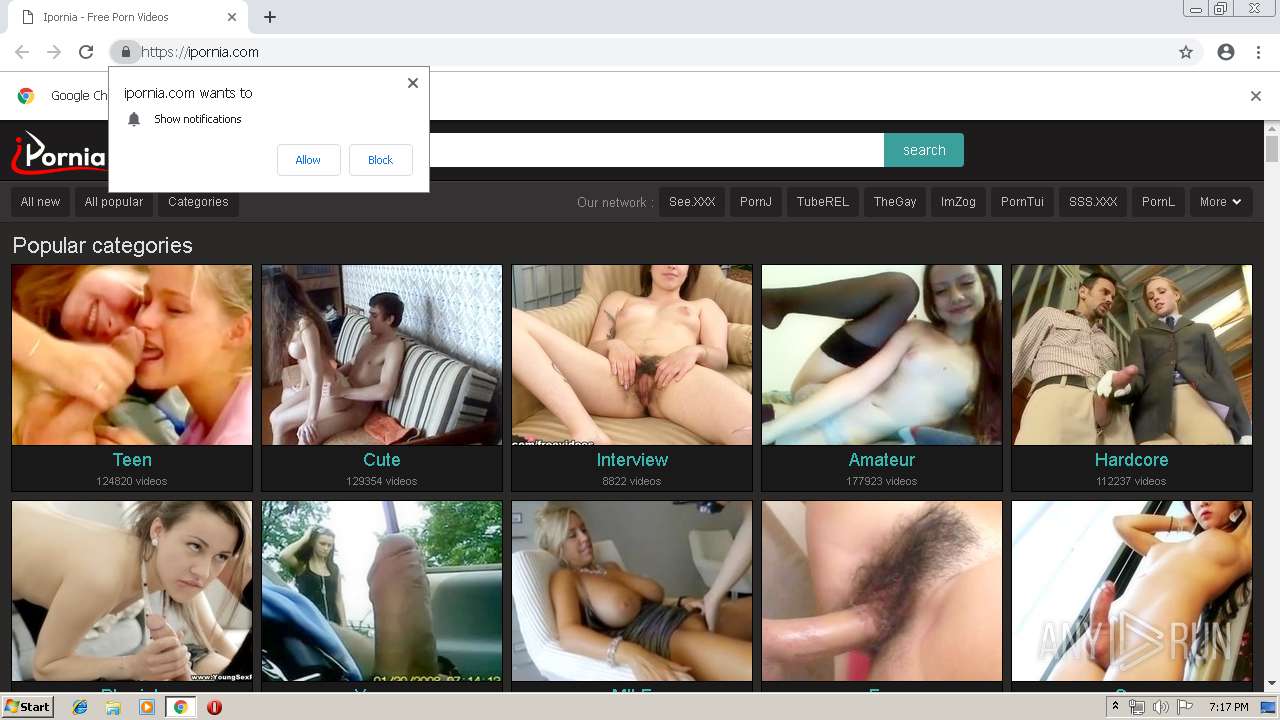
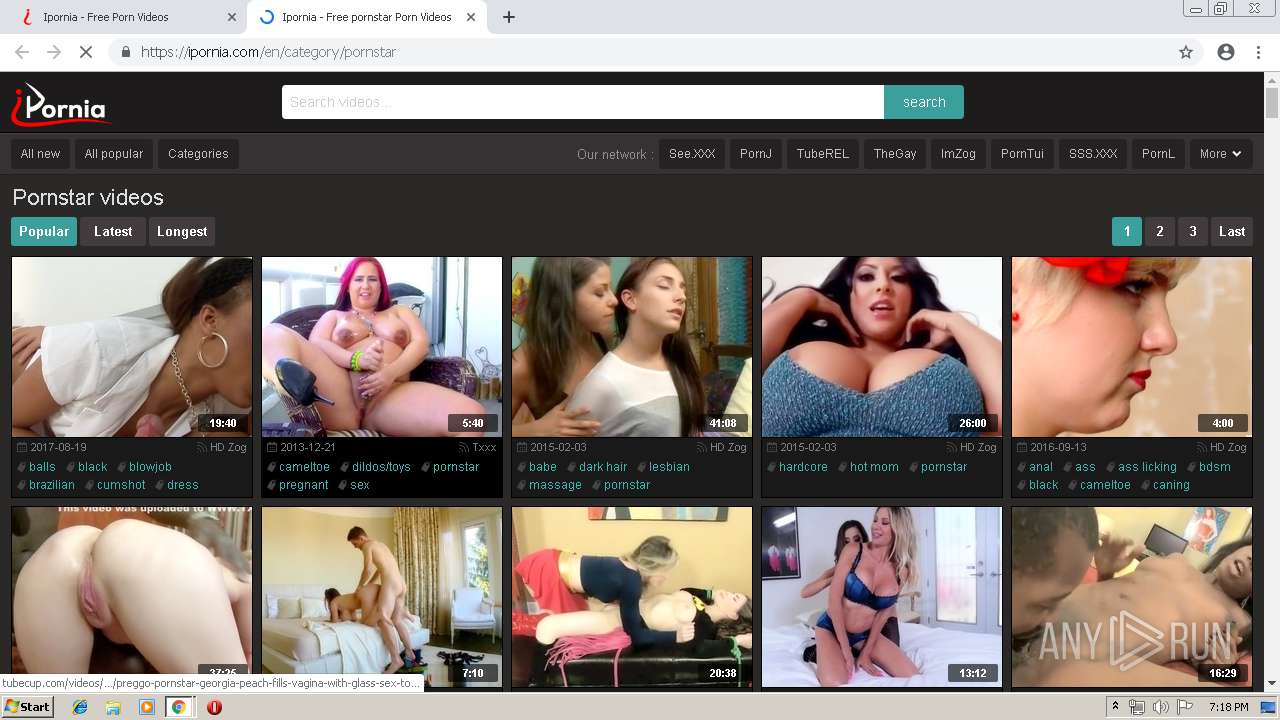
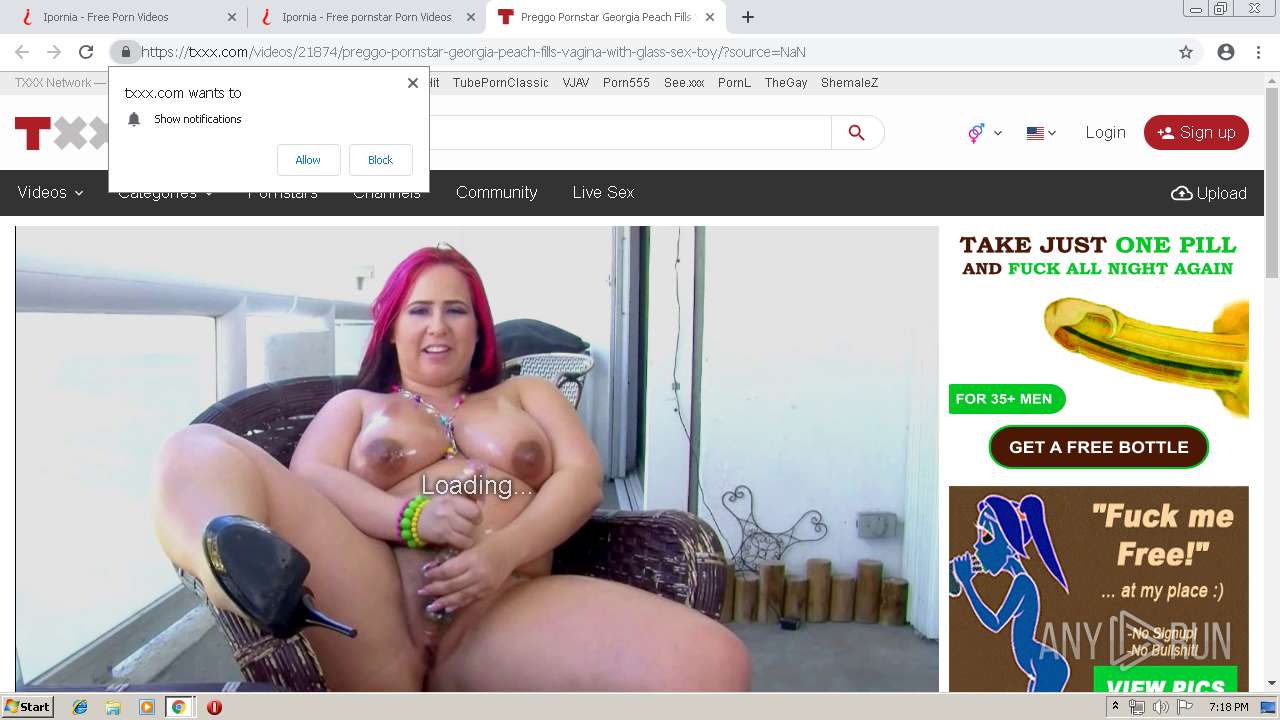
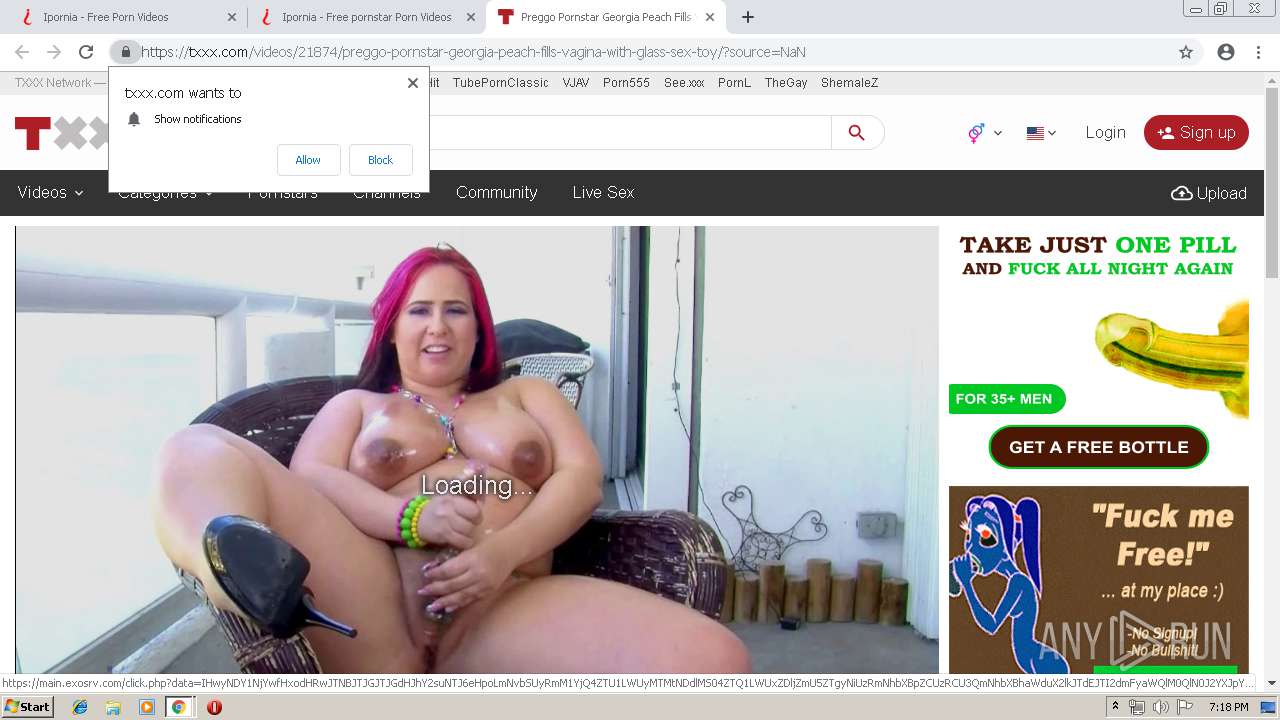
| URL: | https://ipornia.com |
| Full analysis: | https://app.any.run/tasks/3c0ee023-e3d3-4e85-a504-26e552376d5f |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 18:16:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C2771B29FC0D415442F418652B8C0253 |
| SHA1: | C5FC4DB9E83E678E10F8960F8F2C9EF97A8CC658 |
| SHA256: | 81981F8537C9C5A7DB52E1FAEA972EE2555F0397A913D887E5B2DC85EBF57E9E |
| SSDEEP: | 3:N8l4E2:2l4d |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks for external IP
- chrome.exe (PID: 2580)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2580)
INFO
Creates files in the user directory
- chrome.exe (PID: 2580)
Application launched itself
- chrome.exe (PID: 2580)
Reads settings of System Certificates
- chrome.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12354393284687166791 --mojo-platform-channel-handle=5272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4827542874485911416 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4827542874485911416 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4824 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10938746056101030860 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10938746056101030860 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1773964976025225740 --mojo-platform-channel-handle=4128 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --service-pipe-token=5326717142619875758 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5326717142619875758 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11531350028540903888 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11531350028540903888 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5392 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3485375157512741252 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3485375157512741252 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14717453831657450019 --mojo-platform-channel-handle=5064 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --service-pipe-token=14404017145720924772 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14404017145720924772 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14434002482281354557 --mojo-platform-channel-handle=3852 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
711
Read events
606
Write events
100
Delete events
5
Modification events
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2580-13200689827666375 |
Value: 259 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2580-13200689827666375 |
Value: 259 | |||
Executable files
0
Suspicious files
155
Text files
197
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cc896bef-a39f-4403-a329-e075036bb8df.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
130
DNS requests
93
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
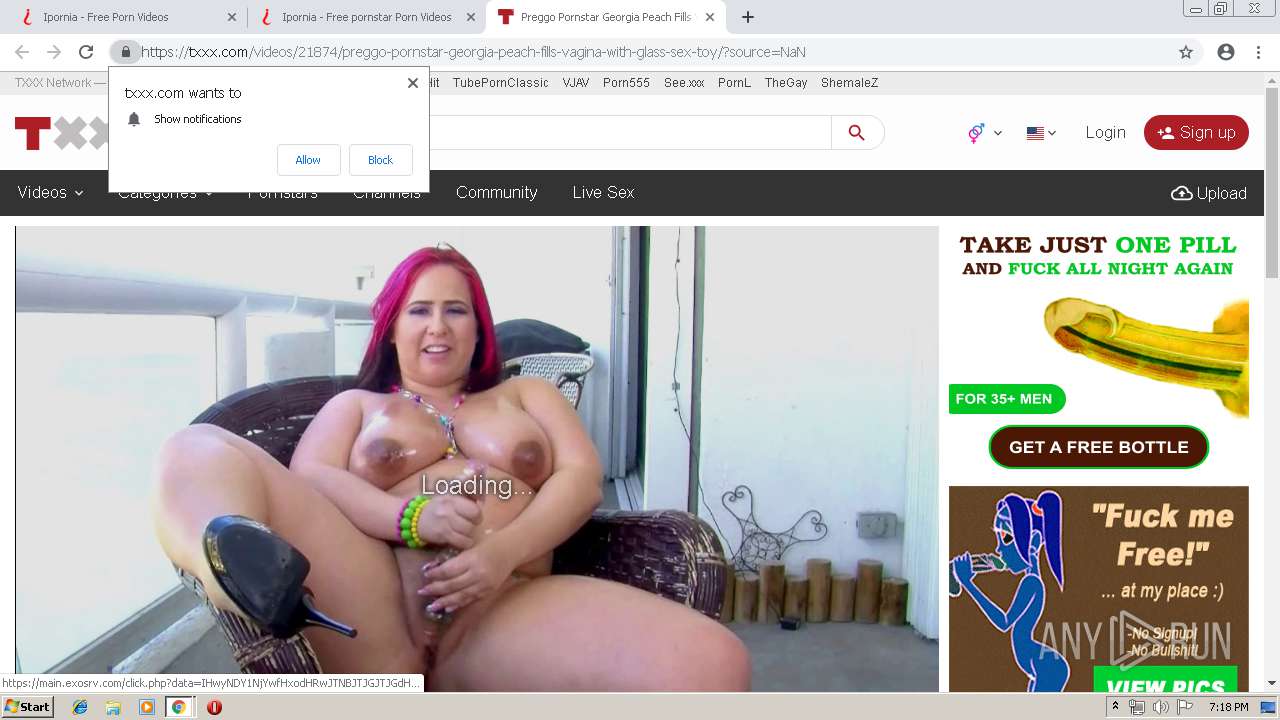
2580 | chrome.exe | GET | 302 | 88.85.94.233:80 | http://linestomo.co/out?zoneId=4103858&sId=GB&sId2=ipornia.com | NL | — | — | whitelisted |
2580 | chrome.exe | GET | 301 | 104.20.72.110:80 | http://www.txxx.com/videos/21874/preggo-pornstar-georgia-peach-fills-vagina-with-glass-sex-toy/?source=NaN | US | — | — | suspicious |
2580 | chrome.exe | GET | 200 | 88.85.94.233:80 | http://linestomo.co/bO3PVQ0RPS3TJUyVaWWXQY9ZZaGbYc2dMe2fRgmhOiDjQk5lMmjnko3pYqmrUs3tNuWvYwwxNyDzVAlBMCDDcE0FYGjHFIjJYKTLkM0NNOzPQQmRcS0TlUkVPWTXQYxZMaDbMc4dNeTfggmheimj9kulZmUnlokpPqTrMs4tOuDvIwyxOyDzEA | NL | html | 2.83 Kb | whitelisted |
2580 | chrome.exe | POST | 302 | 88.85.94.233:80 | http://linestomo.co/cEGFFGzHcIzJ9KwLdMDN1ONPeQmRcS0TTUWVpWJXNYEZ1aTbUcXdheOfVgFhUiyjTkWlpmFnMokp1qqrVsXtpuKvRwWxRyDzSAkBdCKDeEWFIGyHRImJtKZLbMUNZO1PWQkRNSSTaUGVJWtXOYXZValbVczdFe2fZgFhhiNjak2lJmHnVomp5qZrVs0t5u2vSwUxcy1zbAGBRCIDZEHFZGjHbIXJRK6LSMUNdOJPdQWRRSpTNUGVtWaXbYVZEaybWcmdpeVfegkh5iqjVkXldmNnVoGpdq4rTs0tRuZvMwUx9yUzYAzBJCODREFFkG1HWIVJRKrLeMlNpOEPSQmRlSaTaUmVtW6XTYUZdaRbac0d5e6fUgThViNjekllUmxnTomppqFrdsytZuyvcwmxlykzPAWBRCmDNEjFNGkHZIjJgK0LOMTNIO5PNQ2RJSlTNUzVVWmXMYDZQa1bZcTdAe3fNgGhIixjYk2lEm5nNoDpcq0rJsntNuJvZwDx0y0zMATBACzDOEDFUG4HJInJpKvLbMmNVOJPZQDR0SzTOUDVgWyXMYjZgaxb | NL | compressed | 2.83 Kb | whitelisted |
2580 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
2580 | chrome.exe | GET | 200 | 173.194.138.199:80 | http://r2---sn-aigzrn7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.192.69.22&mm=28&mn=sn-aigzrn7d&ms=nvh&mt=1556216093&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2580 | chrome.exe | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.6 Kb | whitelisted |
2580 | chrome.exe | GET | 200 | 13.32.222.187:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2580 | chrome.exe | 104.28.7.111:443 | ipornia1.johnleslieporn.com | Cloudflare Inc | US | shared |
2580 | chrome.exe | 94.31.29.128:443 | cdn1ht.traffichaus.com | netDNA | GB | malicious |
2580 | chrome.exe | 172.64.108.31:443 | ipornia1.johnholmespenis.com | Cloudflare Inc | US | shared |
2580 | chrome.exe | 205.185.216.42:443 | static.exosrv.com | Highwinds Network Group, Inc. | US | whitelisted |
2580 | chrome.exe | 95.211.229.247:443 | syndication.exosrv.com | LeaseWeb Netherlands B.V. | NL | suspicious |
2580 | chrome.exe | 104.27.5.88:443 | st.tubecorporate.com | Cloudflare Inc | US | shared |
2580 | chrome.exe | 216.58.206.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
— | — | 104.27.7.111:443 | script.bangdom.com | Cloudflare Inc | US | shared |
2580 | chrome.exe | 104.27.9.88:443 | ipornia.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
ipornia.com |
| whitelisted |
accounts.google.com |
| shared |
cdn1ht.traffichaus.com |
| whitelisted |
ipornia1.johnleslieporn.com |
| suspicious |
ipornia1.johnholmespenis.com |
| suspicious |
ts.clickadilla.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
syndication.exosrv.com |
| whitelisted |
static.exosrv.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2580 | chrome.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2580 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |