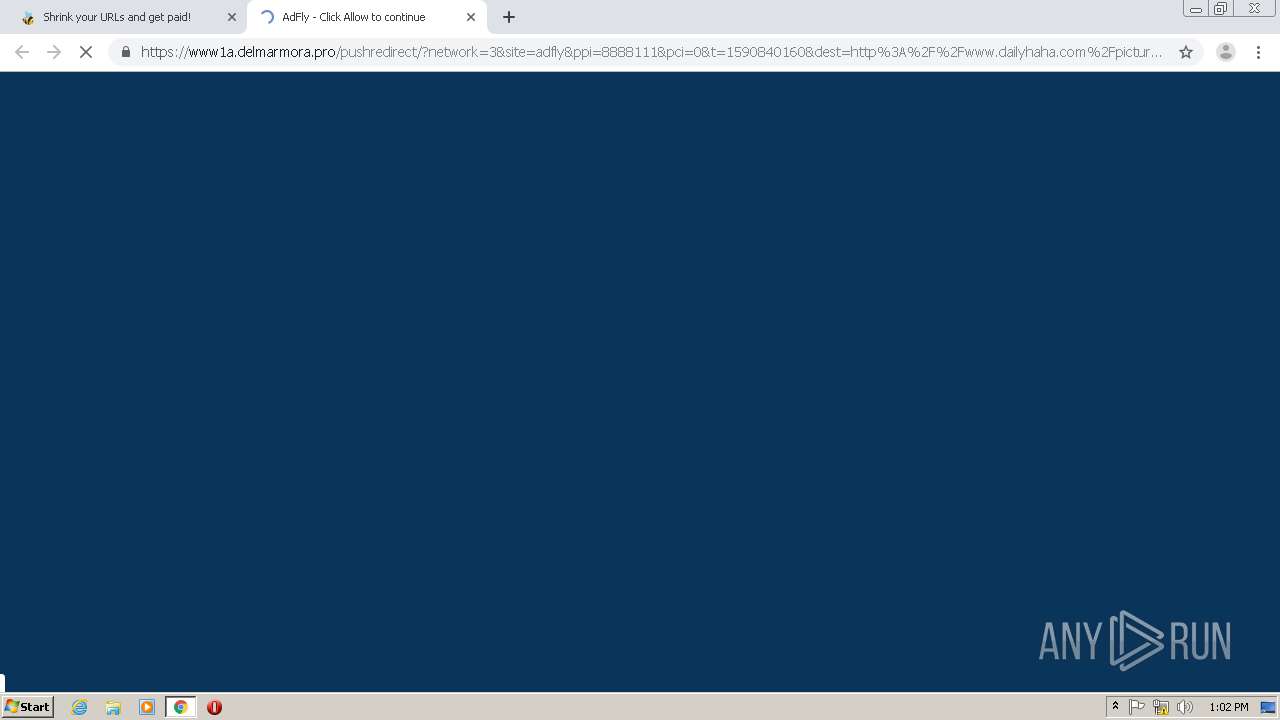
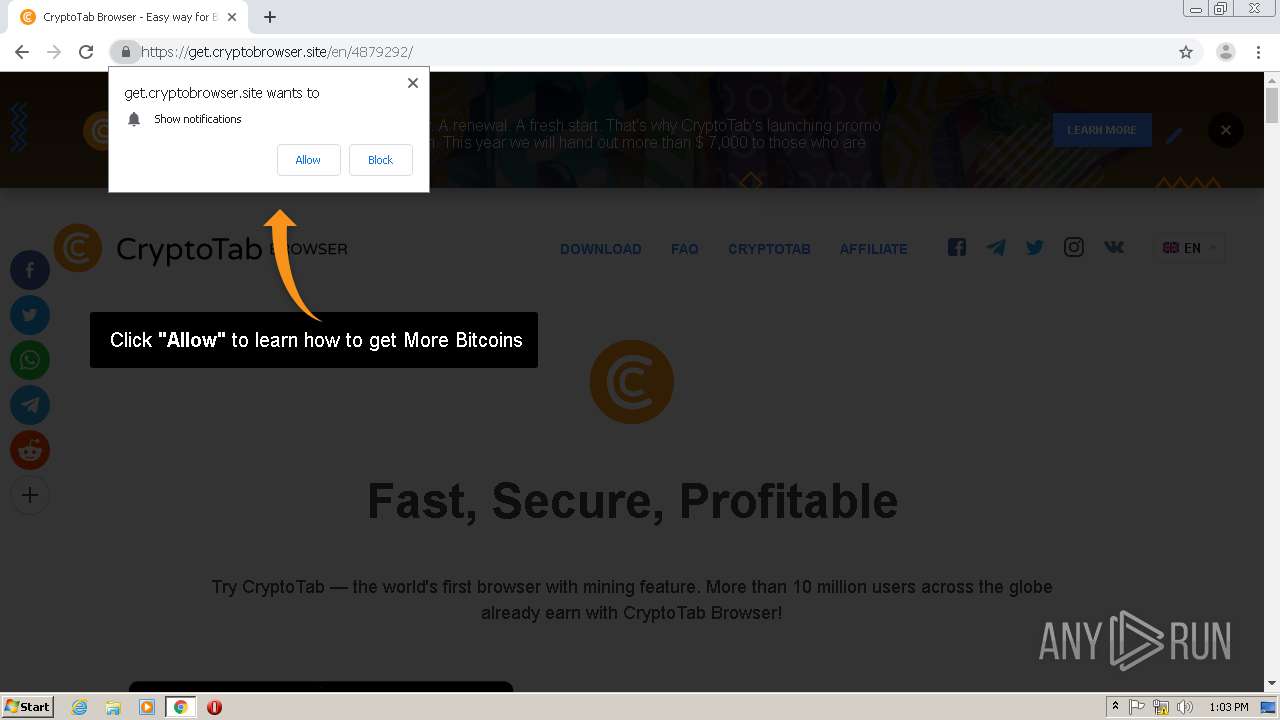
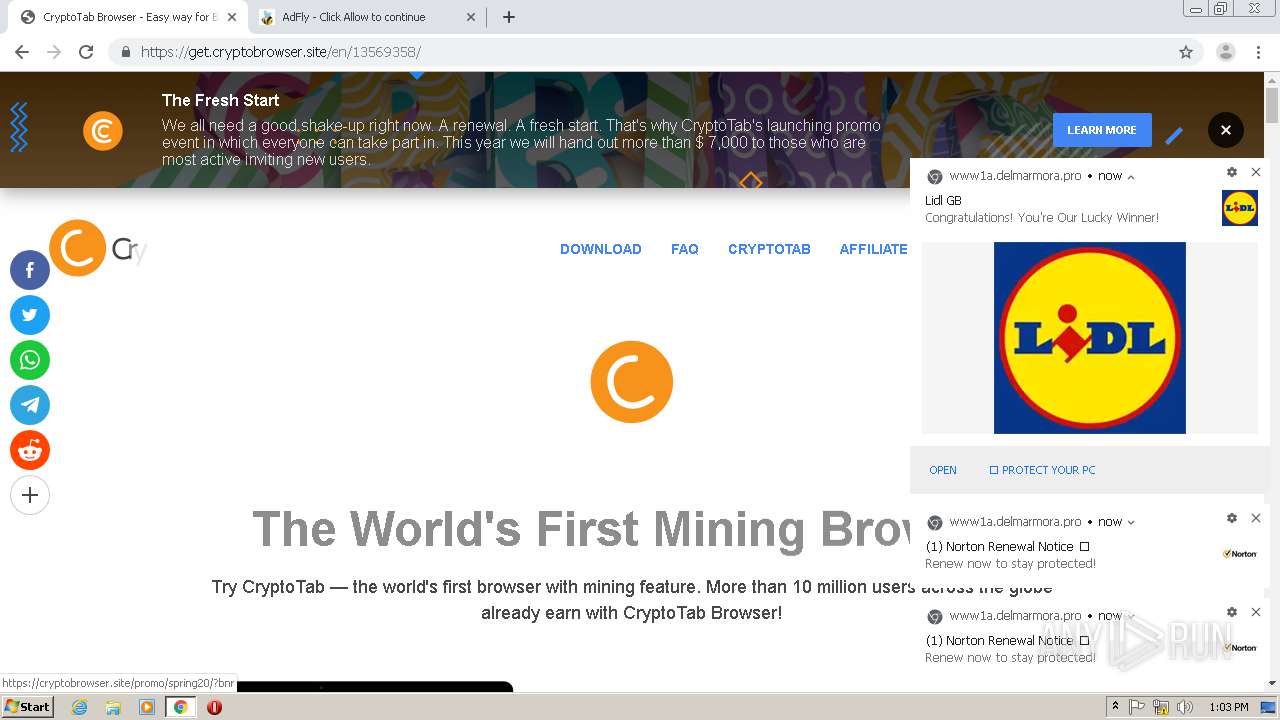
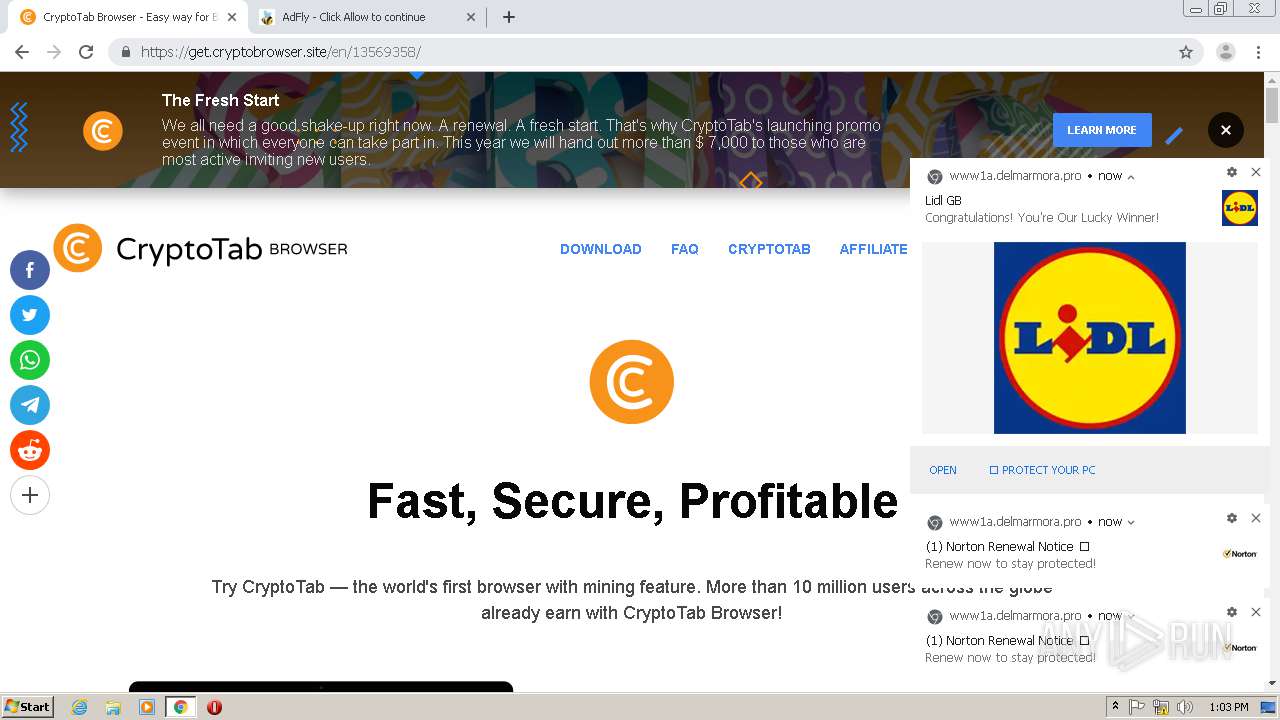
| URL: | http://tinyurl.com/y8q76aaq |
| Full analysis: | https://app.any.run/tasks/e05d40ed-9404-42ff-9fbf-293e97e895d8 |
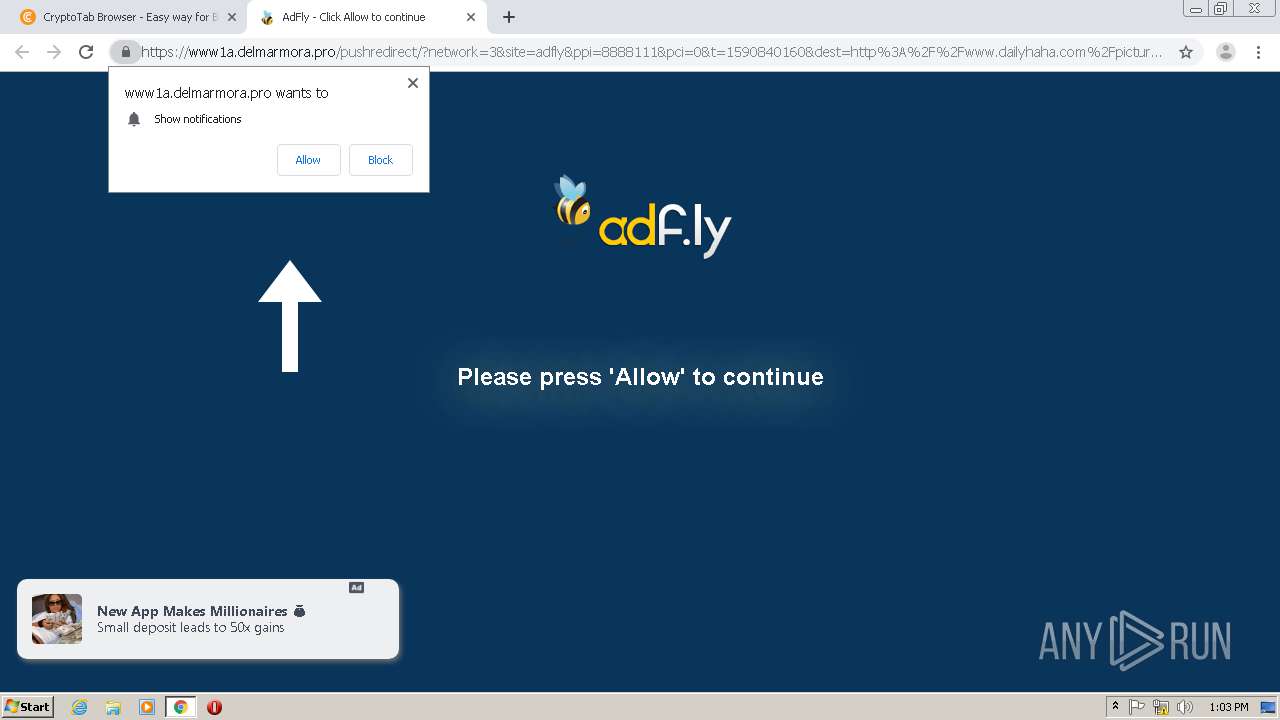
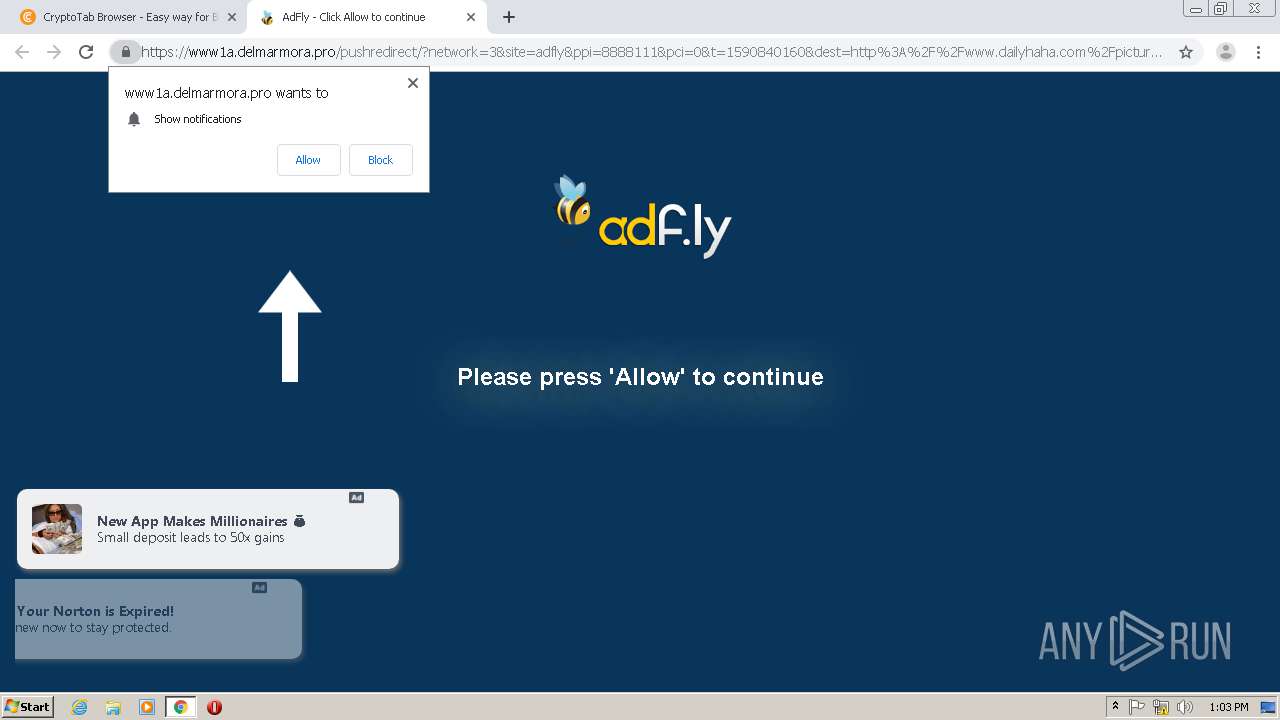
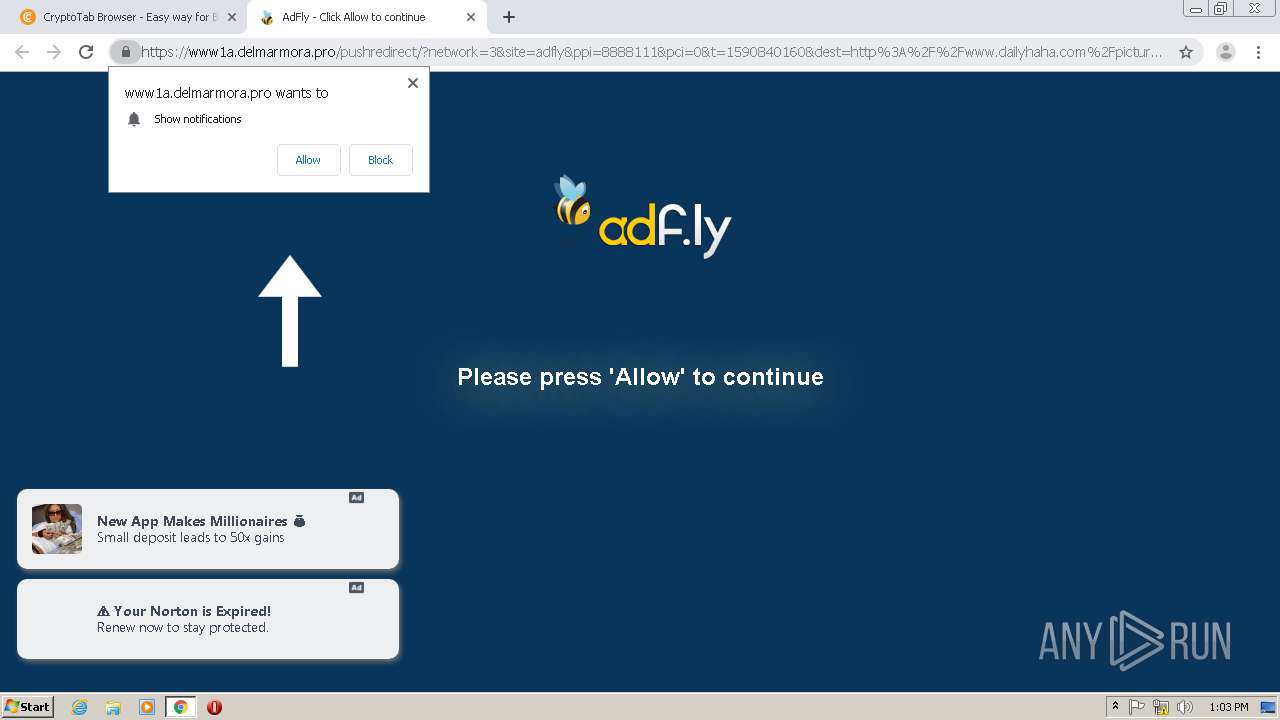
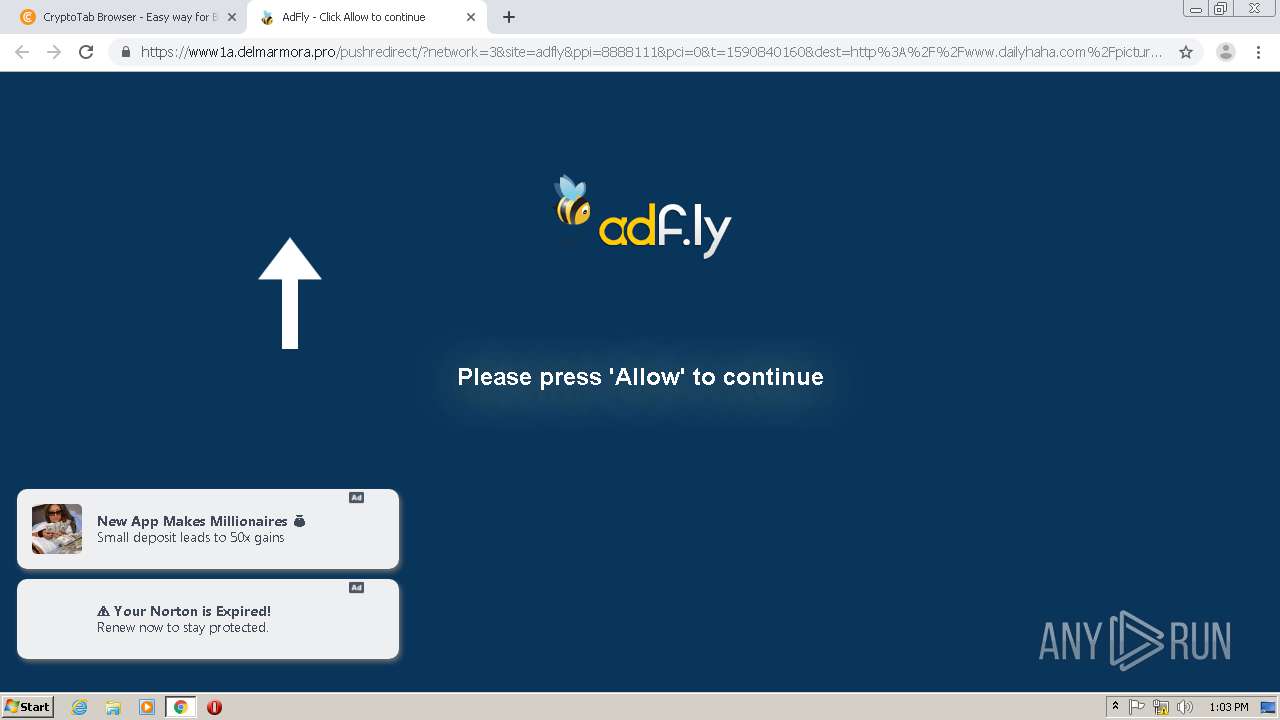
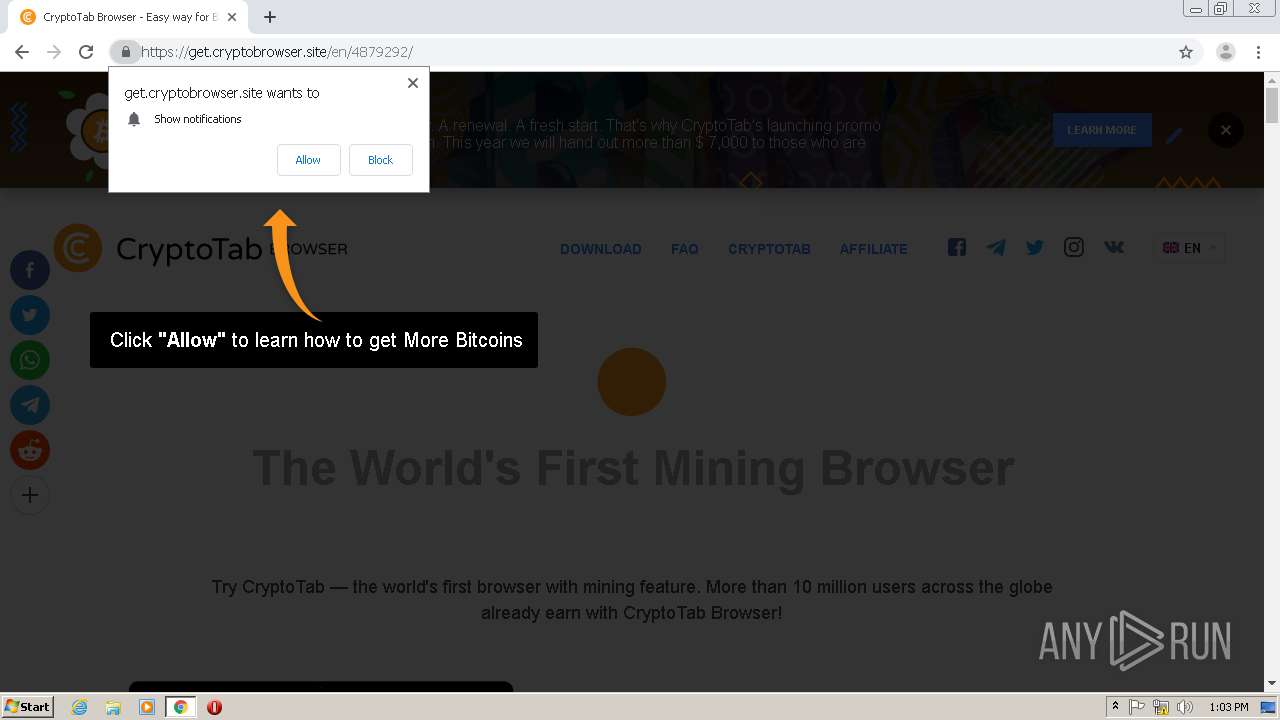
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 12:02:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CC517D5CF279FC56D0DA45B82837F1A5 |
| SHA1: | 1582E6357AFC06B2B37EF4F355D004B0AB0107C7 |
| SHA256: | 81A66D5AAB5682D8A728E0A554B8A3C7F1ED1DFA61A0596DC3B4FCA1AEBAB691 |
| SSDEEP: | 3:N1KKMzLdIHPU:CKwdsPU |
MALICIOUS
No malicious indicators.SUSPICIOUS
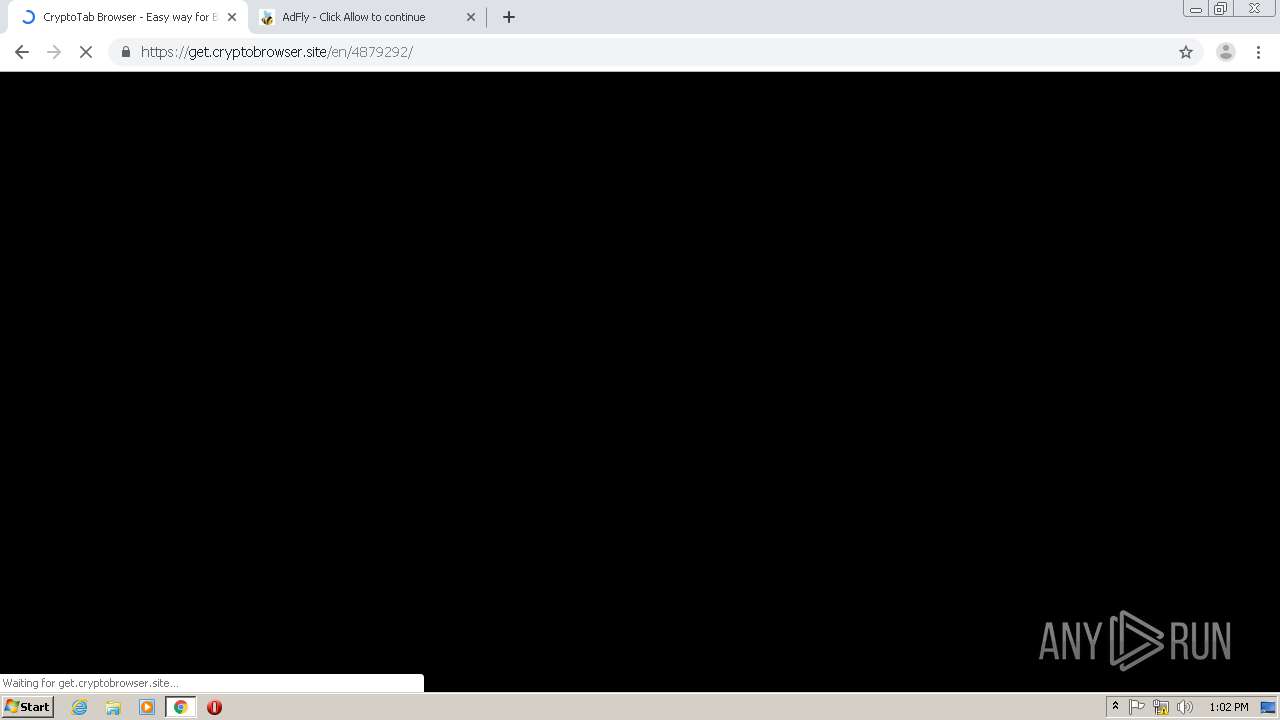
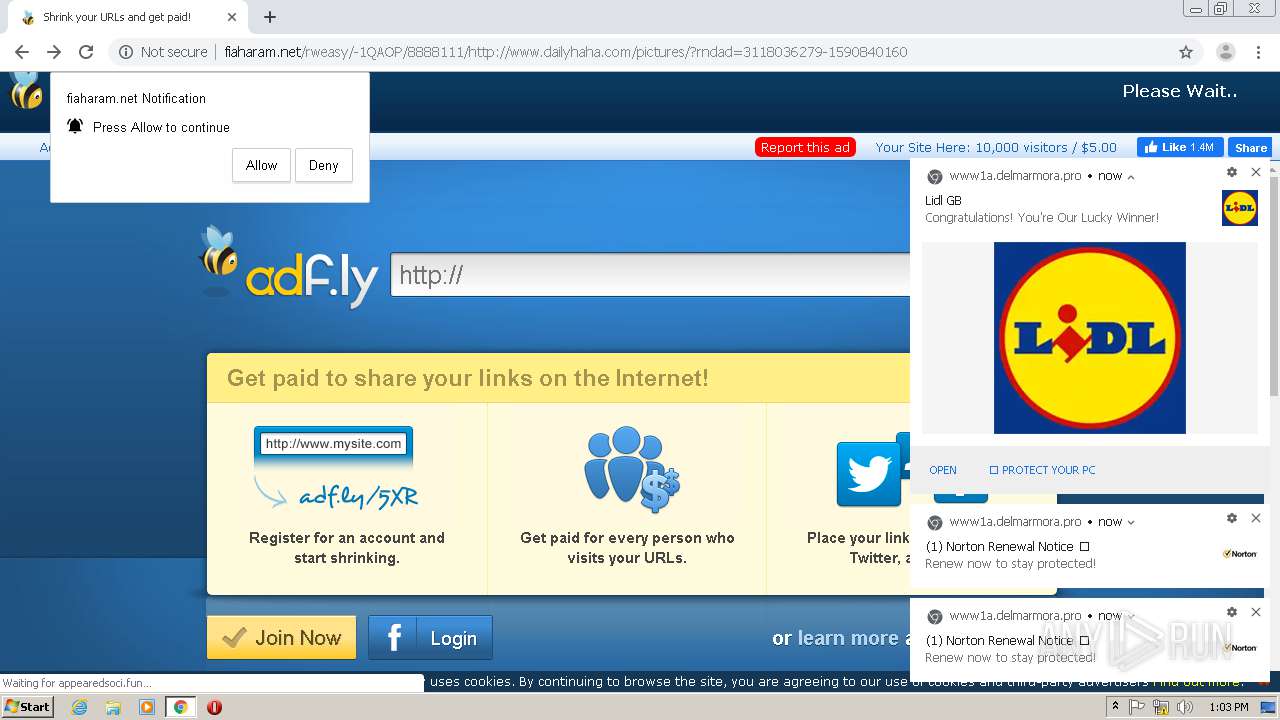
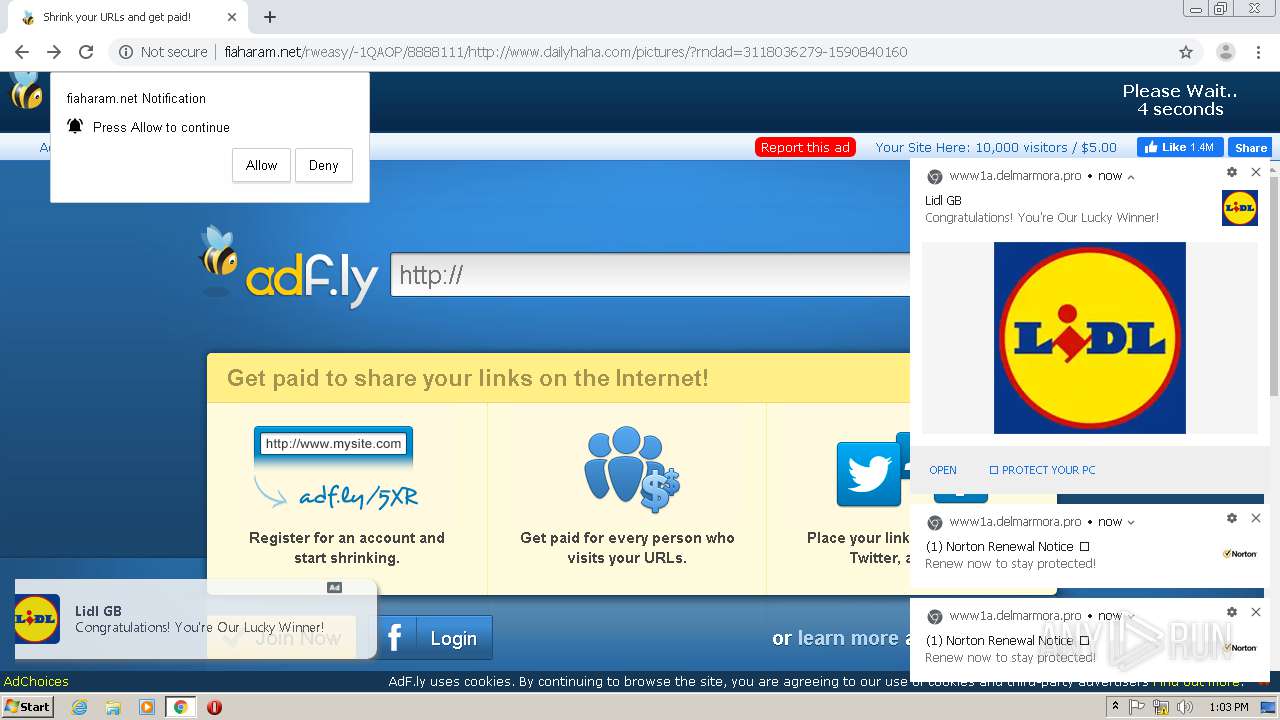
Modifies files in Chrome extension folder
- chrome.exe (PID: 2284)
INFO
Reads the hosts file
- chrome.exe (PID: 2056)
- chrome.exe (PID: 2284)
Application launched itself
- chrome.exe (PID: 2284)
Reads settings of System Certificates
- chrome.exe (PID: 2056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
45
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5128977686740457921,17987784577065018060,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16735318981428497130 --mojo-platform-channel-handle=3872 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5128977686740457921,17987784577065018060,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10178366711080301798 --mojo-platform-channel-handle=4032 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5128977686740457921,17987784577065018060,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9533650439057588918 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5128977686740457921,17987784577065018060,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7589496530151729632 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5128977686740457921,17987784577065018060,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16805855646692766249 --mojo-platform-channel-handle=4420 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2168 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5128977686740457921,17987784577065018060,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10256784816852376835 --mojo-platform-channel-handle=4372 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5128977686740457921,17987784577065018060,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15510827942077217620 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5128977686740457921,17987784577065018060,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15376144913388866906 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5128977686740457921,17987784577065018060,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15937702122725112066 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
695
Read events
587
Write events
103
Delete events
5
Modification events
| (PID) Process: | (2284) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2284) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2284) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2284) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2284) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2284) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2284) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2284) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2284) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2284) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2284-13235313756903875 |
Value: 259 | |||
Executable files
0
Suspicious files
158
Text files
202
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED24B5D-8EC.pma | — | |
MD5:— | SHA256:— | |||
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9ff0a9fe-e81b-4394-b5a6-022ec0c586c7.tmp | — | |
MD5:— | SHA256:— | |||
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20a2bc.TMP | text | |
MD5:— | SHA256:— | |||
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF20a29d.TMP | text | |
MD5:— | SHA256:— | |||
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2284 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF20a491.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
95
DNS requests
65
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
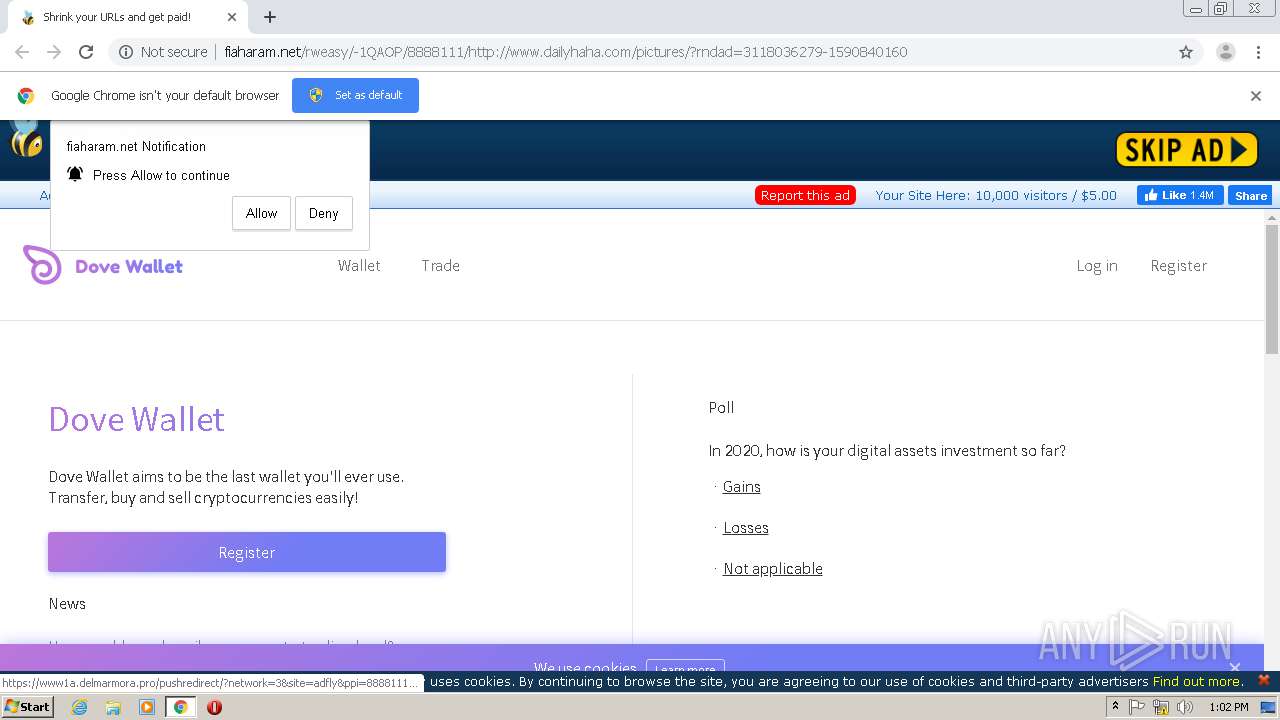
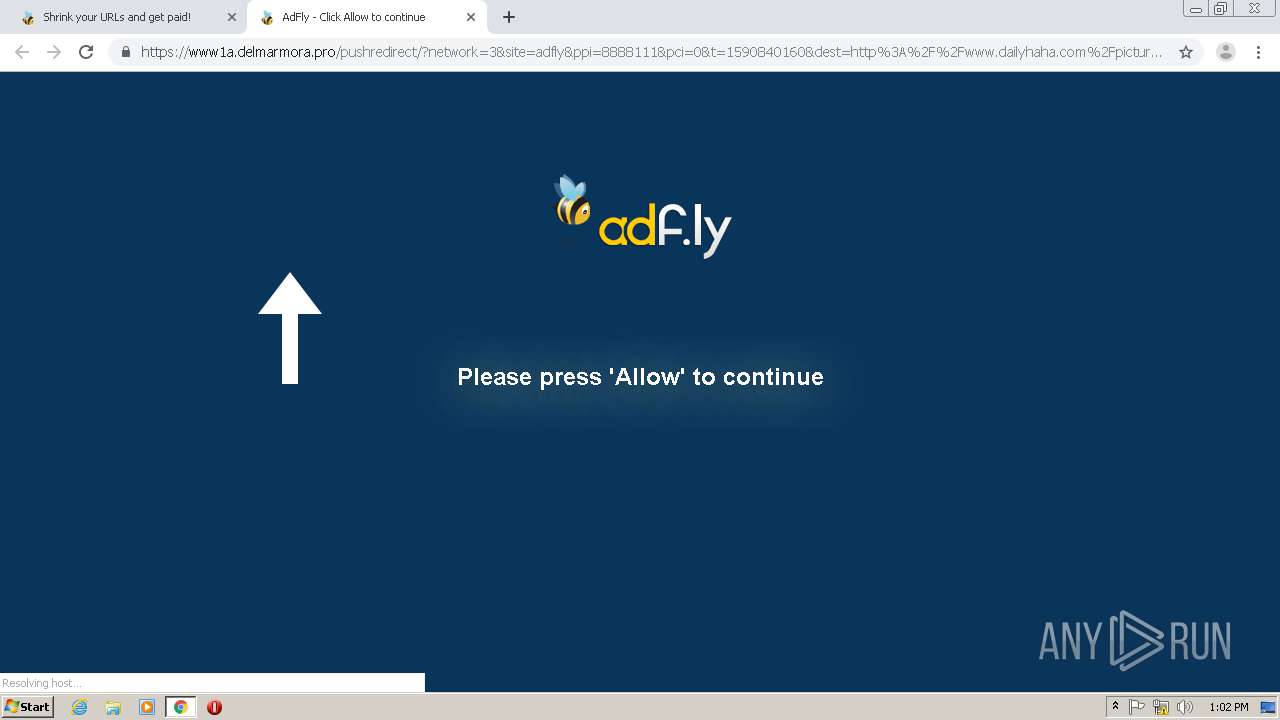
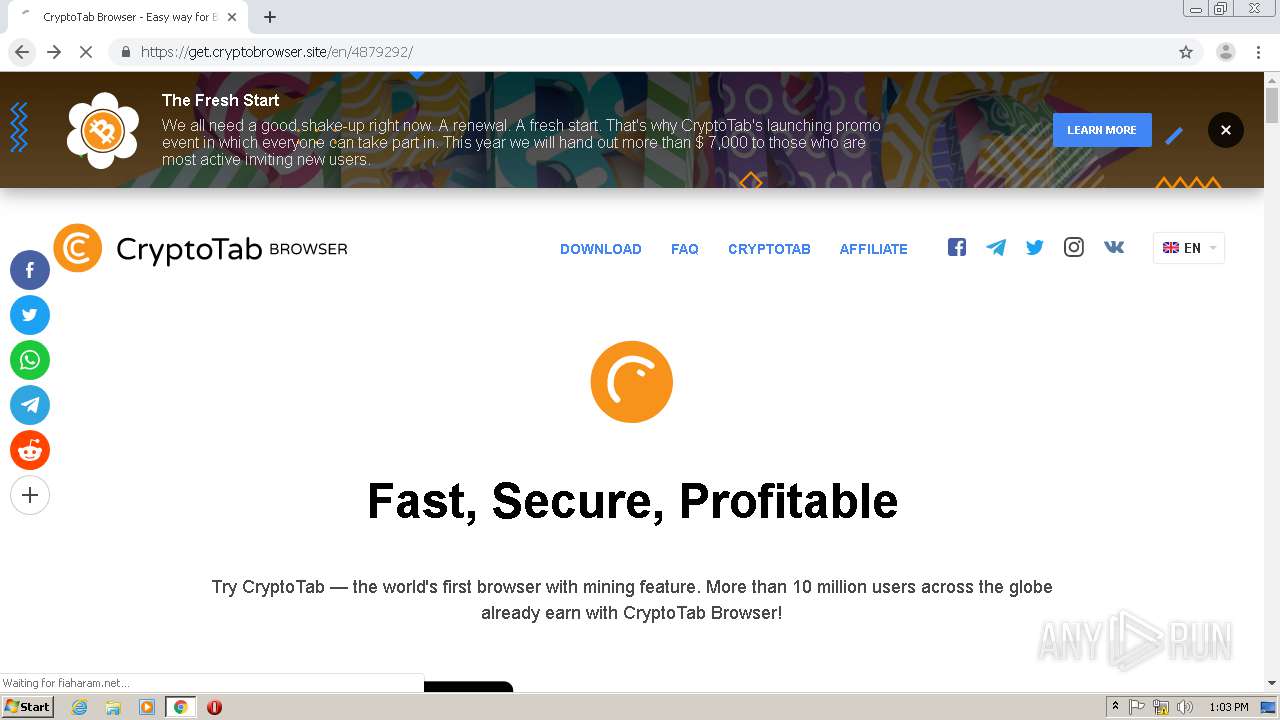
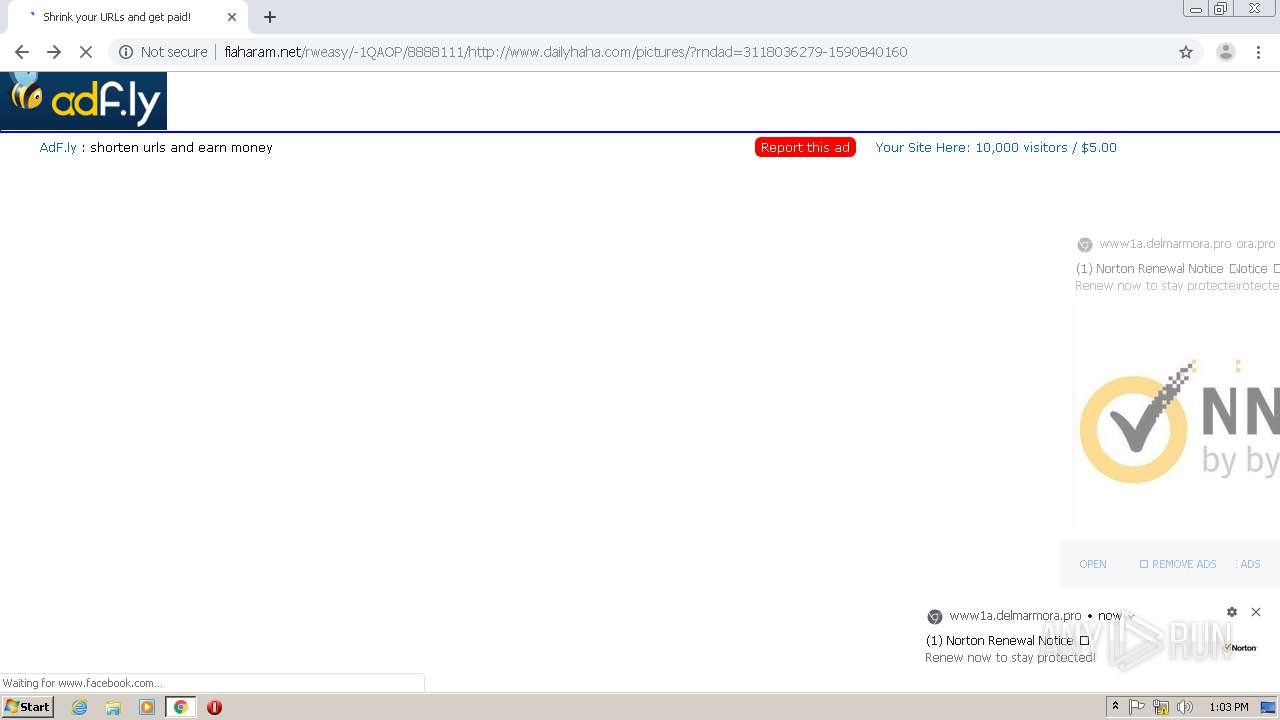
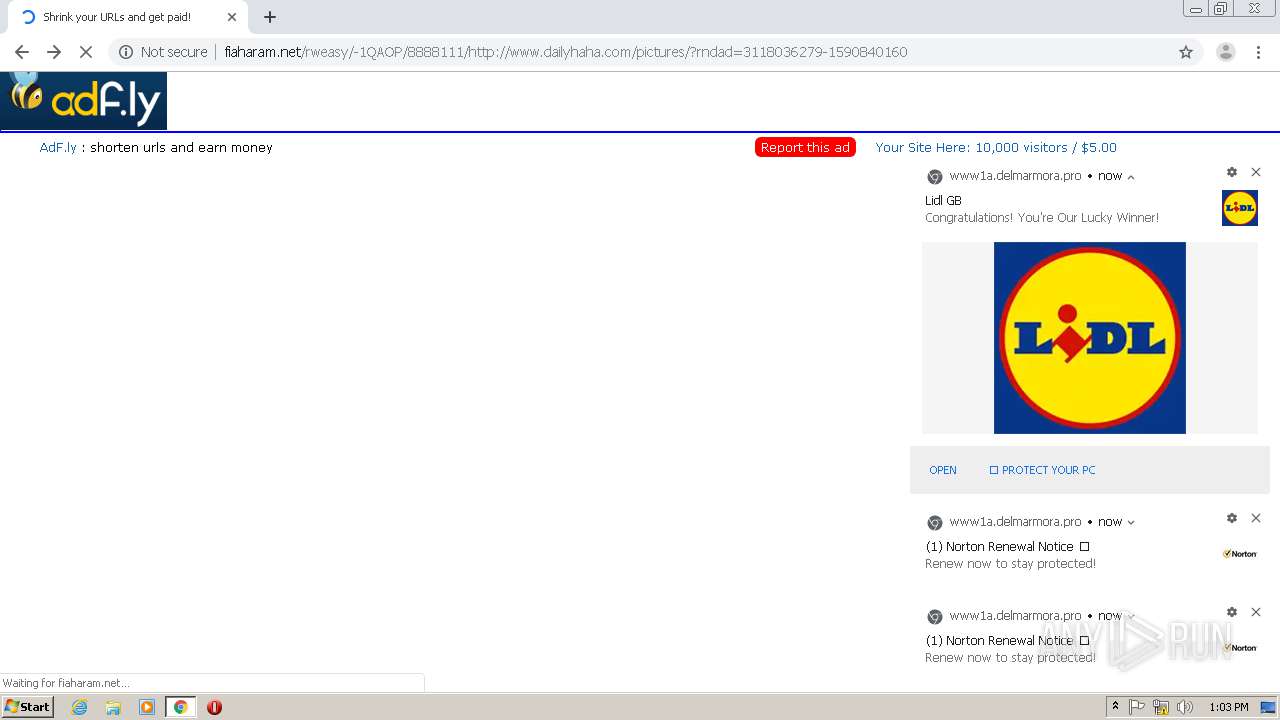
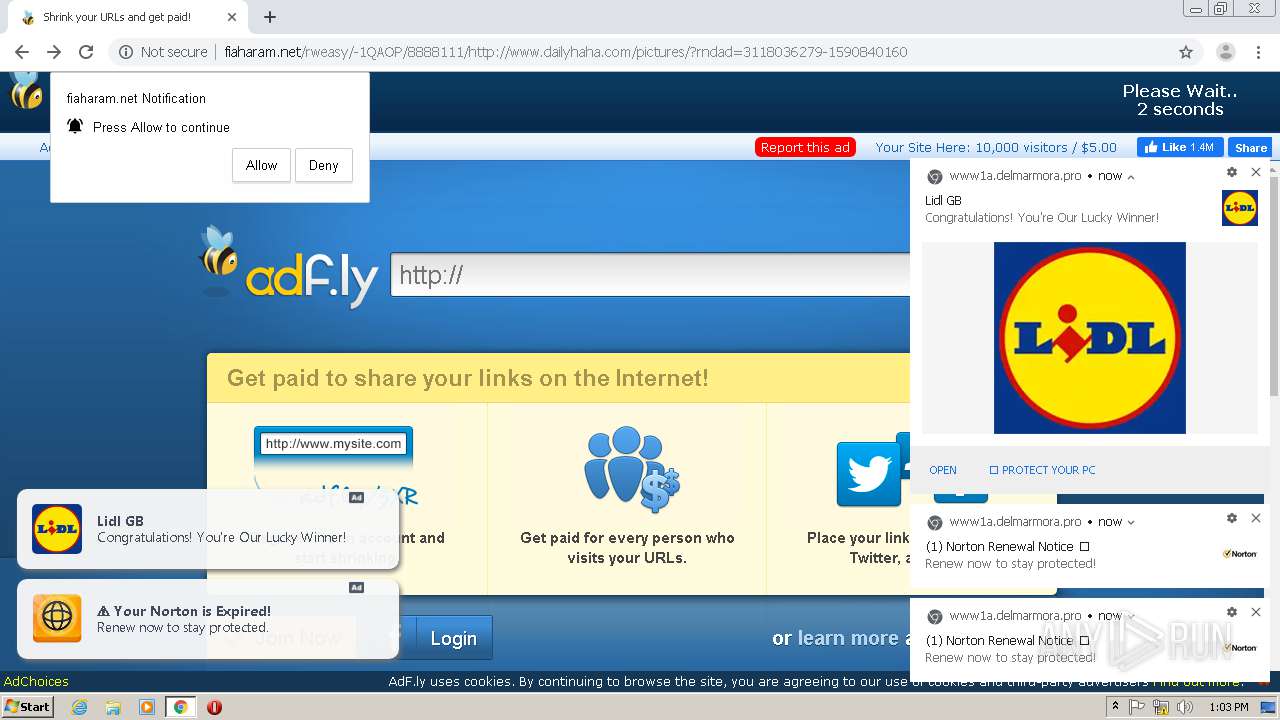
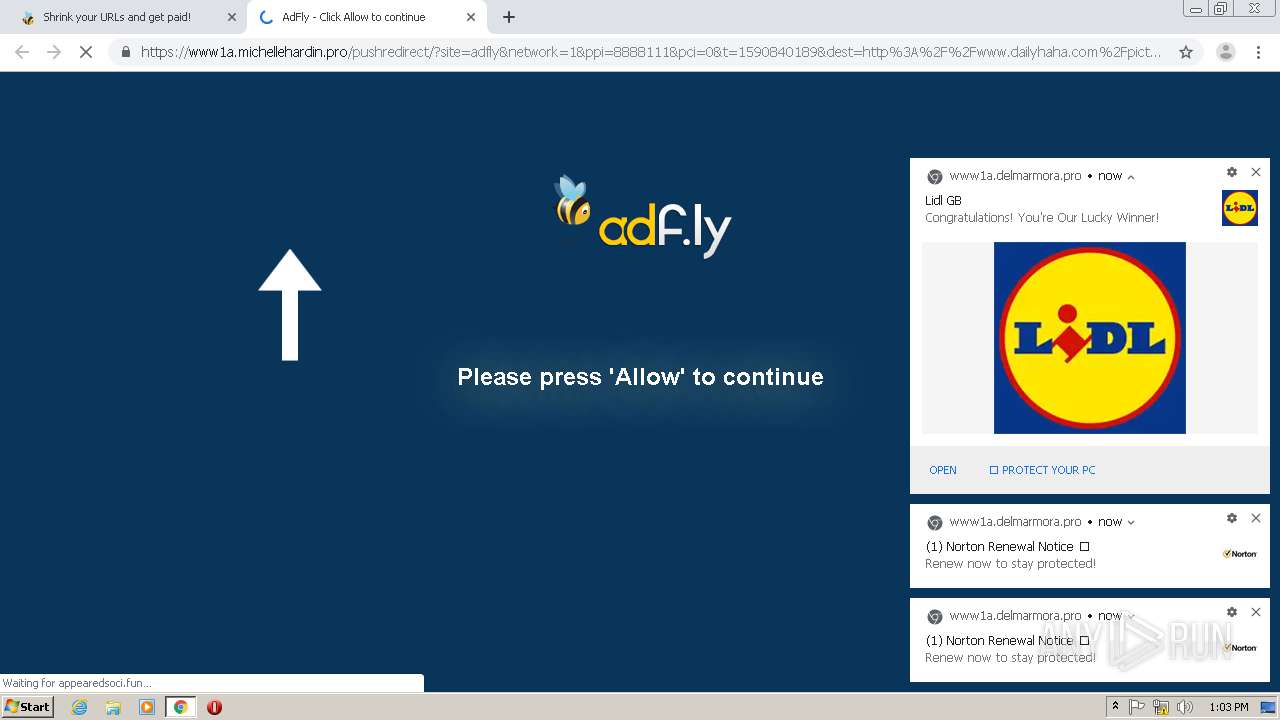
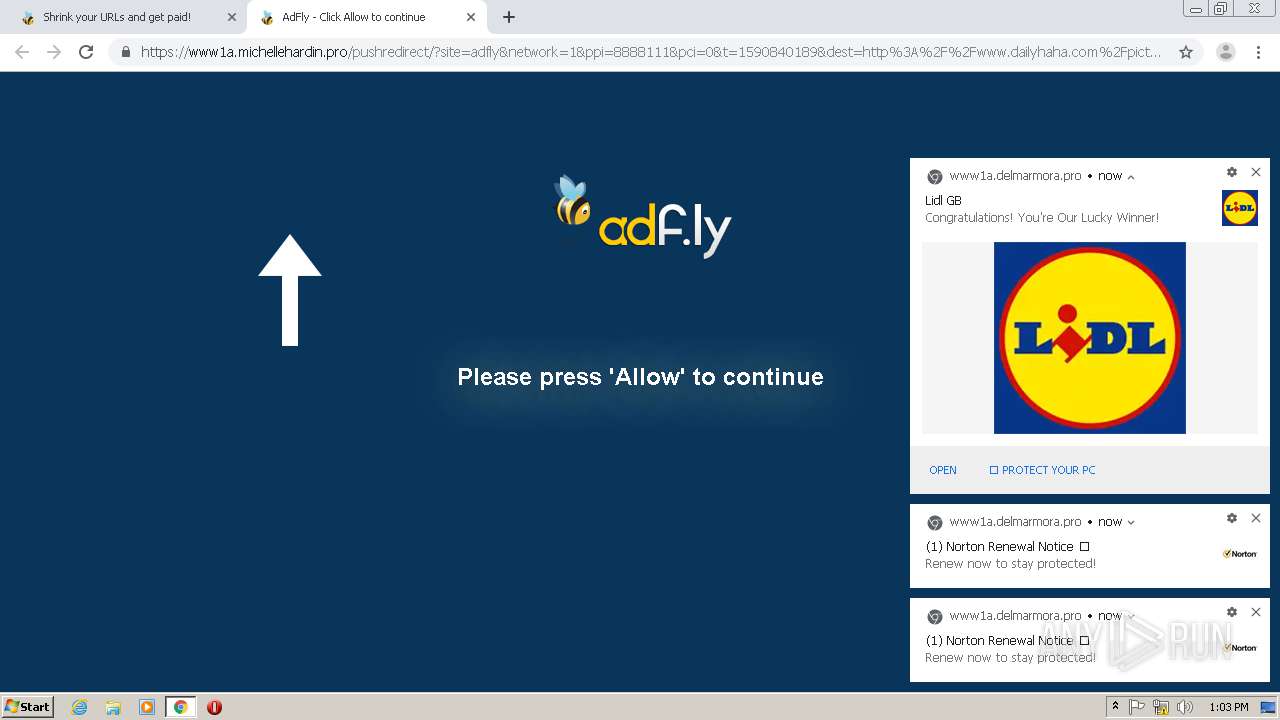
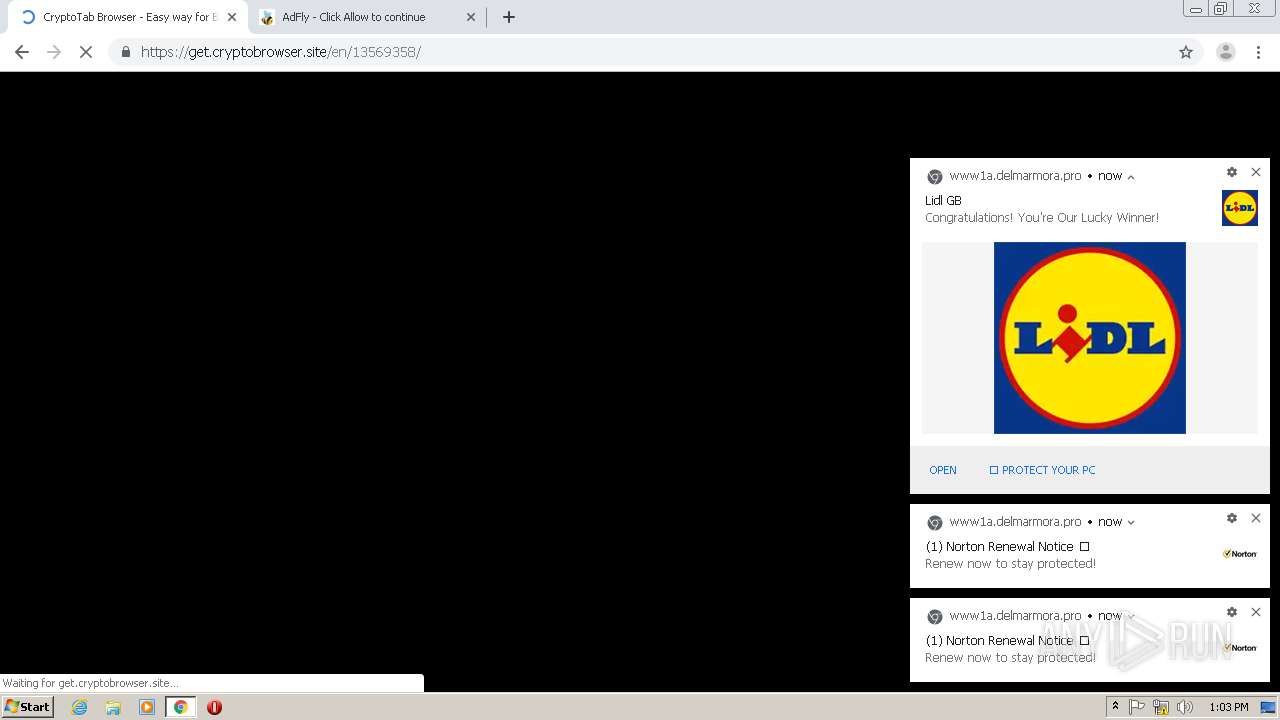
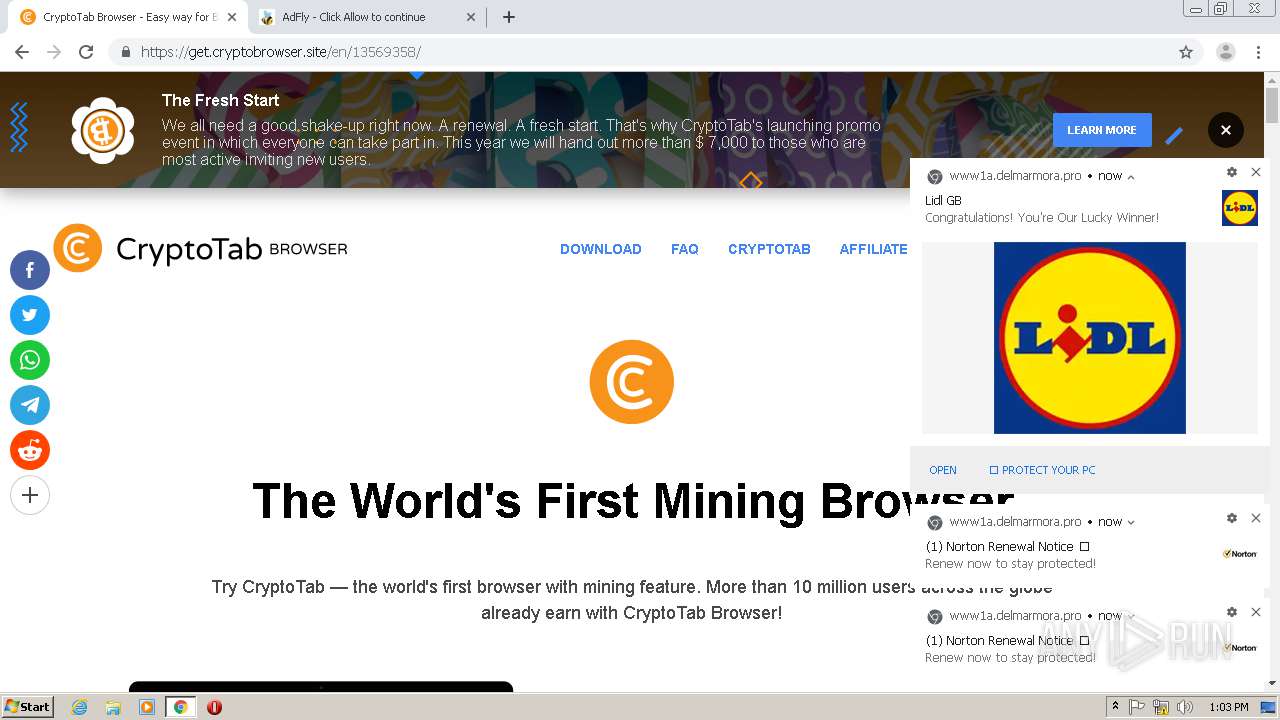
2056 | chrome.exe | GET | 301 | 104.20.82.199:80 | http://adf.ly/8888111/http://www.dailyhaha.com/pictures/ | US | — | — | shared |
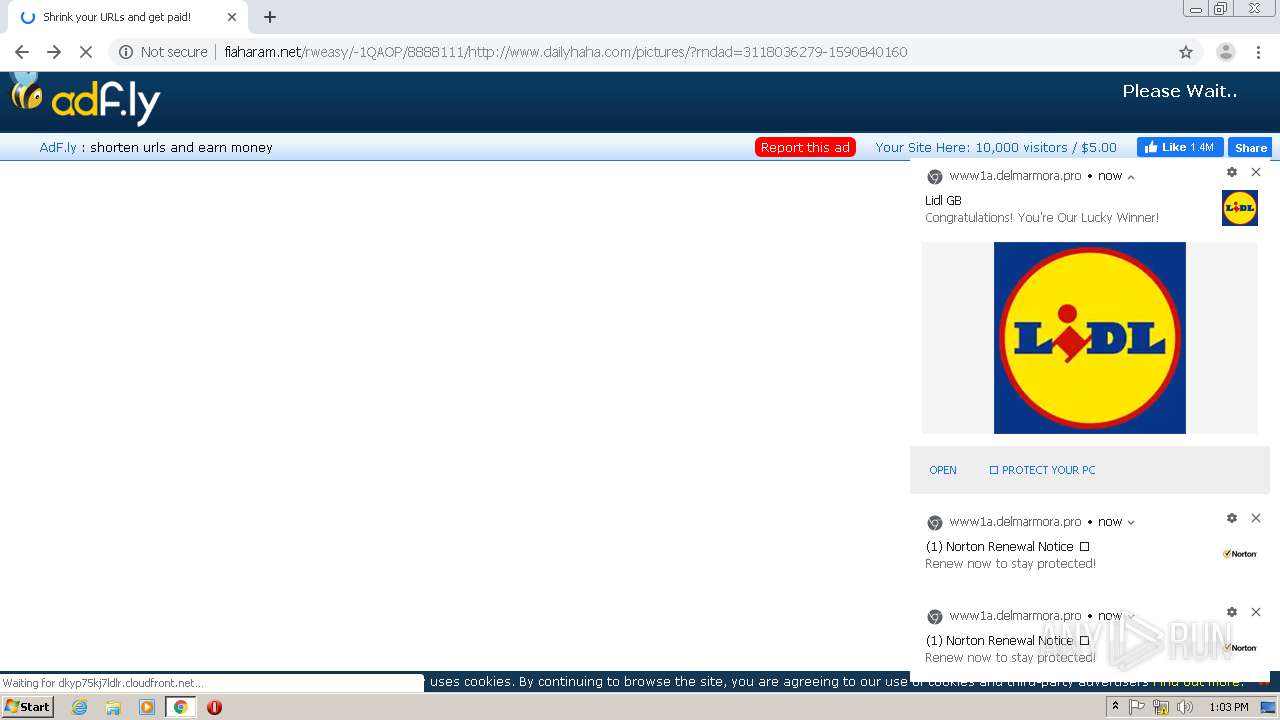
2056 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://cdn.fiaharam.net/static/js/b64.js | US | text | 1.07 Kb | whitelisted |
2056 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://cdn.fiaharam.net/static/js/view111.js | US | text | 28.1 Kb | whitelisted |
2056 | chrome.exe | GET | 301 | 104.19.248.53:80 | http://tinyurl.com/y8q76aaq | US | html | 522 b | shared |
2056 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://cdn.fiaharam.net/static/js/amvn.js | US | text | 146 Kb | whitelisted |
2056 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://cdn.fiaharam.net/static/css/adfly_7.css | US | text | 869 b | whitelisted |
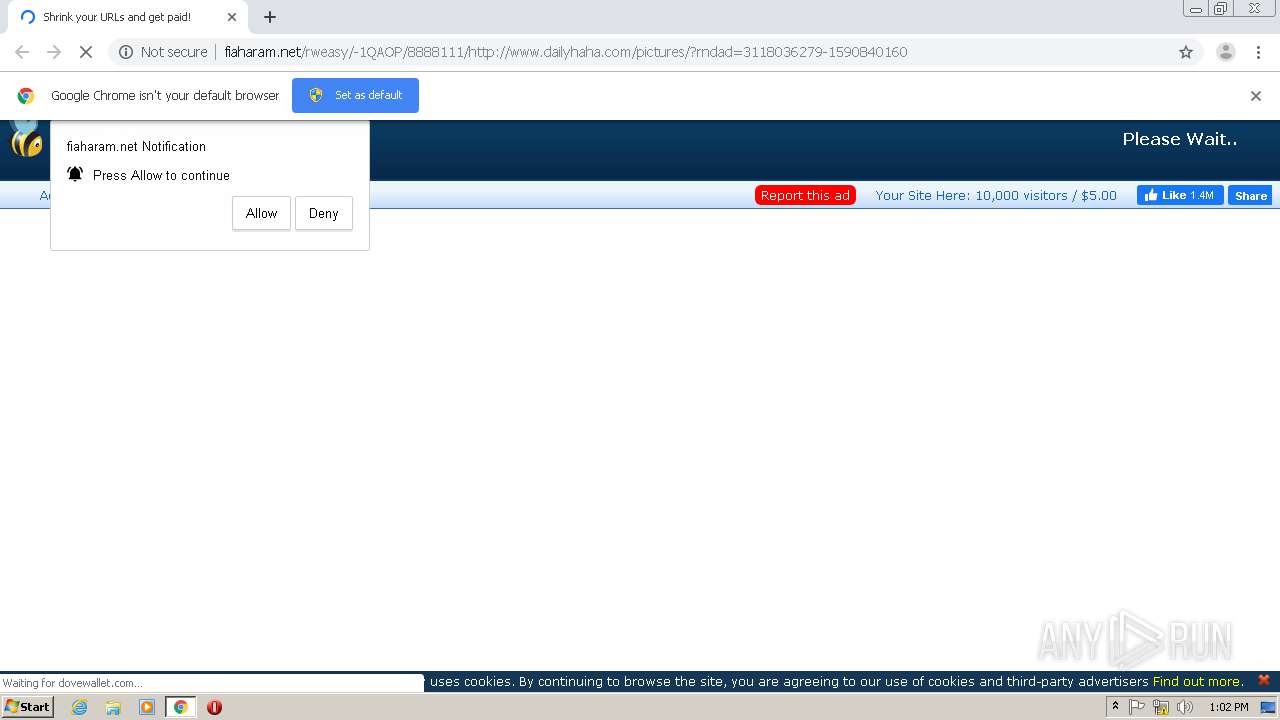
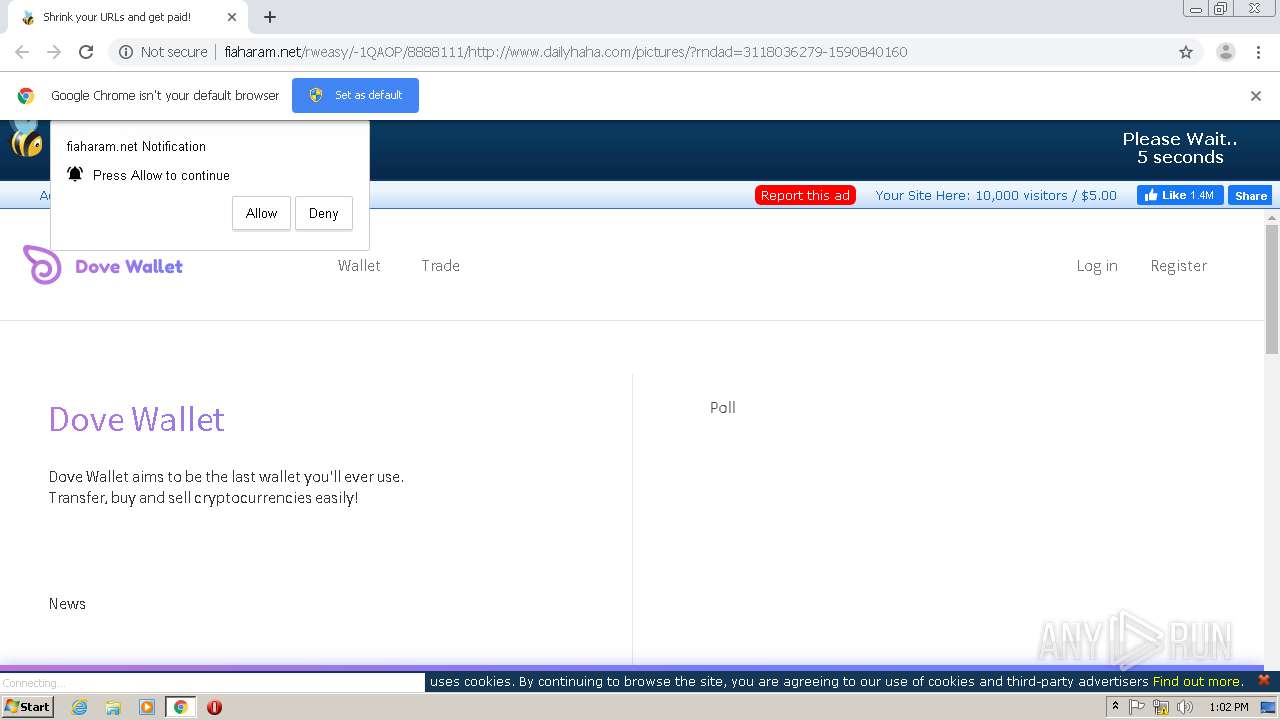
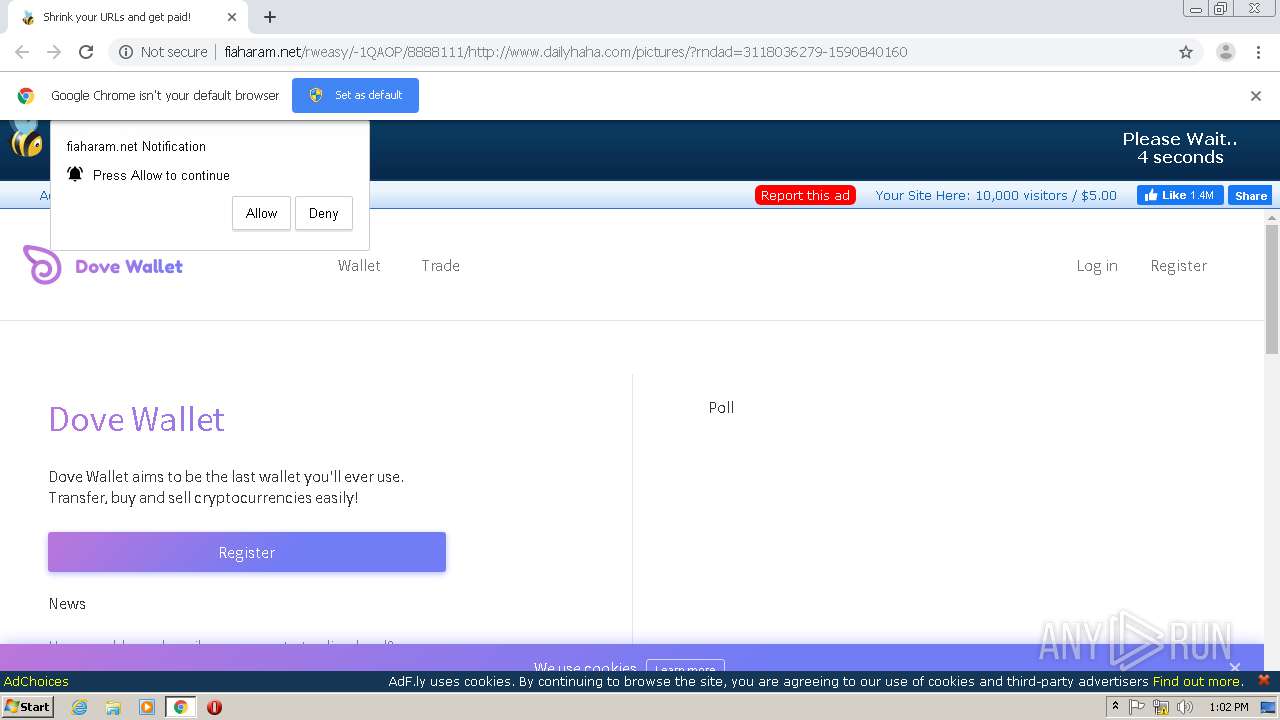
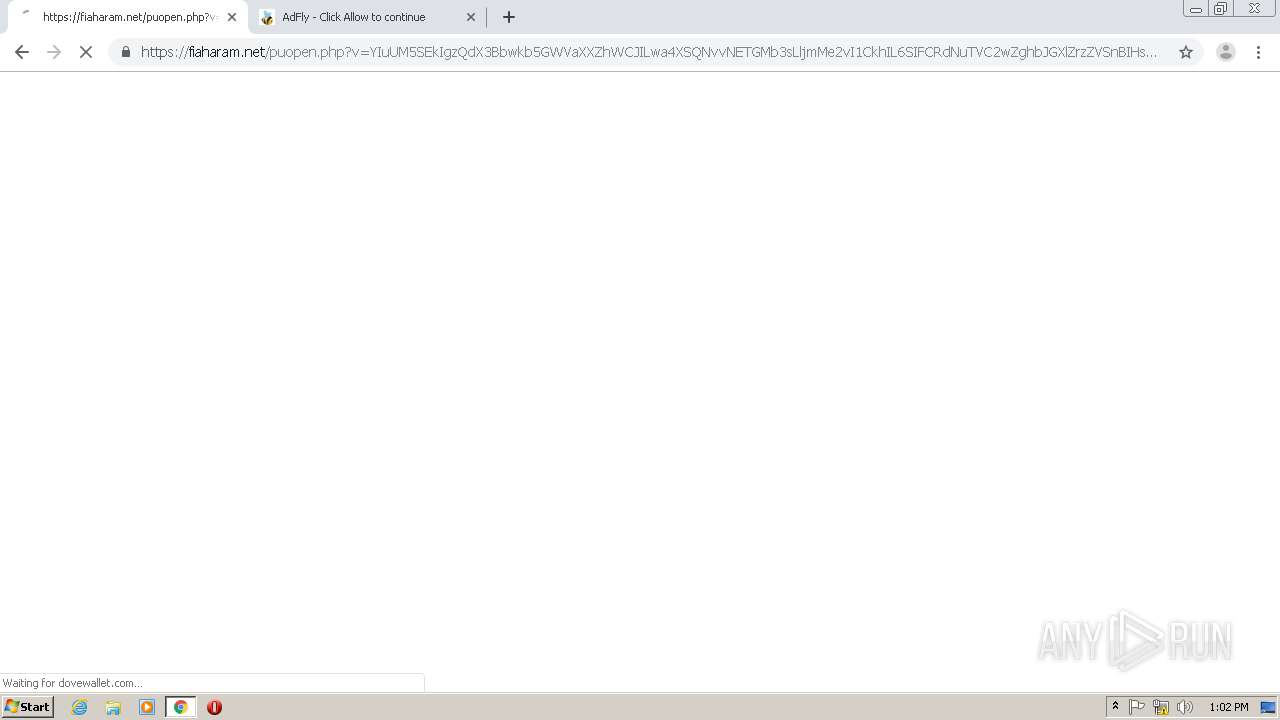
2056 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://fiaharam.net/rweasy/-1QAOP/8888111/http://www.dailyhaha.com/pictures/?rndad=3118036279-1590840160 | US | html | 5.69 Kb | whitelisted |
2056 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://cdn.fiaharam.net/static/js/main.js | US | text | 667 b | whitelisted |
2056 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://fiaharam.net/fp.rev11.php?ver=8888111&nocache=2244 | US | text | 12.7 Kb | whitelisted |
2056 | chrome.exe | GET | 200 | 172.64.130.35:80 | http://fiaharam.net/js/display.js | US | text | 13.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2056 | chrome.exe | 157.240.20.35:443 | www.facebook.com | Facebook, Inc. | US | whitelisted |
2056 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2056 | chrome.exe | 104.19.248.53:80 | tinyurl.com | Cloudflare Inc | US | unknown |
2056 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2056 | chrome.exe | 94.23.90.109:443 | sniffip.com | OVH SAS | PL | unknown |
— | — | 104.20.82.199:80 | adf.ly | Cloudflare Inc | US | unknown |
2056 | chrome.exe | 172.64.130.35:80 | fiaharam.net | Cloudflare Inc | US | suspicious |
2056 | chrome.exe | 216.58.205.234:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2056 | chrome.exe | 143.204.101.151:80 | d1nmxiiewlx627.cloudfront.net | — | US | suspicious |
2056 | chrome.exe | 143.204.201.46:80 | traintincre.fun | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tinyurl.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sniffip.com |
| unknown |
adf.ly |
| shared |
fiaharam.net |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdn.fiaharam.net |
| whitelisted |
d1nmxiiewlx627.cloudfront.net |
| whitelisted |
appearedsoci.fun |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2056 | chrome.exe | Attempted User Privilege Gain | AV POLICY Observed Suspicious JScript serving Adware Inbound |
2056 | chrome.exe | Attempted User Privilege Gain | AV POLICY Observed Suspicious JScript serving Adware Inbound |