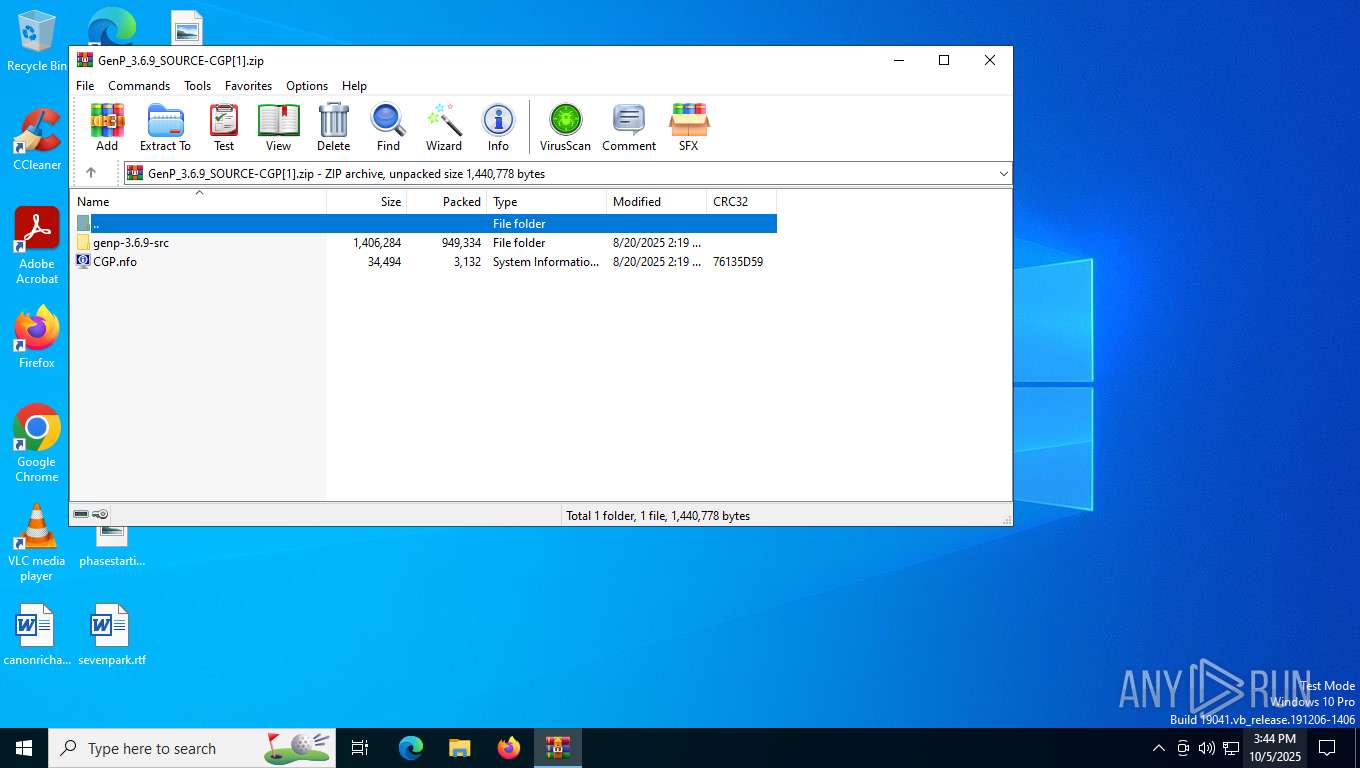
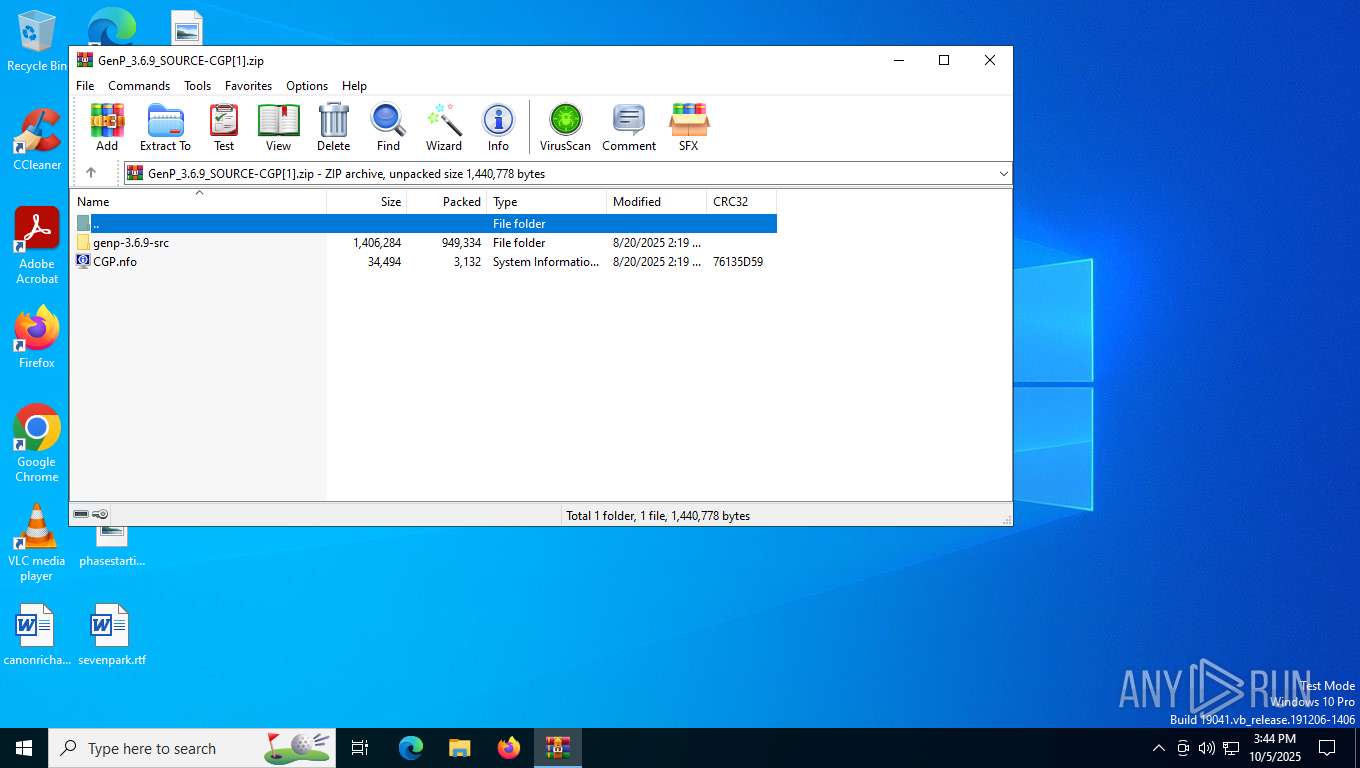
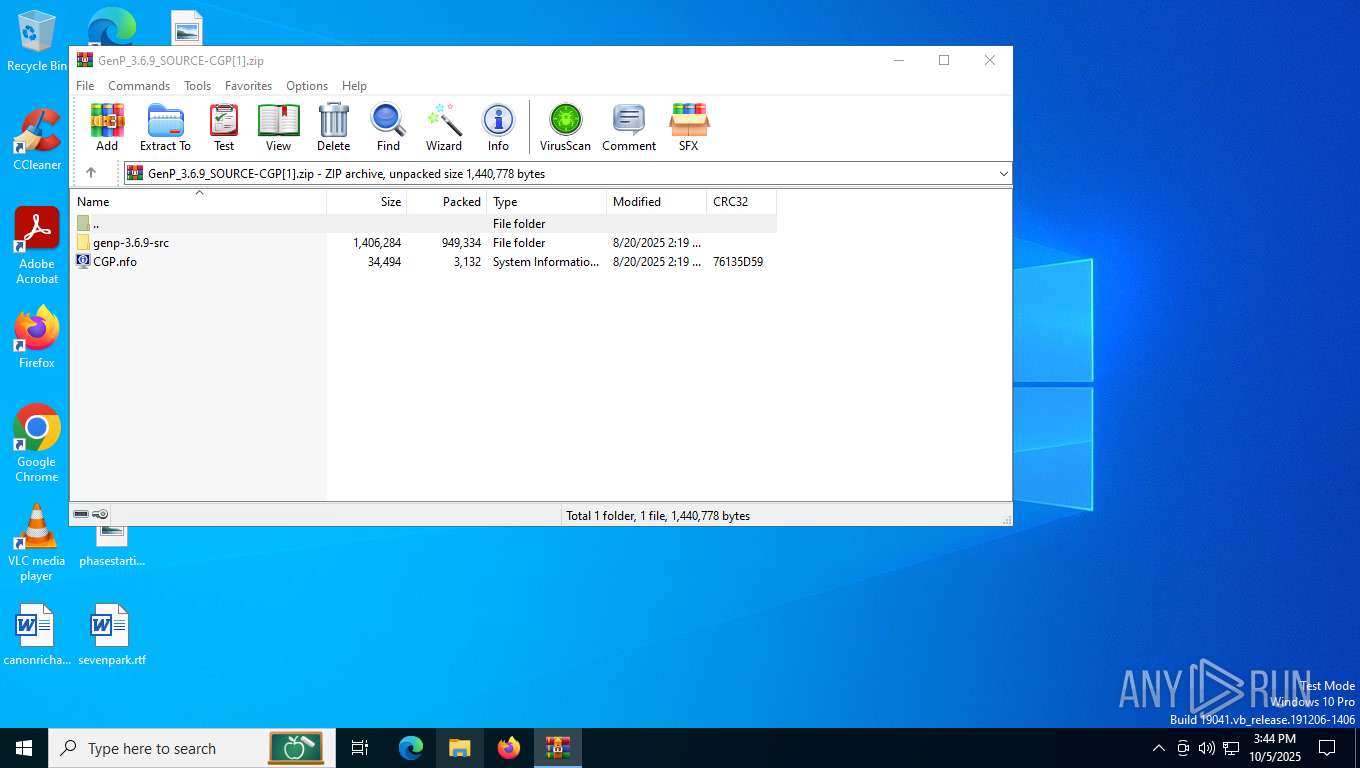
| File name: | GenP_3.6.9_SOURCE-CGP[1].zip |
| Full analysis: | https://app.any.run/tasks/dbd7a05f-07f9-4e7a-815f-1759ee9e8190 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2025, 15:44:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D08EE400B983B53196C50187DBA90625 |
| SHA1: | 841F5AE9C1609F8602863E738F27177921C38F82 |
| SHA256: | 81A252C7058588BD3033E0FA8BCC0723AC25DDB9B2AD83D73329D6CE5E7667E3 |
| SSDEEP: | 49152:zAmiLtKdwWBOEsB5YrAMmqUaPP84ORUva/lJGHw1p6v1EGSBsCLlWIBDrOBCQPcZ:MmUtKdBB3c5YrA7qBPLMEelkJv1EJHWk |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2856)
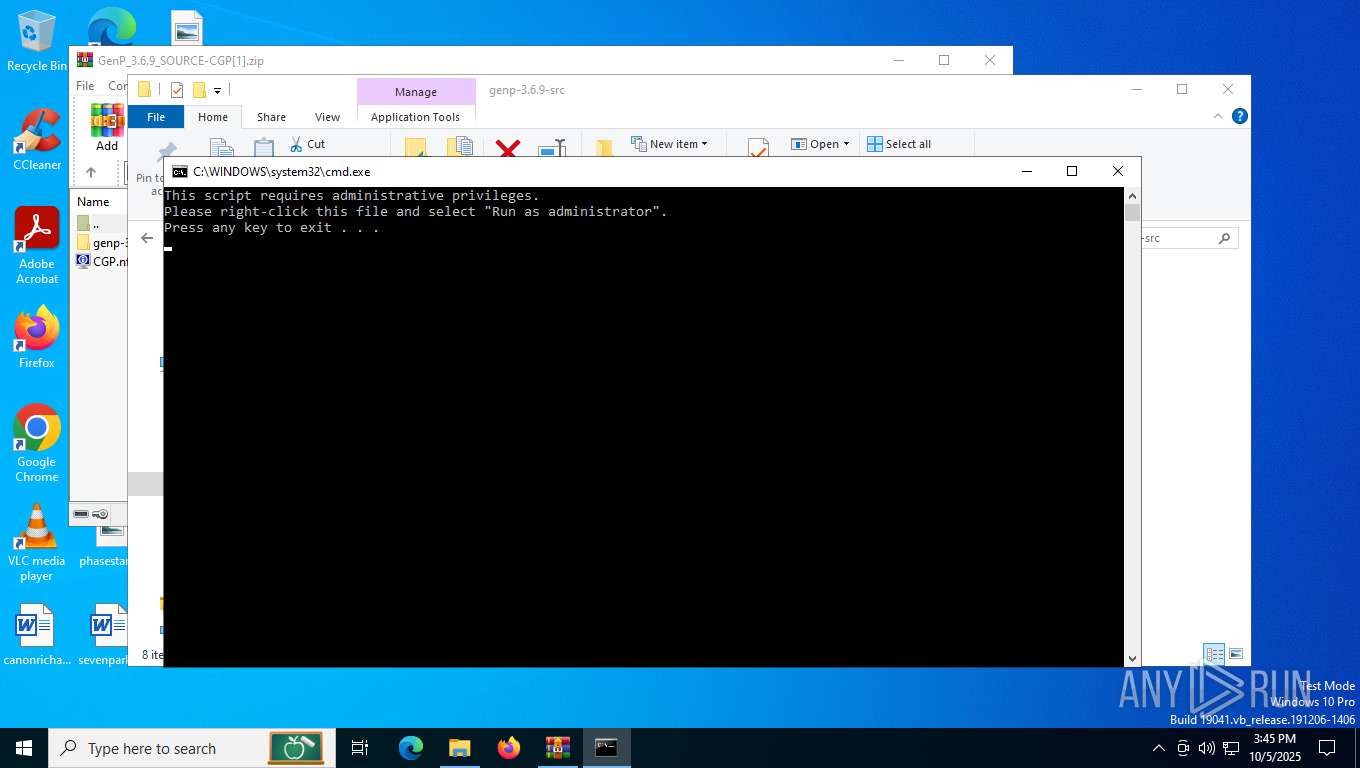
Bypass execution policy to execute commands
- powershell.exe (PID: 4584)
- powershell.exe (PID: 6720)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2164)
SUSPICIOUS
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 4584)
- powershell.exe (PID: 6720)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 7072)
- net.exe (PID: 464)
- cmd.exe (PID: 2164)
- net.exe (PID: 4208)
Process drops legitimate windows executable
- WinRAR.exe (PID: 2856)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2164)
The process executes Powershell scripts
- cmd.exe (PID: 2164)
Executable content was dropped or overwritten
- tar.exe (PID: 3428)
INFO
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 2288)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2856)
Manual execution by a user
- powershell.exe (PID: 4584)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 2164)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5340)
- BackgroundTransferHost.exe (PID: 1188)
- BackgroundTransferHost.exe (PID: 2288)
- BackgroundTransferHost.exe (PID: 356)
- BackgroundTransferHost.exe (PID: 7796)
The sample compiled with english language support
- WinRAR.exe (PID: 2856)
- tar.exe (PID: 3428)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 2288)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 2288)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4584)
- powershell.exe (PID: 6720)
Checks supported languages
- tar.exe (PID: 3428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:08:20 18:19:06 |
| ZipCRC: | 0x76135d59 |
| ZipCompressedSize: | 3132 |
| ZipUncompressedSize: | 34494 |
| ZipFileName: | CGP.nfo |
Total processes
189
Monitored processes
20
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 464 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 520 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
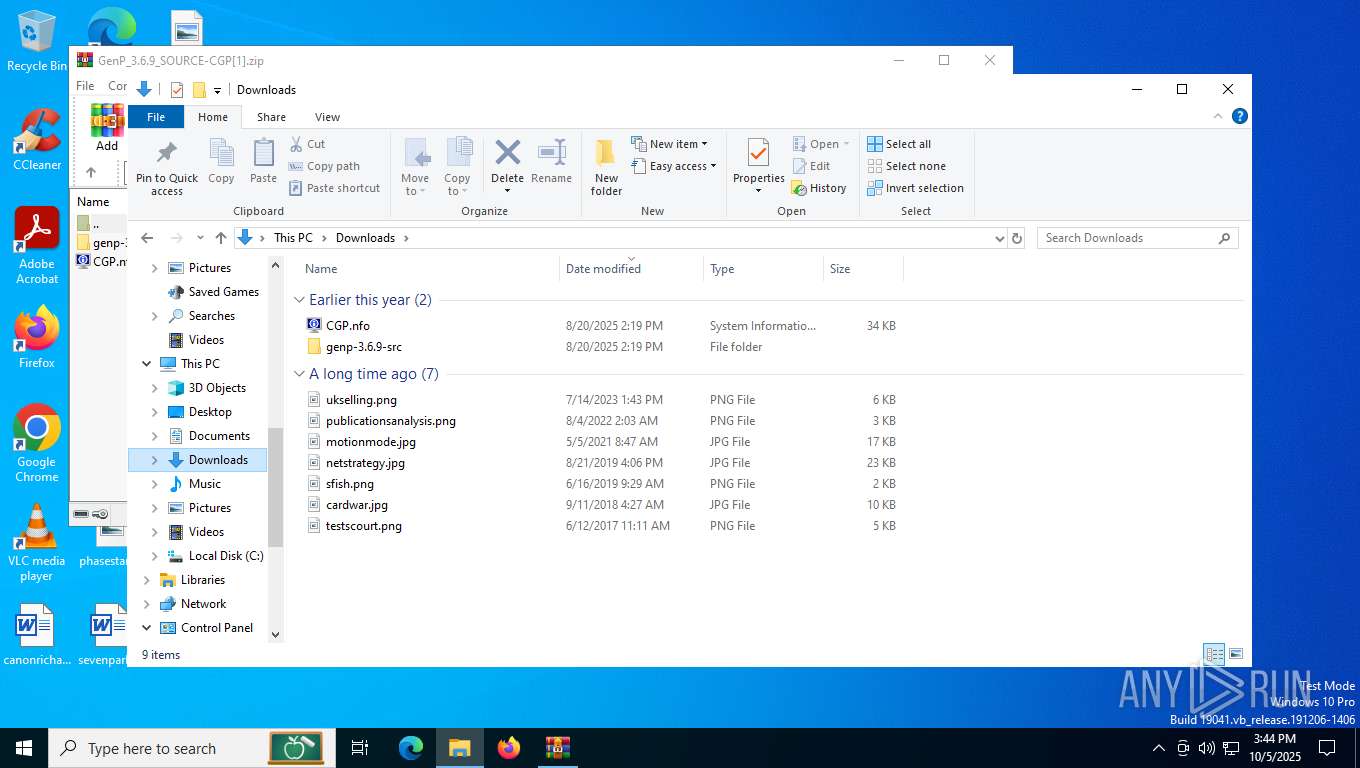
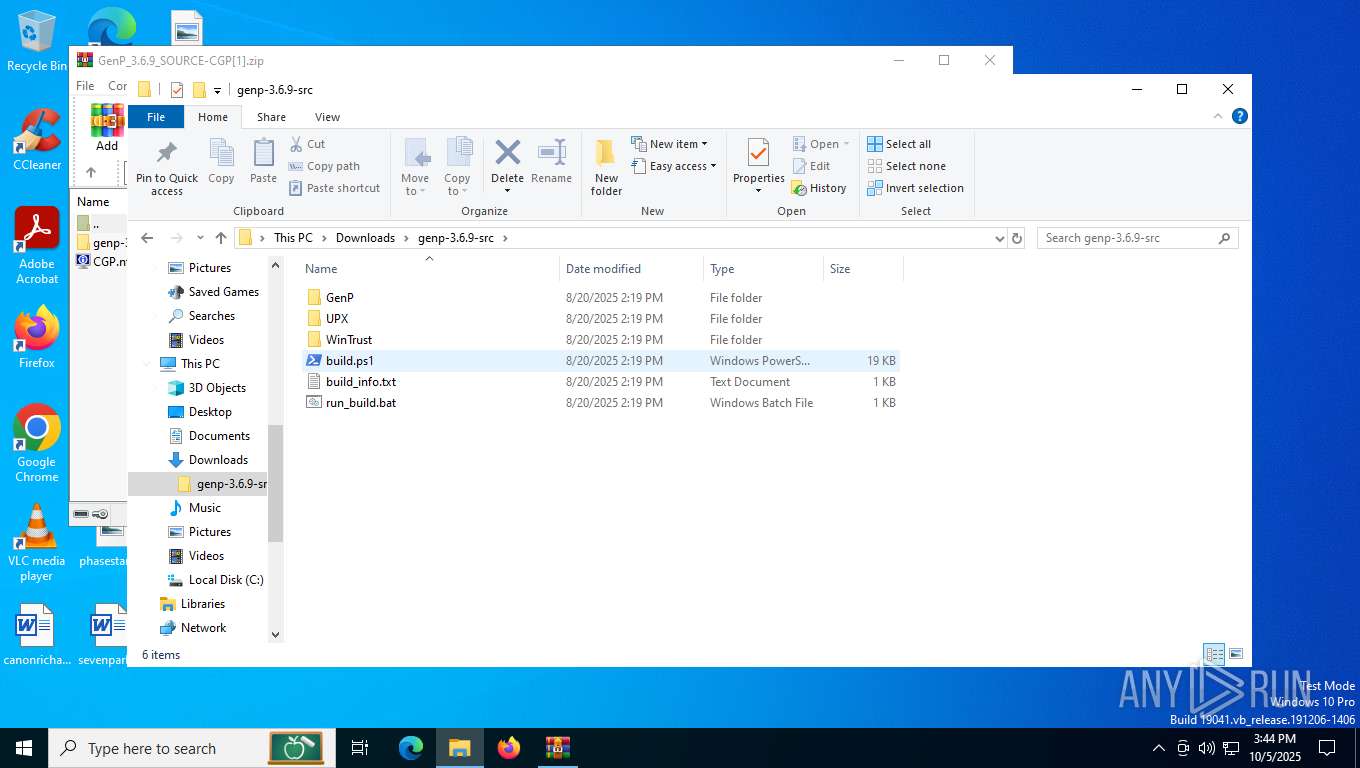
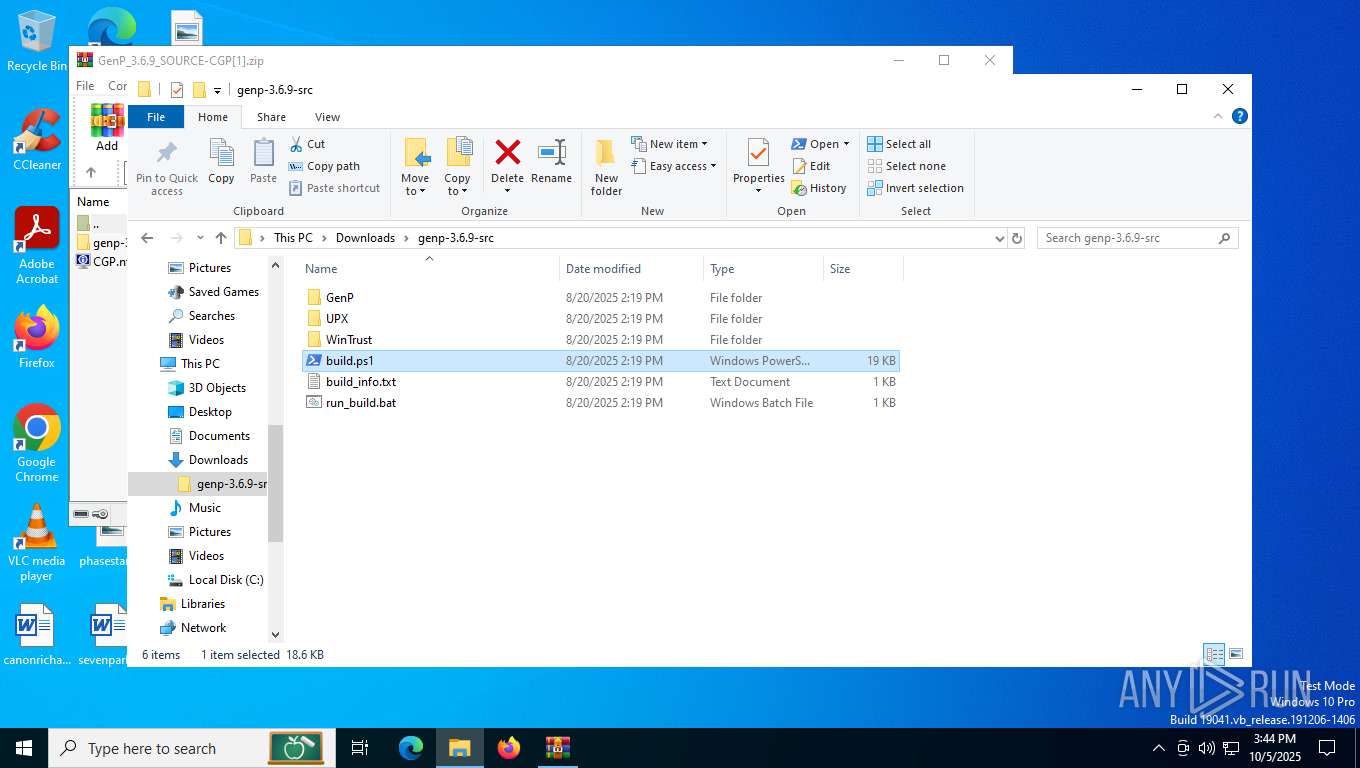
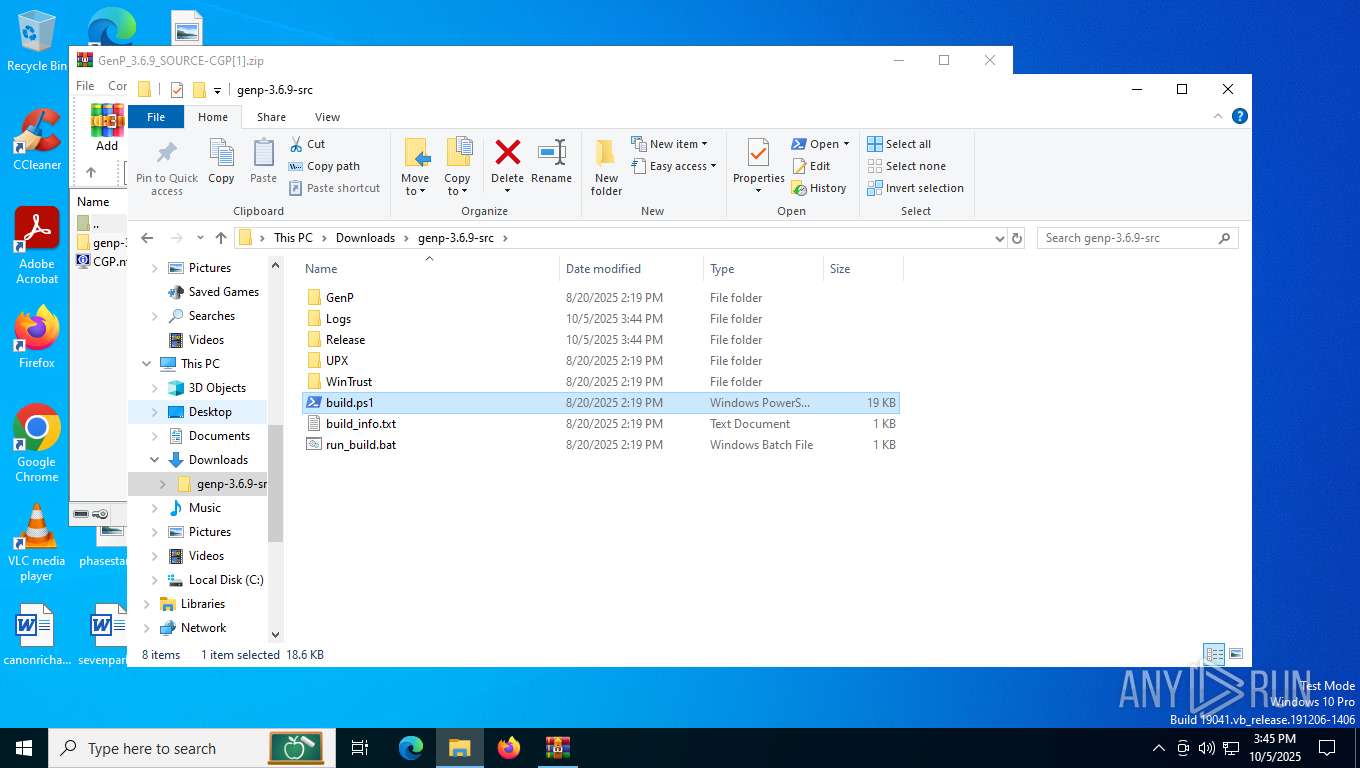
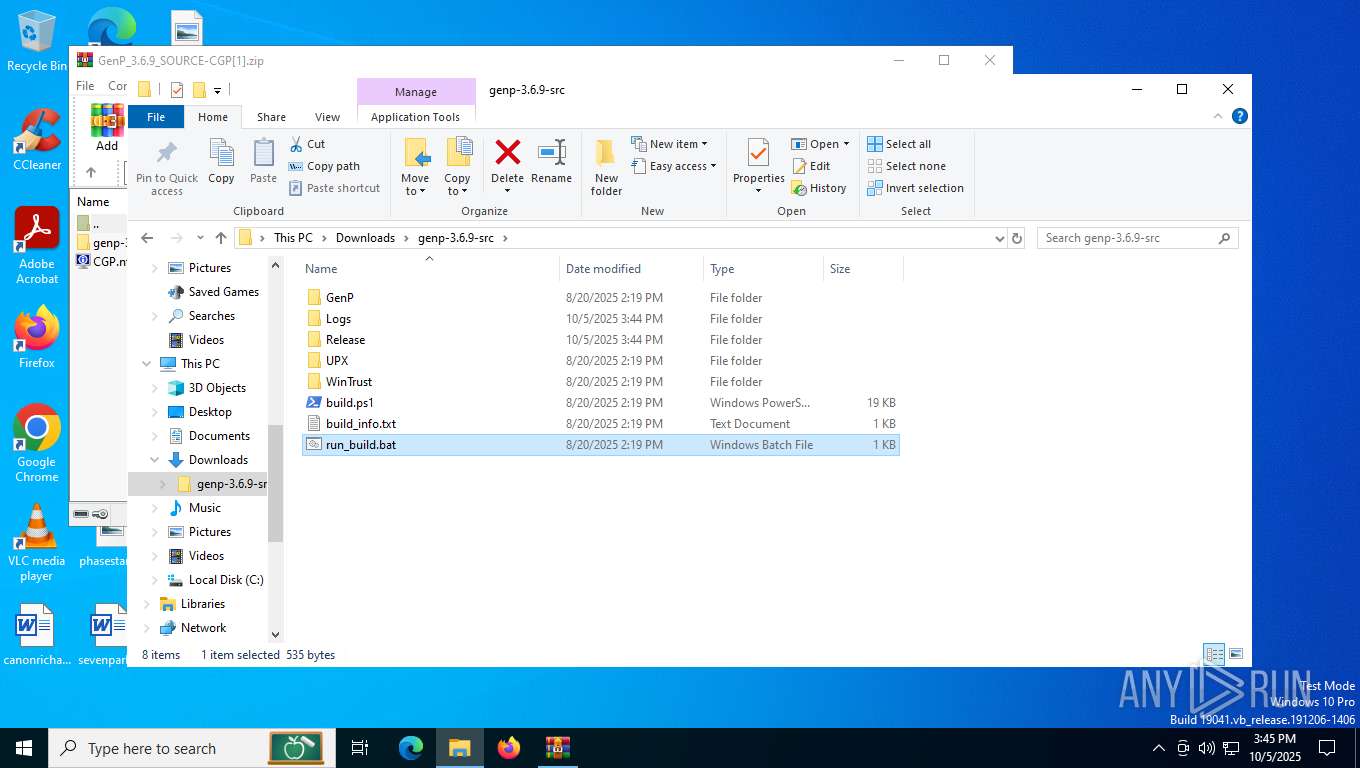
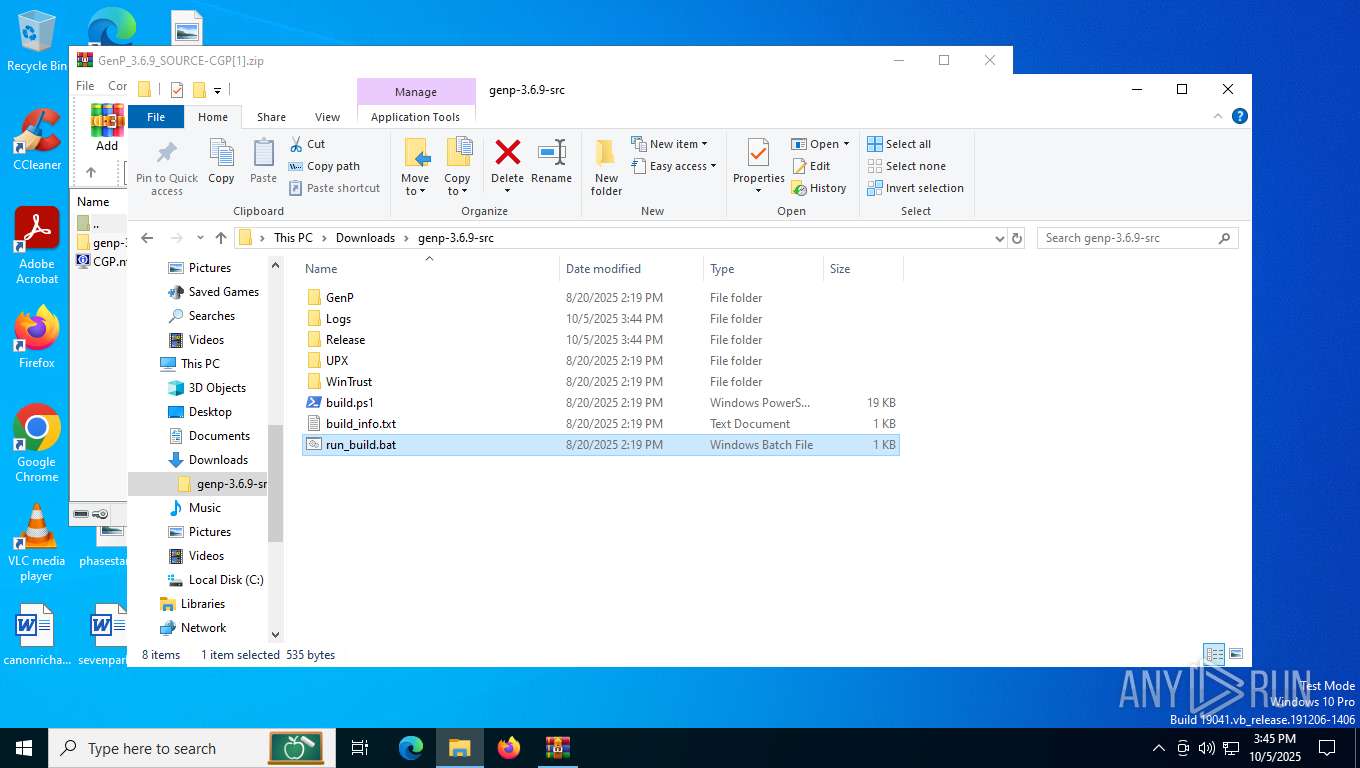
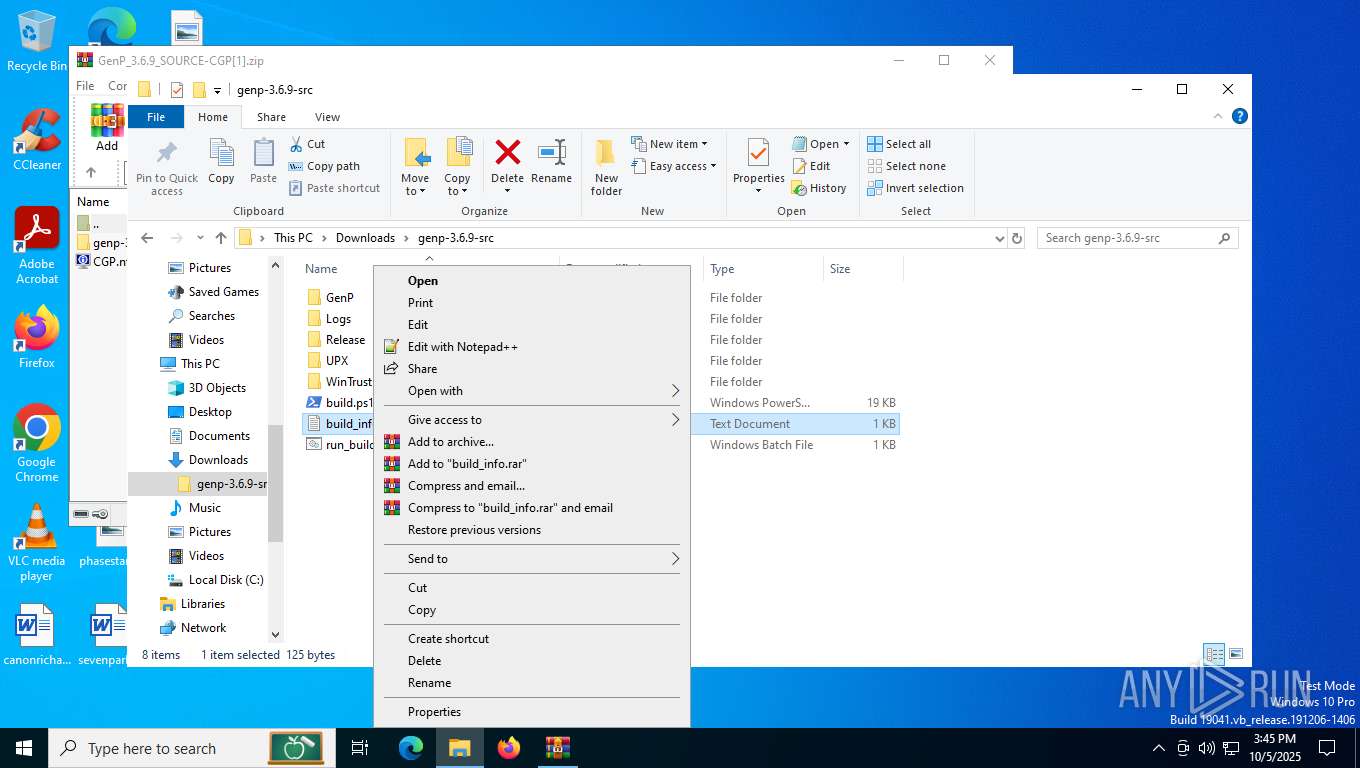
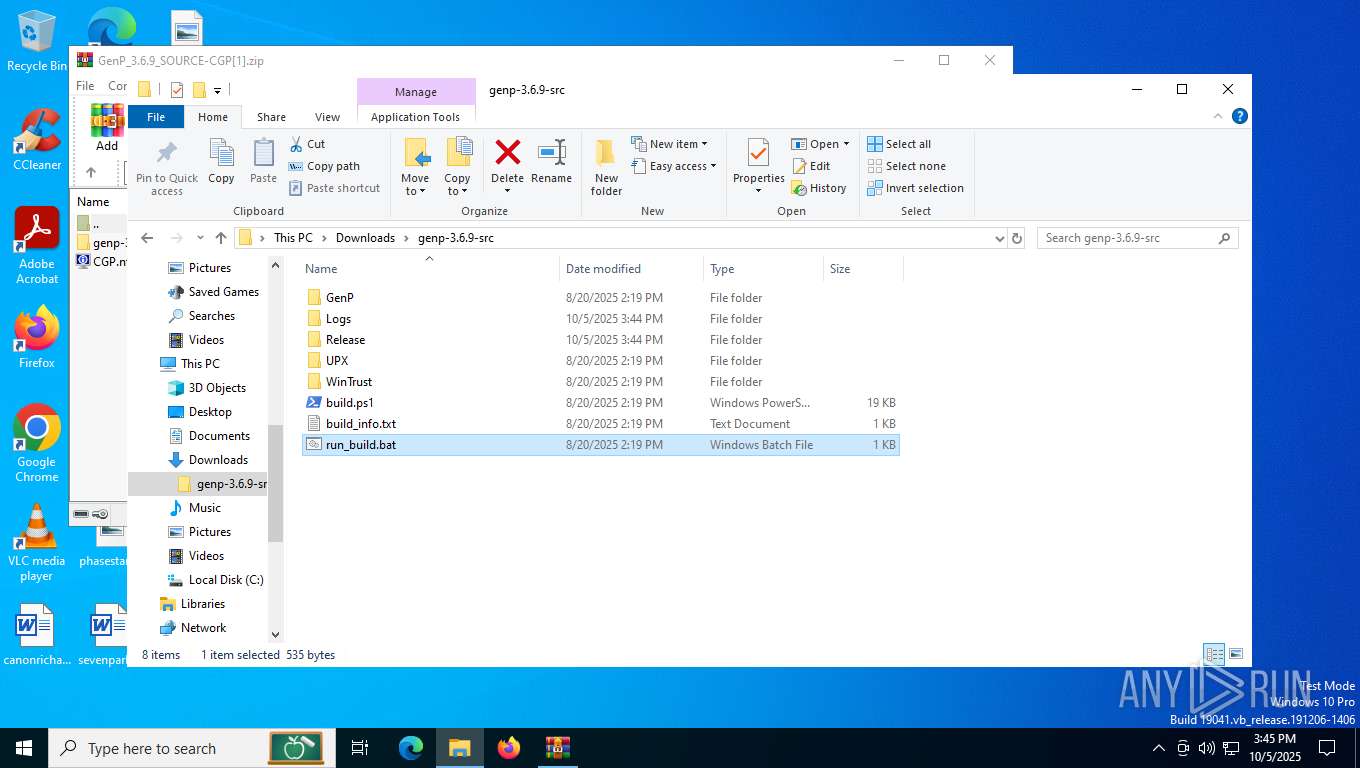
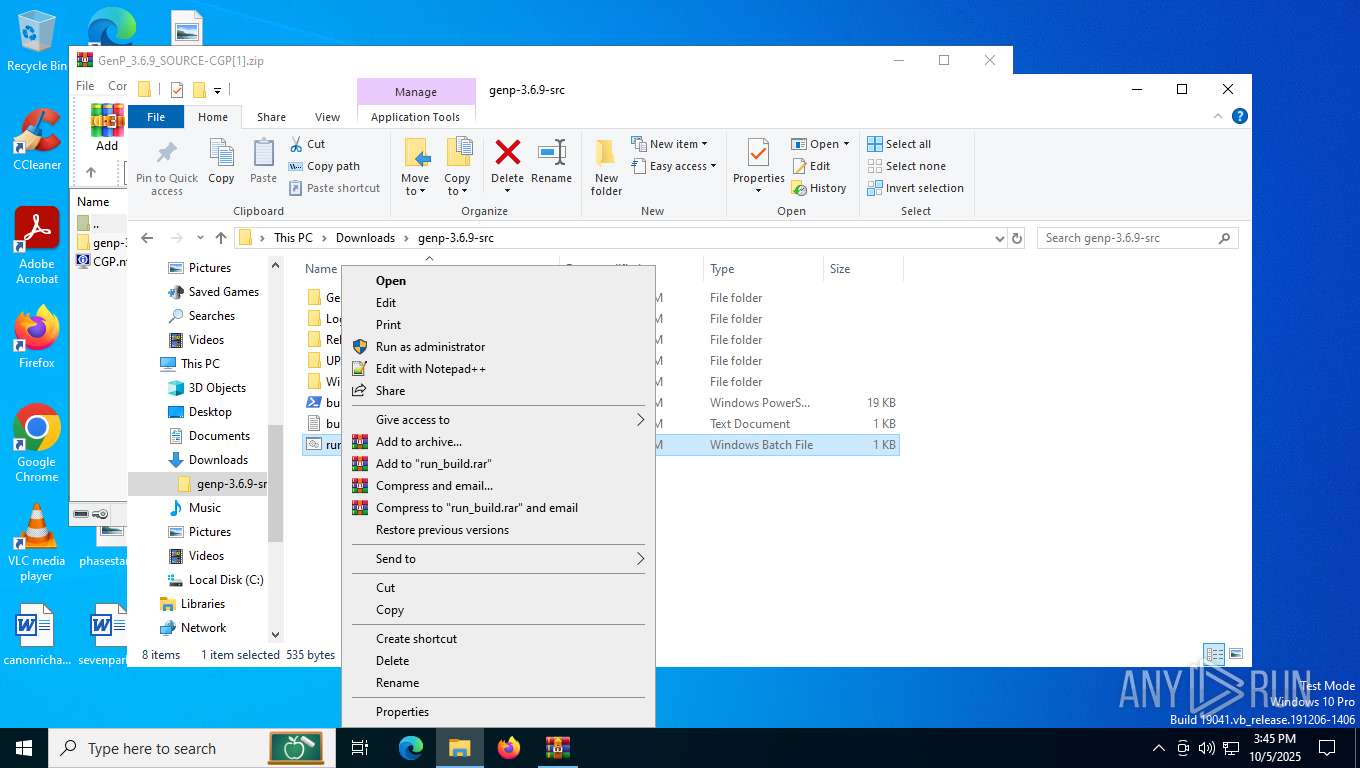
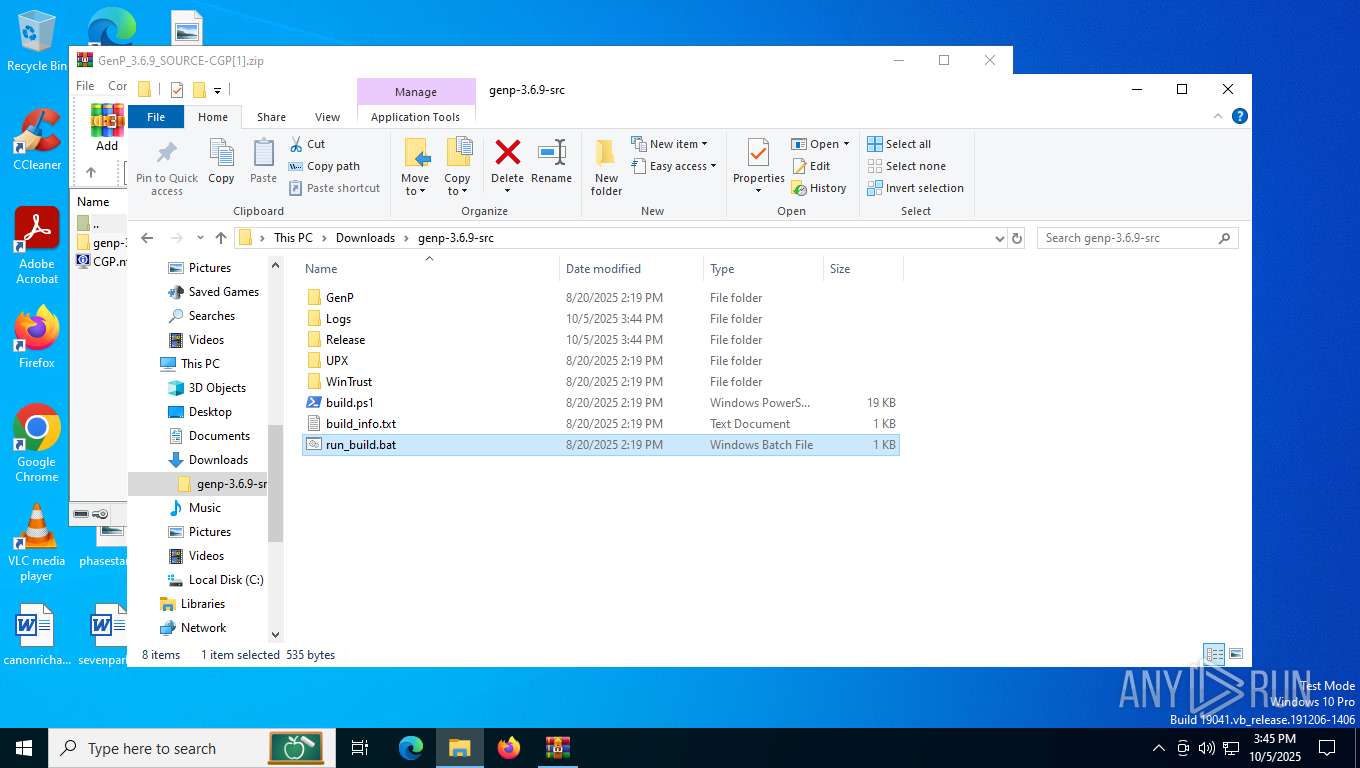
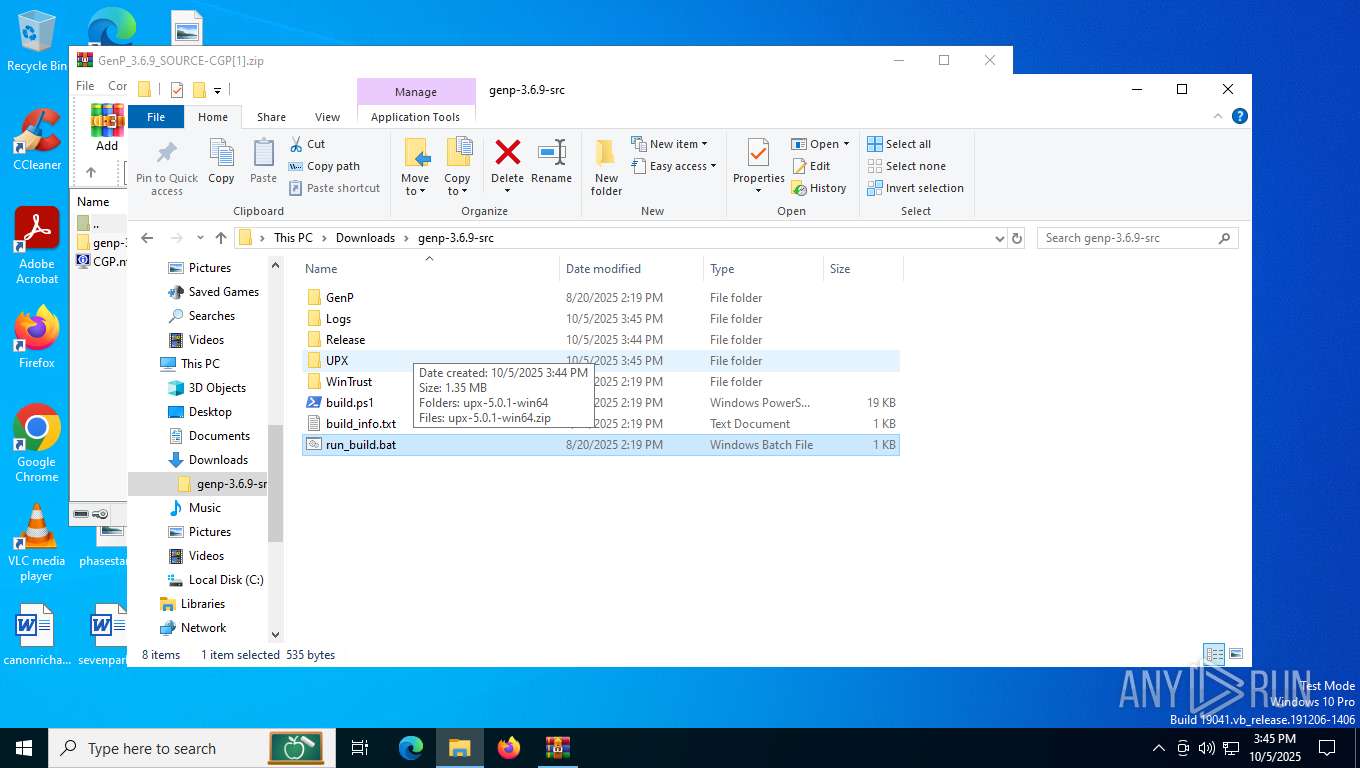
| 2164 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Downloads\genp-3.6.9-src\run_build.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
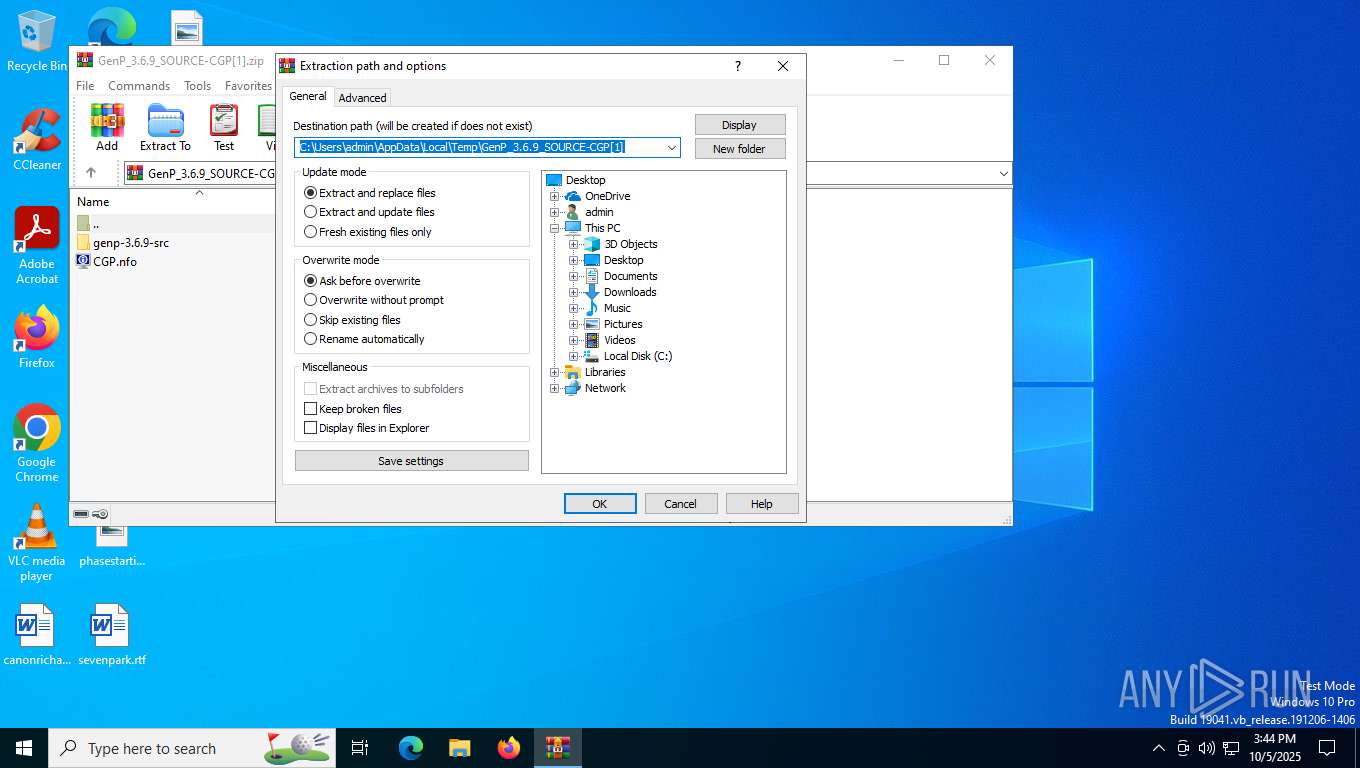
| 2856 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\GenP_3.6.9_SOURCE-CGP[1].zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
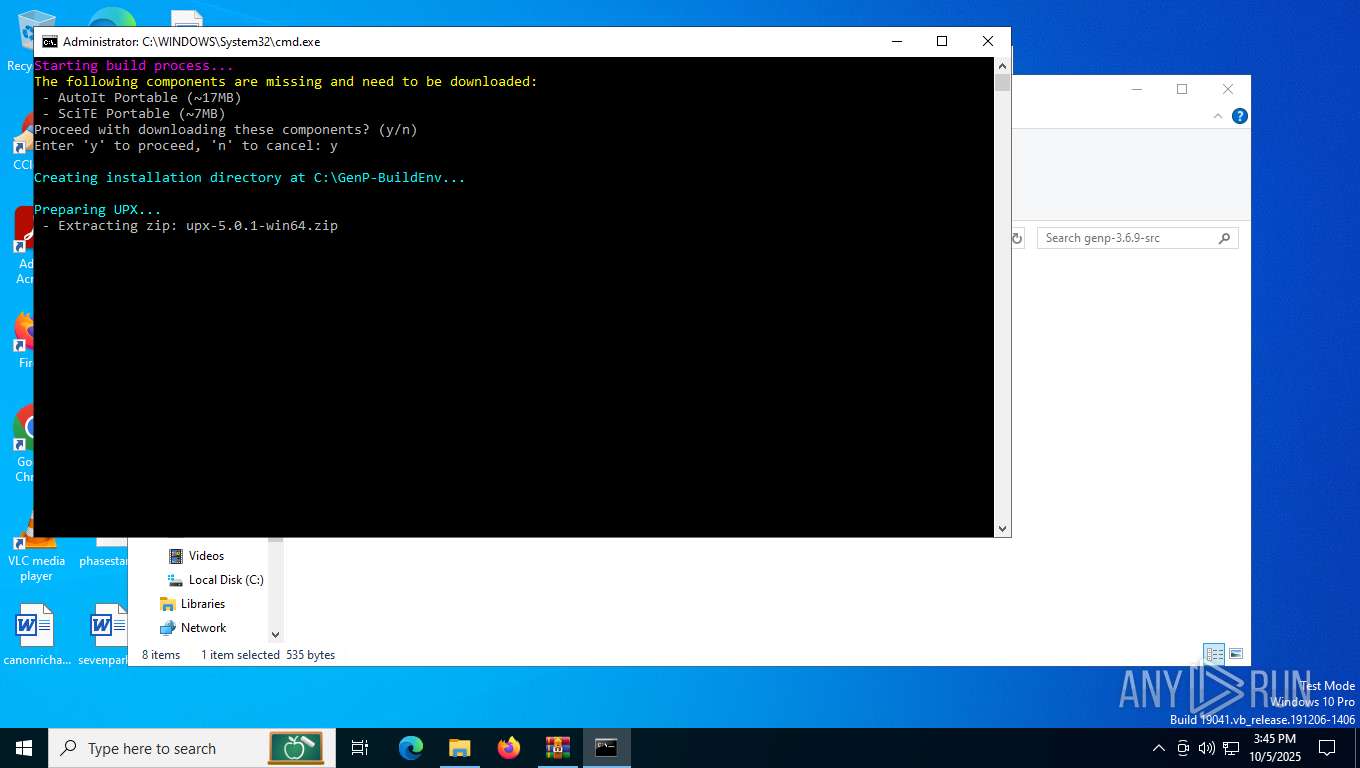
| 3428 | "C:\WINDOWS\system32\tar.exe" -xf "C:\Users\admin\Downloads\genp-3.6.9-src\UPX\upx-5.0.1-win64.zip" -C "C:\Users\admin\Downloads\genp-3.6.9-src\UPX" | C:\Windows\System32\tar.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: bsdtar archive tool Exit code: 0 Version: 3.5.2 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4208 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 828
Read events
16 786
Write events
29
Delete events
13
Modification events
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GenP_3.6.9_SOURCE-CGP[1].zip | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
11
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2288 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\e4b12aa0-7254-436d-9521-3e6e55a27aba.down_data | — | |
MD5:— | SHA256:— | |||
| 2856 | WinRAR.exe | C:\Users\admin\Downloads\genp-3.6.9-src\build.ps1 | text | |
MD5:3489EE25B34B46DEABE8D371EE8B0D76 | SHA256:14BE137B4644140653363FA7B13ADA4B66E50A57257226BD231D62AADF8364AE | |||
| 2288 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\9fa079a9-2127-496b-8585-7c02801609c9.up_meta_secure | binary | |
MD5:D7F6D87453DF64A8E1B40E898FA717B8 | SHA256:6606537072FDA035FFB80480D8E41F16F590737DC1BB1497A75A607BAE9D8ABE | |||
| 4584 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3opycmq0.kdj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4584 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zjglwnfg.asj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2856 | WinRAR.exe | C:\Users\admin\Downloads\genp-3.6.9-src\GenP\GenP-3.6.9.au3 | binary | |
MD5:C89899E68D8AA054E57B4F6C582893A9 | SHA256:FB68BCAD3793F9F952D2E879D39B3491BADFDD5997DB93ACE0A66C7D783F0E8B | |||
| 2288 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:550A2F75CE5E055AAD3C6B1364982D65 | SHA256:008C51708F6C470A11284BF63F41C6E1458DC5913214D5B8B4B125F74D51B68F | |||
| 2288 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:EB93E91FC1DBBA767A902CA29AD36914 | SHA256:261DA88833357B4DADEB307B55B9EEAAC6B9321828C1AC3D9F54B3C000CA5B6E | |||
| 2856 | WinRAR.exe | C:\Users\admin\Downloads\genp-3.6.9-src\GenP\config.ini | text | |
MD5:7AD508E8AC39165EF9DD495A2100E00A | SHA256:13C37C44BF03B61806EEC40A696155DCAD85D3180C831F7E76F6B89BDEDE62D6 | |||
| 2856 | WinRAR.exe | C:\Users\admin\Downloads\CGP.nfo | text | |
MD5:1A73E1F1EE4E0EA1D1D6E8DCC5BA328A | SHA256:01D3466D79BF2E3D0AB0021F806882DF71EA871C9C0A432BE7F4284064EB9522 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
33
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4928 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4928 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2176 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1136 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1372 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2288 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6016 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7072 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5224 | SearchApp.exe | 2.16.241.218:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4928 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4928 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1136 | backgroundTaskHost.exe | 2.16.241.218:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1136 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
3464 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |