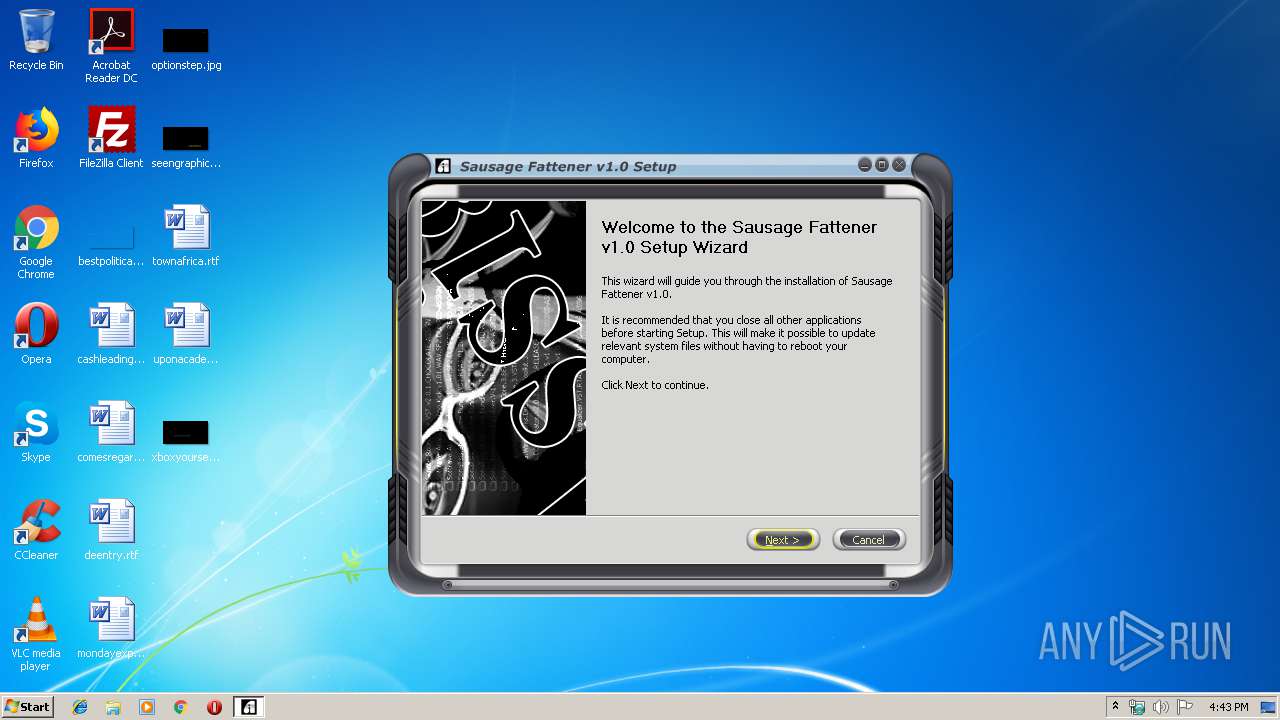
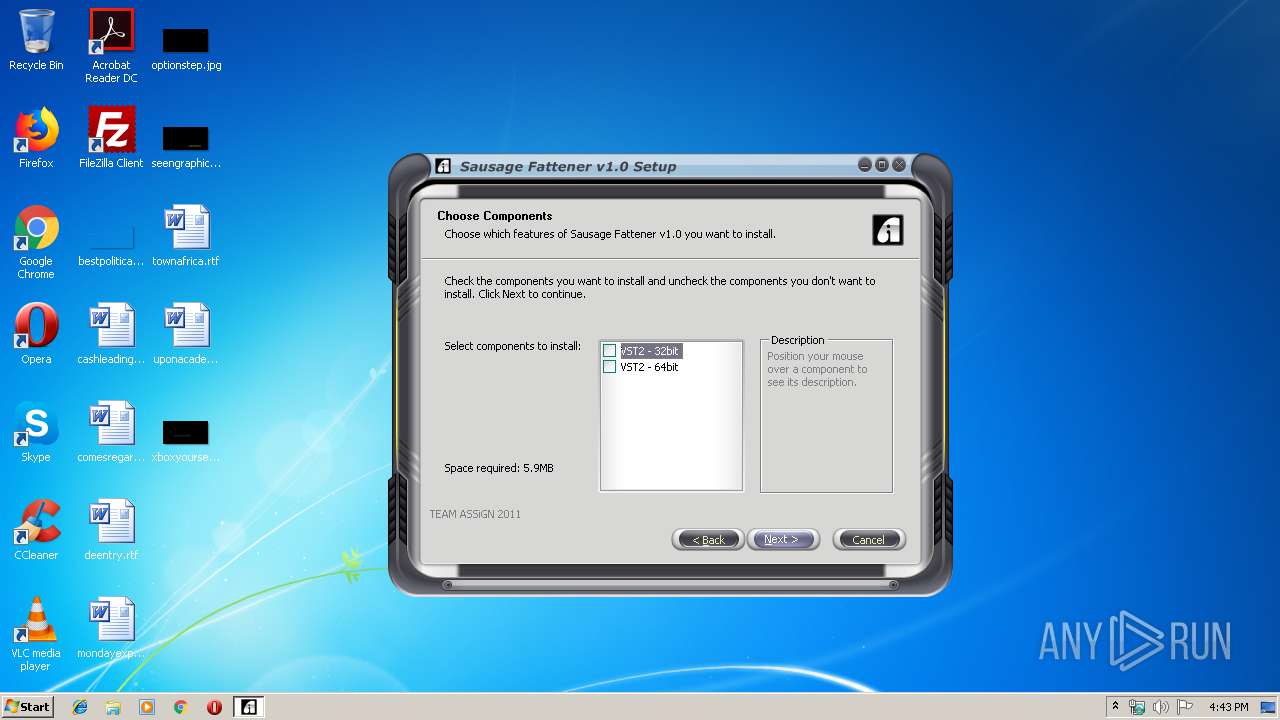
| File name: | sausage fattener windows.exe |
| Full analysis: | https://app.any.run/tasks/5d94d9a0-bc91-49a5-95b5-0bc8b5cb82a4 |
| Verdict: | Malicious activity |
| Analysis date: | September 13, 2019, 15:43:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 81E69B29C4C09391A12B665E7661F48E |
| SHA1: | B103B694D12544C9DB444BADD9E2263D219698B1 |
| SHA256: | 81E45C1E6D6A718624159E116E6DAA8C1547F39BEF7F56163303E7ECA8ABFAE1 |
| SSDEEP: | 98304:QhVVJqioKMFh1qKsbZcMgsGwNmlCNE4CJgcMyfQP/4:QhV1pMzHQCMFGImHgcM54 |
MALICIOUS
Loads dropped or rewritten executable
- sausage fattener windows.exe (PID: 2308)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2172)
Creates files in the user directory
- sausage fattener windows.exe (PID: 2308)
Creates files in the Windows directory
- sausage fattener windows.exe (PID: 2308)
Executable content was dropped or overwritten
- sausage fattener windows.exe (PID: 2308)
Creates files in the program directory
- sausage fattener windows.exe (PID: 2308)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23040 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30cb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:41 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000058D2 | 0x00005A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4331 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17976 |
.data | 0x00009000 | 0x0001AF78 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.6178 |
.ndata | 0x00024000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x00001C58 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.85776 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21482 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.81924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70992 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
110 | 2.82633 | 1638 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2172 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2308 | "C:\Users\admin\AppData\Local\Temp\sausage fattener windows.exe" | C:\Users\admin\AppData\Local\Temp\sausage fattener windows.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3788 | "C:\Users\admin\AppData\Local\Temp\sausage fattener windows.exe" | C:\Users\admin\AppData\Local\Temp\sausage fattener windows.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
402
Read events
398
Write events
4
Delete events
0
Modification events
| (PID) Process: | (2308) sausage fattener windows.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
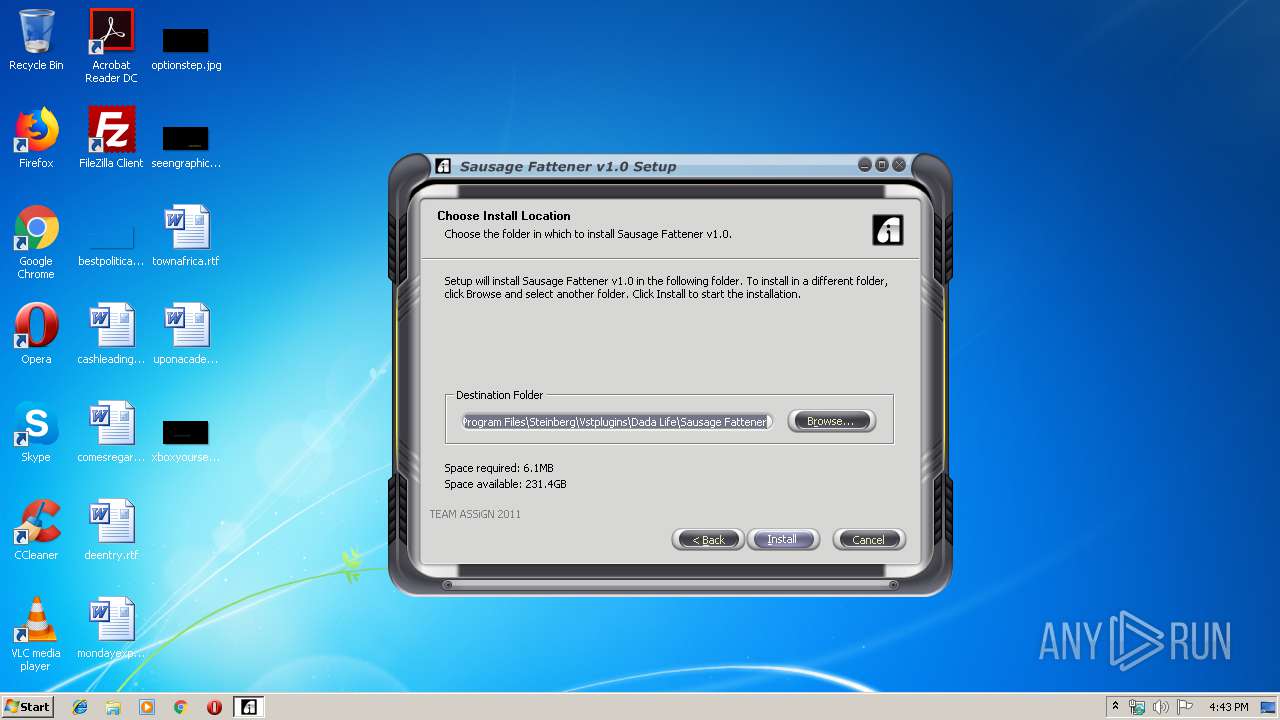
| (PID) Process: | (2308) sausage fattener windows.exe | Key: | HKEY_CURRENT_USER\Software\Tailored Noise\Sausage Fattener |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Steinberg\Vstplugins\Dada Life\Sausage Fattener | |||
| (PID) Process: | (2172) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
Executable files
16
Suspicious files
2
Text files
41
Unknown types
3
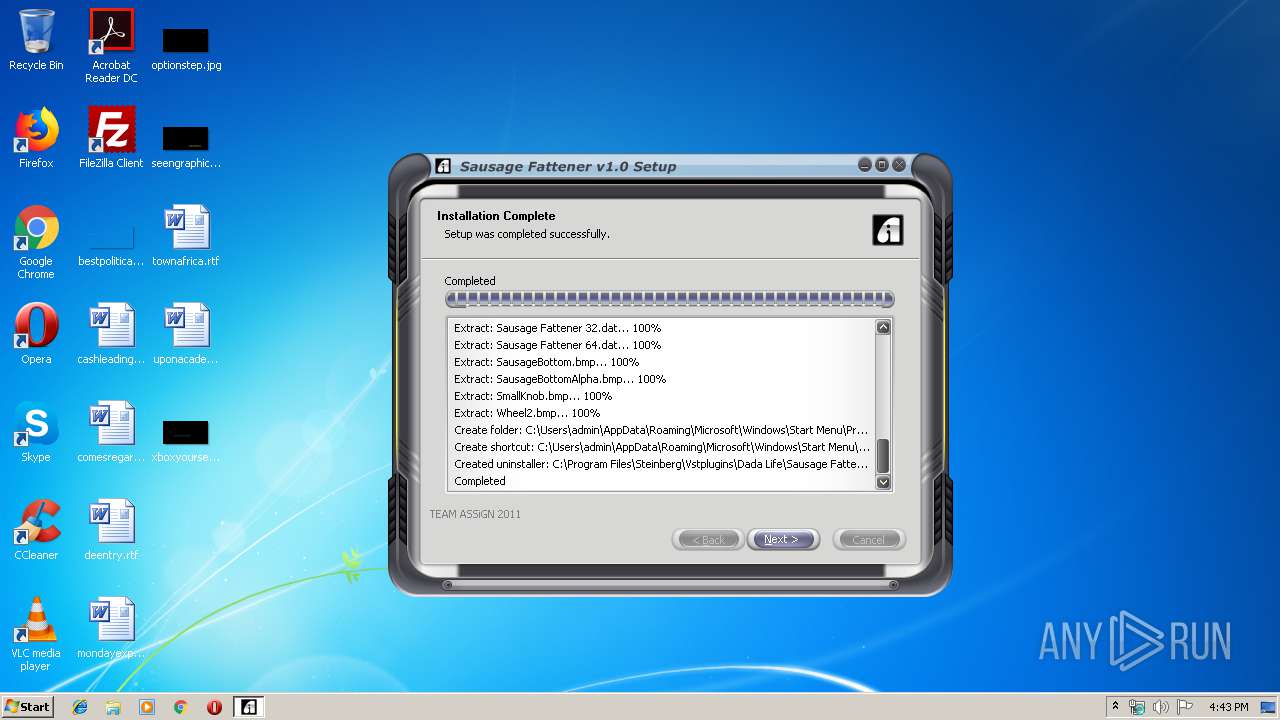
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2308 | sausage fattener windows.exe | C:\Users\admin\AppData\Local\Temp\nsdA500.tmp\bass.dll | executable | |
MD5:A8AF308FF01B4477657955FBF0CC8408 | SHA256:14A38F56BE50A3829EB1EDA2A908DA2DE5913F81D5CB01D8B668593D0FC36594 | |||
| 2308 | sausage fattener windows.exe | C:\Users\admin\AppData\Local\Temp\nsdA500.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 2308 | sausage fattener windows.exe | C:\Users\admin\AppData\Local\Temp\nsdA500.tmp\dat_skin.skf | skf | |
MD5:F172C4E44639C2C67C019E94172C780A | SHA256:2F2F3FF75F666826F4B40B8E277040D286E6D7AD883CABD5F4BF64670D4579AA | |||
| 2308 | sausage fattener windows.exe | C:\Users\admin\AppData\Local\Temp\nsdA500.tmp\NSIS_SkinCrafter_Plugin.dll | executable | |
MD5:028251654A4D65509AA8CCB5F2EE284A | SHA256:8B25CF3F7AA82FADCCB2CE615CE0E40C5A8A3EA7BC51180A92173EE113A0CCFE | |||
| 2308 | sausage fattener windows.exe | C:\Users\admin\AppData\Local\Temp\nsdA500.tmp\SkinNsis.skf | binary | |
MD5:CDAD8F63CC0C9DDEAD1A81F865C80A40 | SHA256:B28E3BE366FAEBAD8D27AEEDCFF7B0F04E5E6C4D52257C9C608E560E1533B75B | |||
| 2308 | sausage fattener windows.exe | C:\Users\admin\AppData\Local\Temp\nsdA500.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2308 | sausage fattener windows.exe | C:\Users\admin\AppData\Local\Temp\nsdA500.tmp\splash.bmp | image | |
MD5:94F52DC67C016167D6EAF6E0C3CF0942 | SHA256:D91B10D9516F3153CFAD2E00B9975A835B1538BE1DC0EC0E2821A7F3755322B0 | |||
| 2308 | sausage fattener windows.exe | C:\Users\admin\AppData\Local\Temp\nsdA500.tmp\Bass.dll | executable | |
MD5:A8AF308FF01B4477657955FBF0CC8408 | SHA256:14A38F56BE50A3829EB1EDA2A908DA2DE5913F81D5CB01D8B668593D0FC36594 | |||
| 2308 | sausage fattener windows.exe | C:\Users\admin\AppData\Local\Temp\nsdA500.tmp\AdvSplash.dll | executable | |
MD5:13CC92F90A299F5B2B2F795D0D2E47DC | SHA256:EB1CA2B3A6E564C32677D0CDC388E26B74EF686E071D7DBCA44D0BFA10488FEB | |||
| 2308 | sausage fattener windows.exe | C:\Windows\system32\gdiplus.dll | executable | |
MD5:D0AAAE16BA162DD89D646887F1539855 | SHA256:D84E7EB505ADEE8EA660F48C89705977F5EB33B7299D0BD981624E3ECE320223 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report