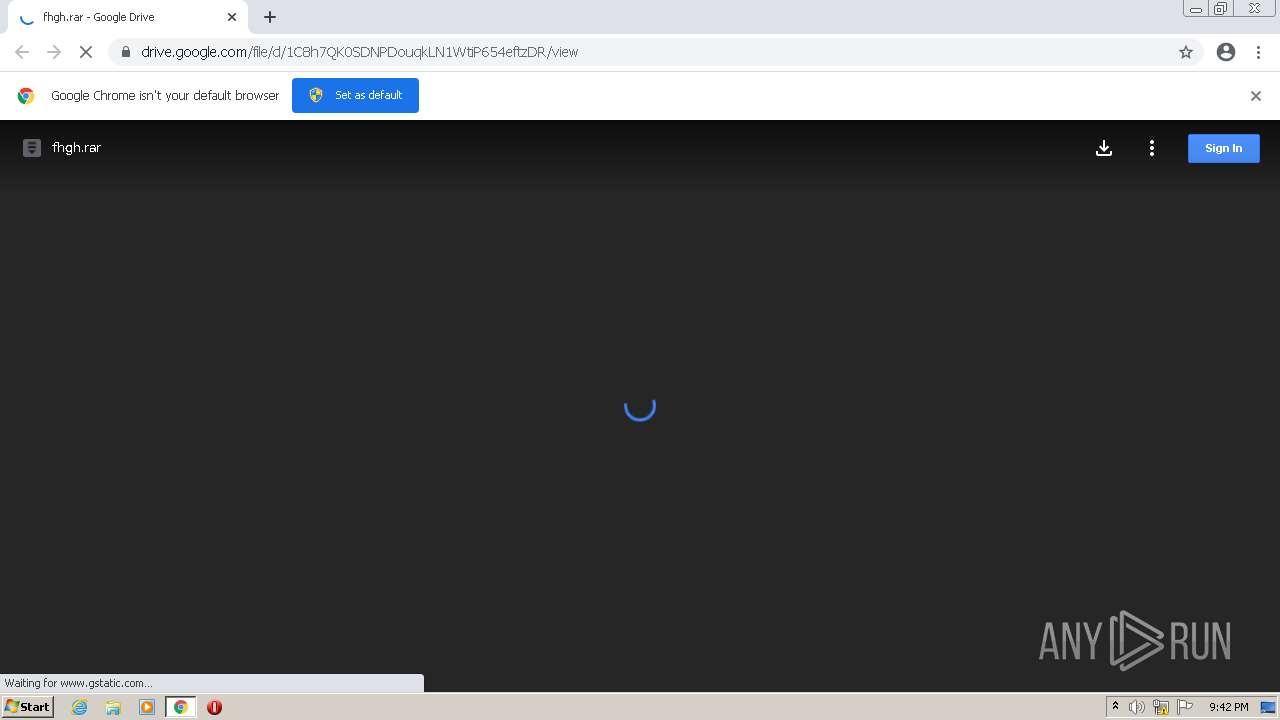
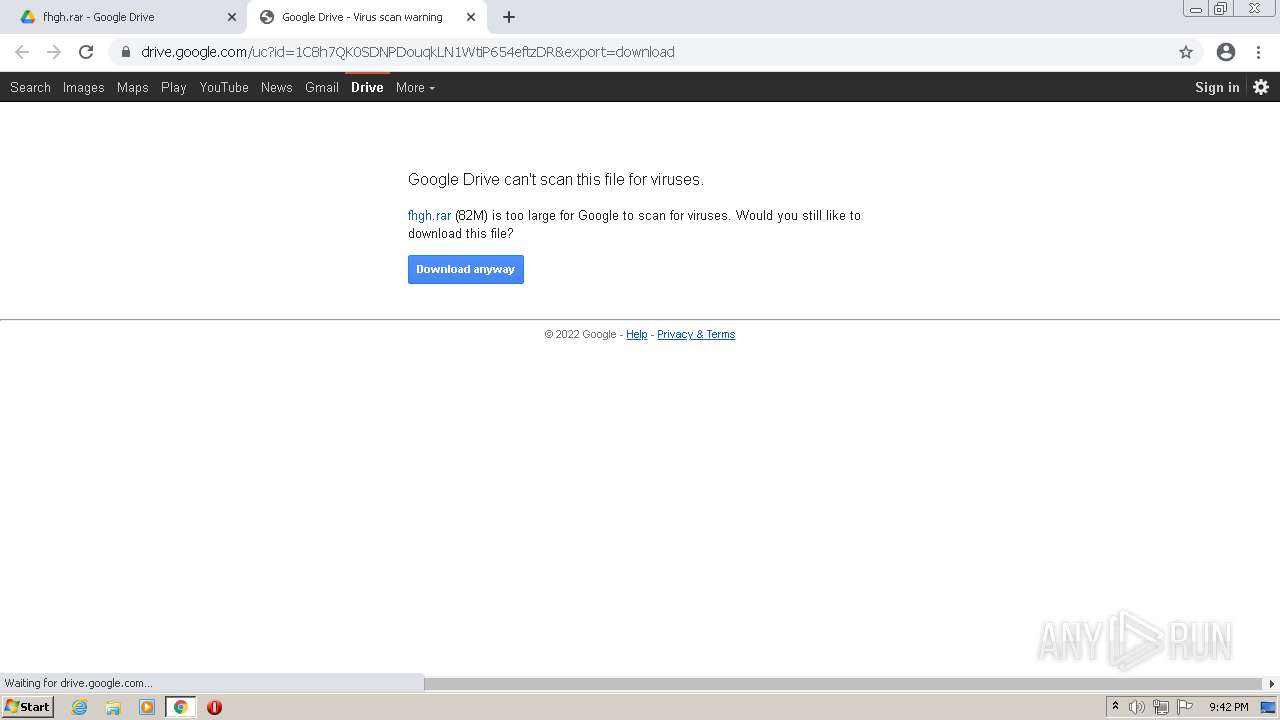
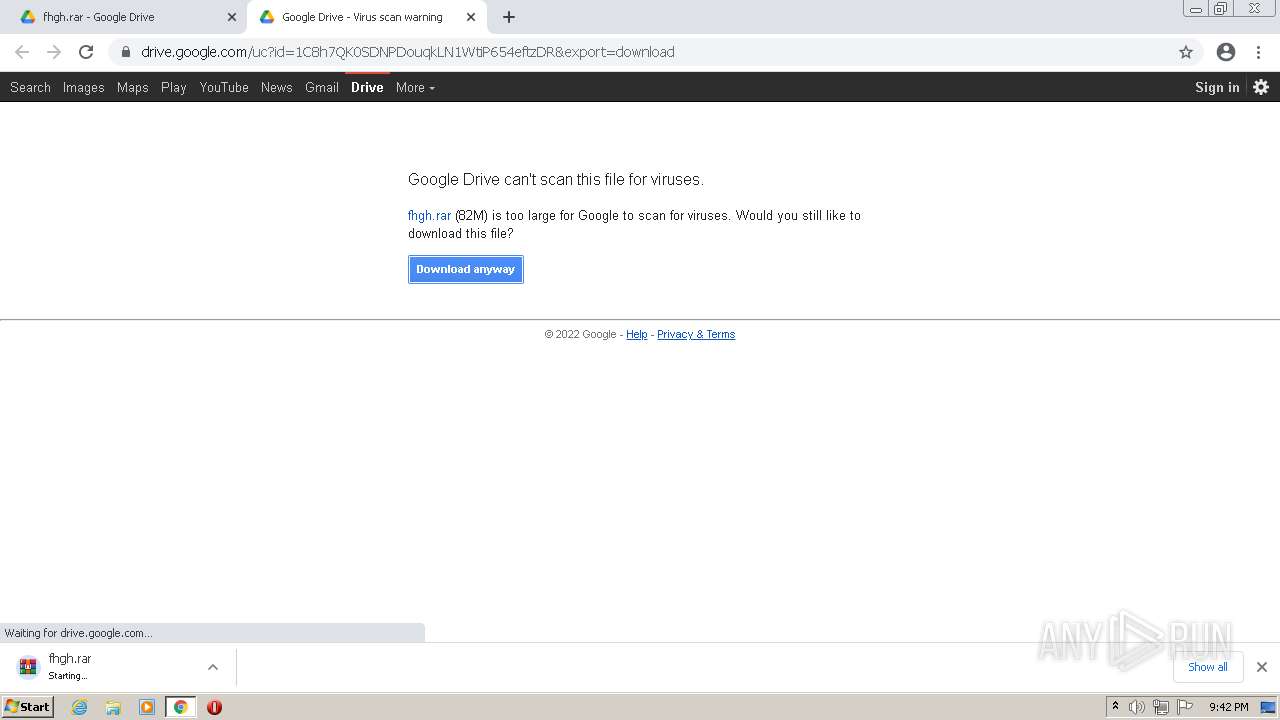
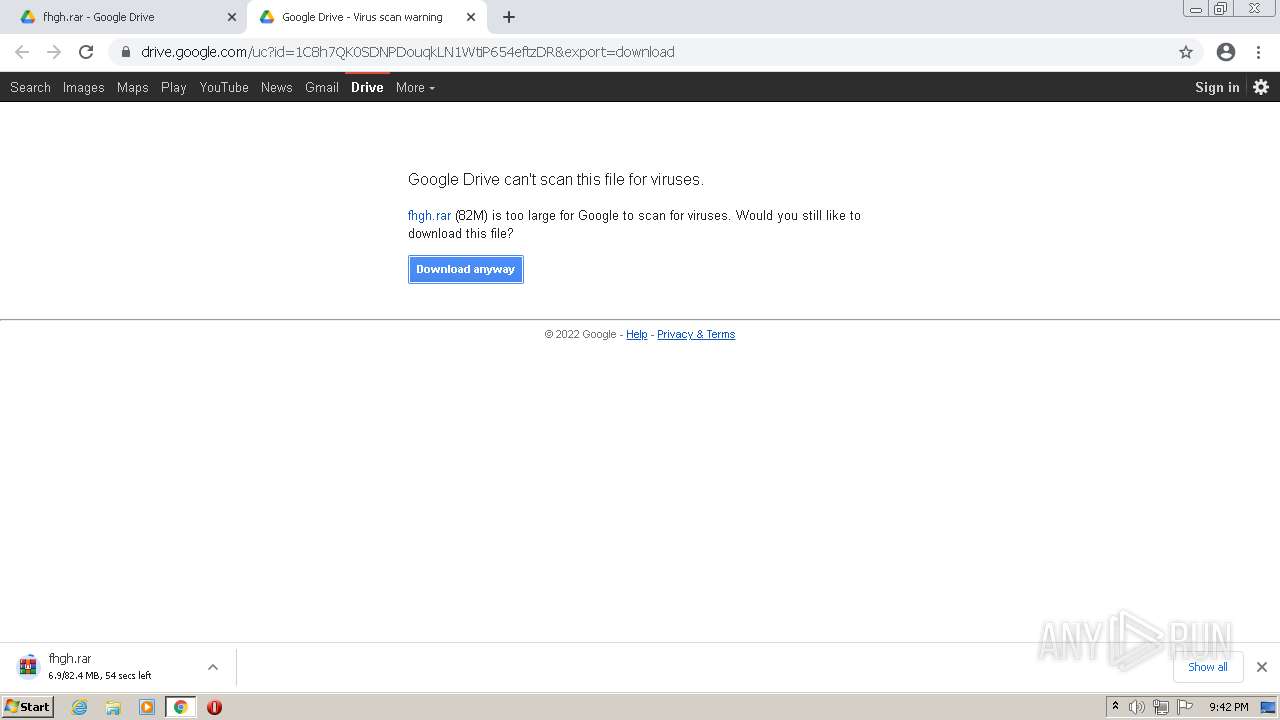
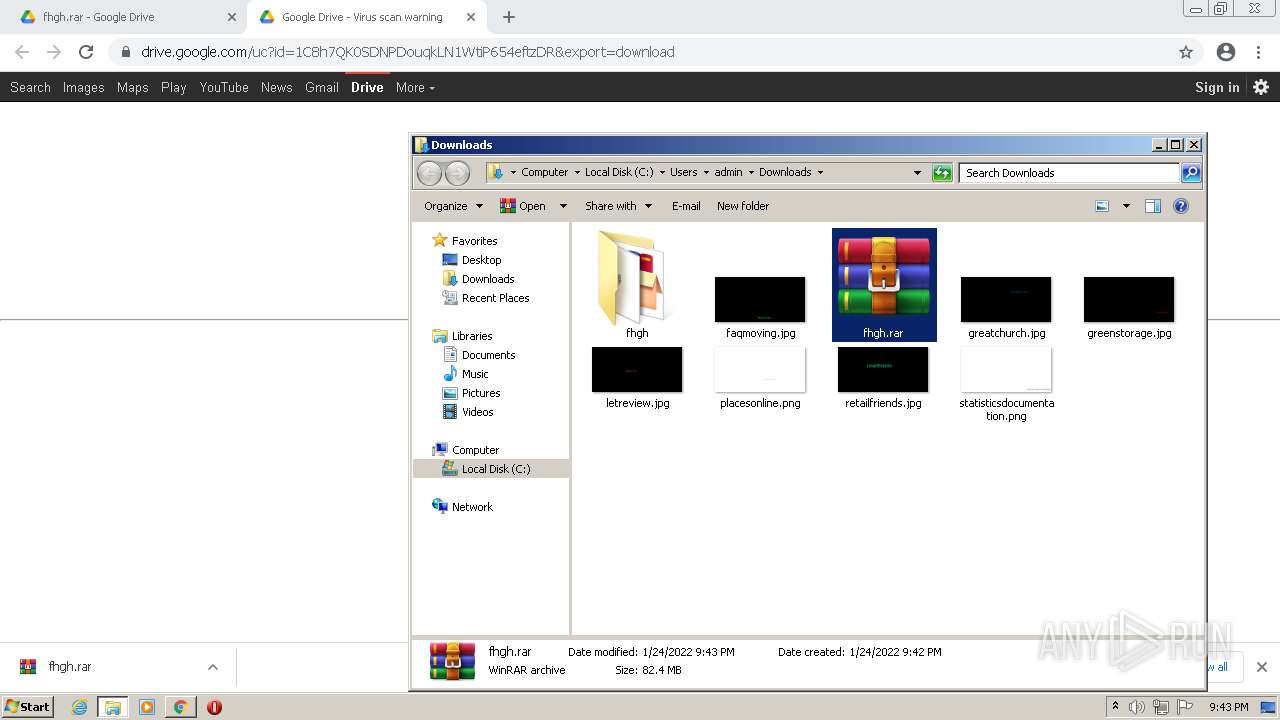
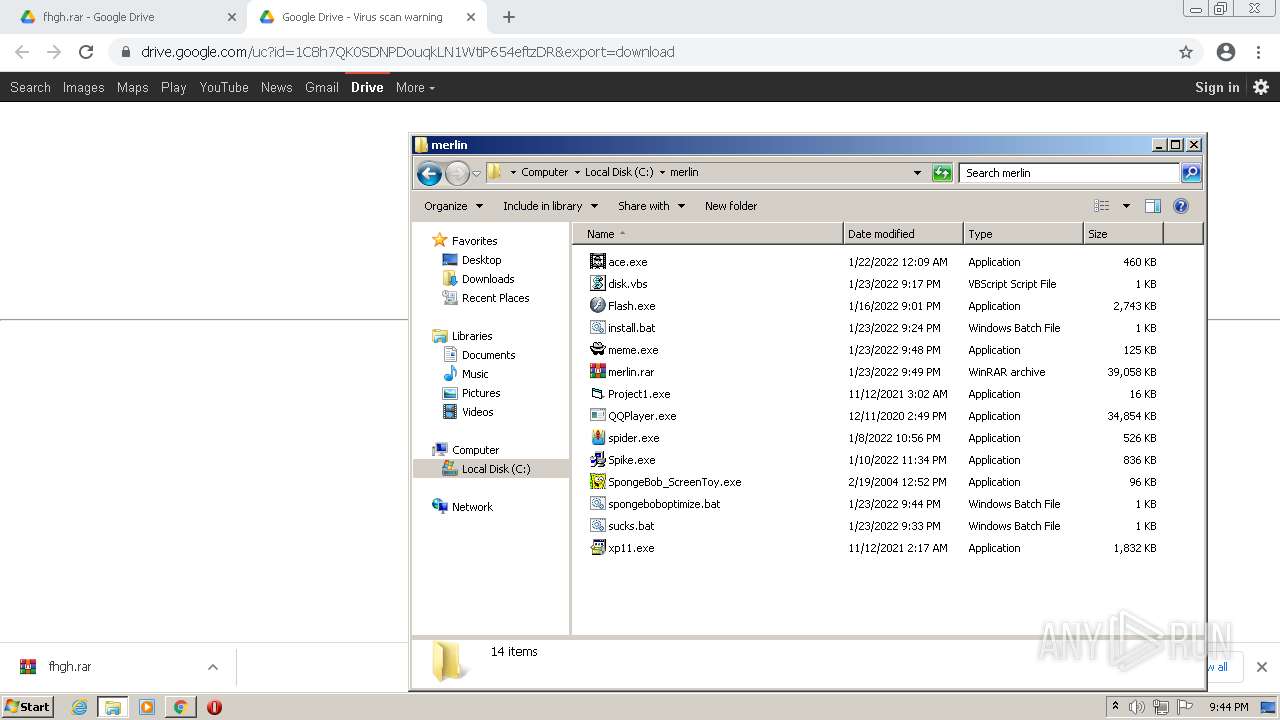
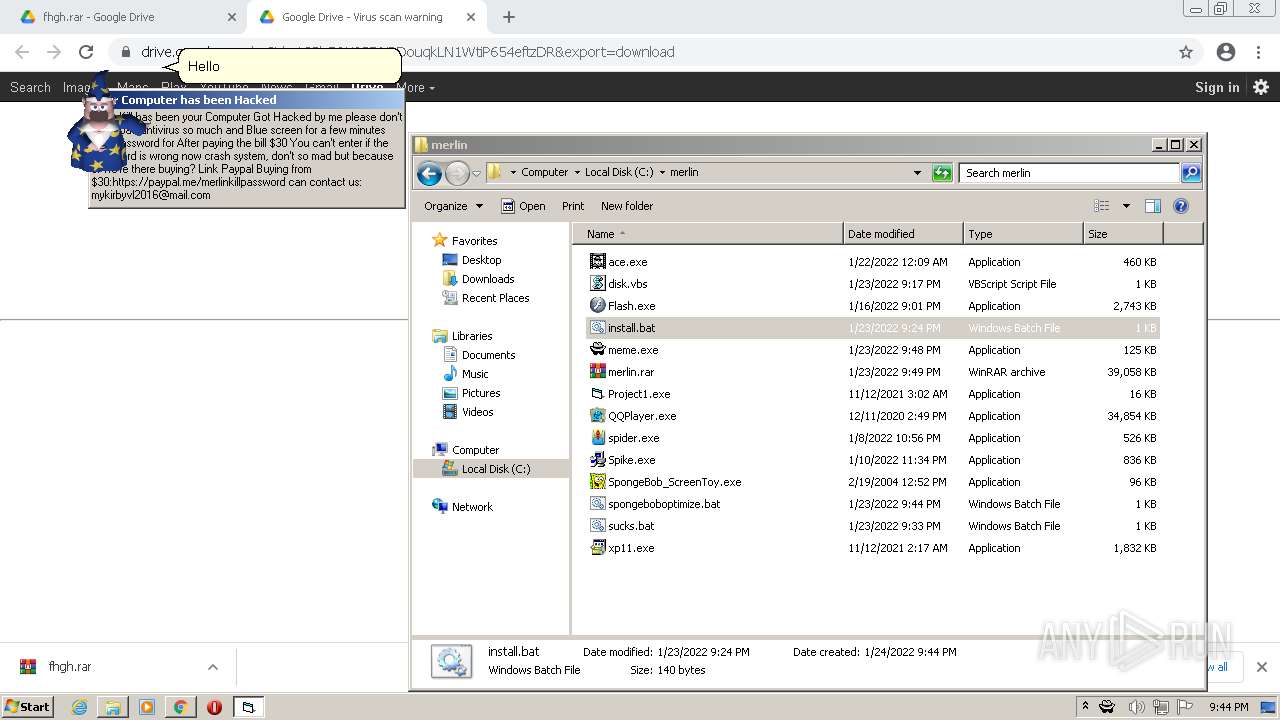
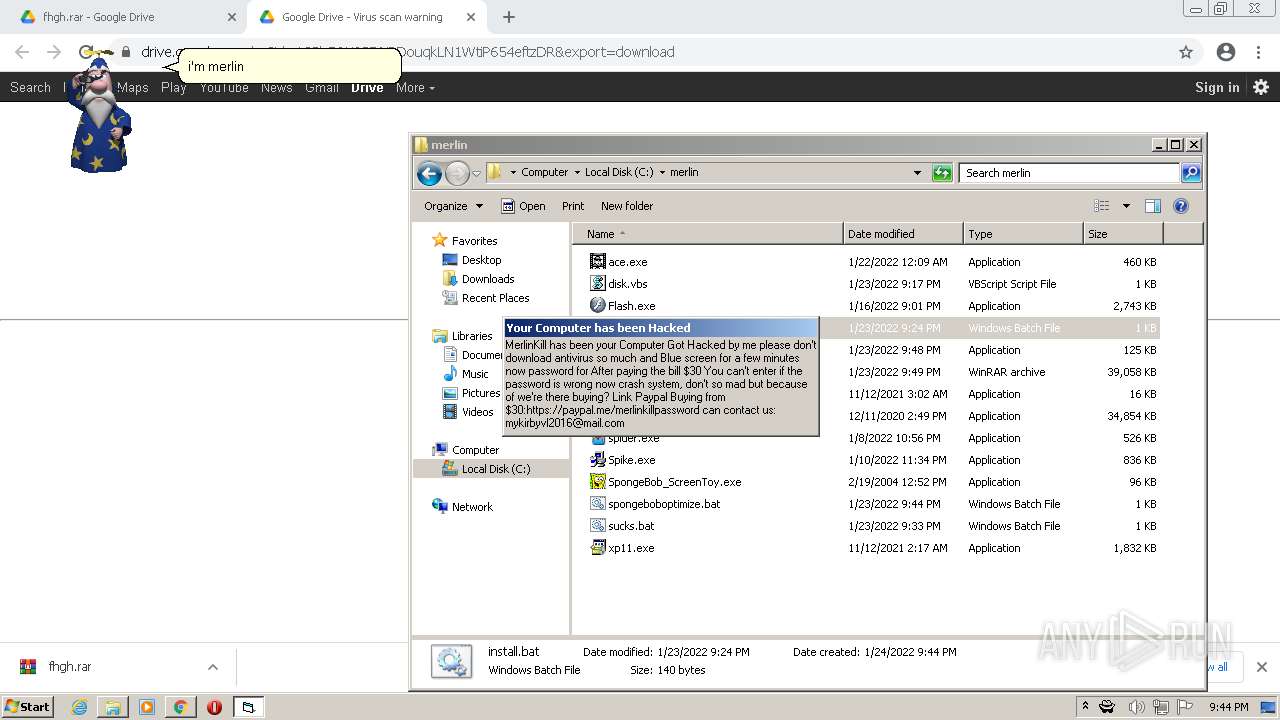
| URL: | https://drive.google.com/file/d/1C8h7QK0SDNPDouqkLN1WtiP654eftzDR/view?usp=sharing |
| Full analysis: | https://app.any.run/tasks/1482f610-04be-4929-a031-9e1dca0b5903 |
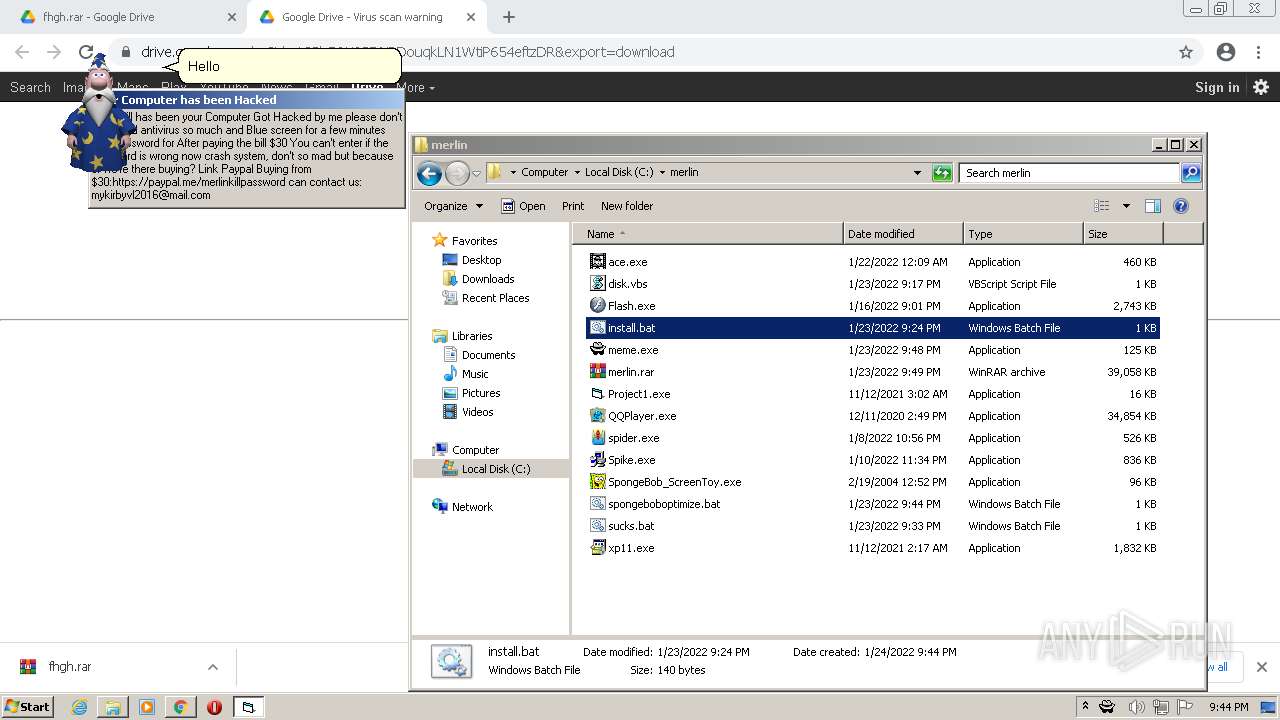
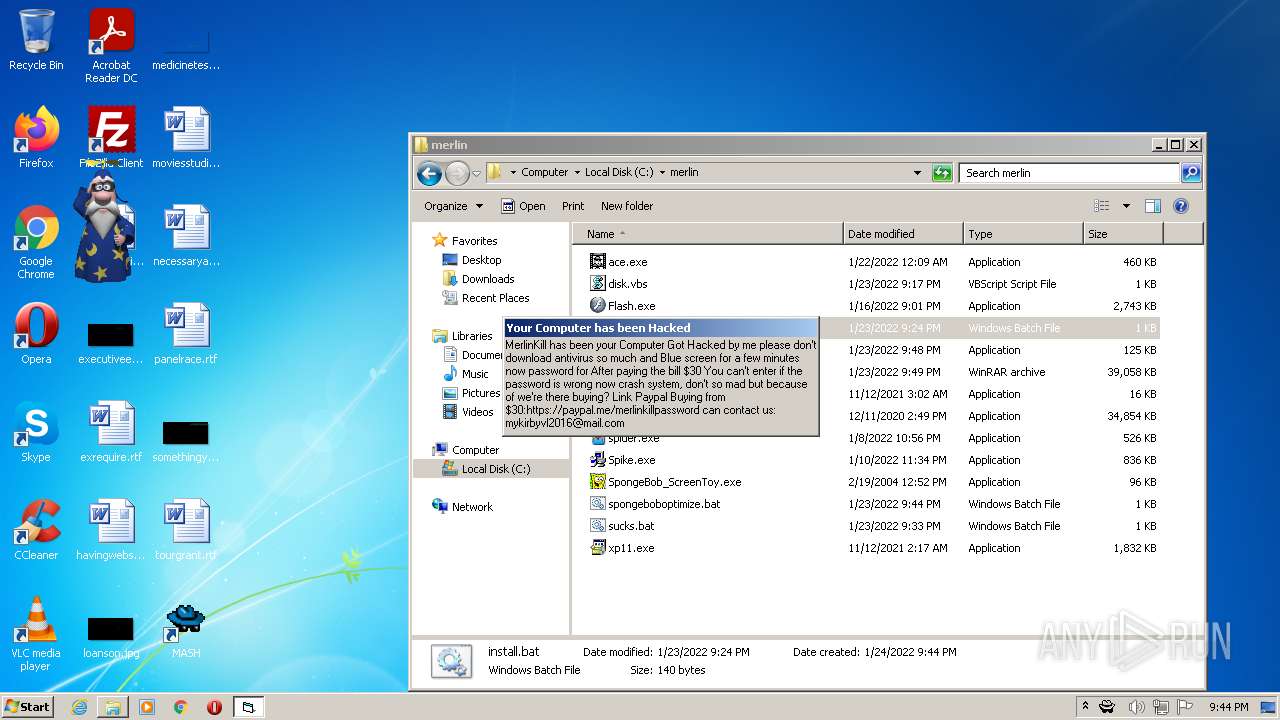
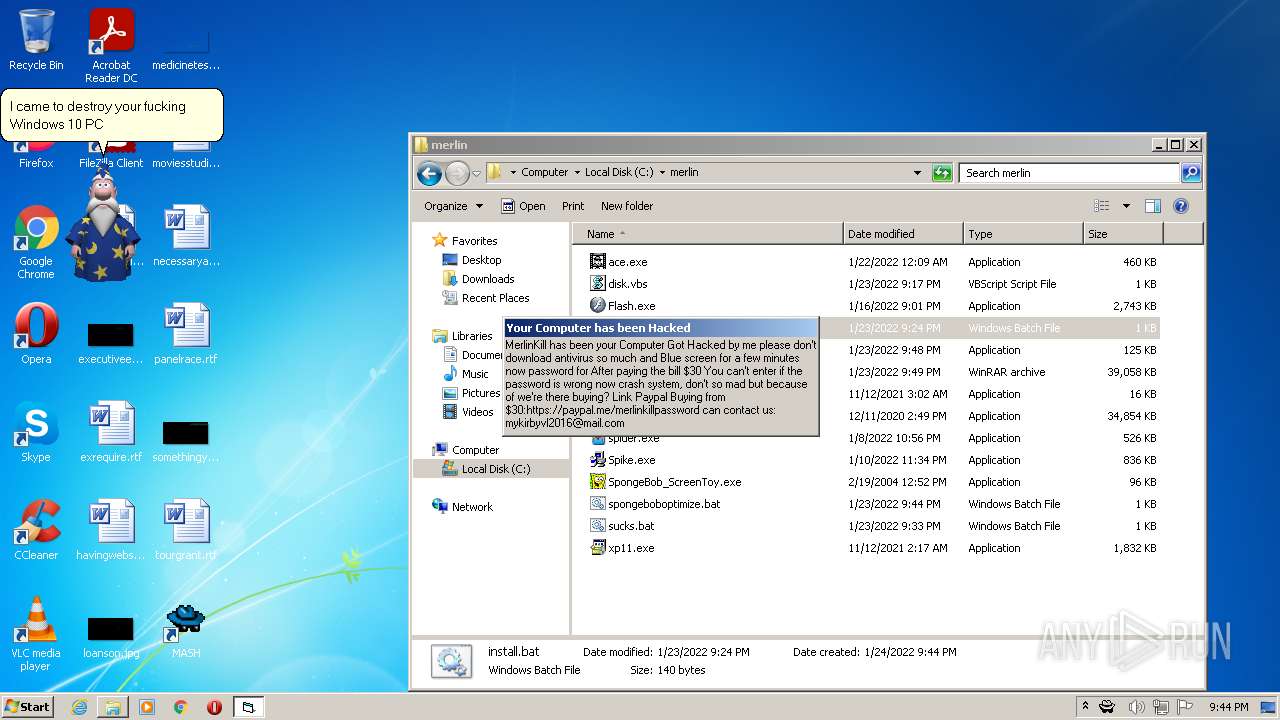
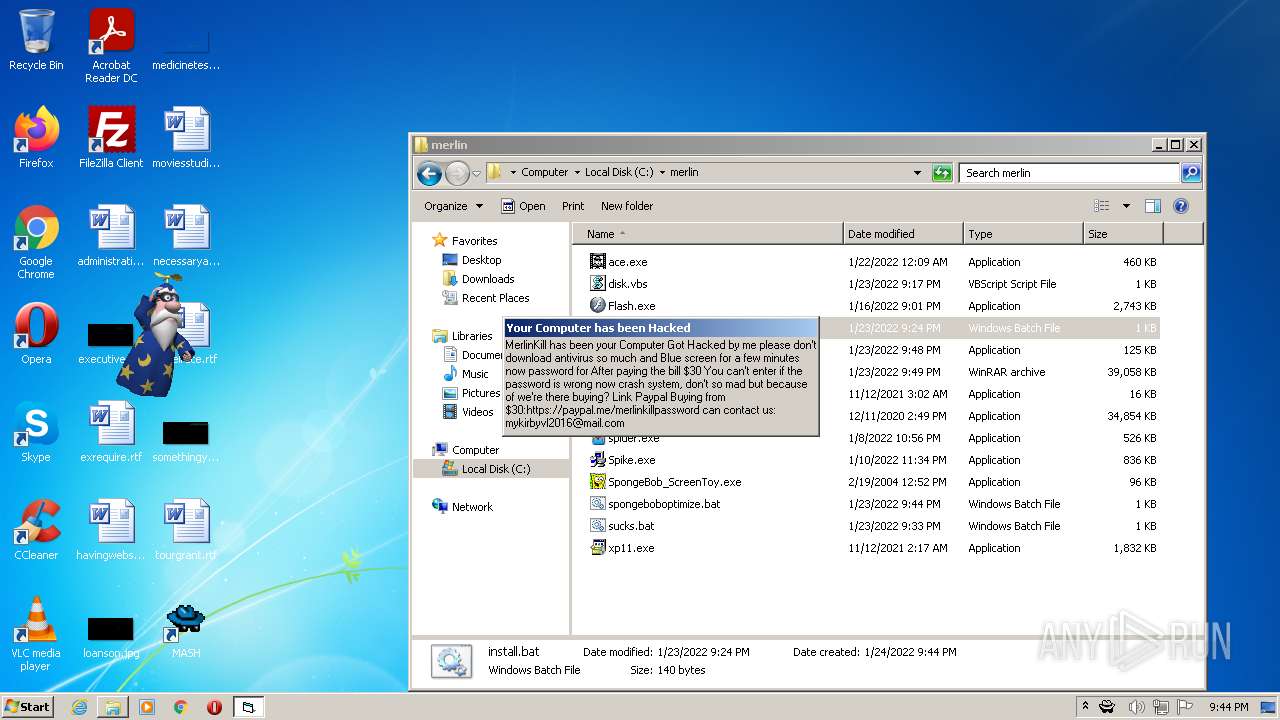
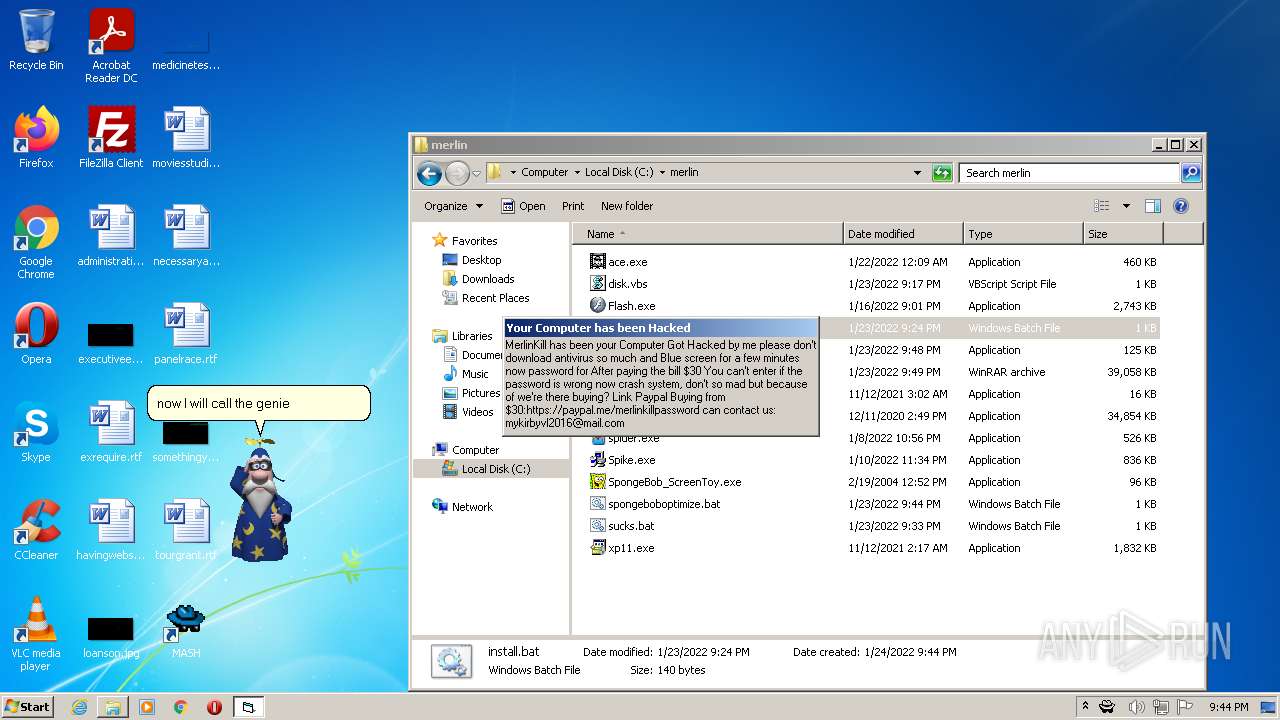
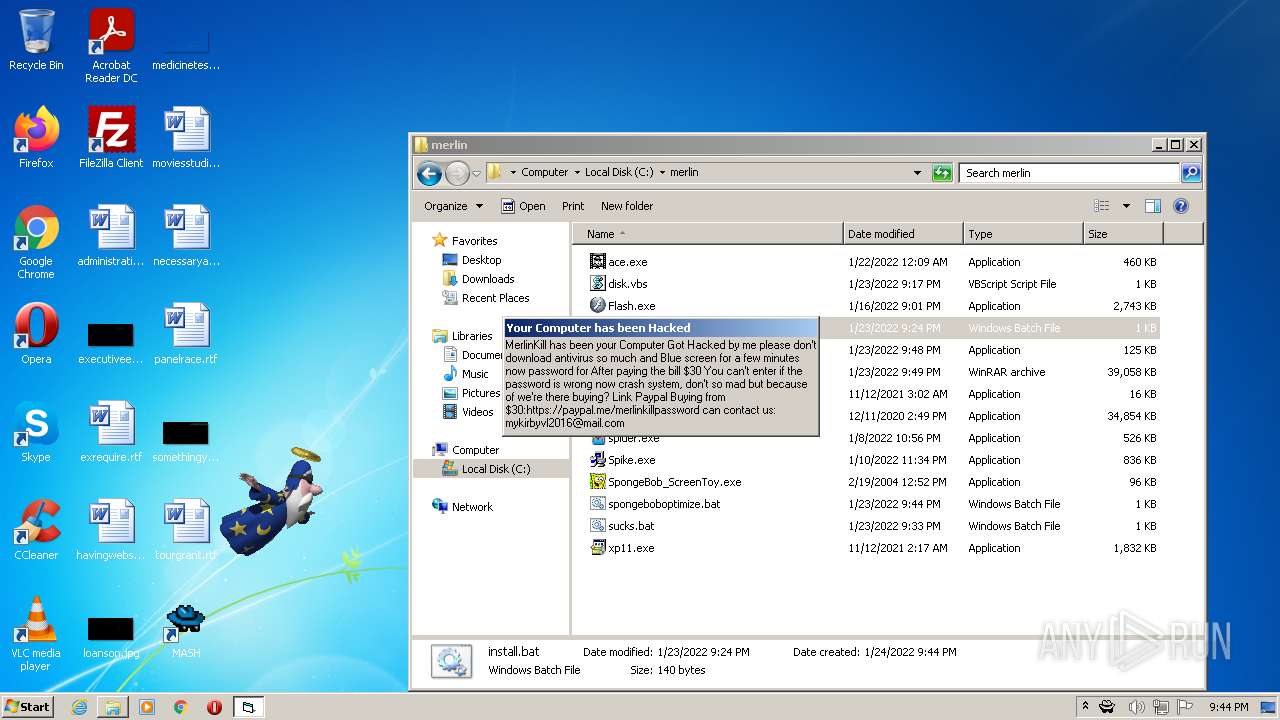
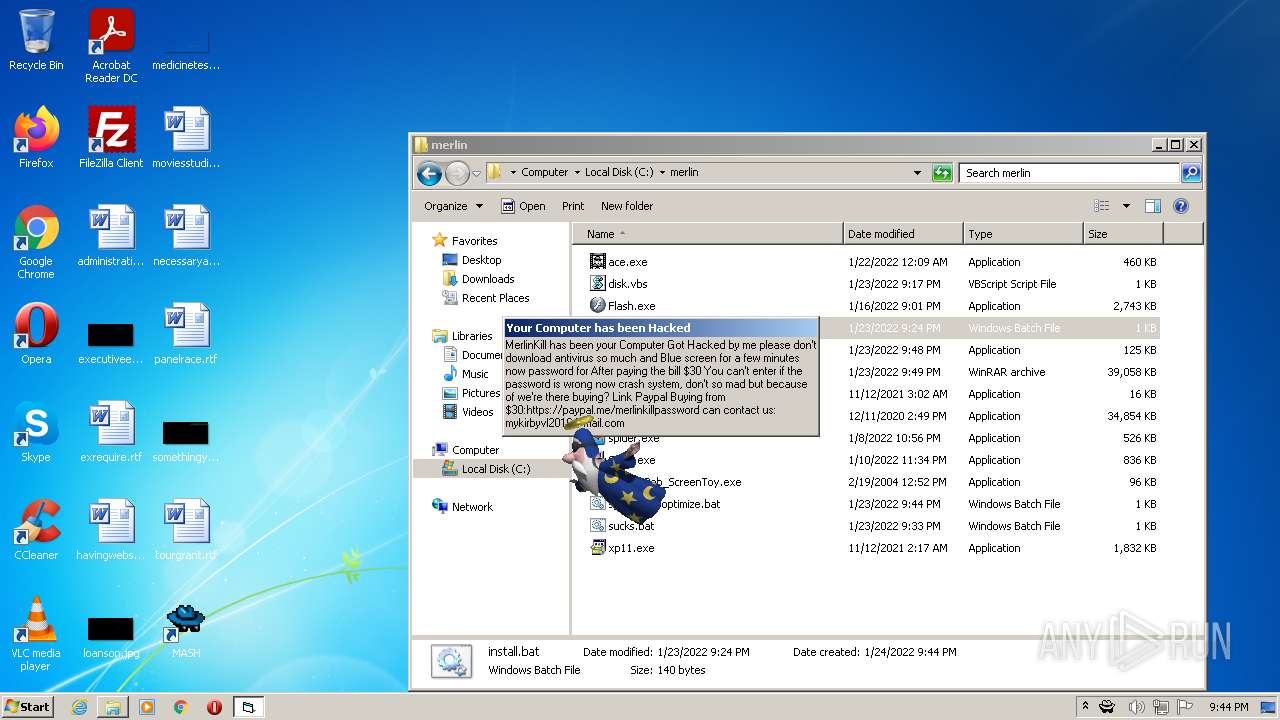
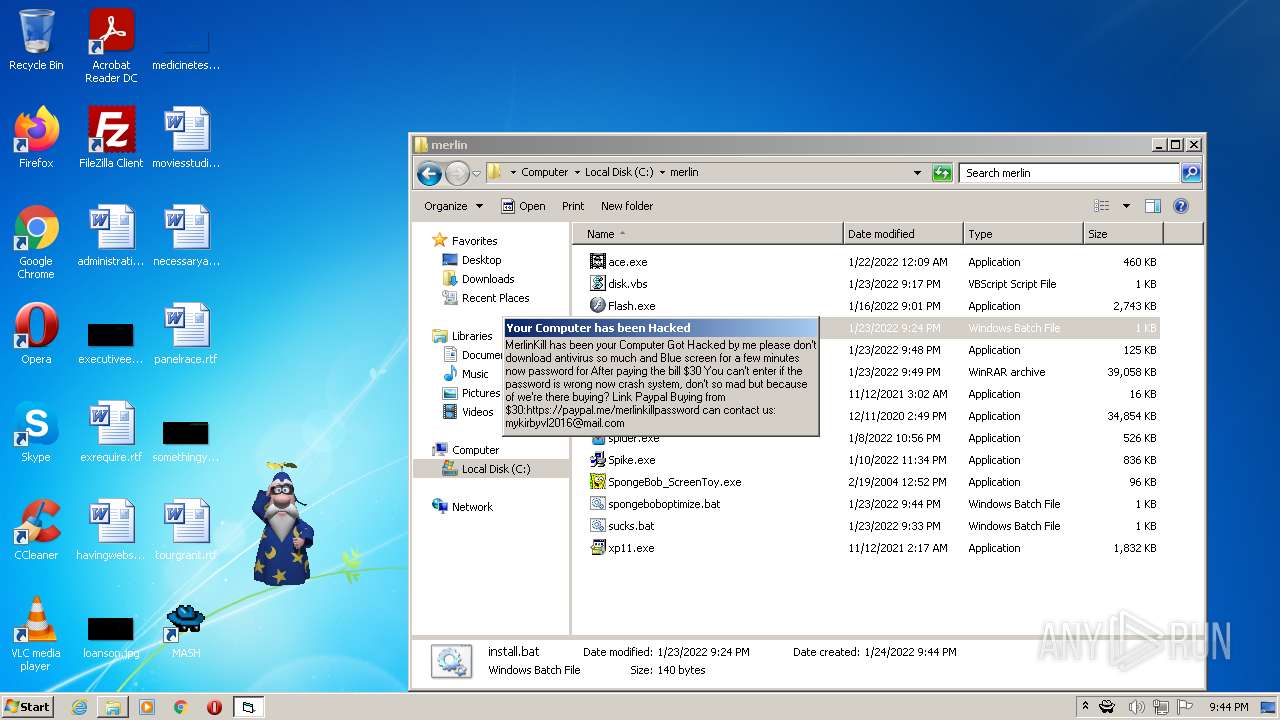
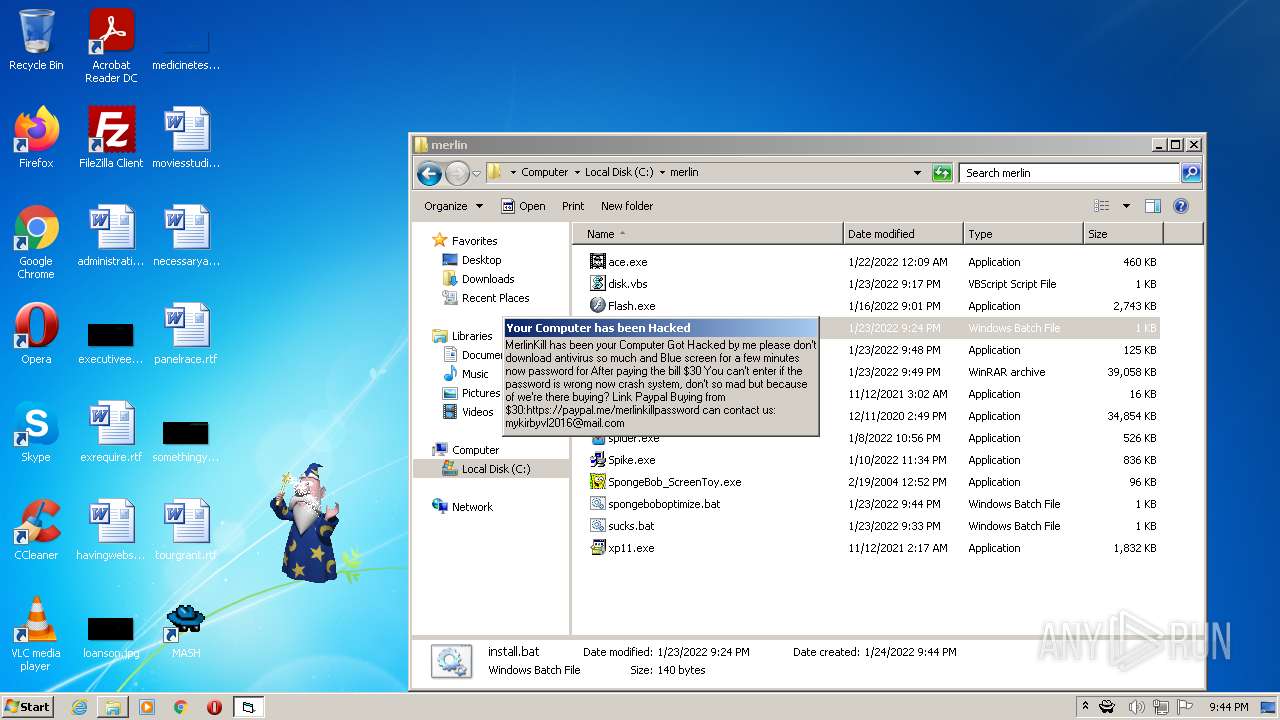
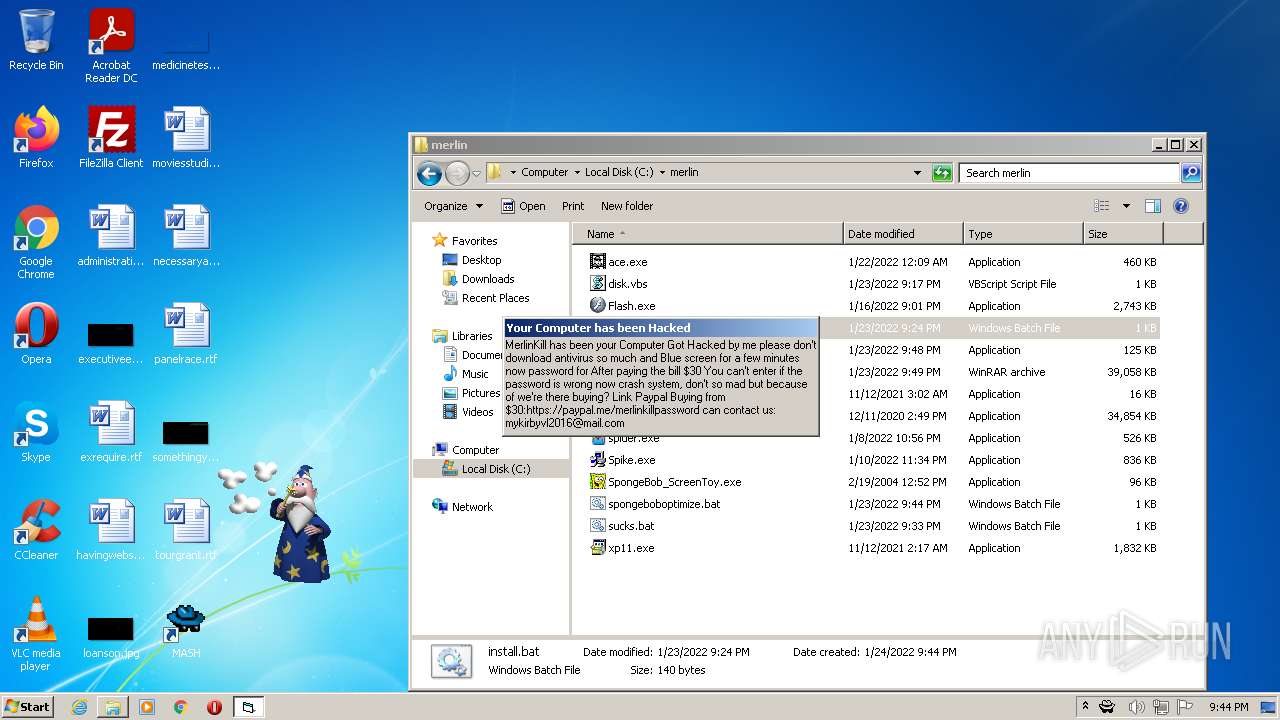
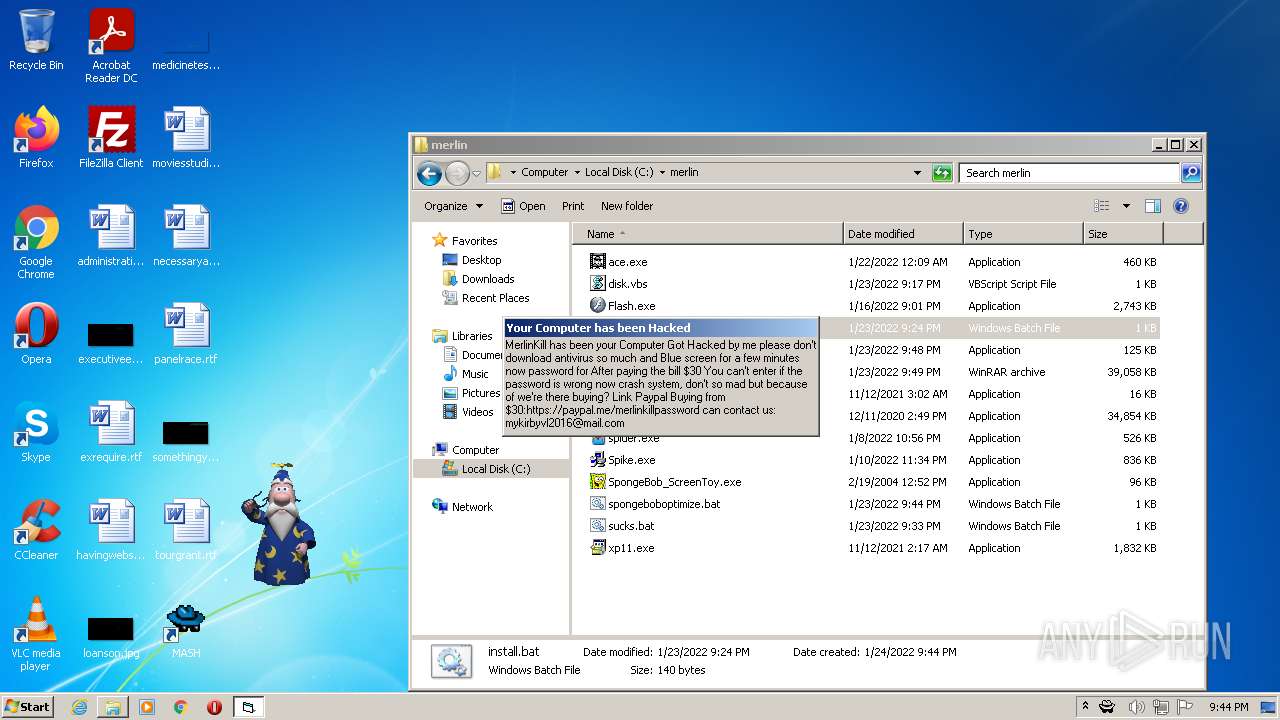
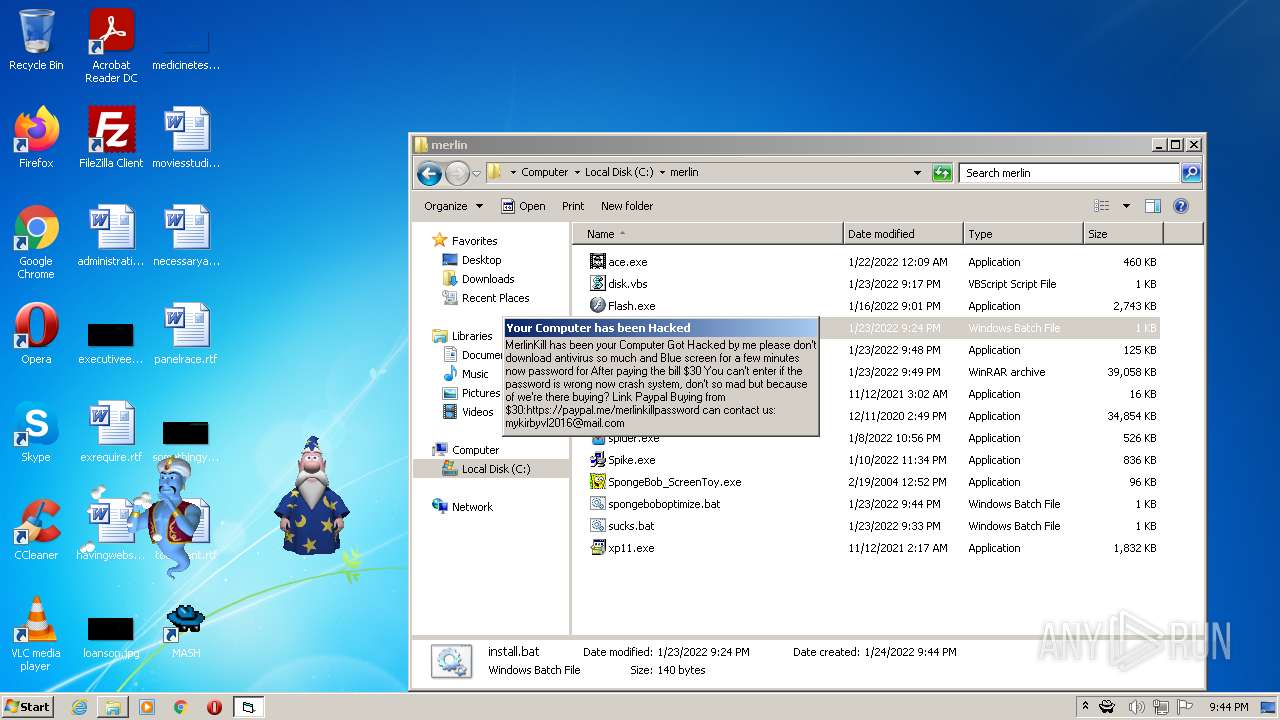
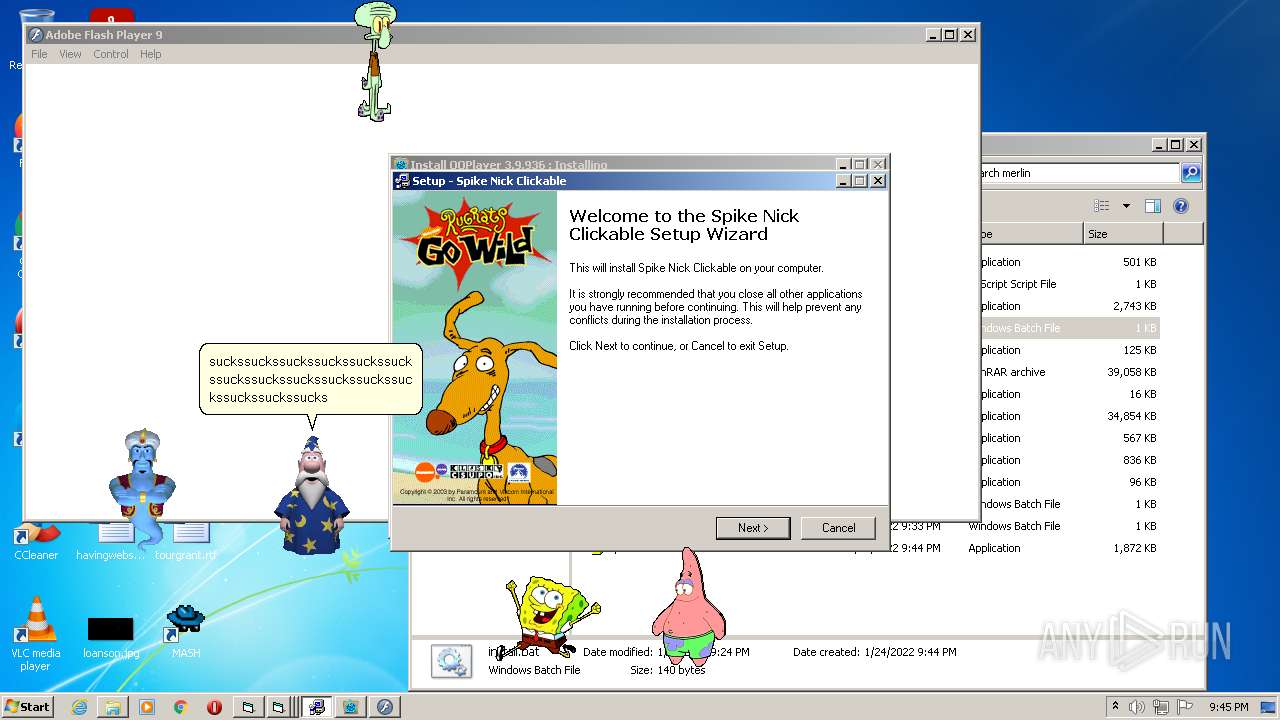
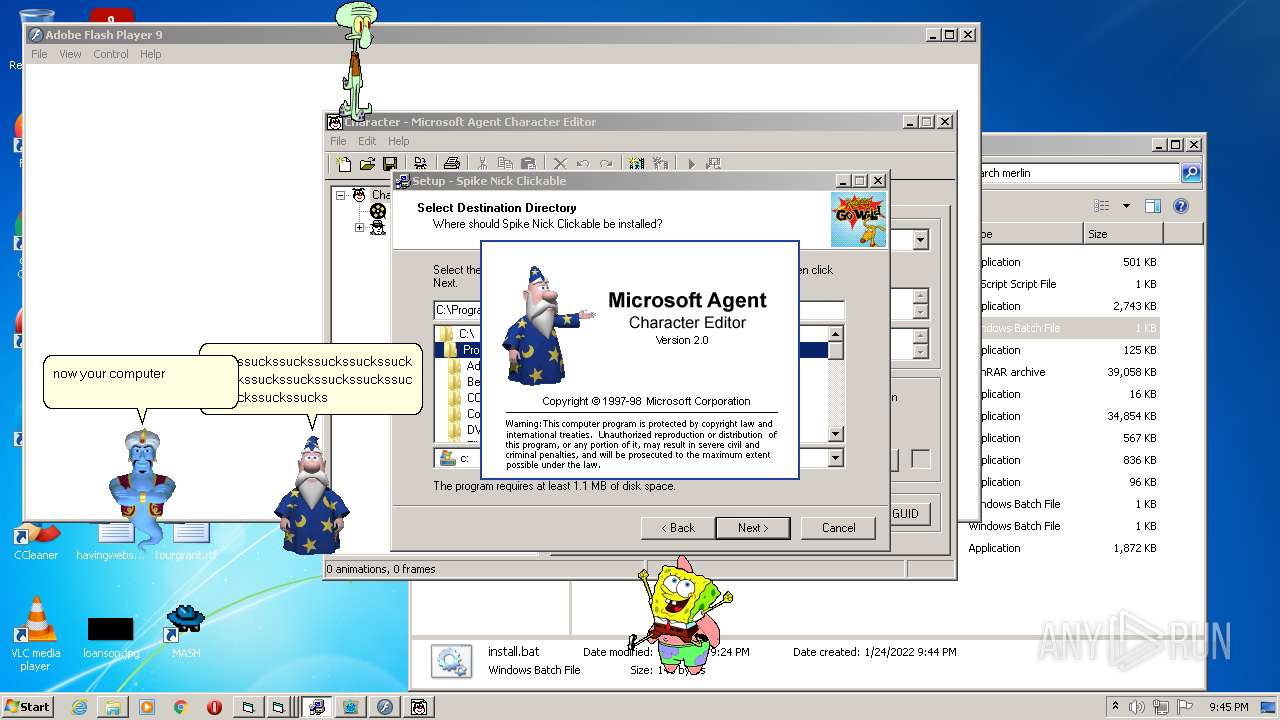
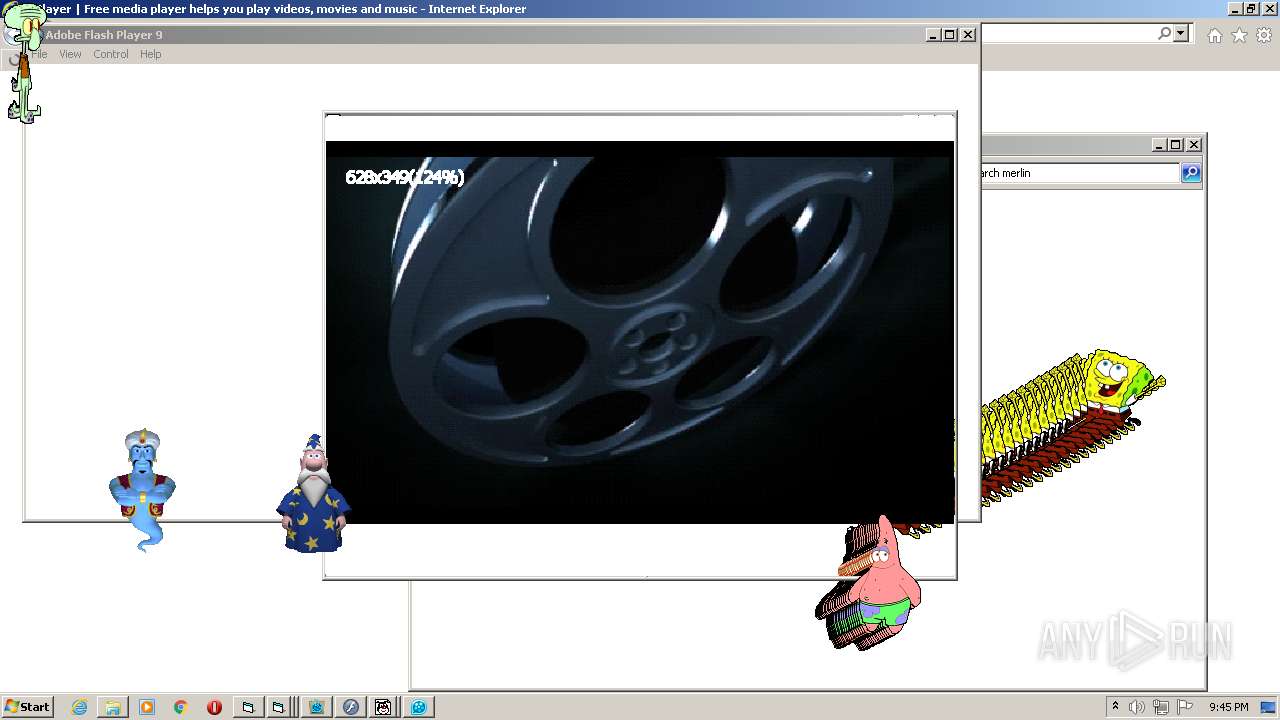
| Verdict: | Malicious activity |
| Threats: | Gootkit is an advanced banking trojan. It is extremely good at evading detection and has an incredibly effective persistence mechanism, making it a dangerous malware that researchers and organizations should be aware of. |
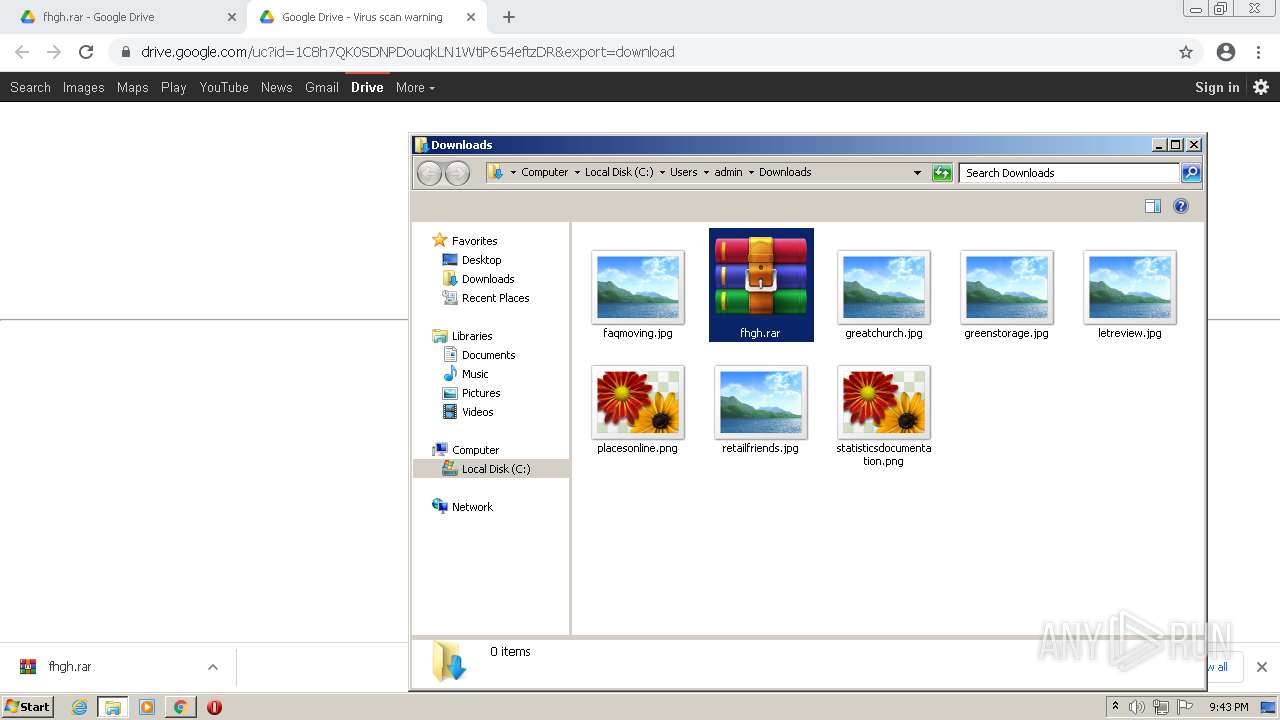
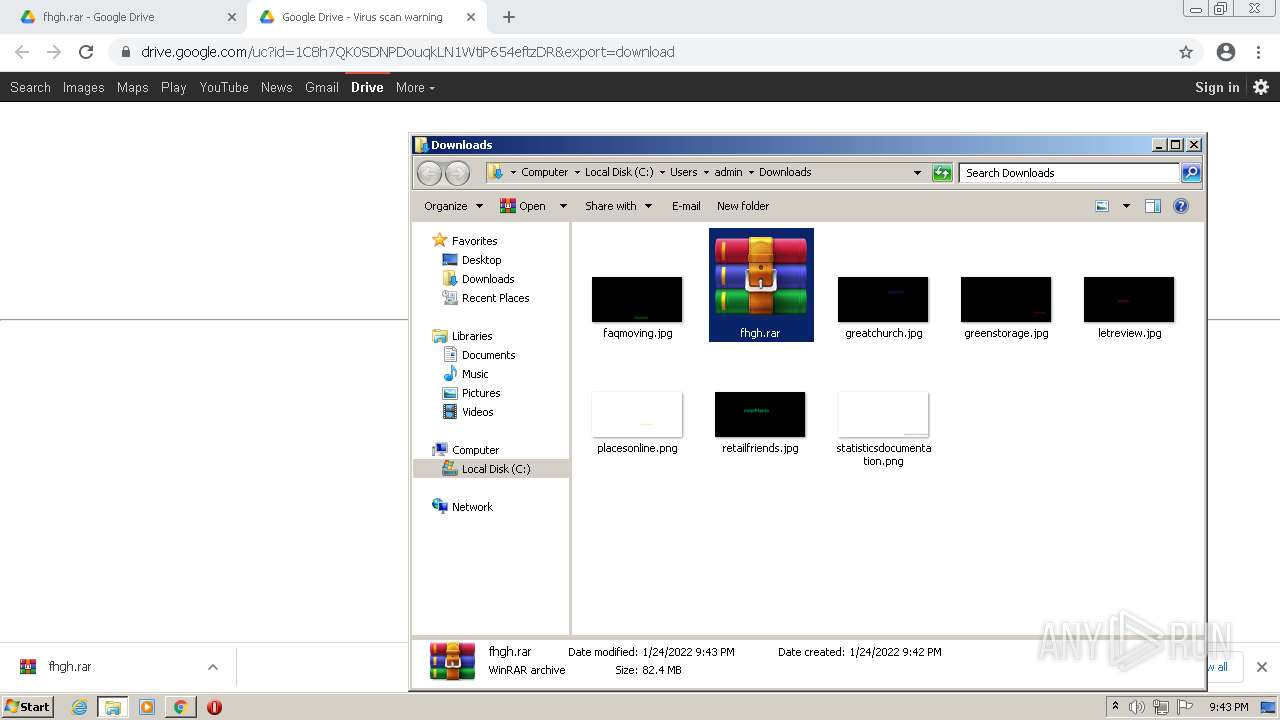
| Analysis date: | January 24, 2022, 21:42:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FF1A55239BFE16C5215F85888768DC08 |
| SHA1: | ED1E853B04721D71AD8D81F38C65831F3A6ABDAD |
| SHA256: | 81BF6B241F683CDD4293F35A9E1D5D1A76AD30C1AB81488AB1B4E44EF6B25178 |
| SSDEEP: | 3:N8PMMtZJulocP7dACFANJ4MWZC:2AdP2mxMWZC |
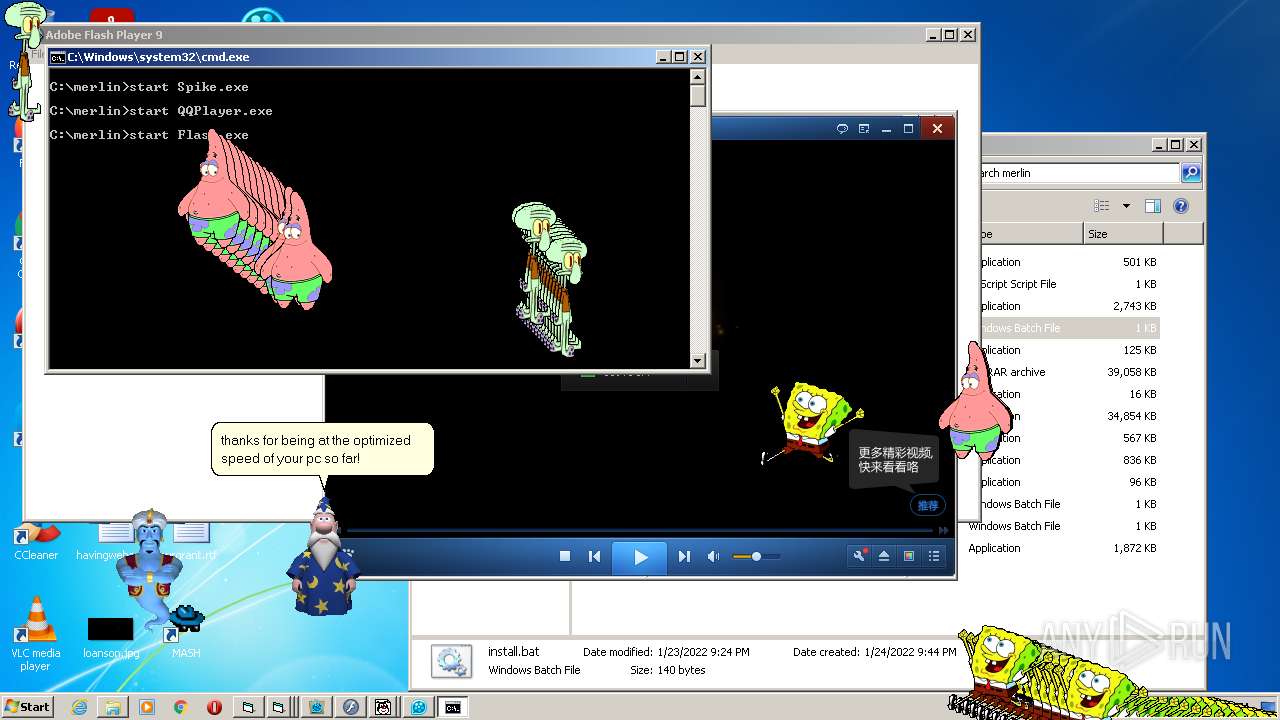
MALICIOUS
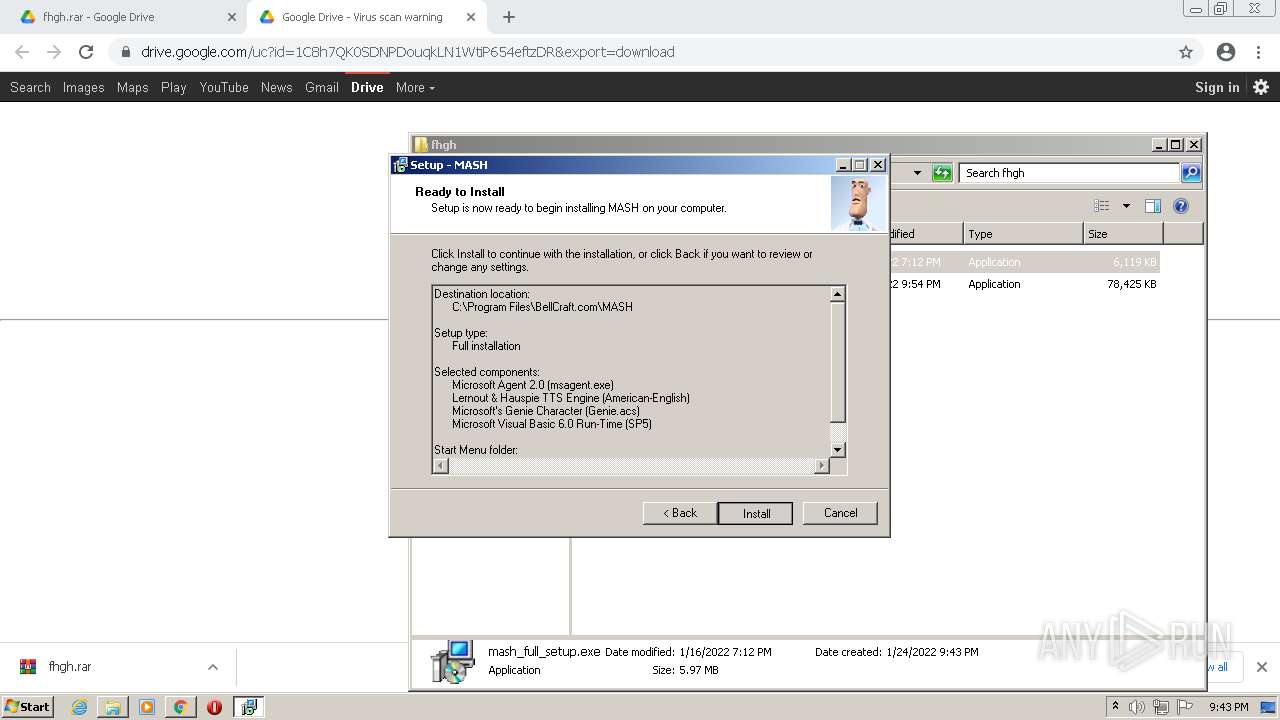
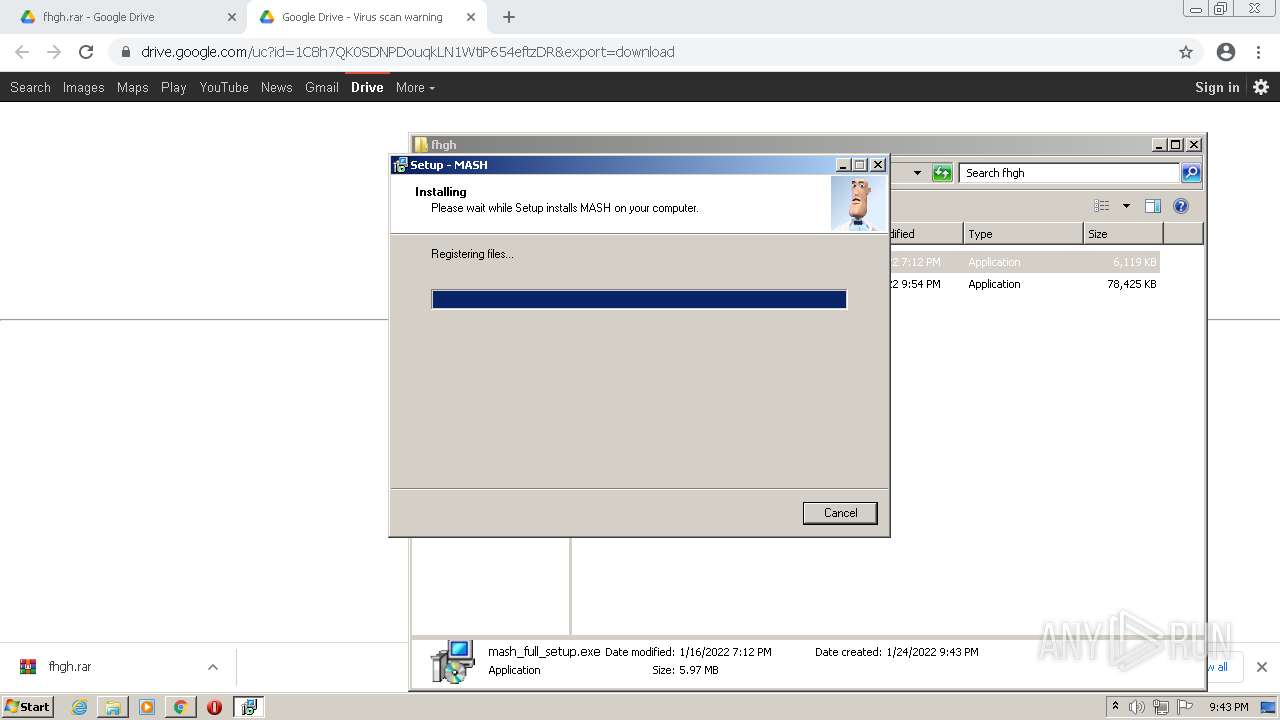
Application was dropped or rewritten from another process
- mash_full_setup.exe (PID: 756)
- mash_full_setup.exe (PID: 3800)
- spchapi.exe (PID: 3304)
- AgentSvr.exe (PID: 2884)
- xp11.exe (PID: 1080)
- xp11.exe (PID: 2588)
- xp11.exe (PID: 1244)
- meme.exe (PID: 3856)
- AgentSvr.exe (PID: 2220)
- Project1.exe (PID: 1080)
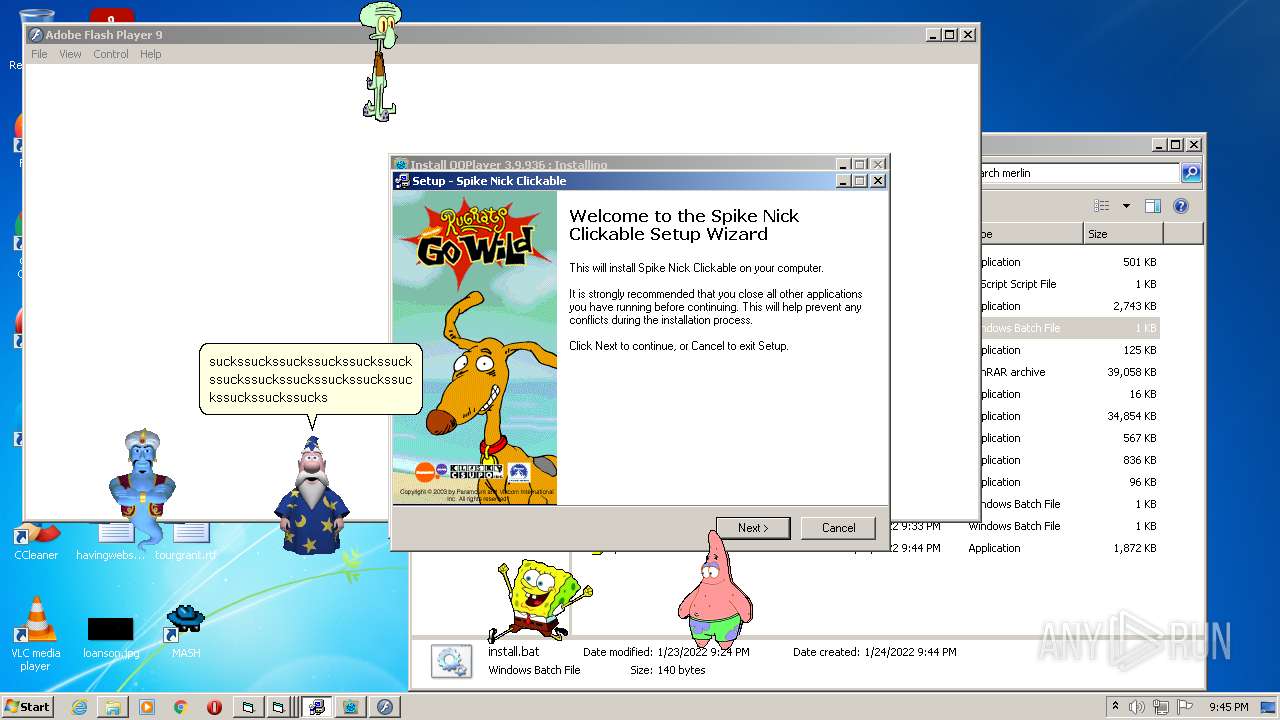
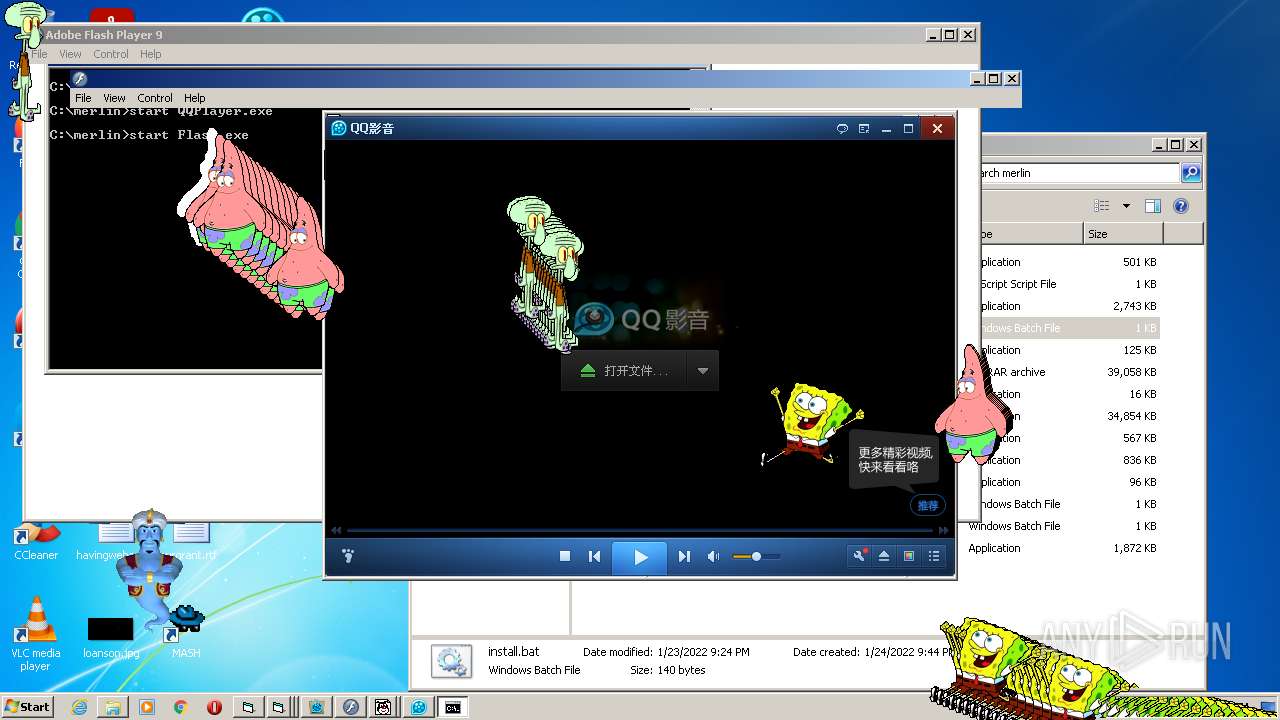
- Spike.exe (PID: 3148)
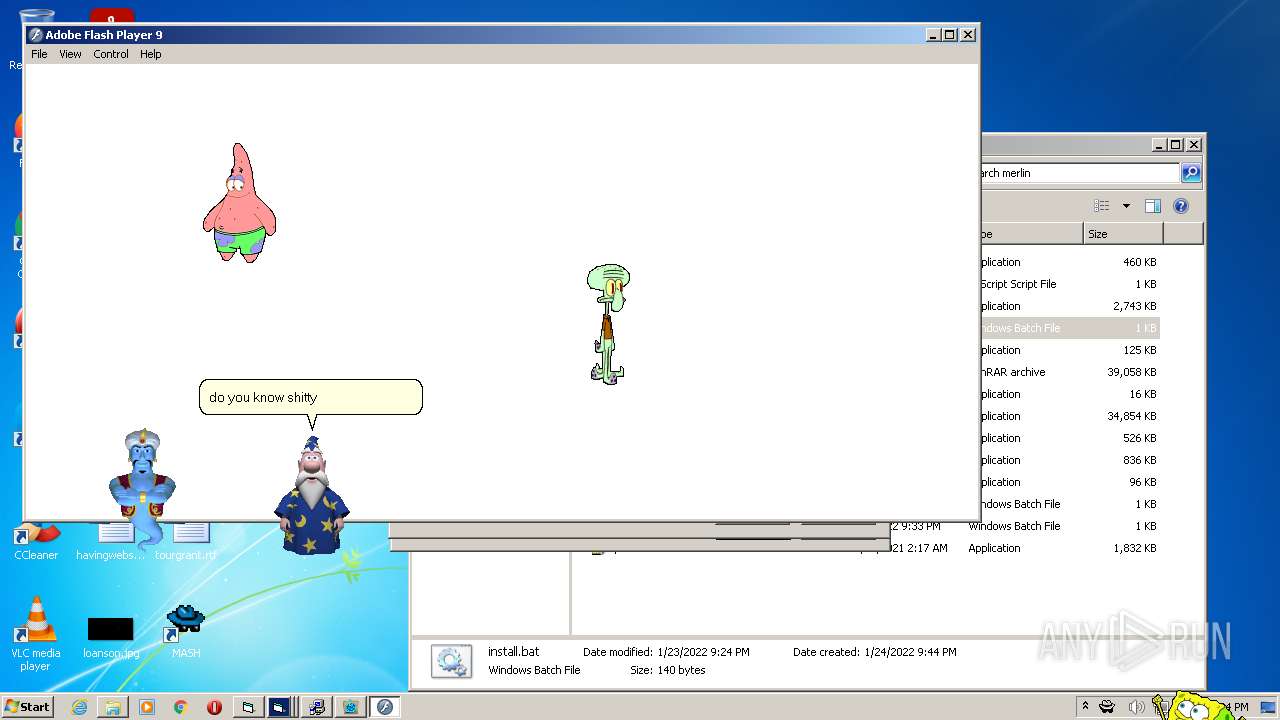
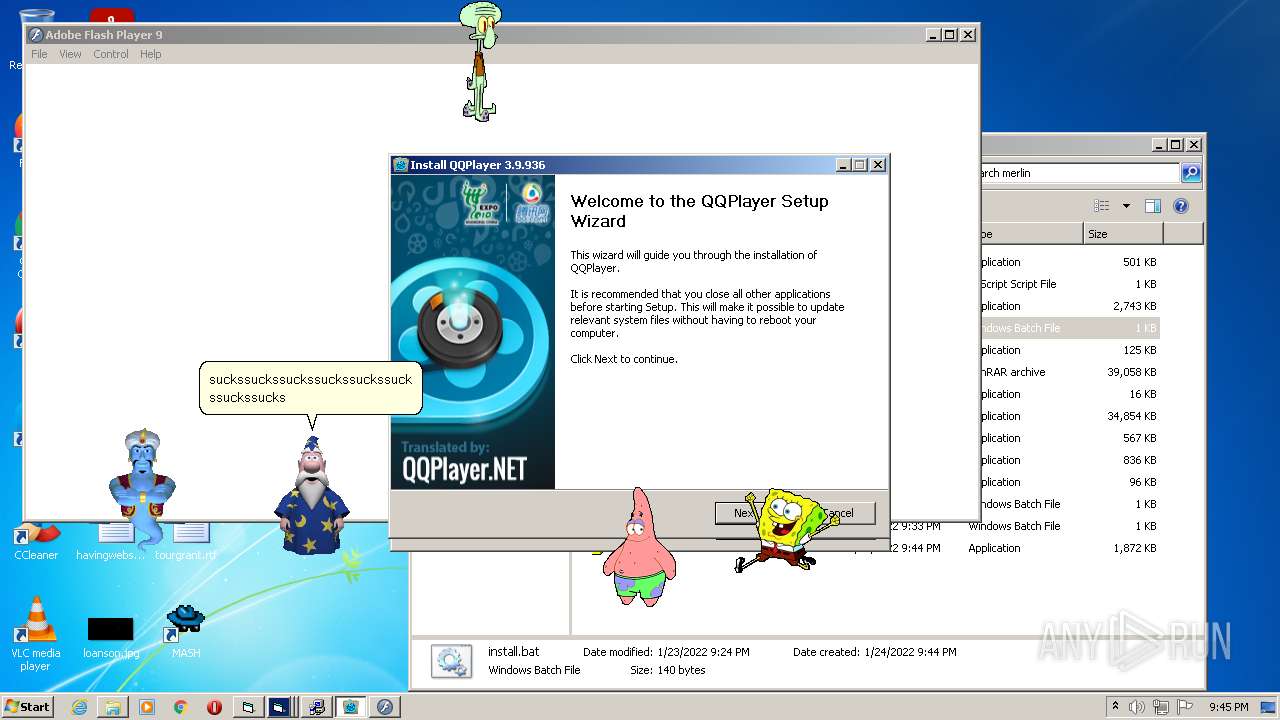
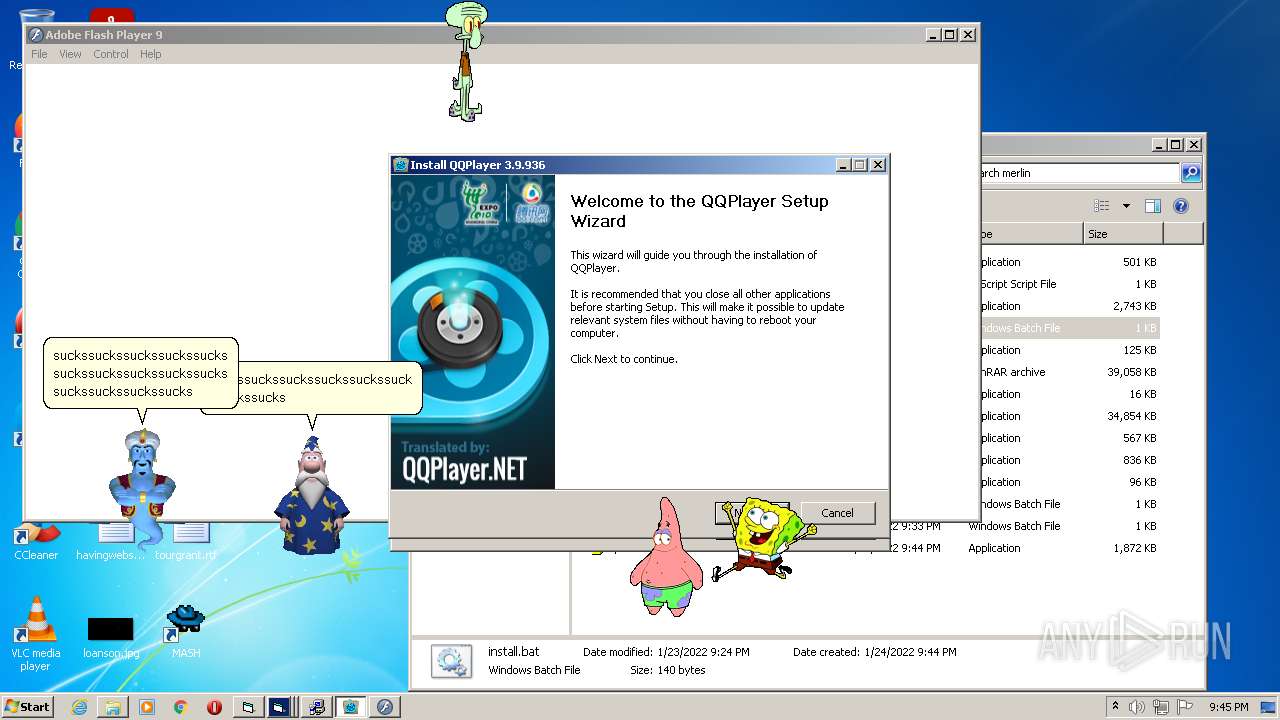
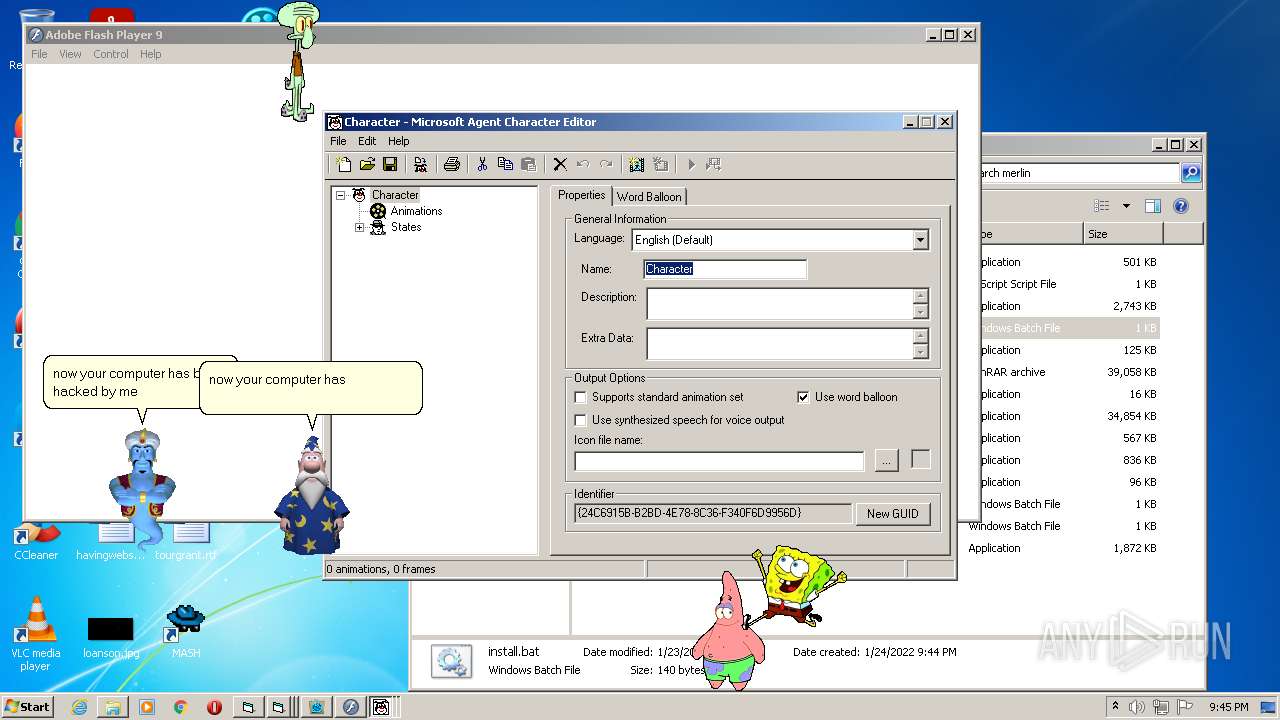
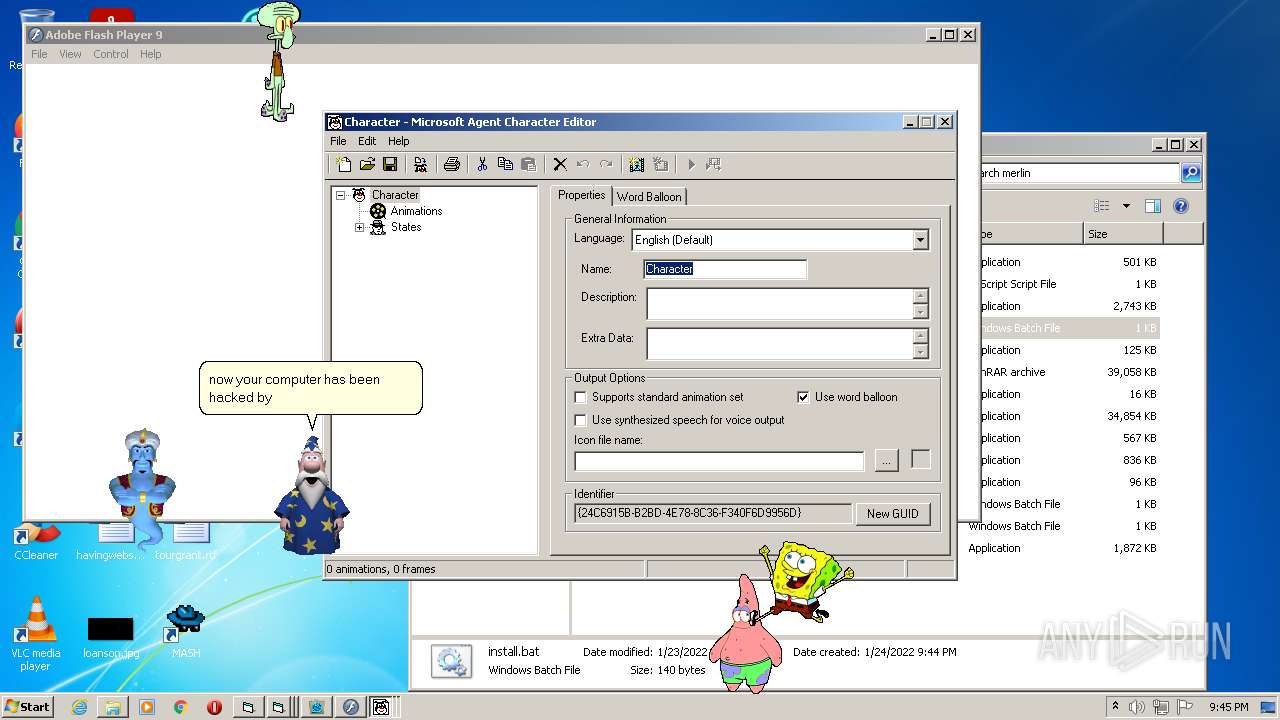
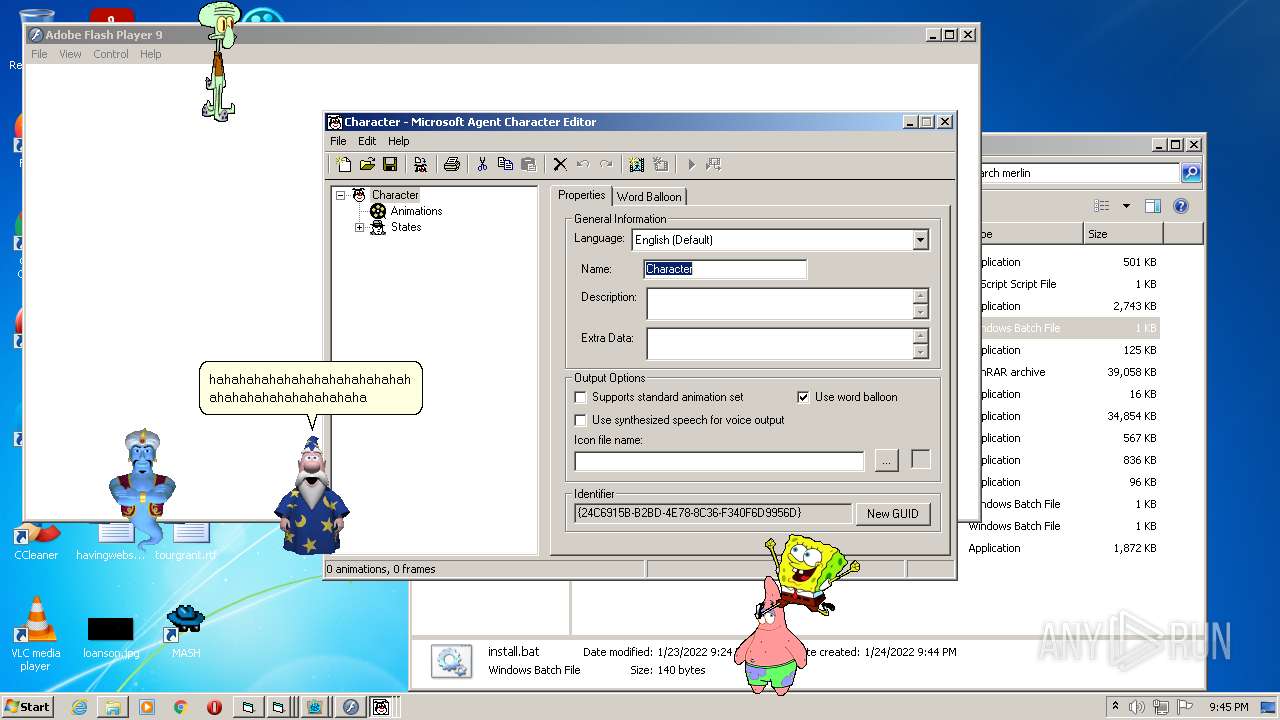
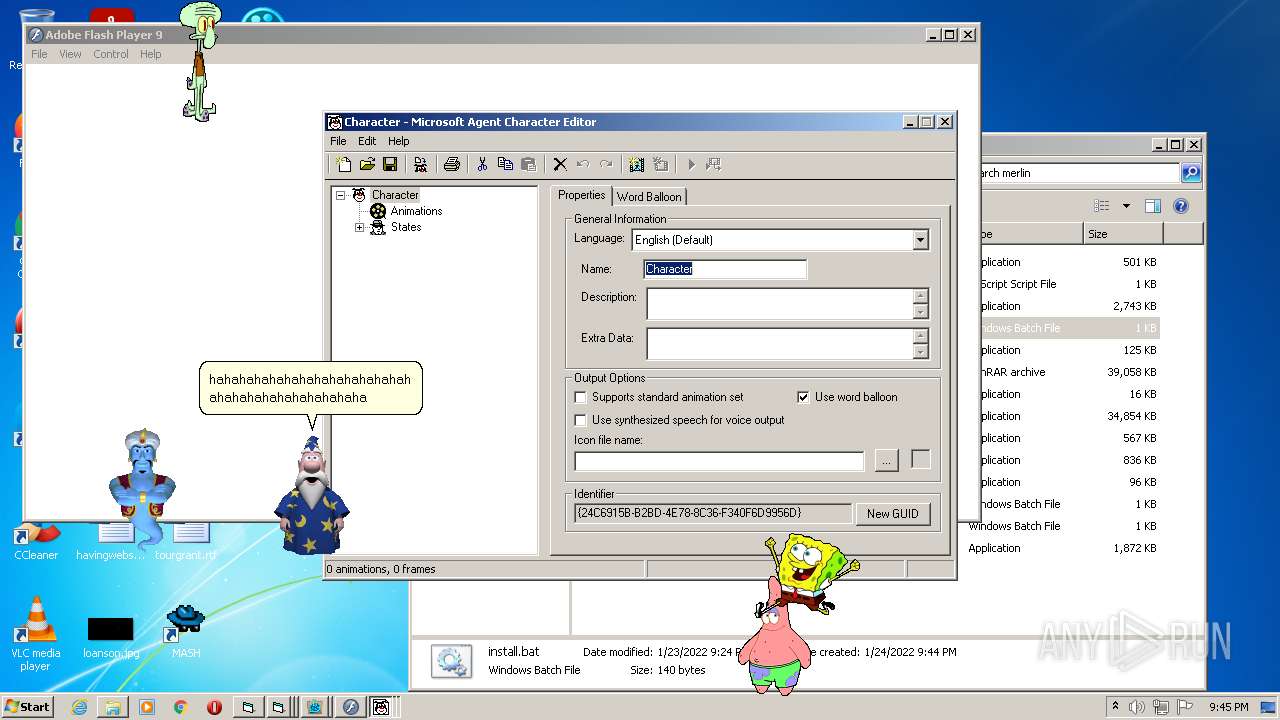
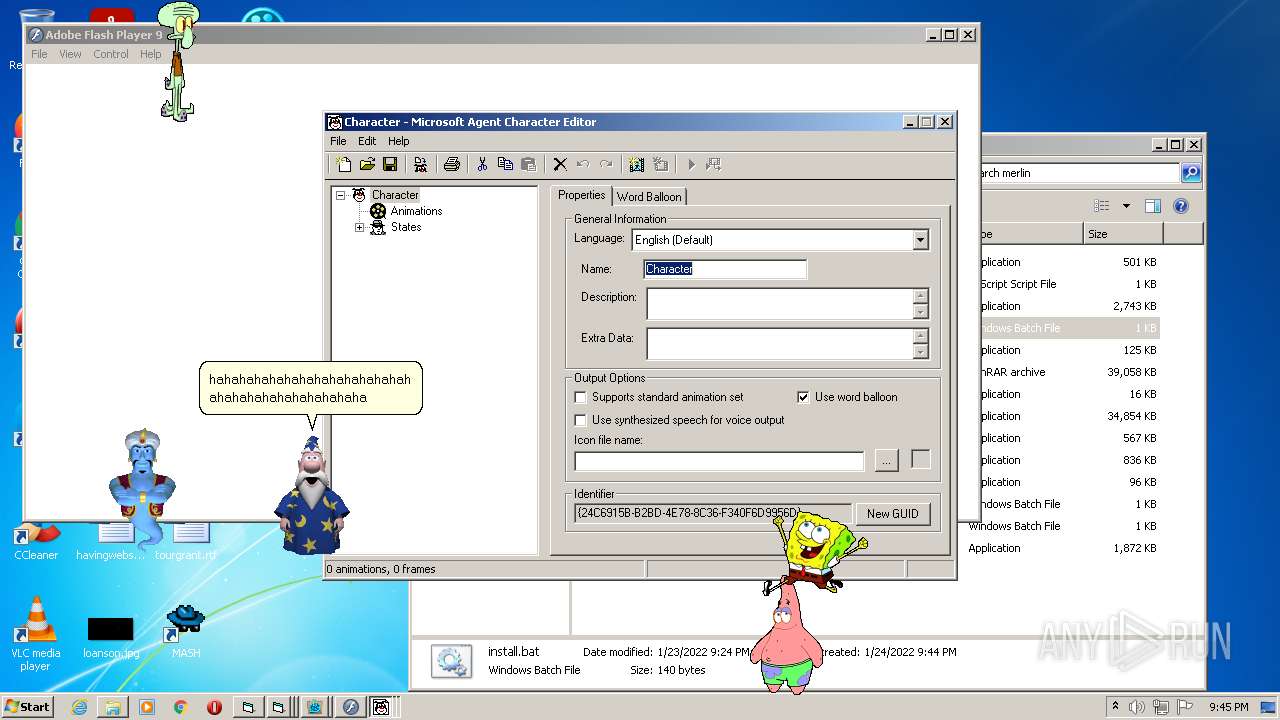
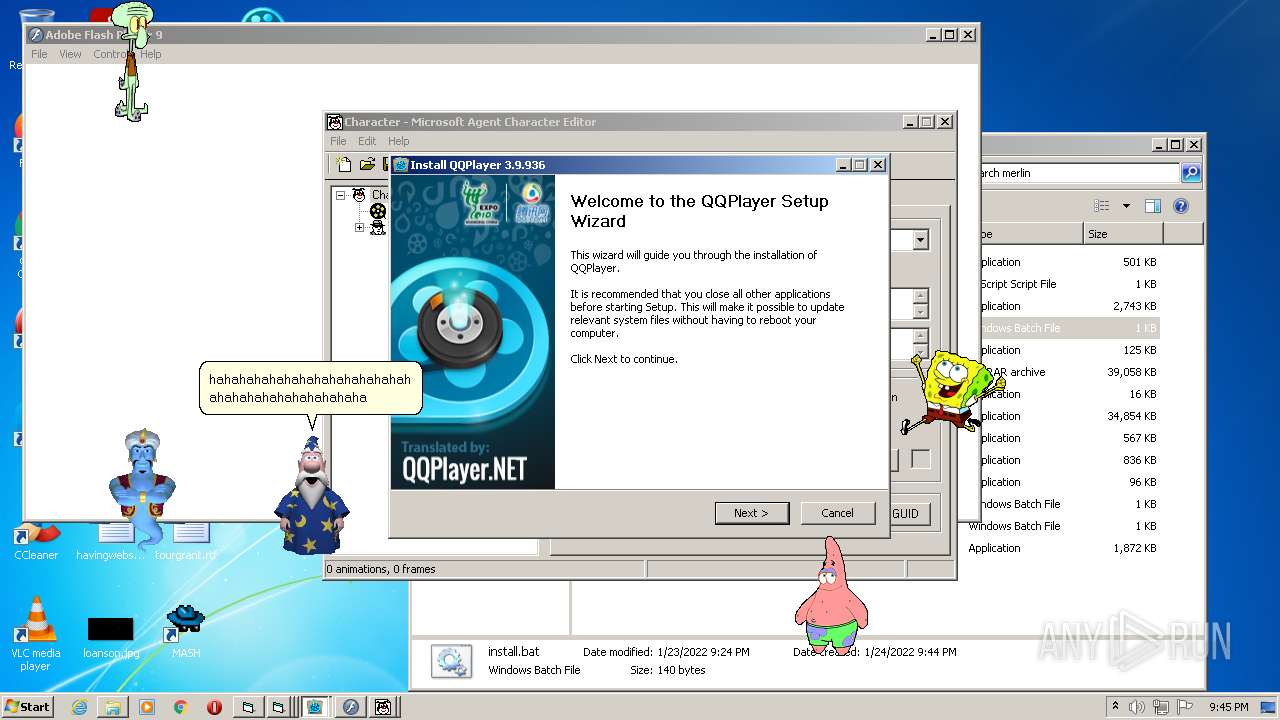
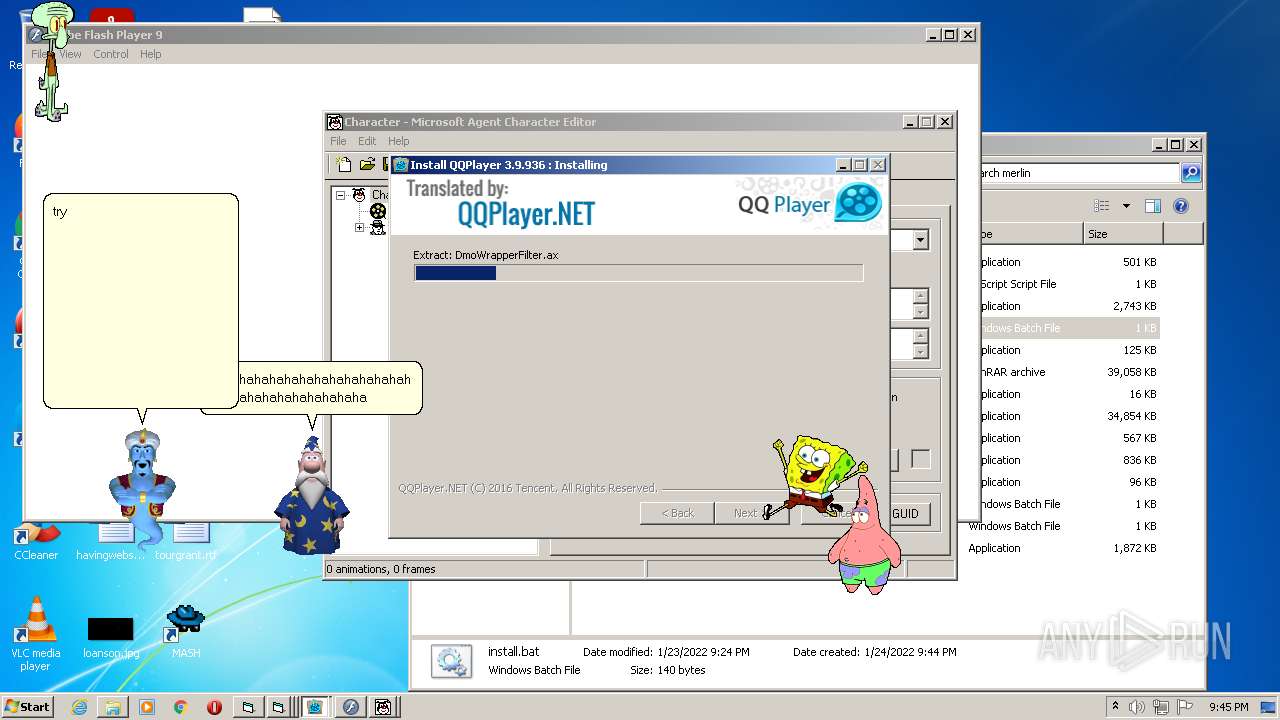
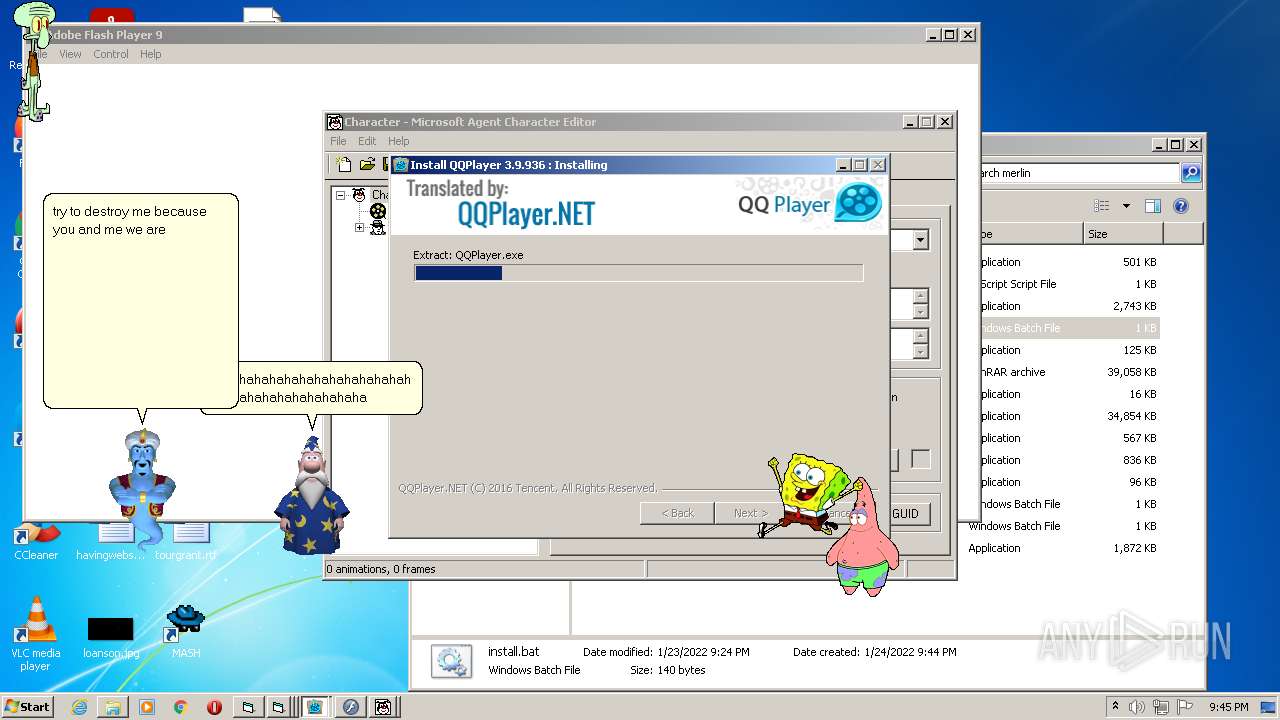
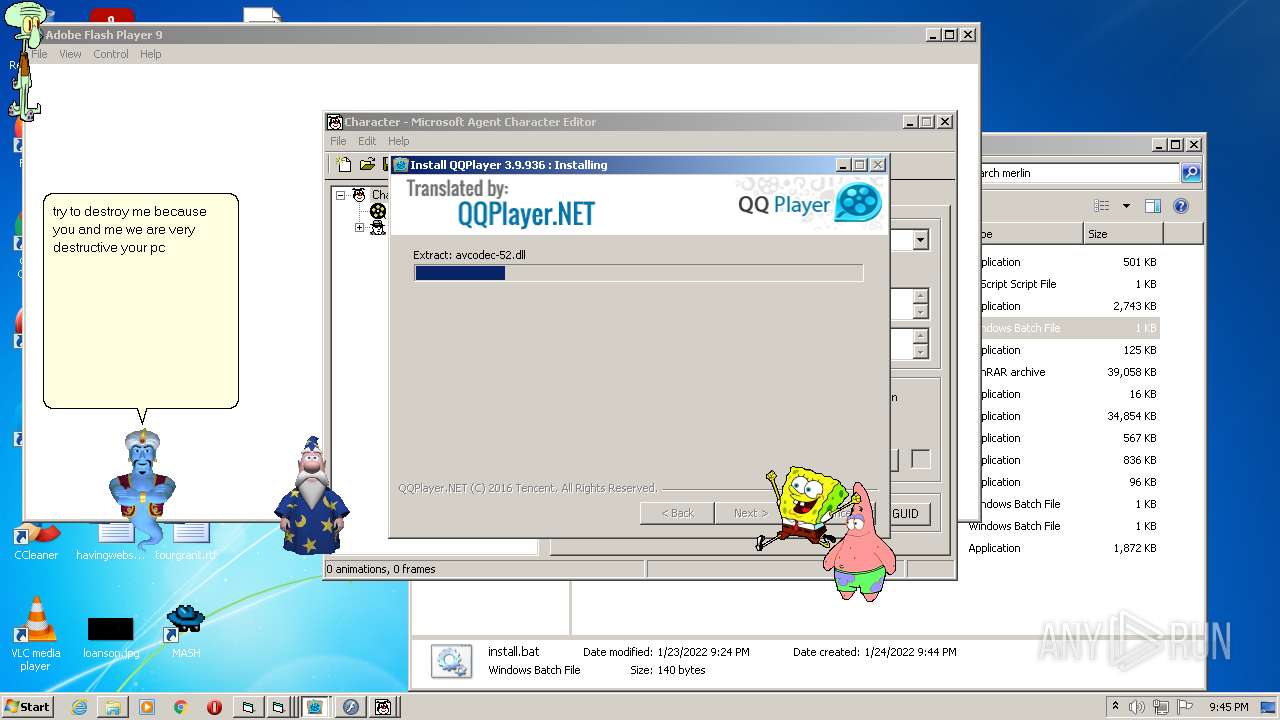
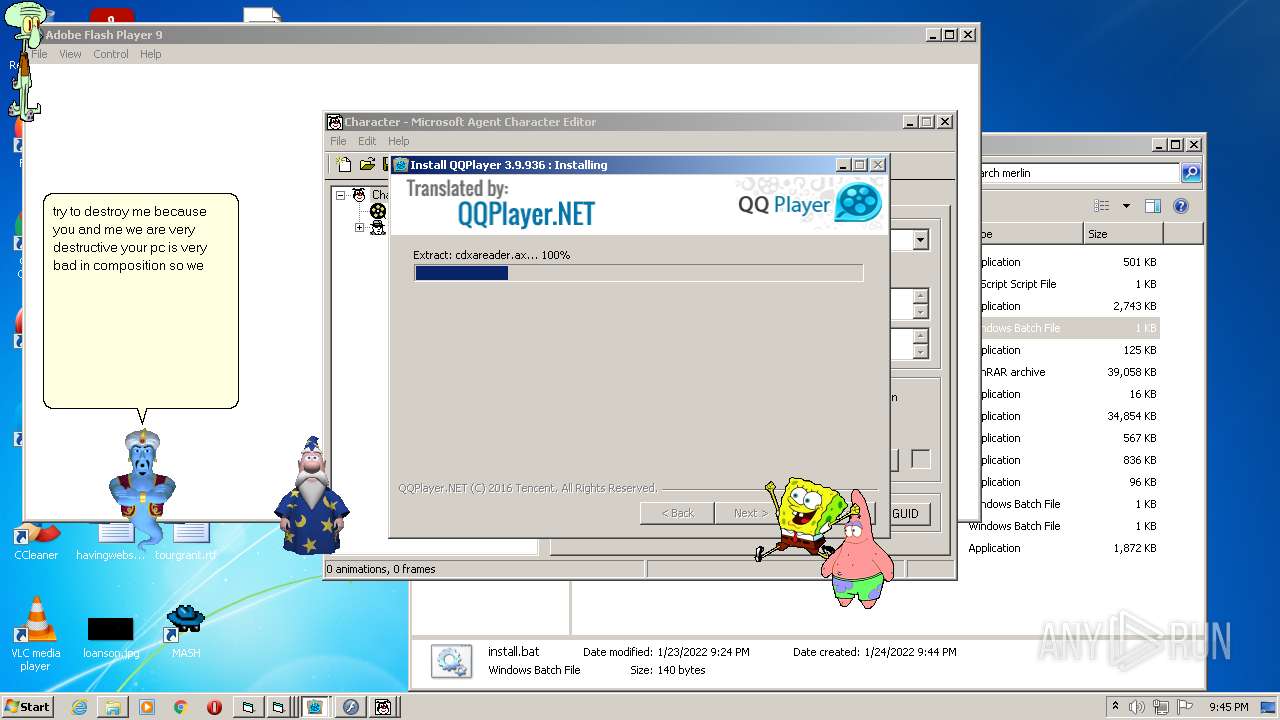
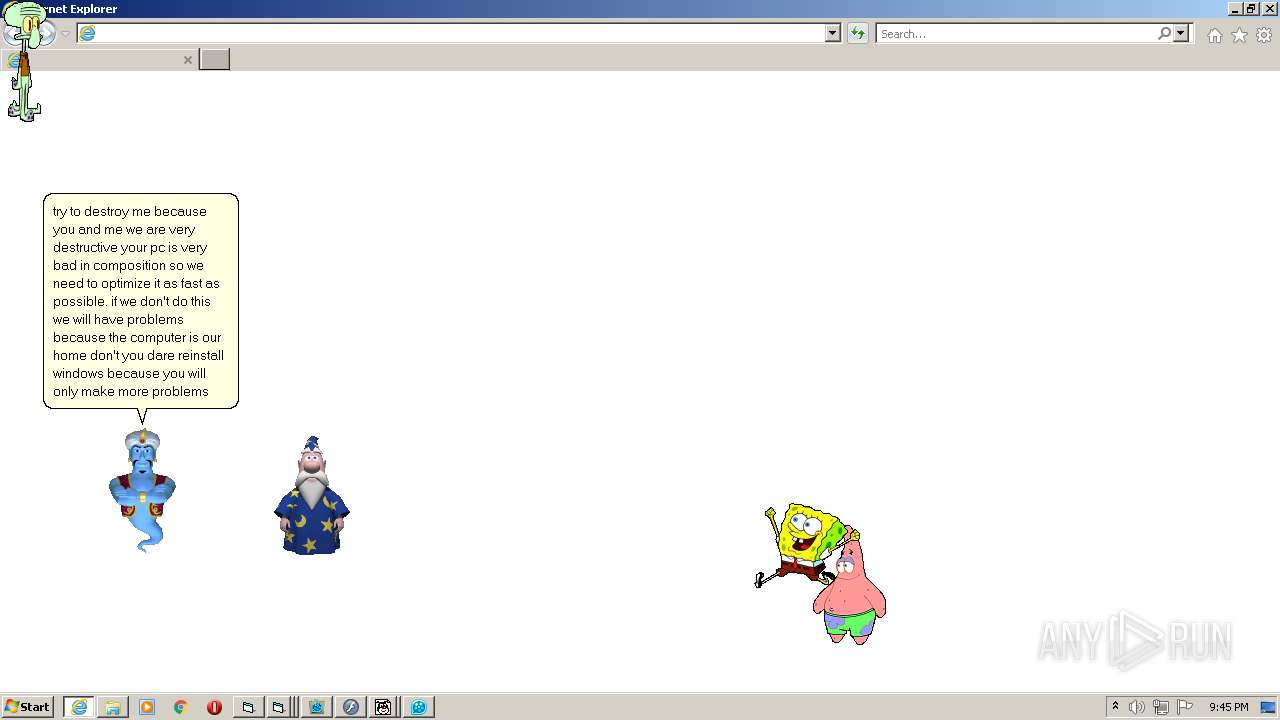
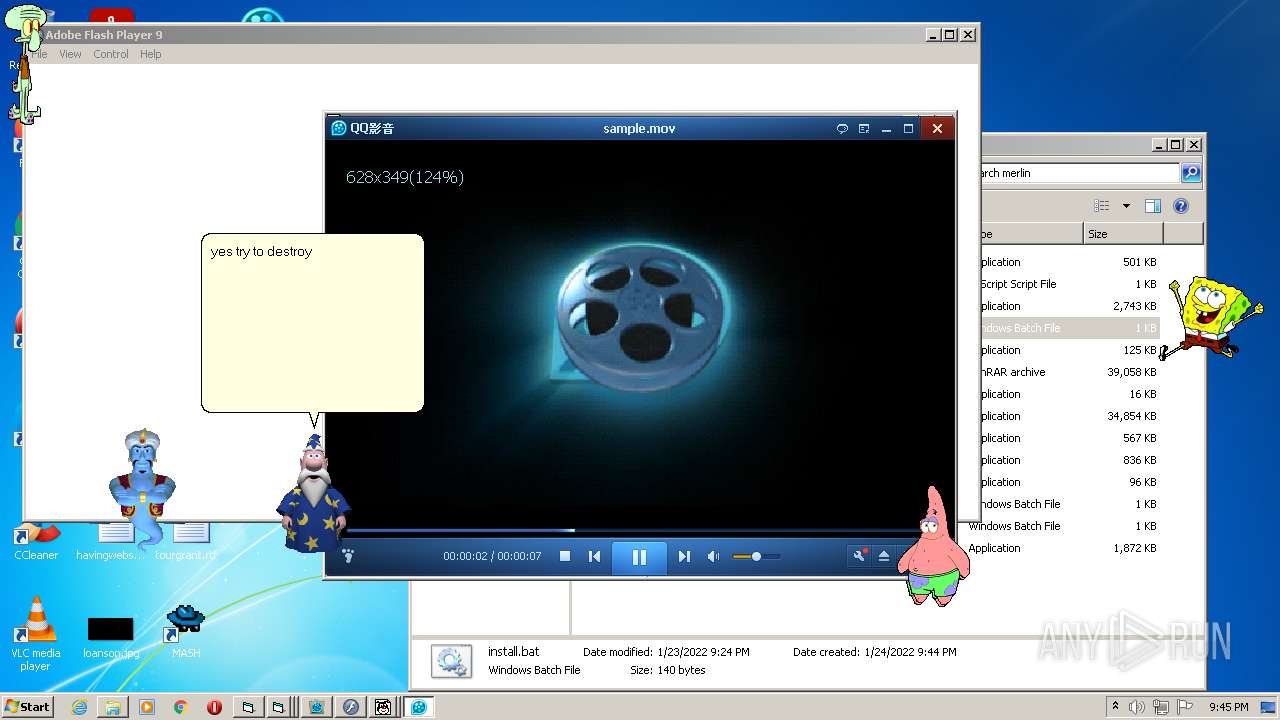
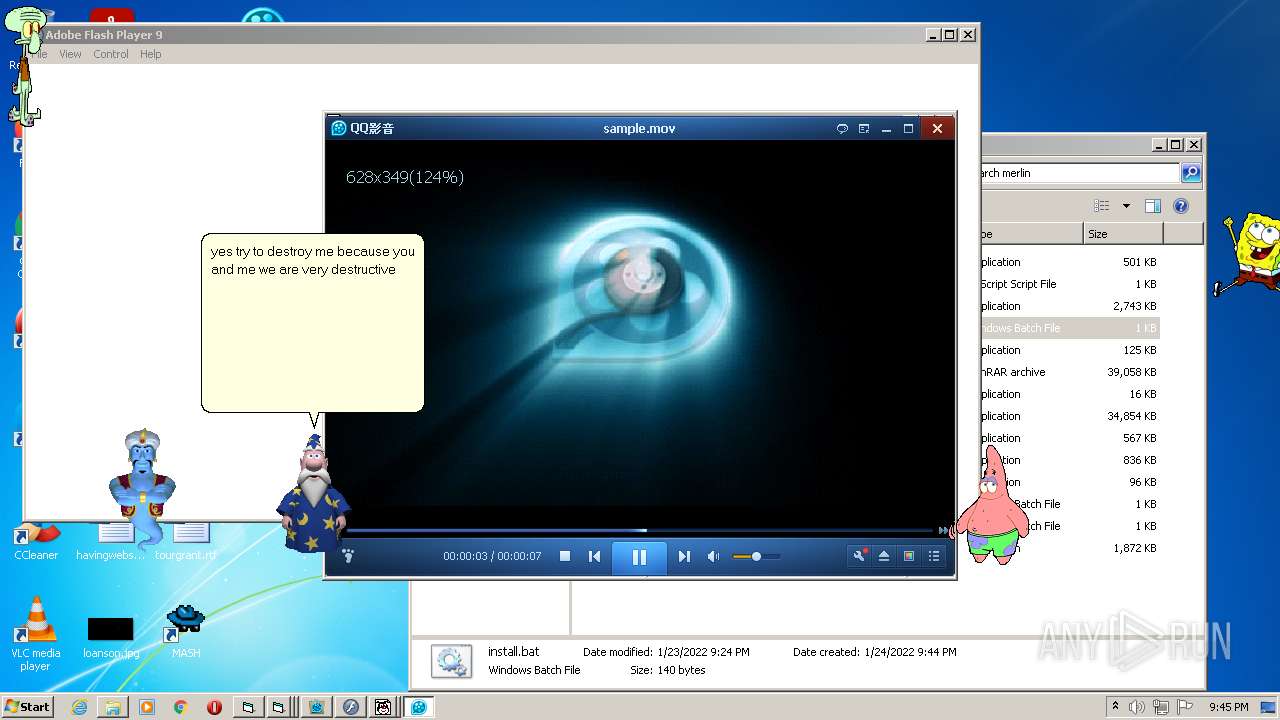
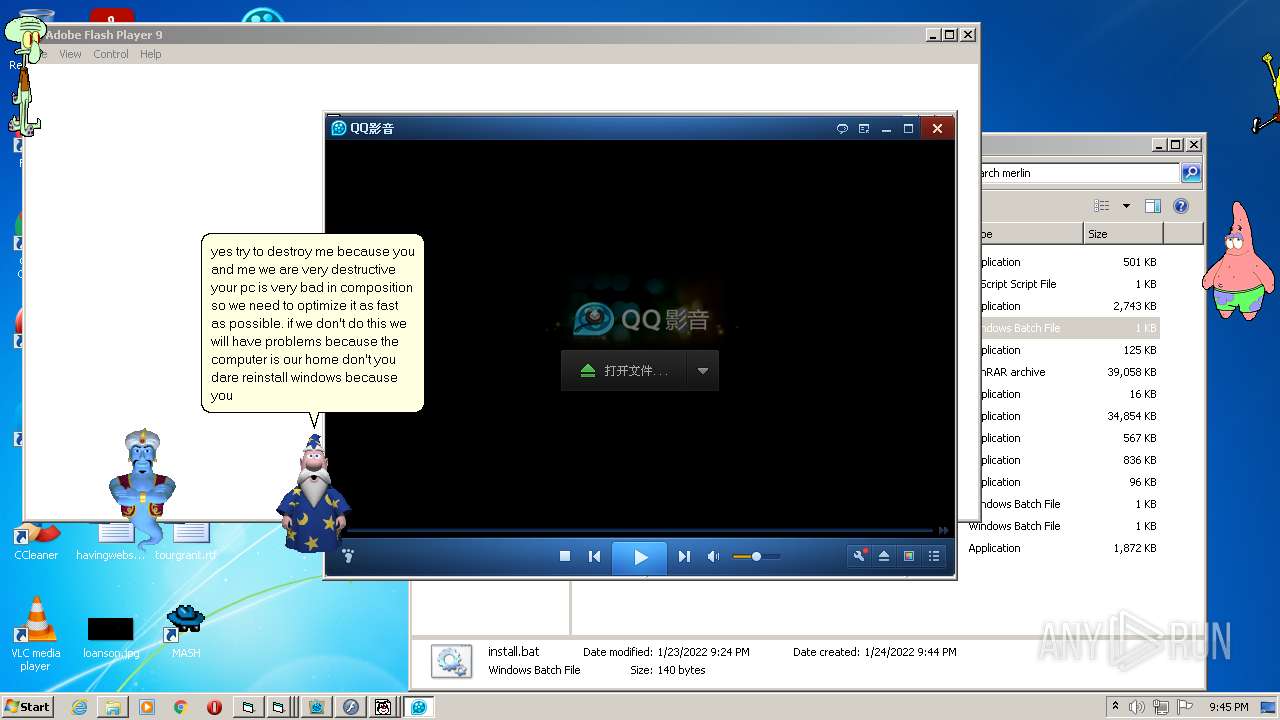
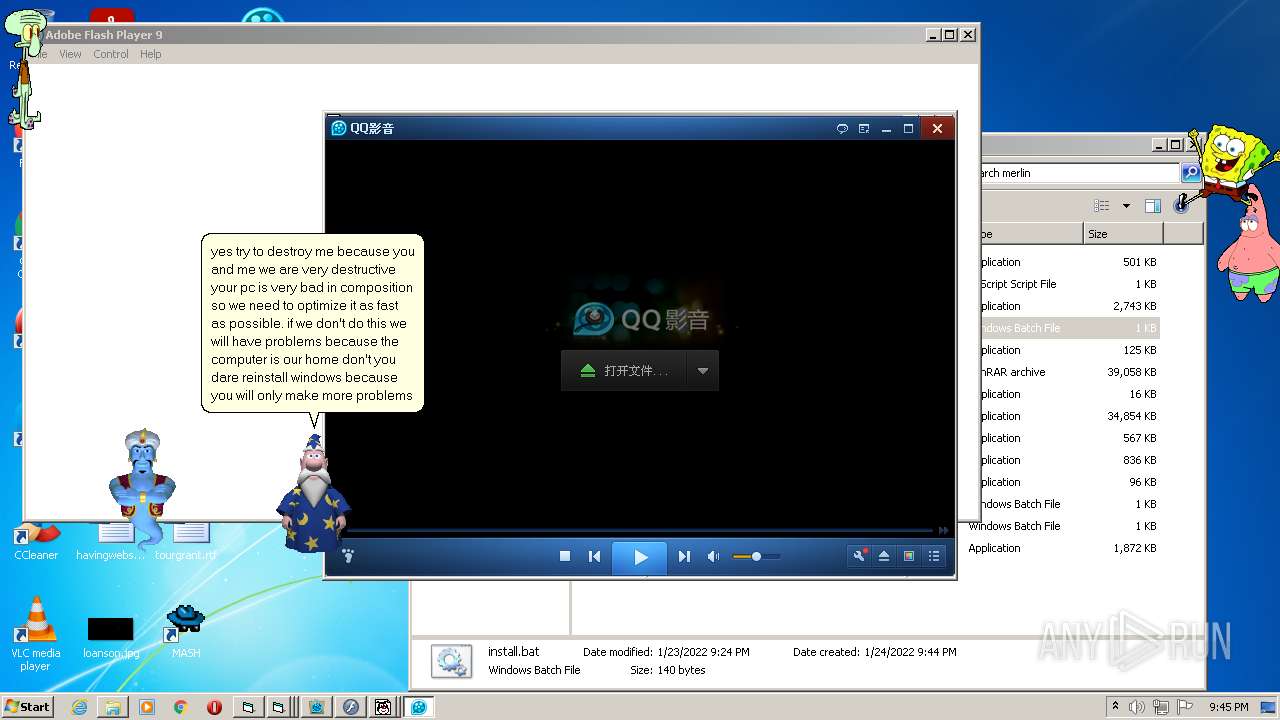
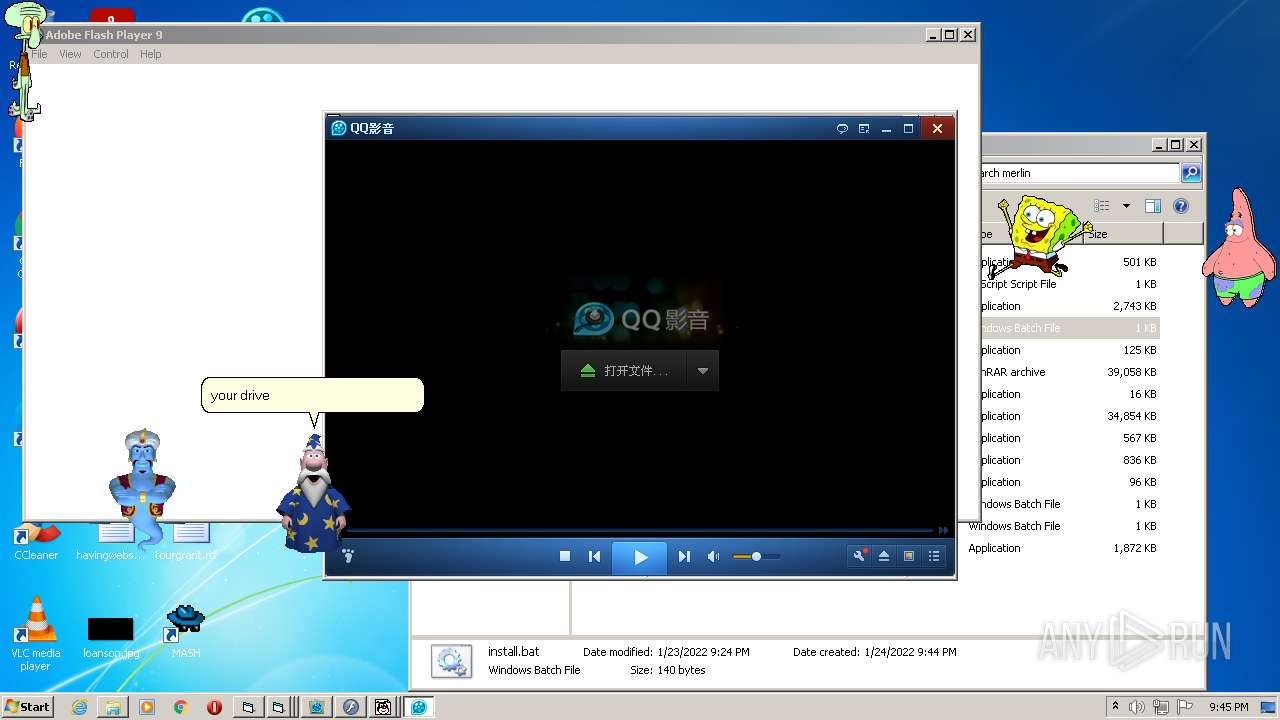
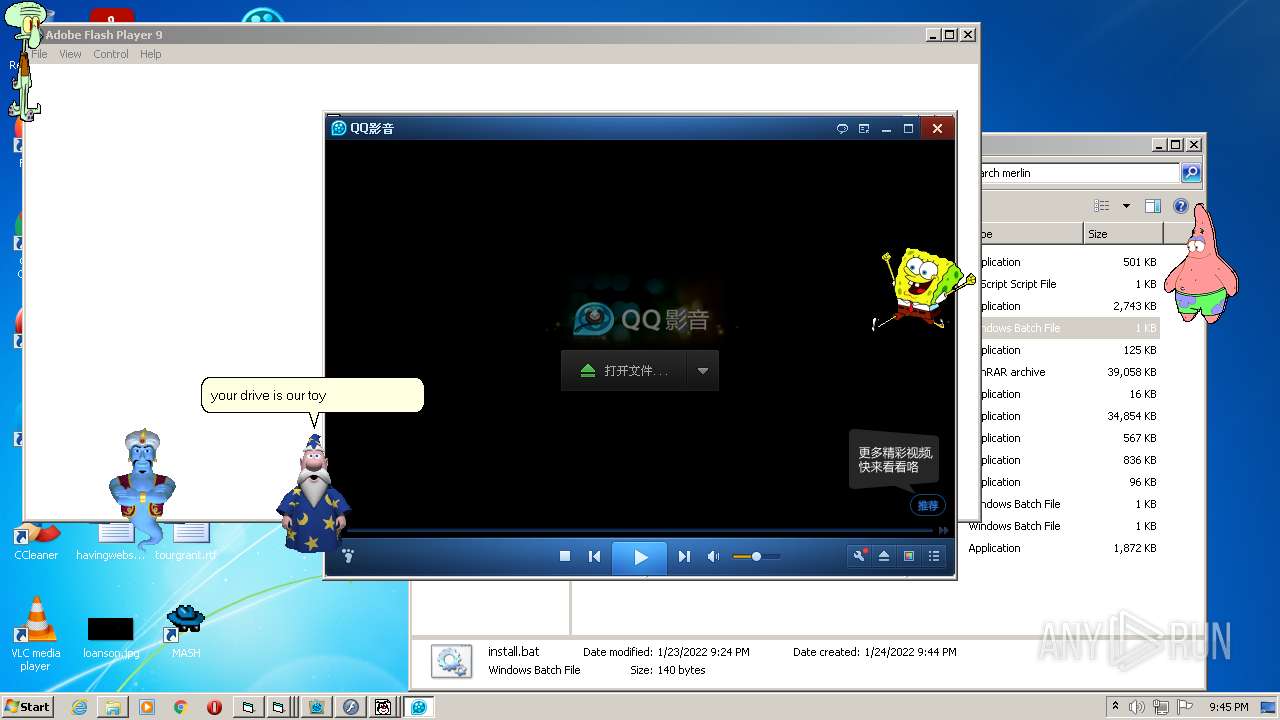
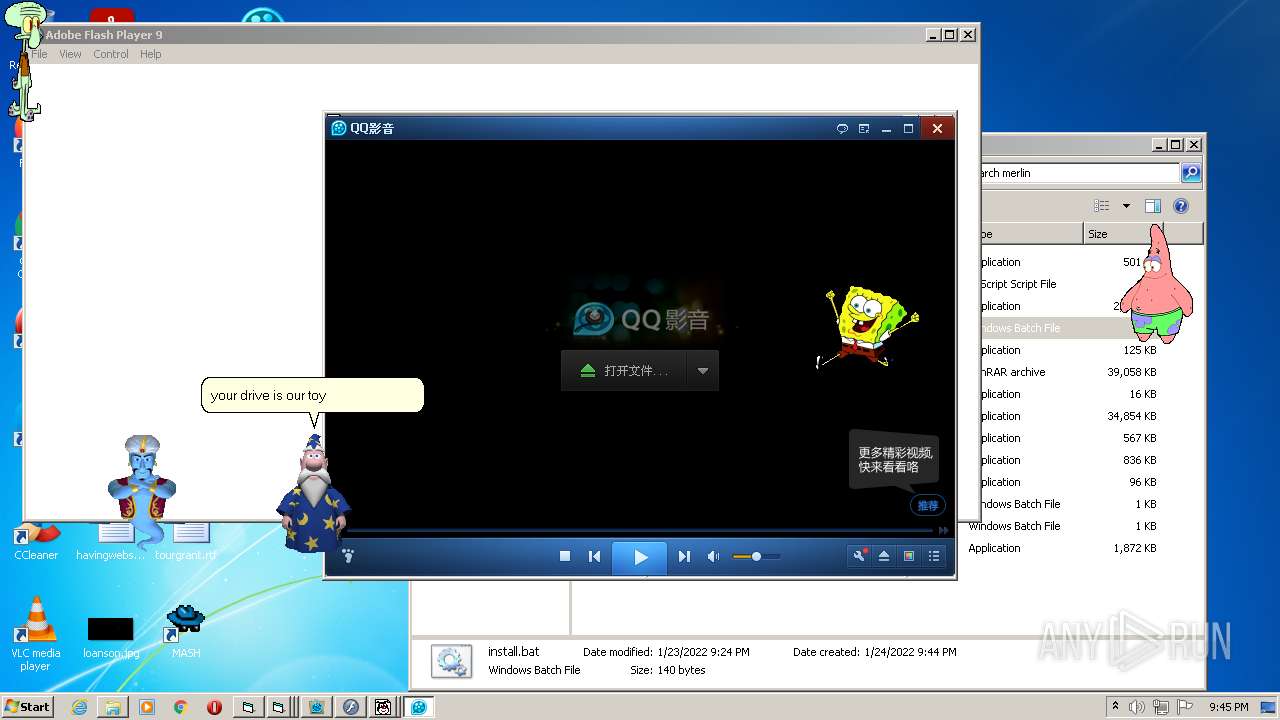
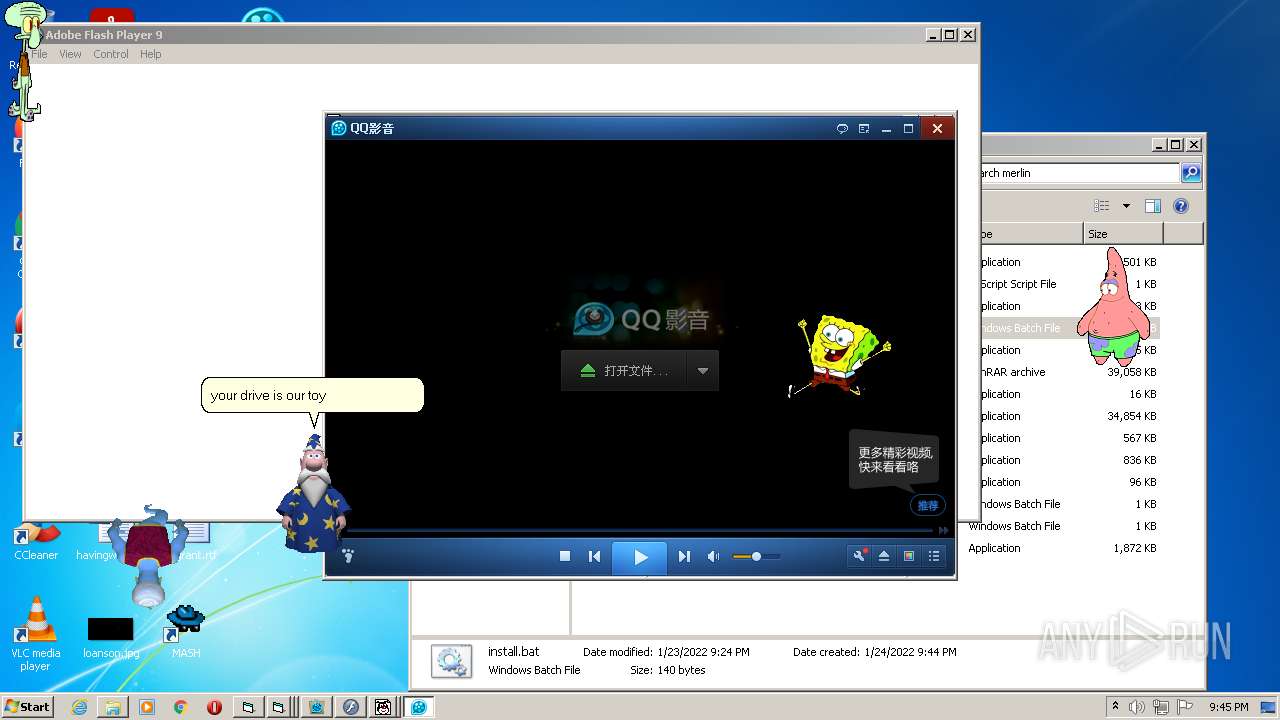
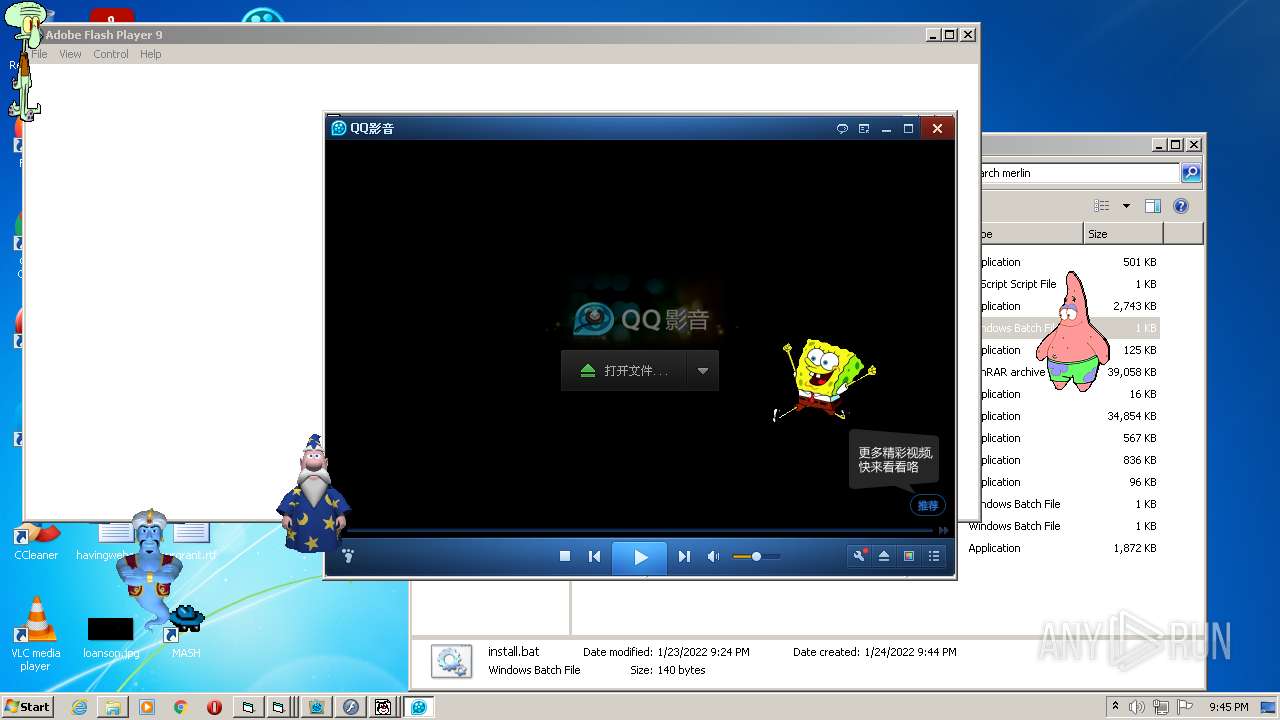
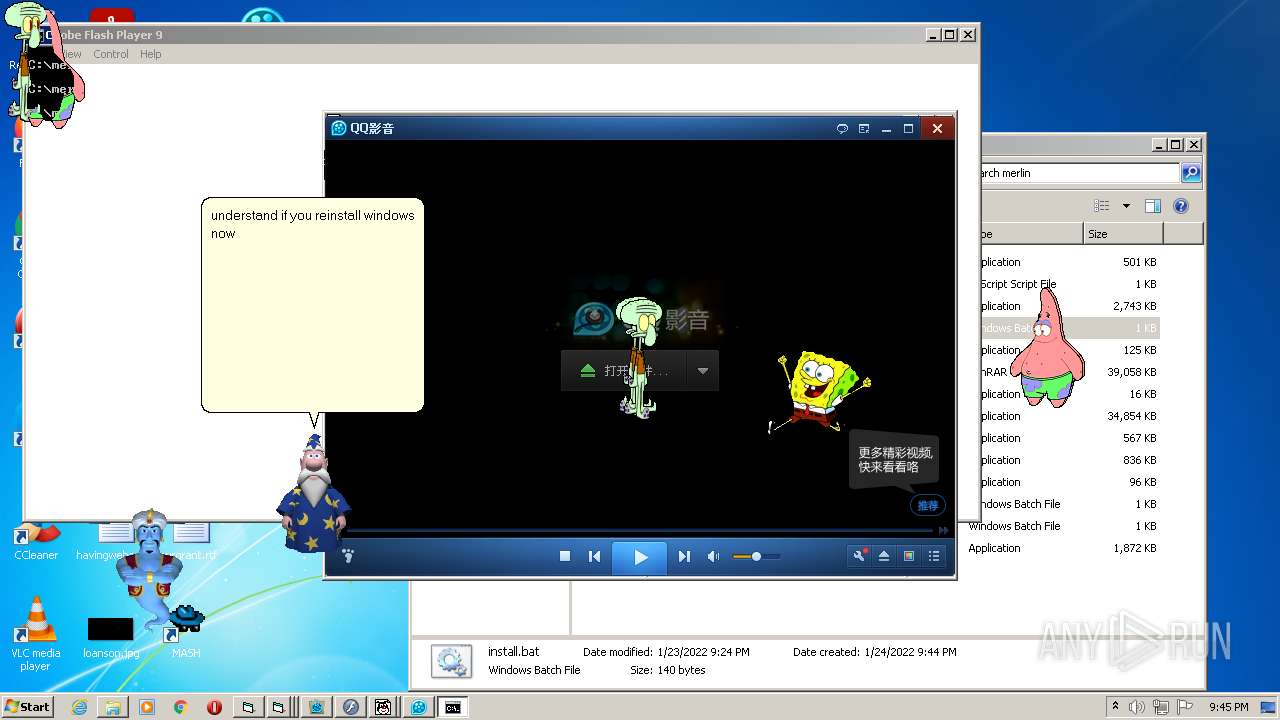
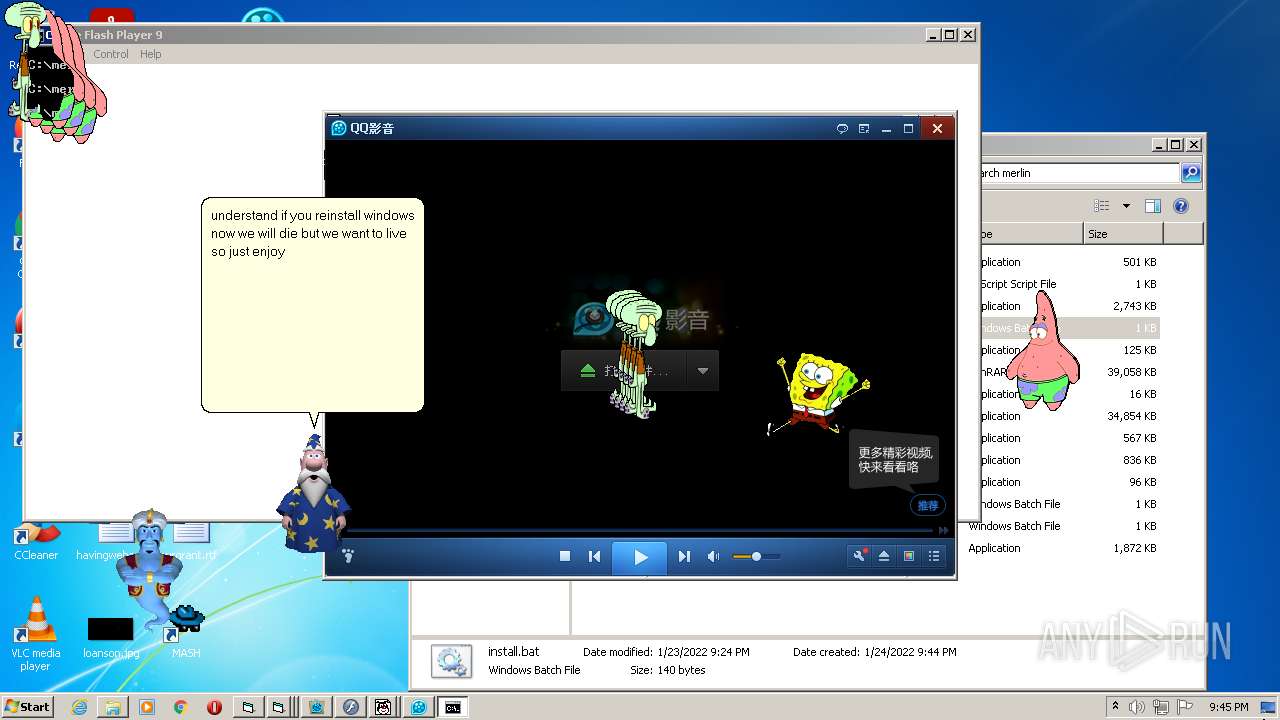
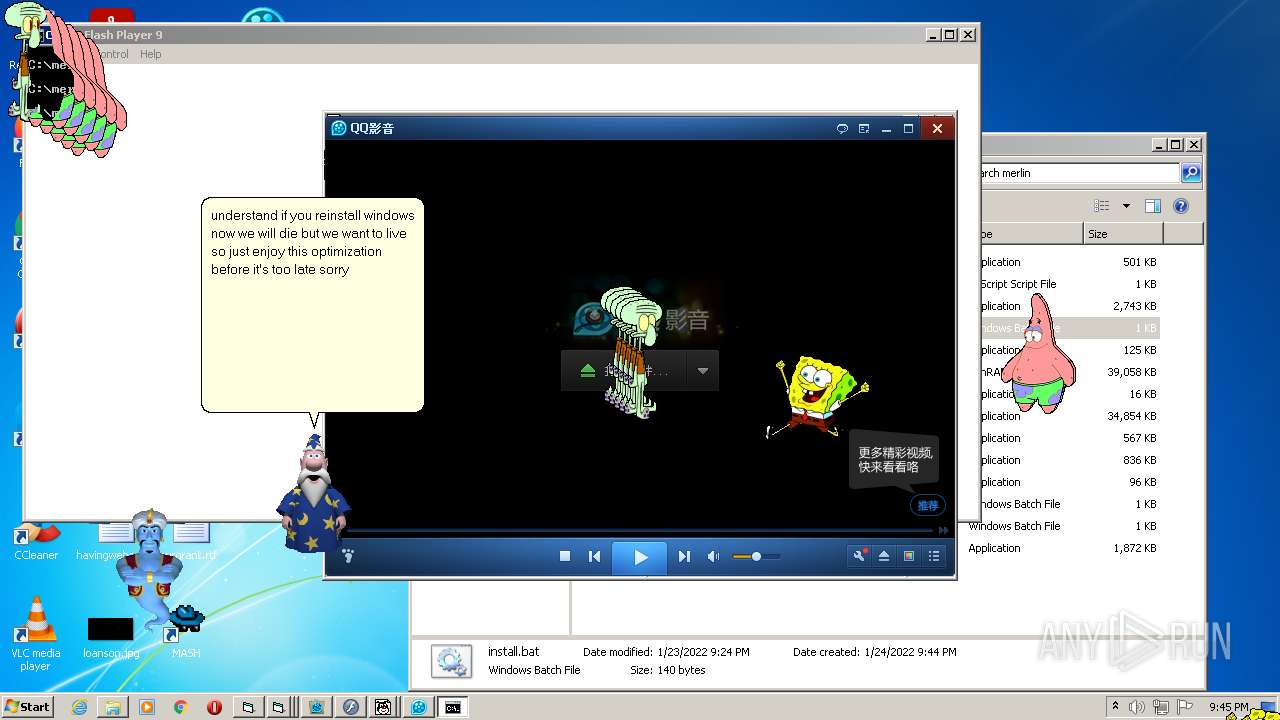
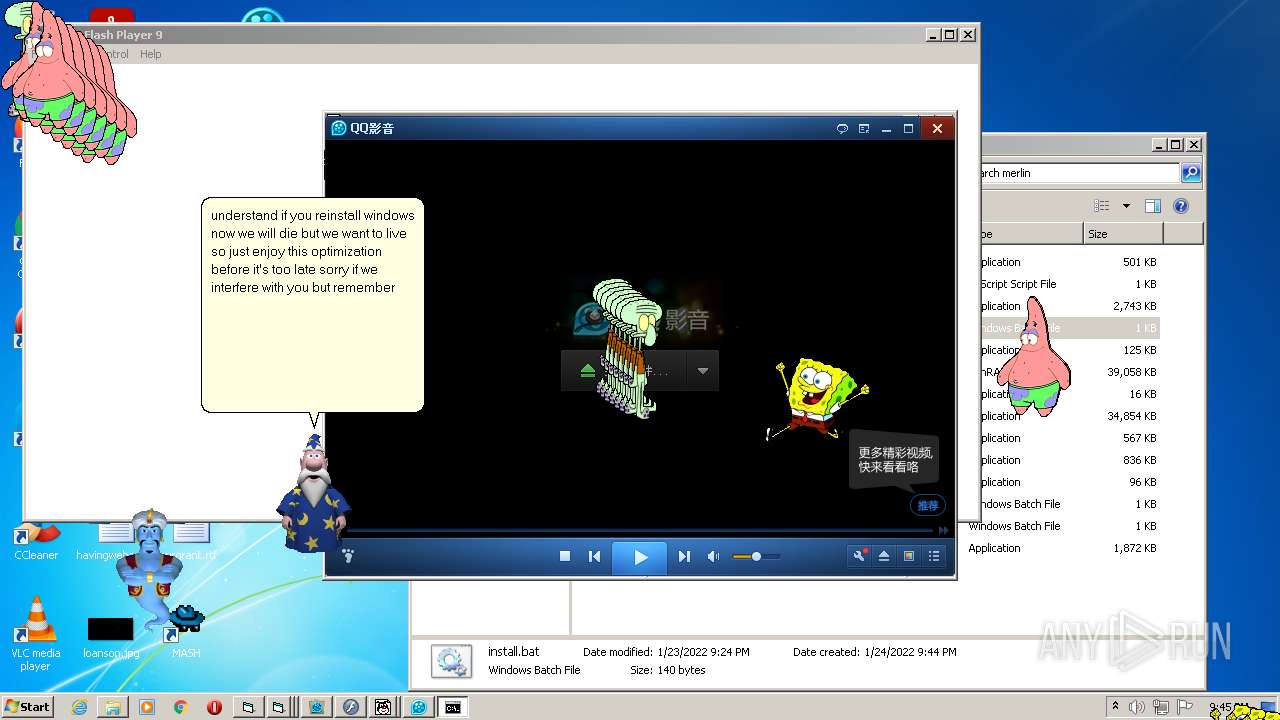
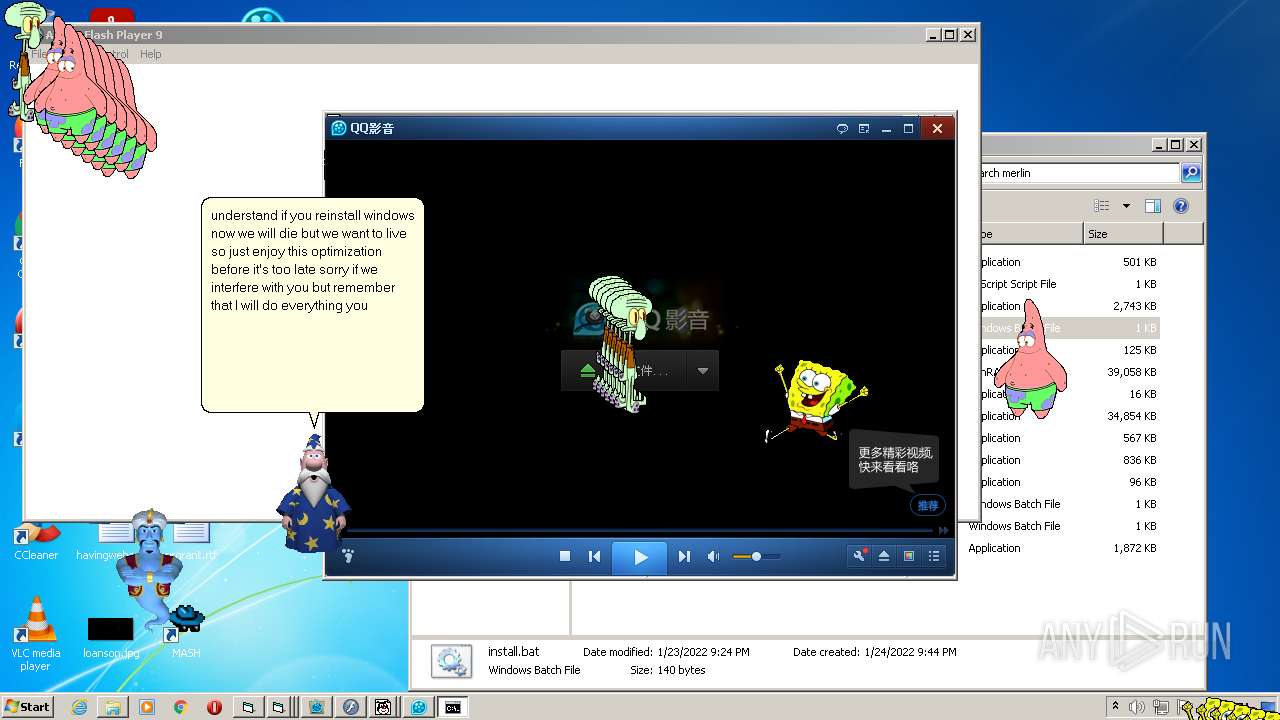
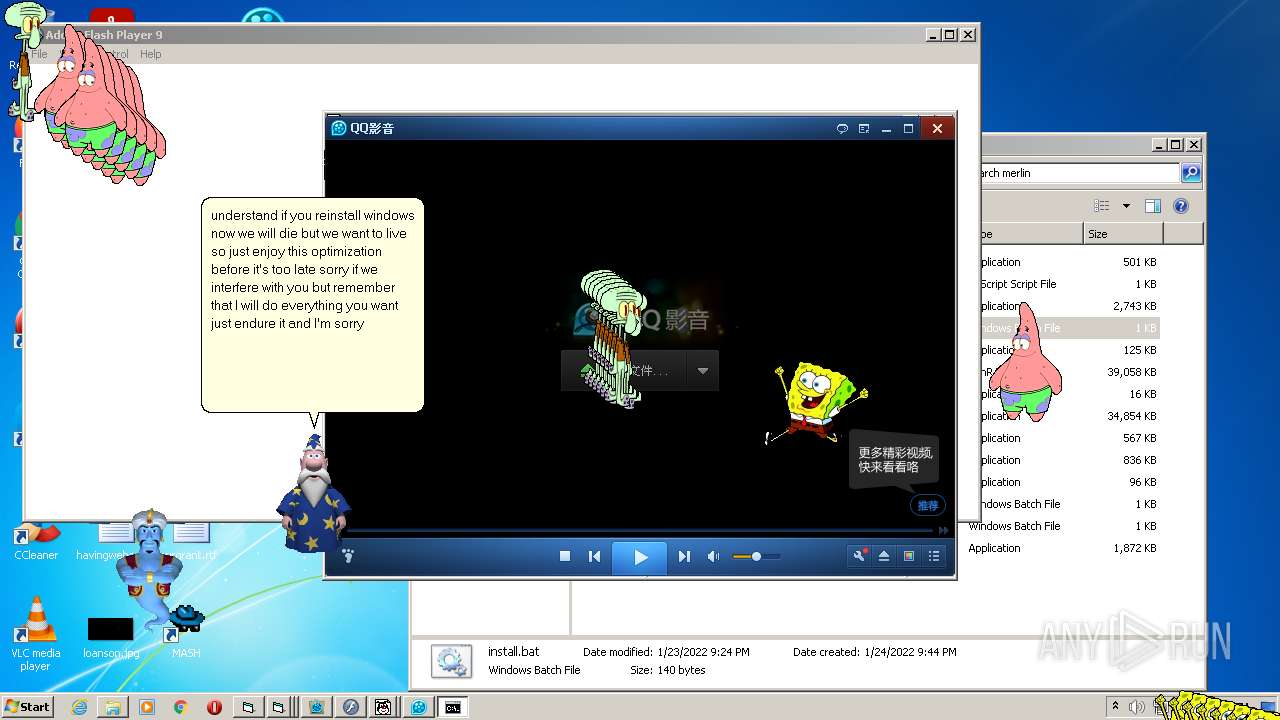
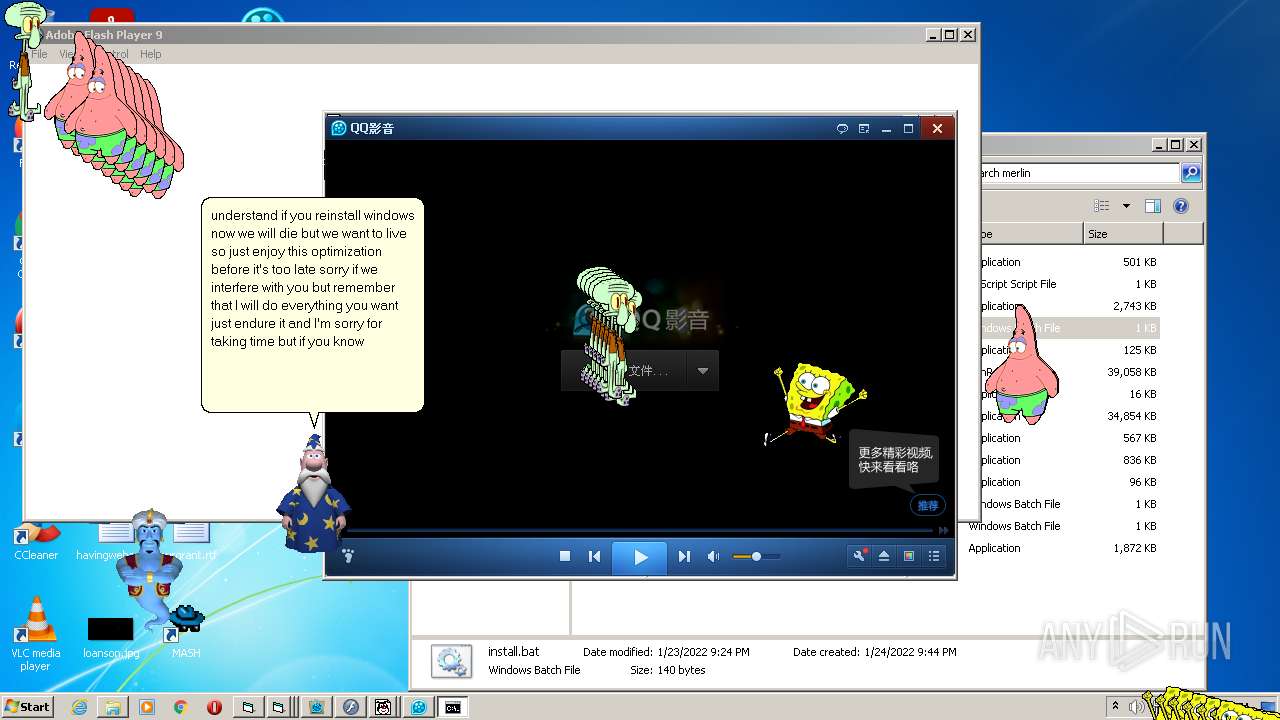
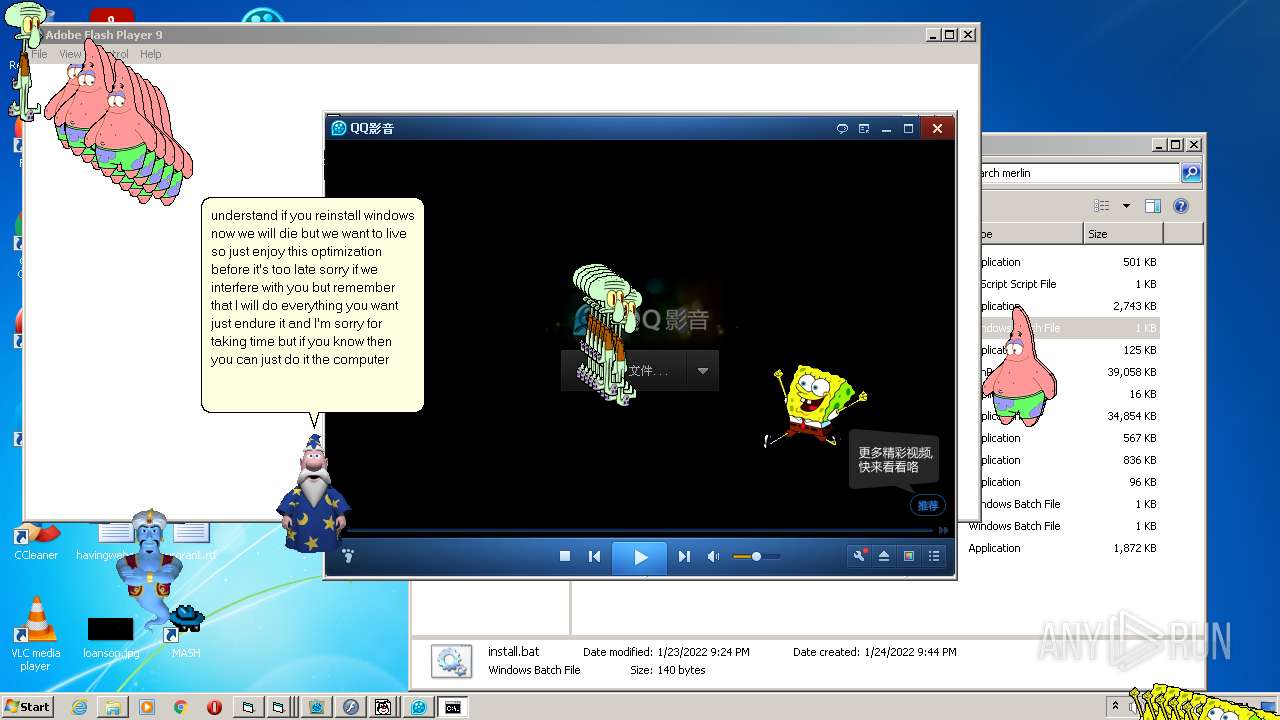
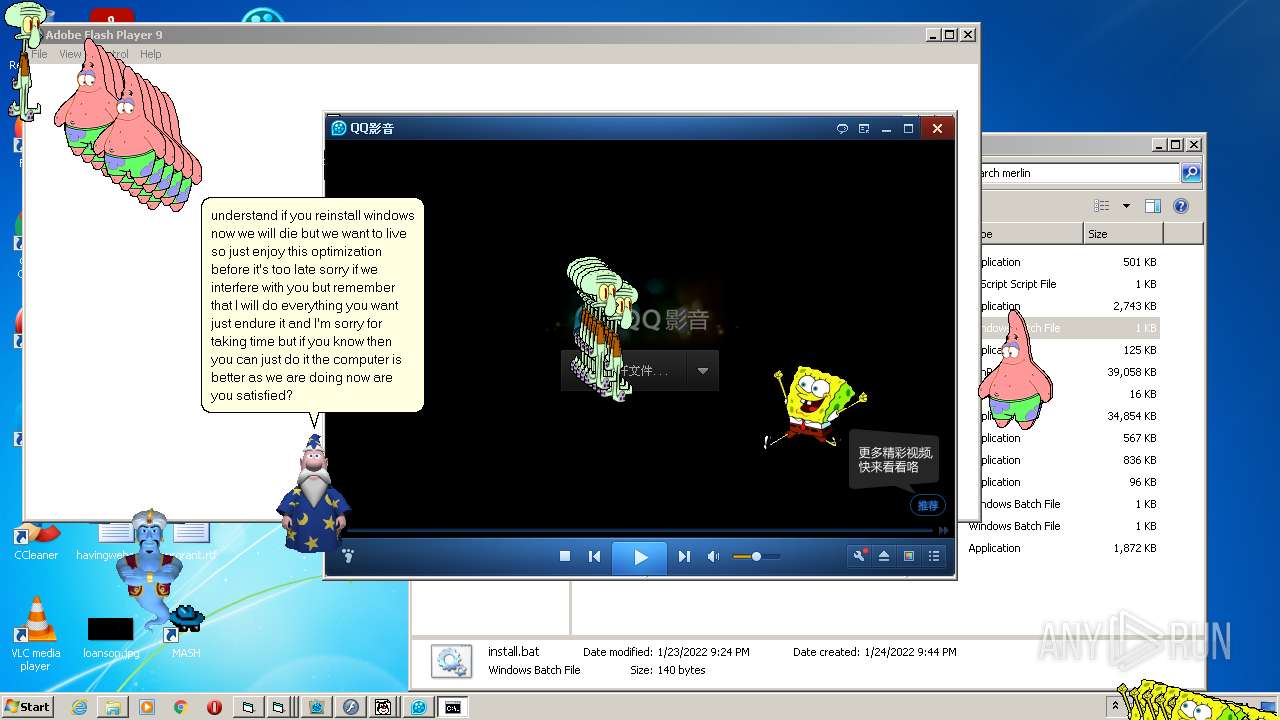
- SpongeBob_ScreenToy.exe (PID: 1292)
- Flash.exe (PID: 1560)
- Spike.exe (PID: 688)
- Spike.exe (PID: 2884)
- ace.exe (PID: 2652)
- ace.exe (PID: 2436)
- ace.exe (PID: 2792)
- ace.exe (PID: 3232)
- ace.exe (PID: 1728)
- ace.exe (PID: 3136)
- Flash.exe (PID: 2864)
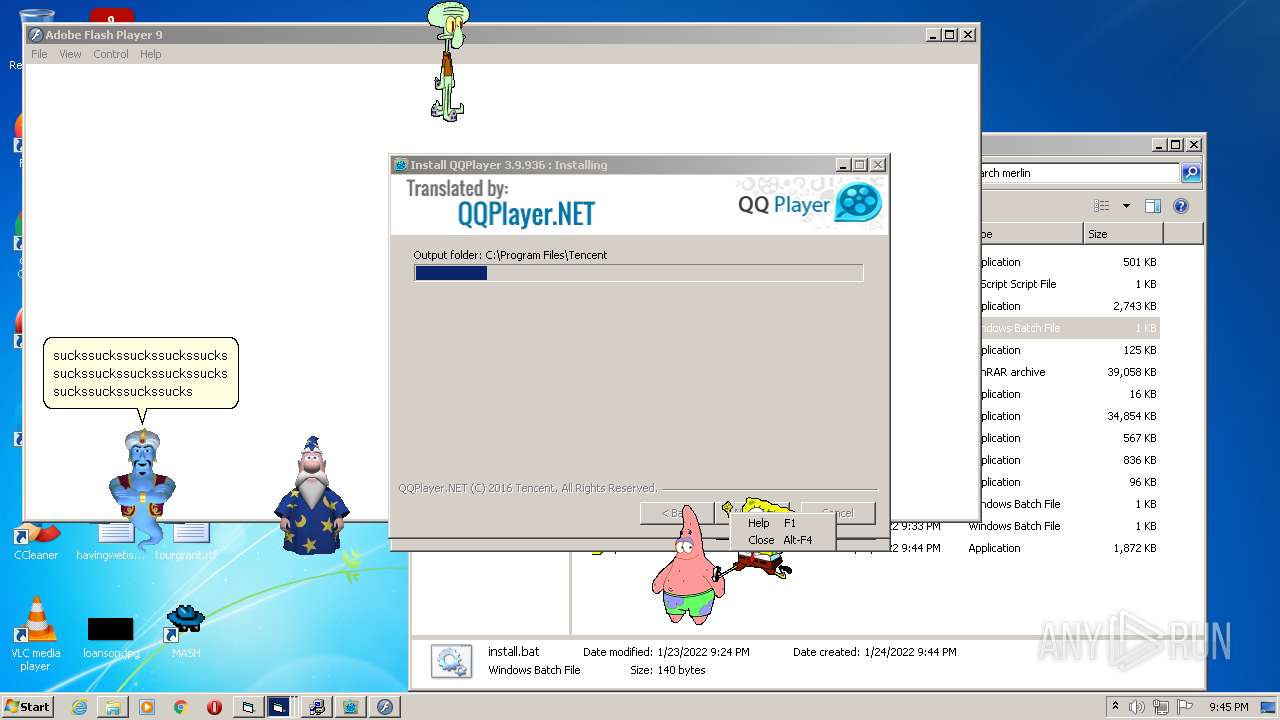
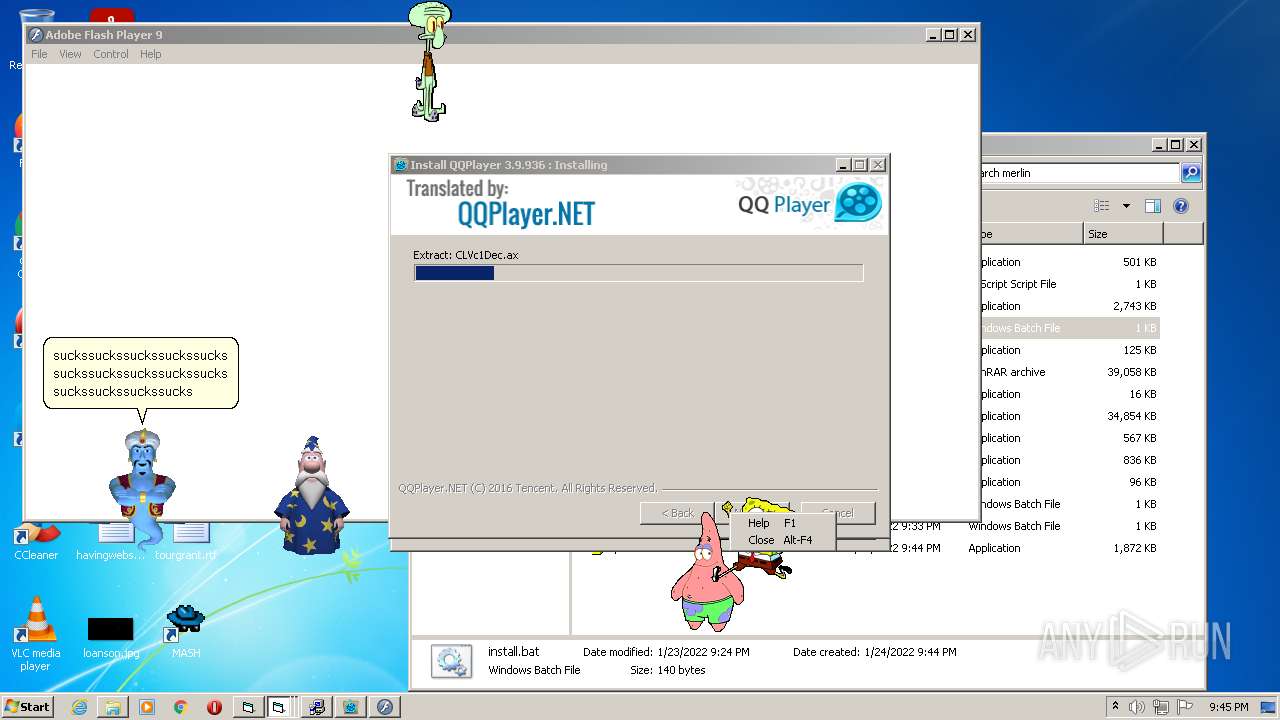
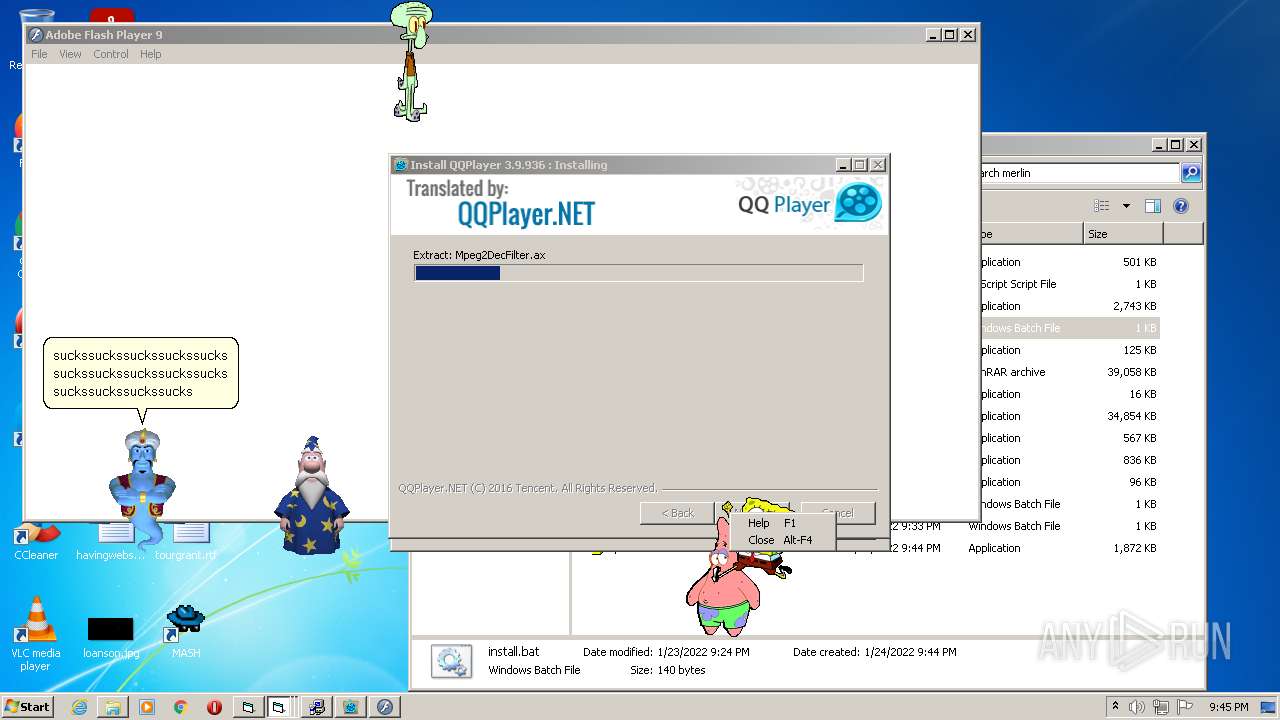
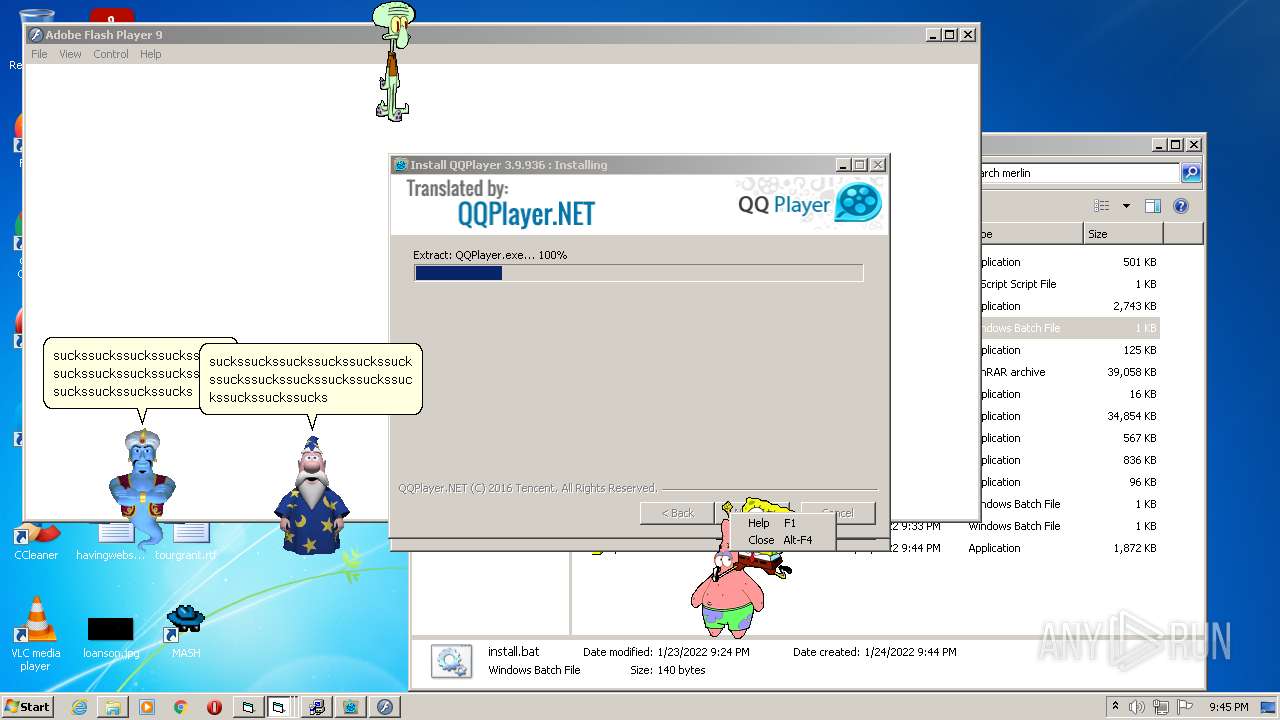
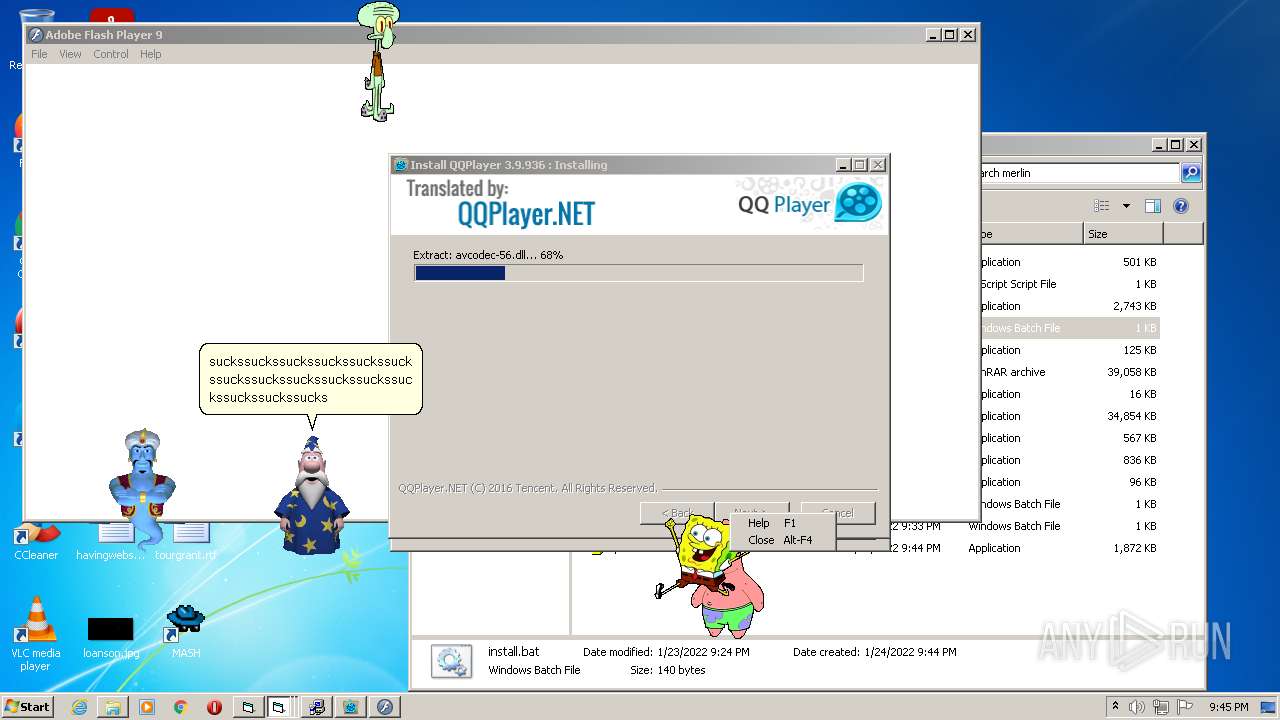
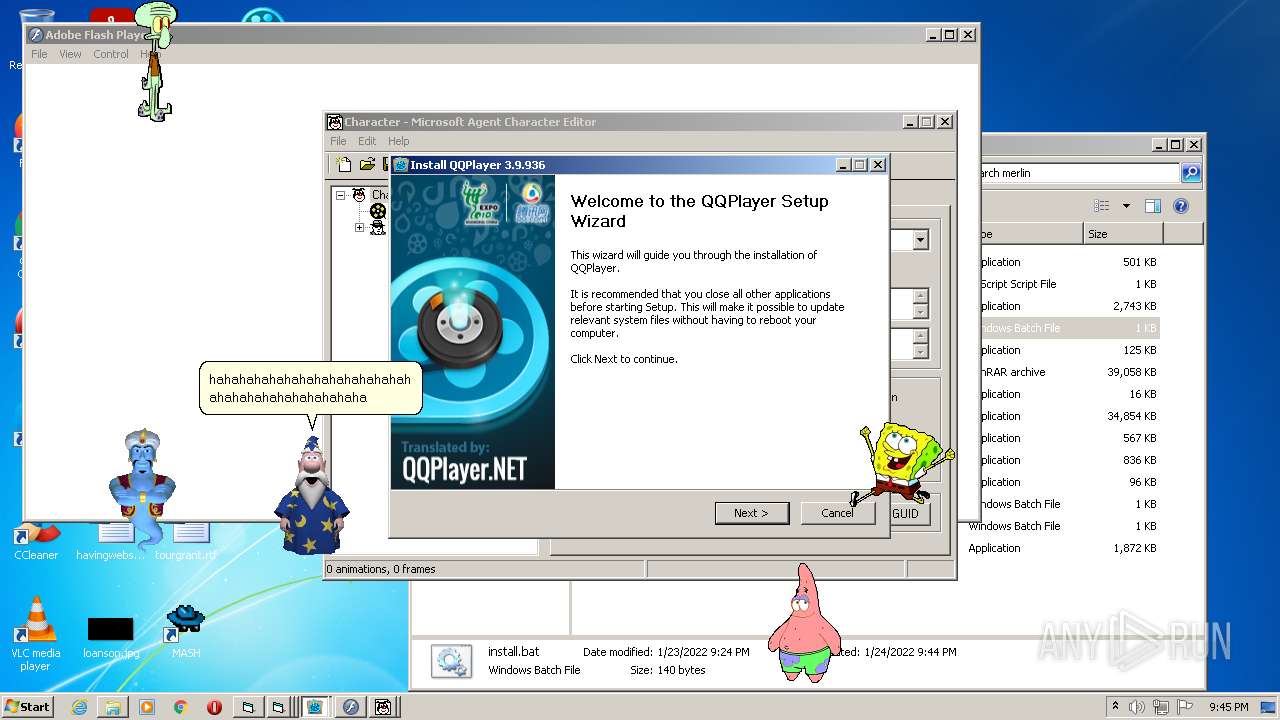
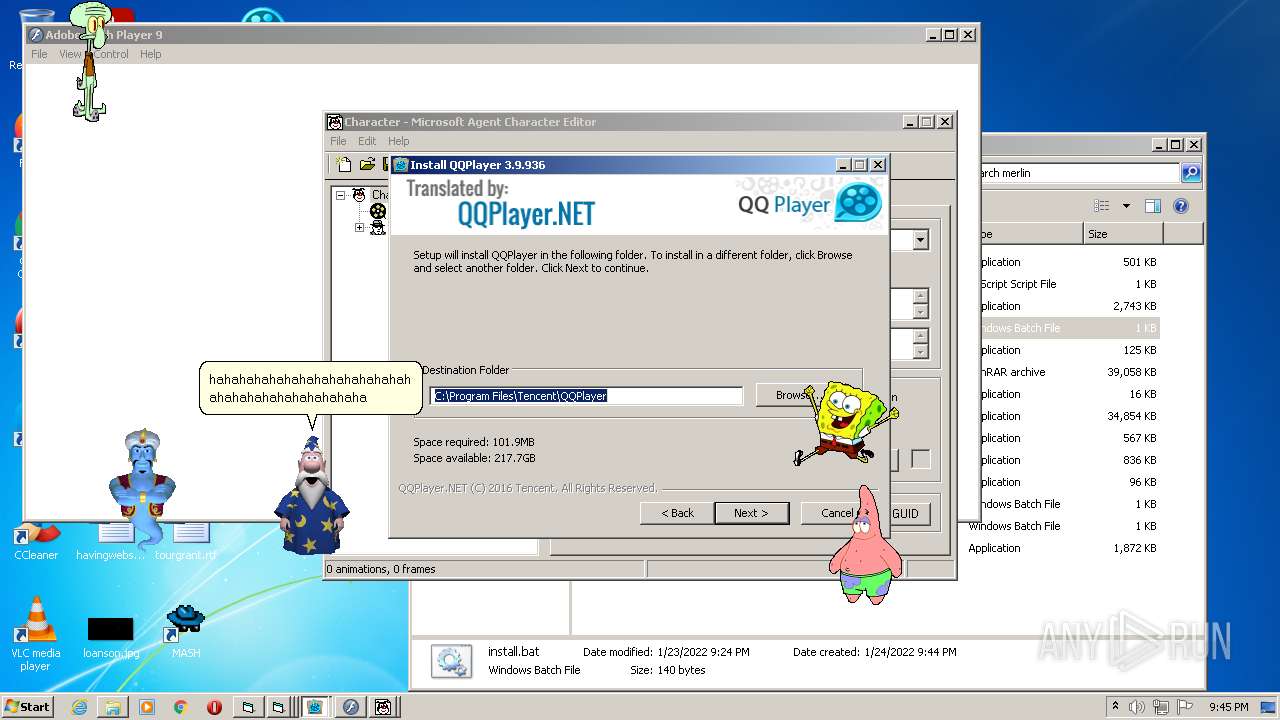
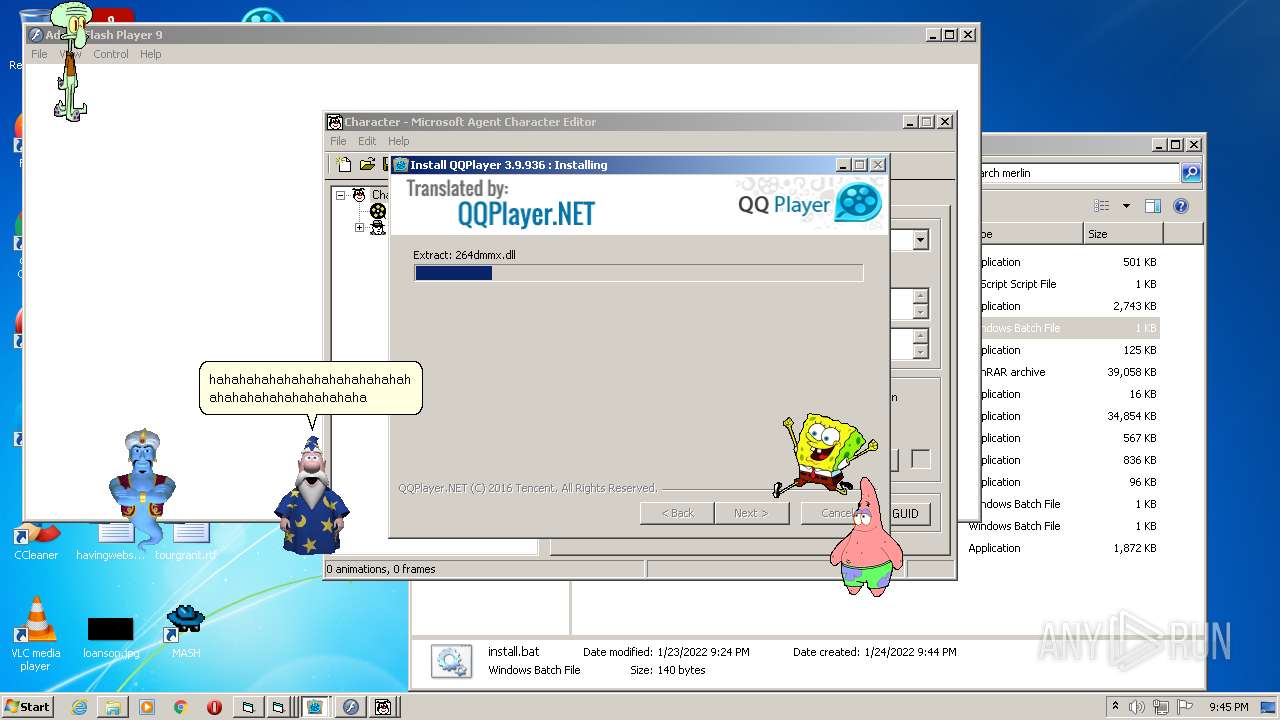
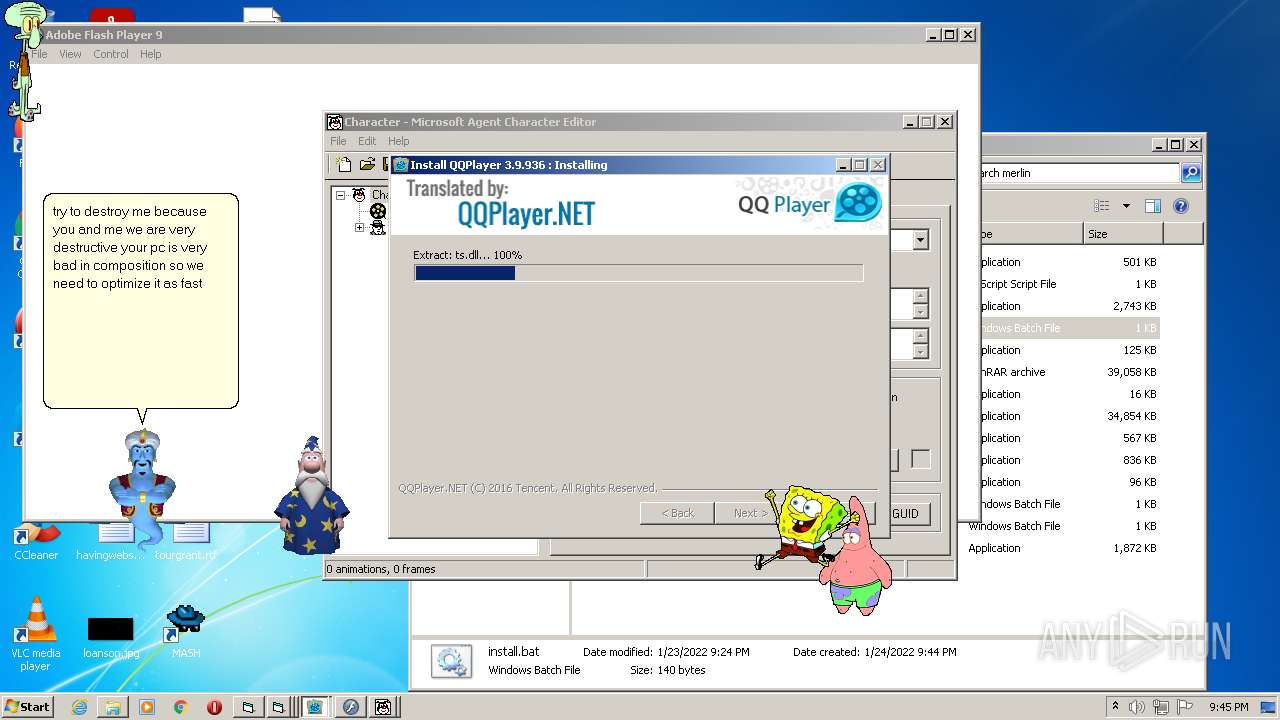
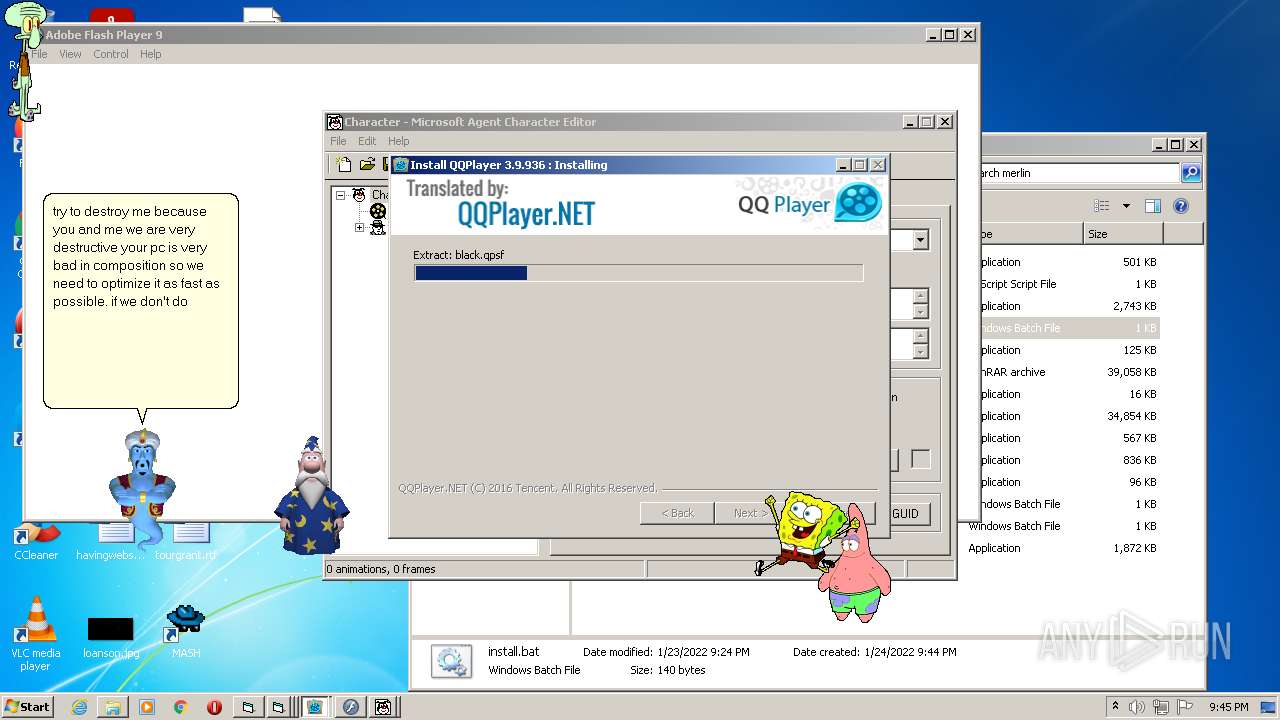
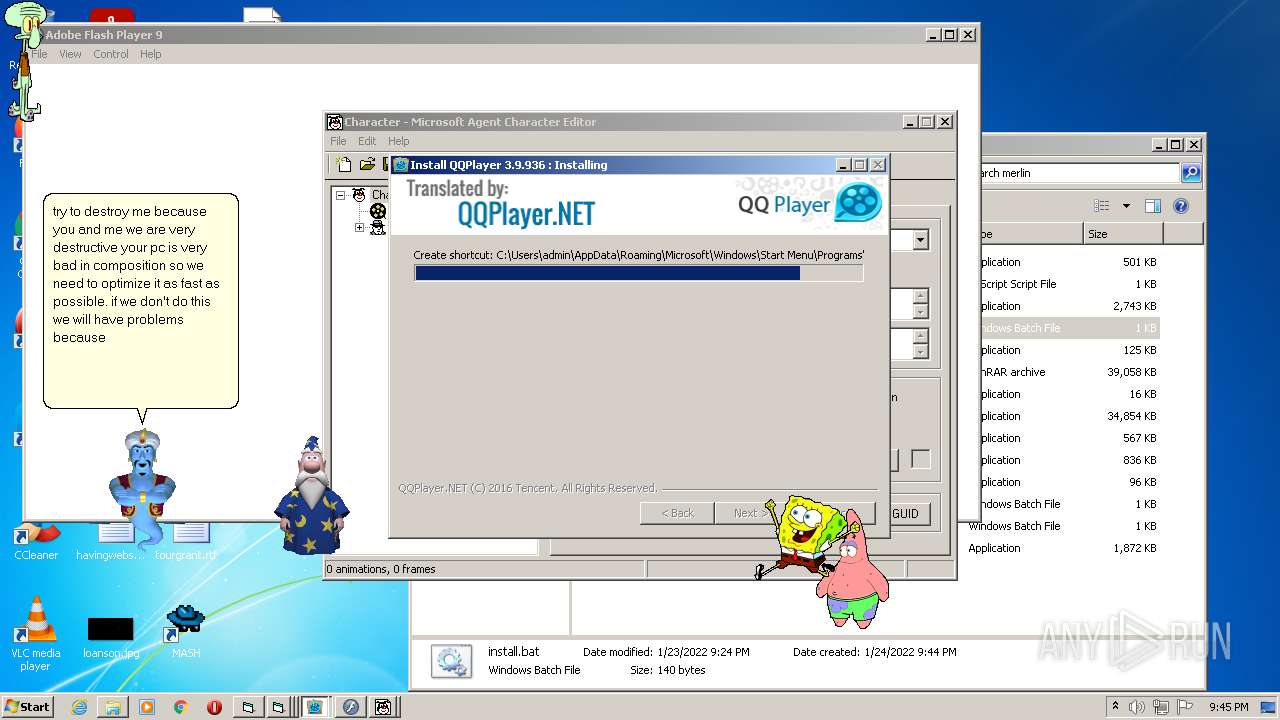
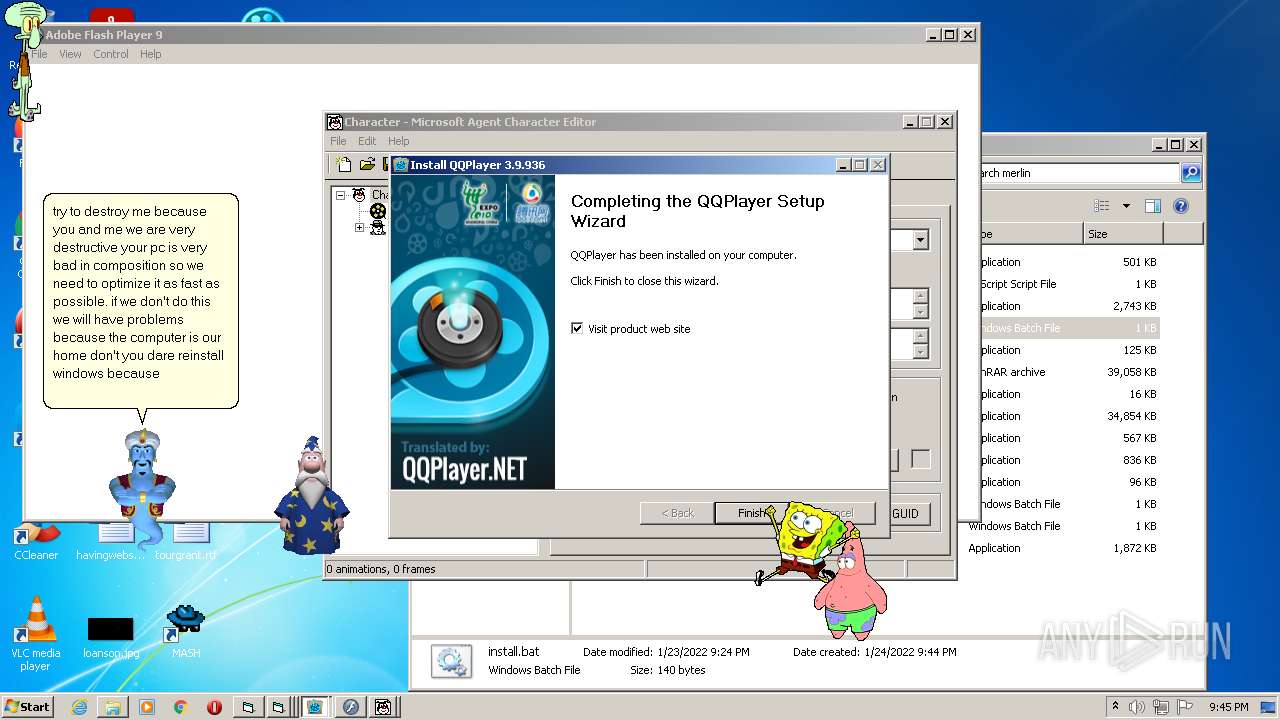
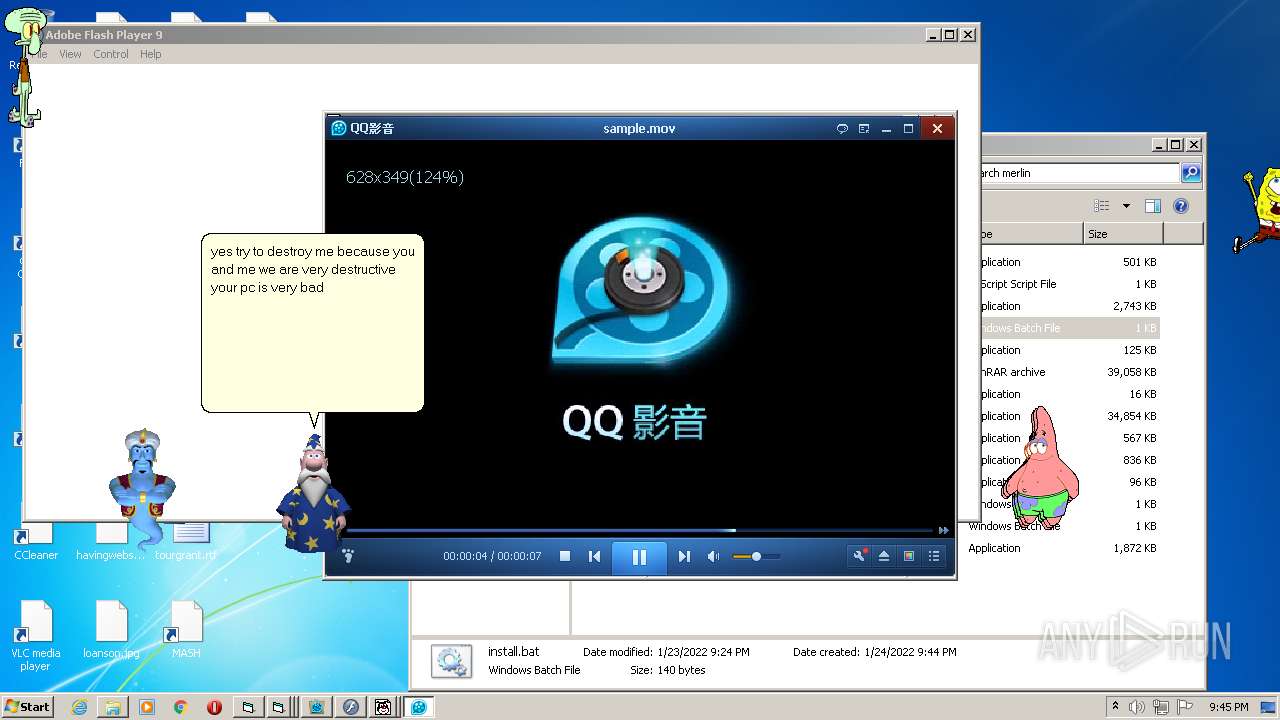
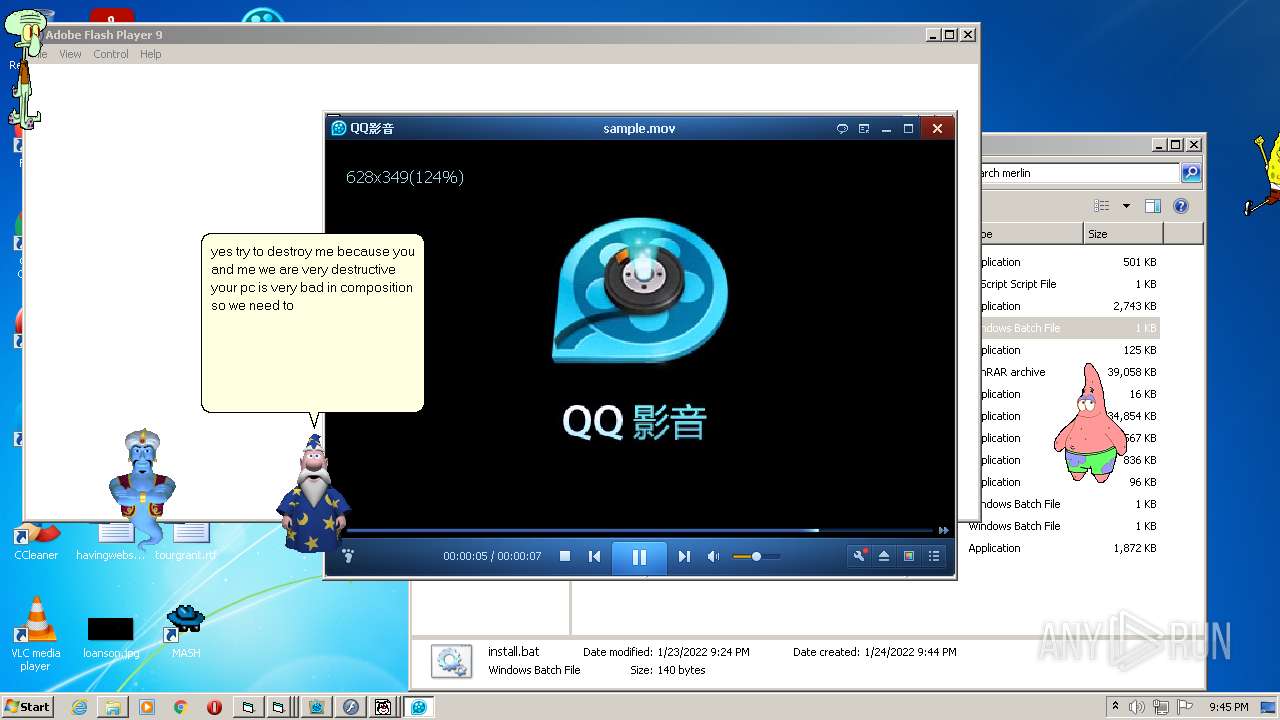
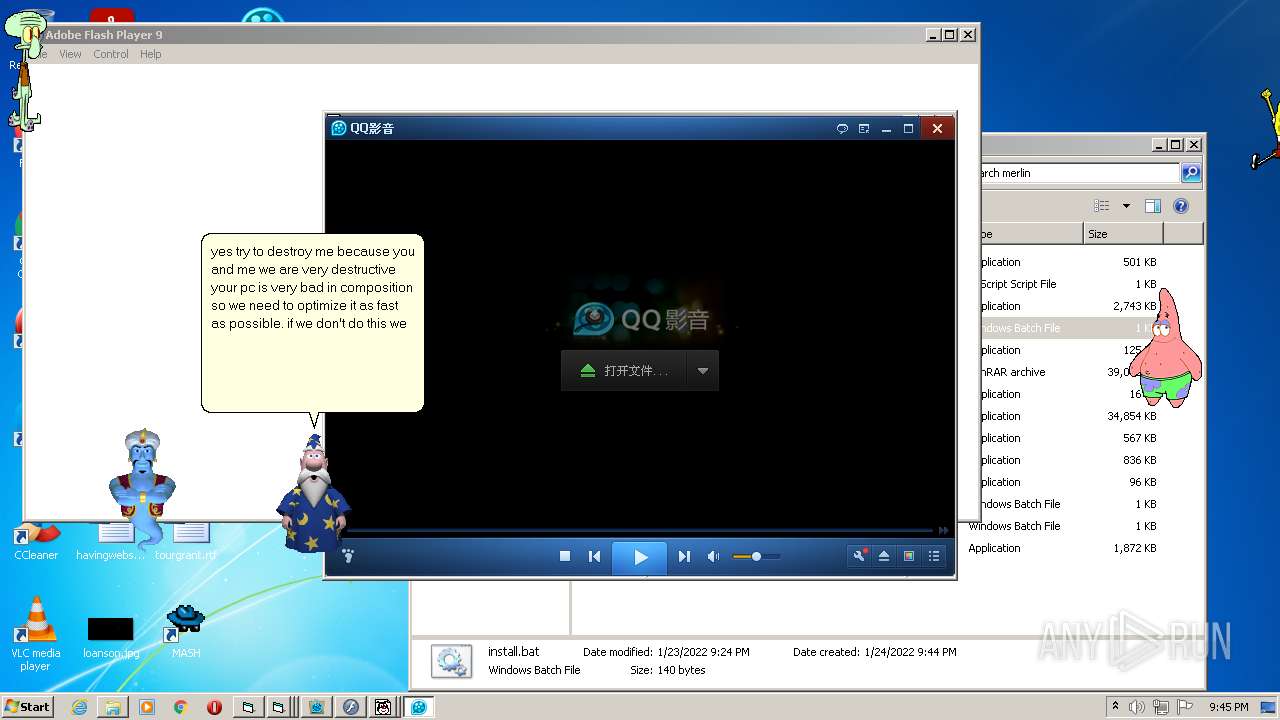
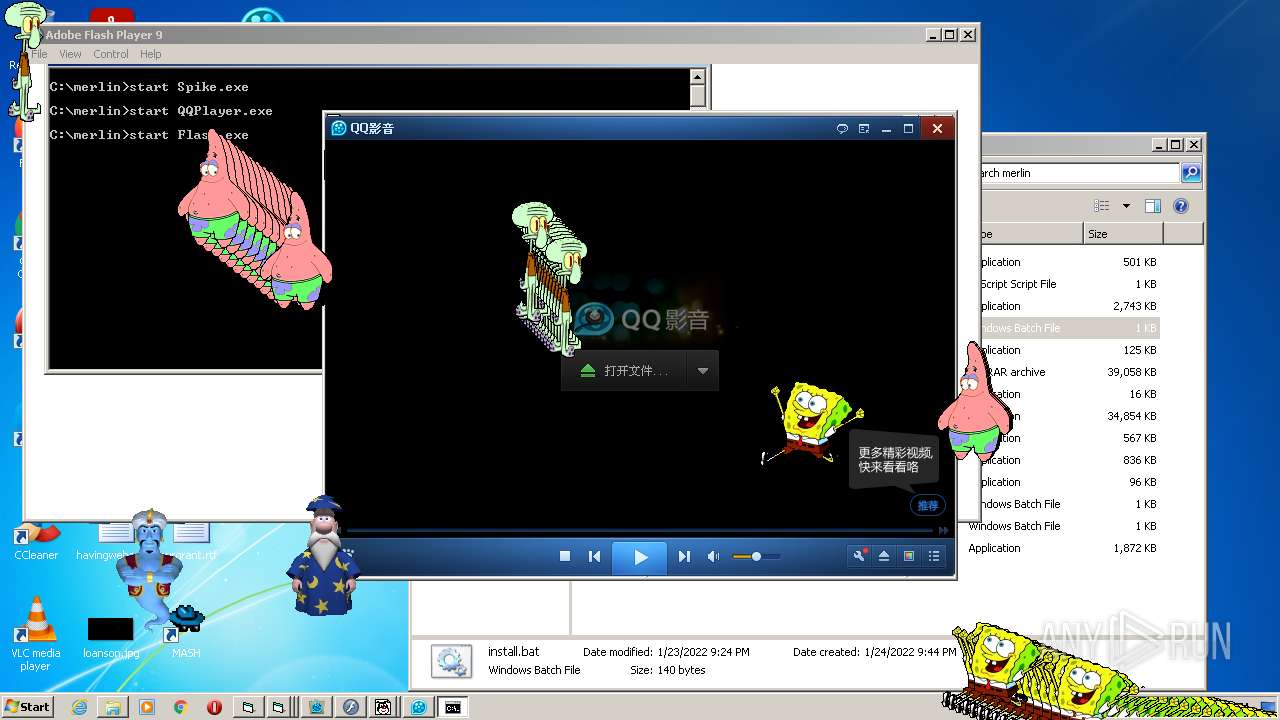
- QQPlayer.exe (PID: 2568)
- INSCD10.tmp (PID: 3696)
- QQPlayer.exe (PID: 4084)
- QQPlayer.exe (PID: 3072)
- QQPlayer.exe (PID: 2816)
- QQPlayer.exe (PID: 2568)
- QQPlayer.exe (PID: 1276)
- QQPlayer.exe (PID: 4080)
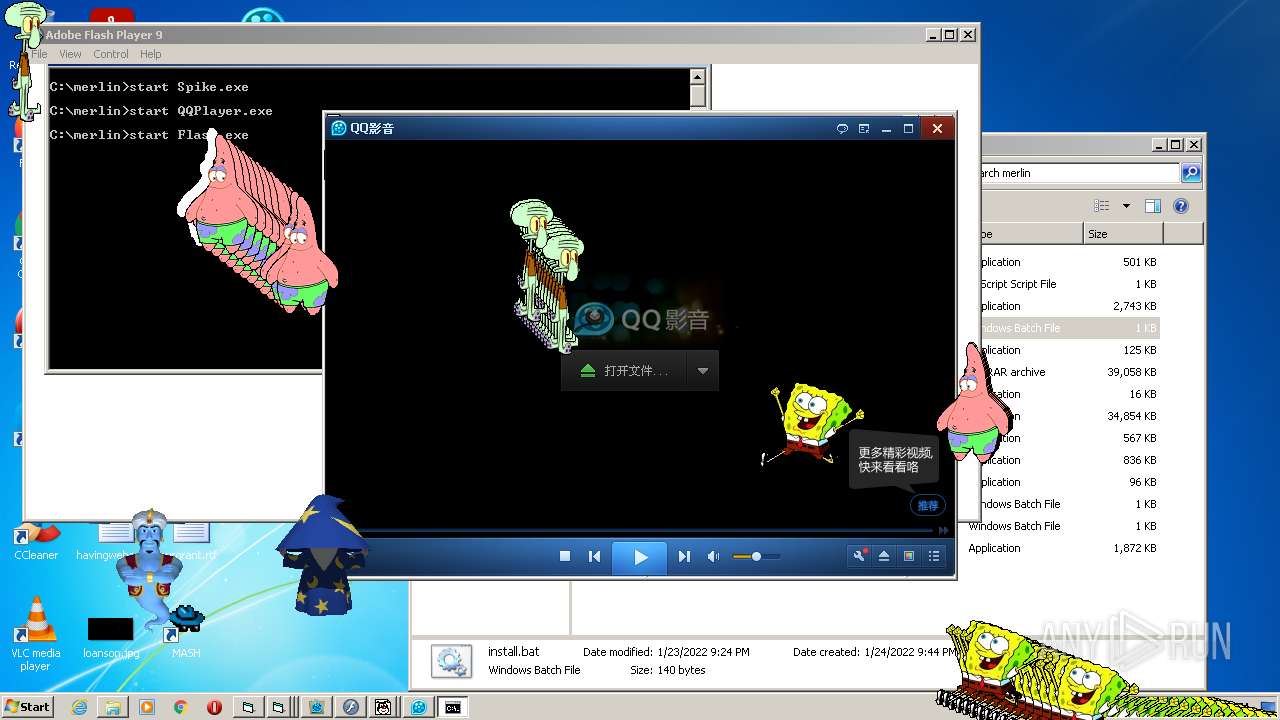
- SpongeBob_ScreenToy.exe (PID: 3140)
- SpongeBob_ScreenToy.exe (PID: 3484)
- SpongeBob_ScreenToy.exe (PID: 1092)
- SpongeBob_ScreenToy.exe (PID: 2160)
- SpongeBob_ScreenToy.exe (PID: 3376)
- SpongeBob_ScreenToy.exe (PID: 2060)
- SpongeBob_ScreenToy.exe (PID: 692)
- SpongeBob_ScreenToy.exe (PID: 3948)
- SpongeBob_ScreenToy.exe (PID: 3968)
- SpongeBob_ScreenToy.exe (PID: 3656)
- SpongeBob_ScreenToy.exe (PID: 3660)
- SpongeBob_ScreenToy.exe (PID: 2348)
- SpongeBob_ScreenToy.exe (PID: 2384)
- SpongeBob_ScreenToy.exe (PID: 3788)
- SpongeBob_ScreenToy.exe (PID: 2128)
- SpongeBob_ScreenToy.exe (PID: 2208)
- SpongeBob_ScreenToy.exe (PID: 116)
- SpongeBob_ScreenToy.exe (PID: 3240)
- SpongeBob_ScreenToy.exe (PID: 1832)
- SpongeBob_ScreenToy.exe (PID: 2692)
- SpongeBob_ScreenToy.exe (PID: 2284)
- SpongeBob_ScreenToy.exe (PID: 2396)
- SpongeBob_ScreenToy.exe (PID: 2572)
- SpongeBob_ScreenToy.exe (PID: 3572)
- SpongeBob_ScreenToy.exe (PID: 2924)
- SpongeBob_ScreenToy.exe (PID: 1780)
- SpongeBob_ScreenToy.exe (PID: 2332)
- SpongeBob_ScreenToy.exe (PID: 3868)
- QQPlayer.exe (PID: 3808)
- Spike.exe (PID: 1528)
- QQPlayer.exe (PID: 2216)
- Spike.exe (PID: 2712)
- Spike.exe (PID: 3392)
- QQPlayer.exe (PID: 3092)
- Flash.exe (PID: 484)
- INSA9DF.tmp (PID: 3296)
- Flash.exe (PID: 480)
Drops executable file immediately after starts
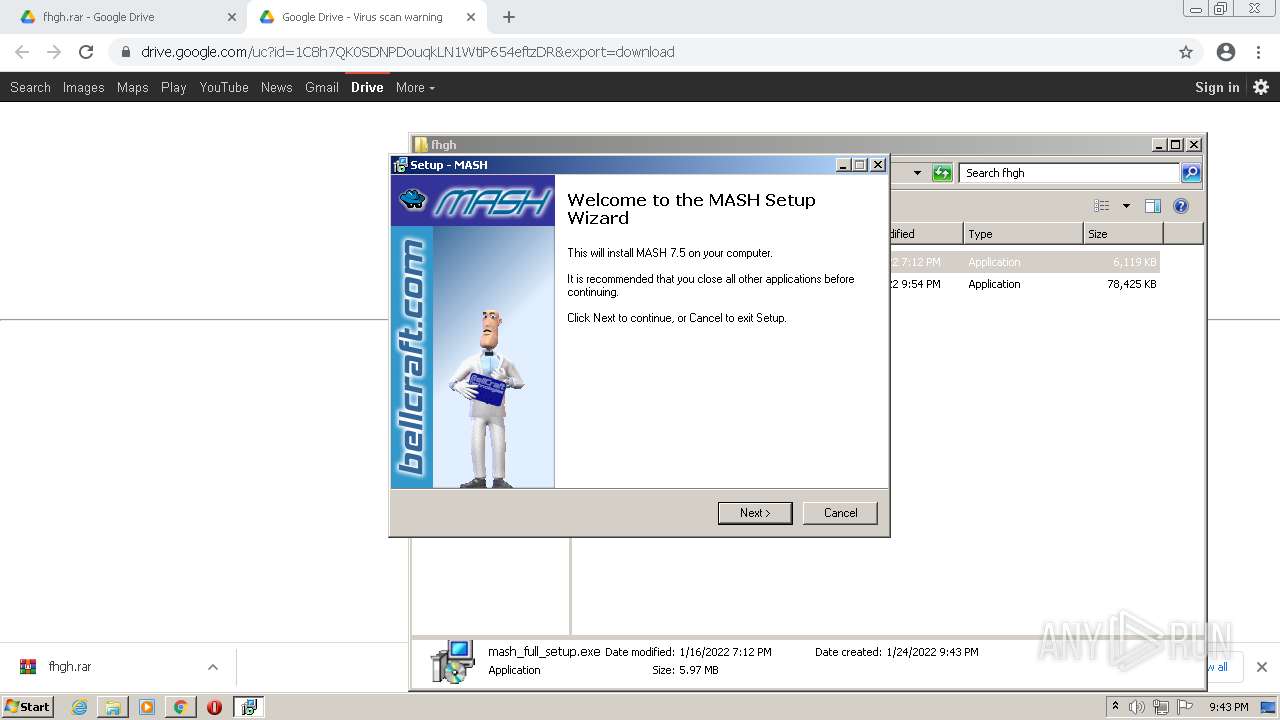
- mash_full_setup.exe (PID: 756)
- mash_full_setup.exe (PID: 3800)
- mash_full_setup.exe.tmp (PID: 3524)
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
- spchcpl.exe (PID: 1440)
- spchapi.exe (PID: 3304)
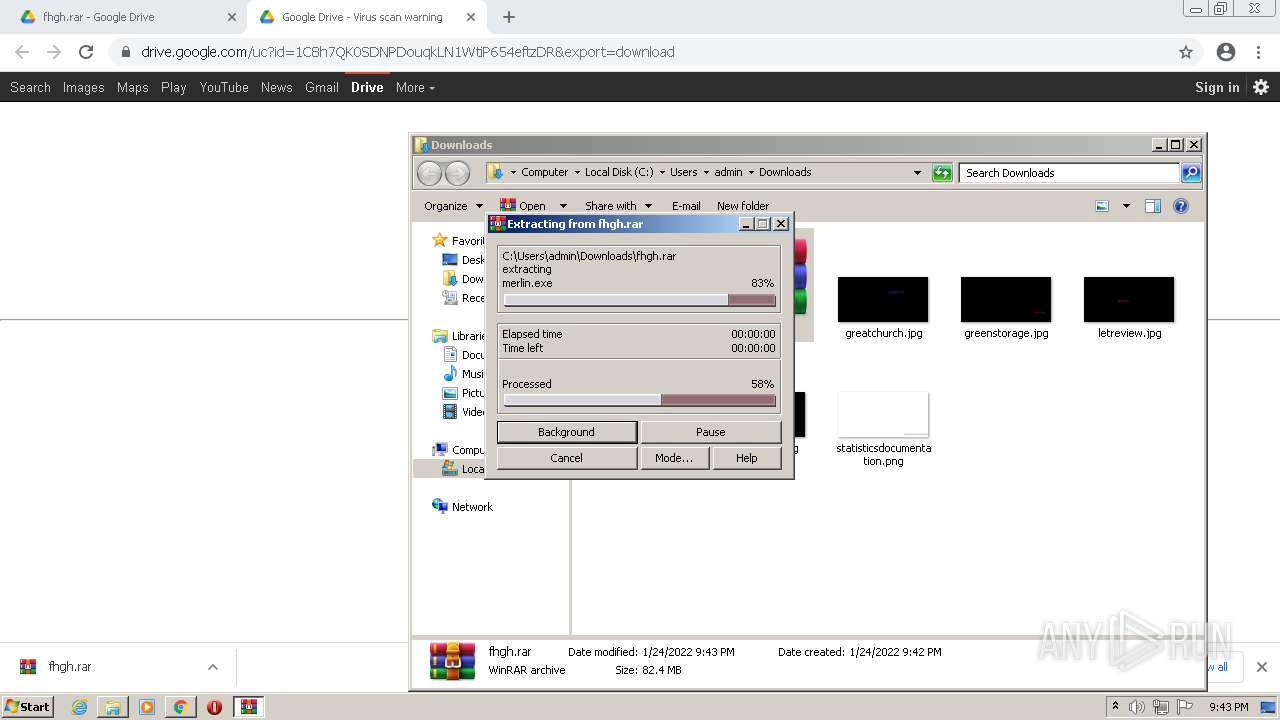
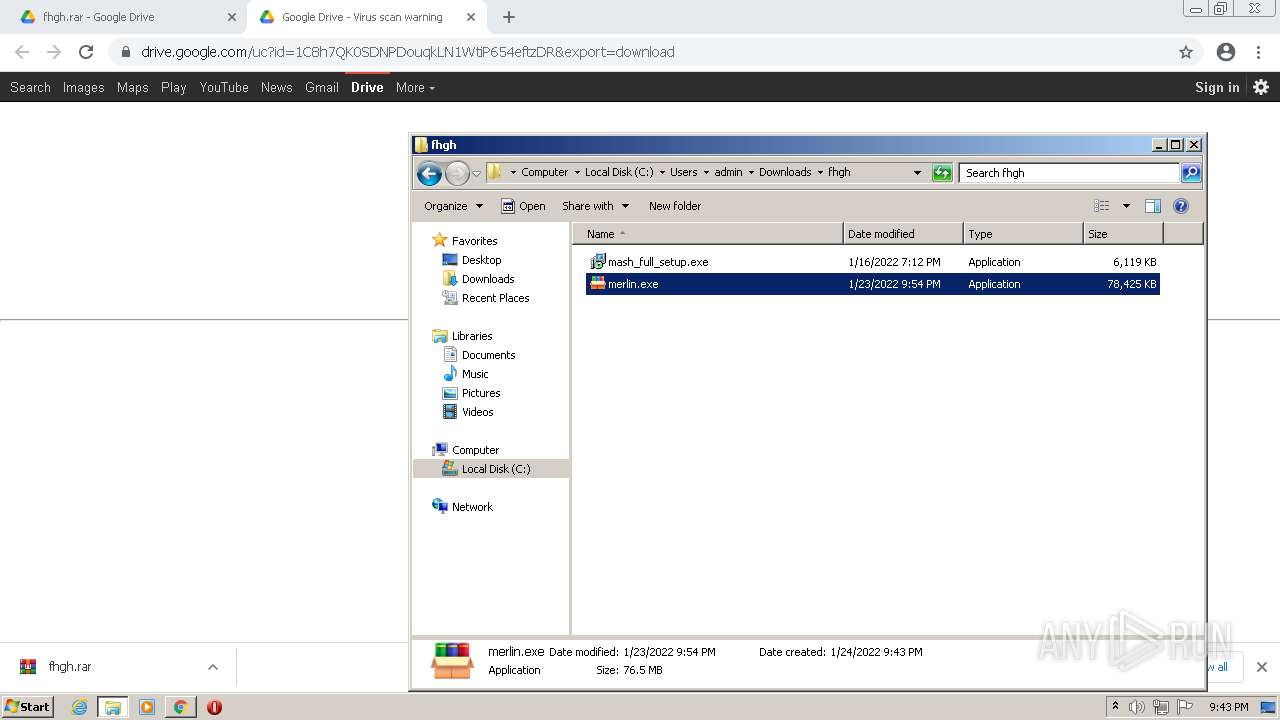
- merlin.exe (PID: 876)
- Spike.exe (PID: 3148)
- Spike.exe (PID: 2884)
- INSCD10.tmp (PID: 3696)
- Flash.exe (PID: 1560)
- QQPlayer.exe (PID: 3072)
- ace.exe (PID: 2652)
- QQPlayer.exe (PID: 1276)
- Spike.exe (PID: 3392)
Registers / Runs the DLL via REGSVR32.EXE
- mash_full_setup.exe.tmp (PID: 3524)
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2228)
- regsvr32.exe (PID: 1952)
- regsvr32.exe (PID: 2348)
- spchapi.exe (PID: 3304)
- regsvr32.exe (PID: 2420)
- regsvr32.exe (PID: 3912)
- regsvr32.exe (PID: 128)
- regsvr32.exe (PID: 2932)
- chrome.exe (PID: 836)
- regsvr32.exe (PID: 1520)
- regsvr32.exe (PID: 2508)
- chrome.exe (PID: 4032)
- DllHost.exe (PID: 1340)
- WinRAR.exe (PID: 2600)
- consent.exe (PID: 1260)
- DllHost.exe (PID: 940)
- chrome.exe (PID: 1696)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 2268)
- wmiprvse.exe (PID: 2652)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 3340)
- grpconv.exe (PID: 3232)
- regsvr32.exe (PID: 2440)
- chrome.exe (PID: 2116)
- svchost.exe (PID: 2496)
- DllHost.exe (PID: 1060)
- DllHost.exe (PID: 2368)
- grpconv.exe (PID: 1148)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 128)
- chrome.exe (PID: 3156)
- mash_full_setup.exe (PID: 3800)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 3840)
- grpconv.exe (PID: 2204)
- chrome.exe (PID: 2600)
- regsvr32.exe (PID: 3768)
- chrome.exe (PID: 568)
- DllHost.exe (PID: 2432)
- DllHost.exe (PID: 476)
- regsvr32.exe (PID: 3812)
- grpconv.exe (PID: 1260)
- mash_full_setup.exe (PID: 756)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 612)
- chrome.exe (PID: 2112)
- merlin.exe (PID: 304)
- regsvr32.exe (PID: 4032)
- chrome.exe (PID: 3968)
- consent.exe (PID: 2352)
- DllHost.exe (PID: 3168)
- DllHost.exe (PID: 3740)
- merlin.exe (PID: 876)
- DllHost.exe (PID: 1680)
- conhost.exe (PID: 576)
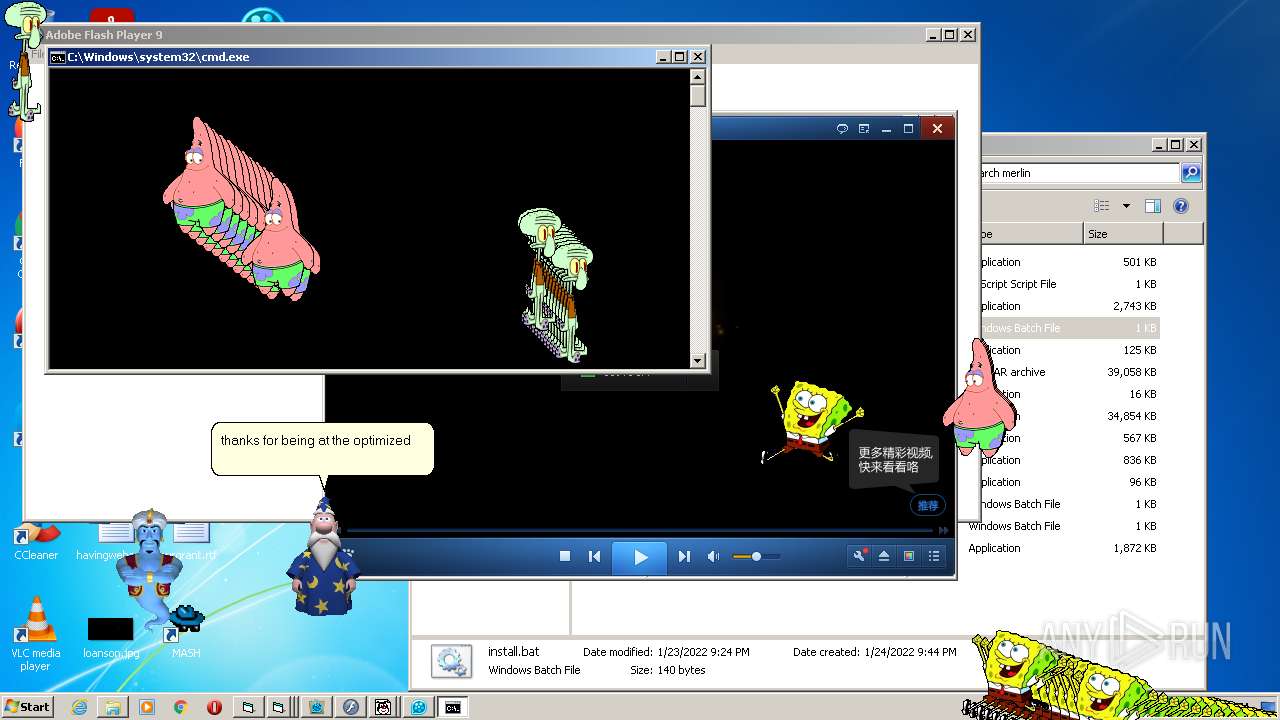
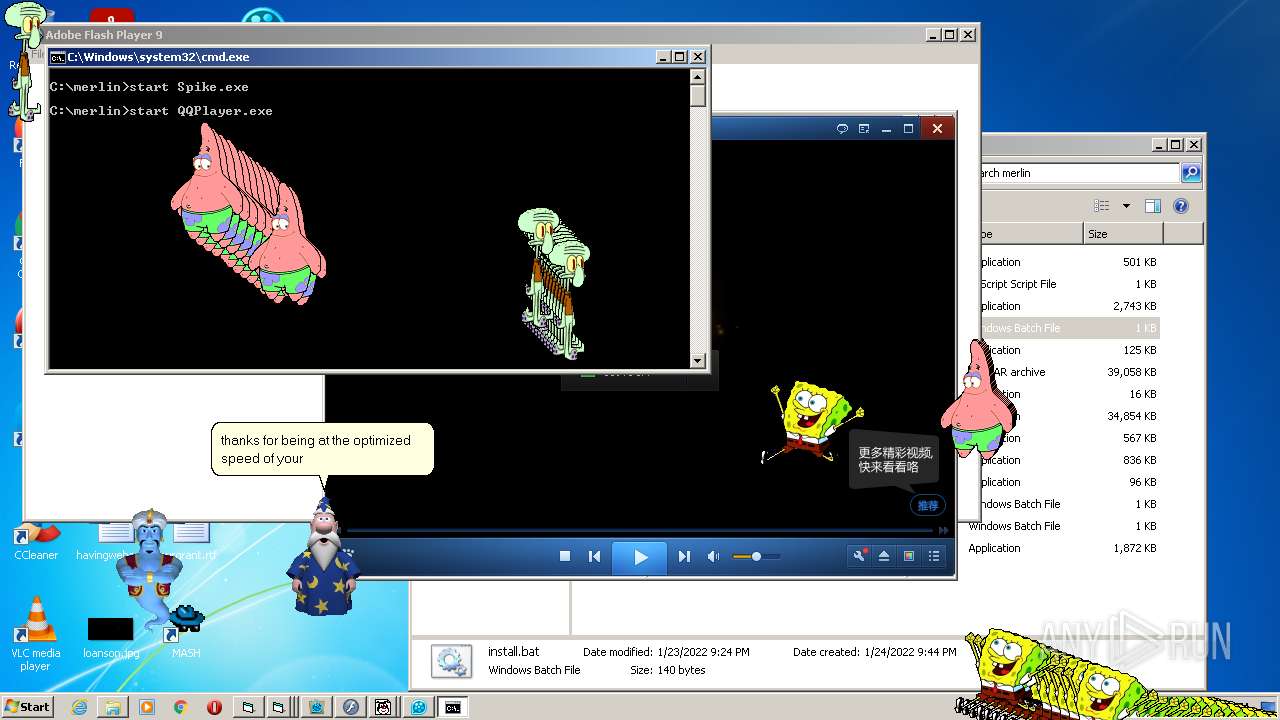
- cmd.exe (PID: 2880)
- DllHost.exe (PID: 3576)
- DllHost.exe (PID: 3252)
- consent.exe (PID: 116)
- xp11.exe (PID: 1244)
- PING.EXE (PID: 2128)
- rundll32.exe (PID: 3840)
- rundll32.exe (PID: 2832)
- grpconv.exe (PID: 2232)
- meme.exe (PID: 3856)
- AgentSvr.exe (PID: 2220)
- Project1.exe (PID: 1080)
- AgentSvr.exe (PID: 2884)
- runonce.exe (PID: 2148)
- DllHost.exe (PID: 2812)
- SpongeBob_ScreenToy.exe (PID: 1292)
- cmd.exe (PID: 2836)
- conhost.exe (PID: 1044)
- Spike.exe (PID: 3148)
- consent.exe (PID: 2824)
- DllHost.exe (PID: 3184)
- Spike.exe (PID: 2884)
- DllHost.exe (PID: 1828)
- QQPlayer.exe (PID: 3072)
- Flash.exe (PID: 1560)
- INSCD10.tmp (PID: 3696)
- Flash.exe (PID: 2864)
- SearchProtocolHost.exe (PID: 3548)
- SearchFilterHost.exe (PID: 4024)
- DllHost.exe (PID: 288)
- ace.exe (PID: 2652)
- ace.exe (PID: 2436)
- ace.exe (PID: 2792)
- ace.exe (PID: 3232)
- ace.exe (PID: 1728)
- ace.exe (PID: 3136)
- DllHost.exe (PID: 3296)
- WScript.exe (PID: 3964)
- consent.exe (PID: 3620)
- DllHost.exe (PID: 2388)
- DllHost.exe (PID: 1768)
- QQPlayer.exe (PID: 1276)
- consent.exe (PID: 2252)
- DllHost.exe (PID: 1284)
- iexplore.exe (PID: 876)
- DllHost.exe (PID: 3828)
- iexplore.exe (PID: 1832)
- DllHost.exe (PID: 1288)
- QQPlayer.exe (PID: 4080)
- WScript.exe (PID: 3468)
- conhost.exe (PID: 2984)
- WScript.exe (PID: 2272)
- SpongeBob_ScreenToy.exe (PID: 2060)
- SpongeBob_ScreenToy.exe (PID: 692)
- SpongeBob_ScreenToy.exe (PID: 3140)
- cmd.exe (PID: 2388)
- SpongeBob_ScreenToy.exe (PID: 3656)
- SpongeBob_ScreenToy.exe (PID: 1092)
- SpongeBob_ScreenToy.exe (PID: 3968)
- SpongeBob_ScreenToy.exe (PID: 3376)
- SpongeBob_ScreenToy.exe (PID: 3660)
- SpongeBob_ScreenToy.exe (PID: 3484)
- SpongeBob_ScreenToy.exe (PID: 2160)
- SpongeBob_ScreenToy.exe (PID: 3948)
- SpongeBob_ScreenToy.exe (PID: 3240)
- SpongeBob_ScreenToy.exe (PID: 2384)
- SpongeBob_ScreenToy.exe (PID: 2208)
- SpongeBob_ScreenToy.exe (PID: 3788)
- SpongeBob_ScreenToy.exe (PID: 2128)
- SpongeBob_ScreenToy.exe (PID: 2348)
- SpongeBob_ScreenToy.exe (PID: 2572)
- SpongeBob_ScreenToy.exe (PID: 1832)
- SpongeBob_ScreenToy.exe (PID: 2284)
- SpongeBob_ScreenToy.exe (PID: 3572)
- SpongeBob_ScreenToy.exe (PID: 2692)
- SpongeBob_ScreenToy.exe (PID: 116)
- SpongeBob_ScreenToy.exe (PID: 3868)
- SpongeBob_ScreenToy.exe (PID: 2924)
- SpongeBob_ScreenToy.exe (PID: 1780)
- SpongeBob_ScreenToy.exe (PID: 2332)
- SpongeBob_ScreenToy.exe (PID: 2396)
- WScript.exe (PID: 2884)
- cmd.exe (PID: 2988)
- Spike.exe (PID: 1528)
- consent.exe (PID: 3548)
- svchost.exe (PID: 2528)
- conhost.exe (PID: 2868)
- DllHost.exe (PID: 3880)
- DllHost.exe (PID: 2236)
- Spike.exe (PID: 3392)
- QQPlayer.exe (PID: 3092)
- consent.exe (PID: 2908)
- INSA9DF.tmp (PID: 3296)
- Flash.exe (PID: 480)
- Flash.exe (PID: 484)
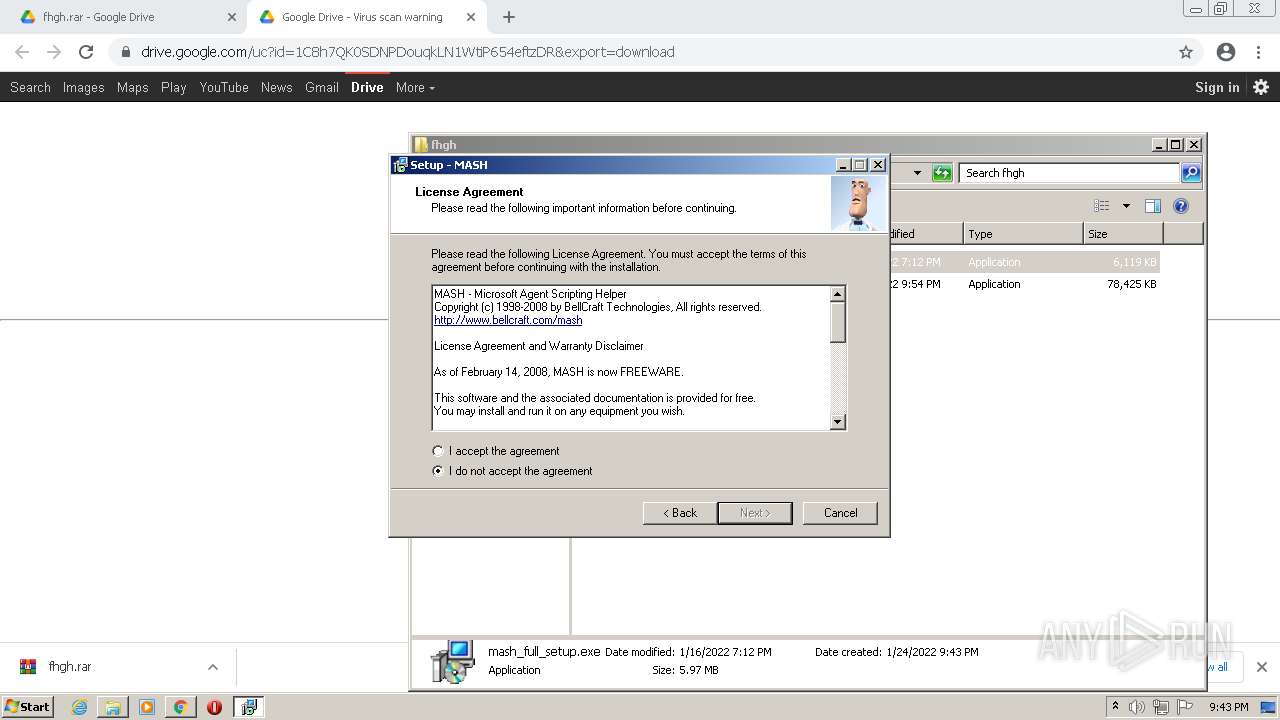
Changes the autorun value in the registry
- tv_enua.exe (PID: 2352)
- rundll32.exe (PID: 3840)
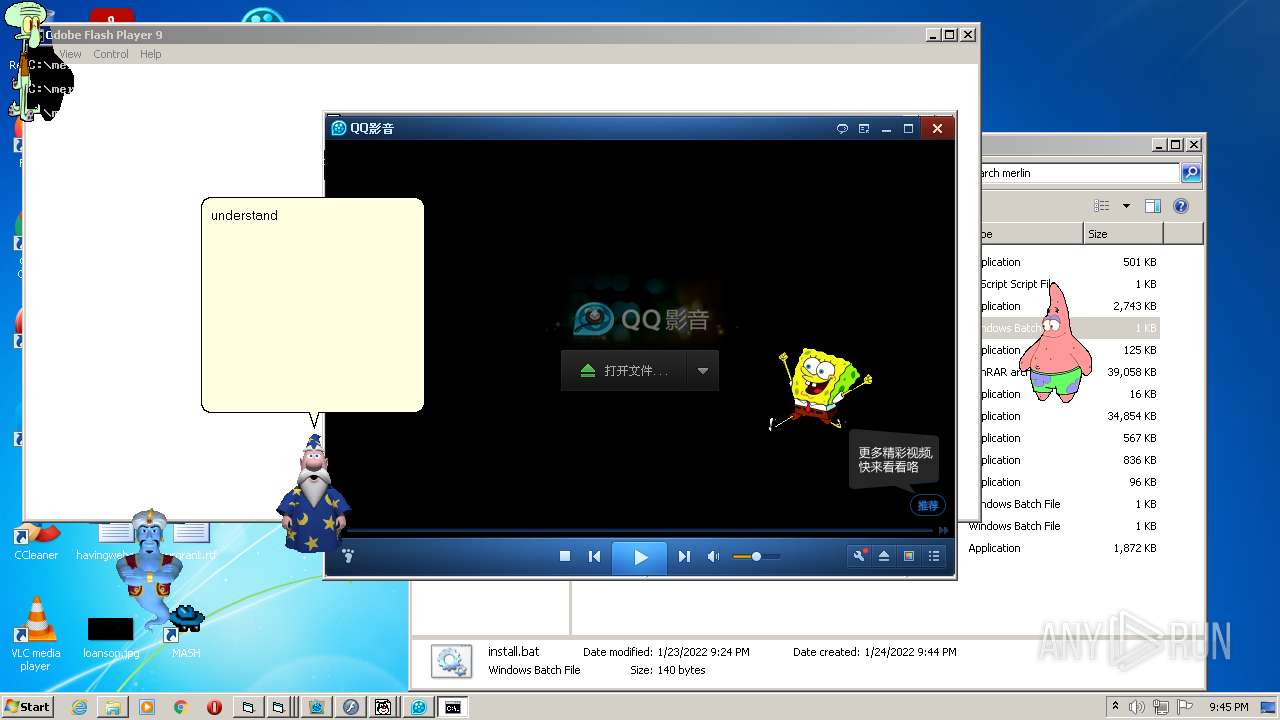
GOOTKIT detected
- spchapi.exe (PID: 3304)
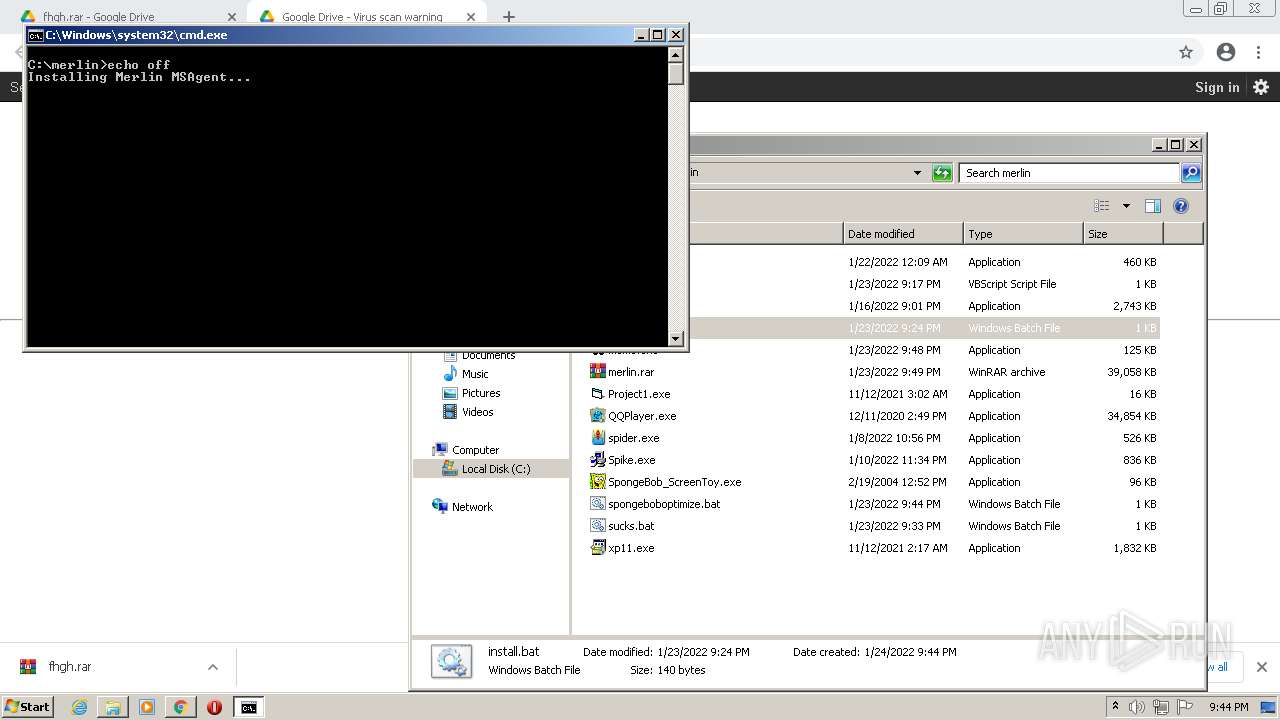
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2880)
SUSPICIOUS
Reads the computer name
- wmiprvse.exe (PID: 2652)
- WinRAR.exe (PID: 2600)
- mash_full_setup.exe.tmp (PID: 3116)
- mash_full_setup.exe.tmp (PID: 3524)
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
- spchcpl.exe (PID: 1440)
- spchapi.exe (PID: 3304)
- merlin.exe (PID: 304)
- merlin.exe (PID: 876)
- cmd.exe (PID: 2880)
- meme.exe (PID: 3856)
- AgentSvr.exe (PID: 2220)
- cmd.exe (PID: 2836)
- Spike.exe (PID: 3148)
- QQPlayer.exe (PID: 3072)
- INSCD10.tmp (PID: 3696)
- Flash.exe (PID: 2864)
- Flash.exe (PID: 1560)
- ace.exe (PID: 2652)
- ace.exe (PID: 2792)
- ace.exe (PID: 3232)
- WScript.exe (PID: 3964)
- QQPlayer.exe (PID: 1276)
- QQPlayer.exe (PID: 4080)
- WScript.exe (PID: 2272)
- WScript.exe (PID: 3468)
- WScript.exe (PID: 2884)
- cmd.exe (PID: 2988)
- Spike.exe (PID: 1528)
- Flash.exe (PID: 480)
- QQPlayer.exe (PID: 3092)
- Flash.exe (PID: 484)
Checks supported languages
- wmiprvse.exe (PID: 2652)
- WinRAR.exe (PID: 2600)
- mash_full_setup.exe (PID: 756)
- mash_full_setup.exe.tmp (PID: 3116)
- mash_full_setup.exe (PID: 3800)
- mash_full_setup.exe.tmp (PID: 3524)
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
- AgentSvr.exe (PID: 2884)
- spchcpl.exe (PID: 1440)
- spchapi.exe (PID: 3304)
- merlin.exe (PID: 304)
- merlin.exe (PID: 876)
- conhost.exe (PID: 576)
- cmd.exe (PID: 2880)
- xp11.exe (PID: 1244)
- meme.exe (PID: 3856)
- AgentSvr.exe (PID: 2220)
- Project1.exe (PID: 1080)
- SpongeBob_ScreenToy.exe (PID: 1292)
- Spike.exe (PID: 3148)
- conhost.exe (PID: 1044)
- cmd.exe (PID: 2836)
- Spike.exe (PID: 2884)
- QQPlayer.exe (PID: 3072)
- Flash.exe (PID: 1560)
- INSCD10.tmp (PID: 3696)
- Flash.exe (PID: 2864)
- ace.exe (PID: 2652)
- ace.exe (PID: 2436)
- ace.exe (PID: 3232)
- ace.exe (PID: 1728)
- ace.exe (PID: 3136)
- ace.exe (PID: 2792)
- WScript.exe (PID: 3964)
- QQPlayer.exe (PID: 1276)
- QQPlayer.exe (PID: 4080)
- WScript.exe (PID: 3468)
- conhost.exe (PID: 2984)
- WScript.exe (PID: 2272)
- SpongeBob_ScreenToy.exe (PID: 2060)
- SpongeBob_ScreenToy.exe (PID: 3140)
- SpongeBob_ScreenToy.exe (PID: 3484)
- SpongeBob_ScreenToy.exe (PID: 692)
- cmd.exe (PID: 2388)
- SpongeBob_ScreenToy.exe (PID: 3656)
- SpongeBob_ScreenToy.exe (PID: 2160)
- SpongeBob_ScreenToy.exe (PID: 3660)
- SpongeBob_ScreenToy.exe (PID: 3948)
- SpongeBob_ScreenToy.exe (PID: 1092)
- SpongeBob_ScreenToy.exe (PID: 3376)
- SpongeBob_ScreenToy.exe (PID: 2384)
- SpongeBob_ScreenToy.exe (PID: 3240)
- SpongeBob_ScreenToy.exe (PID: 3788)
- SpongeBob_ScreenToy.exe (PID: 2208)
- SpongeBob_ScreenToy.exe (PID: 3968)
- SpongeBob_ScreenToy.exe (PID: 2348)
- SpongeBob_ScreenToy.exe (PID: 2572)
- SpongeBob_ScreenToy.exe (PID: 1832)
- SpongeBob_ScreenToy.exe (PID: 2284)
- SpongeBob_ScreenToy.exe (PID: 2128)
- SpongeBob_ScreenToy.exe (PID: 116)
- SpongeBob_ScreenToy.exe (PID: 2692)
- SpongeBob_ScreenToy.exe (PID: 1780)
- SpongeBob_ScreenToy.exe (PID: 2924)
- SpongeBob_ScreenToy.exe (PID: 3868)
- SpongeBob_ScreenToy.exe (PID: 2396)
- SpongeBob_ScreenToy.exe (PID: 2332)
- SpongeBob_ScreenToy.exe (PID: 3572)
- conhost.exe (PID: 2868)
- WScript.exe (PID: 2884)
- cmd.exe (PID: 2988)
- Spike.exe (PID: 1528)
- Spike.exe (PID: 3392)
- QQPlayer.exe (PID: 3092)
- Flash.exe (PID: 480)
- INSA9DF.tmp (PID: 3296)
- Flash.exe (PID: 484)
Reads Windows owner or organization settings
- wmiprvse.exe (PID: 2652)
- mash_full_setup.exe.tmp (PID: 3524)
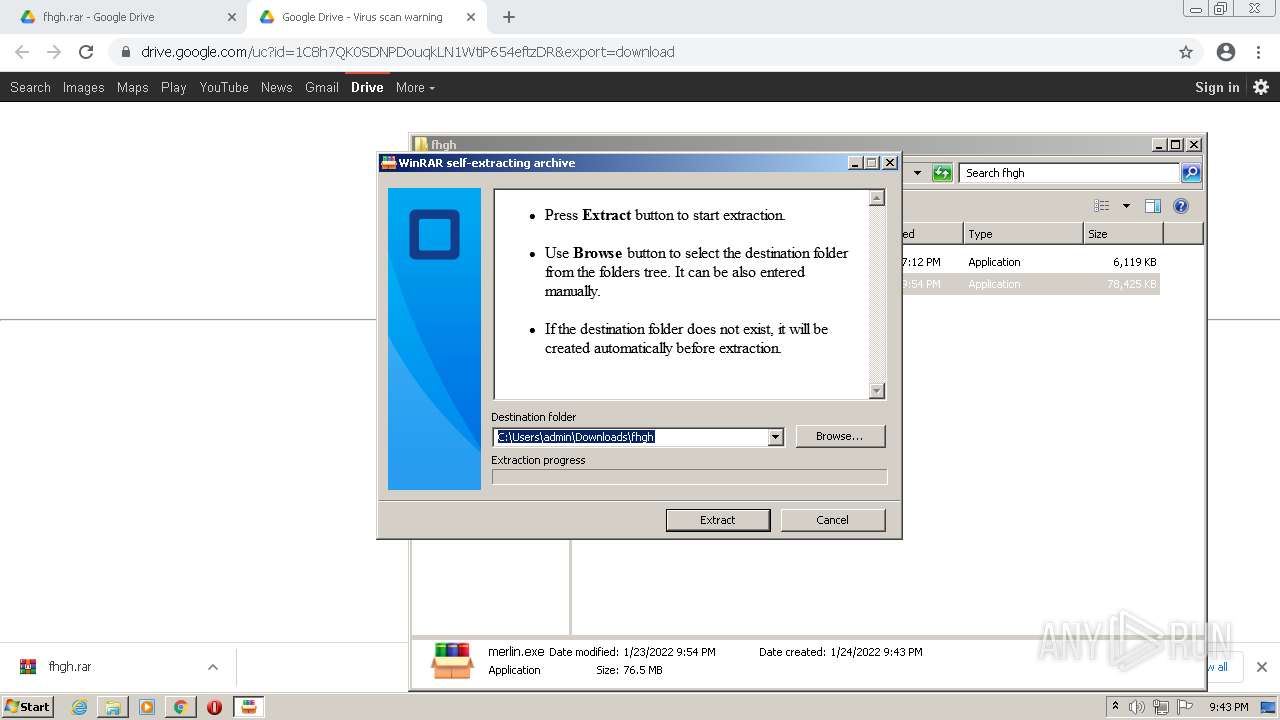
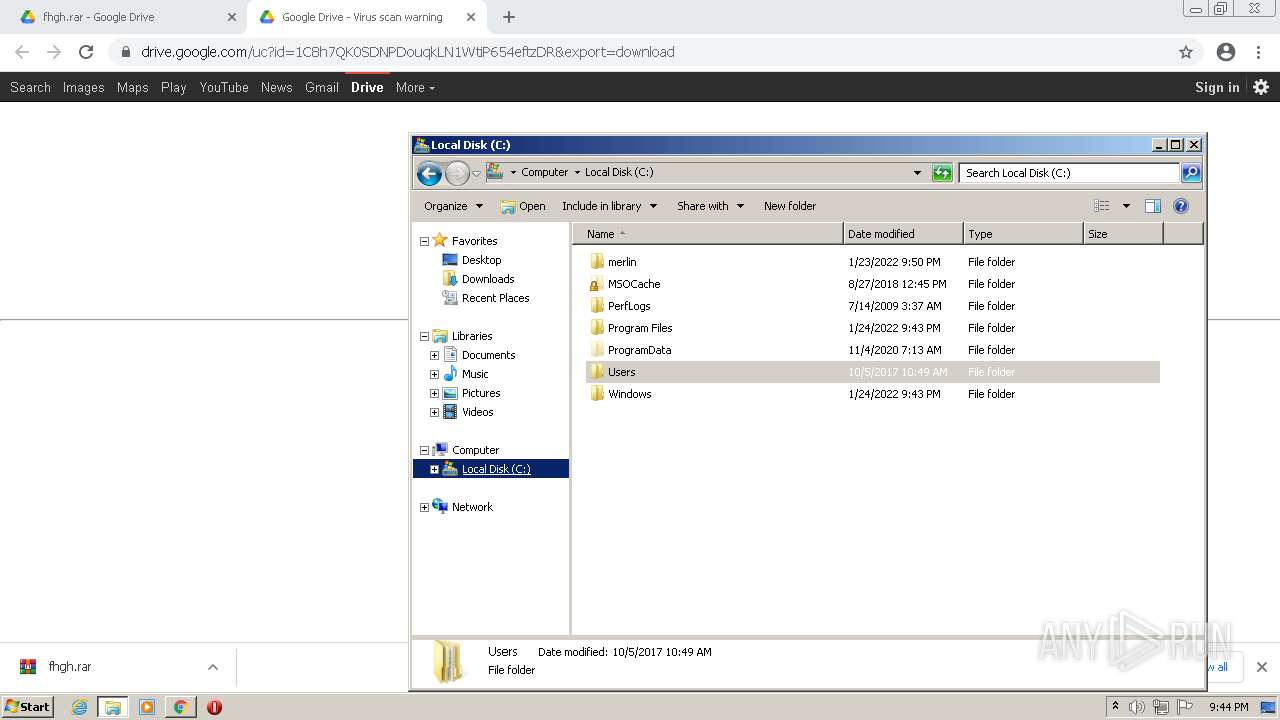
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2600)
- mash_full_setup.exe (PID: 756)
- mash_full_setup.exe (PID: 3800)
- mash_full_setup.exe.tmp (PID: 3524)
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
- spchcpl.exe (PID: 1440)
- spchapi.exe (PID: 3304)
- merlin.exe (PID: 876)
- Spike.exe (PID: 2884)
- Flash.exe (PID: 1560)
- INSCD10.tmp (PID: 3696)
- Spike.exe (PID: 3148)
- ace.exe (PID: 2652)
- QQPlayer.exe (PID: 3072)
- QQPlayer.exe (PID: 1276)
- Spike.exe (PID: 3392)
Drops a file with too old compile date
- WinRAR.exe (PID: 2600)
- mash_full_setup.exe (PID: 756)
- mash_full_setup.exe (PID: 3800)
- mash_full_setup.exe.tmp (PID: 3524)
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
- spchcpl.exe (PID: 1440)
- spchapi.exe (PID: 3304)
- merlin.exe (PID: 876)
- Spike.exe (PID: 2884)
- Flash.exe (PID: 1560)
- INSCD10.tmp (PID: 3696)
- Spike.exe (PID: 3148)
- QQPlayer.exe (PID: 3072)
- ace.exe (PID: 2652)
- QQPlayer.exe (PID: 1276)
- Spike.exe (PID: 3392)
Reads the Windows organization settings
- mash_full_setup.exe.tmp (PID: 3524)
Drops a file that was compiled in debug mode
- mash_full_setup.exe.tmp (PID: 3524)
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
- spchcpl.exe (PID: 1440)
- spchapi.exe (PID: 3304)
- merlin.exe (PID: 876)
- Flash.exe (PID: 1560)
- INSCD10.tmp (PID: 3696)
- QQPlayer.exe (PID: 3072)
- QQPlayer.exe (PID: 1276)
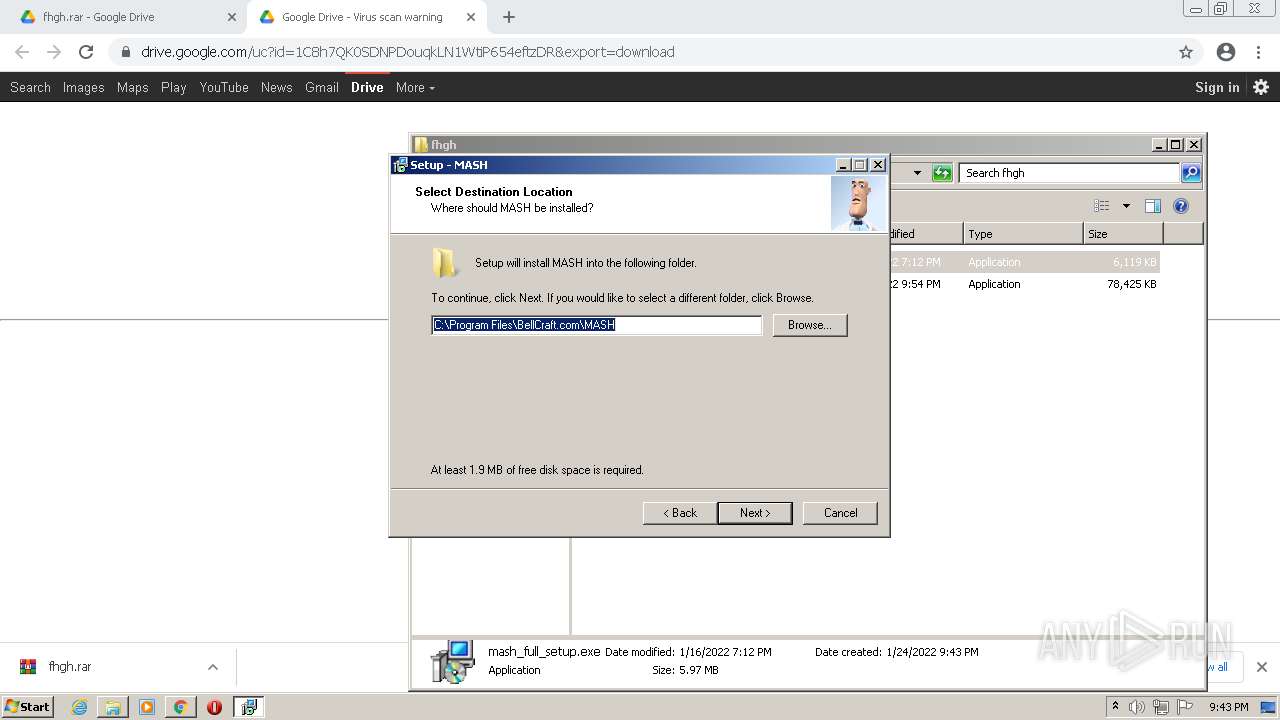
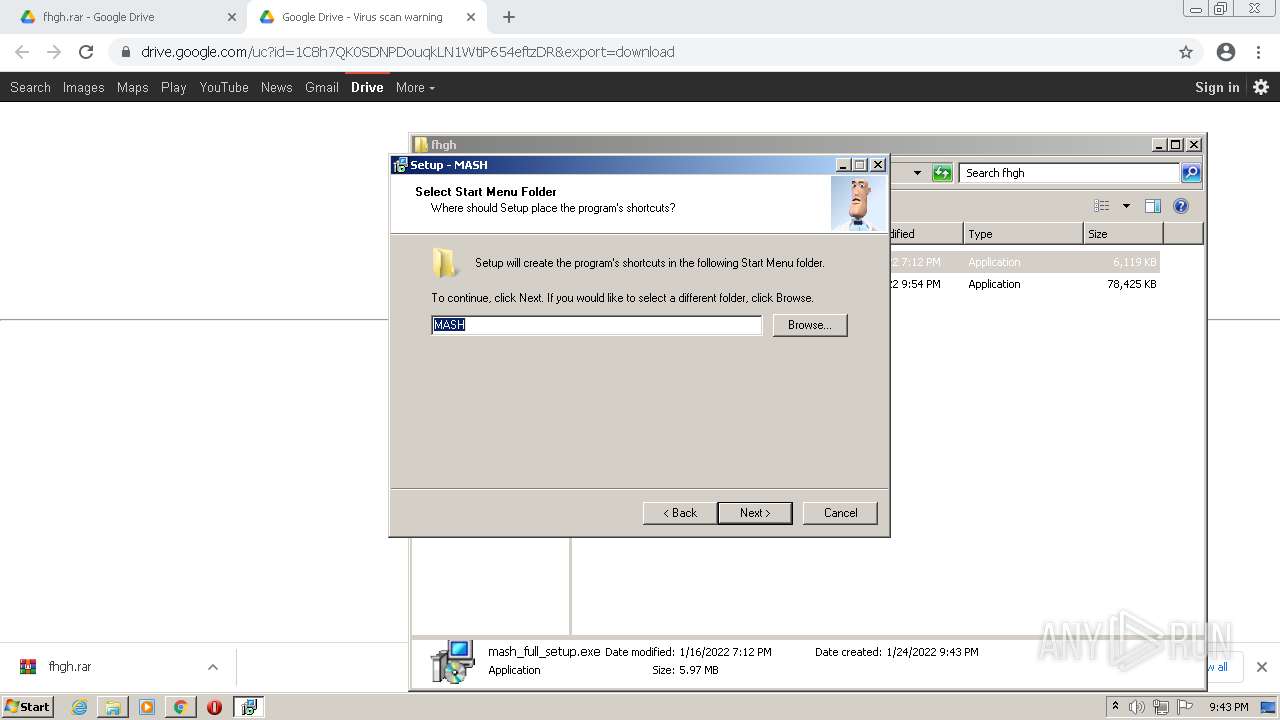
Creates a directory in Program Files
- mash_full_setup.exe.tmp (PID: 3524)
- QQPlayer.exe (PID: 3072)
- INSCD10.tmp (PID: 3696)
- QQPlayer.exe (PID: 1276)
Creates files in the Windows directory
- mash_full_setup.exe.tmp (PID: 3524)
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
- spchcpl.exe (PID: 1440)
- spchapi.exe (PID: 3304)
- rundll32.exe (PID: 3840)
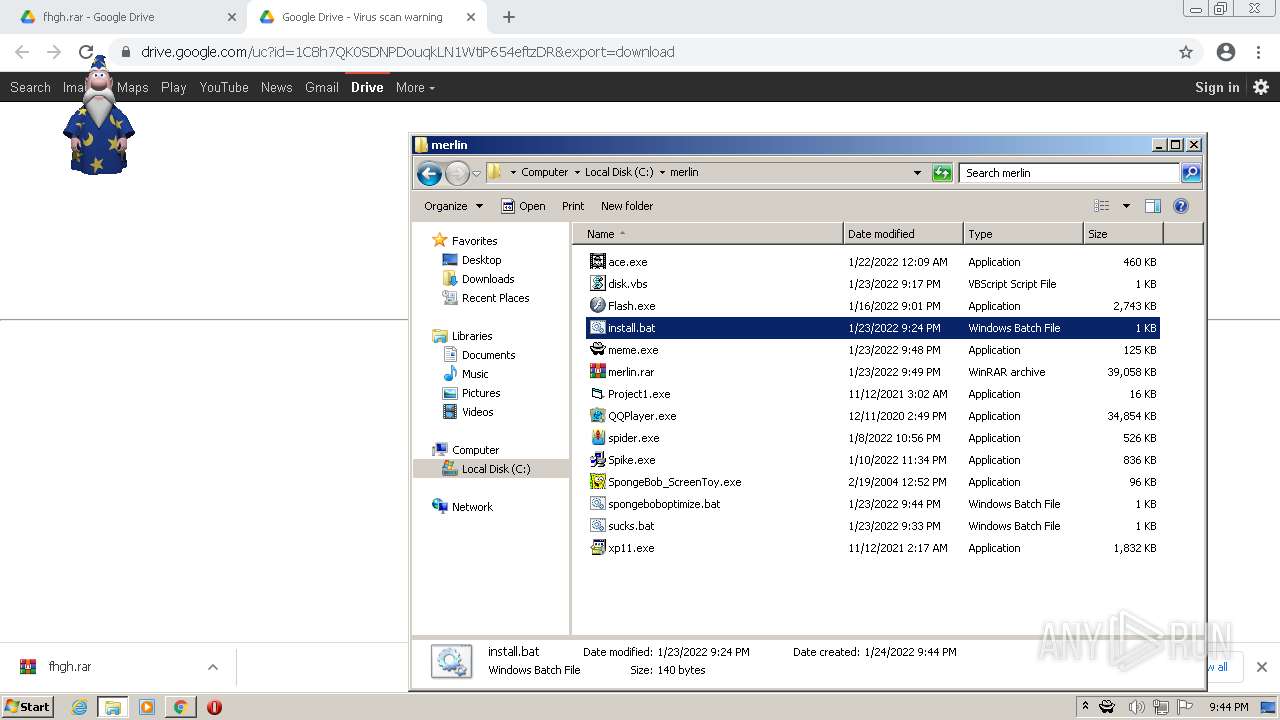
Changes default file association
- mash_full_setup.exe.tmp (PID: 3524)
- QQPlayer.exe (PID: 3072)
- QQPlayer.exe (PID: 1276)
- QQPlayer.exe (PID: 4080)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3768)
- regsvr32.exe (PID: 1520)
- regsvr32.exe (PID: 2348)
- regsvr32.exe (PID: 2420)
- regsvr32.exe (PID: 1952)
- regsvr32.exe (PID: 2932)
- regsvr32.exe (PID: 128)
- regsvr32.exe (PID: 3912)
- regsvr32.exe (PID: 2508)
- regsvr32.exe (PID: 2440)
- spchapi.exe (PID: 3304)
- QQPlayer.exe (PID: 3072)
- QQPlayer.exe (PID: 1276)
Drops a file with a compile date too recent
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
- spchcpl.exe (PID: 1440)
- spchapi.exe (PID: 3304)
Removes files from Windows directory
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
- spchcpl.exe (PID: 1440)
- spchapi.exe (PID: 3304)
- rundll32.exe (PID: 3840)
Reads internet explorer settings
- merlin.exe (PID: 304)
Reads Microsoft Outlook installation path
- merlin.exe (PID: 304)
- iexplore.exe (PID: 1832)
Application launched itself
- merlin.exe (PID: 304)
Uses RUNDLL32.EXE to load library
- xp11.exe (PID: 1244)
- runonce.exe (PID: 2148)
Reads the time zone
- runonce.exe (PID: 2148)
Executed via COM
- AgentSvr.exe (PID: 2220)
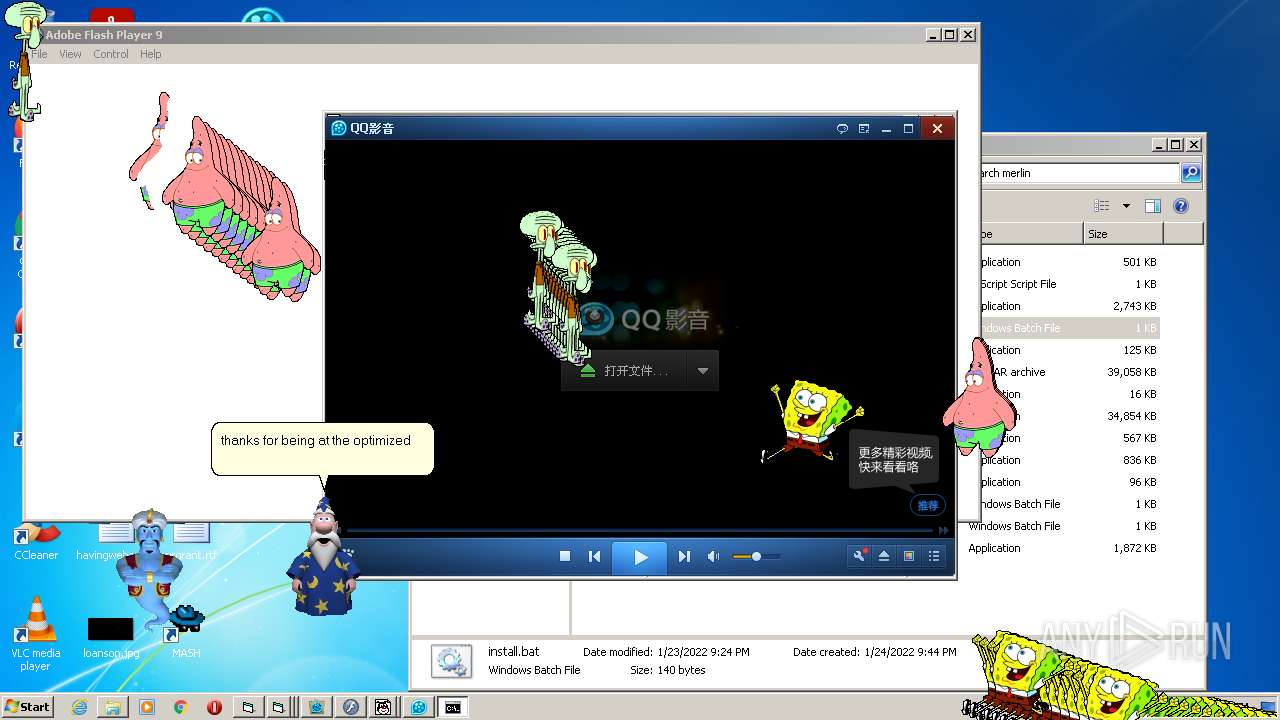
Starts CMD.EXE for commands execution
- meme.exe (PID: 3856)
Starts application with an unusual extension
- Spike.exe (PID: 2884)
- Spike.exe (PID: 3392)
Reads CPU info
- Flash.exe (PID: 2864)
- Flash.exe (PID: 484)
Creates files in the program directory
- QQPlayer.exe (PID: 3072)
- INSCD10.tmp (PID: 3696)
- QQPlayer.exe (PID: 1276)
- QQPlayer.exe (PID: 4080)
Creates a software uninstall entry
- INSCD10.tmp (PID: 3696)
- QQPlayer.exe (PID: 3072)
- QQPlayer.exe (PID: 1276)
Creates files in the user directory
- QQPlayer.exe (PID: 3072)
- QQPlayer.exe (PID: 1276)
- QQPlayer.exe (PID: 4080)
Executes scripts
- meme.exe (PID: 3856)
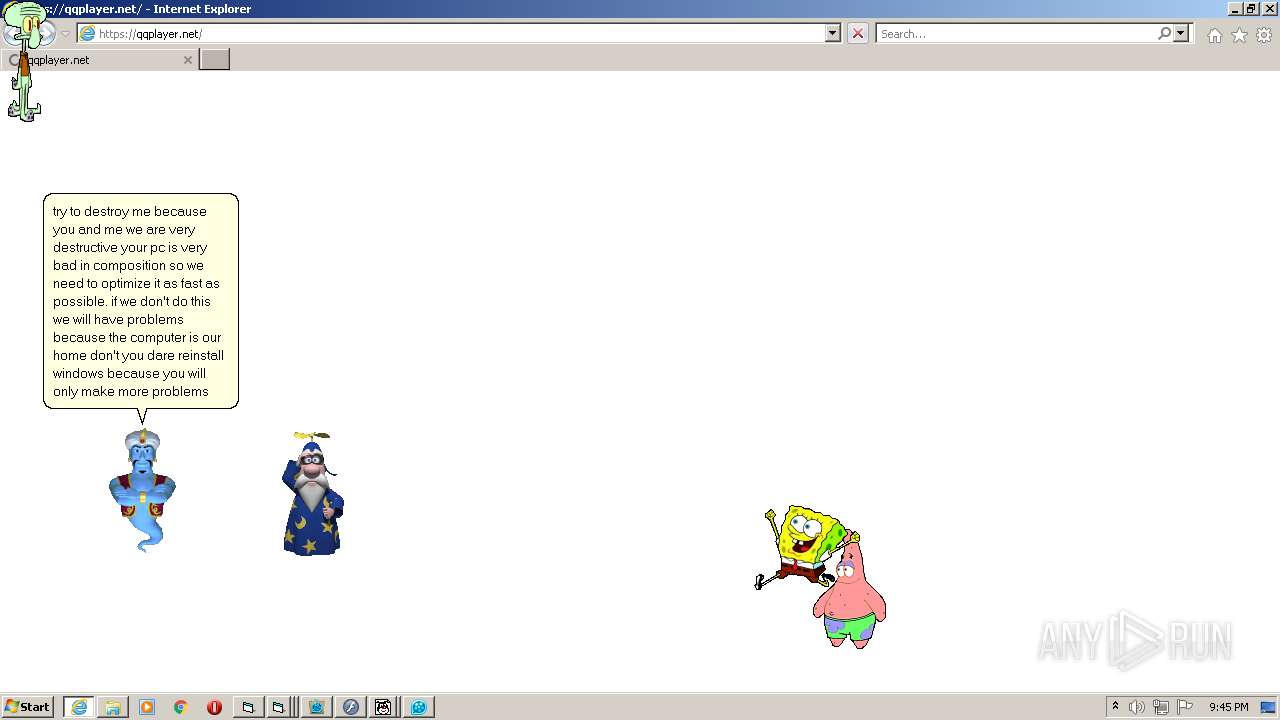
Starts Internet Explorer
- QQPlayer.exe (PID: 1276)
Reads the date of Windows installation
- QQPlayer.exe (PID: 4080)
INFO
Application launched itself
- chrome.exe (PID: 3756)
- iexplore.exe (PID: 876)
Reads the computer name
- chrome.exe (PID: 3756)
- chrome.exe (PID: 836)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 1696)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 2600)
- chrome.exe (PID: 128)
- svchost.exe (PID: 2496)
- chrome.exe (PID: 2116)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 3340)
- DllHost.exe (PID: 476)
- chrome.exe (PID: 4032)
- DllHost.exe (PID: 2432)
- DllHost.exe (PID: 940)
- consent.exe (PID: 1260)
- DllHost.exe (PID: 1340)
- DllHost.exe (PID: 1060)
- regsvr32.exe (PID: 3812)
- regsvr32.exe (PID: 2228)
- regsvr32.exe (PID: 4032)
- DllHost.exe (PID: 2368)
- consent.exe (PID: 2352)
- DllHost.exe (PID: 3168)
- DllHost.exe (PID: 3740)
- DllHost.exe (PID: 1680)
- consent.exe (PID: 116)
- DllHost.exe (PID: 3576)
- DllHost.exe (PID: 3252)
- PING.EXE (PID: 2128)
- rundll32.exe (PID: 3840)
- runonce.exe (PID: 2148)
- rundll32.exe (PID: 2832)
- DllHost.exe (PID: 2812)
- consent.exe (PID: 2824)
- consent.exe (PID: 2252)
- DllHost.exe (PID: 1828)
- DllHost.exe (PID: 3184)
- SearchProtocolHost.exe (PID: 3548)
- SearchFilterHost.exe (PID: 4024)
- DllHost.exe (PID: 288)
- DllHost.exe (PID: 3296)
- consent.exe (PID: 3620)
- DllHost.exe (PID: 2388)
- DllHost.exe (PID: 1768)
- DllHost.exe (PID: 1284)
- DllHost.exe (PID: 3828)
- iexplore.exe (PID: 876)
- DllHost.exe (PID: 1288)
- iexplore.exe (PID: 1832)
- svchost.exe (PID: 2528)
- consent.exe (PID: 2908)
- consent.exe (PID: 3548)
- DllHost.exe (PID: 2236)
- DllHost.exe (PID: 3880)
Checks supported languages
- chrome.exe (PID: 3756)
- chrome.exe (PID: 1696)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 836)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 128)
- chrome.exe (PID: 2600)
- svchost.exe (PID: 2496)
- chrome.exe (PID: 2116)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 612)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 4032)
- DllHost.exe (PID: 476)
- DllHost.exe (PID: 2432)
- chrome.exe (PID: 3840)
- DllHost.exe (PID: 940)
- consent.exe (PID: 1260)
- DllHost.exe (PID: 1060)
- DllHost.exe (PID: 1340)
- regsvr32.exe (PID: 4032)
- chrome.exe (PID: 568)
- regsvr32.exe (PID: 3768)
- regsvr32.exe (PID: 3812)
- regsvr32.exe (PID: 2228)
- regsvr32.exe (PID: 2420)
- regsvr32.exe (PID: 1520)
- regsvr32.exe (PID: 2348)
- regsvr32.exe (PID: 2932)
- regsvr32.exe (PID: 128)
- regsvr32.exe (PID: 1952)
- regsvr32.exe (PID: 3912)
- grpconv.exe (PID: 2204)
- regsvr32.exe (PID: 2508)
- regsvr32.exe (PID: 2440)
- grpconv.exe (PID: 3232)
- grpconv.exe (PID: 1260)
- grpconv.exe (PID: 1148)
- DllHost.exe (PID: 2368)
- chrome.exe (PID: 3968)
- consent.exe (PID: 2352)
- DllHost.exe (PID: 3168)
- DllHost.exe (PID: 3740)
- DllHost.exe (PID: 1680)
- consent.exe (PID: 116)
- DllHost.exe (PID: 3576)
- DllHost.exe (PID: 3252)
- PING.EXE (PID: 2128)
- rundll32.exe (PID: 3840)
- runonce.exe (PID: 2148)
- rundll32.exe (PID: 2832)
- grpconv.exe (PID: 2232)
- consent.exe (PID: 2824)
- DllHost.exe (PID: 2812)
- consent.exe (PID: 2252)
- DllHost.exe (PID: 3184)
- DllHost.exe (PID: 1828)
- SearchProtocolHost.exe (PID: 3548)
- SearchFilterHost.exe (PID: 4024)
- DllHost.exe (PID: 288)
- DllHost.exe (PID: 3296)
- consent.exe (PID: 3620)
- DllHost.exe (PID: 1768)
- DllHost.exe (PID: 2388)
- DllHost.exe (PID: 1284)
- DllHost.exe (PID: 3828)
- iexplore.exe (PID: 876)
- iexplore.exe (PID: 1832)
- DllHost.exe (PID: 1288)
- svchost.exe (PID: 2528)
- consent.exe (PID: 3548)
- consent.exe (PID: 2908)
- DllHost.exe (PID: 3880)
- DllHost.exe (PID: 2236)
Reads the hosts file
- chrome.exe (PID: 3756)
- chrome.exe (PID: 836)
Reads settings of System Certificates
- chrome.exe (PID: 836)
- consent.exe (PID: 116)
- iexplore.exe (PID: 1832)
- QQPlayer.exe (PID: 4080)
Reads the date of Windows installation
- chrome.exe (PID: 2600)
- iexplore.exe (PID: 876)
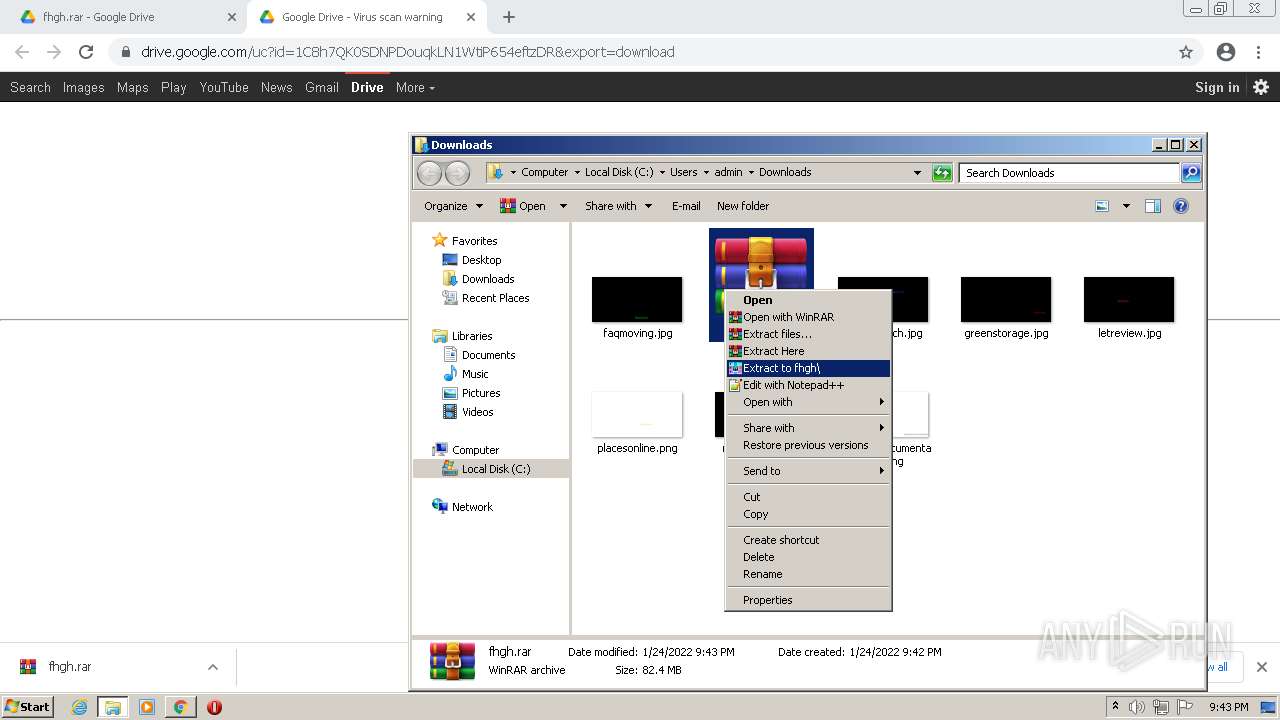
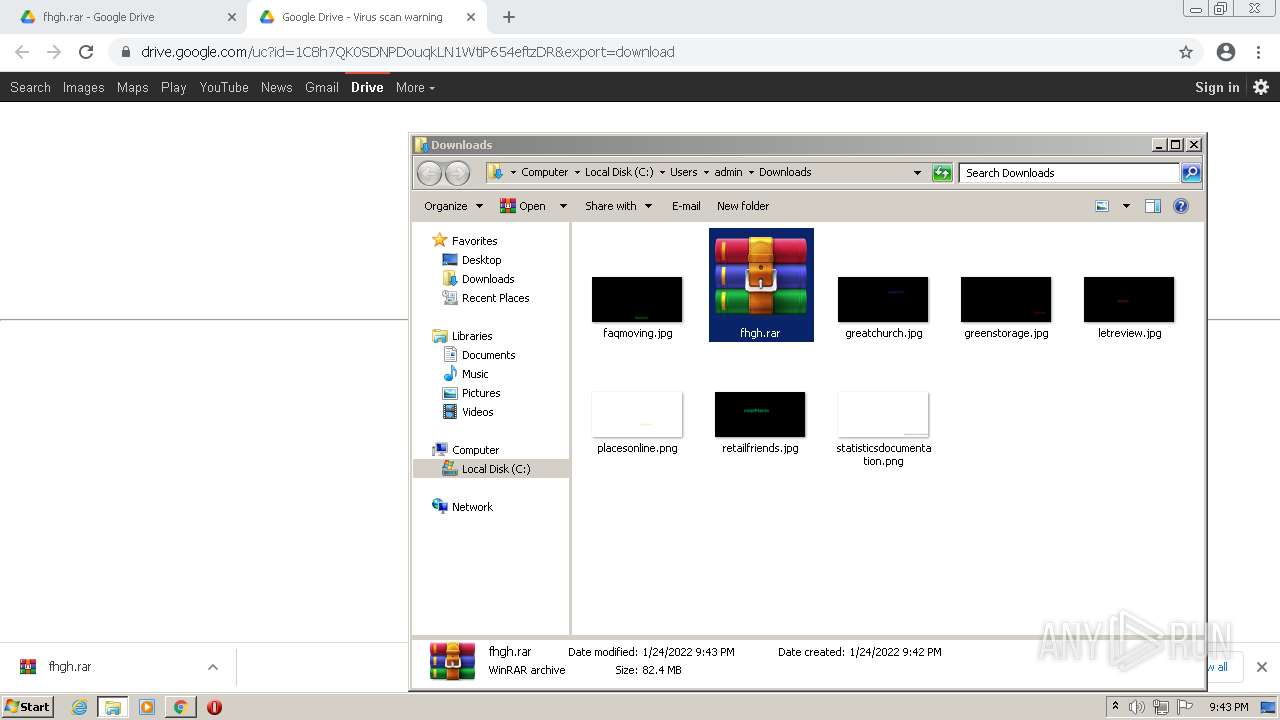
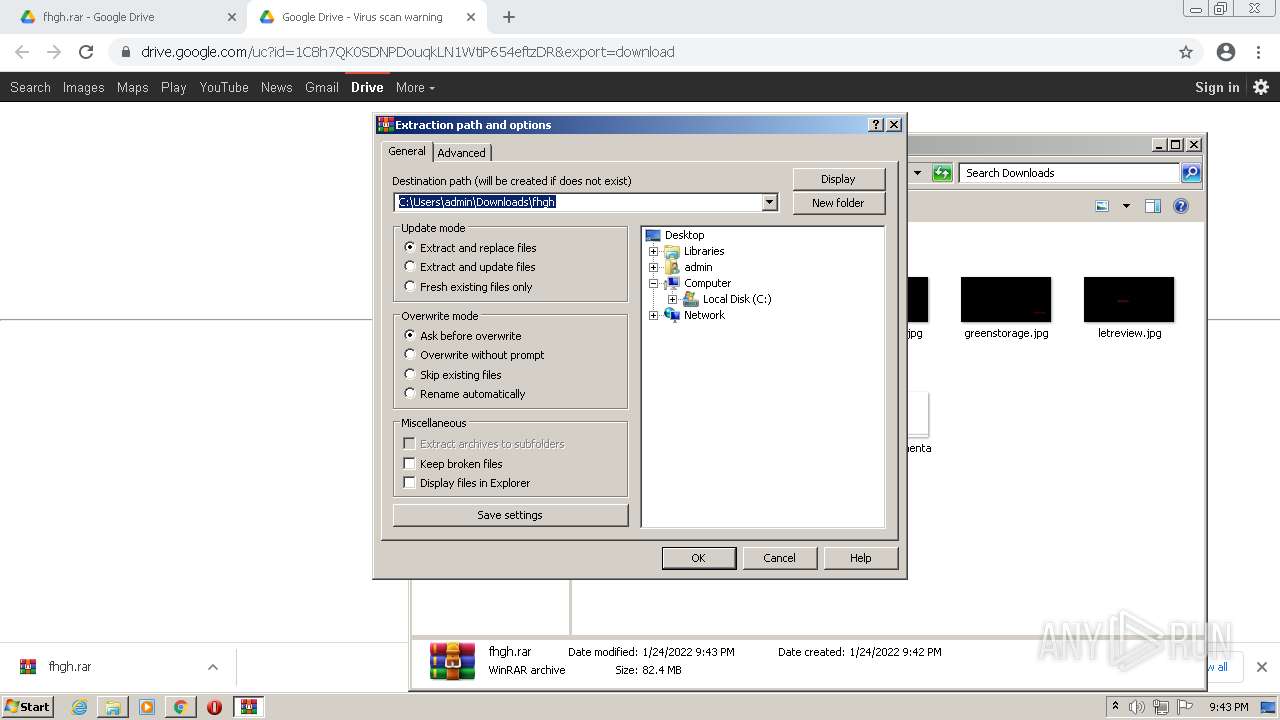
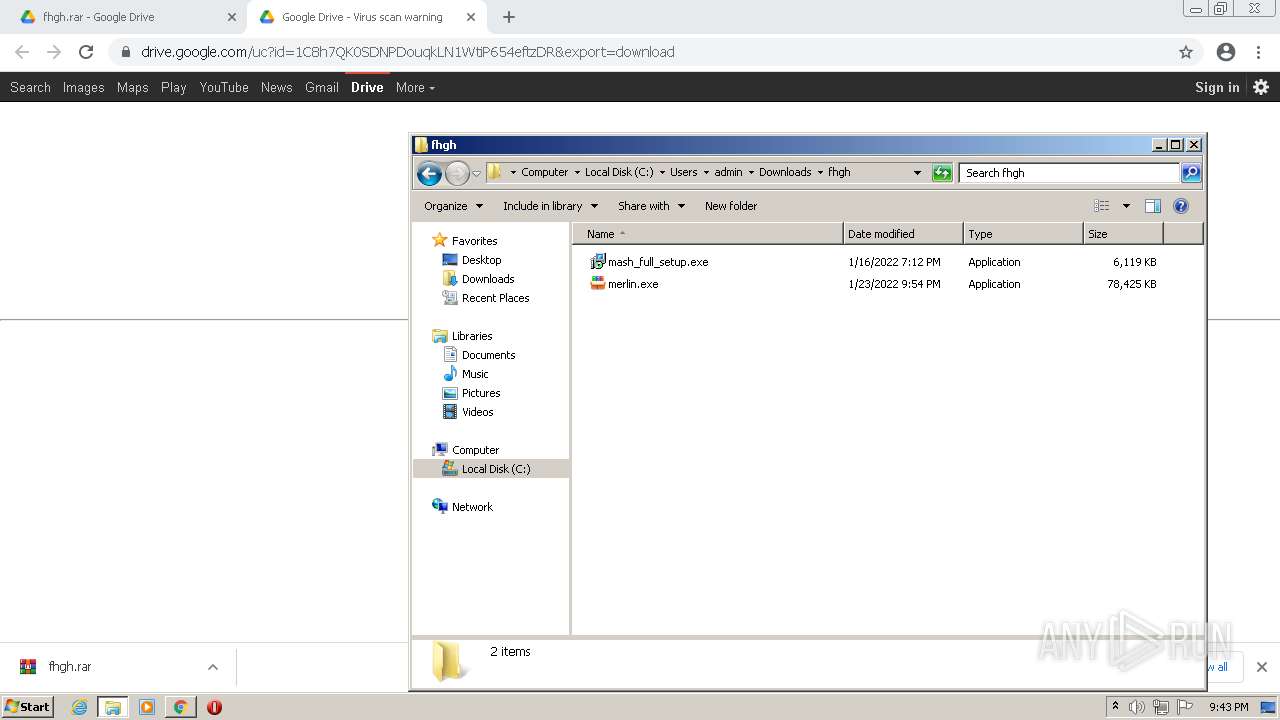
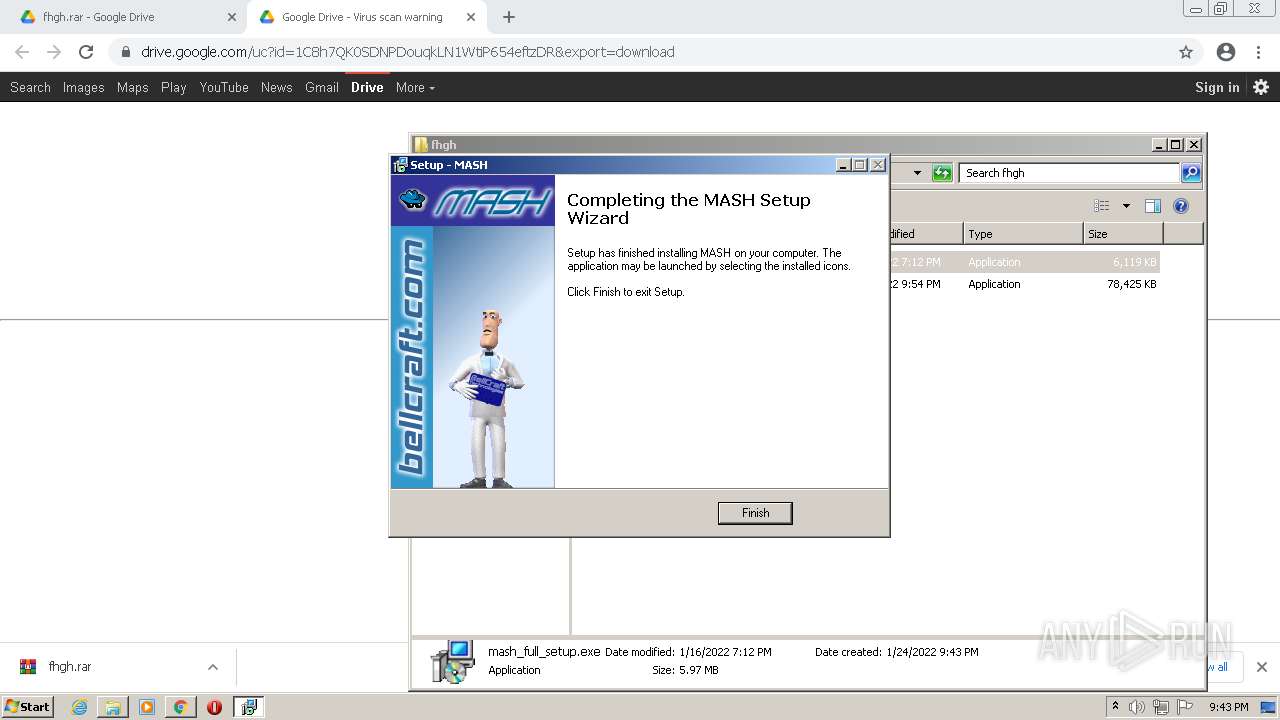
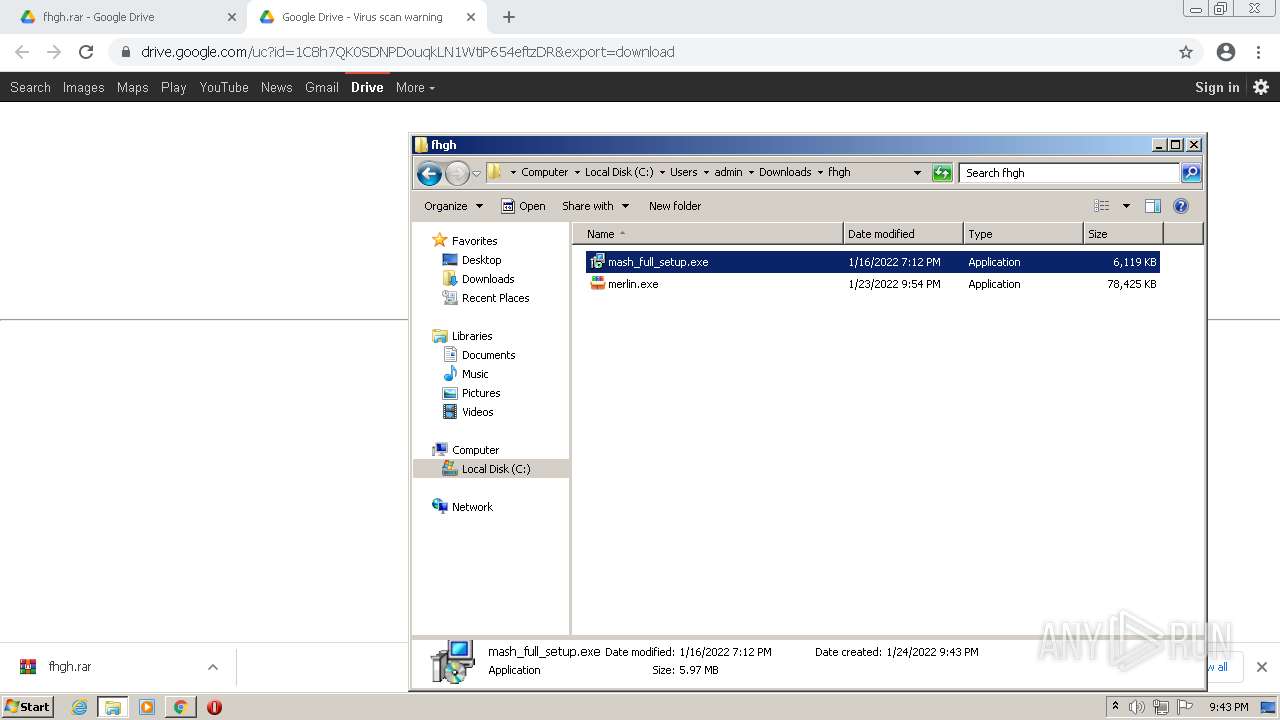
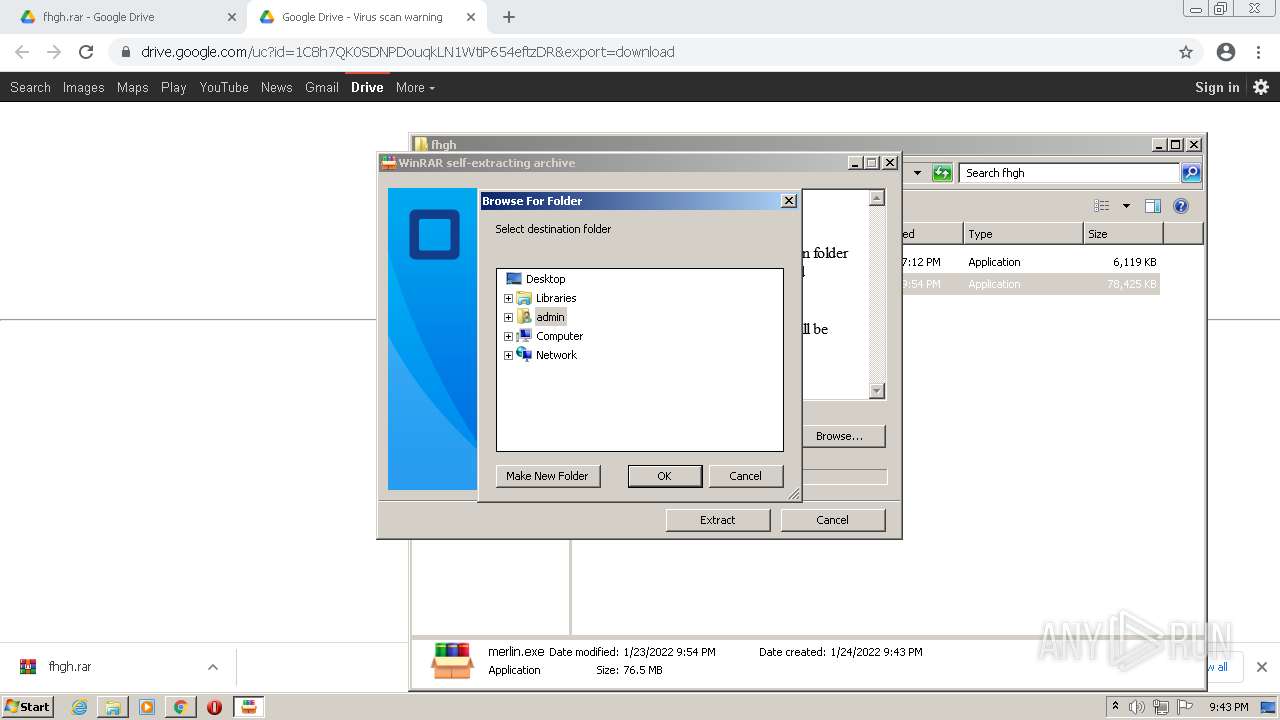
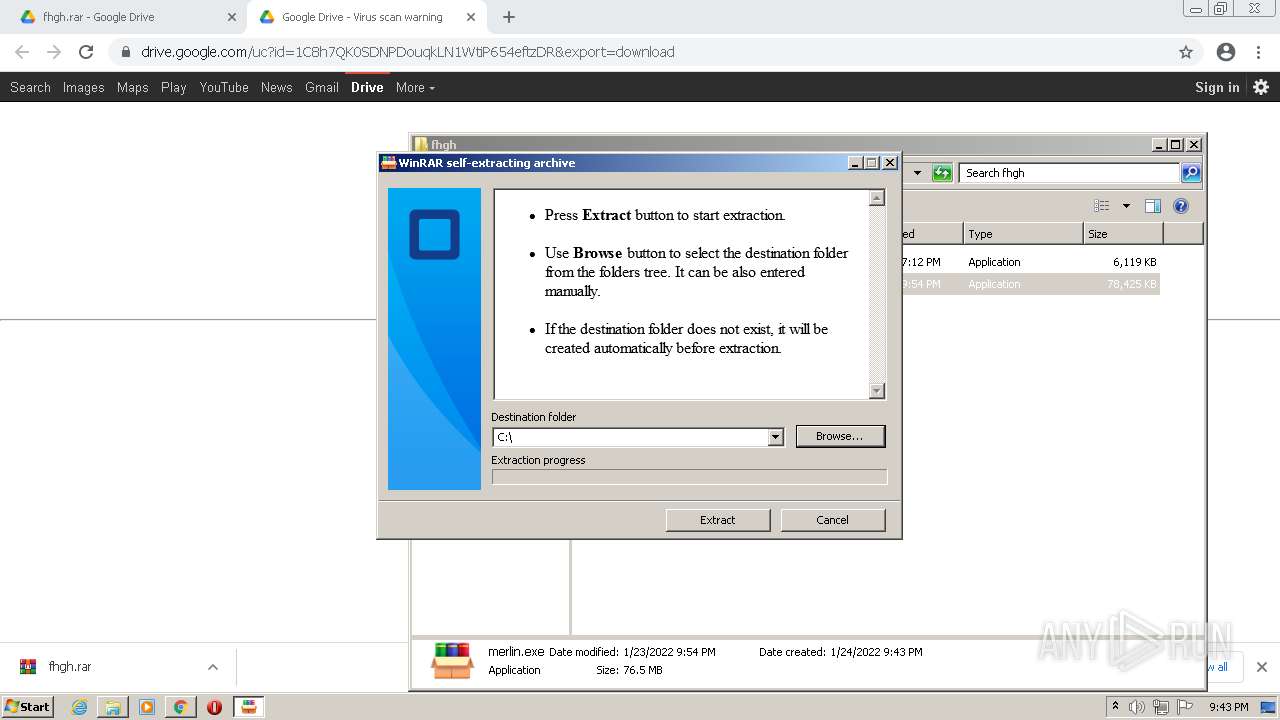
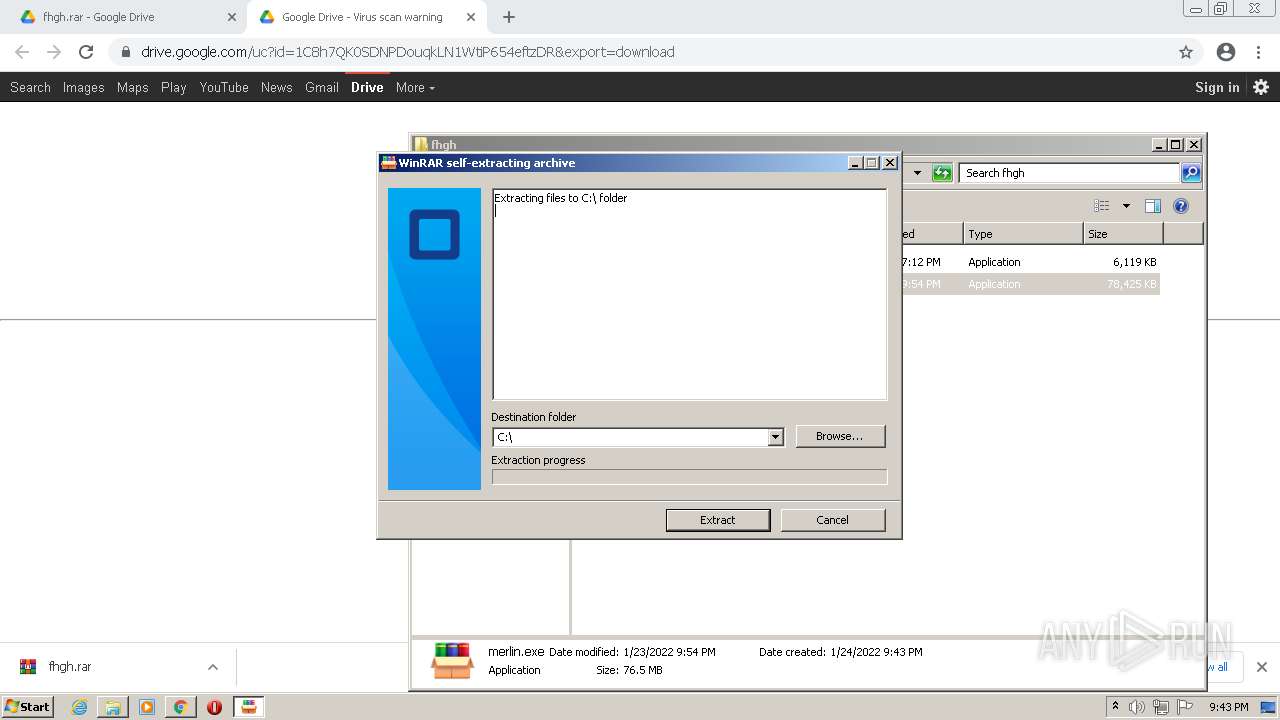
Manual execution by user
- WinRAR.exe (PID: 2600)
- mash_full_setup.exe (PID: 756)
- merlin.exe (PID: 304)
- cmd.exe (PID: 2880)
Checks Windows Trust Settings
- consent.exe (PID: 1260)
- consent.exe (PID: 2352)
- consent.exe (PID: 116)
- consent.exe (PID: 2252)
- consent.exe (PID: 2824)
- WScript.exe (PID: 3964)
- consent.exe (PID: 3620)
- iexplore.exe (PID: 1832)
- QQPlayer.exe (PID: 4080)
- WScript.exe (PID: 2272)
- WScript.exe (PID: 3468)
- WScript.exe (PID: 2884)
- consent.exe (PID: 2908)
- consent.exe (PID: 3548)
Application was dropped or rewritten from another process
- mash_full_setup.exe.tmp (PID: 3524)
- mash_full_setup.exe.tmp (PID: 3116)
- msagent.exe (PID: 3972)
- tv_enua.exe (PID: 2352)
- spchcpl.exe (PID: 1440)
Loads dropped or rewritten executable
- mash_full_setup.exe.tmp (PID: 3524)
- tv_enua.exe (PID: 2352)
- msagent.exe (PID: 3972)
- spchcpl.exe (PID: 1440)
- mash_full_setup.exe.tmp (PID: 3116)
Creates files in the program directory
- mash_full_setup.exe.tmp (PID: 3524)
Reads mouse settings
- regsvr32.exe (PID: 4032)
Creates a software uninstall entry
- mash_full_setup.exe.tmp (PID: 3524)
- tv_enua.exe (PID: 2352)
Reads CPU info
- runonce.exe (PID: 2148)
Dropped object may contain Bitcoin addresses
- QQPlayer.exe (PID: 3072)
- INSCD10.tmp (PID: 3696)
- QQPlayer.exe (PID: 1276)
Changes internet zones settings
- iexplore.exe (PID: 876)
Changes settings of System certificates
- iexplore.exe (PID: 1832)
Reads internet explorer settings
- iexplore.exe (PID: 1832)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1832)
Creates files in the user directory
- iexplore.exe (PID: 1832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
200
Monitored processes
167
Malicious processes
55
Suspicious processes
29
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | consent.exe 884 186 02343618 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
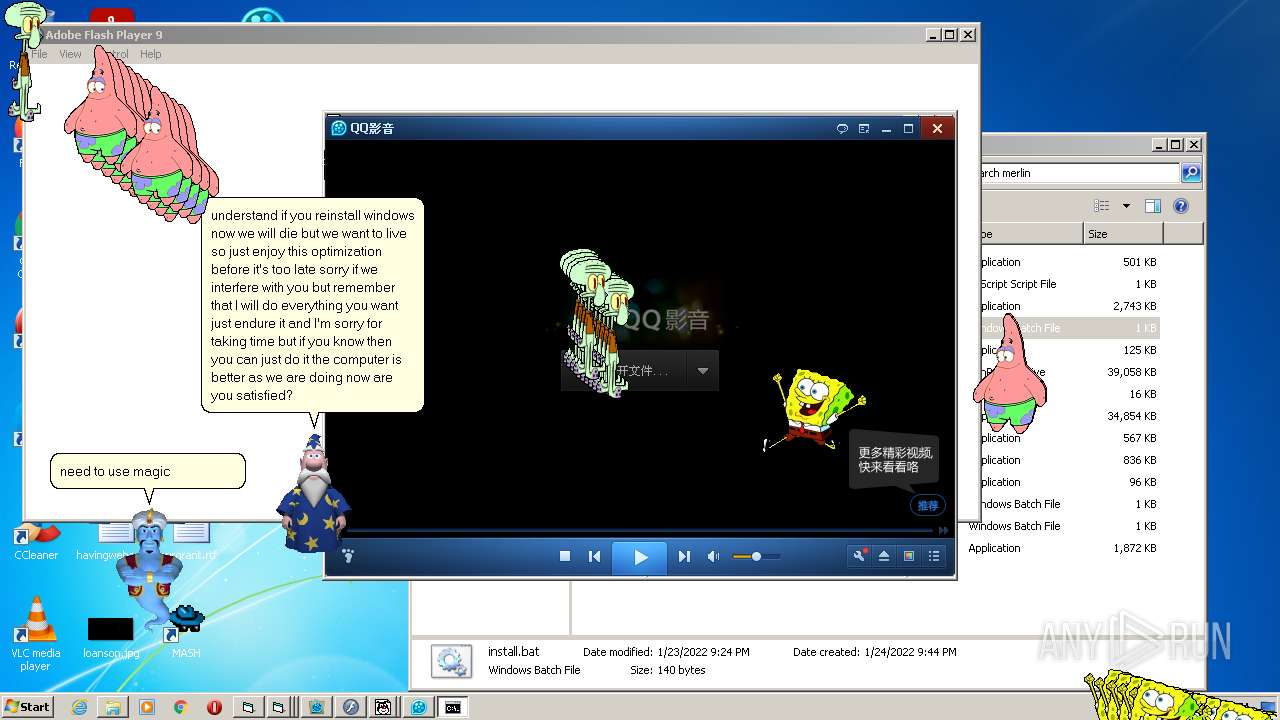
| 116 | SpongeBob_ScreenToy.exe | C:\merlin\SpongeBob_ScreenToy.exe | — | cmd.exe | |||||||||||
User: admin Company: Starfleet Academy Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3472 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 128 | regsvr32 /s "C:\Windows\msagent\AgentMPx.dll" | C:\Windows\system32\regsvr32.exe | — | msagent.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 288 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | "C:\Users\admin\Downloads\fhgh\merlin.exe" | C:\Users\admin\Downloads\fhgh\merlin.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 476 | C:\Windows\system32\DllHost.exe /Processid:{F9717507-6651-4EDB-BFF7-AE615179BCCF} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 480 | Flash.exe | C:\merlin\Flash.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
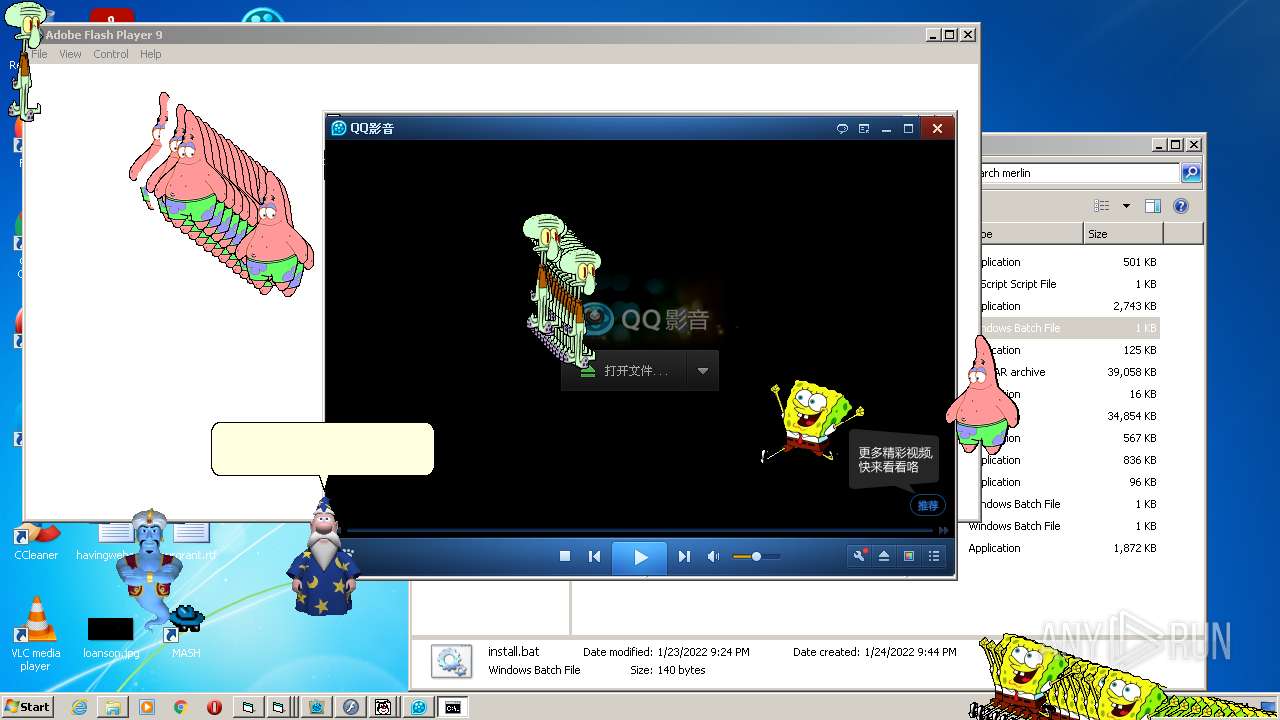
| 484 | "C:\Users\admin\AppData\Local\Temp\3582-490\Flash.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\Flash.exe | — | Flash.exe | |||||||||||
User: admin Company: Adobe Systems, Inc. Integrity Level: MEDIUM Description: Adobe Flash Player 9.0 r16 Exit code: 0 Version: 9,0,16,0 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3200 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
59 351
Read events
54 355
Write events
4 682
Delete events
314
Modification events
| (PID) Process: | (3756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3756) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
422
Suspicious files
107
Text files
435
Unknown types
74
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EF1D2E-EAC.pma | — | |
MD5:— | SHA256:— | |||
| 3756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f239d3c0-d335-40dc-855a-b00c8759f561.tmp | text | |
MD5:— | SHA256:— | |||
| 3756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF193389.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3156 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
112
TCP/UDP connections
164
DNS requests
64
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
884 | svchost.exe | HEAD | 200 | 74.125.97.71:80 | http://r2---sn-aigzrnld.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.46.147&mm=28&mn=sn-aigzrnld&ms=nvh&mt=1643060181&mv=m&mvi=2&pl=25&rmhost=r3---sn-aigzrnld.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | — | — | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.97.71:80 | http://r2---sn-aigzrnld.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.46.147&mm=28&mn=sn-aigzrnld&ms=nvh&mt=1643060181&mv=m&mvi=2&pl=25&rmhost=r3---sn-aigzrnld.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 43.2 Kb | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.97.71:80 | http://r2---sn-aigzrnld.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.46.147&mm=28&mn=sn-aigzrnld&ms=nvh&mt=1643060181&mv=m&mvi=2&pl=25&rmhost=r3---sn-aigzrnld.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 178 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.97.71:80 | http://r2---sn-aigzrnld.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.46.147&mm=28&mn=sn-aigzrnld&ms=nvh&mt=1643060181&mv=m&mvi=2&pl=25&rmhost=r3---sn-aigzrnld.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 9.45 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
836 | chrome.exe | 142.250.185.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
836 | chrome.exe | 142.250.186.174:443 | drive.google.com | Google Inc. | US | whitelisted |
836 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
836 | chrome.exe | 142.250.185.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
836 | chrome.exe | 142.250.186.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
836 | chrome.exe | 172.217.18.110:443 | apis.google.com | Google Inc. | US | whitelisted |
836 | chrome.exe | 142.250.181.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
836 | chrome.exe | 142.250.186.129:443 | doc-00-18-docs.googleusercontent.com | Google Inc. | US | whitelisted |
836 | chrome.exe | 142.250.74.202:443 | peoplestackwebexperiments-pa.clients6.google.com | Google Inc. | US | whitelisted |
836 | chrome.exe | 142.250.185.142:443 | docs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
drive.google.com |
| shared |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
content.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4080 | QQPlayer.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
4080 | QQPlayer.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
4080 | QQPlayer.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
Process | Message |
|---|---|
AgentSvr.exe |
++++++ ITTSCentral::Release() Called ++++++
|
AgentSvr.exe |
++++++ ITTSCentral::Release() Called ++++++
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|