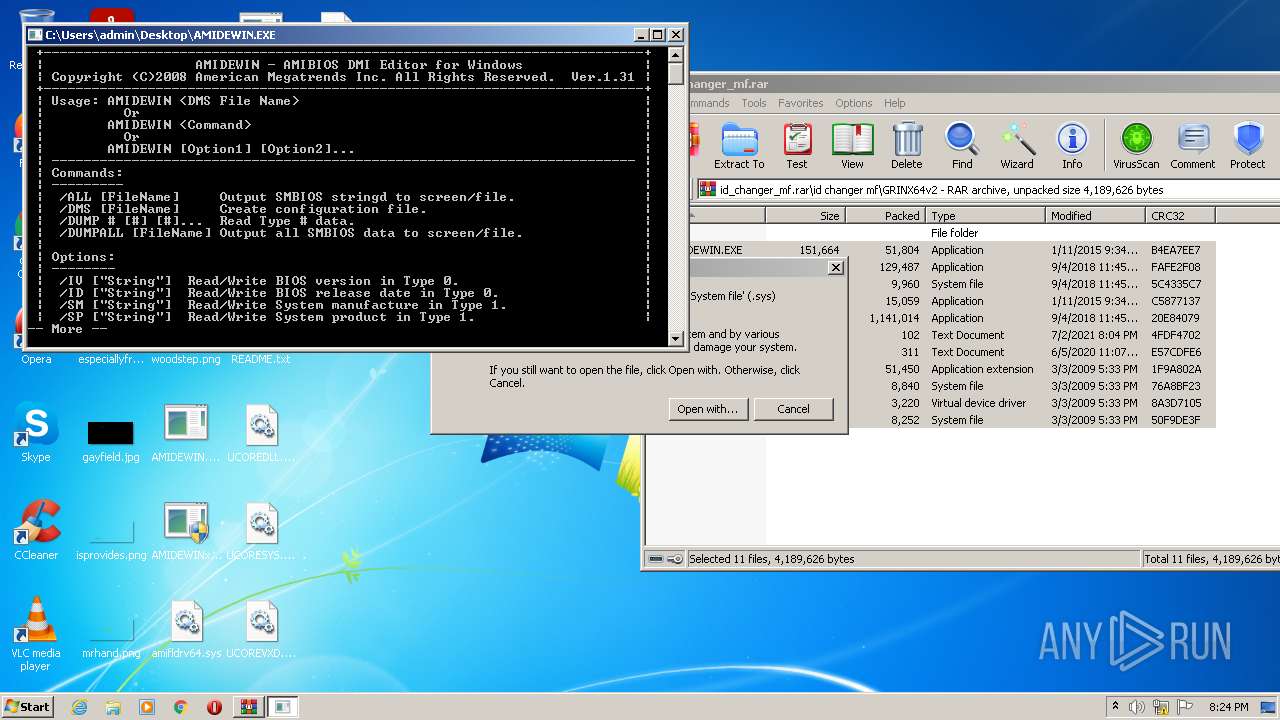
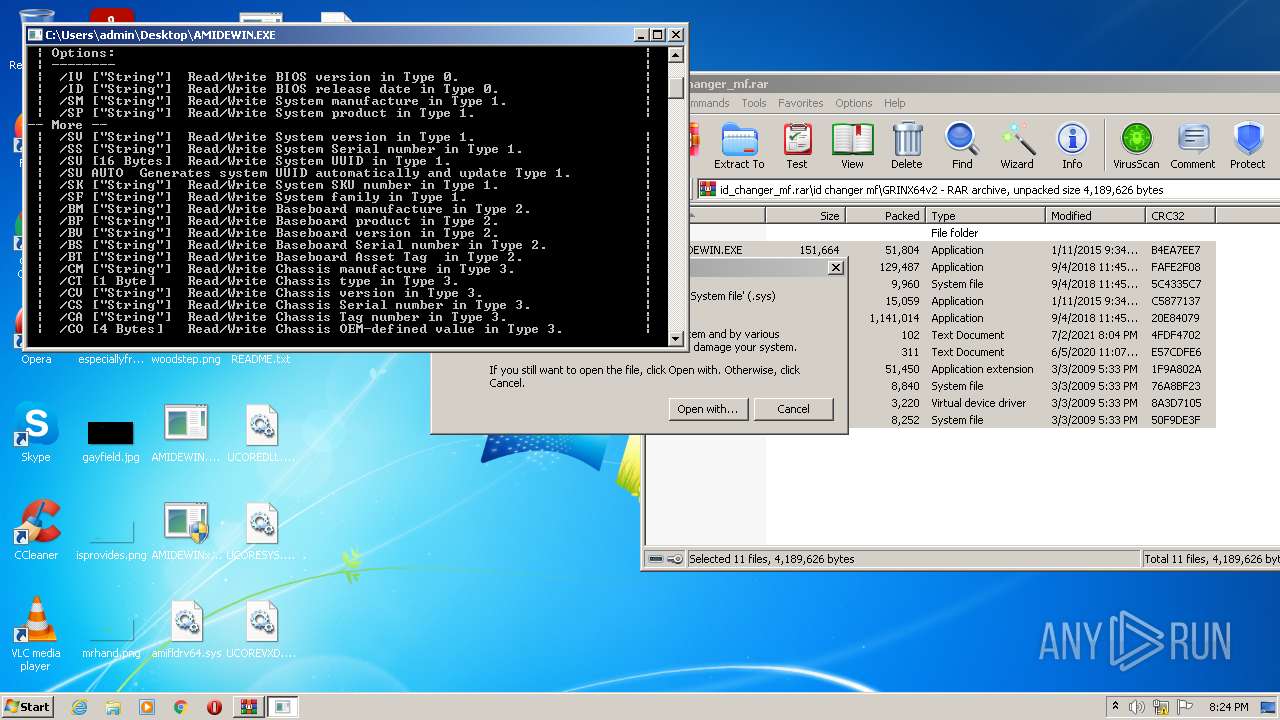
- AMIDEWIN.EXE (PID: 984)
- AMIDEWIN.EXE (PID: 3220)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2476)
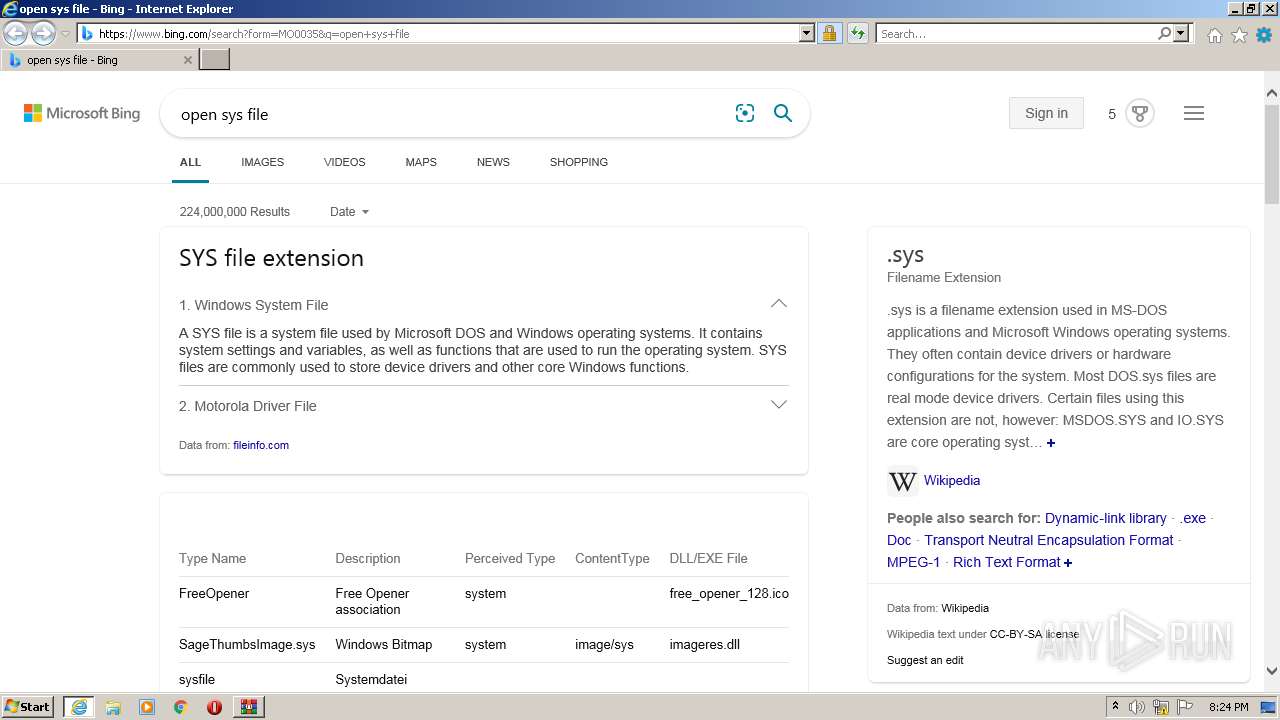
Reads default file associations for system extensions
- WinRAR.exe (PID: 2476)
- SearchProtocolHost.exe (PID: 3400)
- rundll32.exe (PID: 1444)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2476)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2476)
Checks supported languages
- WinRAR.exe (PID: 2476)
- AMIDEWIN.EXE (PID: 984)
- AMIDEWIN.EXE (PID: 3220)
Drops a file with too old compile date
- WinRAR.exe (PID: 2476)
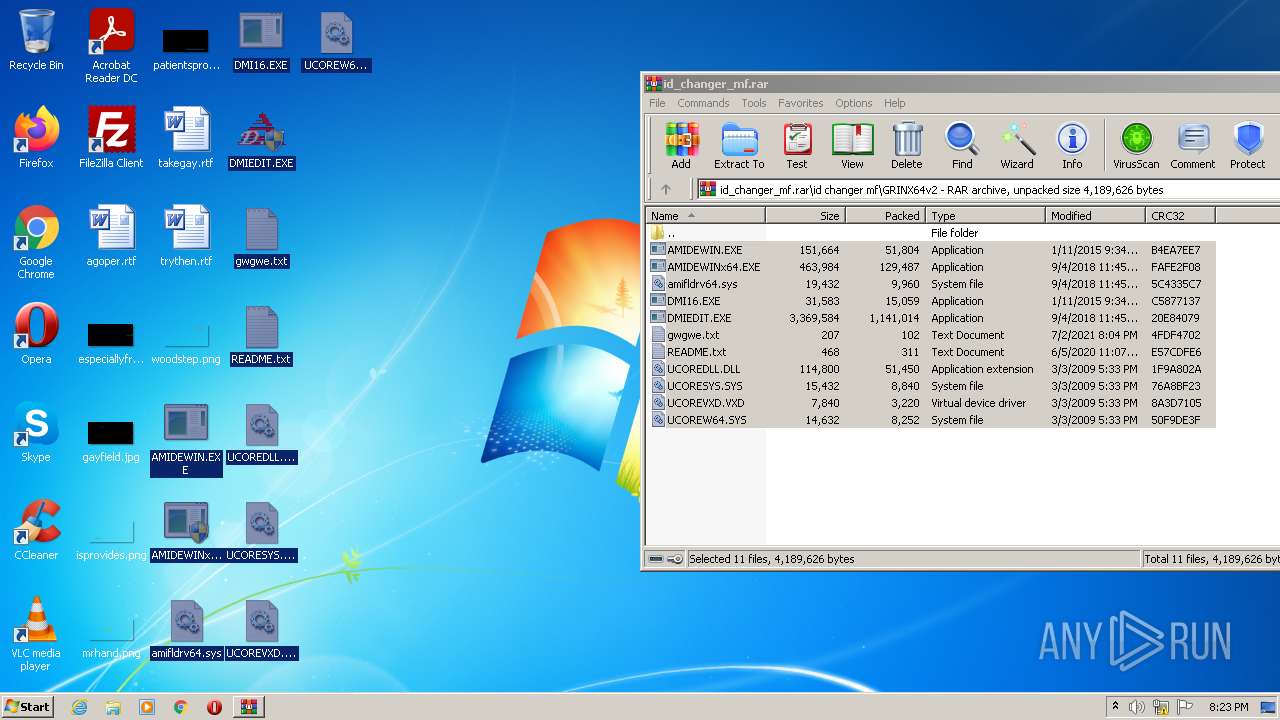
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2476)
Starts Internet Explorer
- rundll32.exe (PID: 1444)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2680)
INFO
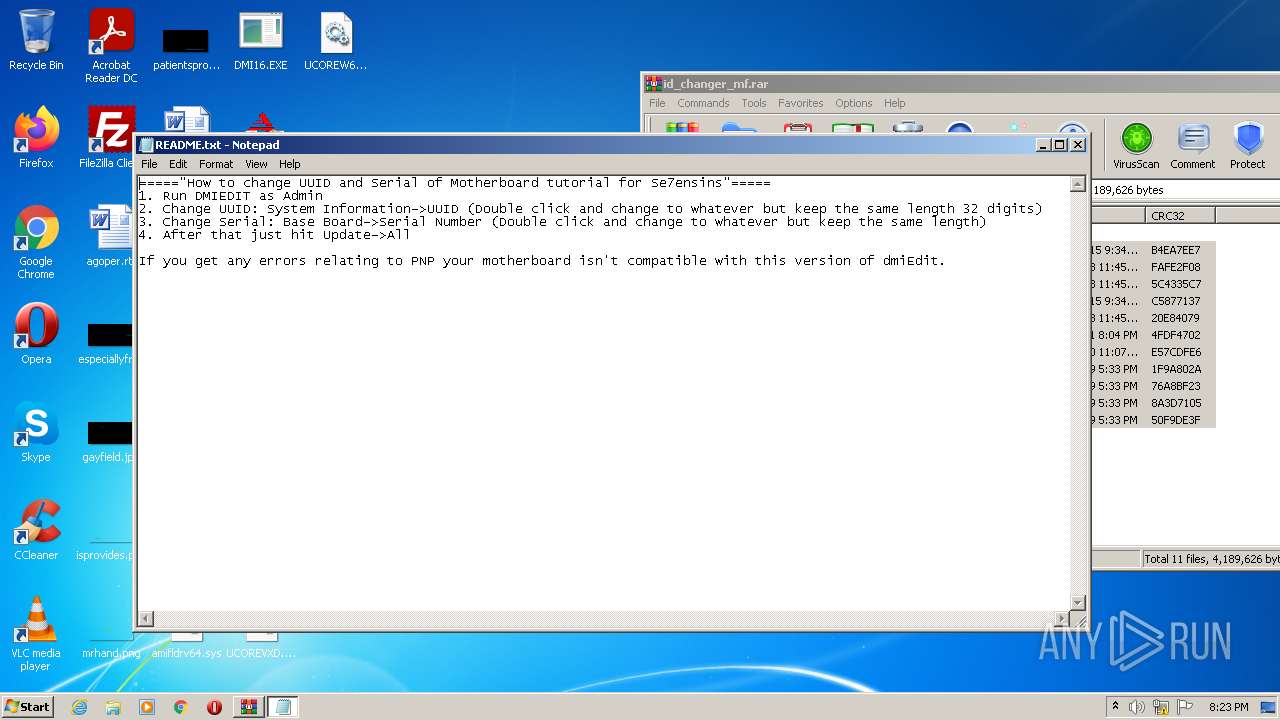
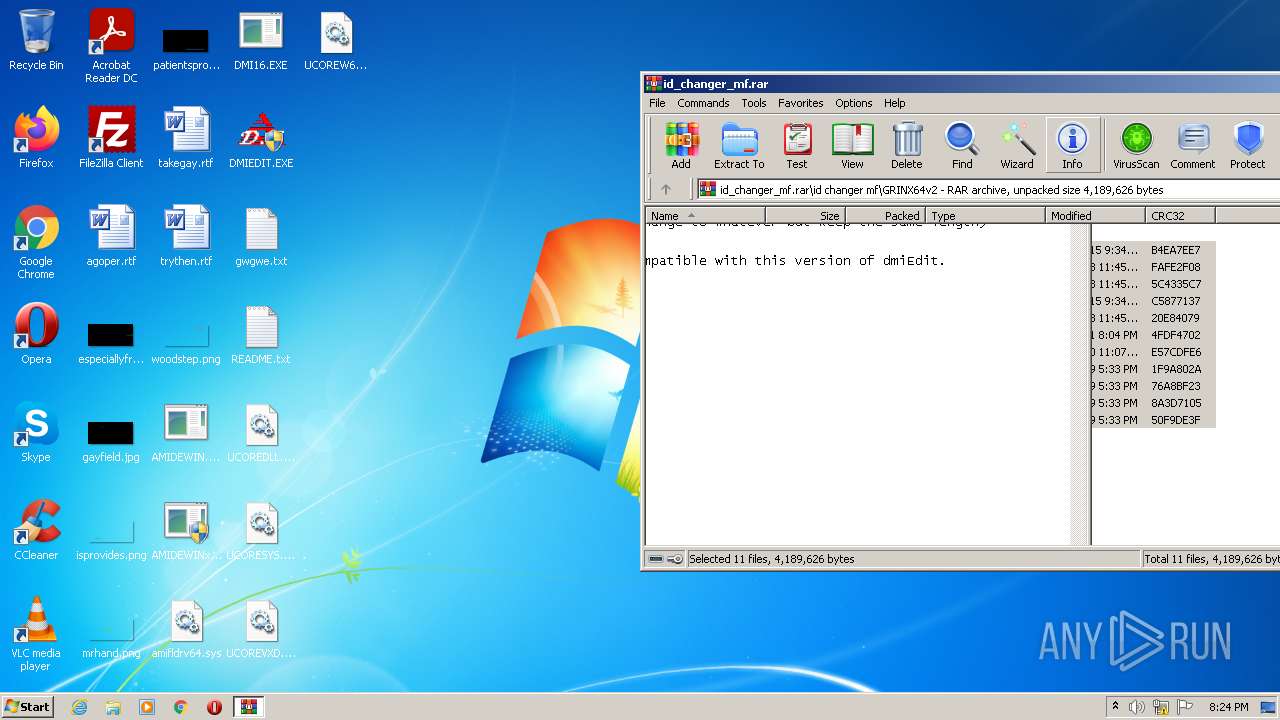
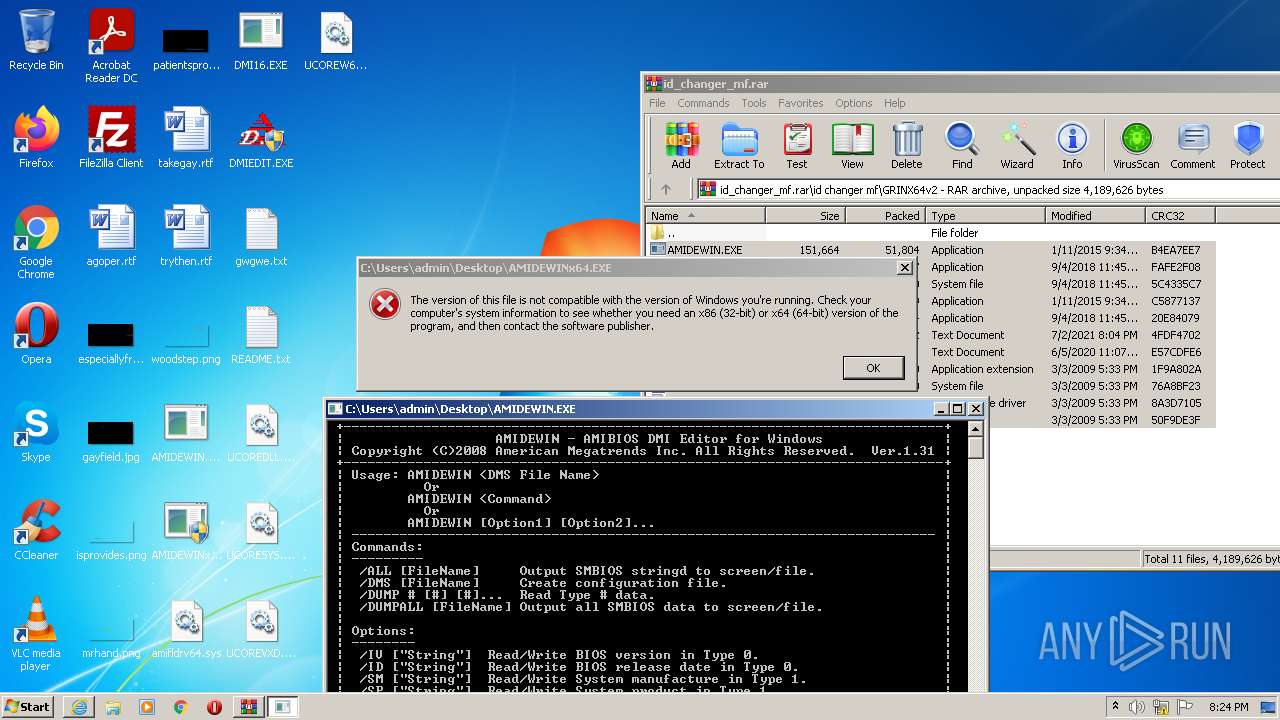
Manual execution by user
- NOTEPAD.EXE (PID: 3720)
- AMIDEWIN.EXE (PID: 984)
- rundll32.exe (PID: 1444)
- AMIDEWIN.EXE (PID: 3220)
Checks supported languages
- iexplore.exe (PID: 1420)
- NOTEPAD.EXE (PID: 3720)
- rundll32.exe (PID: 1444)
- iexplore.exe (PID: 2680)
Reads the computer name
- rundll32.exe (PID: 1444)
- iexplore.exe (PID: 1420)
- iexplore.exe (PID: 2680)
Changes internet zones settings
- iexplore.exe (PID: 1420)
Application launched itself
- iexplore.exe (PID: 1420)
Checks Windows Trust Settings
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 1420)
Creates files in the user directory
- iexplore.exe (PID: 2680)
Reads settings of System Certificates
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 1420)
Reads internet explorer settings
- iexplore.exe (PID: 2680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
48
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
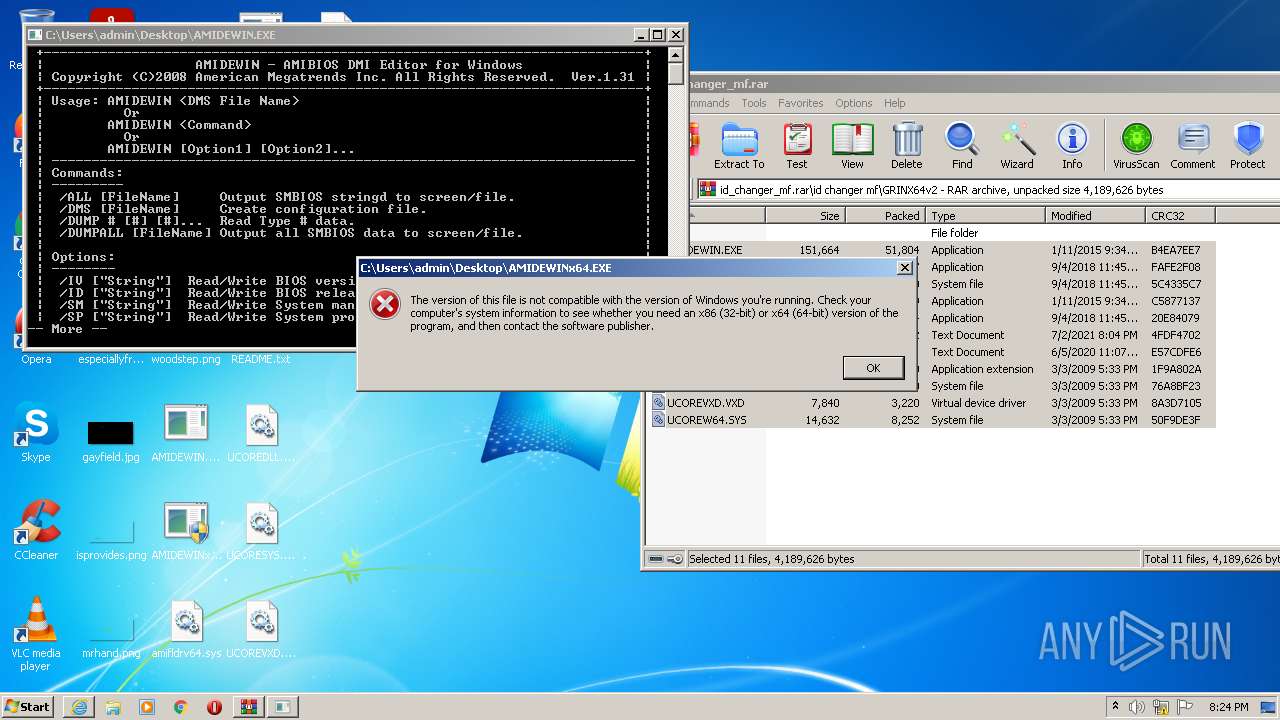
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
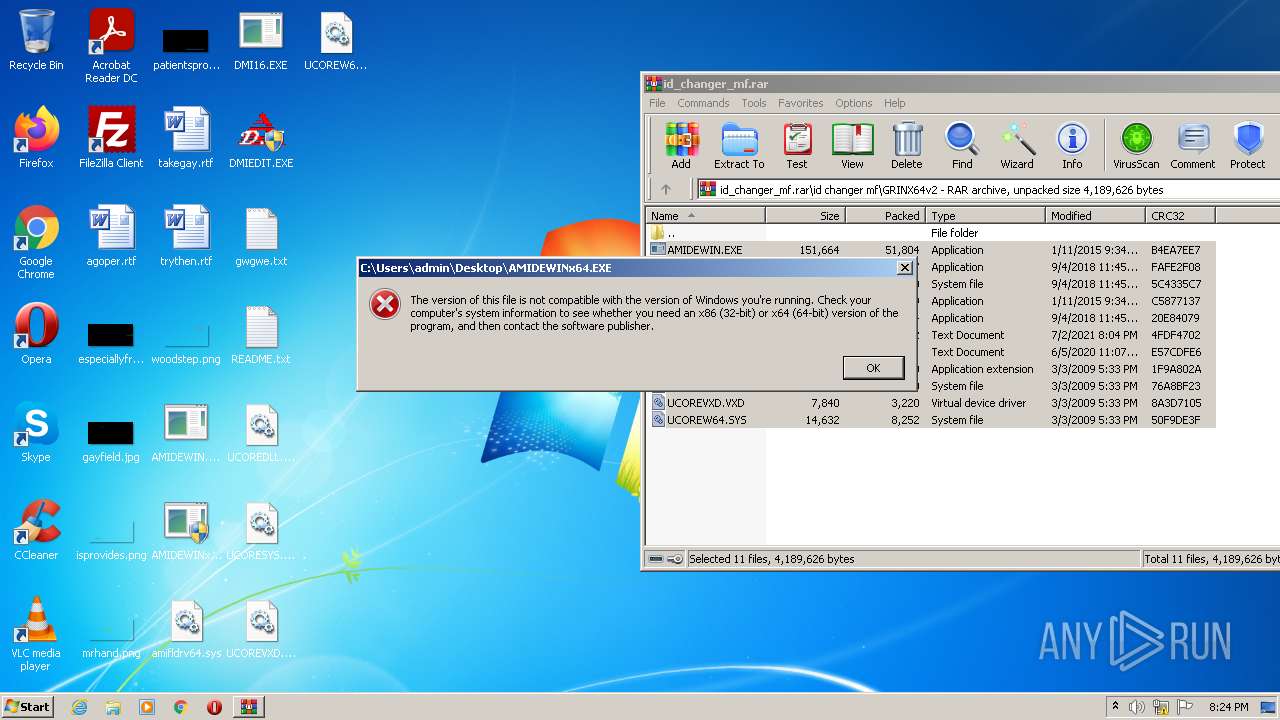
| 984 | "C:\Users\admin\Desktop\AMIDEWIN.EXE" | C:\Users\admin\Desktop\AMIDEWIN.EXE | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=sys | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
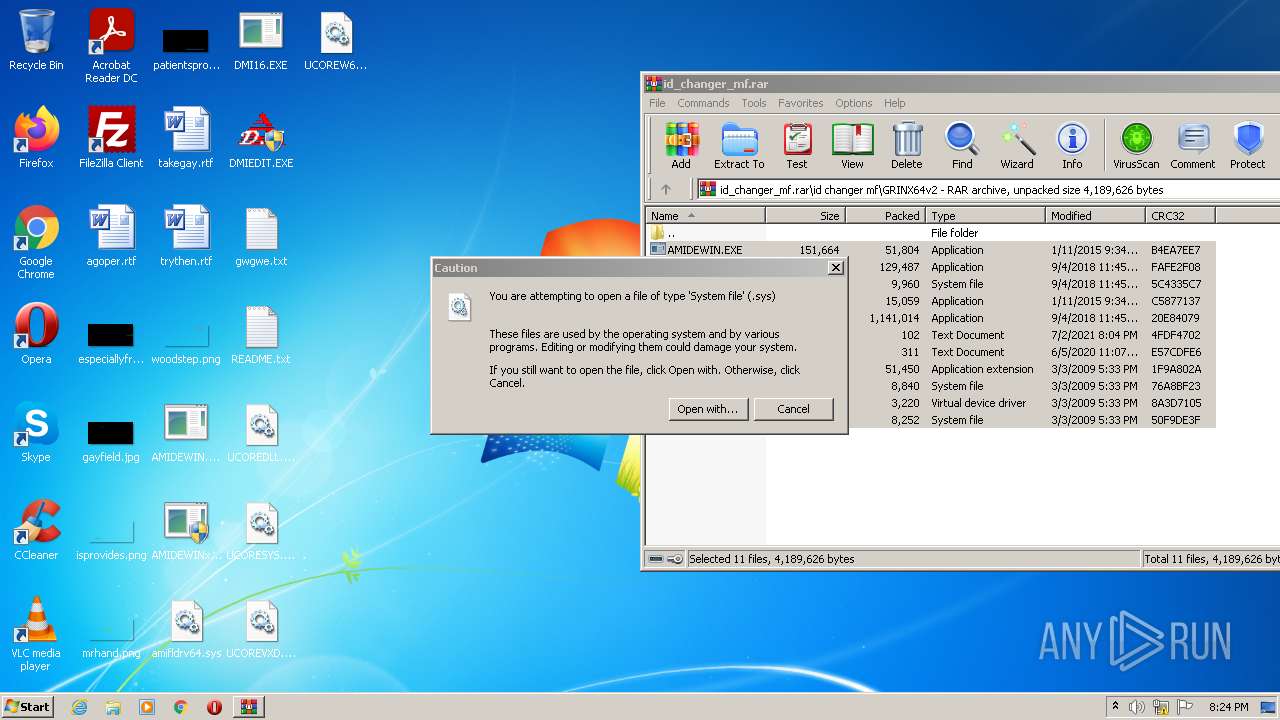
| 1444 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\amifldrv64.sys | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2476 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\id_changer_mf.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1420 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
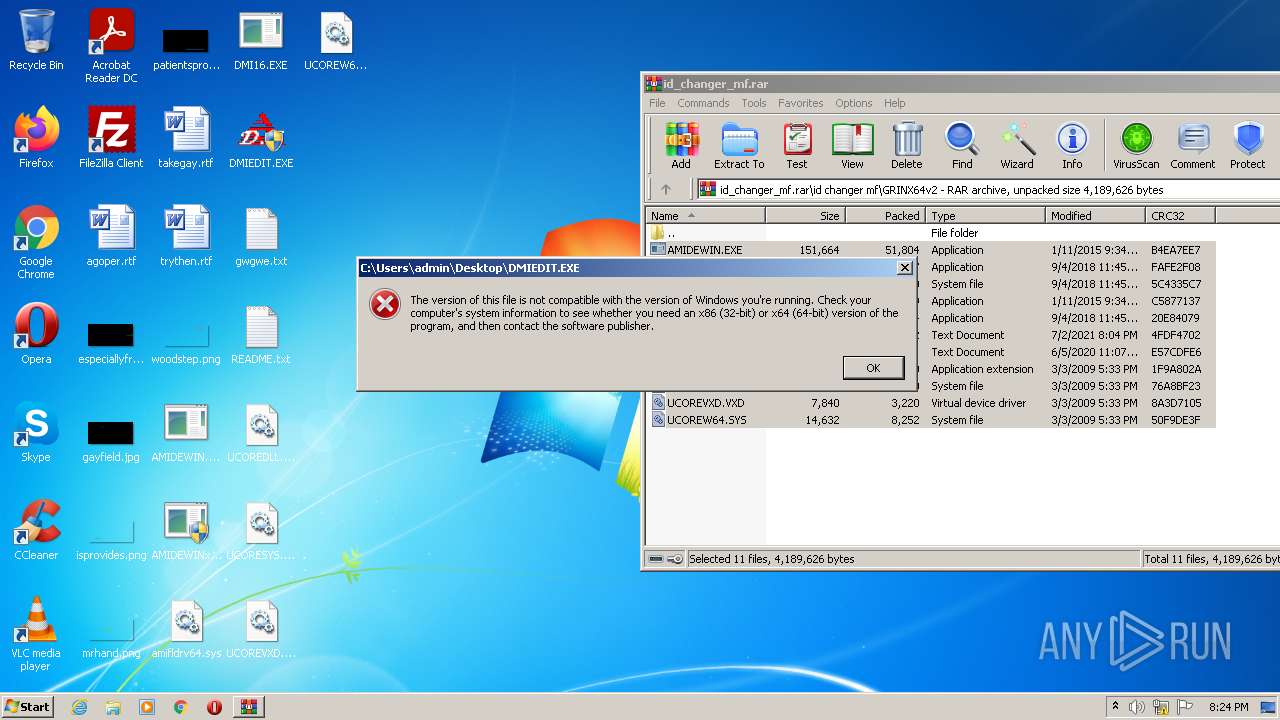
| 3220 | "C:\Users\admin\Desktop\AMIDEWIN.EXE" | C:\Users\admin\Desktop\AMIDEWIN.EXE | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3400 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 3720 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\README.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 750
Read events
10 646
Write events
104
Delete events
0
Modification events
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\id_changer_mf.rar | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
18
Suspicious files
5
Text files
114
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
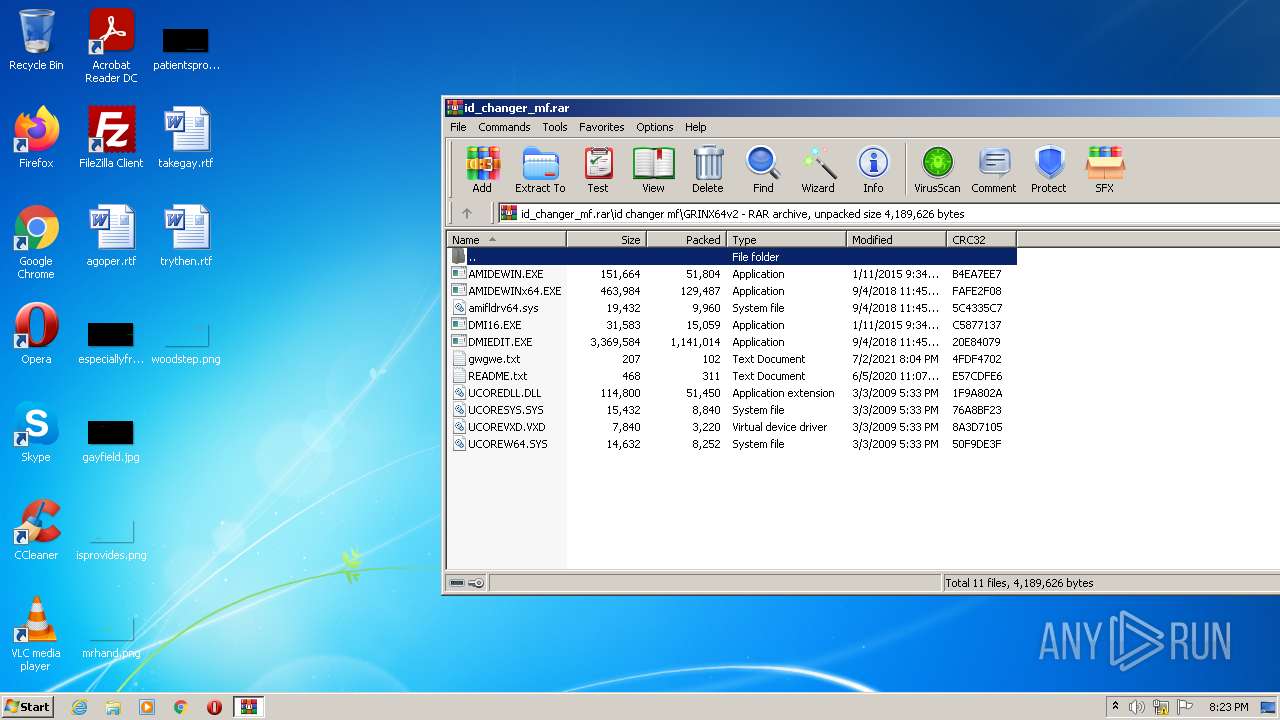
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.8439\id changer mf\GRINX64v2\gwgwe.txt | text | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2476.9309\id changer mf\GRINX64v2\gwgwe.txt | text | |
MD5:— | SHA256:— | |||
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.8439\id changer mf\GRINX64v2\AMIDEWIN.EXE | executable | |
MD5:182EC3A59BD847FB1BC3E12A41D48FA6 | SHA256:948DBD2BC128F8DC08267E110020FEE3FF5DE17CF4AAEF89372DE29623AF96FA | |||
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.8439\id changer mf\GRINX64v2\DMIEDIT.EXE | executable | |
MD5:FBAF6262FD84F9966338518D4DE46FDD | SHA256:5D37E5E7CE01549965BF2166ADCBA33D1E2C4BD2C90711032F3987B58452CE49 | |||
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.8439\id changer mf\GRINX64v2\UCOREW64.SYS | executable | |
MD5:A17C58C0582EE560C72F60764ED63224 | SHA256:A7C8F4FAF3CBB088CAC7753D81F8EC4C38CCB97CD9DA817741F49272E8D01200 | |||
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.8439\id changer mf\GRINX64v2\amifldrv64.sys | executable | |
MD5:785045F8B25CD2E937DDC6B09DEBE01A | SHA256:37073E42FFA0322500F90CD7E3C8D02C4CDD695D31C77E81560ABEC20BFB68BA | |||
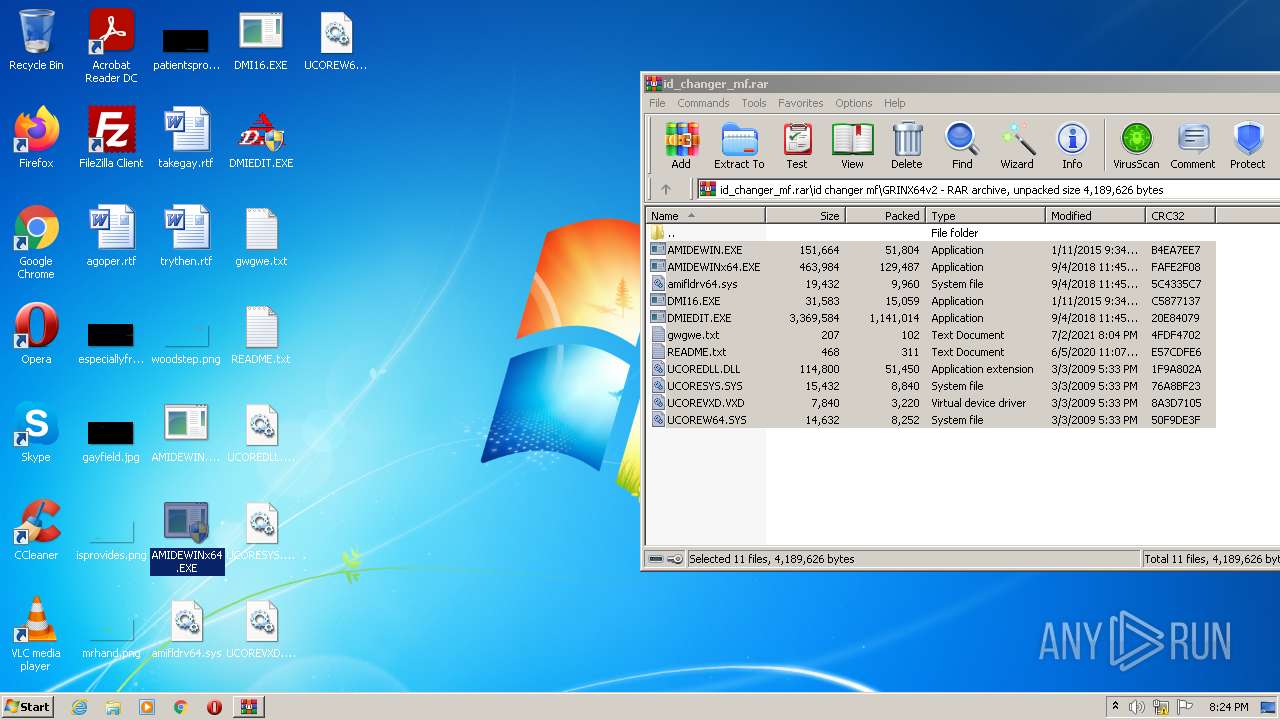
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.8439\id changer mf\GRINX64v2\AMIDEWINx64.EXE | executable | |
MD5:6A6505B2413D2C7B16C6D059448DB9E5 | SHA256:53E3B72F8EB13ACF3CB69D4CB124E8DC64FC541555C3C95CC8003B8046853955 | |||
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.8439\id changer mf\GRINX64v2\UCORESYS.SYS | executable | |
MD5:9555D36FB21B993E5C4B98C2FC2B3671 | SHA256:FD6F56189CD723B32FC06392867FCD5128E63D8B5801E4F7A83523F820531981 | |||
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2476.9309\id changer mf\GRINX64v2\amifldrv64.sys | executable | |
MD5:785045F8B25CD2E937DDC6B09DEBE01A | SHA256:37073E42FFA0322500F90CD7E3C8D02C4CDD695D31C77E81560ABEC20BFB68BA | |||
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.8439\id changer mf\GRINX64v2\README.txt | text | |
MD5:0E28E605E0988892043002E8D6FA719B | SHA256:1541F150F12295D926578FC8920F2F398D046BDDA66BC3026BF2533BBA07666B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
24
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2680 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2680 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cc69da76b950a3bc | US | compressed | 4.70 Kb | whitelisted |
2680 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2680 | iexplore.exe | GET | 301 | 2.16.186.27:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=sys | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2680 | iexplore.exe | 2.16.186.27:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
2680 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2680 | iexplore.exe | 104.111.242.51:443 | go.microsoft.com | Akamai International B.V. | NL | unknown |
2680 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1420 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2680 | iexplore.exe | 20.190.160.6:443 | login.live.com | Microsoft Corporation | US | suspicious |
2680 | iexplore.exe | 40.126.31.1:443 | login.microsoftonline.com | Microsoft Corporation | US | whitelisted |
— | — | 20.190.159.138:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
api.bing.com |
| whitelisted |