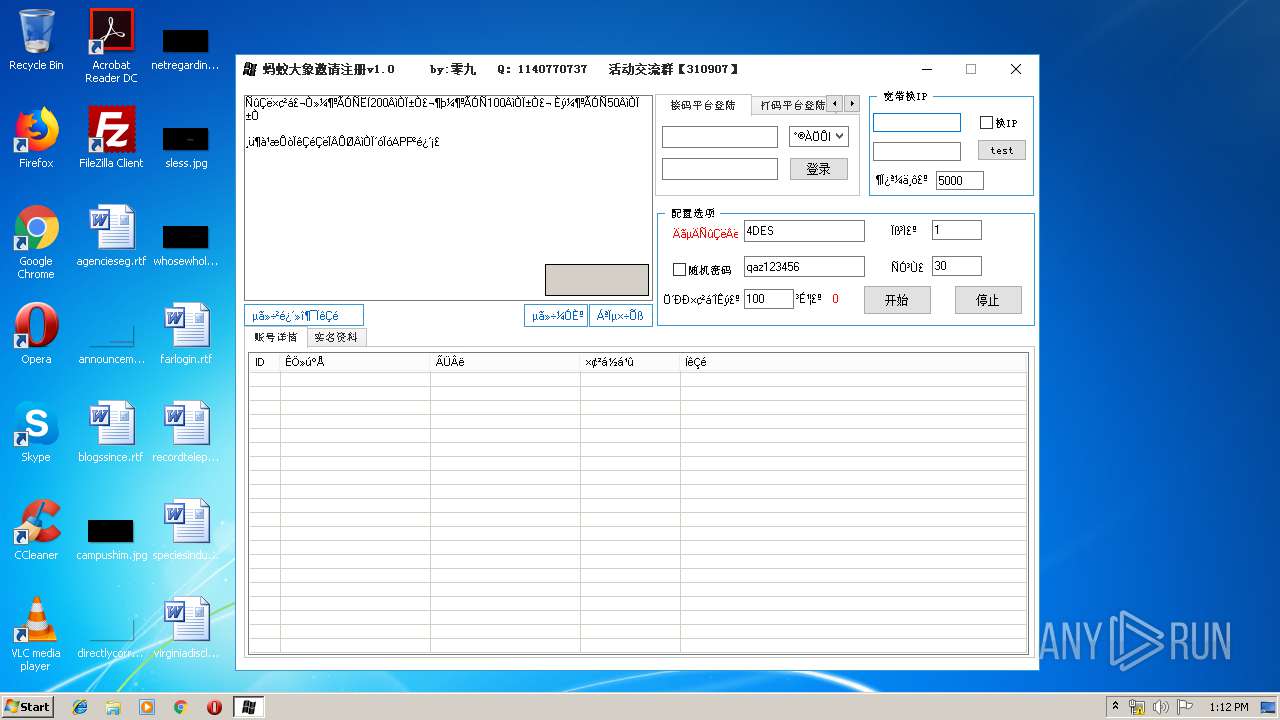
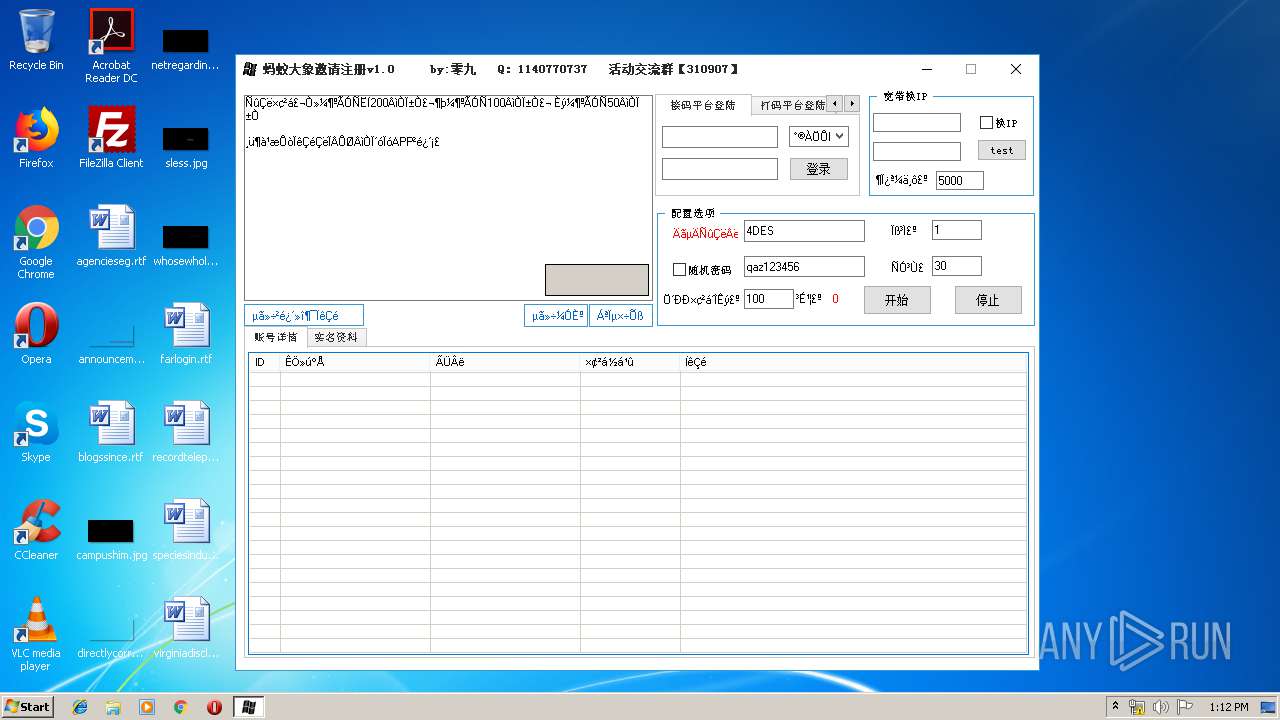
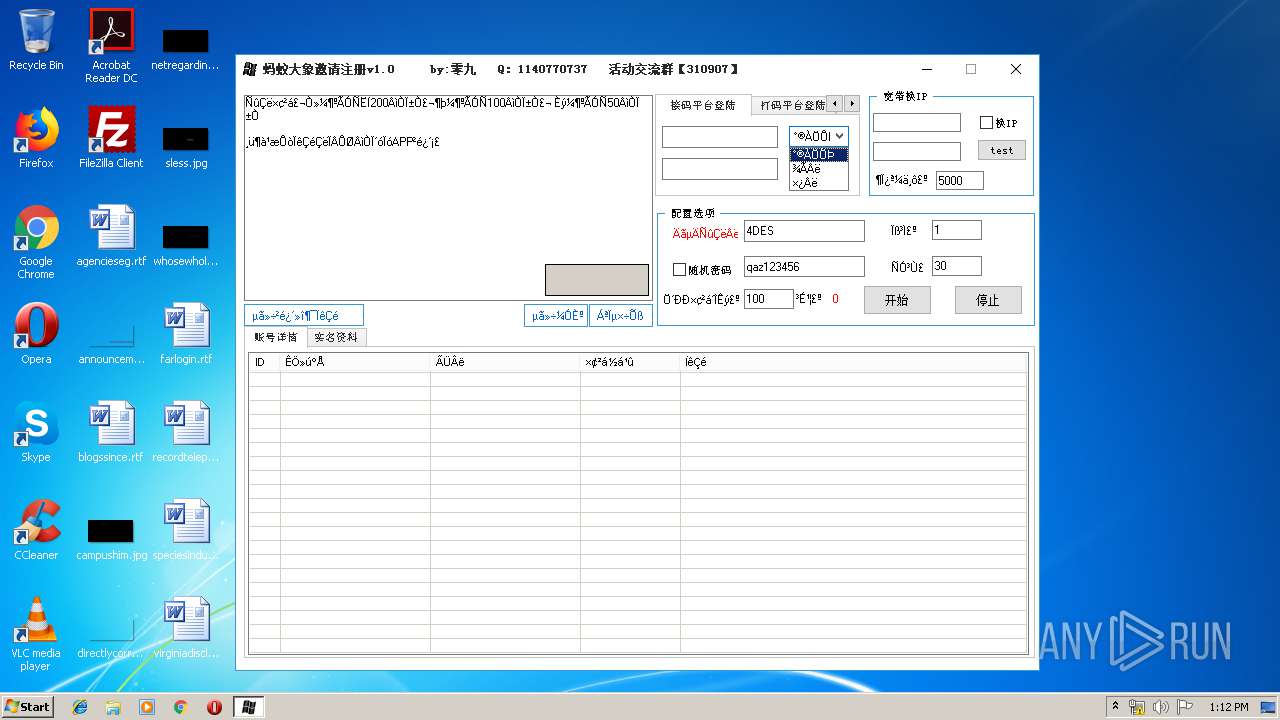
| File name: | 蚂蚁大象邀请注册机v1.0 by:零九.exe |
| Full analysis: | https://app.any.run/tasks/38b473ef-2b85-49bf-9488-8a56b16aa340 |
| Verdict: | No threats detected |
| Analysis date: | April 01, 2019, 12:12:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 11F505031DEBC9052AF5F4682040471B |
| SHA1: | DBB0E5A16AB417346A7C093F36BFF6588B31E287 |
| SHA256: | 819D445C13FF5867671305FC4B534F112BB4CF3F59C6A670E1D2FA621938B458 |
| SSDEEP: | 12288:psg7LQCgzKctnTp7xZxVemNeOO7CYHS4AtziII:1r457ne/OO7CYHS4D |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:50:16 |
| Detected languages: |
|
| FileVersion: | 1.2.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | 东东云购注册机 by零九 |
| ProductVersion: | 1.2.0.0 |
| CompanyName: | 零九 |
| LegalCopyright: | 零九 版权所有 |
| Comments: | 本程序使用易语言编写(http://www.eyuyan.com) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0000 |
| Pages in file: | 0x0000 |
| Relocations: | 0x0000 |
| Size of header: | 0x0000 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Apr-2016 03:50:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
Esp0 | 0x00001000 | 0x00105000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Esp1 | 0x00106000 | 0x0008E000 | 0x0008E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9996 |
.rsrc | 0x00194000 | 0x00012000 | 0x00011600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.21672 |
.Esp | 0x001A6000 | 0x000001FF | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.92121 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.81594 | 616 | Latin 1 / Western European | Chinese - PRC | RT_VERSION |
2 | 7.2836 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 1.01505 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 6.95411 | 180 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
1031 | 7.67913 | 584 | Latin 1 / Western European | Chinese - PRC | RT_BITMAP |
1032 | 4.12193 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_CURSOR |
1033 | 4.32193 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_CURSOR |
1037 | 7.05441 | 234 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
1038 | 7.36962 | 324 | Latin 1 / Western European | Chinese - PRC | RT_BITMAP |
1138 | 7.35103 | 344 | Latin 1 / Western European | Chinese - PRC | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINMM.dll |
Total processes
32
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3576 | "C:\Users\admin\AppData\Local\Temp\蚂蚁大象邀请注册机v1.0 by:零九.exe" | C:\Users\admin\AppData\Local\Temp\蚂蚁大象邀请注册机v1.0 by:零九.exe | — | explorer.exe | |||||||||||
User: admin Company: 零九 Integrity Level: MEDIUM Description: 易语言程序 Exit code: 0 Version: 1.2.0.0 Modules
| |||||||||||||||
Total events
7
Read events
0
Write events
7
Delete events
0
Modification events
| (PID) Process: | (3576) 蚂蚁大象邀请注册机v1.0 by:零九.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | vga.drv 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
| (PID) Process: | (3576) 蚂蚁大象邀请注册机v1.0 by:零九.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\?????????v1_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3576) 蚂蚁大象邀请注册机v1.0 by:零九.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\?????????v1_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3576) 蚂蚁大象邀请注册机v1.0 by:零九.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\?????????v1_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3576) 蚂蚁大象邀请注册机v1.0 by:零九.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\?????????v1_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3576) 蚂蚁大象邀请注册机v1.0 by:零九.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\?????????v1_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3576) 蚂蚁大象邀请注册机v1.0 by:零九.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\?????????v1_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3576 | 蚂蚁大象邀请注册机v1.0 by:零九.exe | C:\Users\admin\AppData\Local\Temp\×¢²áÅäÖÃ.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report