| URL: | https://choogeet.net |
| Full analysis: | https://app.any.run/tasks/91496fa4-d6bf-43bd-90ca-380d5be5da3d |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2024, 12:47:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DDC39125DB9818D8D1955CC92F408565 |
| SHA1: | 54C58441E3181F0F162DC9096437A0C5D794B375 |
| SHA256: | 81F1D845C71865BAFE0C6B2F64148B98CC882EA4492BA6DE49F5C63471DCAED6 |
| SSDEEP: | 3:N8QkAY0:2Qkg |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
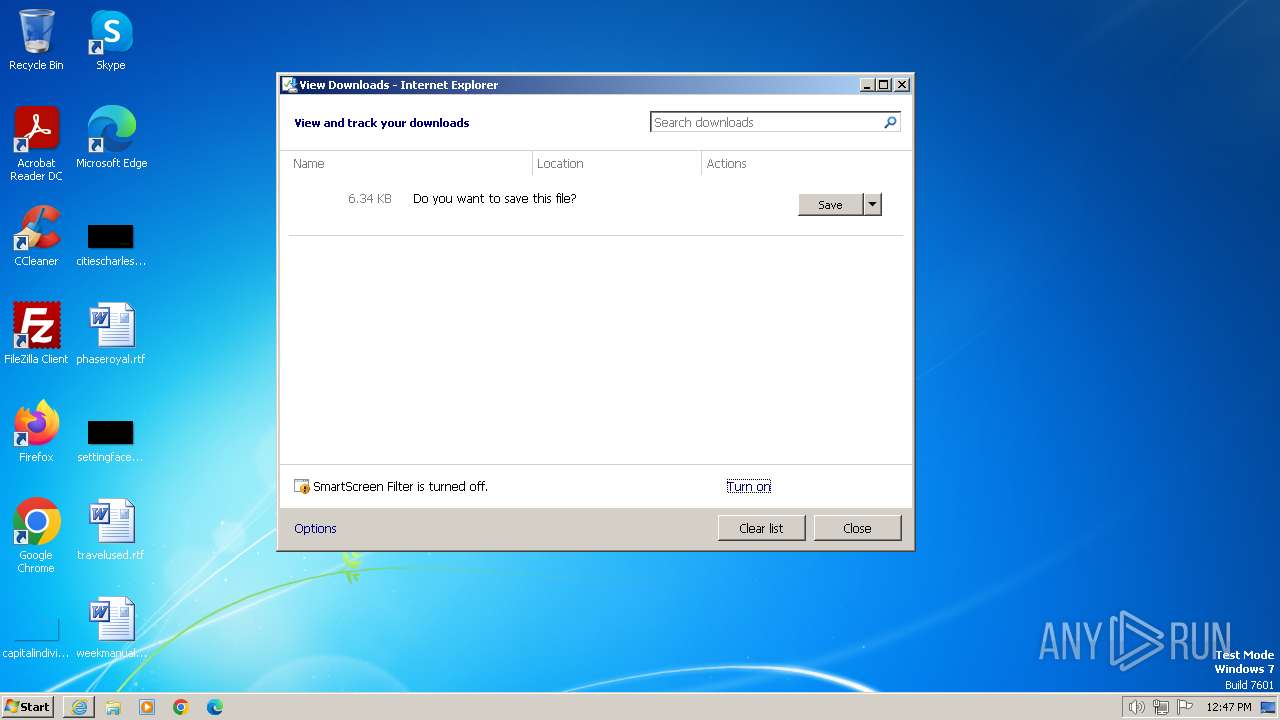
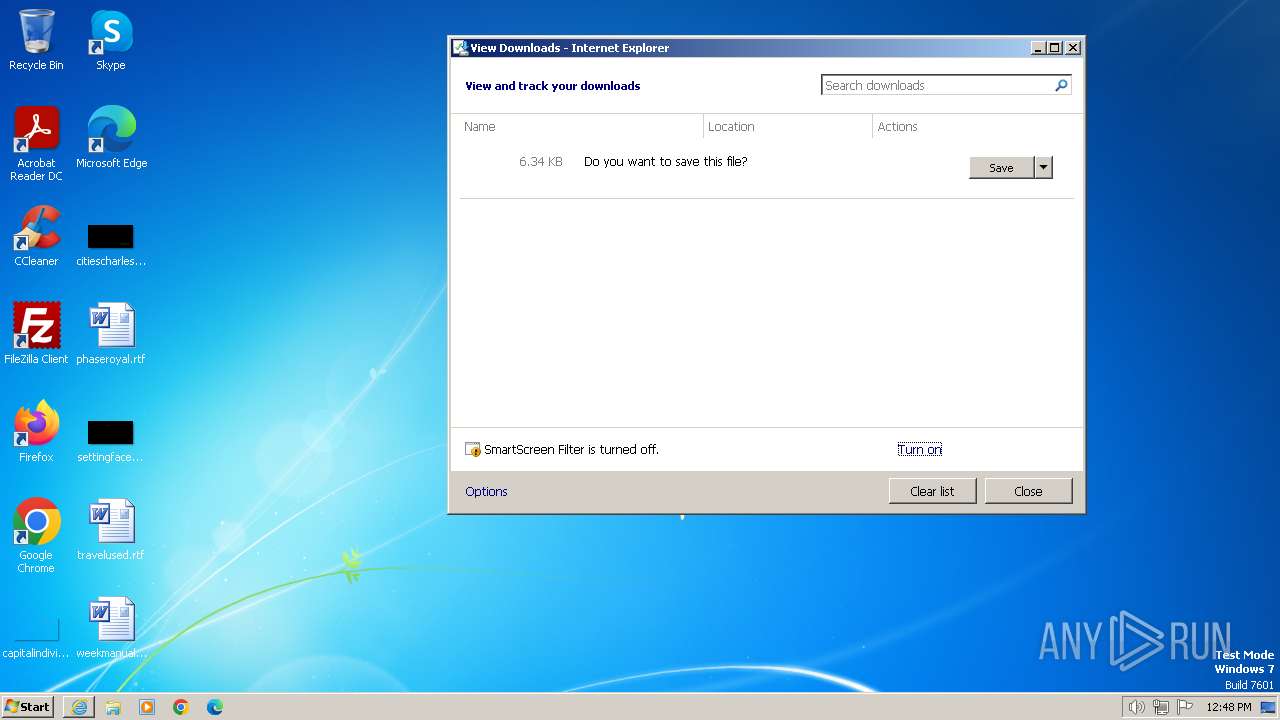
Modifies the phishing filter of IE
- iexplore.exe (PID: 3864)
Manual execution by a user
- explorer.exe (PID: 4044)
Application launched itself
- iexplore.exe (PID: 3864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2044 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3864 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://choogeet.net" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4044 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 504
Read events
15 441
Write events
48
Delete events
15
Modification events
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31093078 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31093078 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
12
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:E0E194DD12D4D608734A3148052847E3 | SHA256:065A2E7E99E1A6800E1B2D52B52DC3F23FB1997B7267A70EB55847AFA67E3C8F | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF493.tmp | compressed | |
MD5:753DF6889FD7410A2E9FE333DA83A429 | SHA256:B42DC237E44CBC9A43400E7D3F9CBD406DBDEFD62BFE87328F8663897D69DF78 | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{1624425F-DD4A-11EE-AE0A-12A9866C77DE}.dat | binary | |
MD5:3CA99B40940C72E834CA5AD63795E5A2 | SHA256:E130C47C40E56A9DAAAEE682B14B0296BC9117D68524342BCEEB2D051AAC33BB | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\09FA610ACA6D337A5EE677336666061D | der | |
MD5:40DC60E1498D5AA917E5D39BC8AA08BB | SHA256:99B3C6B2151935E4821BF56833ABE6C2DC0E529F4C3C639B83744805FEF238E7 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF492.tmp | cat | |
MD5:DD73CEAD4B93366CF3465C8CD32E2796 | SHA256:A6752B7851B591550E4625B832A393AABCC428DE18D83E8593CD540F7D7CAE22 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF491.tmp | compressed | |
MD5:753DF6889FD7410A2E9FE333DA83A429 | SHA256:B42DC237E44CBC9A43400E7D3F9CBD406DBDEFD62BFE87328F8663897D69DF78 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\09FA610ACA6D337A5EE677336666061D | binary | |
MD5:28DCB573F60F46B55826C4E72BD4D7B2 | SHA256:F3802CB9F14155FF3E06E633608284B704C0341D3BE762BE67D37755629BAA18 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:B17D1072FA219D0DD71F4F721D3B8992 | SHA256:16369414EFB27B5093CF2C3F0AF9E66A3C436E3B994C233CAF1833C96AE1F9C3 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFBFAE2FAD31A36D52.TMP | gmc | |
MD5:C11B869E87F939F902701C3A1BB1BE05 | SHA256:4BA846920CCFEDF896C6741E849D885709572BAB68F4B1A7E63414551A978E7A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
11
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | iexplore.exe | GET | 304 | 23.32.238.114:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d362edf7b65e9a48 | unknown | — | — | unknown |
2044 | iexplore.exe | GET | 304 | 23.32.238.147:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?927e0d673a39dd41 | unknown | — | — | unknown |
2044 | iexplore.exe | GET | 200 | 23.32.238.114:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5b0325f31ae0f9b6 | unknown | compressed | 67.5 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 23.32.238.147:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0302b3af7cdfdbed | unknown | compressed | 67.5 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 2.19.217.103:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2044 | iexplore.exe | GET | 200 | 195.138.255.19:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgNhKpCbRBHrGDKMSUJEuaABxA%3D%3D | unknown | binary | 503 b | unknown |
1080 | svchost.exe | GET | 304 | 23.32.238.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3e412f7b4eff0943 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2044 | iexplore.exe | 139.45.197.252:443 | choogeet.net | RETN Limited | GB | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2044 | iexplore.exe | 23.32.238.114:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2044 | iexplore.exe | 23.32.238.147:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2044 | iexplore.exe | 2.19.217.103:80 | x1.c.lencr.org | Akamai International B.V. | NL | unknown |
2044 | iexplore.exe | 195.138.255.19:80 | r3.o.lencr.org | AS33891 Netzbetrieb GmbH | DE | unknown |
1080 | svchost.exe | 23.32.238.163:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
choogeet.net |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |