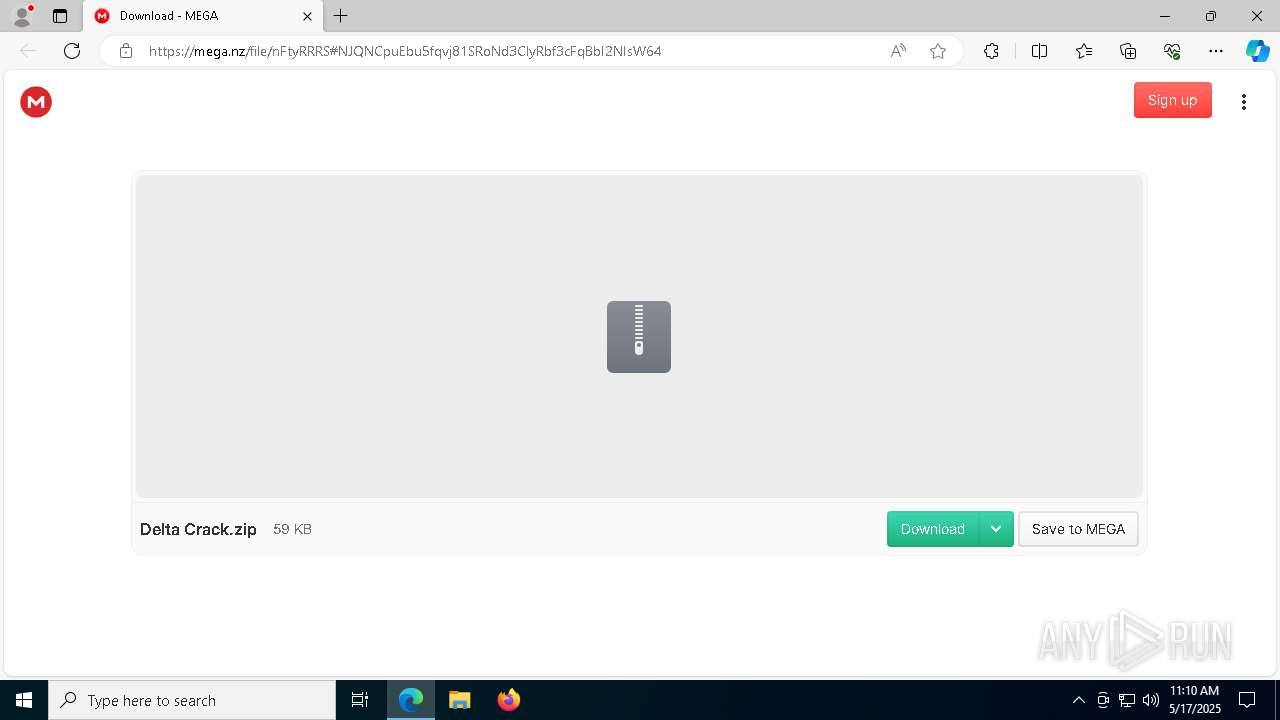
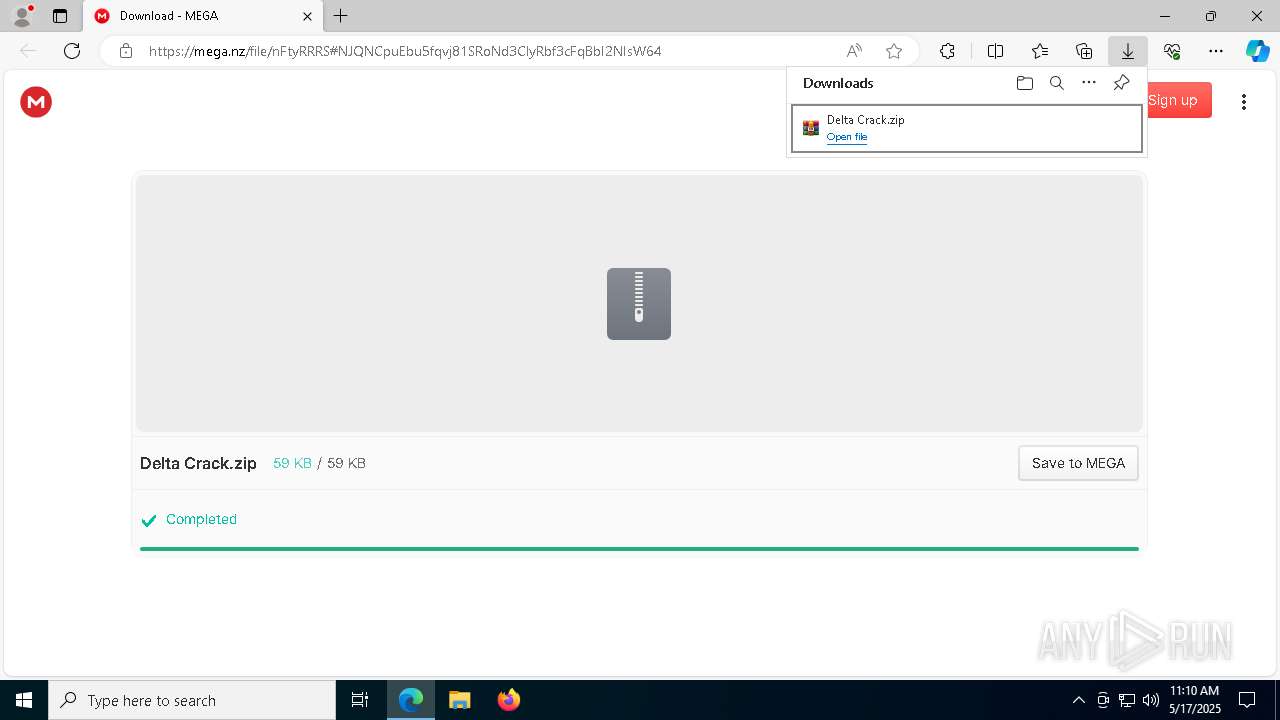
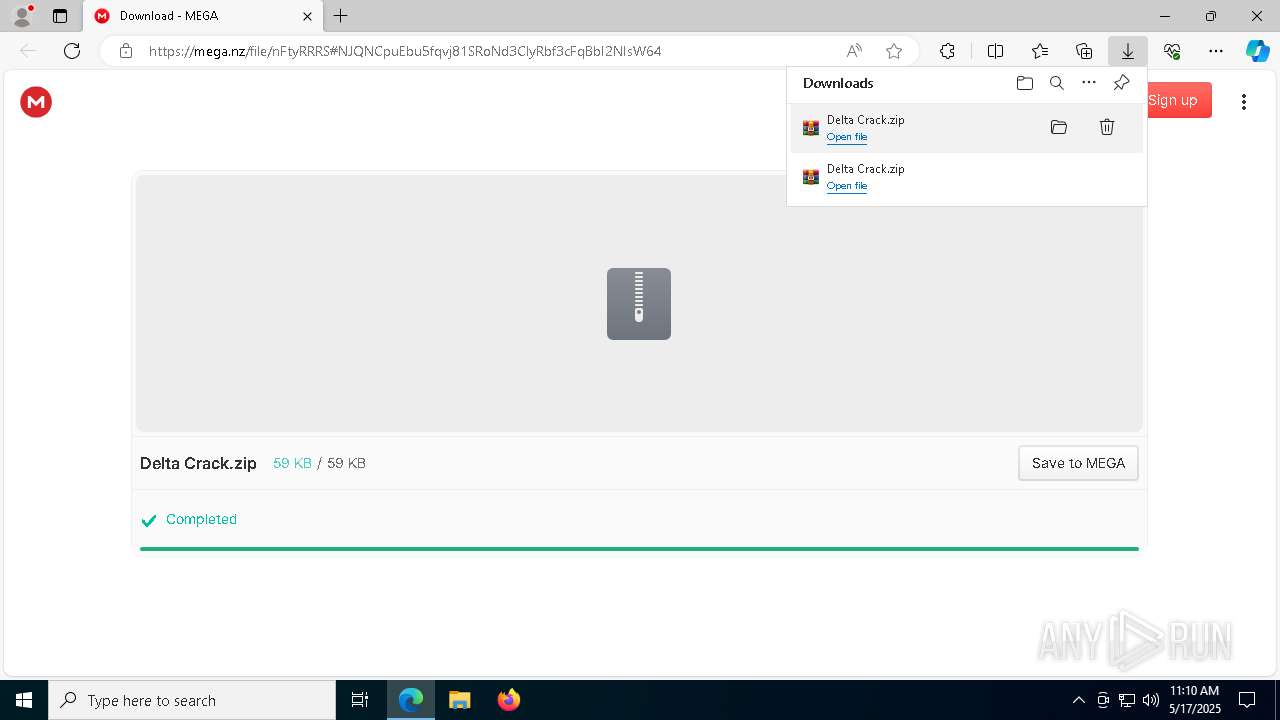
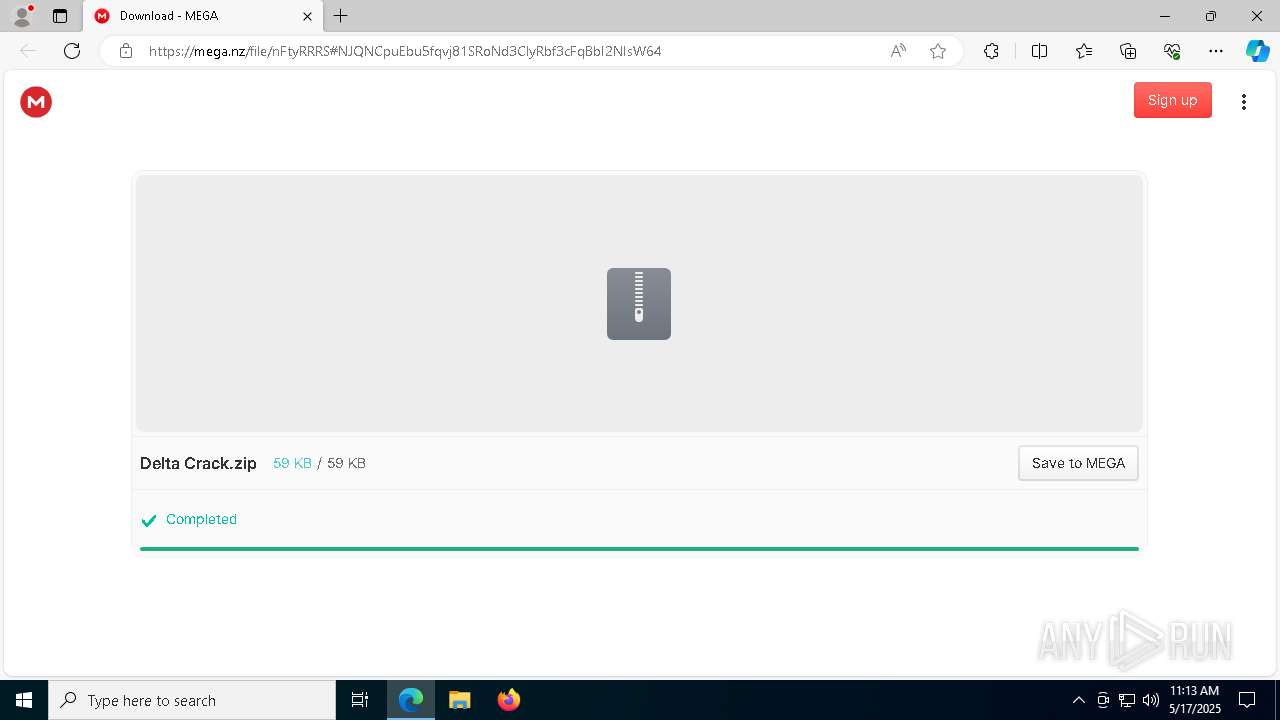
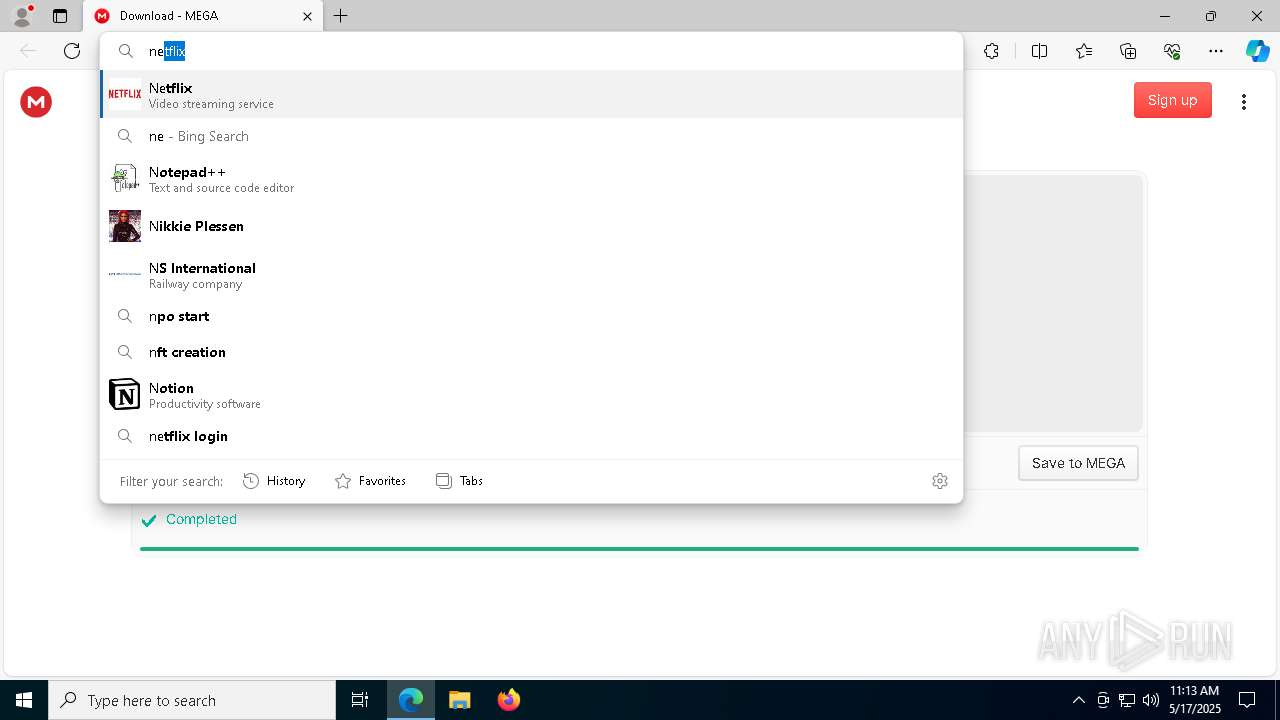
| URL: | https://mega.nz/file/nFtyRRRS#NJQNCpuEbu5fqvj81SRoNd3ClyRbf3cFqBbI2NIsW64 |
| Full analysis: | https://app.any.run/tasks/c4158cde-183e-4609-a061-f5d4bd83ece7 |
| Verdict: | Malicious activity |
| Threats: | XWorm is a remote access trojan (RAT) sold as a malware-as-a-service. It possesses an extensive hacking toolset and is capable of gathering private information and files from the infected computer, hijacking MetaMask and Telegram accounts, and tracking user activity. XWorm is typically delivered to victims' computers through multi-stage attacks that start with phishing emails. |
| Analysis date: | May 17, 2025, 11:10:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6FAD0F26C22C85A76104EA1DC1F44E63 |
| SHA1: | CF845D92BDACB1506B8BDC1E540F744690AFE9E5 |
| SHA256: | 81900481A6D49FED8074CB23246D0944E17262824DF7806822F8EF60E5EC4272 |
| SSDEEP: | 3:N8X/icG33hwrzjdvABhdNv:2RyhkjxkV |
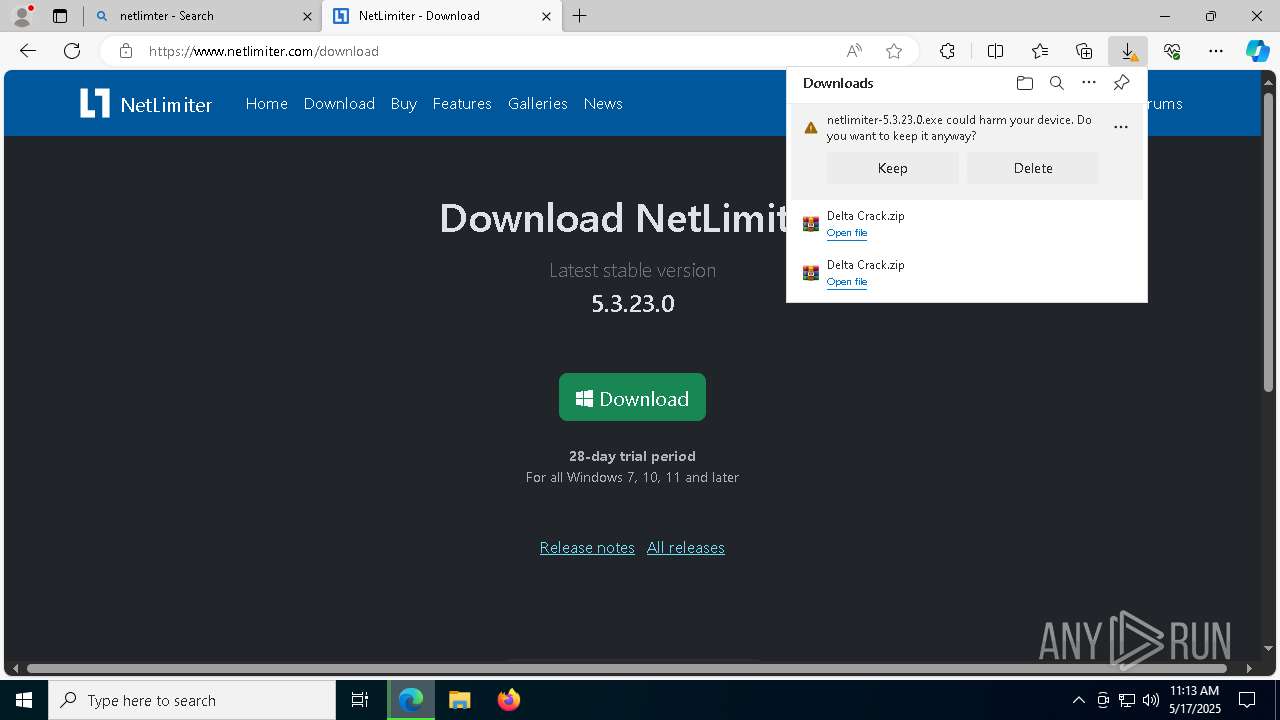
MALICIOUS
Changes the autorun value in the registry
- DeltaLoaderCrack.exe (PID: 6068)
Create files in the Startup directory
- DeltaLoaderCrack.exe (PID: 6068)
XWORM has been detected (YARA)
- DeltaLoaderCrack.exe (PID: 6068)
XWORM has been detected
- DeltaLoaderCrack.exe (PID: 6068)
SUSPICIOUS
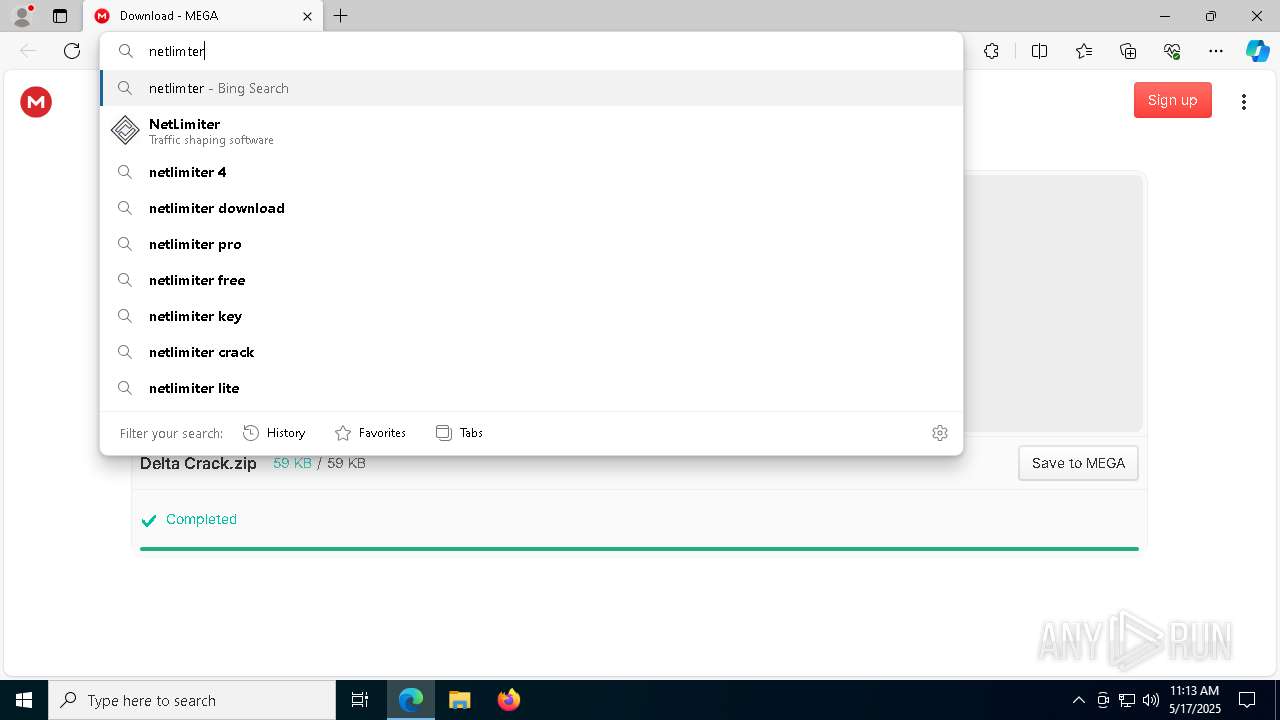
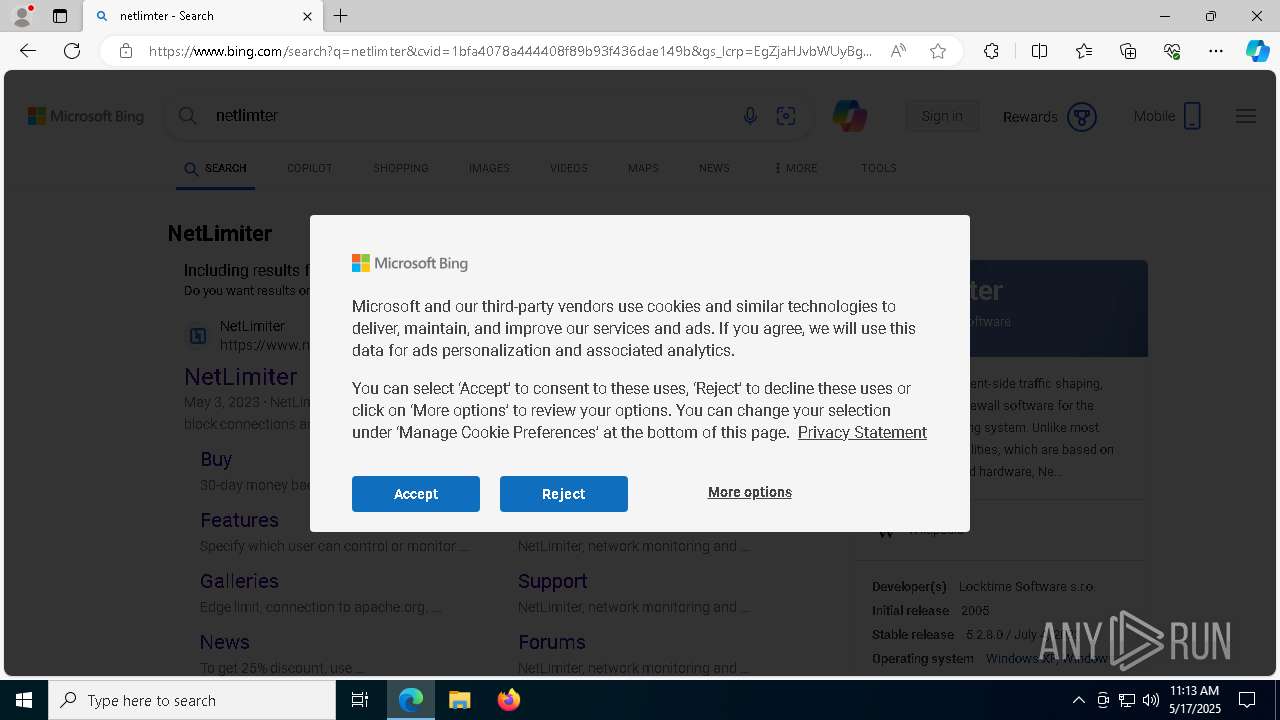
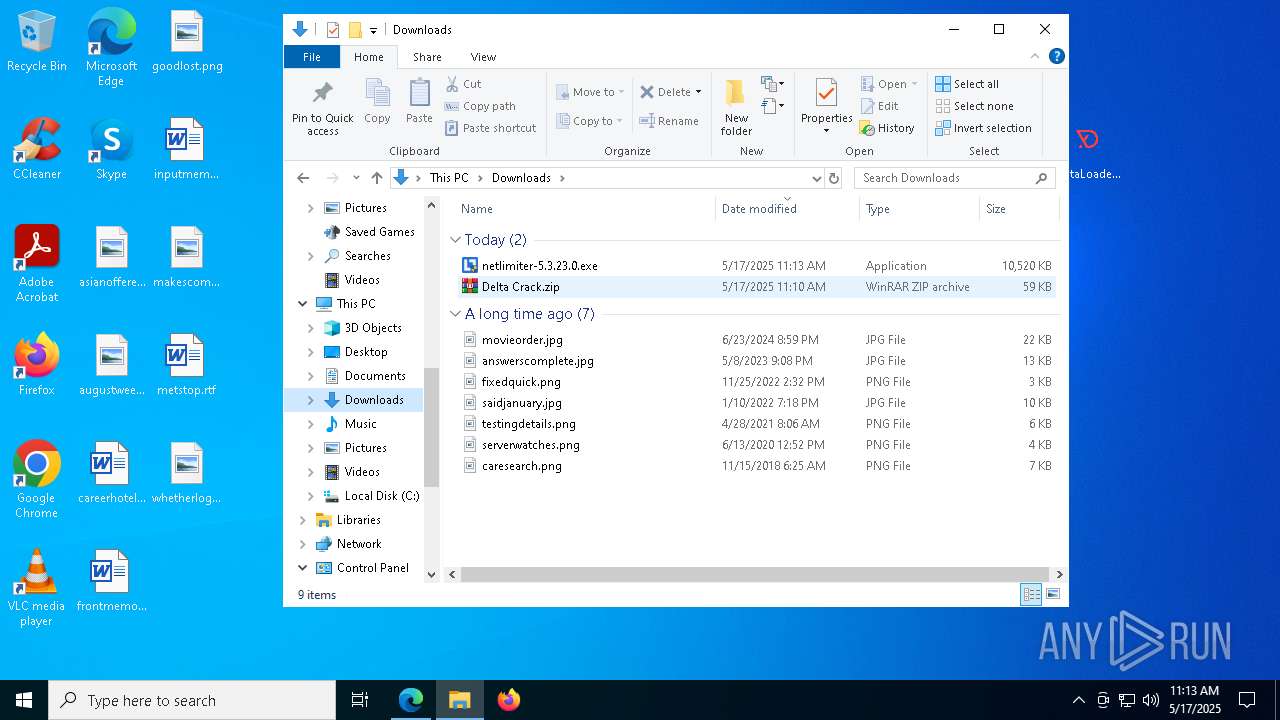
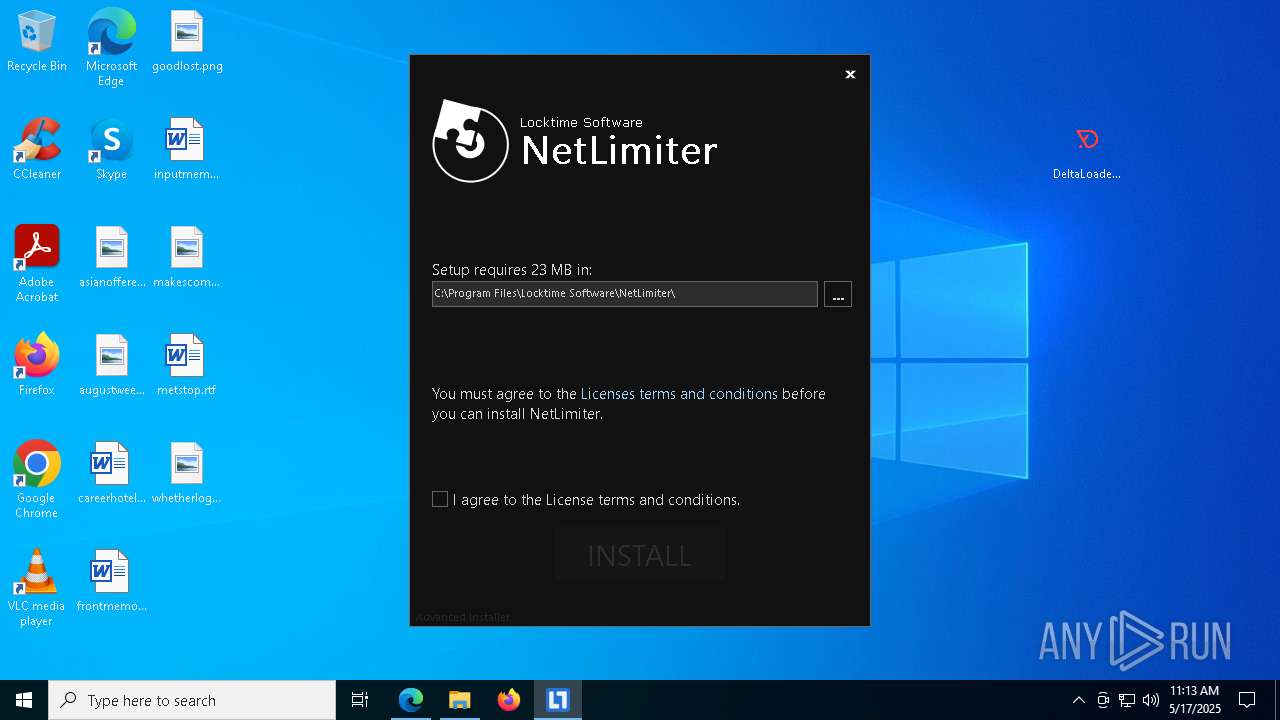
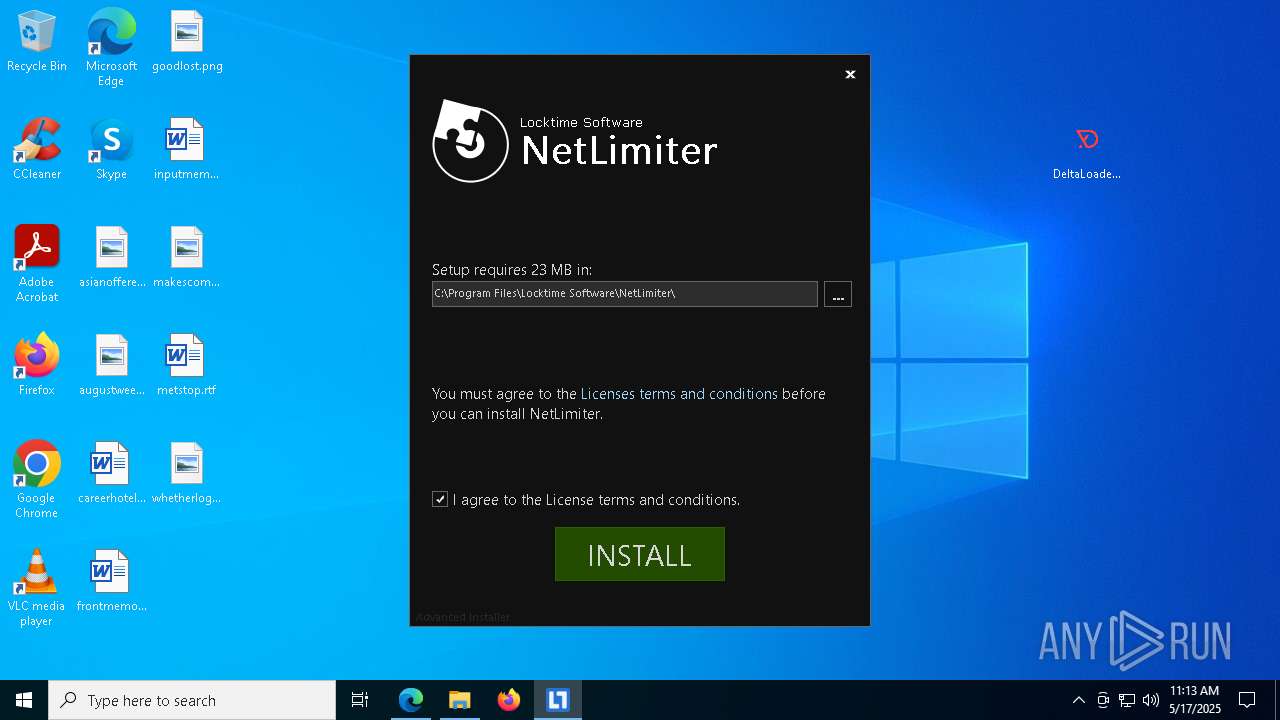
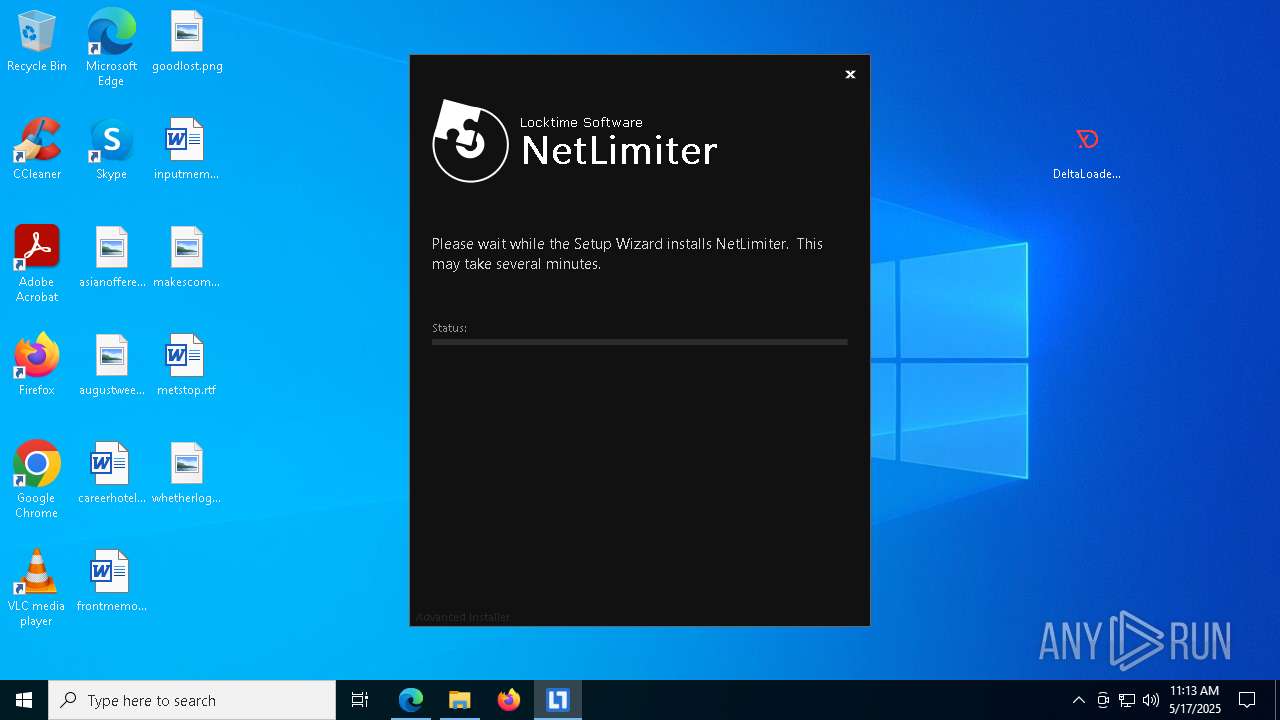
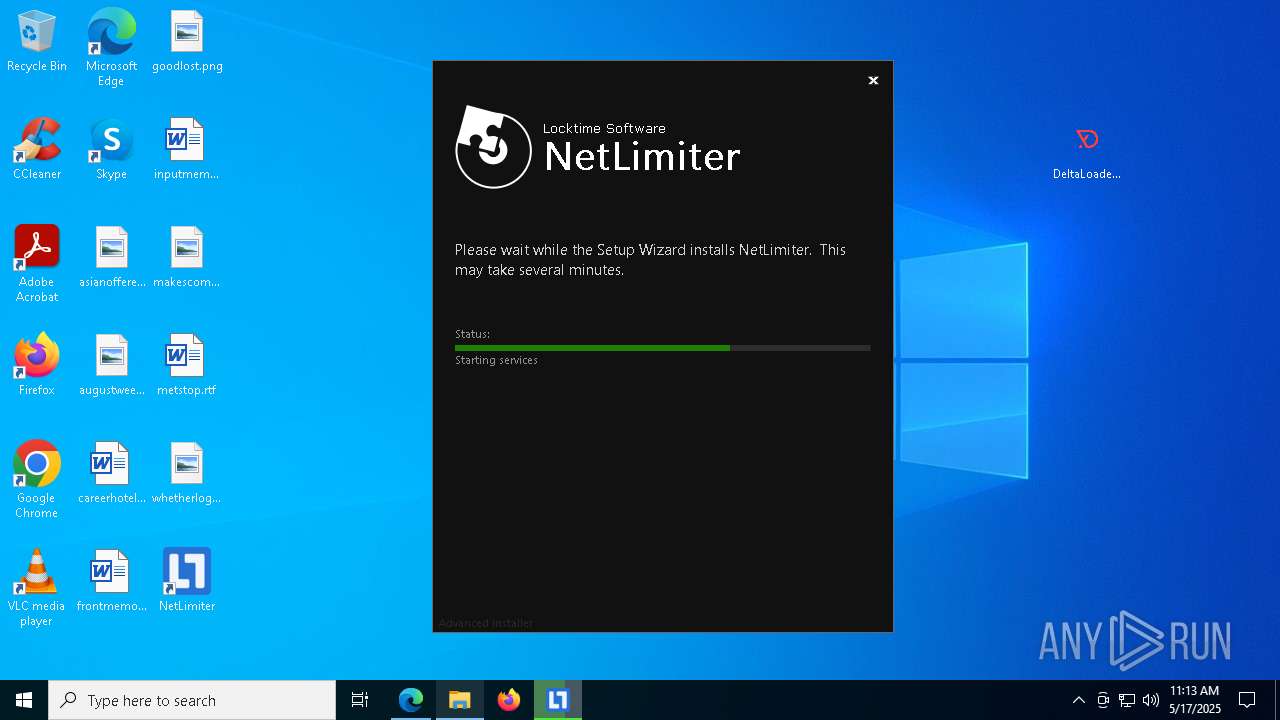
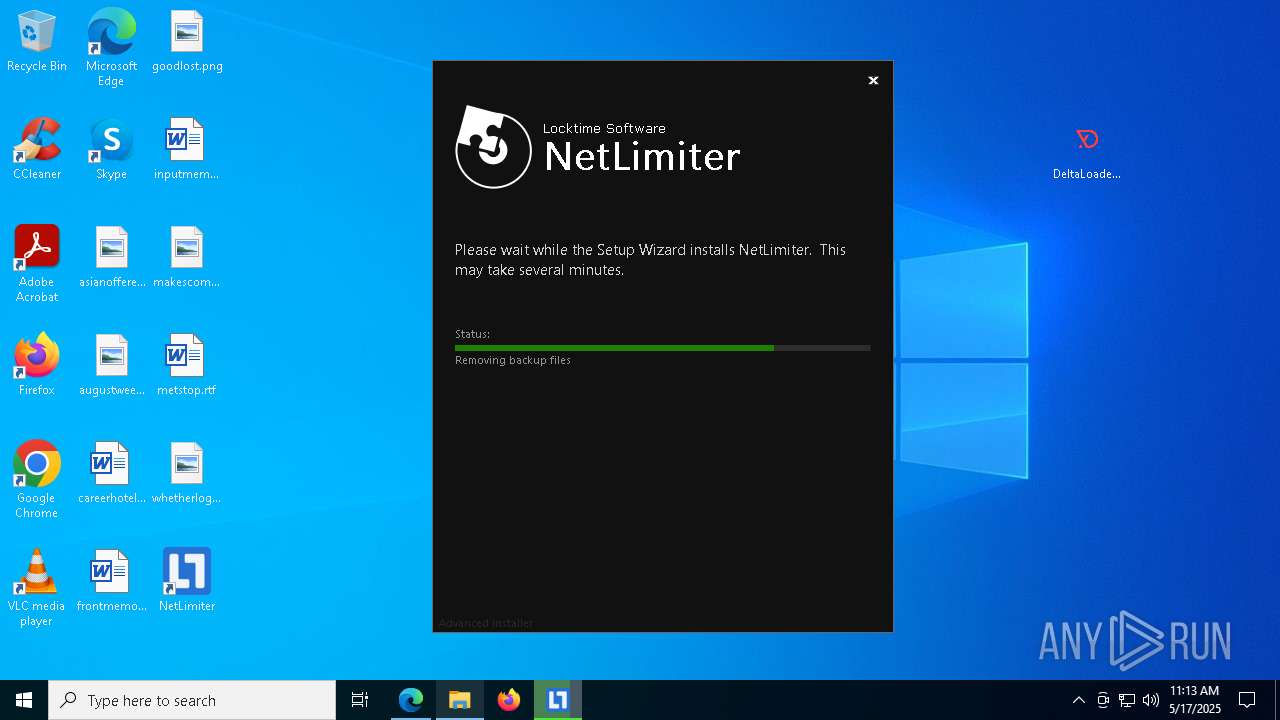
Executable content was dropped or overwritten
- DeltaLoaderCrack.exe (PID: 6068)
- netlimiter-5.3.23.0.exe (PID: 5164)
- netlimiter-5.3.23.0.exe (PID: 6044)
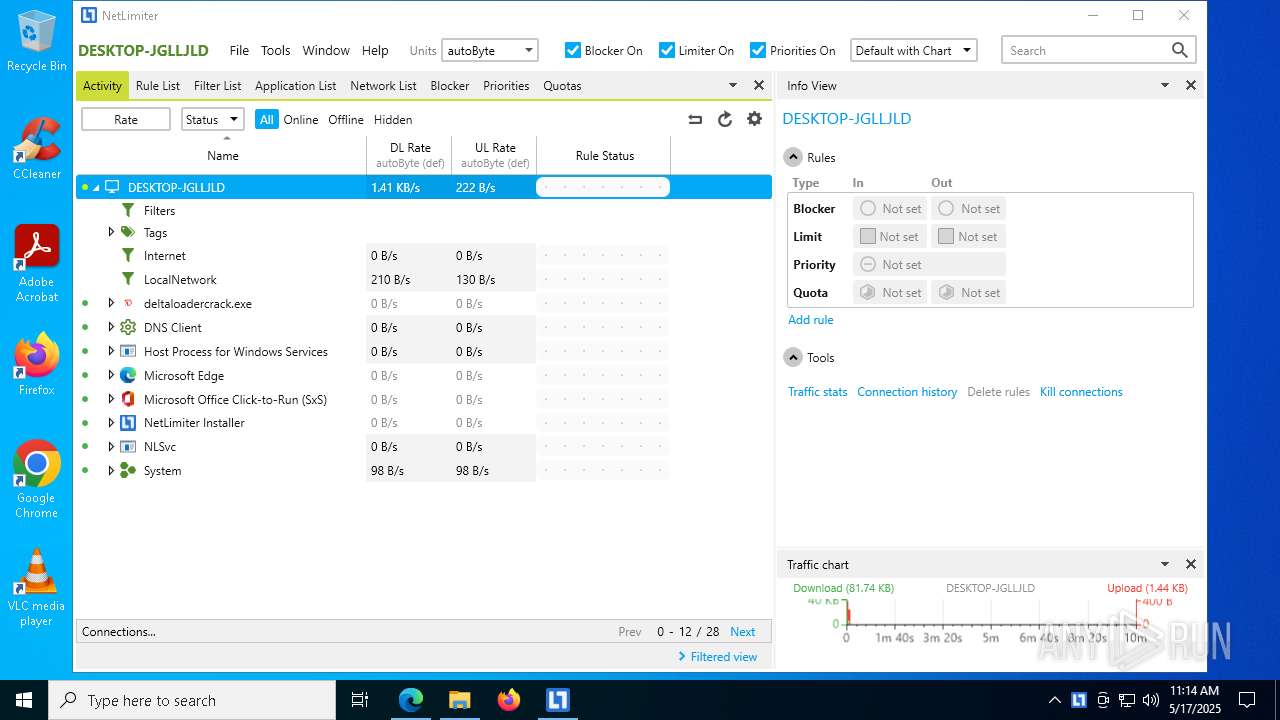
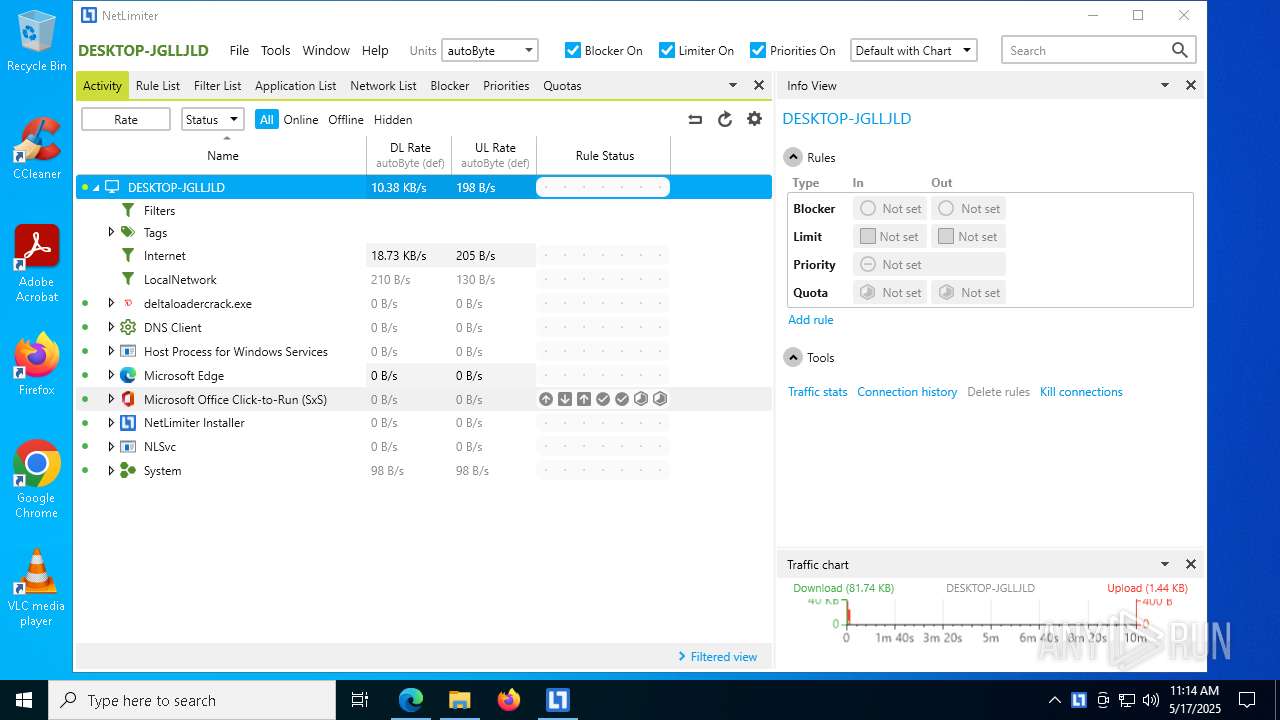
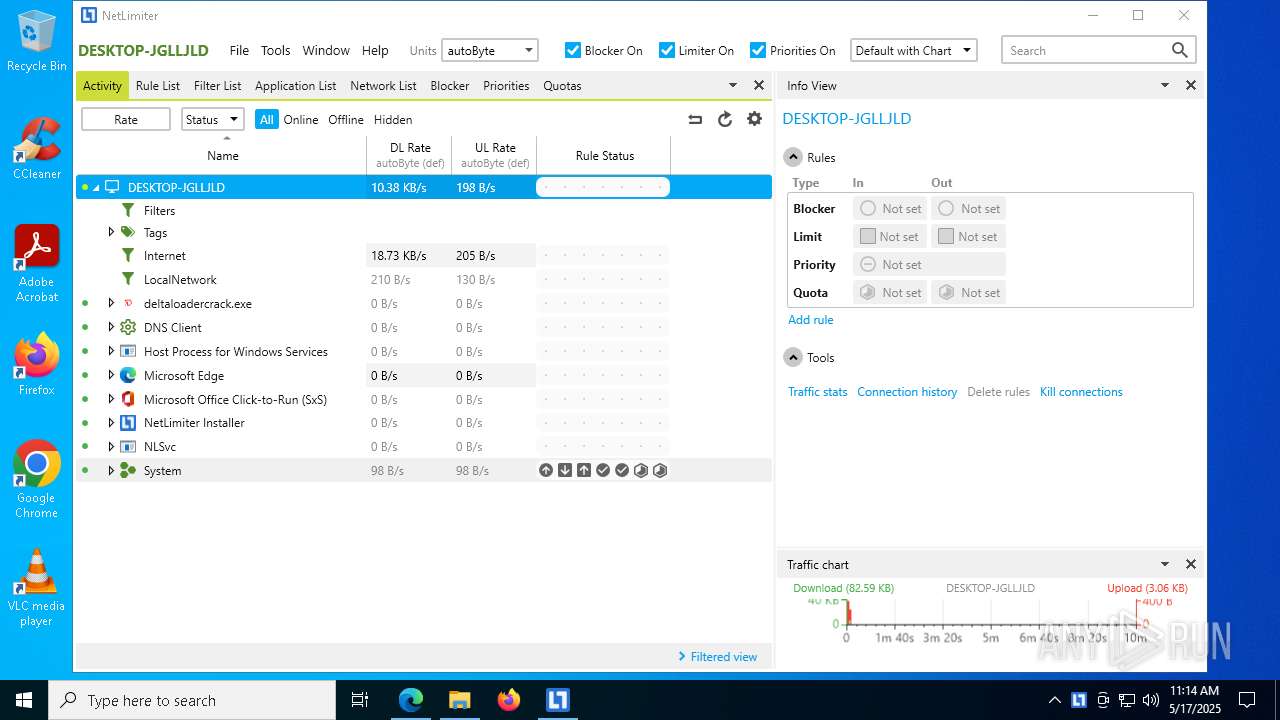
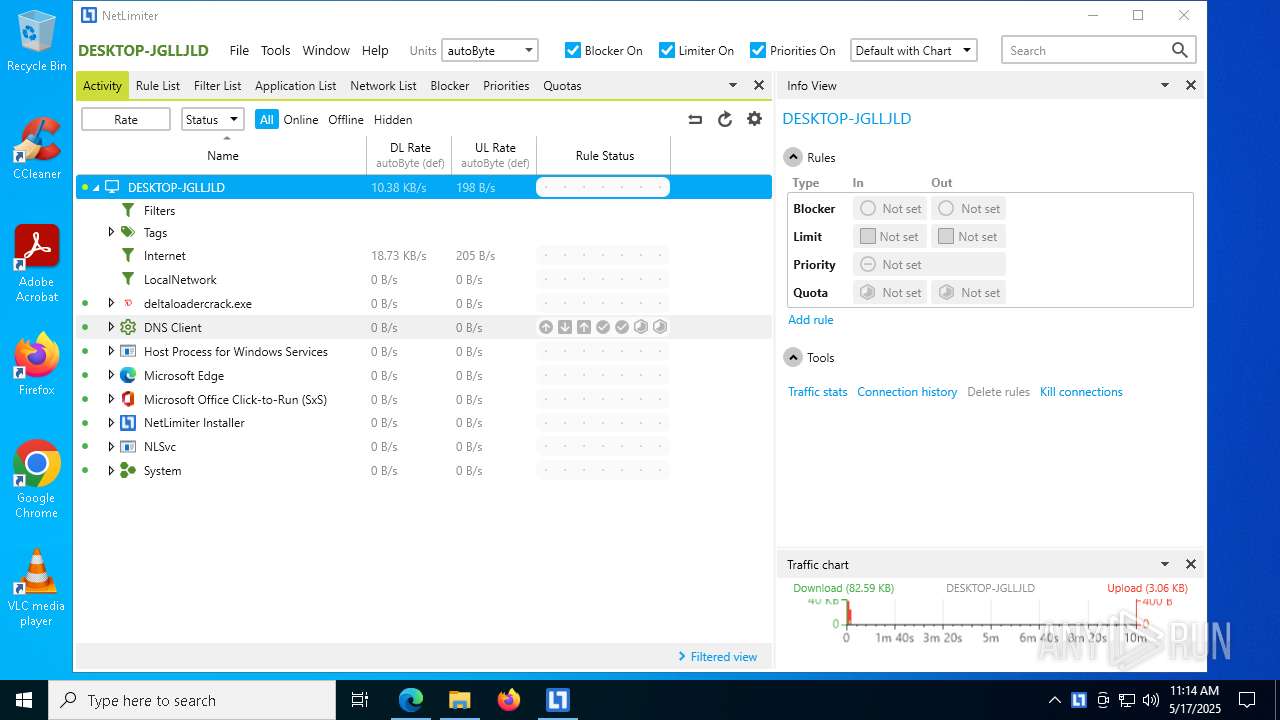
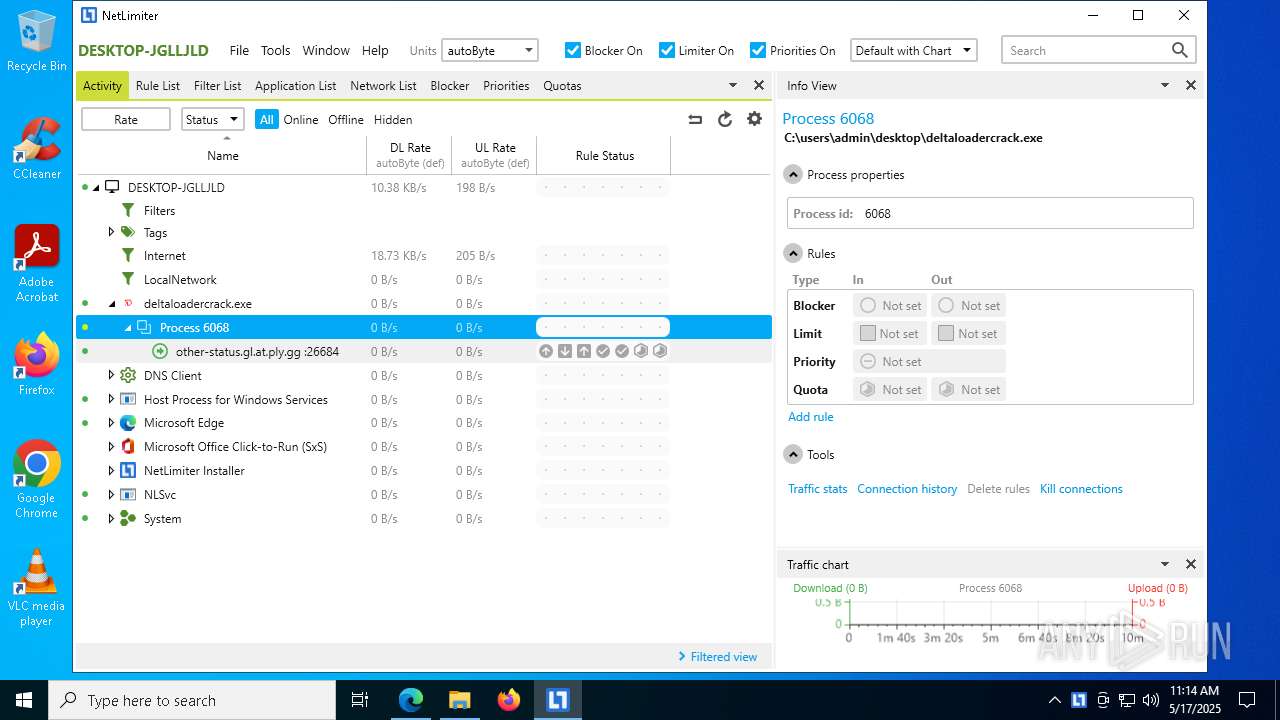
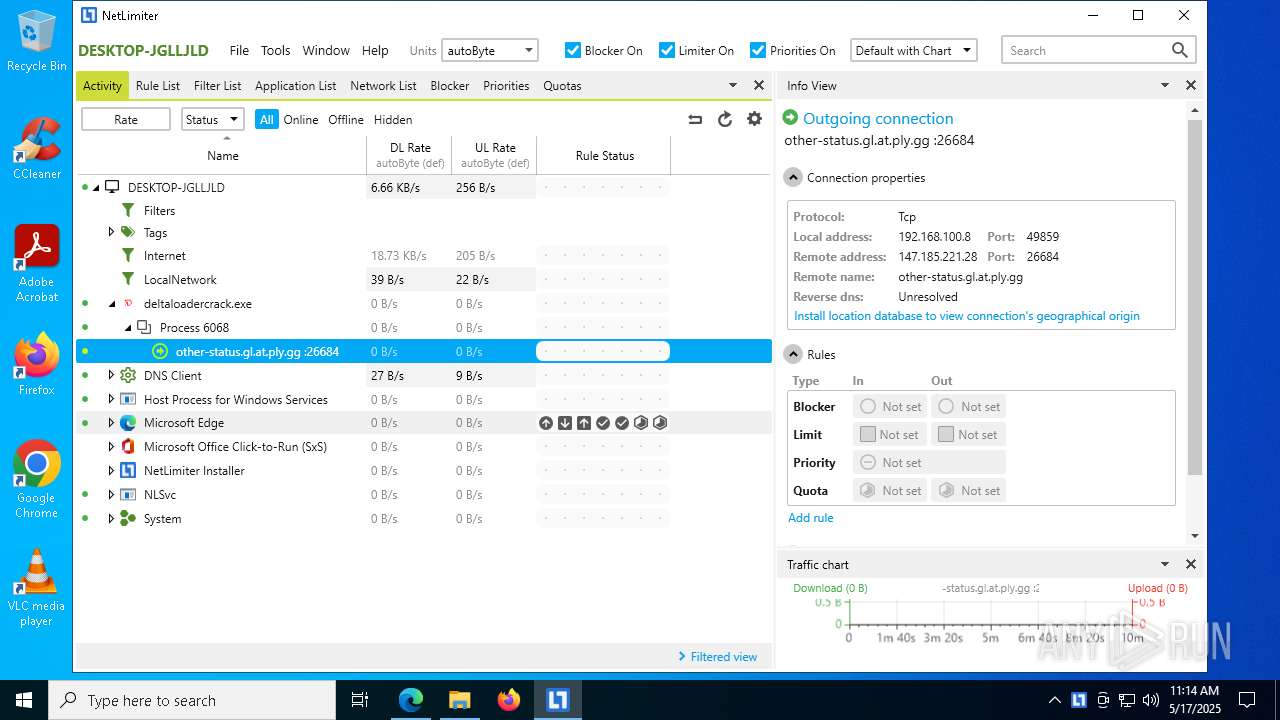
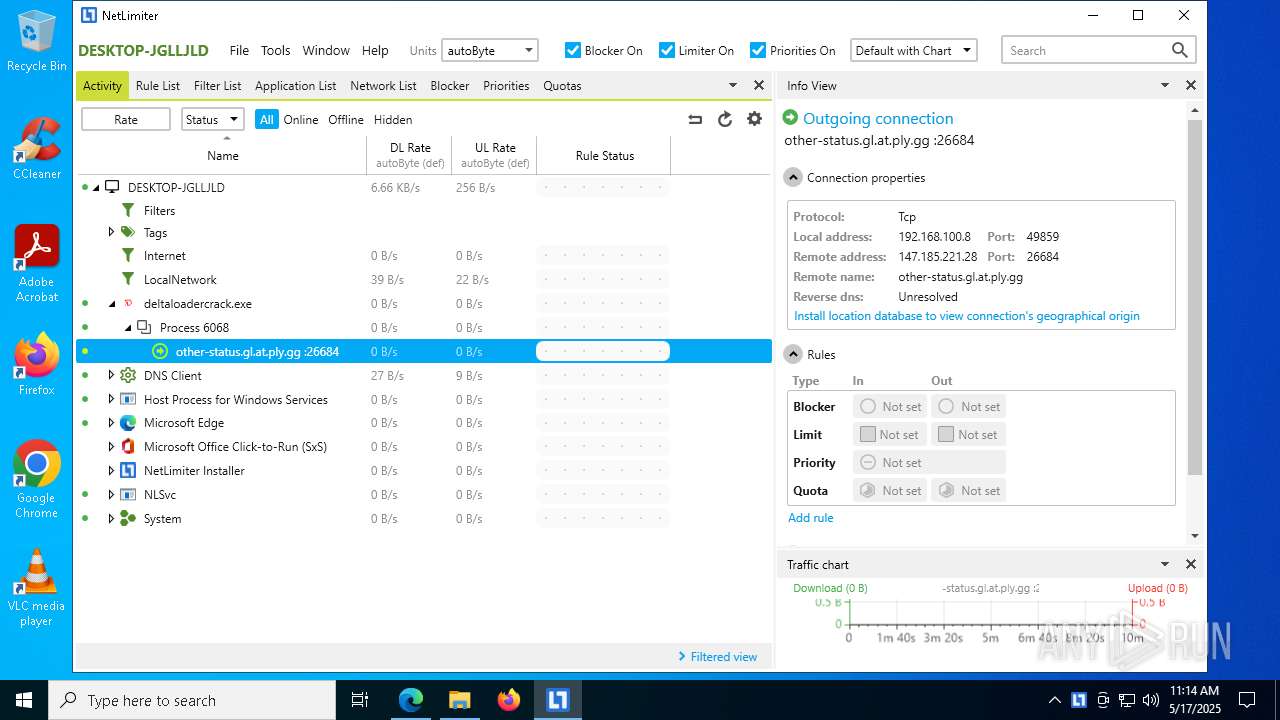
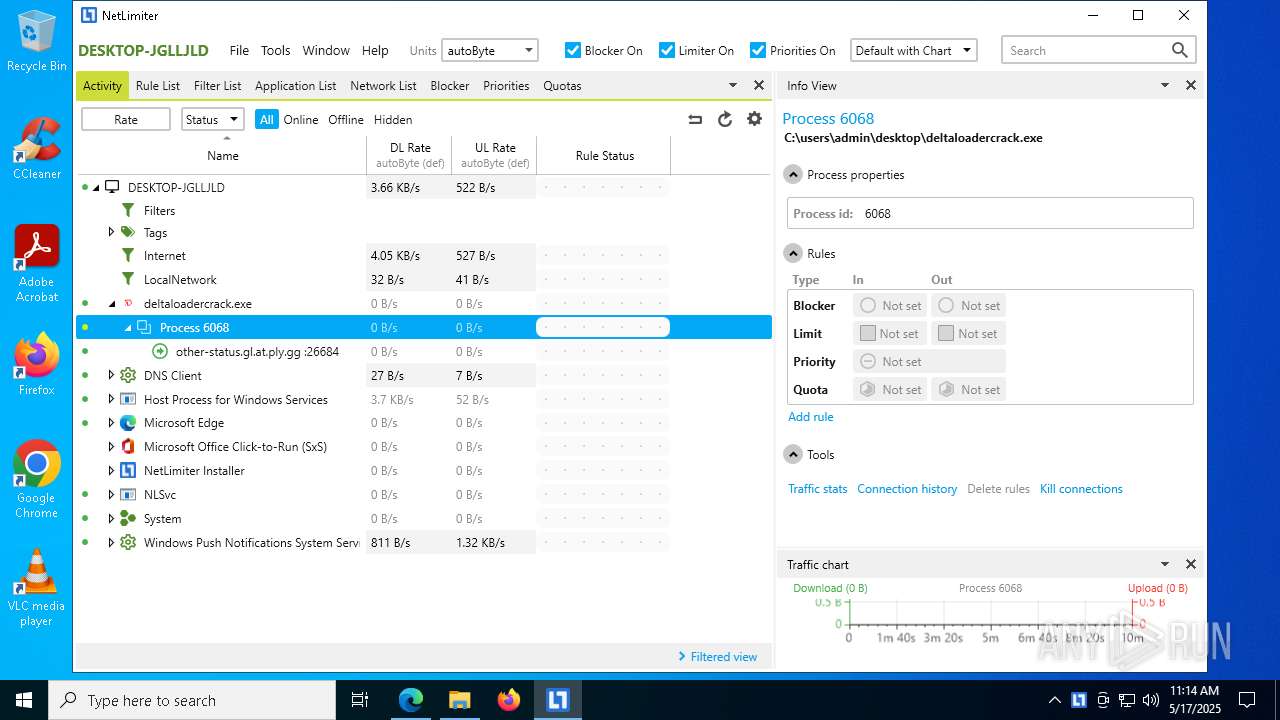
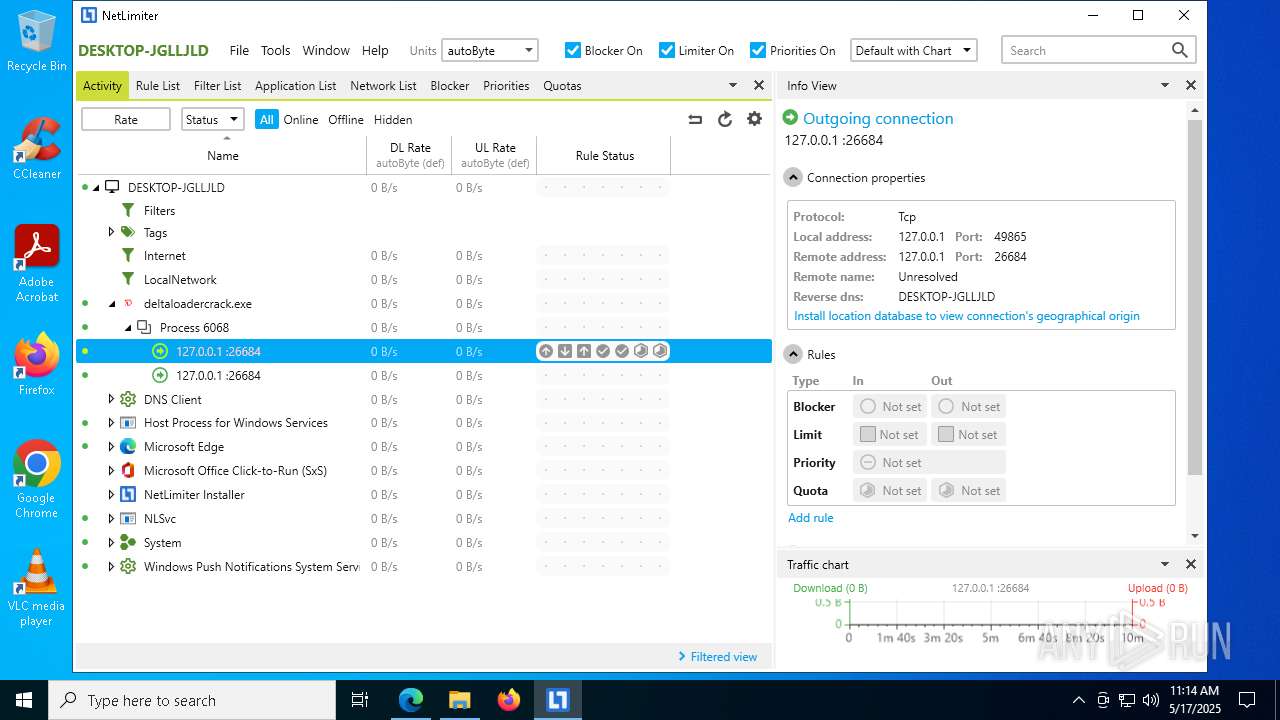
Connects to unusual port
- DeltaLoaderCrack.exe (PID: 6068)
Process drops legitimate windows executable
- netlimiter-5.3.23.0.exe (PID: 5164)
- netlimiter-5.3.23.0.exe (PID: 6044)
- msiexec.exe (PID: 2596)
- msiexec.exe (PID: 7084)
- msiexec.exe (PID: 7892)
The process drops C-runtime libraries
- msiexec.exe (PID: 2596)
- msiexec.exe (PID: 7084)
Detects AdvancedInstaller (YARA)
- netlimiter-5.3.23.0.exe (PID: 5164)
- msiexec.exe (PID: 7892)
There is functionality for taking screenshot (YARA)
- netlimiter-5.3.23.0.exe (PID: 5164)
Application launched itself
- netlimiter-5.3.23.0.exe (PID: 5164)
Executes as Windows Service
- VSSVC.exe (PID: 1228)
- NLSvc.exe (PID: 776)
Drops a system driver (possible attempt to evade defenses)
- netlimiter-5.3.23.0.exe (PID: 5164)
- msiexec.exe (PID: 7892)
INFO
Checks supported languages
- identity_helper.exe (PID: 5392)
- DeltaLoaderCrack.exe (PID: 6068)
Application launched itself
- msedge.exe (PID: 864)
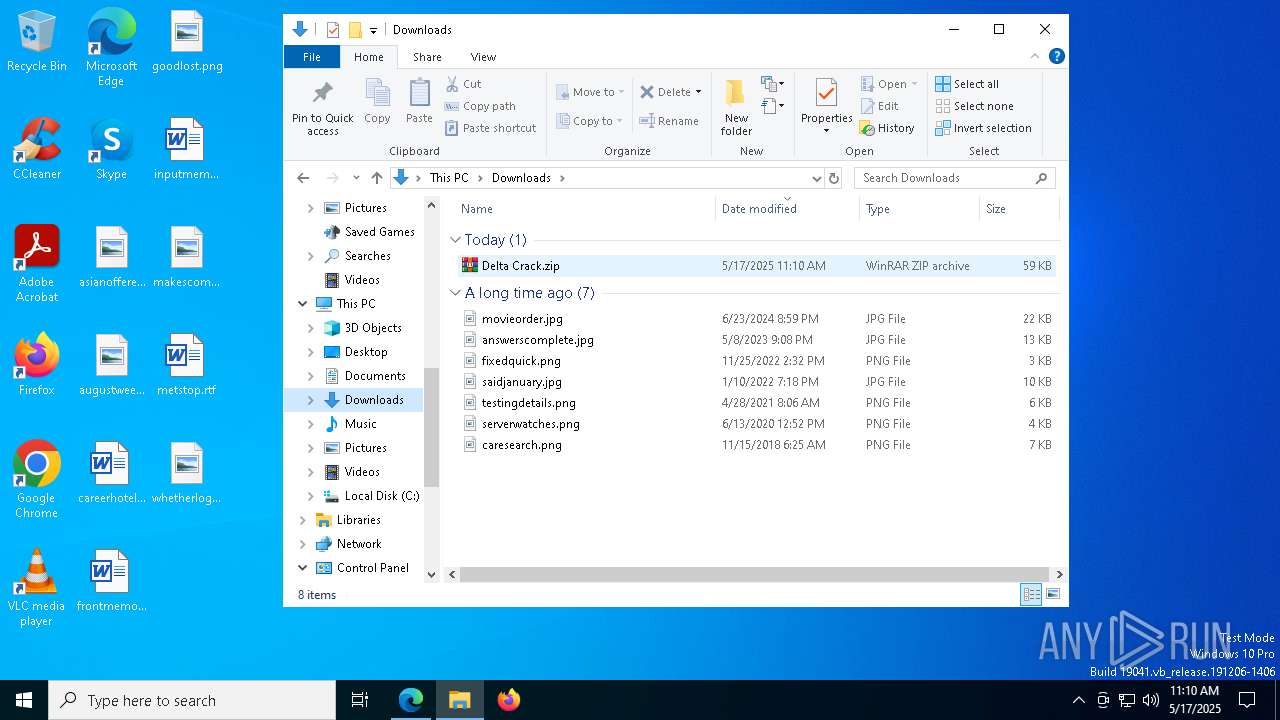
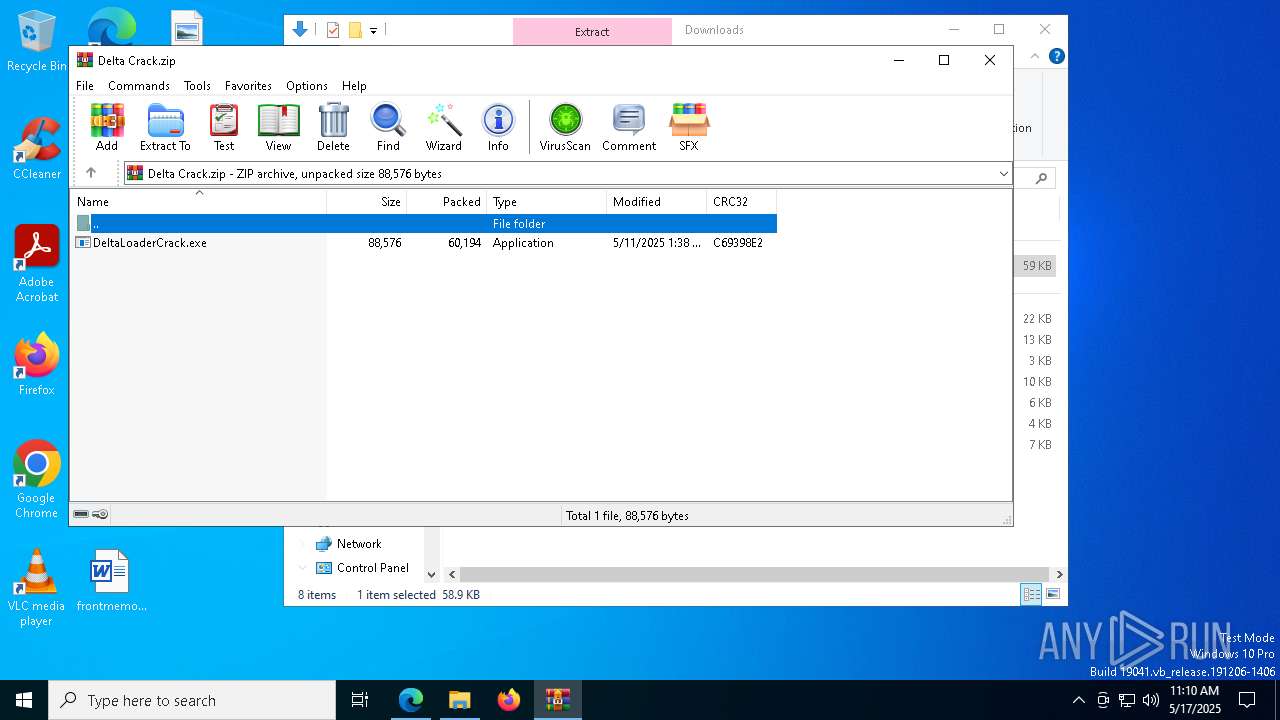
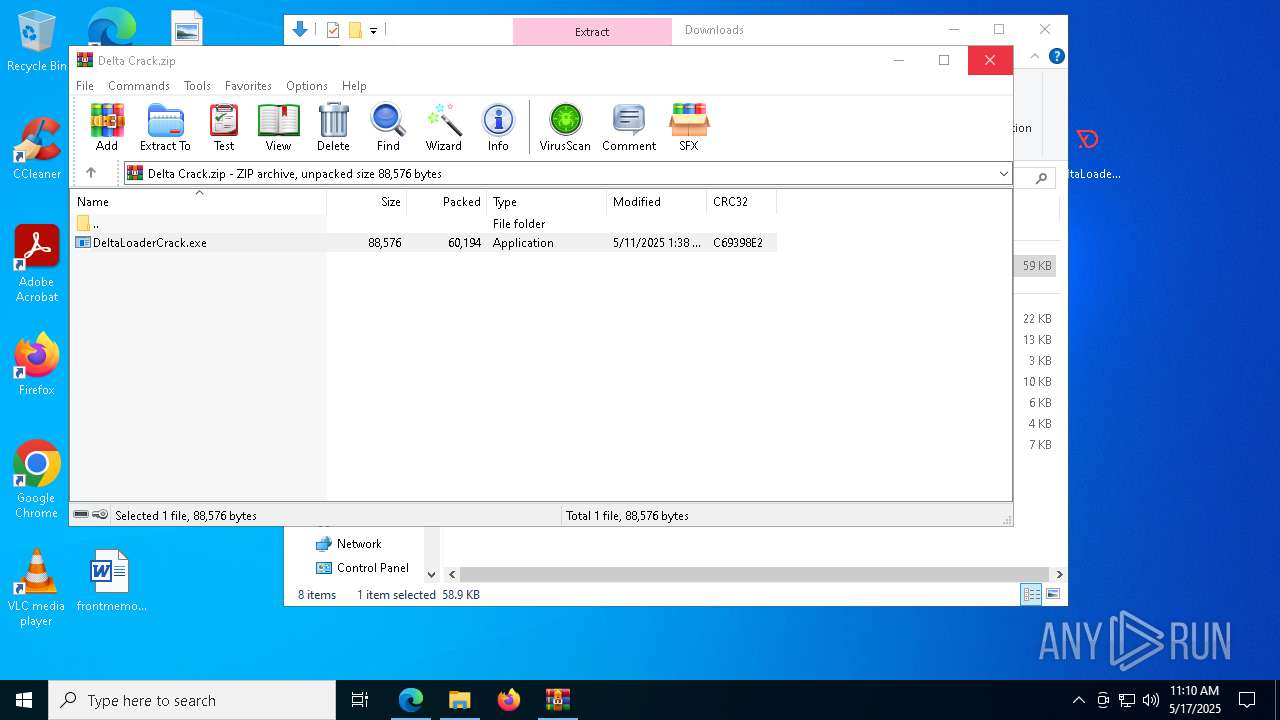
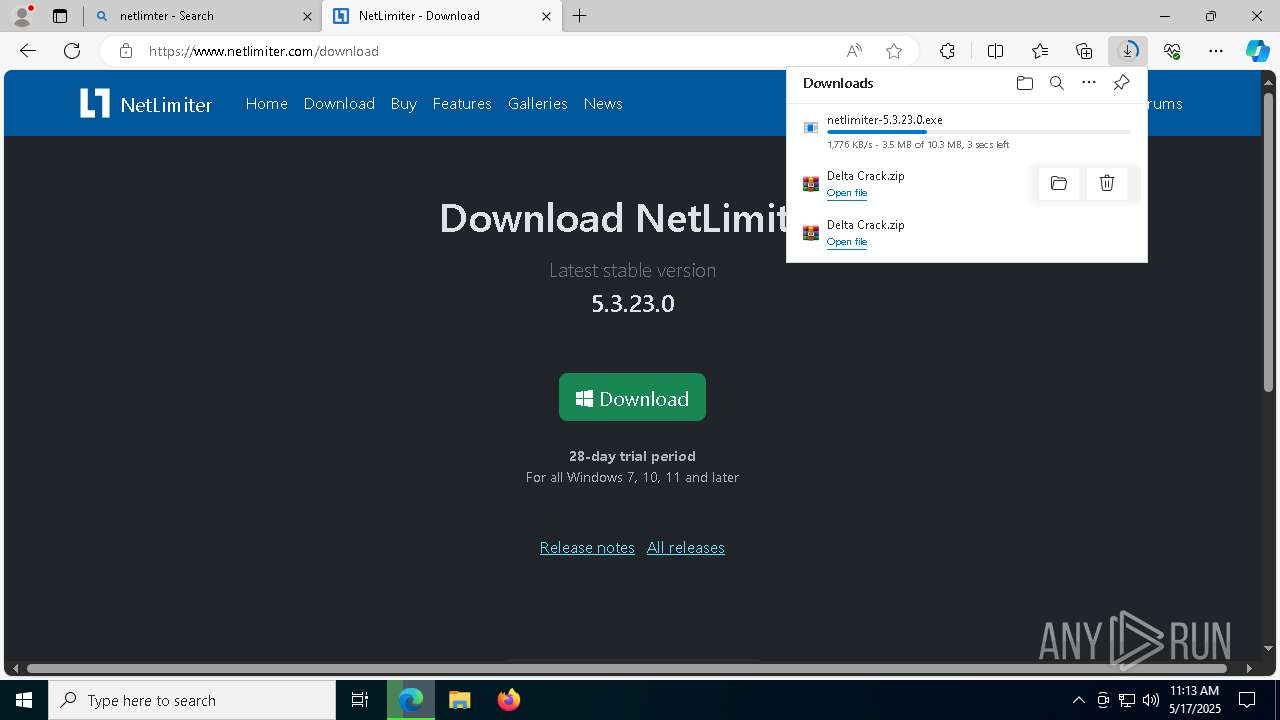
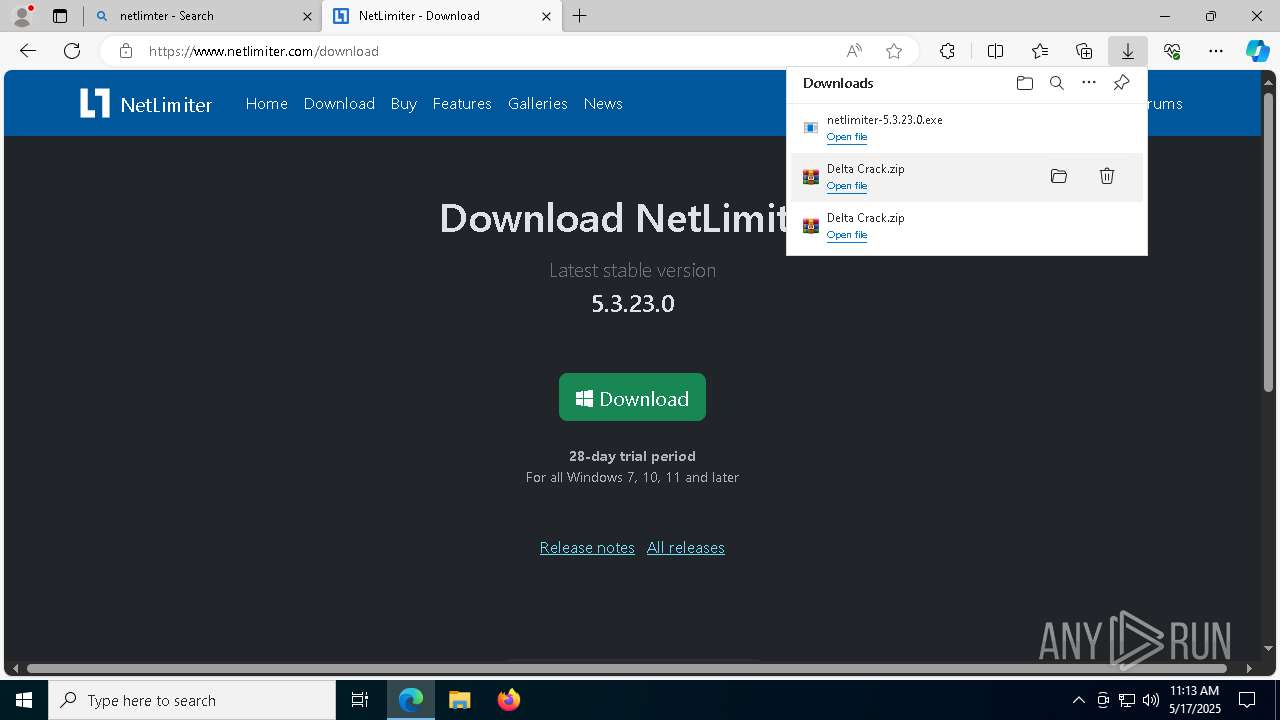
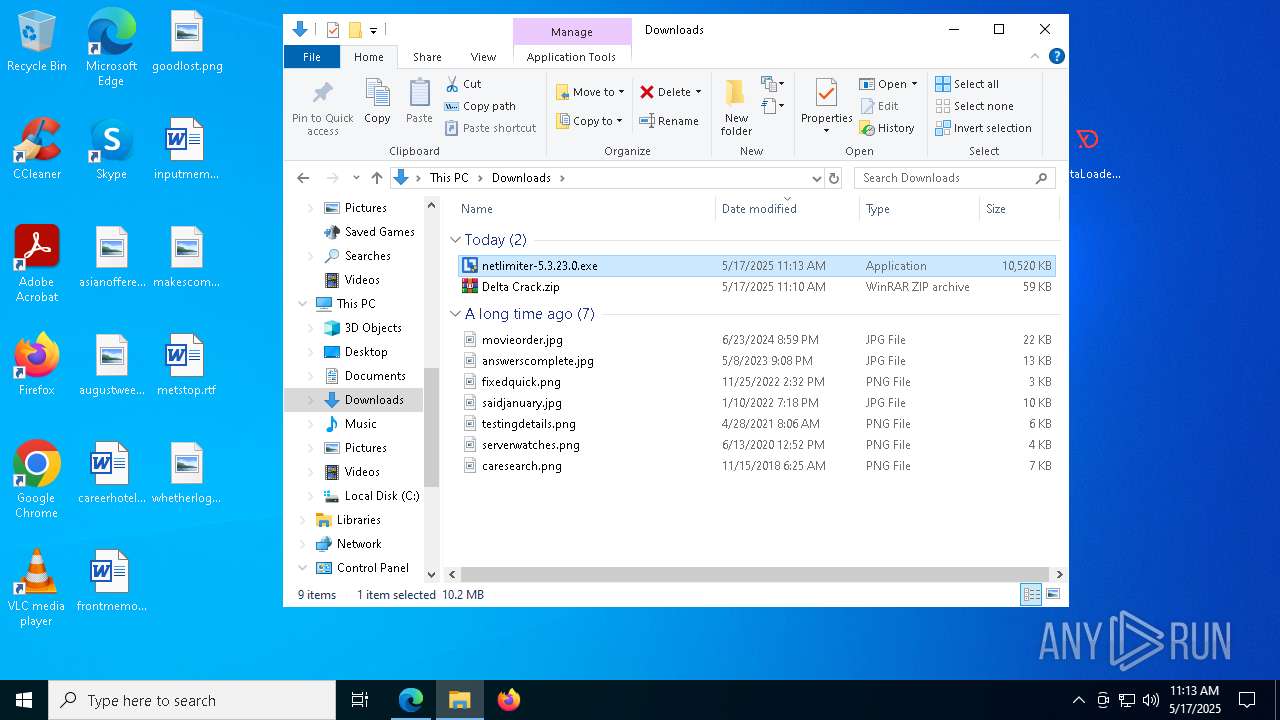
Manual execution by a user
- WinRAR.exe (PID: 8072)
- DeltaLoaderCrack.exe (PID: 6068)
- netlimiter-5.3.23.0.exe (PID: 2408)
- netlimiter-5.3.23.0.exe (PID: 5164)
- NLClientApp.exe (PID: 6908)
Reads Environment values
- identity_helper.exe (PID: 5392)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8072)
- msedge.exe (PID: 7900)
- msedge.exe (PID: 864)
- msedge.exe (PID: 7316)
- msiexec.exe (PID: 7892)
- msiexec.exe (PID: 2596)
- msiexec.exe (PID: 7084)
Reads the computer name
- identity_helper.exe (PID: 5392)
- DeltaLoaderCrack.exe (PID: 6068)
Reads the machine GUID from the registry
- DeltaLoaderCrack.exe (PID: 6068)
Creates files or folders in the user directory
- DeltaLoaderCrack.exe (PID: 6068)
Reads the software policy settings
- slui.exe (PID: 8172)
The sample compiled with english language support
- msedge.exe (PID: 7900)
- msedge.exe (PID: 864)
- netlimiter-5.3.23.0.exe (PID: 5164)
- msiexec.exe (PID: 2596)
- netlimiter-5.3.23.0.exe (PID: 6044)
- msiexec.exe (PID: 7084)
- msiexec.exe (PID: 7892)
Manages system restore points
- SrTasks.exe (PID: 4380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
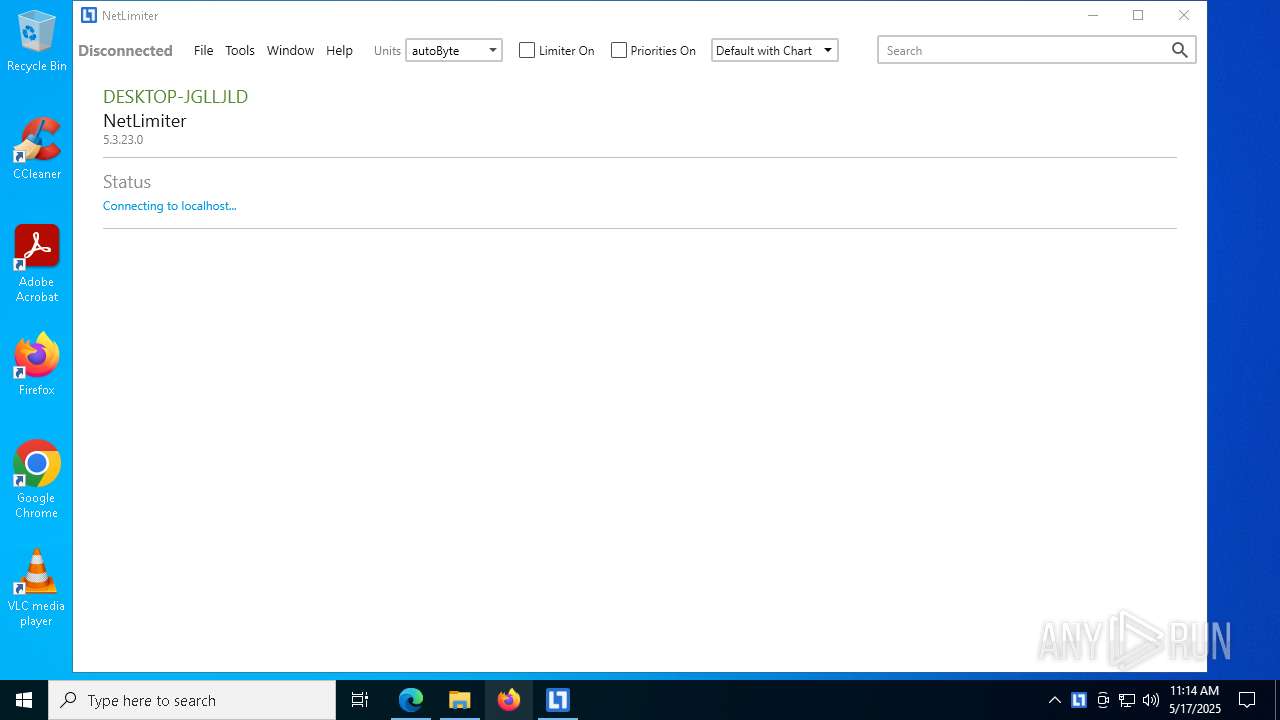
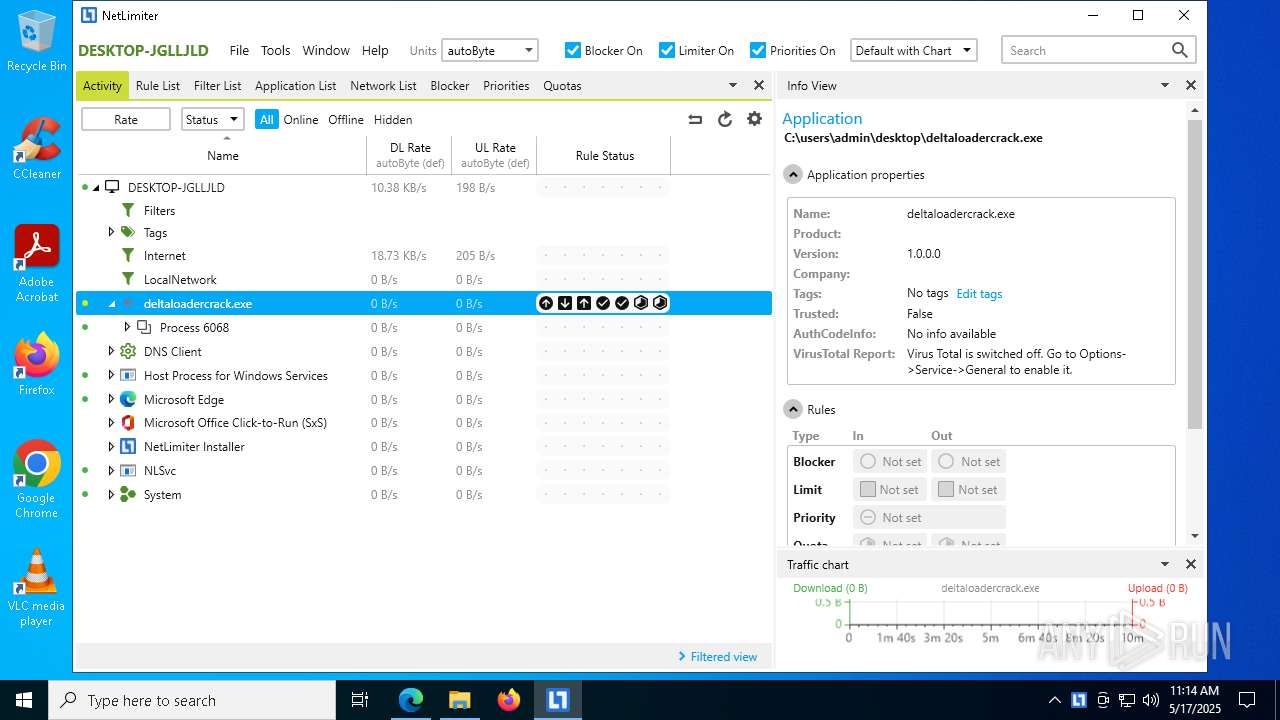
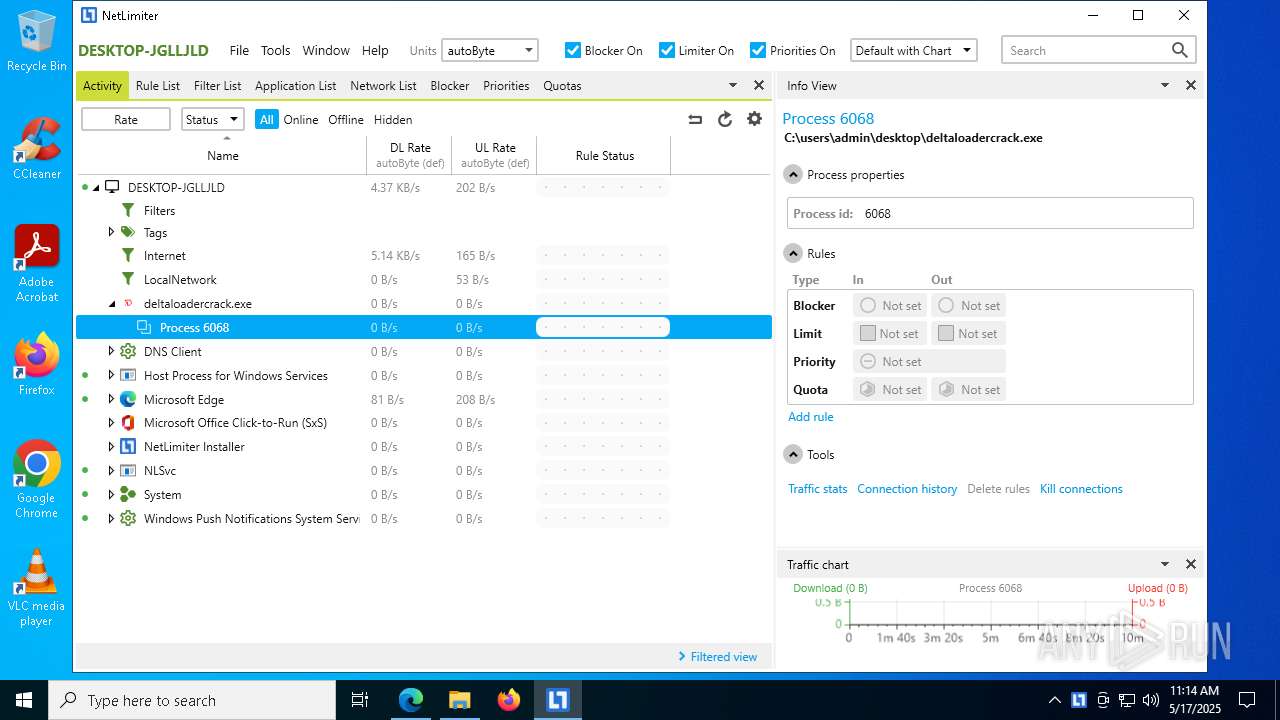
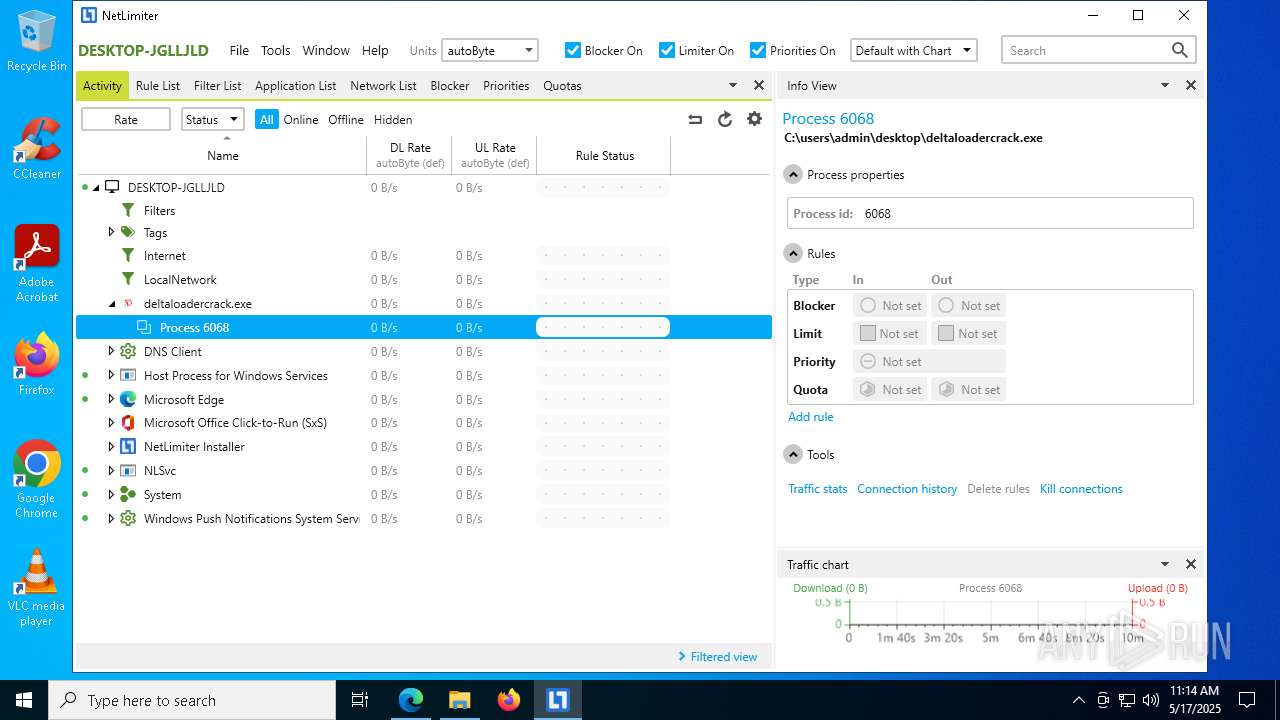
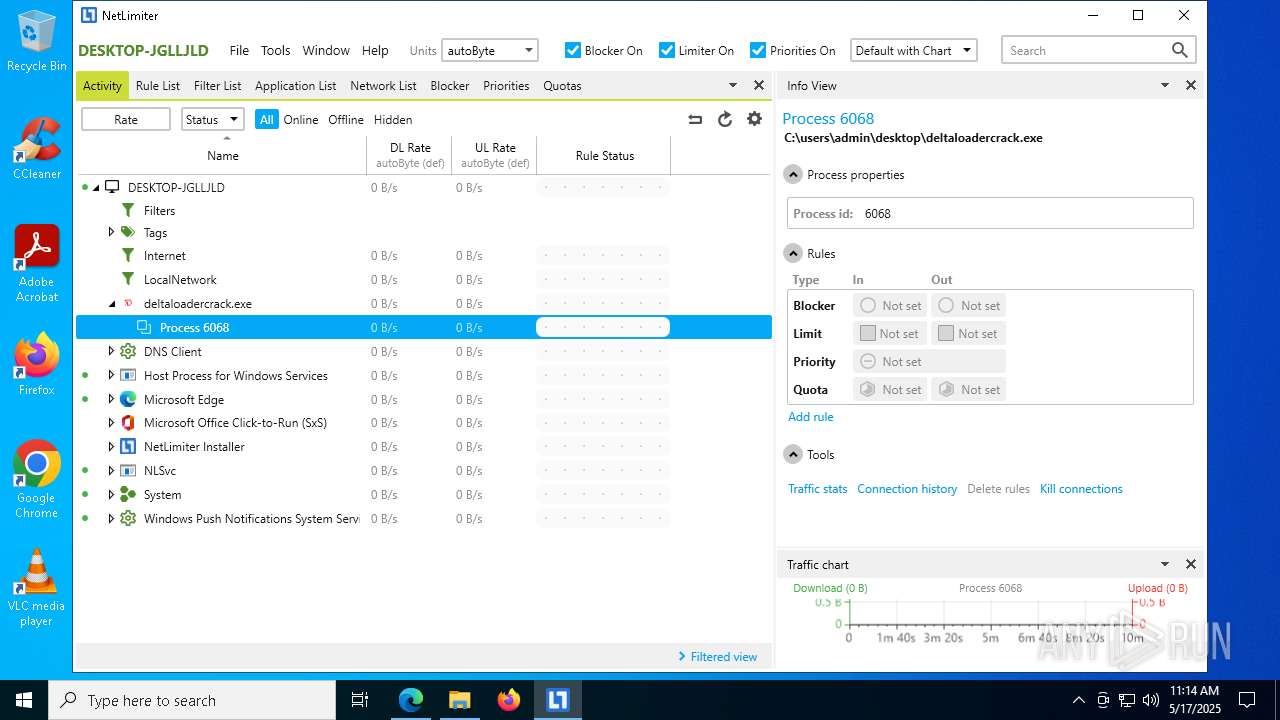
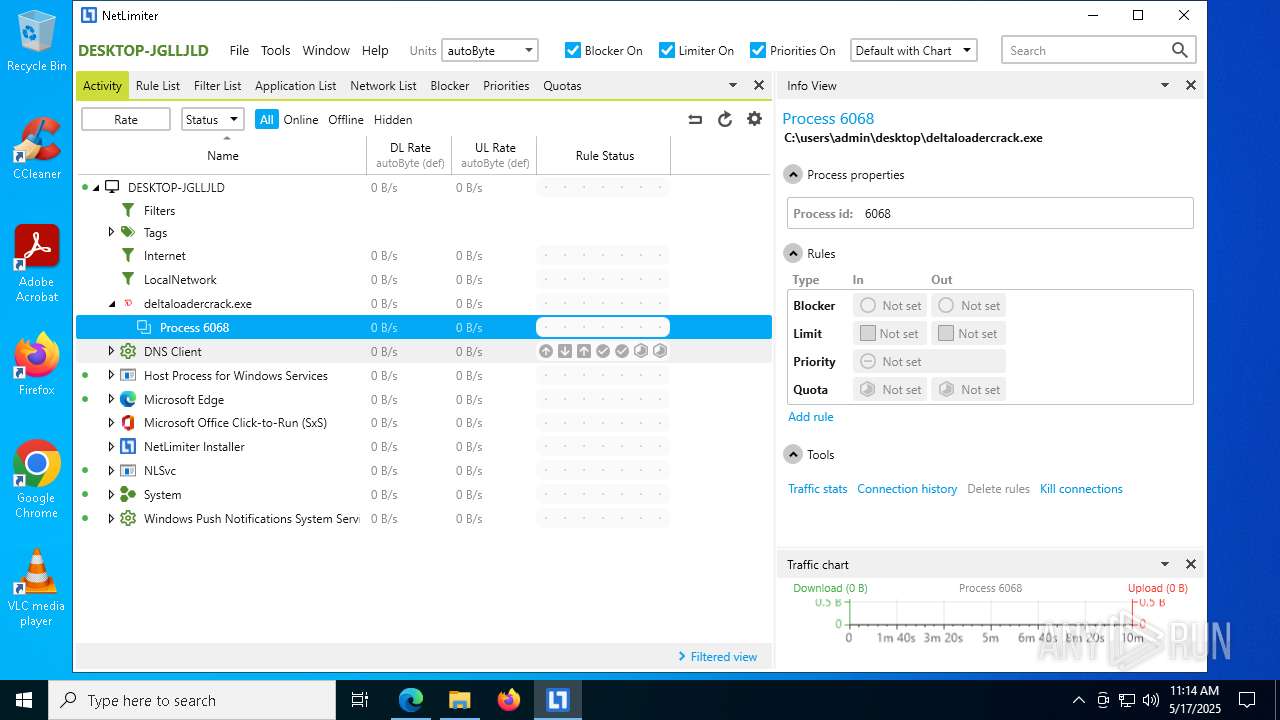
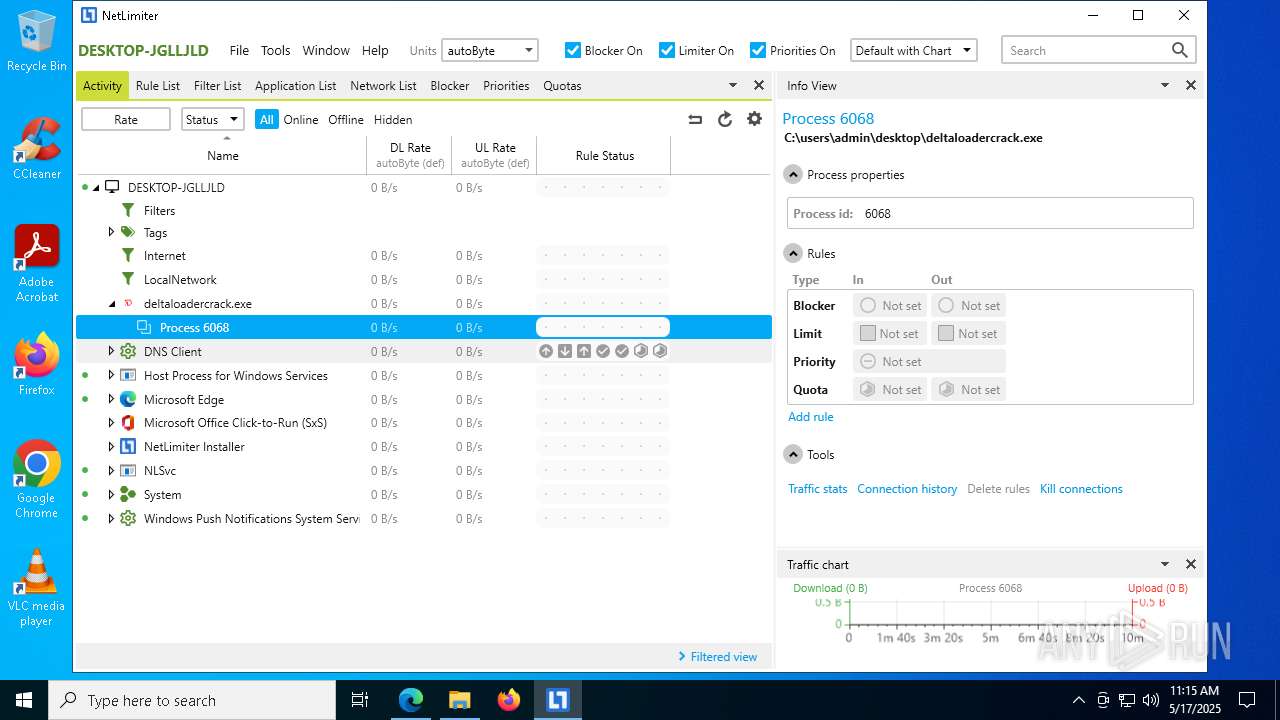
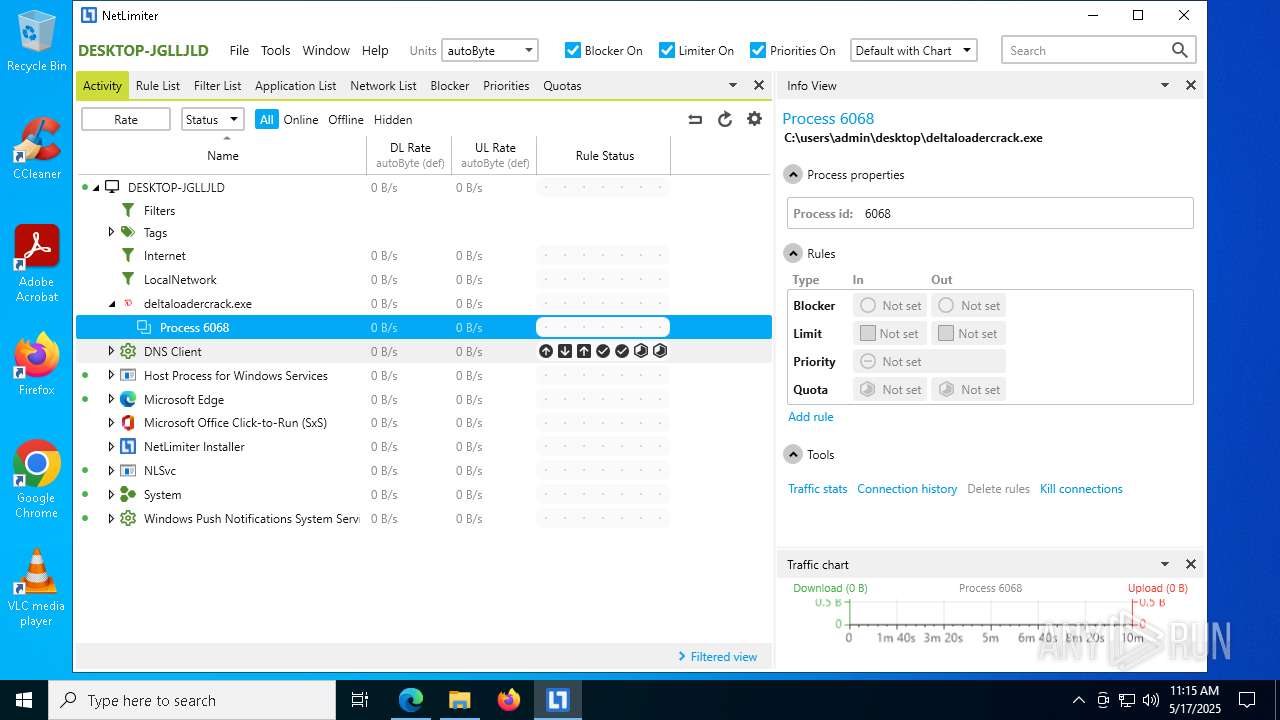
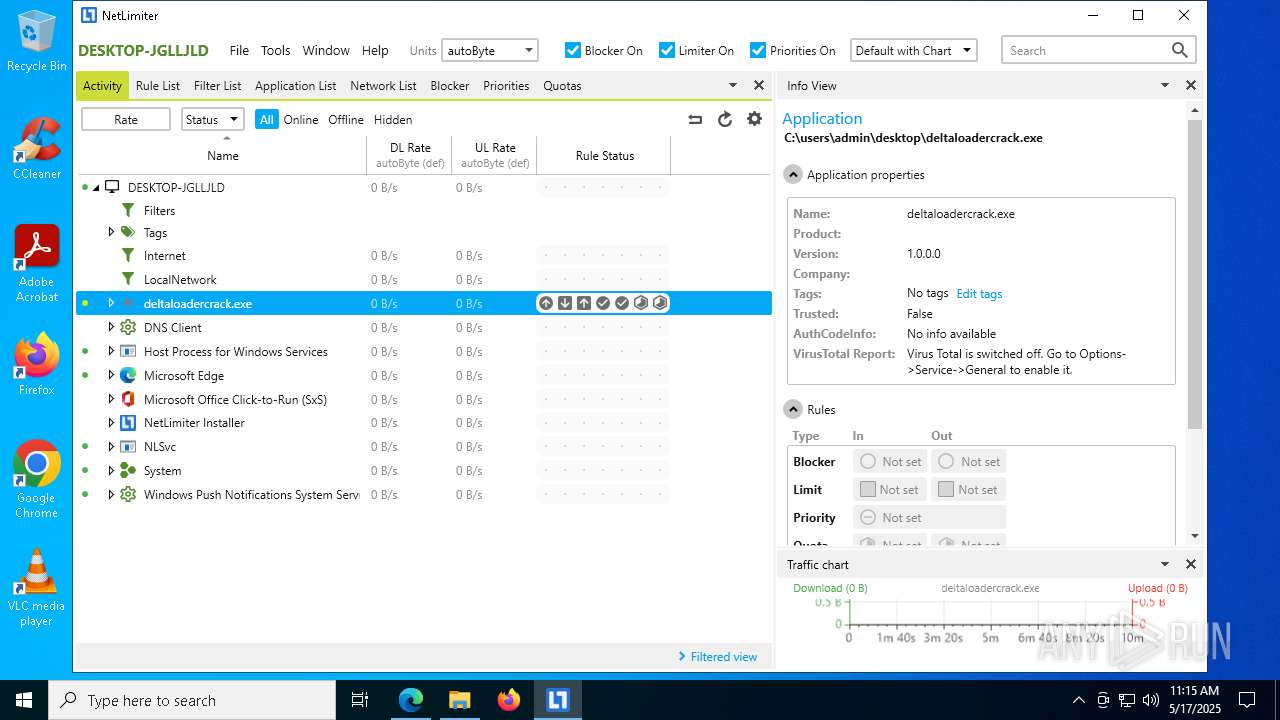
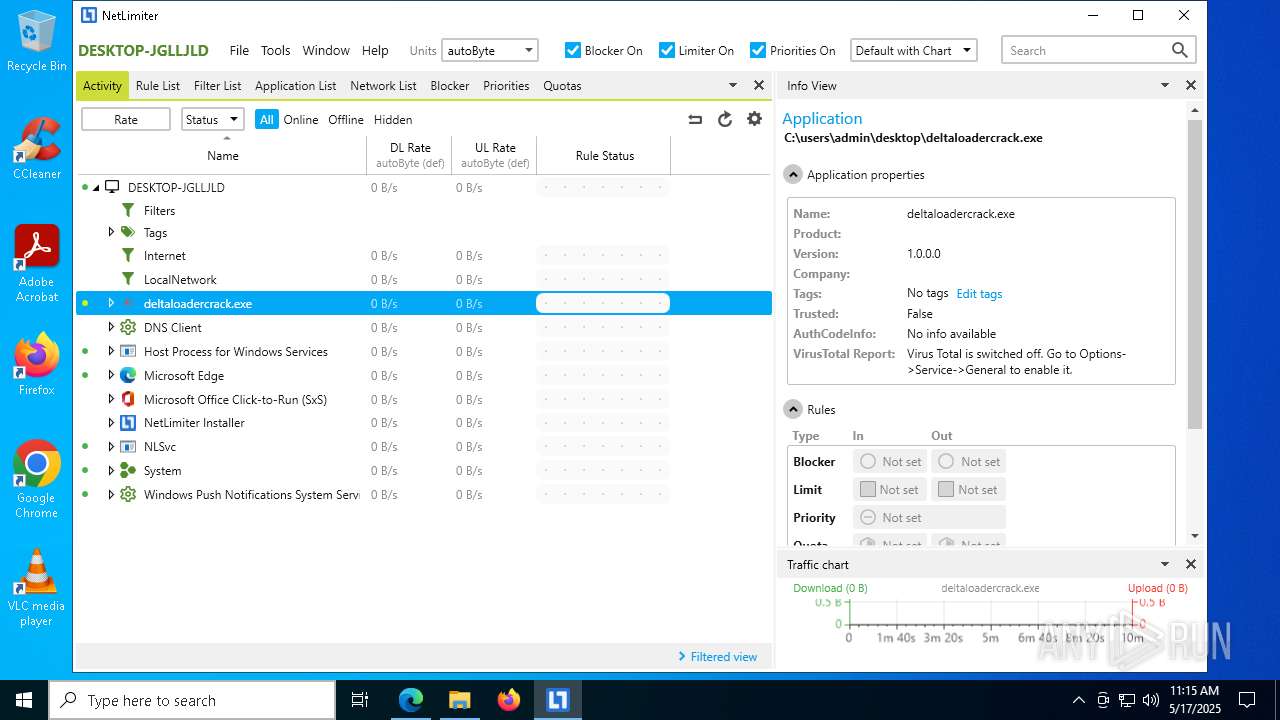
XWorm
(PID) Process(6068) DeltaLoaderCrack.exe
C2127.0.0.1,other-status.gl.at.ply.gg:26684
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameratnik
Mutex9cN3WkQsChAu7KUa
Total processes
237
Monitored processes
95
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Locktime Software\NetLimiter\NLSvc.exe" /afterinstall | C:\Program Files\Locktime Software\NetLimiter\NLSvc.exe | — | msiexec.exe | |||||||||||
User: admin Company: Locktime Software Integrity Level: HIGH Description: NLSvc Exit code: 0 Version: 5.3.23.0 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6616 --field-trial-handle=2240,i,17282380626132922699,11656428432859200334,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=7052 --field-trial-handle=2240,i,17282380626132922699,11656428432859200334,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Locktime Software\NetLimiter\NLSvc.exe" | C:\Program Files\Locktime Software\NetLimiter\NLSvc.exe | services.exe | ||||||||||||
User: SYSTEM Company: Locktime Software Integrity Level: SYSTEM Description: NLSvc Version: 5.3.23.0 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://mega.nz/file/nFtyRRRS#NJQNCpuEbu5fqvj81SRoNd3ClyRbf3cFqBbI2NIsW64" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5820 --field-trial-handle=2240,i,17282380626132922699,11656428432859200334,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7436 --field-trial-handle=2240,i,17282380626132922699,11656428432859200334,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Locktime Software\NetLimiter\NLSvcCliCnnCheck.exe" cb89a33b841a45c7b0be5e955a6f67f5 | C:\Program Files\Locktime Software\NetLimiter\NLSvcCliCnnCheck.exe | — | NLClientApp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6816 --field-trial-handle=2240,i,17282380626132922699,11656428432859200334,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
40 560
Read events
39 995
Write events
537
Delete events
28
Modification events
| (PID) Process: | (864) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E847E639E9932F00 | |||
| (PID) Process: | (864) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (864) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (864) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (864) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (864) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CE0CF039E9932F00 | |||
| (PID) Process: | (864) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F8B33EEF-D1FB-496D-8958-2CF723522636} | |||
| (PID) Process: | (864) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {95E615EB-BAAF-4C7B-B1F2-916FE3368350} | |||
| (PID) Process: | (864) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F41E11CD-7EC4-4E1D-B526-CAD32E2175C9} | |||
| (PID) Process: | (864) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0C7A95D6-486B-4F73-8C3C-5DC93D14DDEE} | |||
Executable files
533
Suspicious files
605
Text files
232
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b826.TMP | — | |
MD5:— | SHA256:— | |||
| 864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b836.TMP | — | |
MD5:— | SHA256:— | |||
| 864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b836.TMP | — | |
MD5:— | SHA256:— | |||
| 864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b855.TMP | — | |
MD5:— | SHA256:— | |||
| 864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b874.TMP | — | |
MD5:— | SHA256:— | |||
| 864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
128
DNS requests
104
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.26:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5756 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5756 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2420 | svchost.exe | HEAD | 200 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747702798&P2=404&P3=2&P4=V2cO5f3kvebz7MGvu1Z5jOQ8KkyLzn8mJcwjN63LJoxokOcdcpdURNZNUezOGVrOzy6ZqNIgrlTSHQLYAjUXow%3d%3d | unknown | — | — | whitelisted |
2420 | svchost.exe | GET | 206 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747702798&P2=404&P3=2&P4=V2cO5f3kvebz7MGvu1Z5jOQ8KkyLzn8mJcwjN63LJoxokOcdcpdURNZNUezOGVrOzy6ZqNIgrlTSHQLYAjUXow%3d%3d | unknown | — | — | whitelisted |
2420 | svchost.exe | GET | 206 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747702798&P2=404&P3=2&P4=V2cO5f3kvebz7MGvu1Z5jOQ8KkyLzn8mJcwjN63LJoxokOcdcpdURNZNUezOGVrOzy6ZqNIgrlTSHQLYAjUXow%3d%3d | unknown | — | — | whitelisted |
2420 | svchost.exe | GET | 206 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747702798&P2=404&P3=2&P4=V2cO5f3kvebz7MGvu1Z5jOQ8KkyLzn8mJcwjN63LJoxokOcdcpdURNZNUezOGVrOzy6ZqNIgrlTSHQLYAjUXow%3d%3d | unknown | — | — | whitelisted |
2420 | svchost.exe | GET | 206 | 146.75.122.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1747702798&P2=404&P3=2&P4=V2cO5f3kvebz7MGvu1Z5jOQ8KkyLzn8mJcwjN63LJoxokOcdcpdURNZNUezOGVrOzy6ZqNIgrlTSHQLYAjUXow%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.26:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7316 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
864 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7316 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7316 | msedge.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
7316 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
mega.nz |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7316 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7316 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7316 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7316 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7316 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7316 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7316 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7316 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7316 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7316 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |