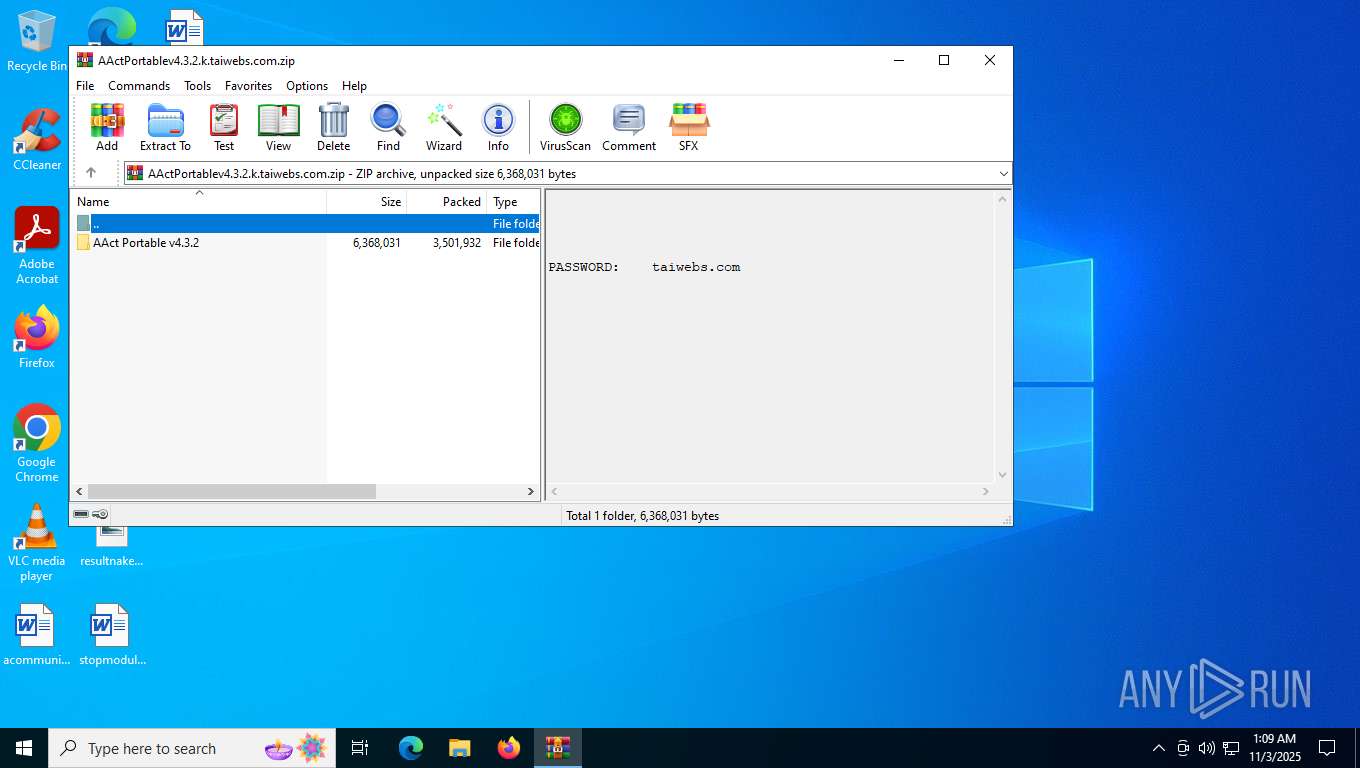
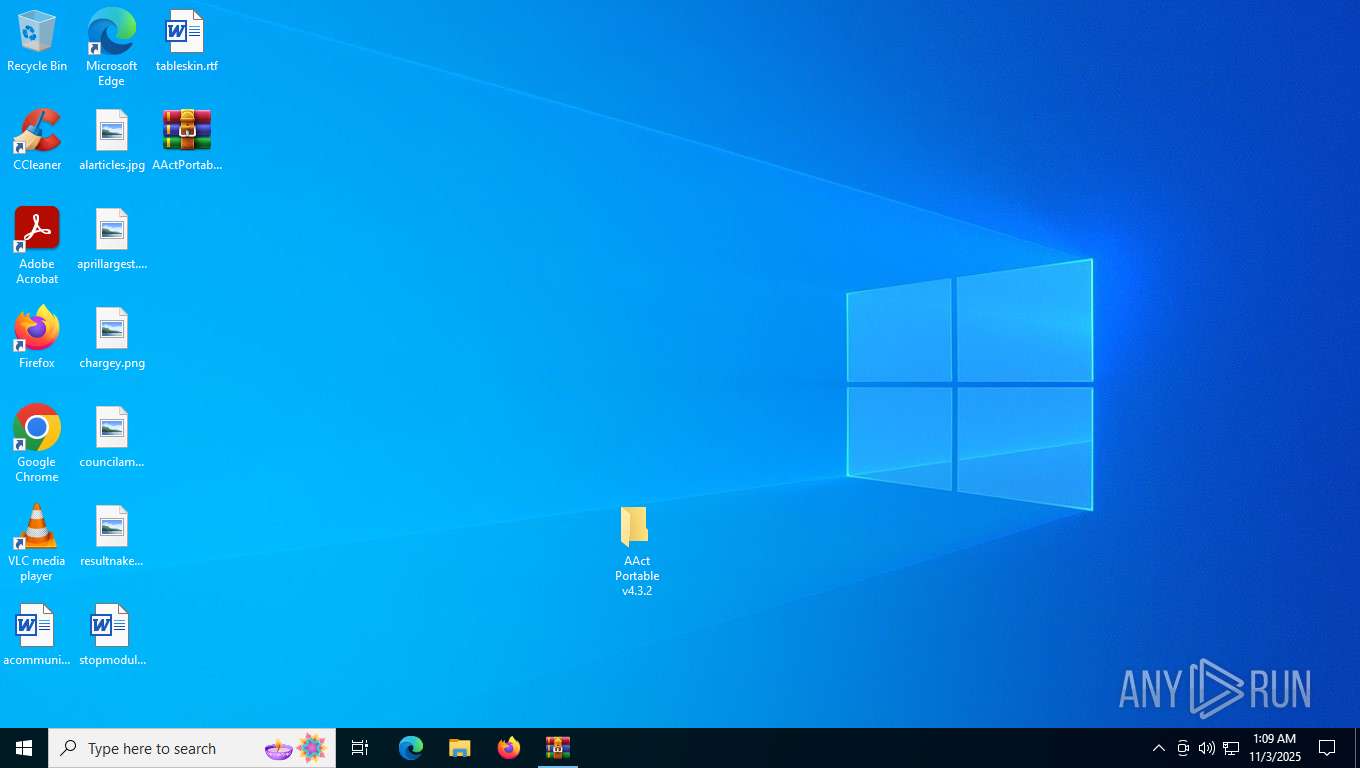
| File name: | AActPortablev4.3.2.k.taiwebs.com.zip |
| Full analysis: | https://app.any.run/tasks/7b0ad4e1-74b6-41c6-81fb-28631f7aae00 |
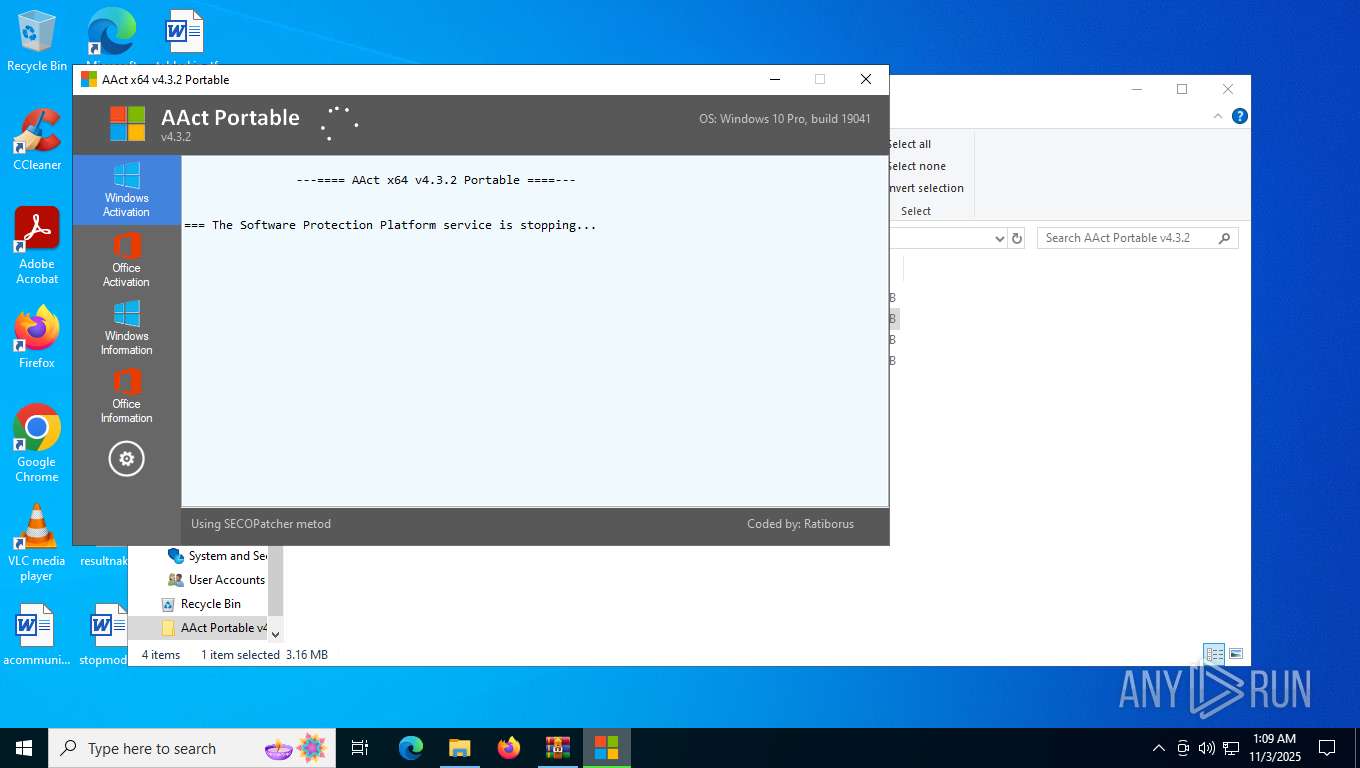
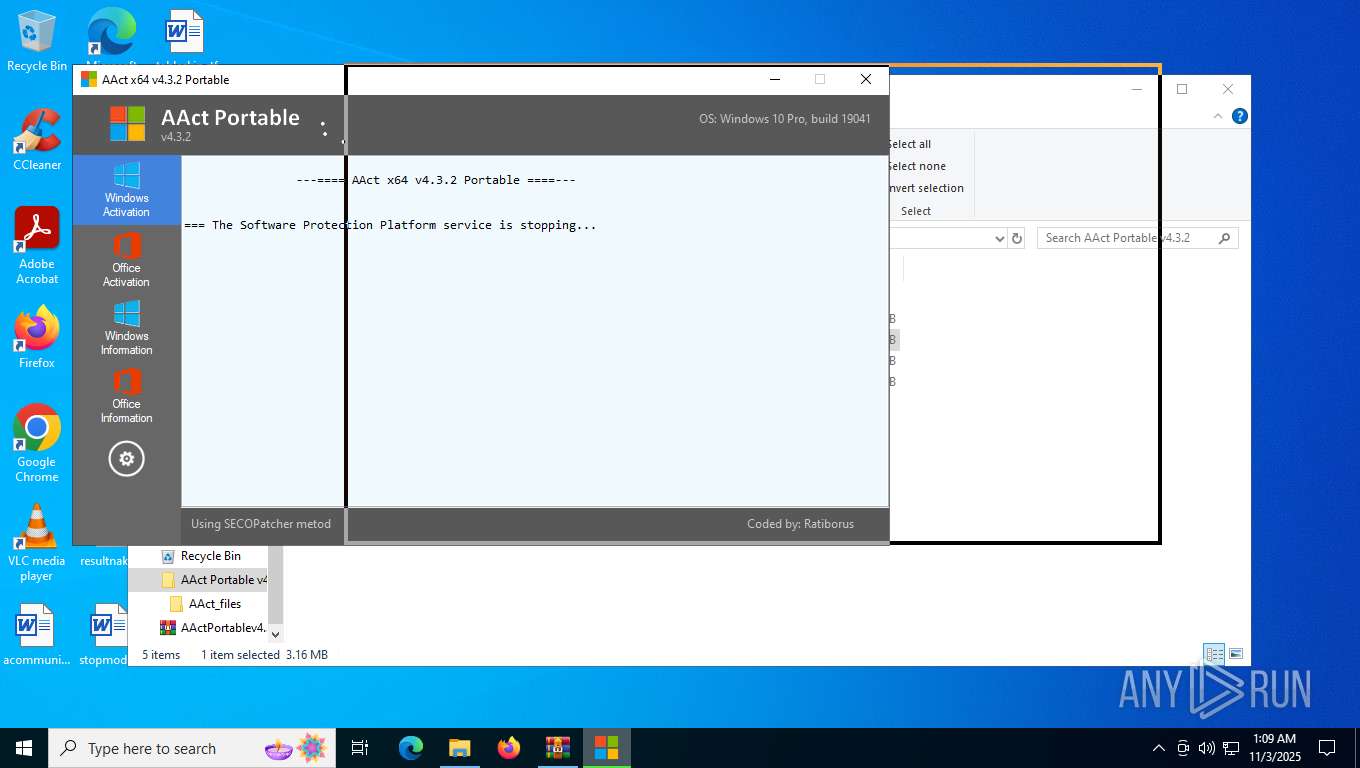
| Verdict: | Malicious activity |
| Analysis date: | November 03, 2025, 01:09:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 6F5AB24305D78AF3CEEA8223CB4BEE20 |
| SHA1: | AF49DF78D059D06FC09B4FD602999D39E930F725 |
| SHA256: | 81EFD13110DB1E422C23550C8994E8EE06FD3AF1ACA7357282BE8E75AA7E05A0 |
| SSDEEP: | 98304:TguOS/nw0oS6ymc7js2ZMFOT0/5wxvWEkzyQ5XVWRDUeu/lEGbGoqgd4o4a821N/:lfIeGlN |
MALICIOUS
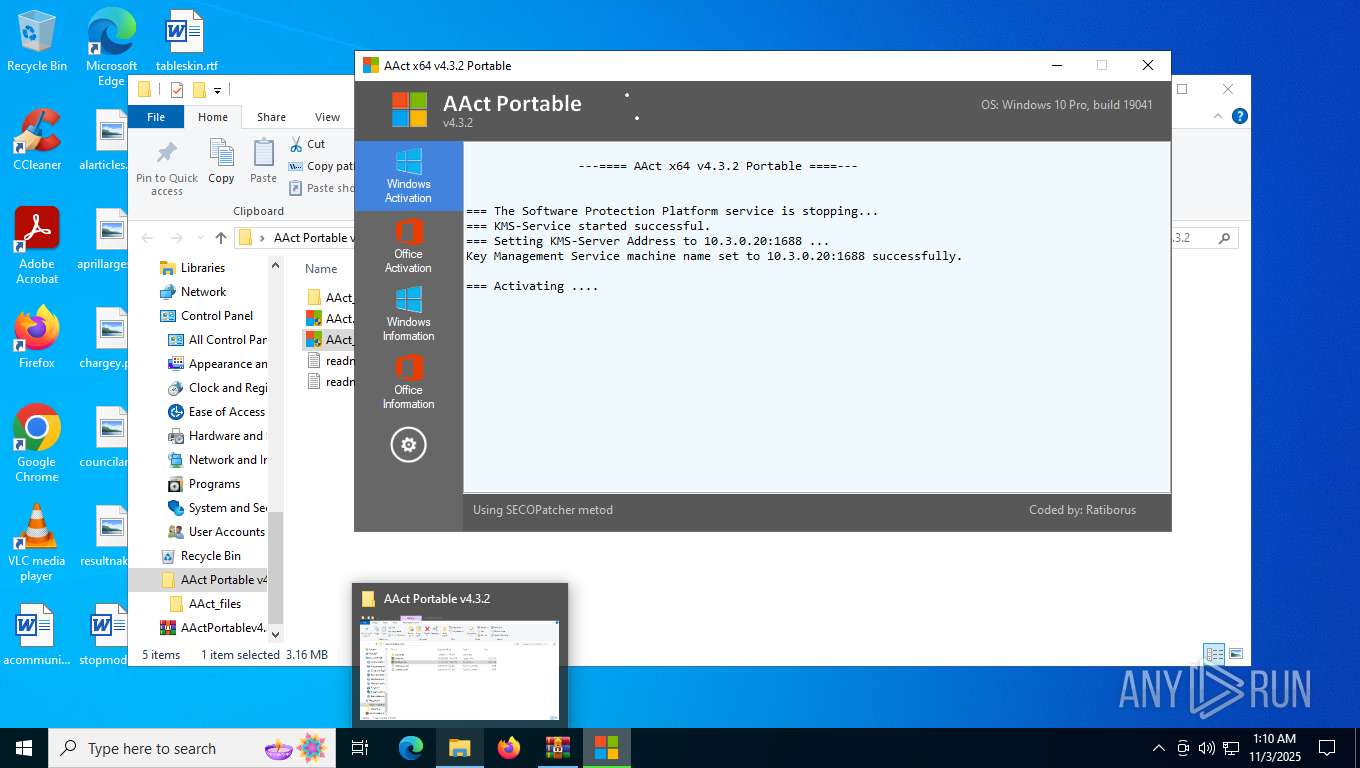
Uses WMIC.EXE to add exclusions to the Windows Defender
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 1936)
- cmd.exe (PID: 5692)
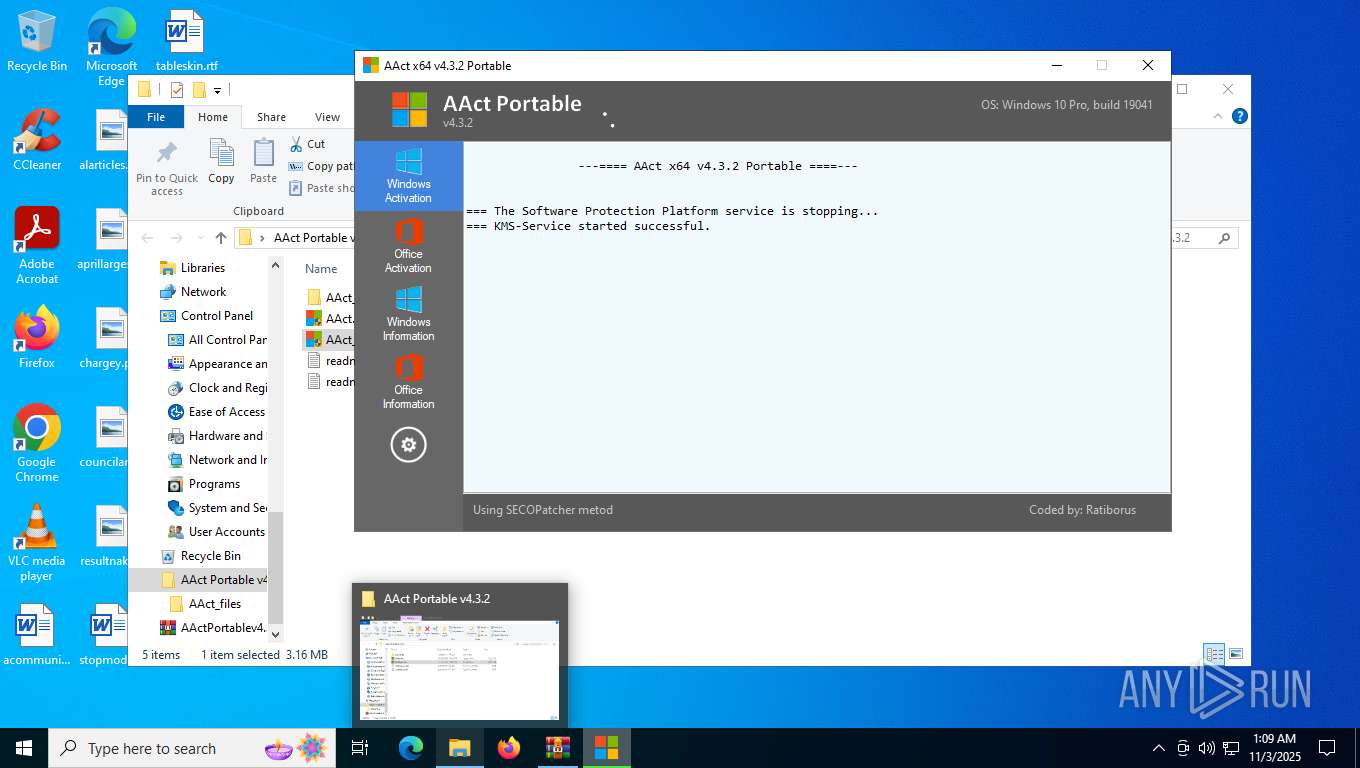
Starts NET.EXE for service management
- net.exe (PID: 7732)
- cmd.exe (PID: 7792)
- cmd.exe (PID: 6316)
- net.exe (PID: 828)
Changes image file execution options
- reg.exe (PID: 7308)
Opens a text file (SCRIPT)
- cscript.exe (PID: 7944)
- cscript.exe (PID: 6376)
- cscript.exe (PID: 5912)
- cscript.exe (PID: 3460)
- cscript.exe (PID: 6404)
- cscript.exe (PID: 6128)
Accesses name of the domain to which a computer belongs via WMI (SCRIPT)
- cscript.exe (PID: 5912)
- cscript.exe (PID: 6404)
- cscript.exe (PID: 3460)
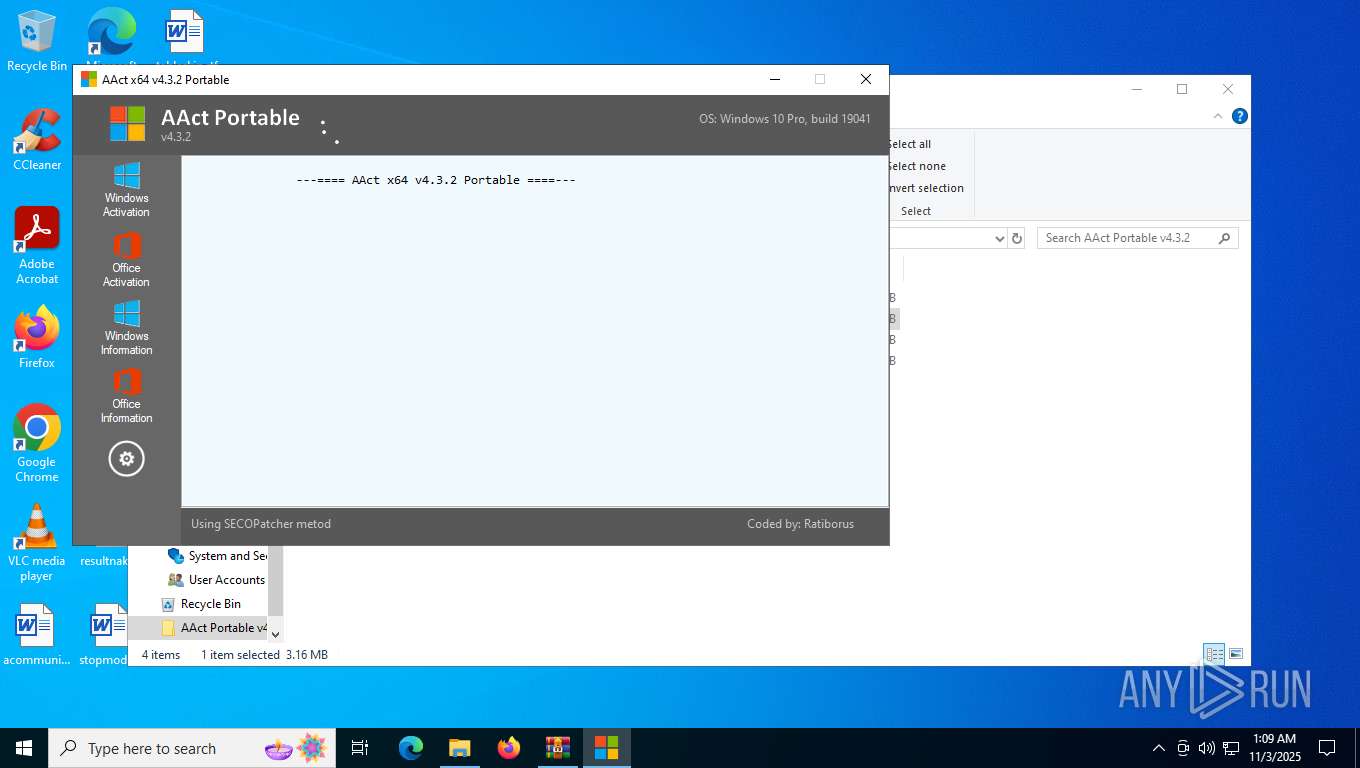
SUSPICIOUS
Found strings related to reading or modifying Windows Defender settings
- AAct_x64.exe (PID: 7952)
Starts CMD.EXE for commands execution
- AAct_x64.exe (PID: 7952)
Stops a currently running service
- sc.exe (PID: 6972)
- sc.exe (PID: 7628)
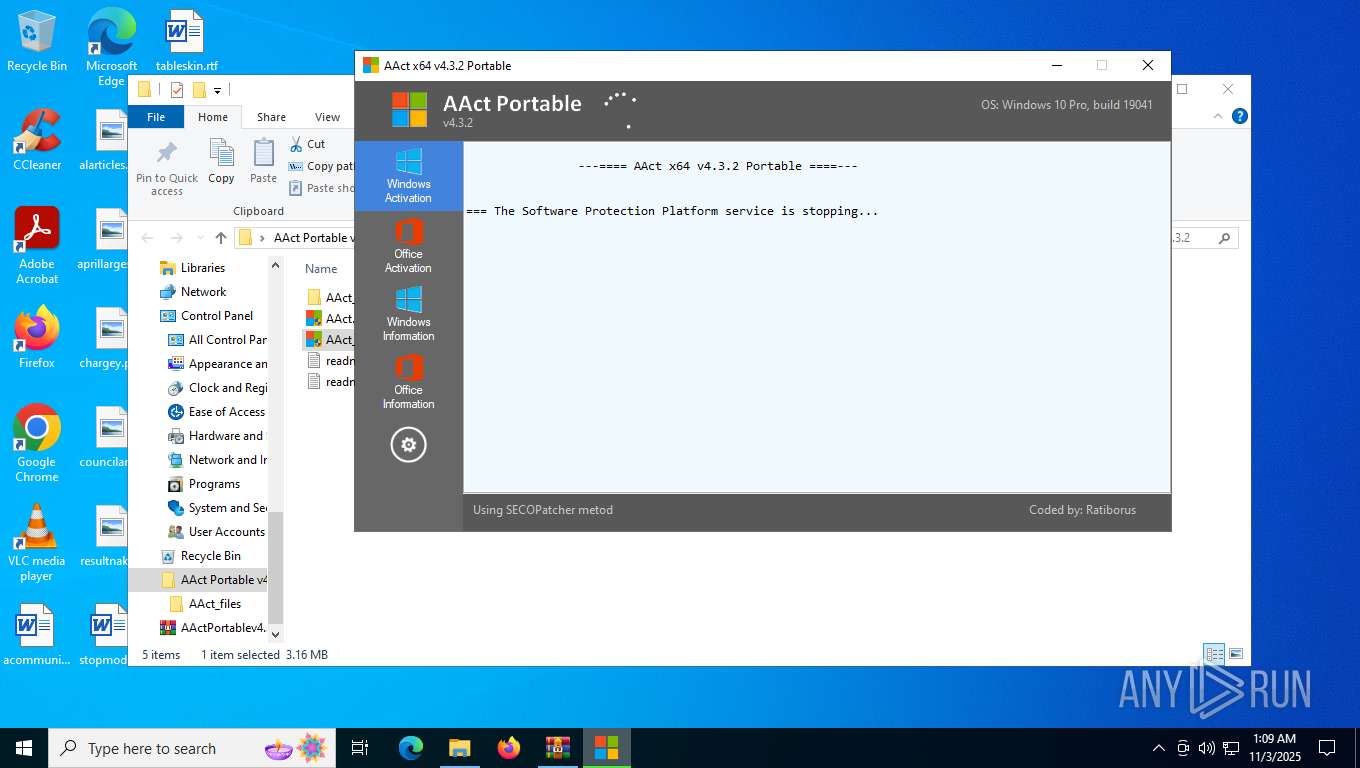
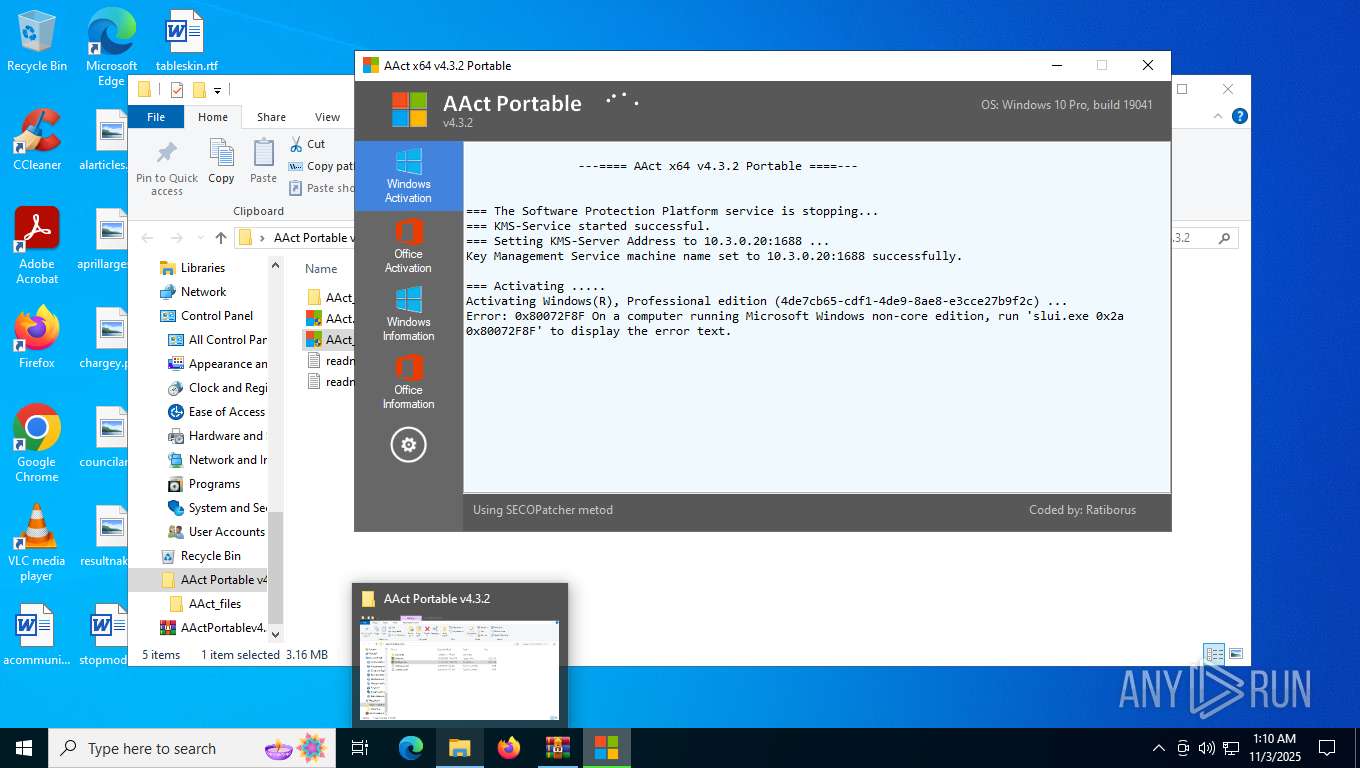
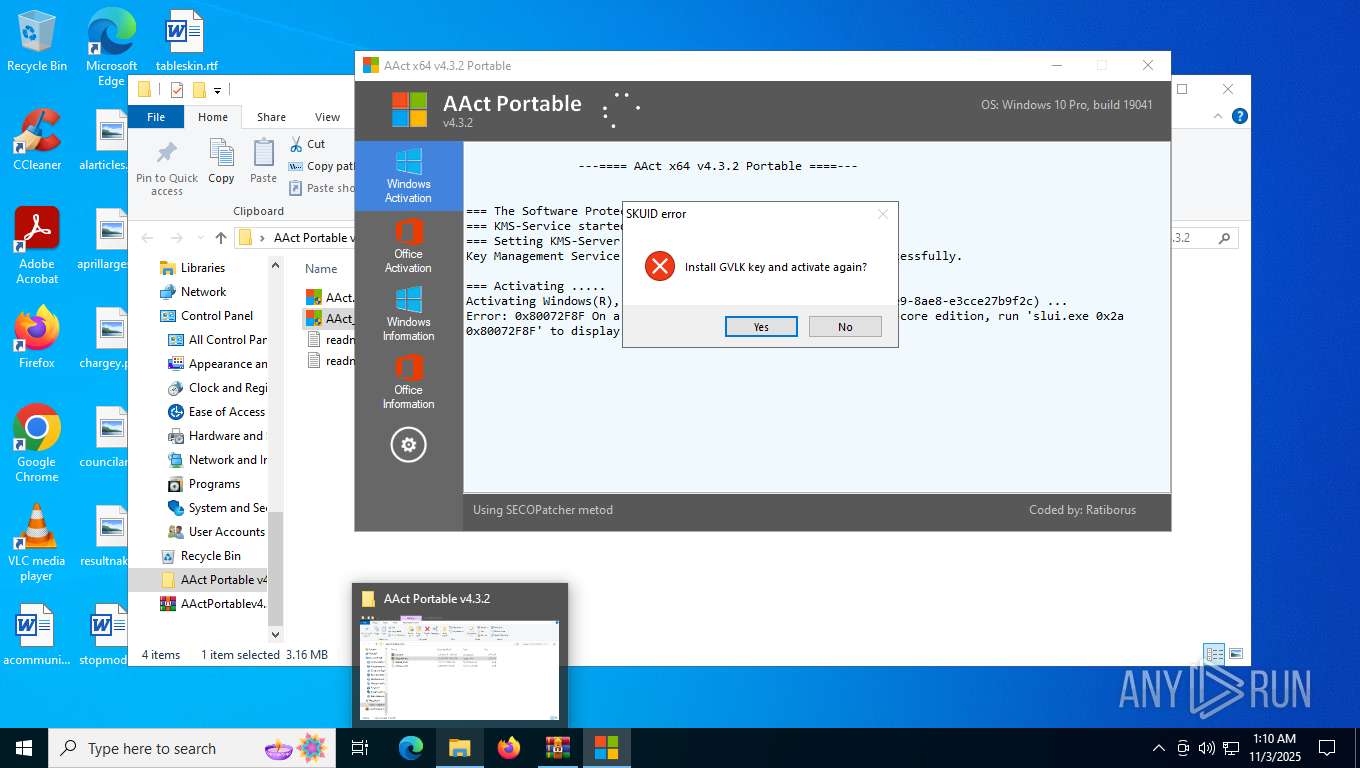
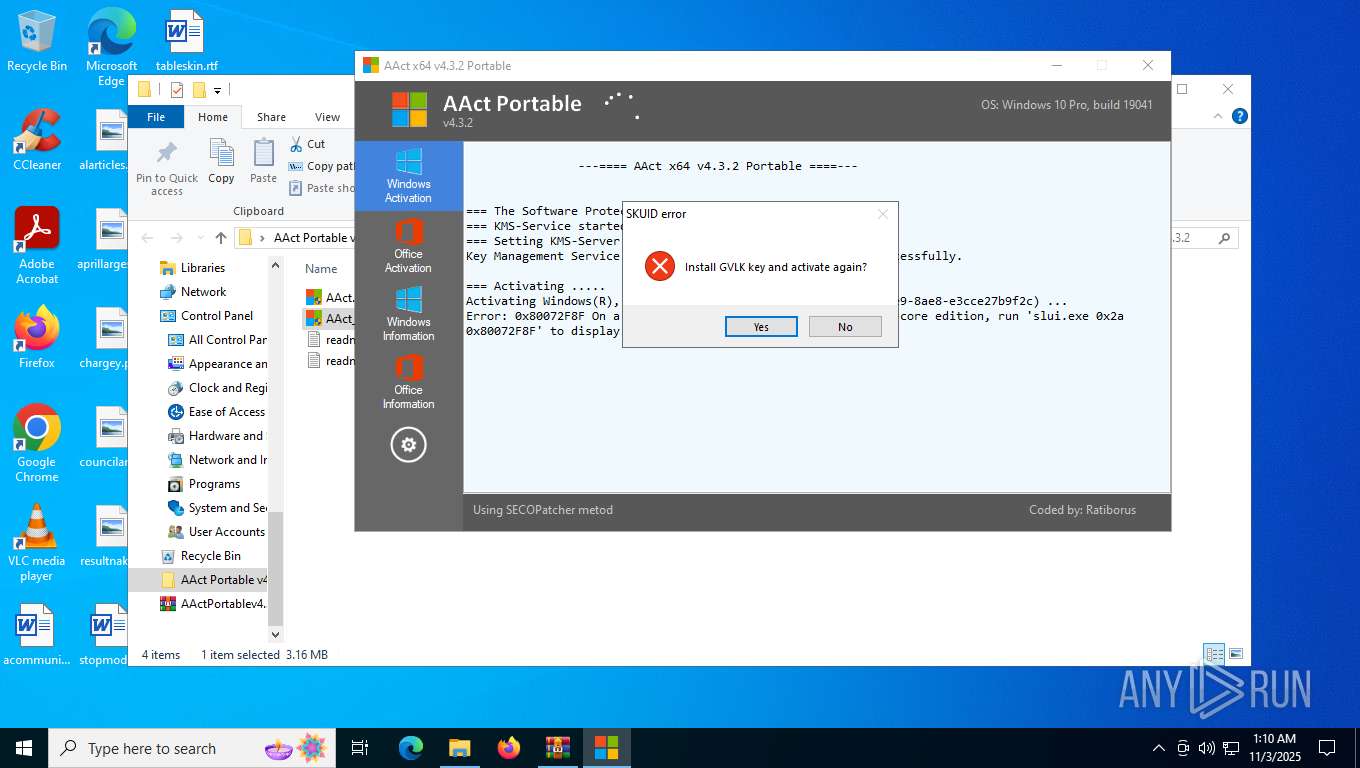
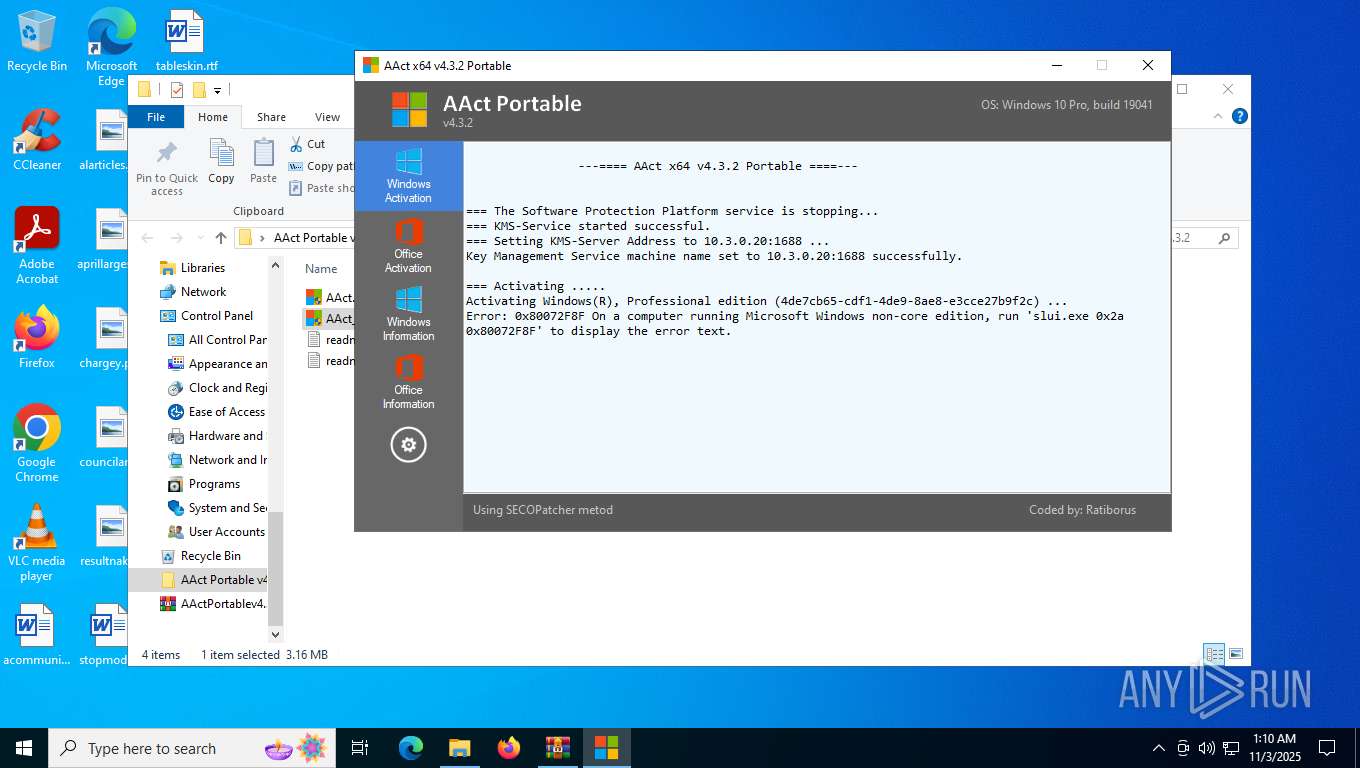
KMS tool has been detected
- cmd.exe (PID: 2580)
- AAct_x64.exe (PID: 7952)
- cmd.exe (PID: 4668)
- cmd.exe (PID: 6792)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6780)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 2588)
- cmd.exe (PID: 7296)
- AAct_x64.exe (PID: 7952)
- cmd.exe (PID: 5276)
- cmd.exe (PID: 8004)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 5420)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 4764)
- cmd.exe (PID: 8112)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 2580)
- cmd.exe (PID: 6792)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 5460)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 5692)
Hides command output
- cmd.exe (PID: 5972)
- cmd.exe (PID: 6364)
Starts SC.EXE for service management
- cmd.exe (PID: 5972)
- cmd.exe (PID: 6364)
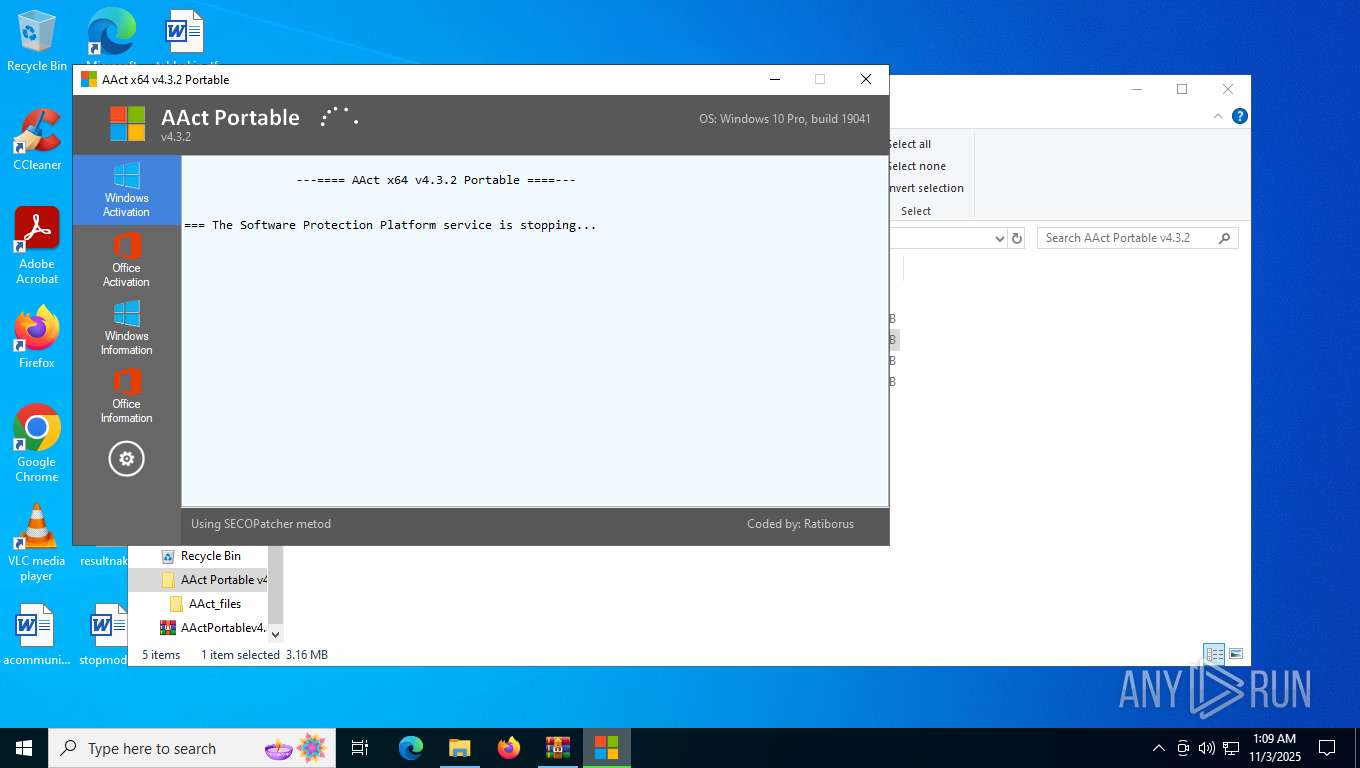
Executable content was dropped or overwritten
- AAct_x64.exe (PID: 7952)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 4668)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 7944)
- cscript.exe (PID: 5912)
- cscript.exe (PID: 6376)
- cscript.exe (PID: 3460)
- cscript.exe (PID: 6404)
- cscript.exe (PID: 6128)
The process executes VB scripts
- cmd.exe (PID: 3332)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 2716)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 1664)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 7944)
- cscript.exe (PID: 5912)
- cscript.exe (PID: 6376)
- cscript.exe (PID: 3460)
- cscript.exe (PID: 6404)
- cscript.exe (PID: 6128)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 7944)
- cscript.exe (PID: 6376)
- cscript.exe (PID: 5912)
- cscript.exe (PID: 3460)
- cscript.exe (PID: 6404)
- cscript.exe (PID: 6128)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 7944)
- cscript.exe (PID: 6376)
- cscript.exe (PID: 5912)
- cscript.exe (PID: 6404)
- cscript.exe (PID: 3460)
- cscript.exe (PID: 6128)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 7944)
- cscript.exe (PID: 5912)
- cscript.exe (PID: 6376)
- cscript.exe (PID: 6404)
- cscript.exe (PID: 3460)
- cscript.exe (PID: 6128)
The process downloads a VBScript from the remote host
- cmd.exe (PID: 5892)
INFO
Checks supported languages
- AAct_x64.exe (PID: 7952)
- KMSSS.exe (PID: 6260)
Manual execution by a user
- AAct_x64.exe (PID: 7952)
- AAct_x64.exe (PID: 7904)
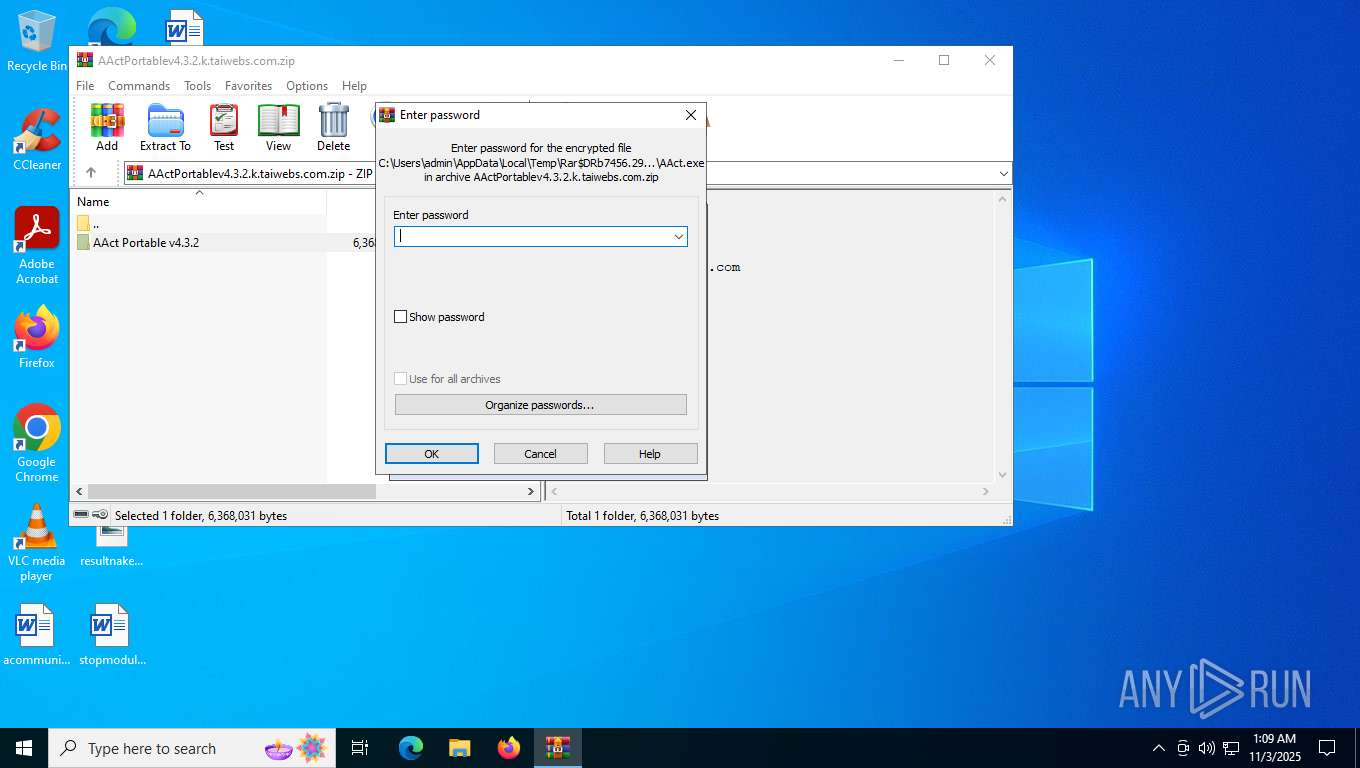
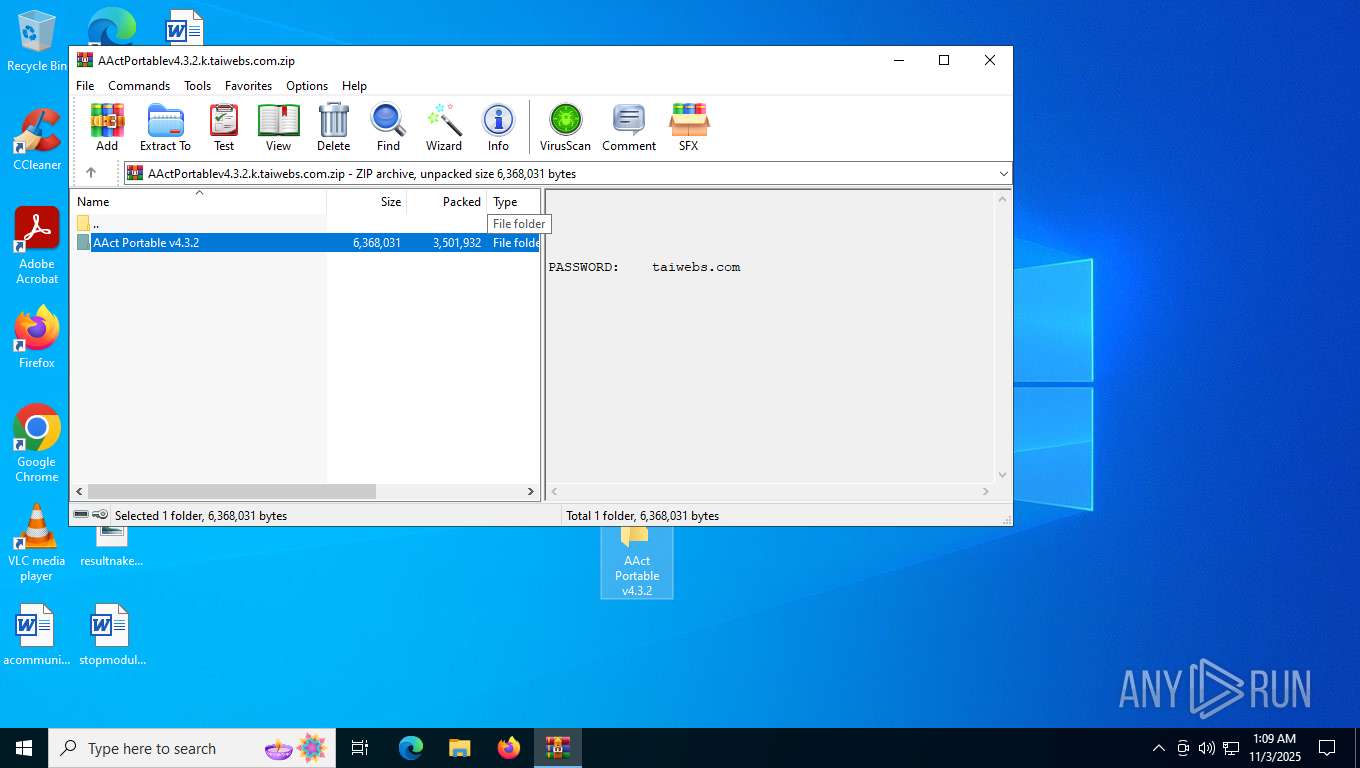
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7456)
Reads product name
- AAct_x64.exe (PID: 7952)
Reads Environment values
- AAct_x64.exe (PID: 7952)
Checks operating system version
- AAct_x64.exe (PID: 7952)
Checks Windows version
- cmd.exe (PID: 8044)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8036)
- WMIC.exe (PID: 6548)
- WMIC.exe (PID: 2928)
- WMIC.exe (PID: 2056)
- WMIC.exe (PID: 7232)
- cscript.exe (PID: 7944)
- cscript.exe (PID: 6376)
- cscript.exe (PID: 5912)
- cscript.exe (PID: 3460)
- cscript.exe (PID: 6404)
- cscript.exe (PID: 6128)
Reads the computer name
- AAct_x64.exe (PID: 7952)
- KMSSS.exe (PID: 6260)
UPX packer has been detected
- AAct_x64.exe (PID: 7952)
Reads the machine GUID from the registry
- KMSSS.exe (PID: 6260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:06:26 10:09:22 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
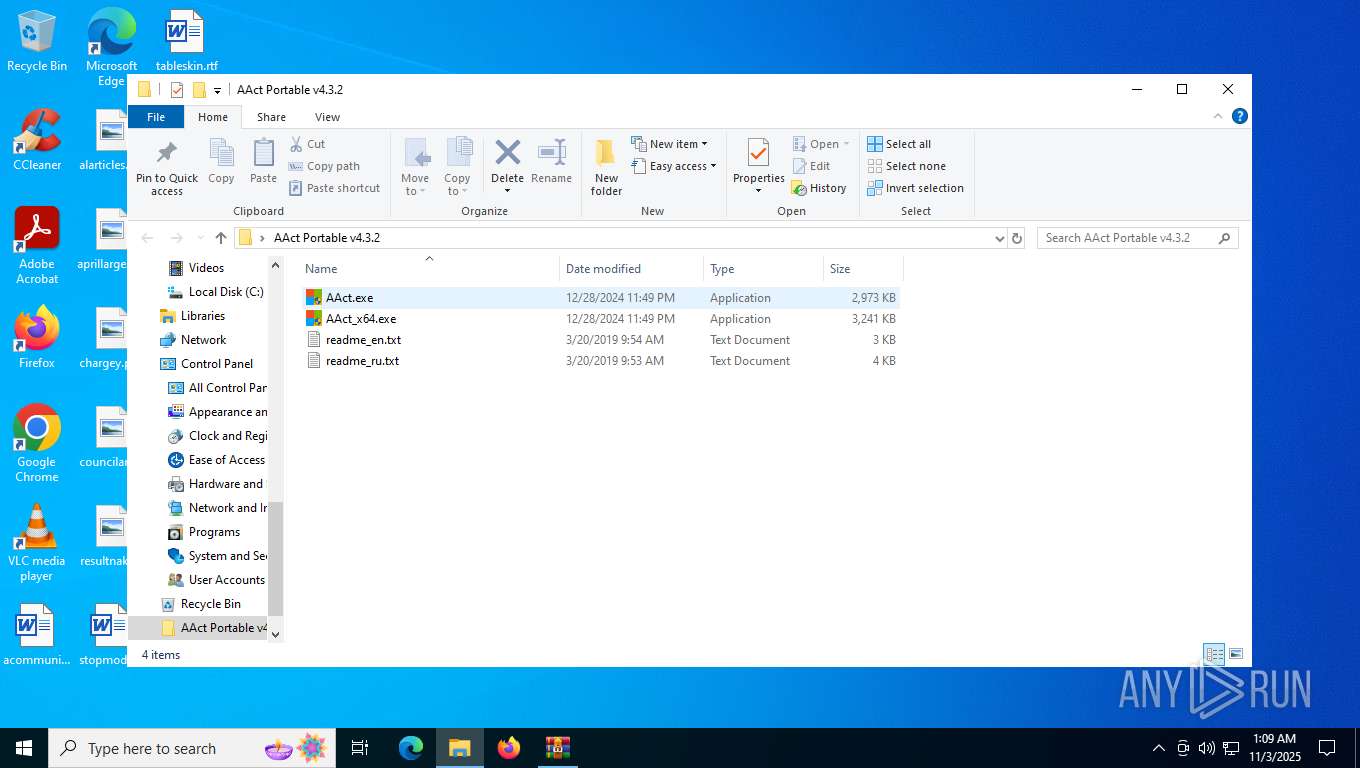
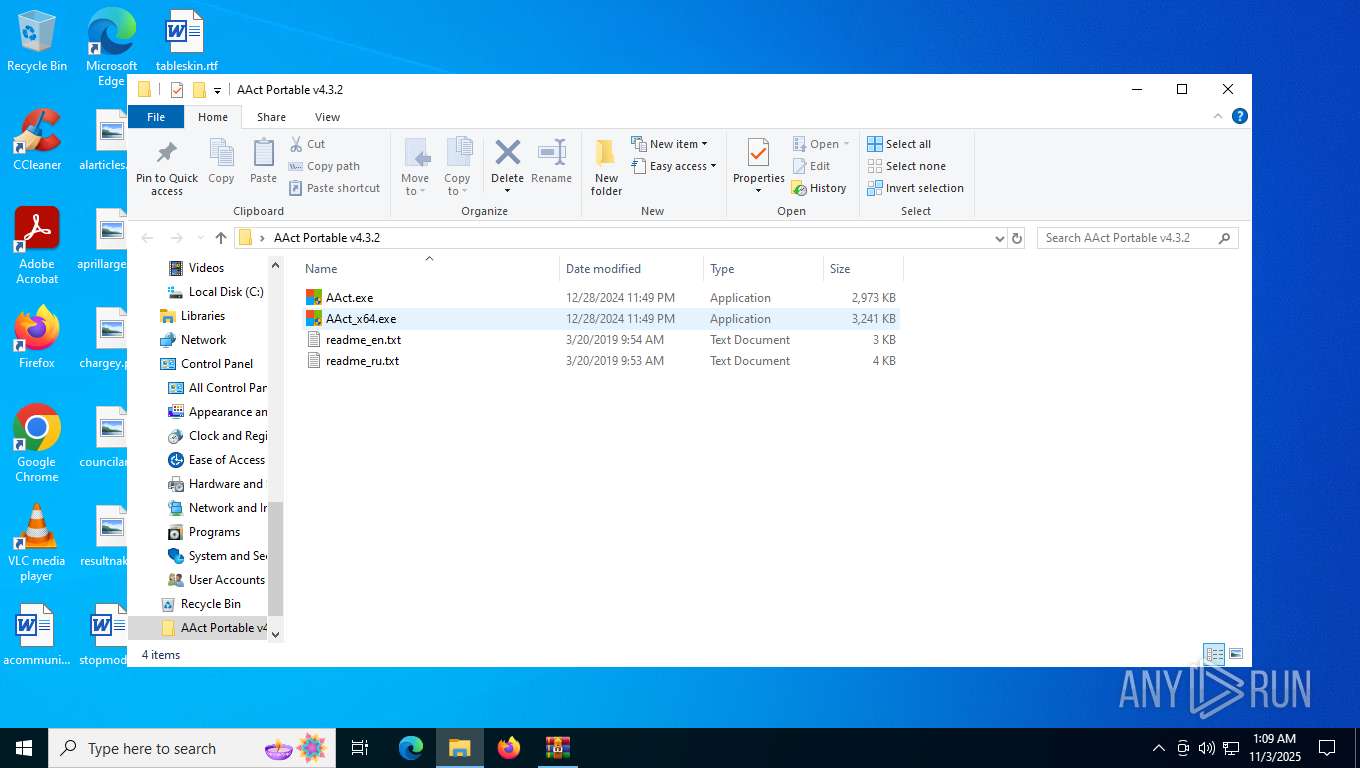
| ZipFileName: | AAct Portable v4.3.2/ |
Total processes
267
Monitored processes
114
Malicious processes
13
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 828 | net.exe stop sppsvc /y | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1664 | "C:\WINDOWS\System32\cmd.exe" /c cscript.exe C:\WINDOWS\System32\slmgr.vbs //NoLogo /ato | C:\Windows\System32\cmd.exe | — | AAct_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147954575 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1936 | "C:\WINDOWS\System32\cmd.exe" /c WMIC /NAMESPACE:\\root\Microsoft\Windows\Defender PATH MSFT_MpPreference call Add ExclusionPath="C:\WINDOWS\System32\SppExtComObjHook.dll" | C:\Windows\System32\cmd.exe | — | AAct_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147749889 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | taskkill.exe /t /f /IM KMSSS.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2056 | WMIC /NAMESPACE:\\root\Microsoft\Windows\Defender PATH MSFT_MpPreference call Add ExclusionPath="C:\WINDOWS\System32\SppExtComObjHook.dll" | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 2147749889 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2160 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | taskkill.exe /t /f /IM SppExtComObj.Exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 317
Read events
8 300
Write events
15
Delete events
2
Modification events
| (PID) Process: | (7456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\AActPortablev4.3.2.k.taiwebs.com.zip | |||
| (PID) Process: | (7456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7456.29663\AAct Portable v4.3.2\AAct_x64.exe | executable | |
MD5:B0EA09E68C6064053157A044C302A6B7 | SHA256:40484D7E7BB238273F58F8BBE6B679DB8691B39A9DCA46DB1D5D425A3F67E49B | |||
| 7456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7456.29663\AAct Portable v4.3.2\readme_en.txt | text | |
MD5:E8A1118CDDD4C40B687D3440B7C36F90 | SHA256:D404B95D28EA2D6011A472F769C34ADCB9249C3771D4C549A73C06470C1D9548 | |||
| 7456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7456.29663\AAct Portable v4.3.2\readme_ru.txt | text | |
MD5:45D8BE91E4849301C7C33C505C79E07F | SHA256:9A2940501689EF5E7D2008DAA4A27A2B2EAC3ED520E69626BF8704CD1EC15DDD | |||
| 7456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7456.29663\AAct Portable v4.3.2\AAct.exe | executable | |
MD5:8A8C4ED6BBBA7CF30A076C95E6A06708 | SHA256:CF06BD0760DC3DA05D595E9D4BB04758B7AC289F12B7B81A438E728B67C82D62 | |||
| 7952 | AAct_x64.exe | C:\Users\admin\Desktop\AAct Portable v4.3.2\AAct_files\KMSSS.exe | executable | |
MD5:01A80AAD5DABED1C1580F7E00213CF9D | SHA256:FD7499214ABAA13BF56D006AB7DE78EB8D6ADF17926C24ACE024D067049BC81D | |||
| 7952 | AAct_x64.exe | C:\Users\admin\Desktop\AAct Portable v4.3.2\AAct_files\SECOPatcher.dll | executable | |
MD5:8998BE879286D69A2522109650FEC7B8 | SHA256:03B9136FB9414EBA54D0890D9EFAD1CC0E40ABD55EBE2A5BD5554EA7BCC6D2BE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
32
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1584 | svchost.exe | GET | 200 | 95.101.35.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7640 | SIHClient.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
6232 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7640 | SIHClient.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
7640 | SIHClient.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1584 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5196 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1584 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1584 | svchost.exe | 95.101.35.35:80 | crl.microsoft.com | Orange | NL | whitelisted |
1584 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6232 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6232 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |