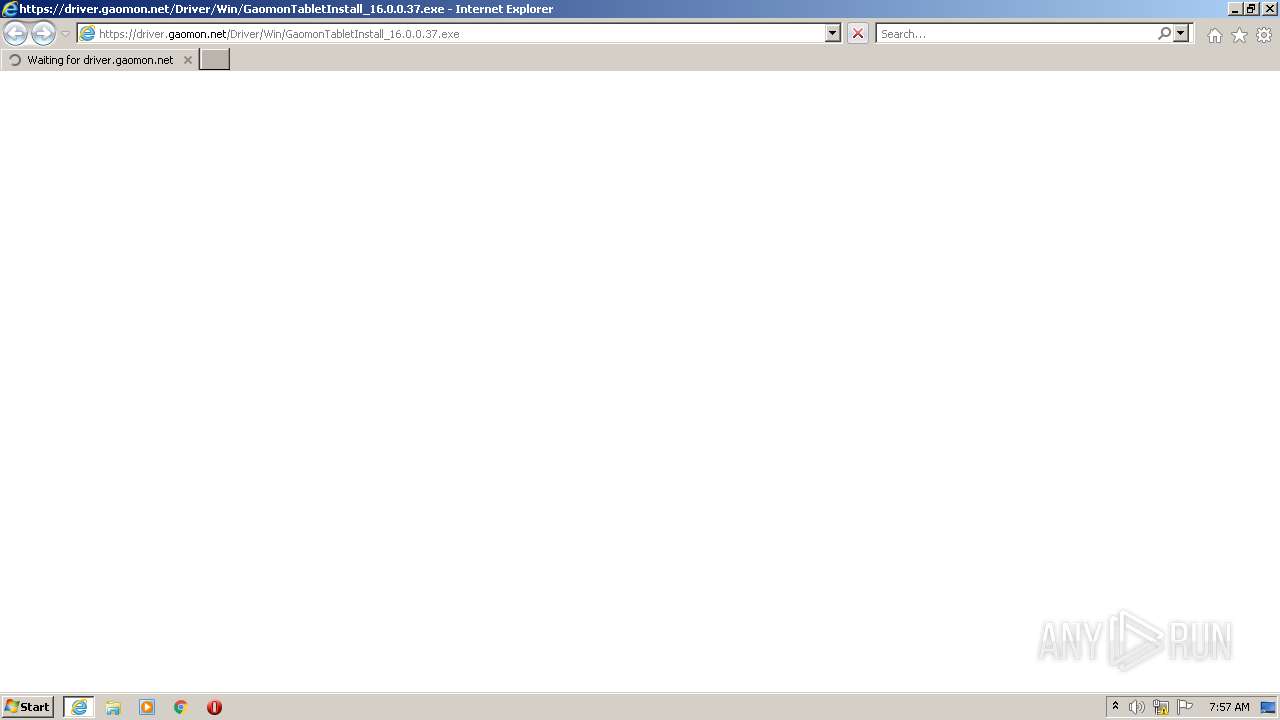
| URL: | https://driver.gaomon.net/Driver/Win/GaomonTabletInstall_16.0.0.37.exe |
| Full analysis: | https://app.any.run/tasks/f561ae95-0605-4d25-9b9c-8a0e32434b69 |
| Verdict: | Malicious activity |
| Analysis date: | February 01, 2022, 07:57:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F7FE77BCFC65CA8824BC3D2C94E320FC |
| SHA1: | 8F3BE79F1463C54B20C59601AEF8BB0D2998F1E6 |
| SHA256: | 81816F0EB247FDF7A951B80A18DBA7E359D7C54F58FB745F91A8F78011A0CE68 |
| SSDEEP: | 3:N8PMMm/wfL1+nWEaU1UNdAn:2K/wjkWEaAU4 |
MALICIOUS
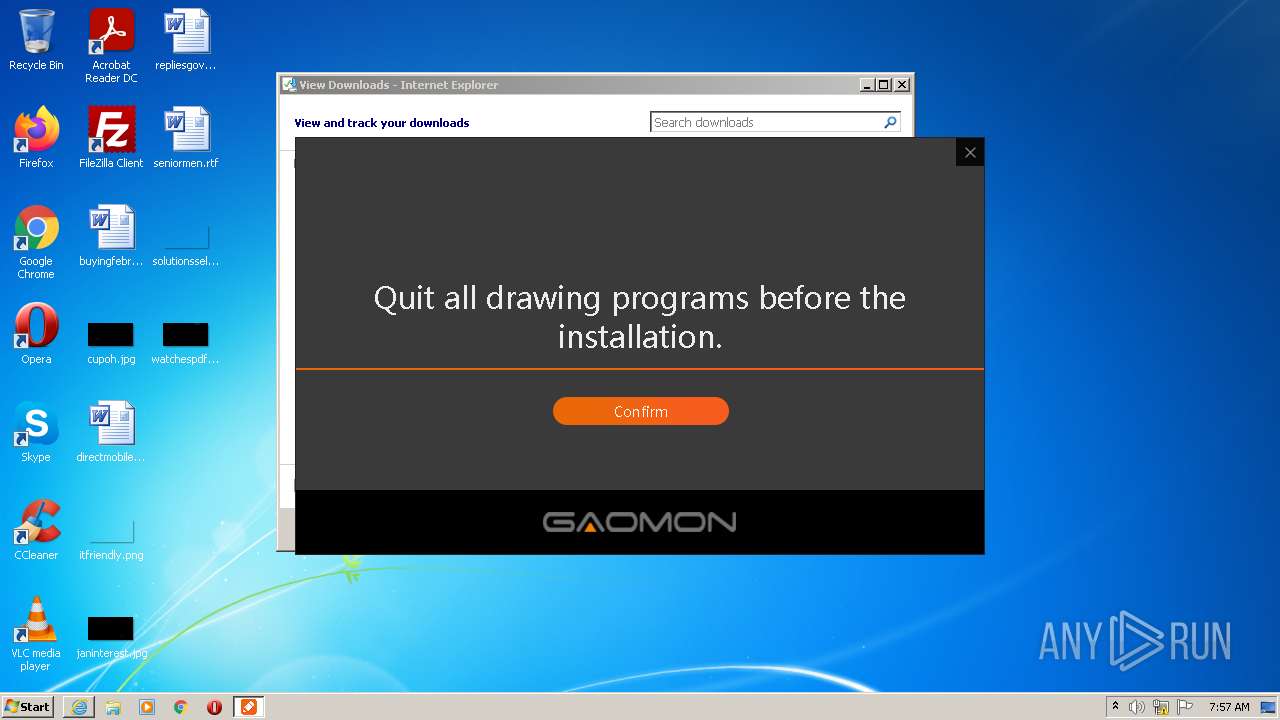
Application was dropped or rewritten from another process
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
- GaomonTabletInstall_16.0.0.37.exe (PID: 4064)
- WintabTerminator.exe (PID: 2940)
- devcon.exe (PID: 3932)
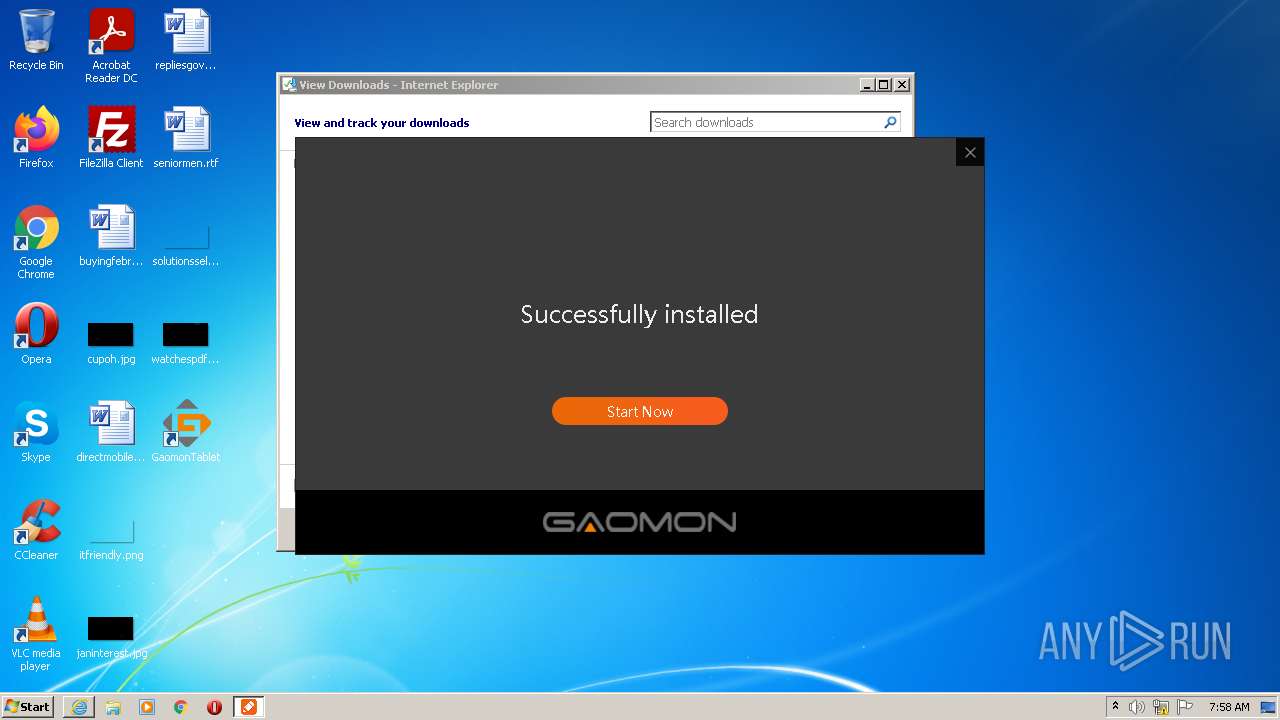
- GaomonTablet.exe (PID: 3176)
- TabletServer.exe (PID: 4028)
- GaomonTablet.exe (PID: 2184)
- TabletDriver.exe (PID: 2688)
Changes the autorun value in the registry
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
Drops executable file immediately after starts
- DrvInst.exe (PID: 2832)
- DrvInst.exe (PID: 3804)
Loads dropped or rewritten executable
- GaomonTablet.exe (PID: 2184)
- TabletServer.exe (PID: 4028)
- GaomonTablet.exe (PID: 3176)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3888)
Executable content was dropped or overwritten
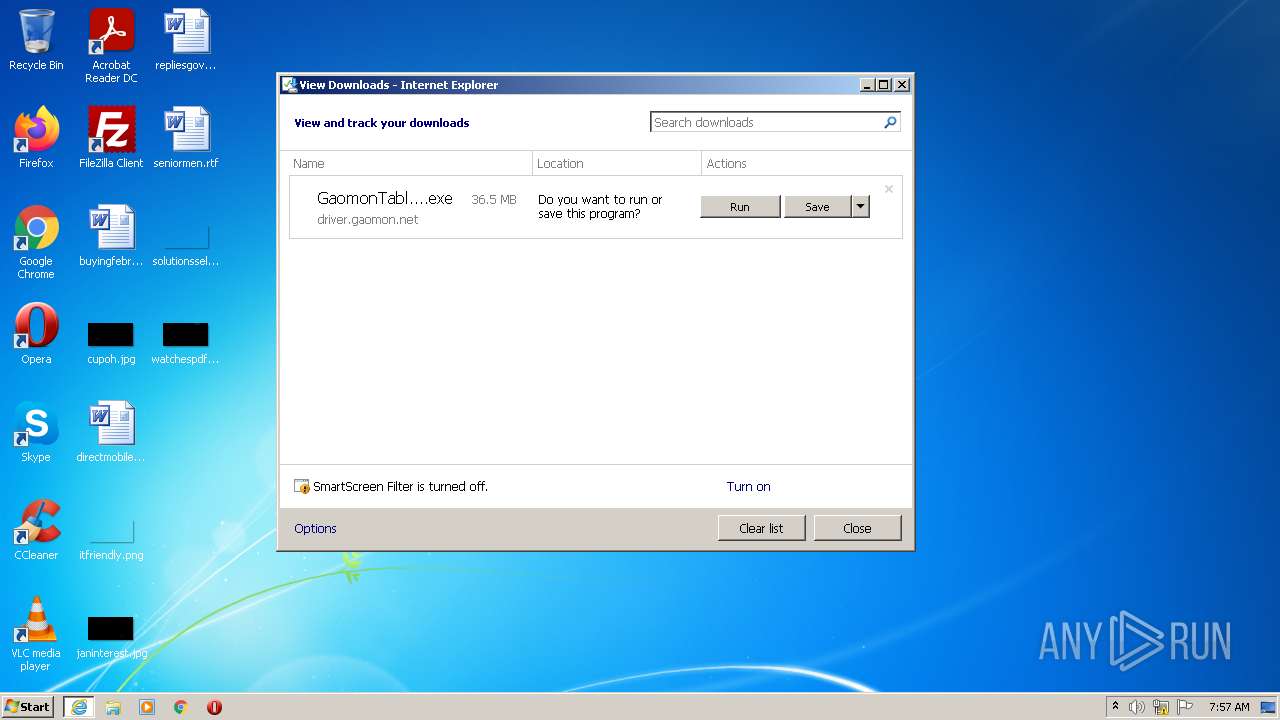
- iexplore.exe (PID: 3888)
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
- devcon.exe (PID: 3932)
- DrvInst.exe (PID: 2832)
- DrvInst.exe (PID: 3804)
Checks supported languages
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
- WintabTerminator.exe (PID: 2940)
- devcon.exe (PID: 3932)
- cmd.exe (PID: 2896)
- GaomonTablet.exe (PID: 3176)
- DrvInst.exe (PID: 2832)
- TabletServer.exe (PID: 4028)
- TabletDriver.exe (PID: 2688)
- DrvInst.exe (PID: 3804)
- DrvInst.exe (PID: 2612)
- GaomonTablet.exe (PID: 2184)
- DrvInst.exe (PID: 1588)
- DrvInst.exe (PID: 3912)
- DrvInst.exe (PID: 3556)
Reads the computer name
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
- GaomonTablet.exe (PID: 3176)
- devcon.exe (PID: 3932)
- TabletServer.exe (PID: 4028)
- DrvInst.exe (PID: 2832)
- TabletDriver.exe (PID: 2688)
- DrvInst.exe (PID: 3804)
- DrvInst.exe (PID: 2612)
- DrvInst.exe (PID: 1588)
- DrvInst.exe (PID: 3912)
- DrvInst.exe (PID: 3556)
Drops a file that was compiled in debug mode
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
- DrvInst.exe (PID: 2832)
- devcon.exe (PID: 3932)
- DrvInst.exe (PID: 3804)
Starts CMD.EXE for commands execution
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
Creates files in the Windows directory
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
- DrvInst.exe (PID: 2832)
- DrvInst.exe (PID: 3804)
Drops a file with too old compile date
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
- devcon.exe (PID: 3932)
- DrvInst.exe (PID: 2832)
Creates files in the program directory
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
Creates a software uninstall entry
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
Executed via COM
- DrvInst.exe (PID: 2832)
- DrvInst.exe (PID: 2612)
- DrvInst.exe (PID: 1588)
- DrvInst.exe (PID: 3804)
- DrvInst.exe (PID: 3912)
- DrvInst.exe (PID: 3556)
- rundll32.exe (PID: 3316)
- rundll32.exe (PID: 848)
Creates files in the user directory
- GaomonTabletInstall_16.0.0.37.exe (PID: 2160)
- TabletServer.exe (PID: 4028)
- TabletDriver.exe (PID: 2688)
- GaomonTablet.exe (PID: 3176)
Removes files from Windows directory
- DrvInst.exe (PID: 2832)
- DrvInst.exe (PID: 3804)
Creates files in the driver directory
- DrvInst.exe (PID: 2832)
- DrvInst.exe (PID: 3804)
INFO
Reads the computer name
- iexplore.exe (PID: 1324)
- iexplore.exe (PID: 3888)
- rundll32.exe (PID: 848)
Checks supported languages
- iexplore.exe (PID: 1324)
- iexplore.exe (PID: 3888)
- rundll32.exe (PID: 3316)
- rundll32.exe (PID: 848)
Application launched itself
- iexplore.exe (PID: 1324)
Changes internet zones settings
- iexplore.exe (PID: 1324)
Checks Windows Trust Settings
- iexplore.exe (PID: 1324)
- iexplore.exe (PID: 3888)
- devcon.exe (PID: 3932)
- DrvInst.exe (PID: 2832)
- DrvInst.exe (PID: 3804)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1324)
Reads settings of System Certificates
- iexplore.exe (PID: 3888)
- iexplore.exe (PID: 1324)
- devcon.exe (PID: 3932)
- DrvInst.exe (PID: 2832)
- DrvInst.exe (PID: 3804)
Reads the date of Windows installation
- iexplore.exe (PID: 1324)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1324)
Changes settings of System certificates
- iexplore.exe (PID: 1324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
19
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | rundll32.exe C:\Windows\system32\newdev.dll,pDiDeviceInstallNotification \\.\pipe\PNP_Device_Install_Pipe_1.{4948e99d-f7b1-4966-9663-fab789605949} "(null)" | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://driver.gaomon.net/Driver/Win/GaomonTabletInstall_16.0.0.37.exe" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1588 | DrvInst.exe "1" "200" "HID\tablethid&Col04\1&2d595ca7&0&0003" "" "" "65df2711f" "00000000" "00000650" "00000654" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2160 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\GaomonTabletInstall_16.0.0.37.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\GaomonTabletInstall_16.0.0.37.exe | iexplore.exe | ||||||||||||
User: admin Company: ???????????? Integrity Level: HIGH Description: ???? Exit code: 0 Version: 16.0.0.37 Modules
| |||||||||||||||
| 2184 | "C:\Users\admin\AppData\Roaming\GaomonTablet\GaomonTablet.exe" | C:\Users\admin\AppData\Roaming\GaomonTablet\GaomonTablet.exe | — | GaomonTabletInstall_16.0.0.37.exe | |||||||||||
User: admin Company: ???????????? Integrity Level: HIGH Description: GaomonTablet Exit code: 0 Version: 16.0.0.37 Modules
| |||||||||||||||
| 2612 | DrvInst.exe "1" "200" "HID\tablethid&Col01\1&2d595ca7&0&0000" "" "" "61702cfa7" "00000000" "00000644" "00000600" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2688 | Json={ \@BrandName\@ : \@Gaomon\@, \@CfgWnd\@ : 393652, \@CustomerCode\@ : [ \@GM001\@, \@OEM02\@ ], \@DataPath\@ : \@C:\\Users\\admin\\AppData\\Roaming\\Gaomon\\data\@, \@WndMarkValue\@ : 1981 } JsonEnd | C:\Users\admin\AppData\Roaming\GaomonTablet\TabletDriver.exe | — | GaomonTablet.exe | |||||||||||
User: admin Integrity Level: HIGH Description: TabletDriver Exit code: 0 Version: 16.0.0.21 Modules
| |||||||||||||||
| 2832 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{3b815bf2-6af2-1056-55e7-b812c608f724}\vmulti.inf" "0" "6a6f1639b" "000005F4" "WinSta0\Default" "00000574" "208" "c:\users\admin\appdata\roaming\gaomontablet\driver\hid\i386" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Roaming\GAOMON~1\driver\TABLET~1\i386\TABETD~1.BAT" | C:\Windows\System32\cmd.exe | — | GaomonTabletInstall_16.0.0.37.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2940 | "C:\Users\admin\AppData\Local\Temp\WintabTerminator.exe" | C:\Users\admin\AppData\Local\Temp\WintabTerminator.exe | — | GaomonTabletInstall_16.0.0.37.exe | |||||||||||
User: admin Company: TODO: <???> Integrity Level: HIGH Description: WintabTerminator Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
22 249
Read events
22 008
Write events
239
Delete events
2
Modification events
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30938945 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30938945 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1324) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
57
Suspicious files
23
Text files
26
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\GaomonTabletInstall_16.0.0.37.exe.0r35go3.partial | — | |
MD5:— | SHA256:— | |||
| 3888 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\GaomonTabletInstall_16.0.0.37[1].exe | executable | |
MD5:— | SHA256:— | |||
| 1324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\GaomonTabletInstall_16.0.0.37.exe | — | |
MD5:— | SHA256:— | |||
| 3888 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CE5584B63C007E700FA9D83C9AE5C558 | binary | |
MD5:— | SHA256:— | |||
| 1324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 1324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 3888 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_86C2A03C133240EC4C95180B9FD368BB | binary | |
MD5:— | SHA256:— | |||
| 3888 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CE5584B63C007E700FA9D83C9AE5C558 | der | |
MD5:— | SHA256:— | |||
| 1324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3888 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_86C2A03C133240EC4C95180B9FD368BB | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
19
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1324 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3888 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAeYNgOt45kIIZygDCe8imw%3D | US | der | 471 b | whitelisted |
3888 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR0tOcjGcdlkhVARHvHzj6Qwhh26wQUpI3lvnx55HAjbS4pNK0jWNz1MX8CEAKt%2Fi6DZFlqLs1EizWVJ1g%3D | US | der | 471 b | whitelisted |
1324 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3888 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7eb56ded0e7ecd60 | US | compressed | 4.70 Kb | whitelisted |
1324 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d85cd64283bf8617 | US | compressed | 4.70 Kb | whitelisted |
3888 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?60db967d845610f5 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | iexplore.exe | 79.133.177.225:443 | driver.gaomon.net | SOT LINE Limited Company | RU | malicious |
3888 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
1324 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1324 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
1324 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3888 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1324 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
driver.gaomon.net |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |