| File name: | jucheck.exe |
| Full analysis: | https://app.any.run/tasks/04d4d63c-632b-49fa-b486-05303b34b837 |
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2025, 13:43:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 754F467BBFD0AE633CA68E5BFB9EFCF1 |
| SHA1: | C67BC81415D8E7553C256C781A177402BAB6B473 |
| SHA256: | 819A12D82FF854C7D9EBF51C43BB7FC037A9CAC80F1B479286DBF7D62B167545 |
| SSDEEP: | 49152:2aukMA4aVqd/7R/XNjjhI9rWWfZt8lW3mUNVDRjW7:2+MA4asd/7RljjhyfZeW3PZC |
MALICIOUS
No malicious indicators.SUSPICIOUS
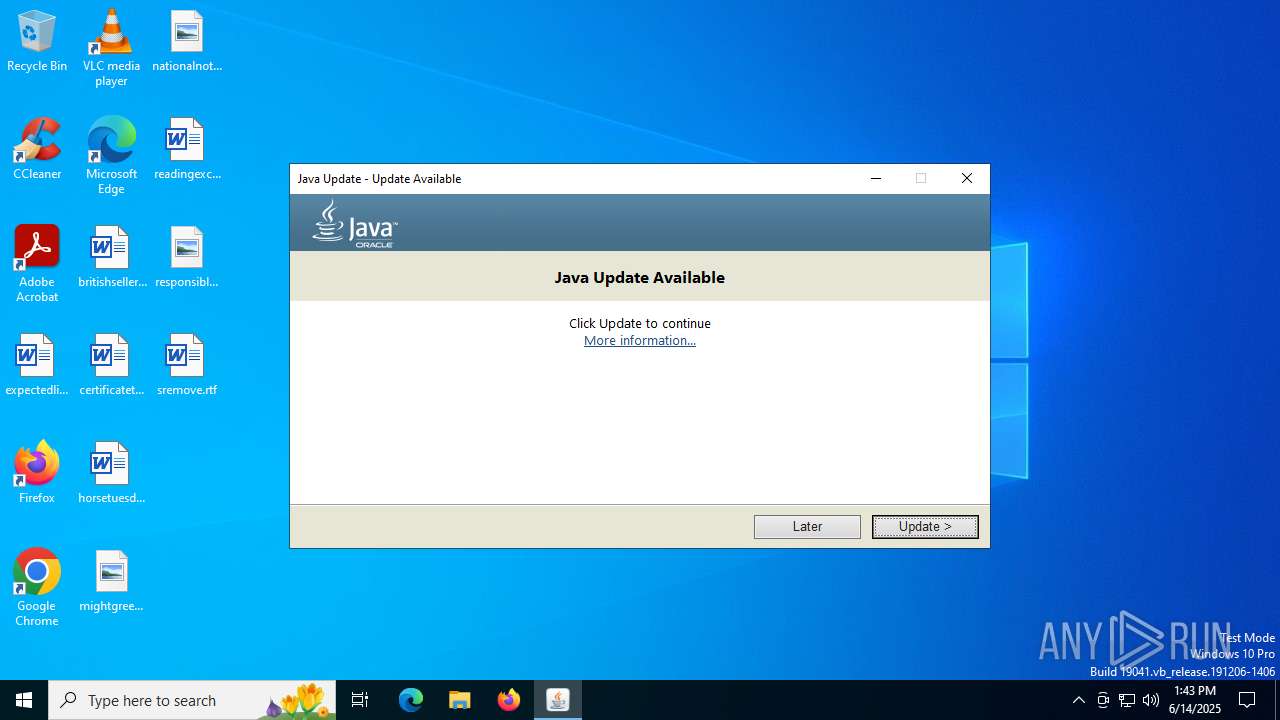
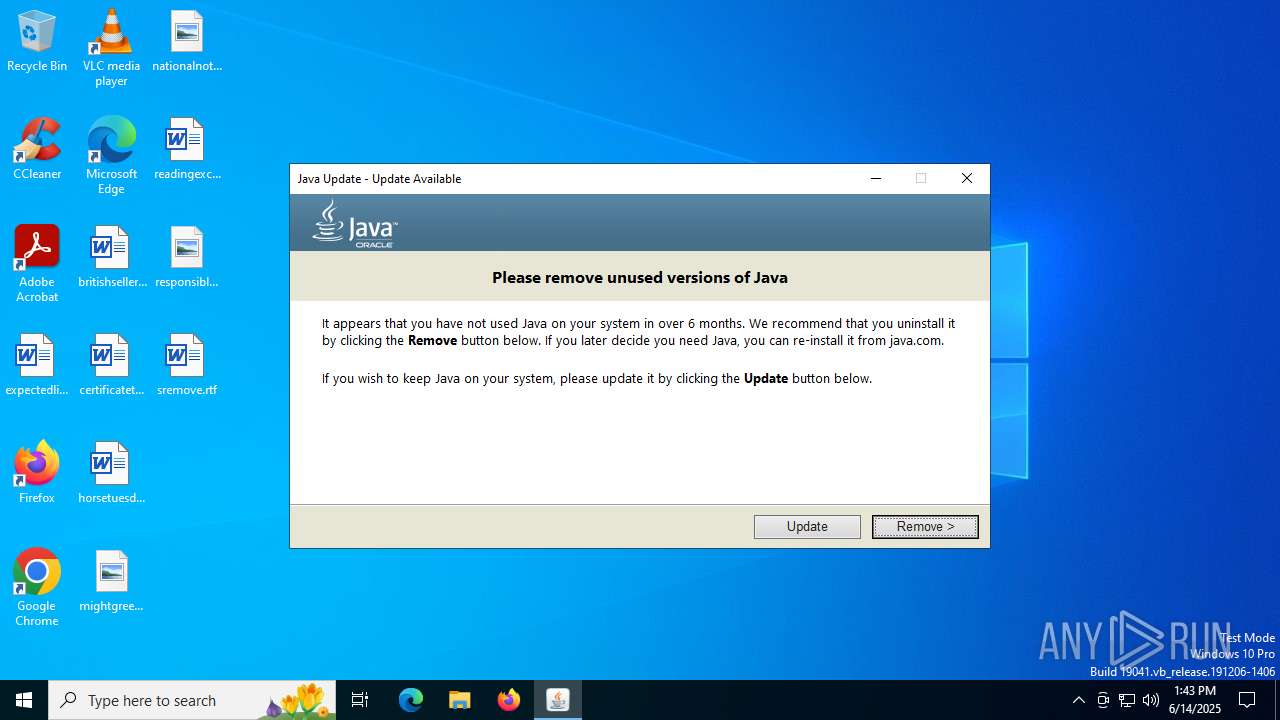
Checks for Java to be installed
- jucheck.exe (PID: 3504)
- jre-8u451-windows-au.exe (PID: 2612)
- jp2launcher.exe (PID: 3864)
Reads security settings of Internet Explorer
- jucheck.exe (PID: 3504)
- jp2launcher.exe (PID: 3864)
- jre-8u451-windows-au.exe (PID: 2612)
Reads Microsoft Outlook installation path
- jucheck.exe (PID: 3504)
- jre-8u451-windows-au.exe (PID: 2612)
Reads Internet Explorer settings
- jucheck.exe (PID: 3504)
- jre-8u451-windows-au.exe (PID: 2612)
Executable content was dropped or overwritten
- jucheck.exe (PID: 3504)
- jre-8u451-windows-au.exe (PID: 3944)
INFO
The sample compiled with english language support
- jucheck.exe (PID: 3504)
- jre-8u451-windows-au.exe (PID: 3944)
Checks supported languages
- jucheck.exe (PID: 3504)
- javaws.exe (PID: 1720)
- jre-8u451-windows-au.exe (PID: 3944)
- jre-8u451-windows-au.exe (PID: 2612)
- jp2launcher.exe (PID: 3864)
Reads the computer name
- javaws.exe (PID: 1720)
- jucheck.exe (PID: 3504)
- jp2launcher.exe (PID: 3864)
- jre-8u451-windows-au.exe (PID: 3944)
- jre-8u451-windows-au.exe (PID: 2612)
Create files in a temporary directory
- jucheck.exe (PID: 3504)
- jre-8u451-windows-au.exe (PID: 3944)
- jp2launcher.exe (PID: 3864)
JAVA mutex has been found
- jucheck.exe (PID: 3504)
- jp2launcher.exe (PID: 3864)
- javaws.exe (PID: 1720)
Reads the software policy settings
- jucheck.exe (PID: 3504)
- jre-8u451-windows-au.exe (PID: 2612)
Reads the machine GUID from the registry
- jucheck.exe (PID: 3504)
- jp2launcher.exe (PID: 3864)
- jre-8u451-windows-au.exe (PID: 2612)
Checks proxy server information
- jp2launcher.exe (PID: 3864)
- jre-8u451-windows-au.exe (PID: 2612)
- jucheck.exe (PID: 3504)
Creates files or folders in the user directory
- jucheck.exe (PID: 3504)
- jp2launcher.exe (PID: 3864)
- jre-8u451-windows-au.exe (PID: 2612)
Java executable
- jre-8u451-windows-au.exe (PID: 3944)
- jre-8u451-windows-au.exe (PID: 2612)
Process checks computer location settings
- jucheck.exe (PID: 3504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:12:04 08:49:21+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.36 |
| CodeSize: | 543744 |
| InitializedDataSize: | 676864 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4fa66 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.8.441.7 |
| ProductVersionNumber: | 2.8.441.7 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Oracle Corporation |
| FileDescription: | Java Update Checker |
| FileVersion: | 2.8.441.7 |
| FullVersion: | 2.8.441.7 |
| InternalName: | Java Update Checker |
| LegalCopyright: | Copyright © 2025 |
| OriginalFileName: | jucheck.exe |
| ProductName: | Java Platform SE Auto Updater |
| ProductVersion: | 2.8.441.7 |
Total processes
141
Monitored processes
5
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1720 | "C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe" -J-Djdk.disableLastUsageTracking=true -SSVBaselineUpdate | C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe | — | jucheck.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\AppData\Local\Temp\jds1544390.tmp\jre-8u451-windows-au.exe" "/installmethod=jau-m" "FAMILYUPGRADE=1" | C:\Users\admin\AppData\Local\Temp\jds1544390.tmp\jre-8u451-windows-au.exe | jre-8u451-windows-au.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Version: 8.0.4510.10 Modules
| |||||||||||||||
| 3504 | "C:\Users\admin\AppData\Local\Temp\jucheck.exe" | C:\Users\admin\AppData\Local\Temp\jucheck.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java Update Checker Exit code: 0 Version: 2.8.441.7 Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_271" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxwbHVnaW4uamFyAC1EamRrLmRpc2FibGVMYXN0VXNhZ2VUcmFja2luZz10cnVlAC1Eam5scHguanZtPUM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcYmluXGphdmF3LmV4ZQAtRGpubHB4LnZtYXJncz1MVVJxWkdzdVpHbHpZV0pzWlV4aGMzUlZjMkZuWlZSeVlXTnJhVzVuUFhSeWRXVUE= -ma LVNTVkJhc2VsaW5lVXBkYXRlAC1ub3RXZWJKYXZh | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | javaws.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 3944 | "C:\Users\admin\AppData\Local\Temp\jre-8u451-windows-au.exe" /installmethod=jau-m FAMILYUPGRADE=1 | C:\Users\admin\AppData\Local\Temp\jre-8u451-windows-au.exe | jucheck.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Version: 8.0.4510.10 Modules
| |||||||||||||||
Total events
10 521
Read events
10 293
Write events
193
Delete events
35
Modification events
| (PID) Process: | (3504) jucheck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy\jucheck |
| Operation: | write | Name: | Method |
Value: jau-m | |||
| (PID) Process: | (3864) jp2launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1675955855080 | |||
| (PID) Process: | (3864) jp2launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.roaming.profile |
Value: false | |||
| (PID) Process: | (3864) jp2launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.version |
Value: 8 | |||
| (PID) Process: | (3864) jp2launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expired.version |
Value: 11.271.2 | |||
| (PID) Process: | (3864) jp2launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.browser.path |
Value: C:\Program Files\Internet Explorer\IEXPLORE.EXE | |||
| (PID) Process: | (3504) jucheck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy\jucheck |
| Operation: | write | Name: | LastUpdateBeginTime |
Value: Sat, 14 Jun 2025 13:43:41 GMT | |||
| (PID) Process: | (3504) jucheck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy\jucheck |
| Operation: | delete value | Name: | LocalFileName |
Value: | |||
| (PID) Process: | (3504) jucheck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy\jucheck |
| Operation: | delete value | Name: | InstallOptions |
Value: | |||
| (PID) Process: | (3504) jucheck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\JavaSoft\Java Update\Policy\jucheck |
| Operation: | delete value | Name: | UpdateDescription |
Value: | |||
Executable files
5
Suspicious files
10
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | jucheck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:8828A172FC752BA8771E41AE4AE8F60A | SHA256:4AEC4A6863AC37A2462BE2265C3F106AD9AE6143694096CC829BBC08A0CF05C6 | |||
| 3504 | jucheck.exe | C:\Users\admin\AppData\Local\Temp\jusched.log | text | |
MD5:A83B1927C7D44CAD95A5FDE35B2CA4C5 | SHA256:15014C41782B8D1DA77F76C7F4CE7F6D8D45BDA83F6E969F441D541C14BE0A0A | |||
| 3504 | jucheck.exe | C:\Users\admin\AppData\Local\Temp\au-descriptor-1.8.0_451-b10.xml | xml | |
MD5:A171AD503E5FF3810E3D50D8E99F5C4C | SHA256:2432429D010EB4BDC79540F489B61A2AE6C042DC1ECE1BA6E034E0A8B1EAAC29 | |||
| 3864 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\securitypack.jar | java | |
MD5:579F40A1C25FDE94A61ED52A00CAB0B4 | SHA256:D3624969251BE360F2821EB0C5863172EC67B752587EE35693B600790E06CBD0 | |||
| 3504 | jucheck.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:E16E473F95B2D7B0B6551E738528845C | SHA256:88966C250D90C8135E821D83604BD96F66C8444C1E6A92623A3D434CCFB7F431 | |||
| 3864 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\baseline.versions | text | |
MD5:92DBCB0A62D10EED5787E79EA539EA5F | SHA256:3481790408FD8E52189FD797088BF5B68B50FF7BDBE81A4B22761C2B9BAD74AE | |||
| 3864 | jp2launcher.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\83aa4cc77f591dfc2374580bbd95f6ba_bb926e54-e3ca-40fd-ae90-2764341e7792 | binary | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 3864 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\blacklisted.certs | text | |
MD5:8273F70416F494F7FA5B6C70A101E00E | SHA256:583500B76965EB54B03493372989AB4D3426F85462D1DB232C5AE6706A4D6C58 | |||
| 3504 | jucheck.exe | C:\Users\admin\AppData\Local\Temp\jre-8u451-windows-au.exe | executable | |
MD5:4562E554BDF111F2969468E7202BA1E2 | SHA256:116BDE30C6041C5F5D1F3C9581E3A6BD25854E604037A08C60ABA4C12C79E5A7 | |||
| 3504 | jucheck.exe | C:\Users\admin\AppData\Local\Temp\jds1542875.tmp | executable | |
MD5:4562E554BDF111F2969468E7202BA1E2 | SHA256:116BDE30C6041C5F5D1F3C9581E3A6BD25854E604037A08C60ABA4C12C79E5A7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
25
DNS requests
13
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3504 | jucheck.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
3864 | jp2launcher.exe | POST | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
3864 | jp2launcher.exe | POST | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
3864 | jp2launcher.exe | POST | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
3864 | jp2launcher.exe | POST | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
6160 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3504 | jucheck.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3504 | jucheck.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7052 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3504 | jucheck.exe | 104.102.53.139:443 | javadl-esd-secure.oracle.com | AKAMAI-AS | DE | whitelisted |
3504 | jucheck.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3864 | jp2launcher.exe | 104.102.53.139:443 | javadl-esd-secure.oracle.com | AKAMAI-AS | DE | whitelisted |
3864 | jp2launcher.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
javadl-esd-secure.oracle.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
javadl.oracle.com |
| whitelisted |
sdlc-esd.oracle.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3864 | jp2launcher.exe | Potentially Bad Traffic | ET INFO Vulnerable Java Version 1.8.x Detected |
3864 | jp2launcher.exe | Potentially Bad Traffic | ET INFO Vulnerable Java Version 1.8.x Detected |