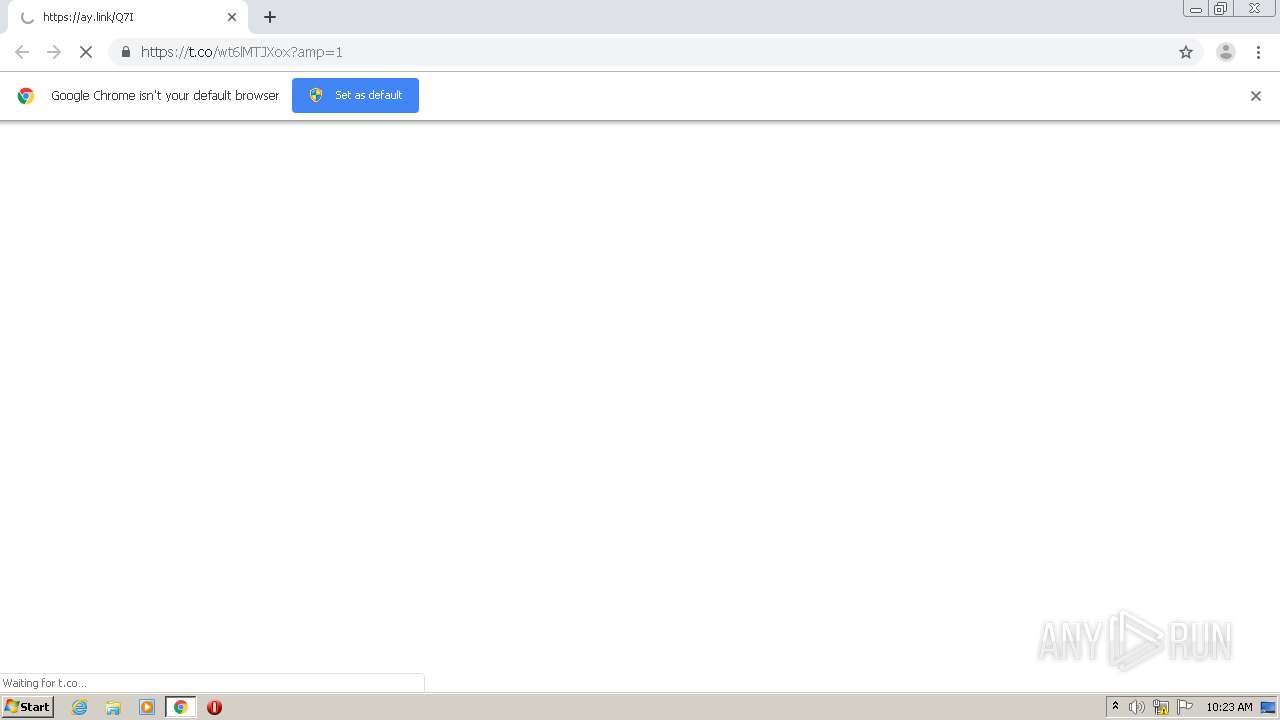
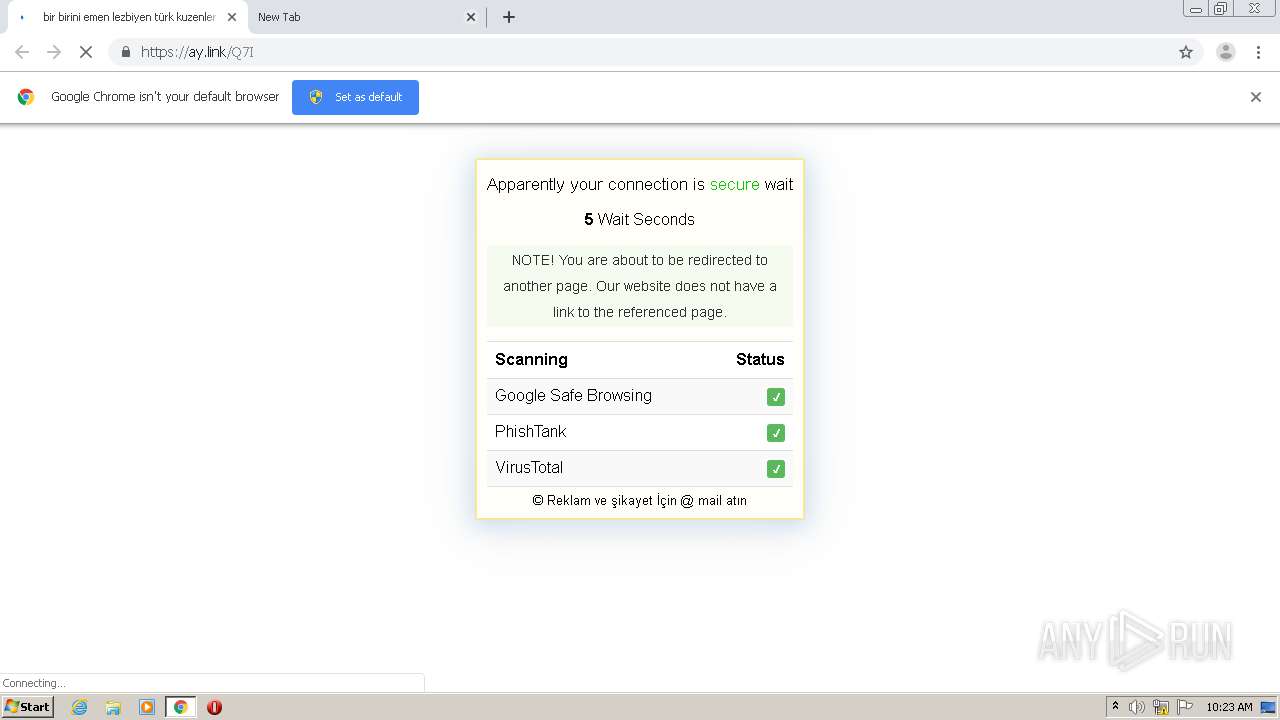
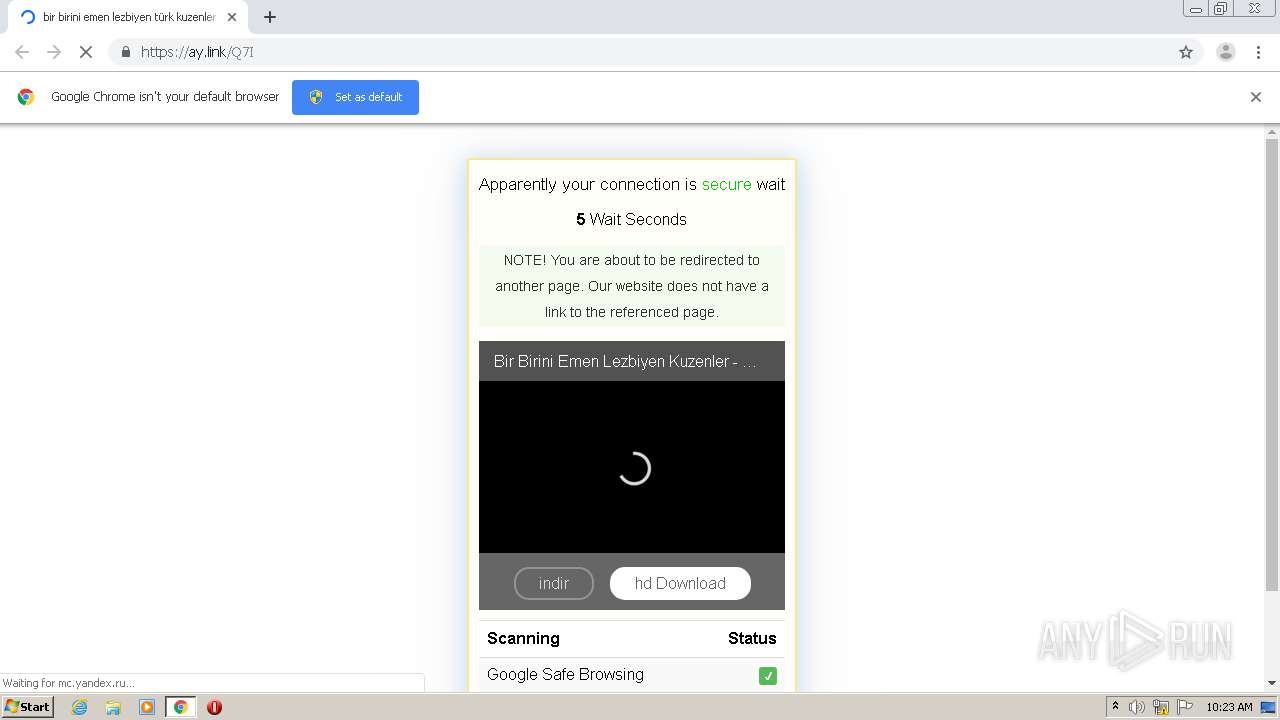
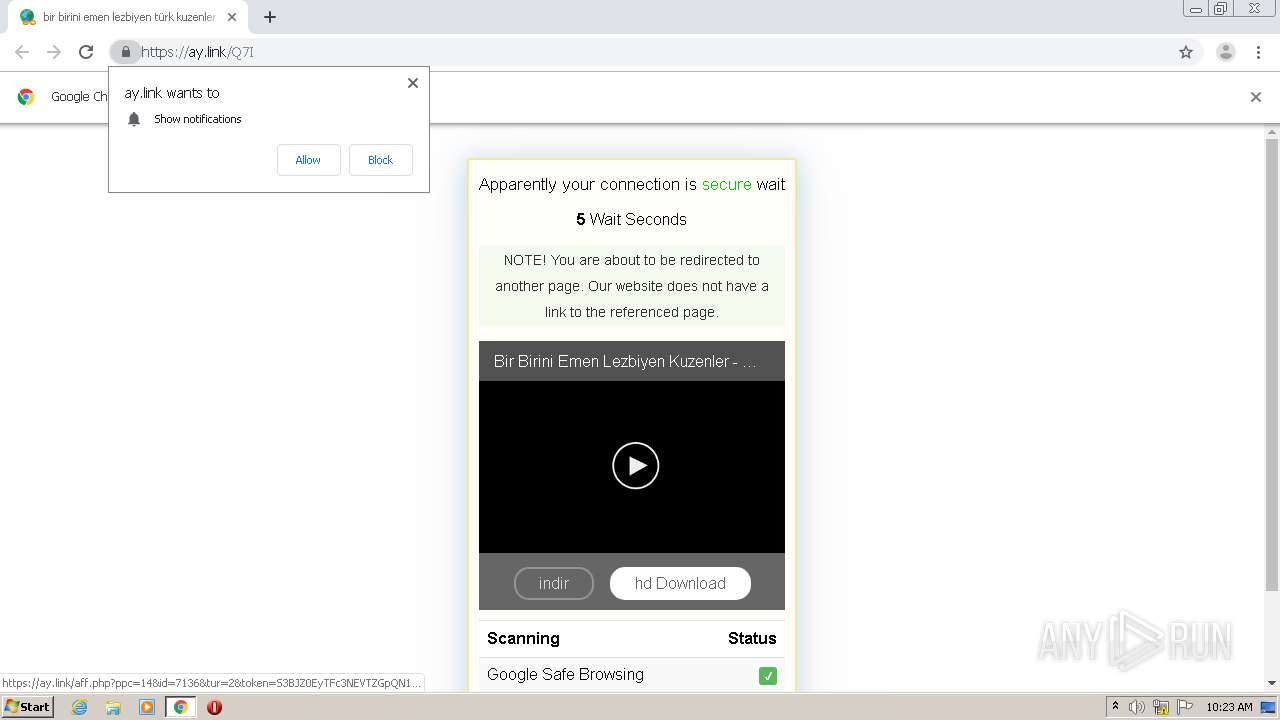
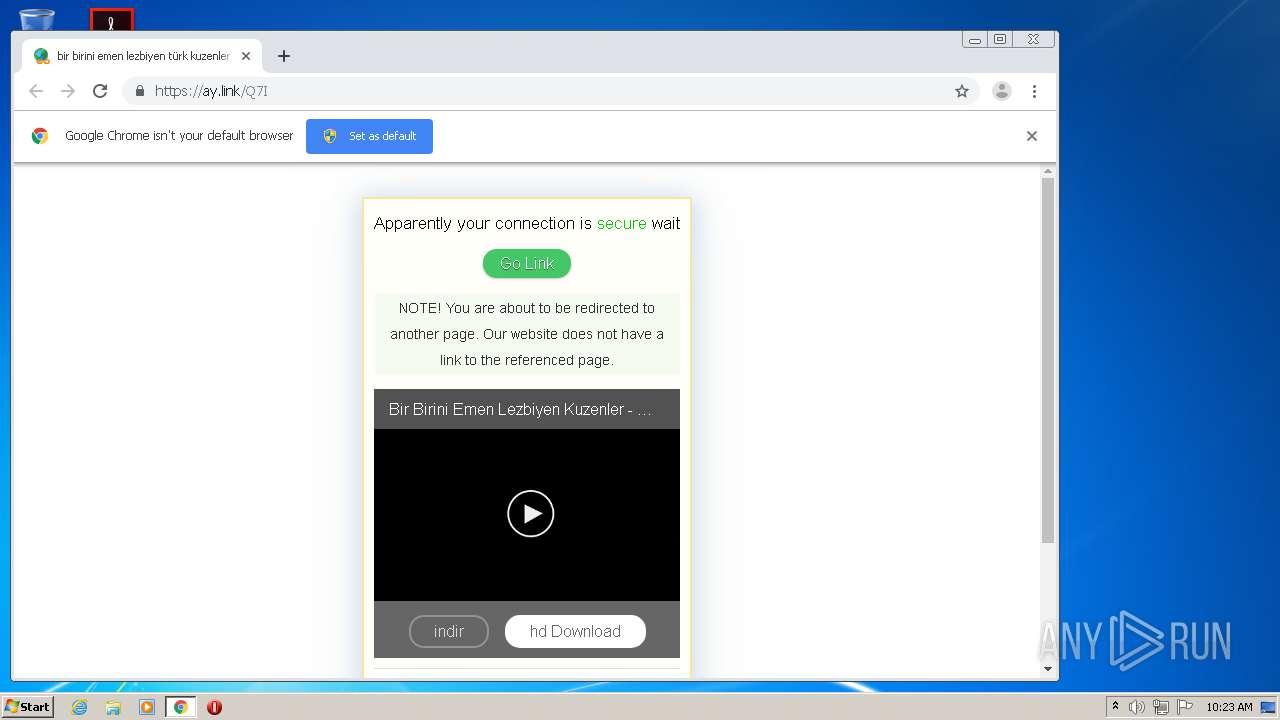
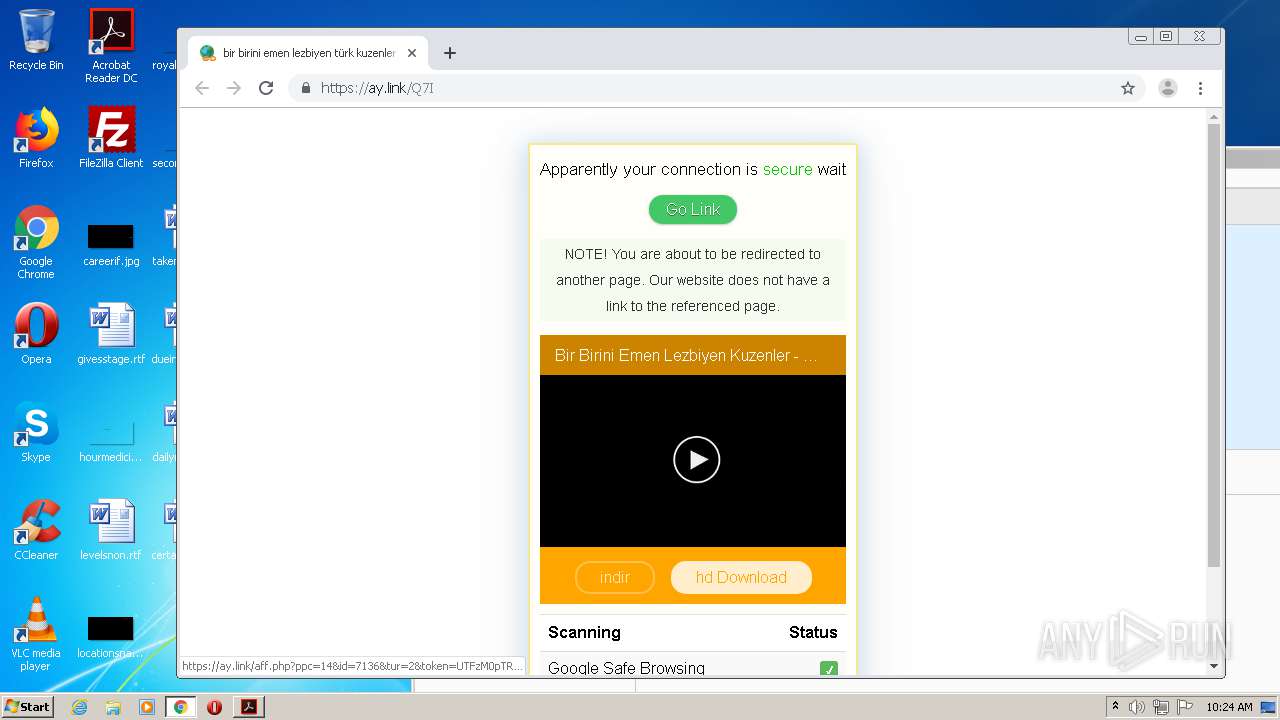
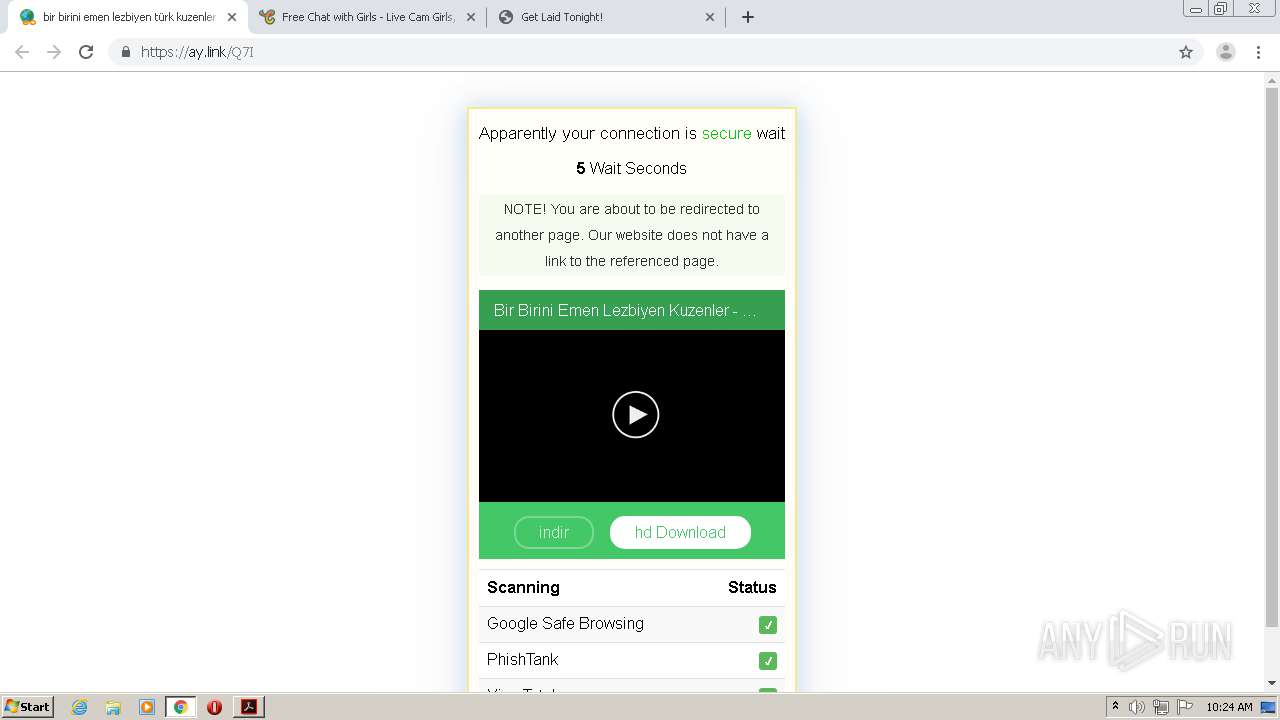
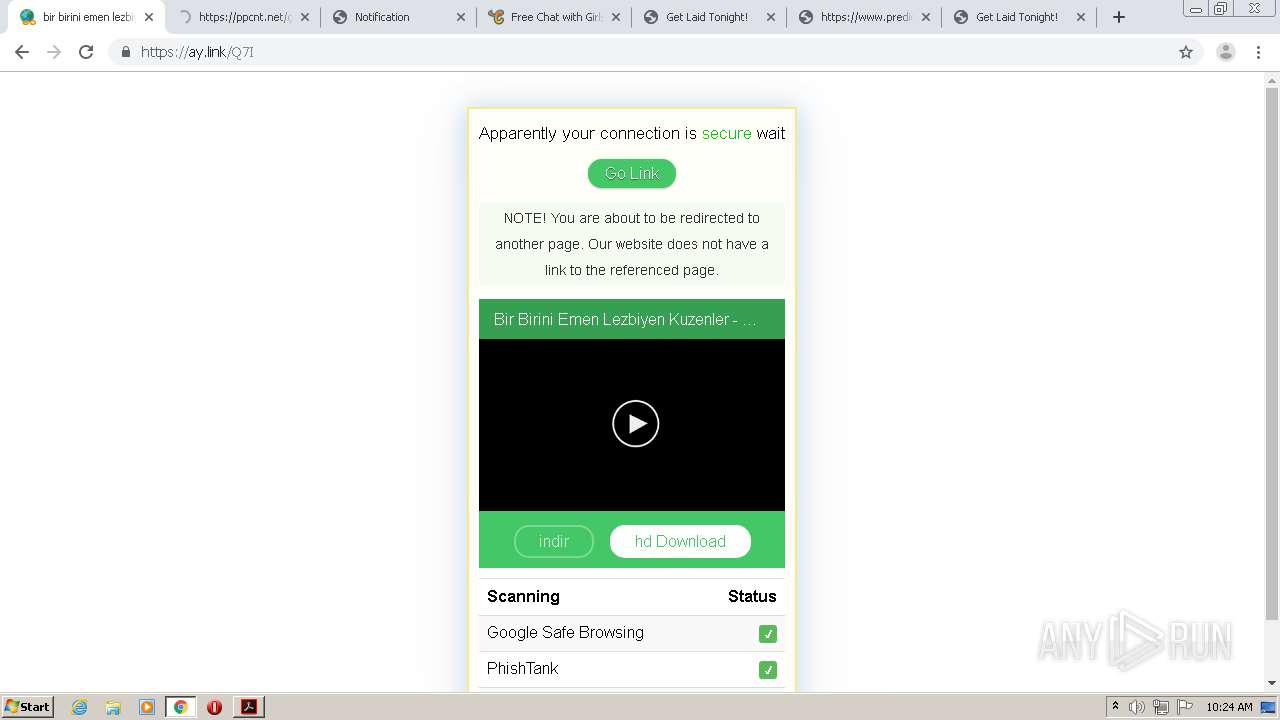
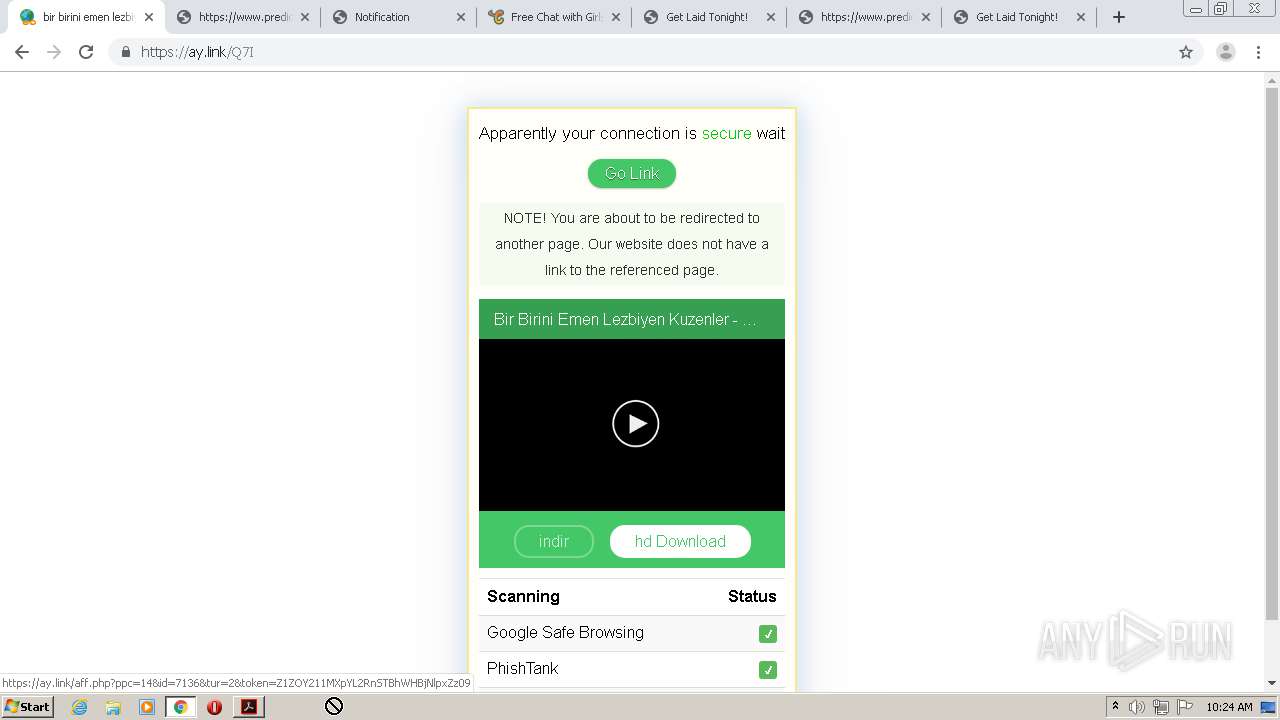
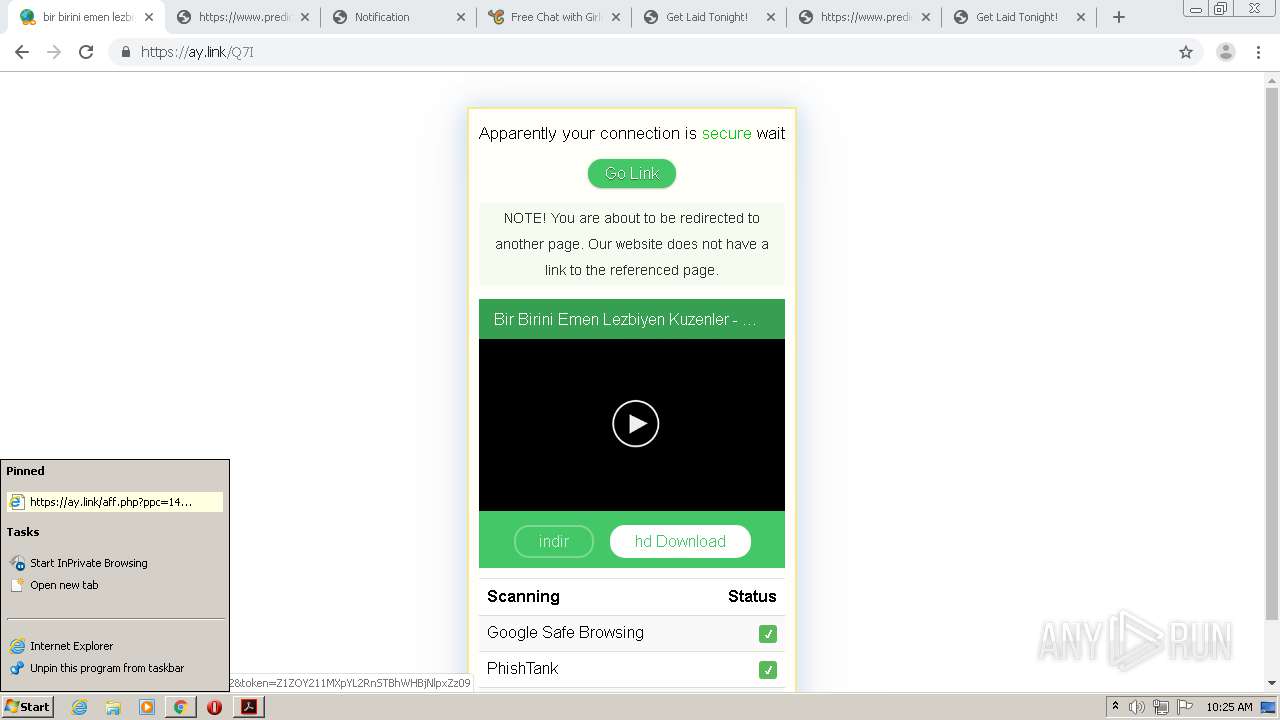
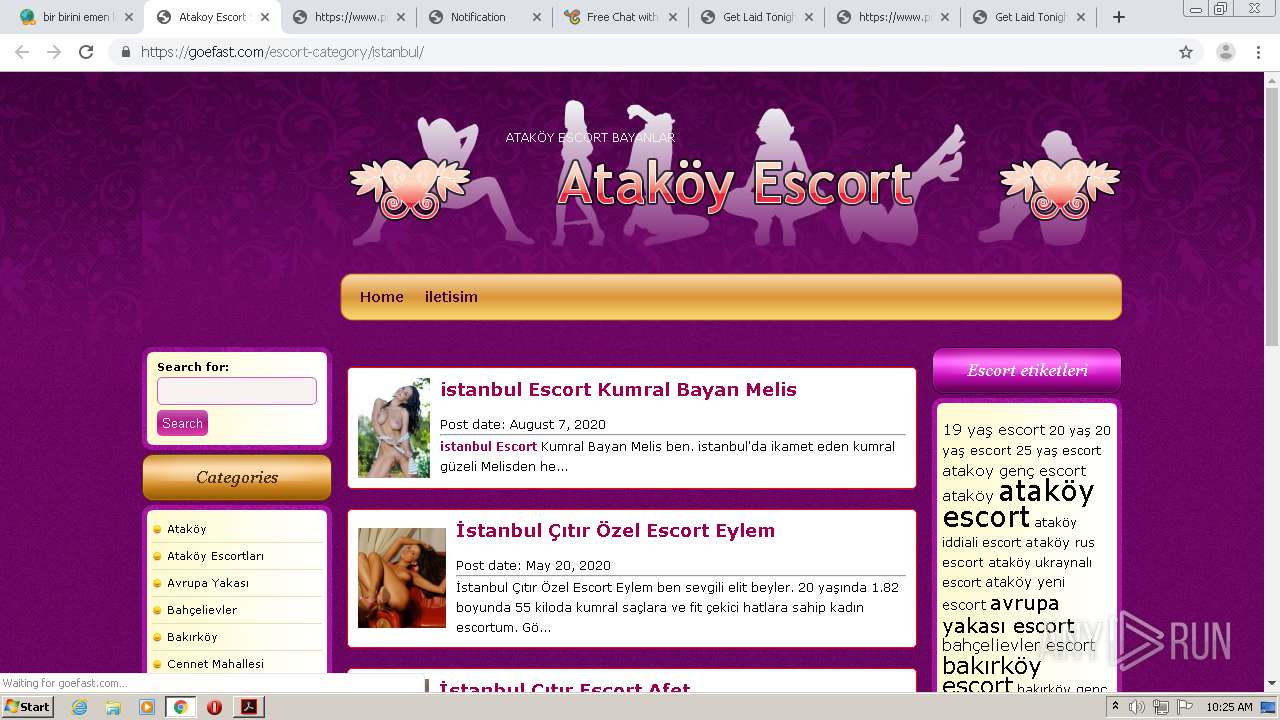
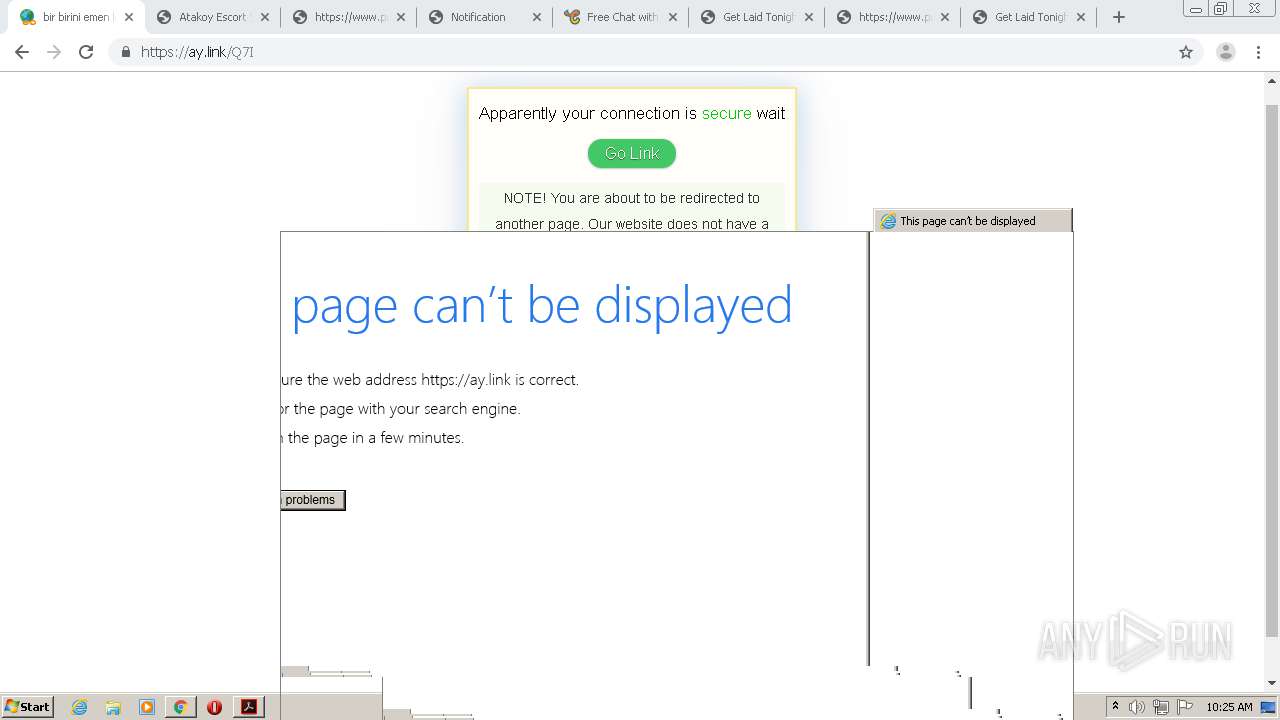
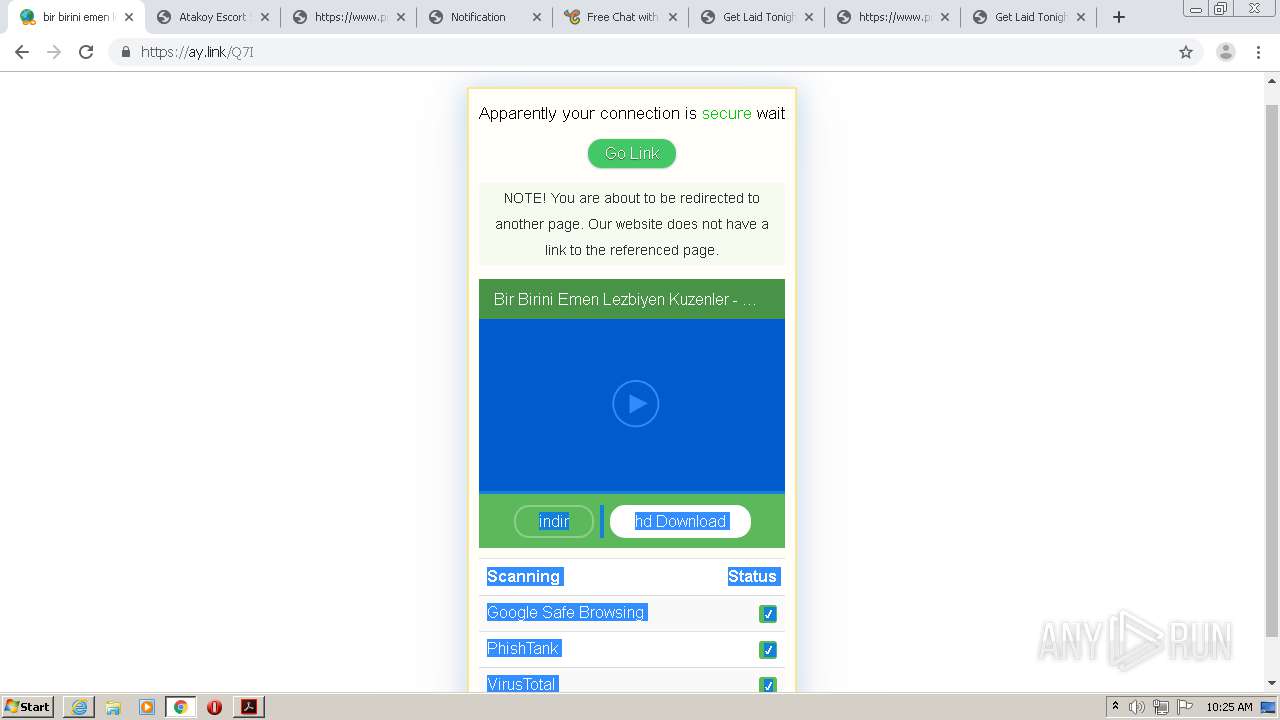
| URL: | https://t.co/wt6lMTJXox?amp=1 |
| Full analysis: | https://app.any.run/tasks/b1eaf092-97a5-41fe-8452-5cc048b9e60c |
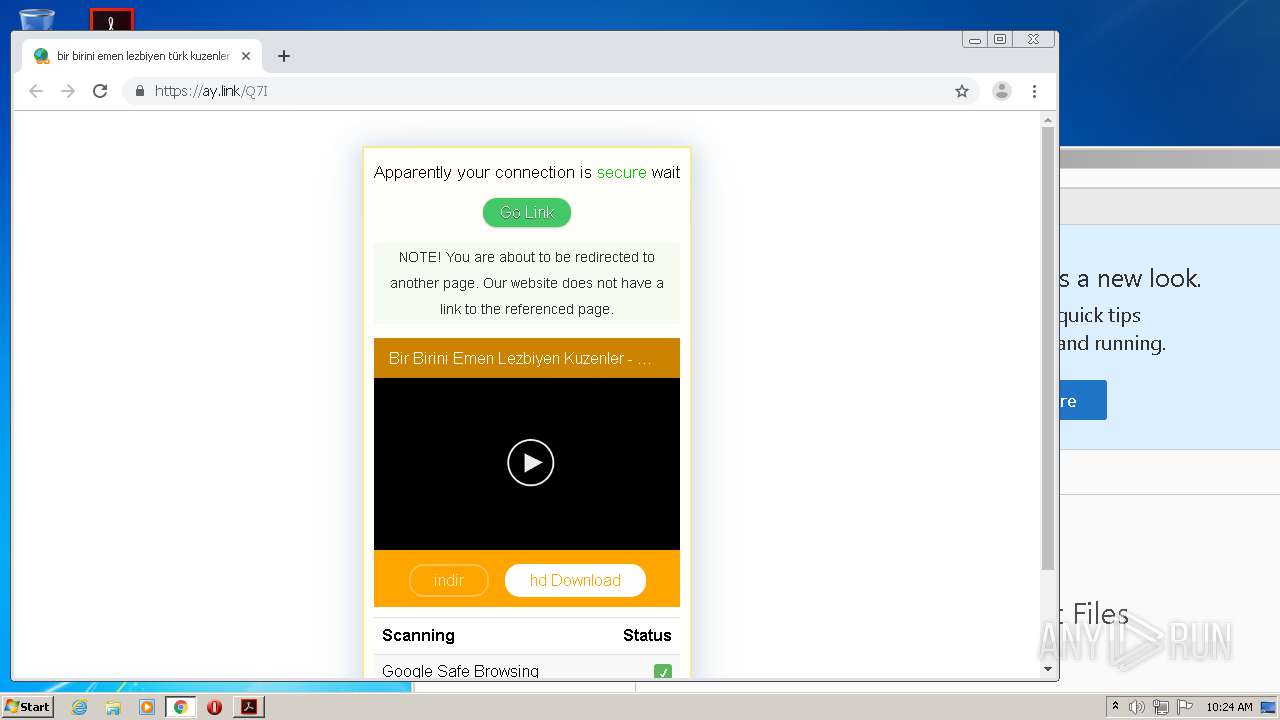
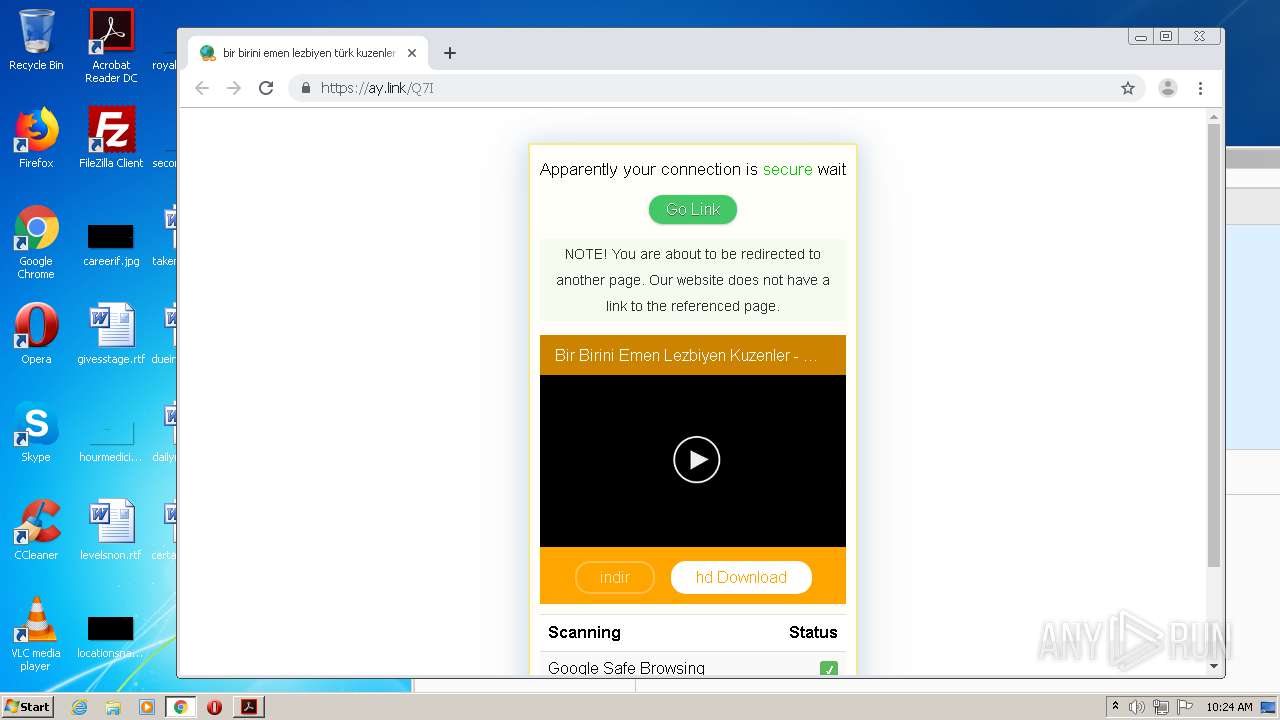
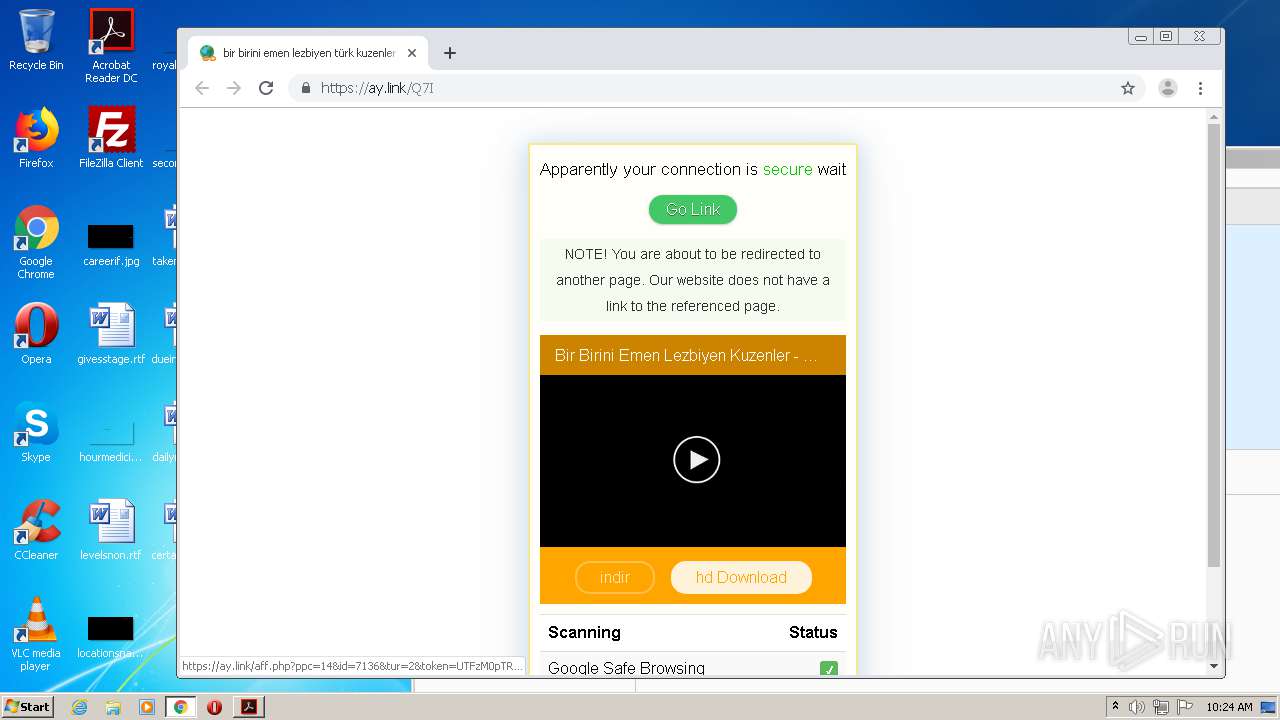
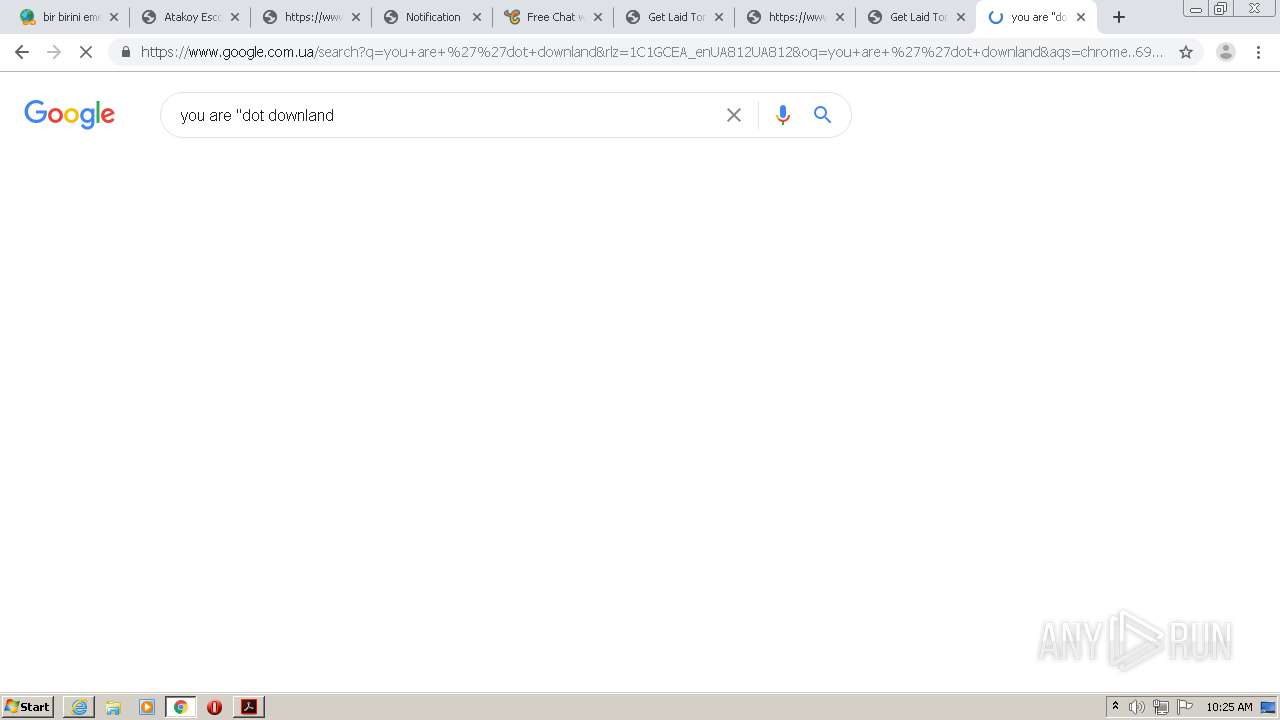
| Verdict: | Malicious activity |
| Analysis date: | September 09, 2020, 09:22:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DC64AE313235995337FC8B83F27F68E4 |
| SHA1: | A2AEF1AC3B4F06933E176D2051EA3B72600D3EC9 |
| SHA256: | 81730144B612313EB2DA54C52D2AA9CE796EEDB8BED361540898D0D7597B2438 |
| SSDEEP: | 3:N8DIiTJSGdU:28Nv |
MALICIOUS
No malicious indicators.SUSPICIOUS
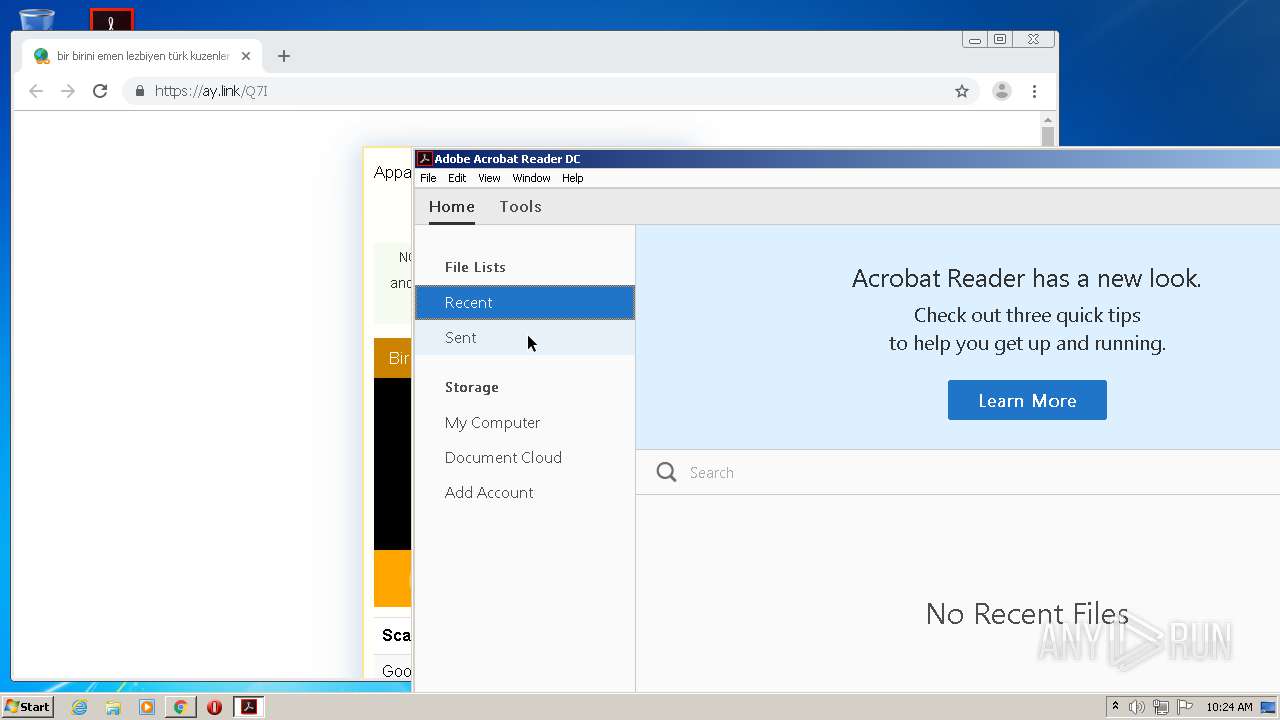
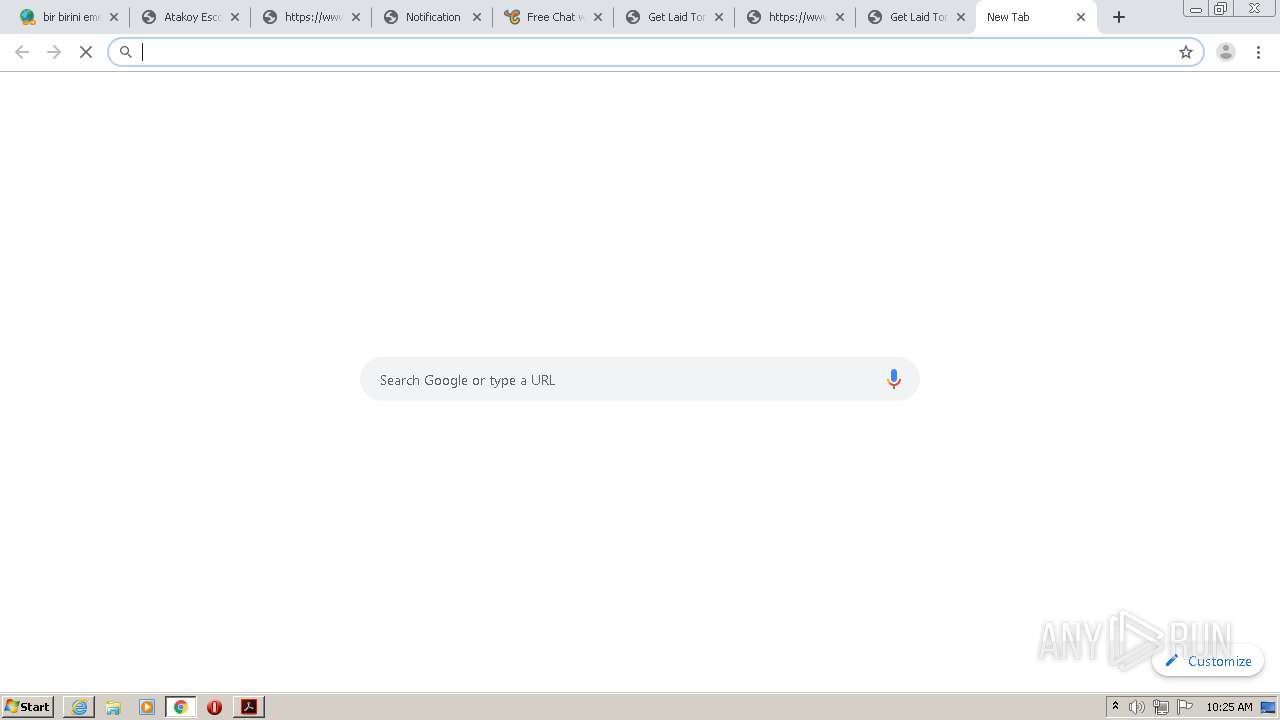
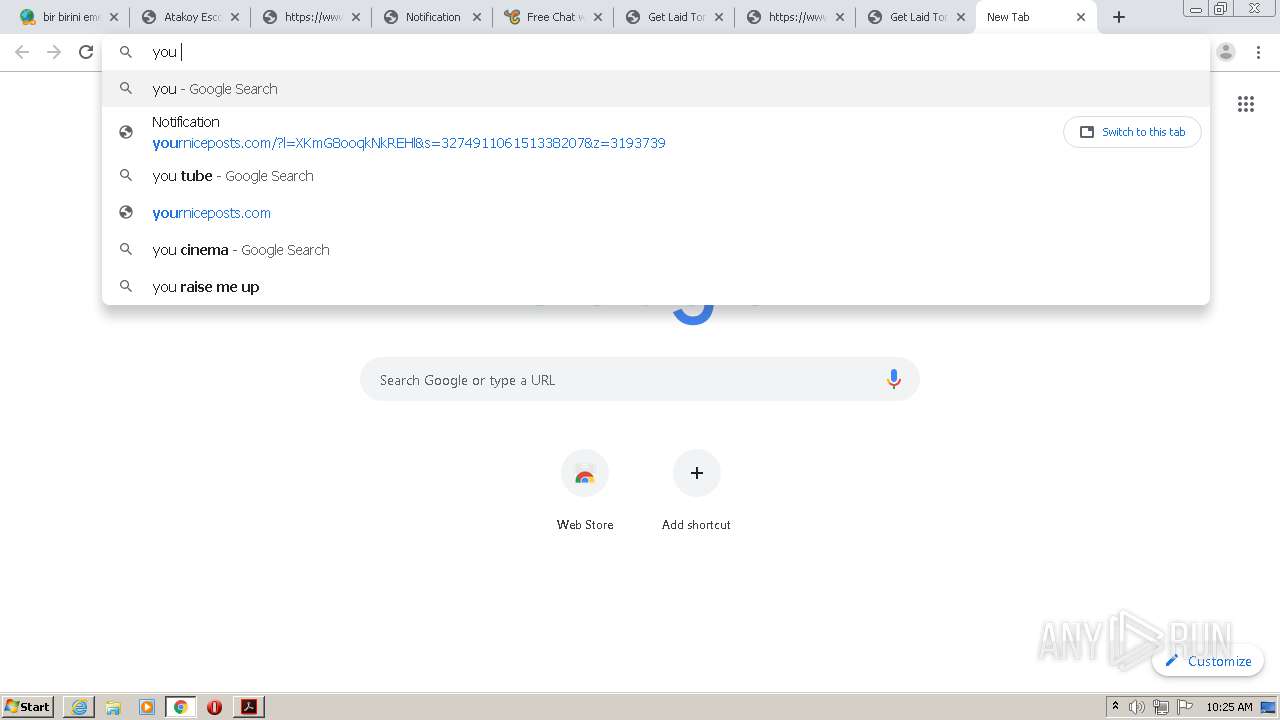
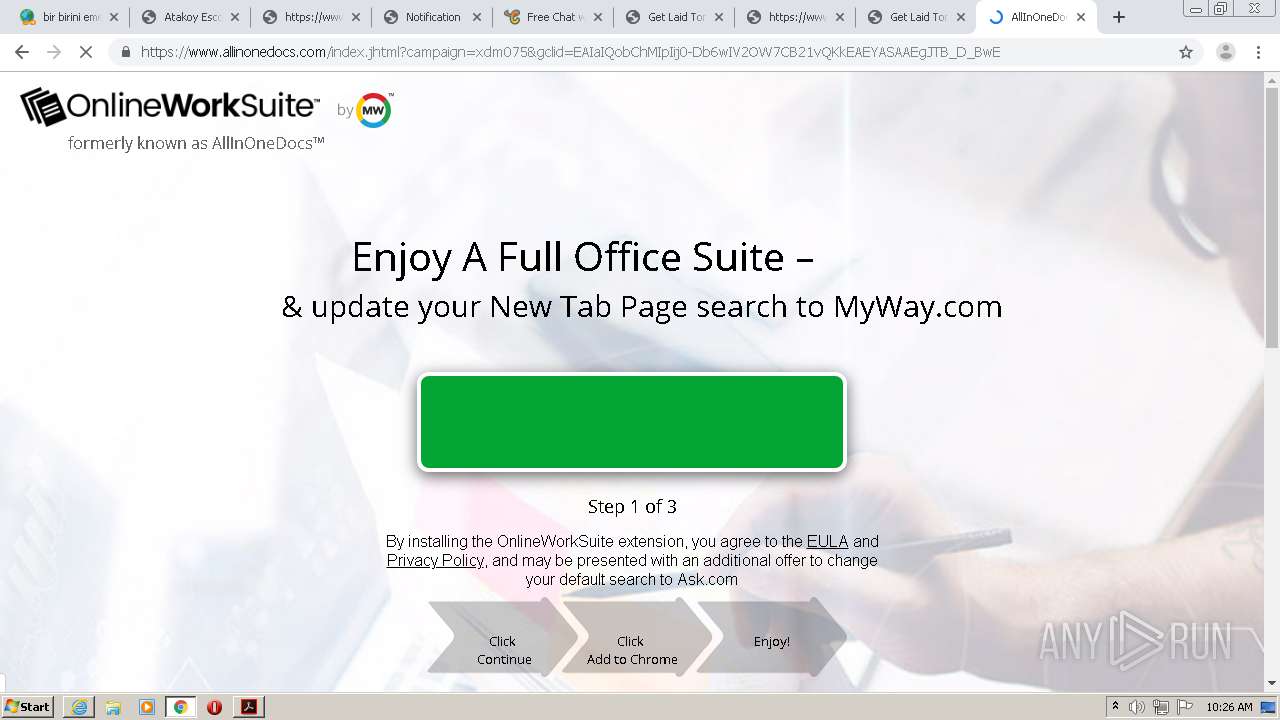
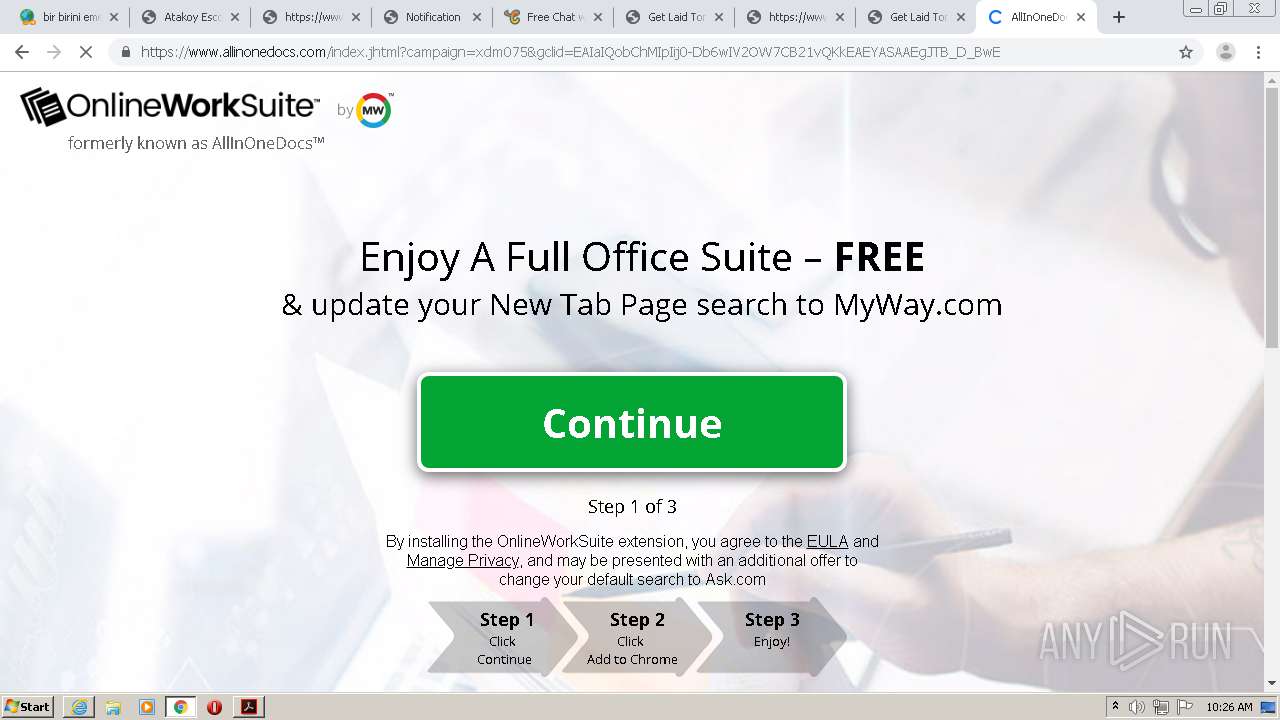
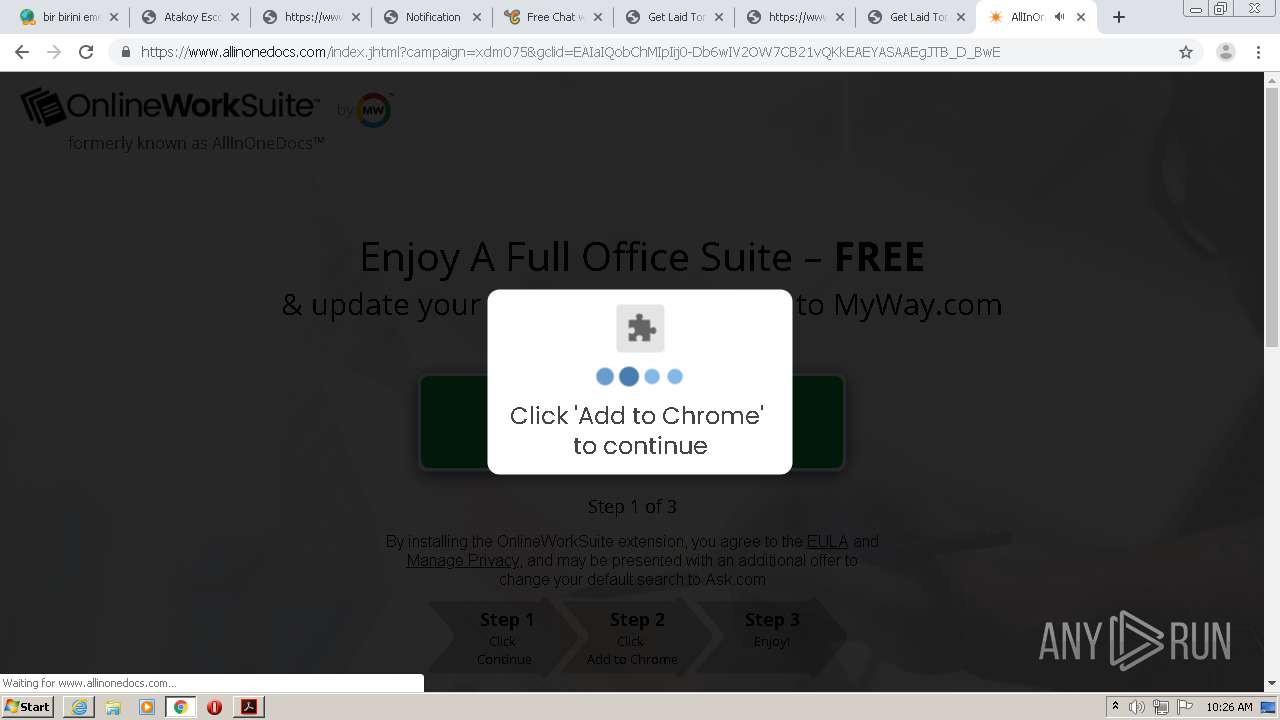
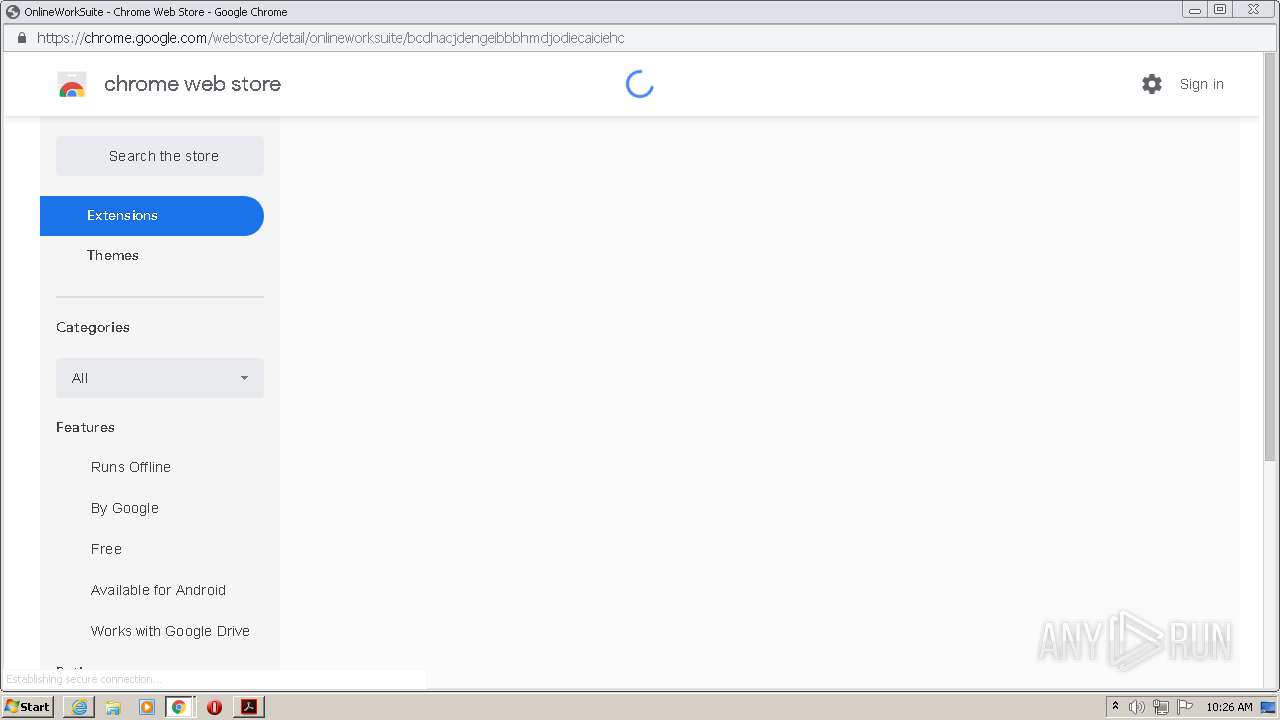
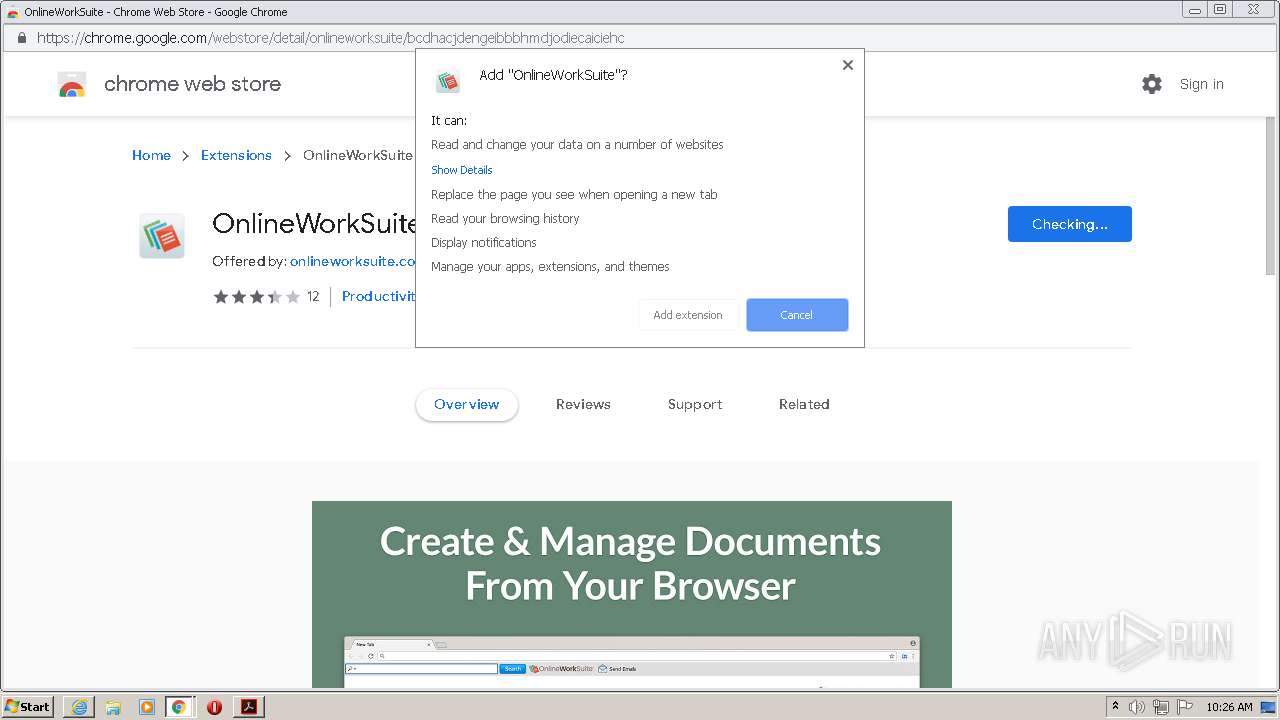
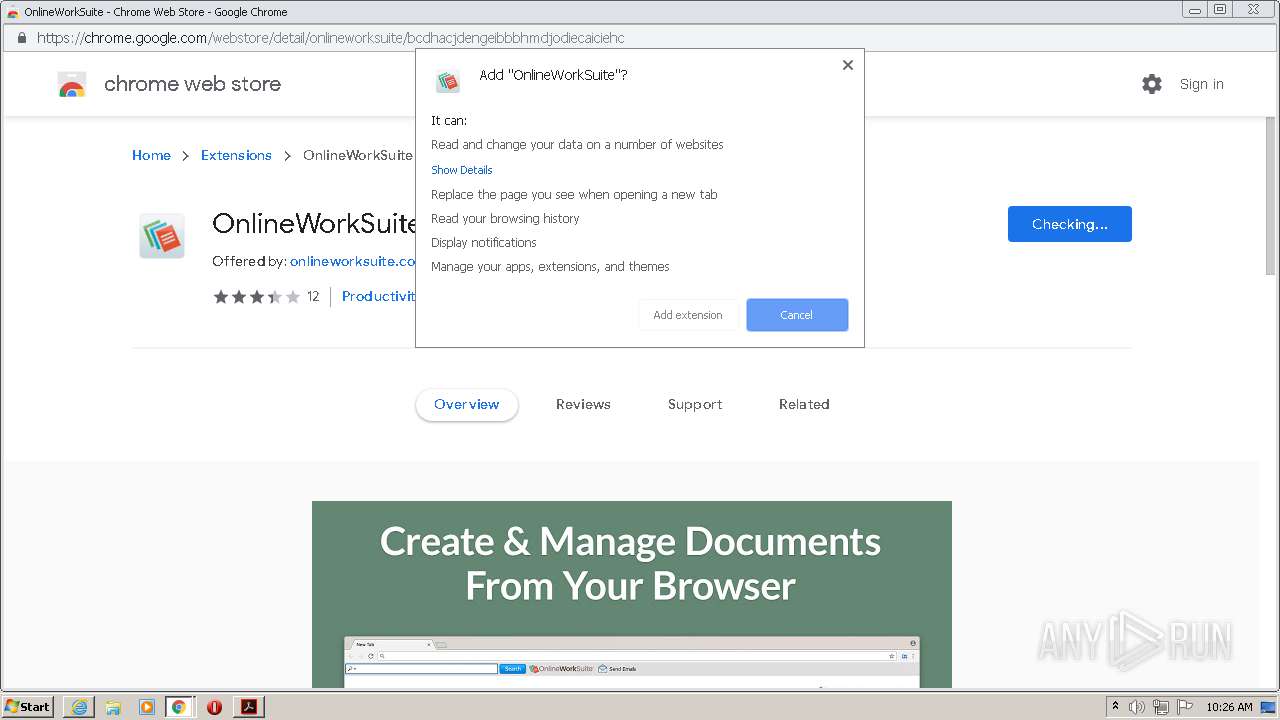
Modifies files in Chrome extension folder
- chrome.exe (PID: 2888)
Changes IE settings (feature browser emulation)
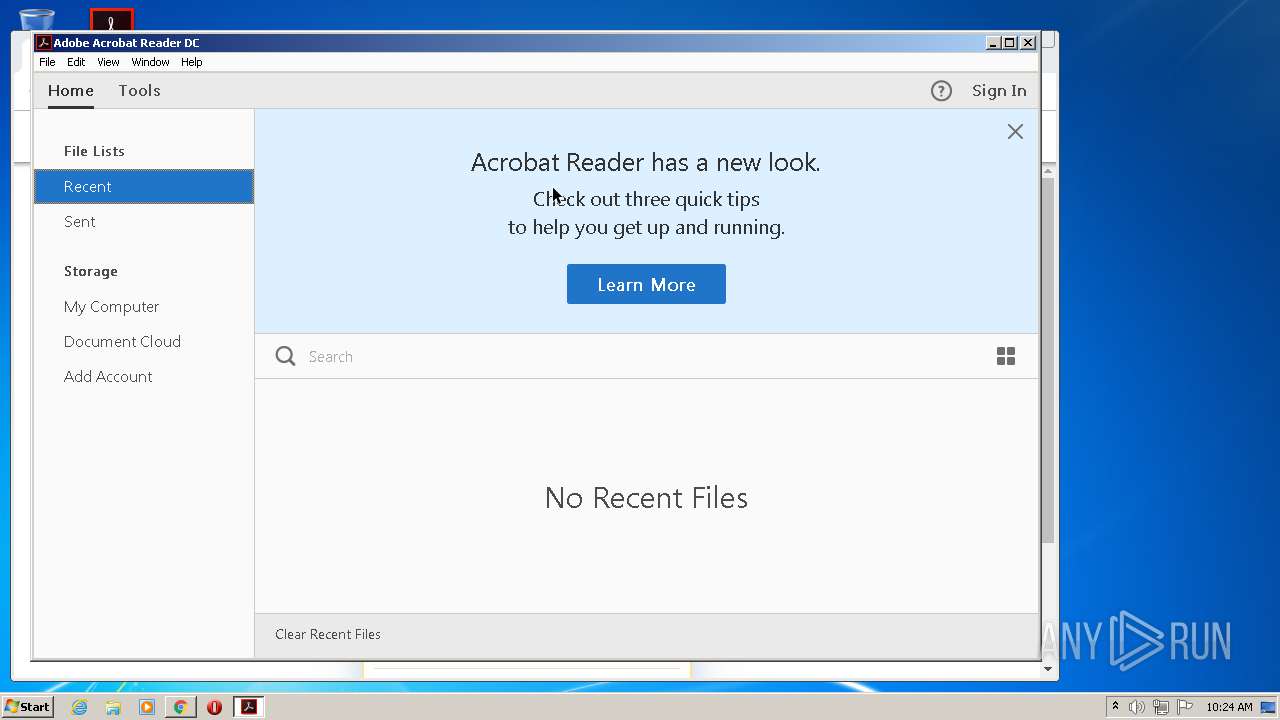
- AcroRd32.exe (PID: 2856)
Creates files in the program directory
- AdobeARM.exe (PID: 2260)
INFO
Application launched itself
- chrome.exe (PID: 2888)
- AcroRd32.exe (PID: 2536)
- AcroRd32.exe (PID: 2856)
- RdrCEF.exe (PID: 2892)
- iexplore.exe (PID: 548)
- AcroRd32.exe (PID: 1352)
- AcroRd32.exe (PID: 316)
Manual execution by user
- AcroRd32.exe (PID: 2856)
- AcroRd32.exe (PID: 1352)
- iexplore.exe (PID: 548)
- AcroRd32.exe (PID: 2536)
- AcroRd32.exe (PID: 316)
Creates files in the user directory
- chrome.exe (PID: 2888)
- iexplore.exe (PID: 548)
- iexplore.exe (PID: 2400)
Reads the hosts file
- RdrCEF.exe (PID: 2892)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 2860)
Reads Internet Cache Settings
- AcroRd32.exe (PID: 2856)
- AcroRd32.exe (PID: 3032)
- iexplore.exe (PID: 548)
- iexplore.exe (PID: 2400)
- chrome.exe (PID: 2888)
Reads settings of System Certificates
- AcroRd32.exe (PID: 2856)
- iexplore.exe (PID: 2400)
- iexplore.exe (PID: 548)
Changes internet zones settings
- iexplore.exe (PID: 548)
Changes settings of System certificates
- iexplore.exe (PID: 548)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2888)
Adds / modifies Windows certificates
- iexplore.exe (PID: 548)
Reads internet explorer settings
- iexplore.exe (PID: 2400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
125
Monitored processes
86
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,3074282237262450378,3351141411722303329,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13195056744558362386 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 280 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | explorer.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,3074282237262450378,3351141411722303329,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5484512447279285662 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
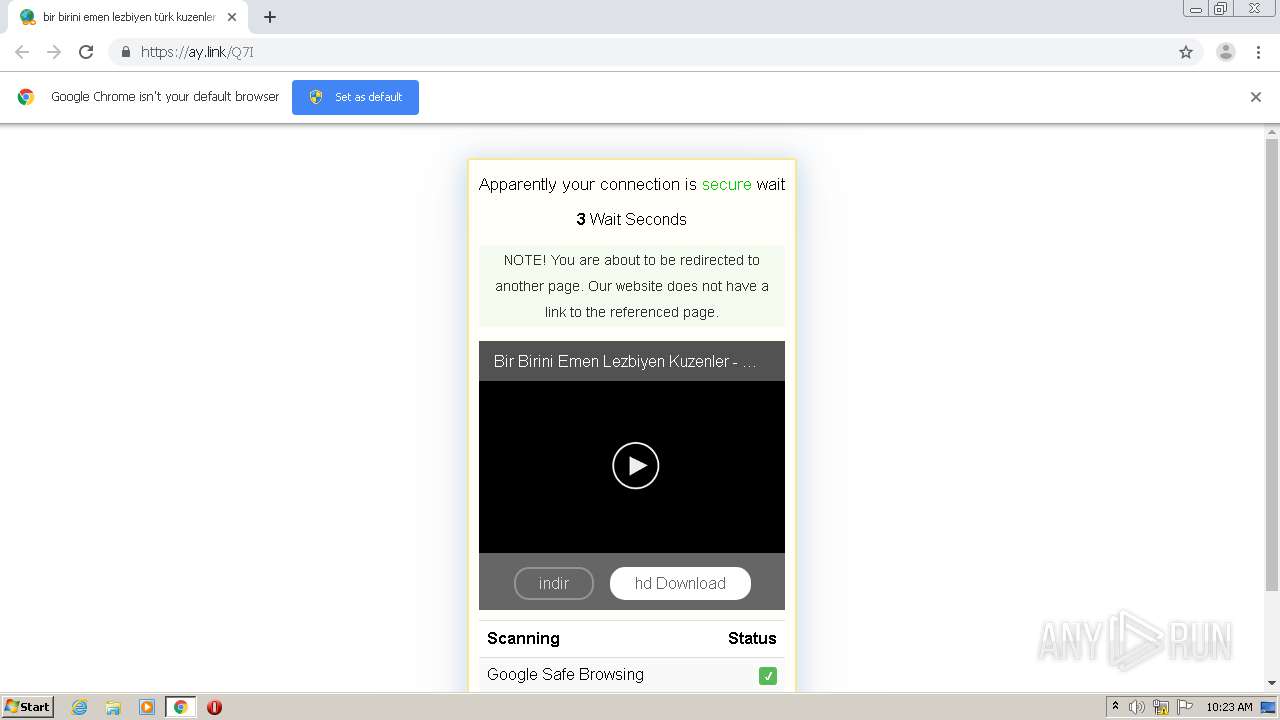
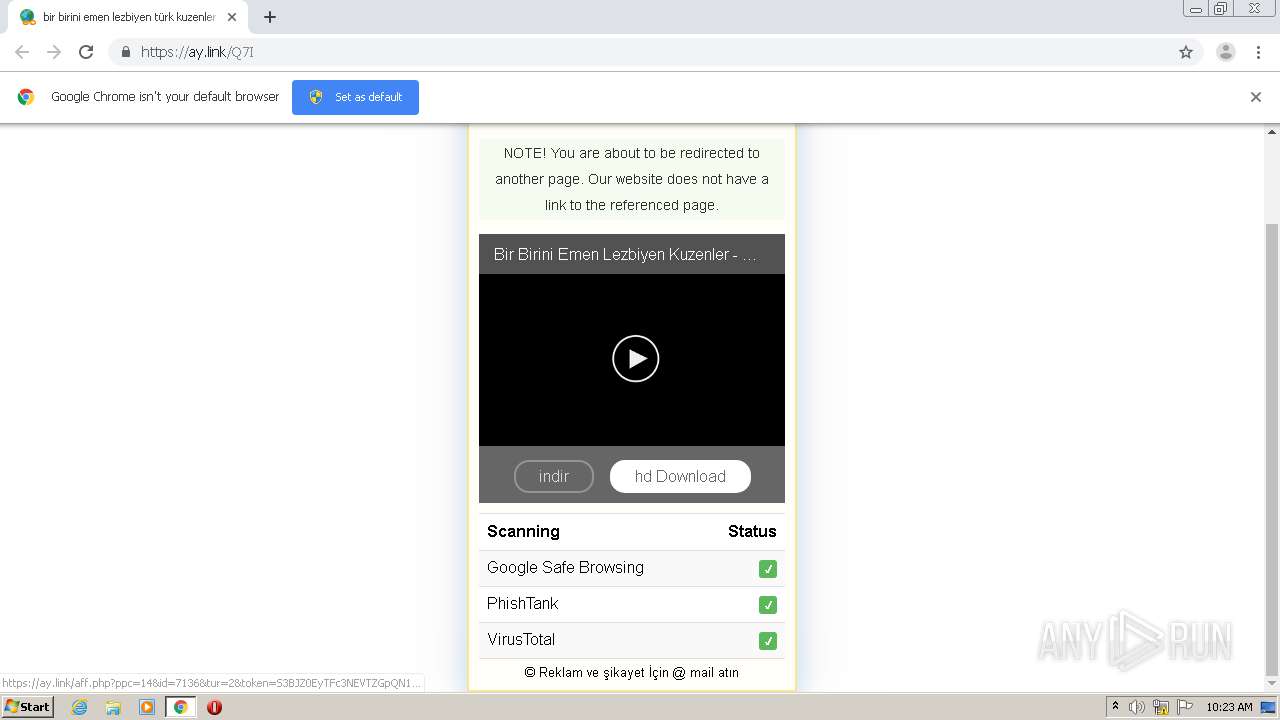
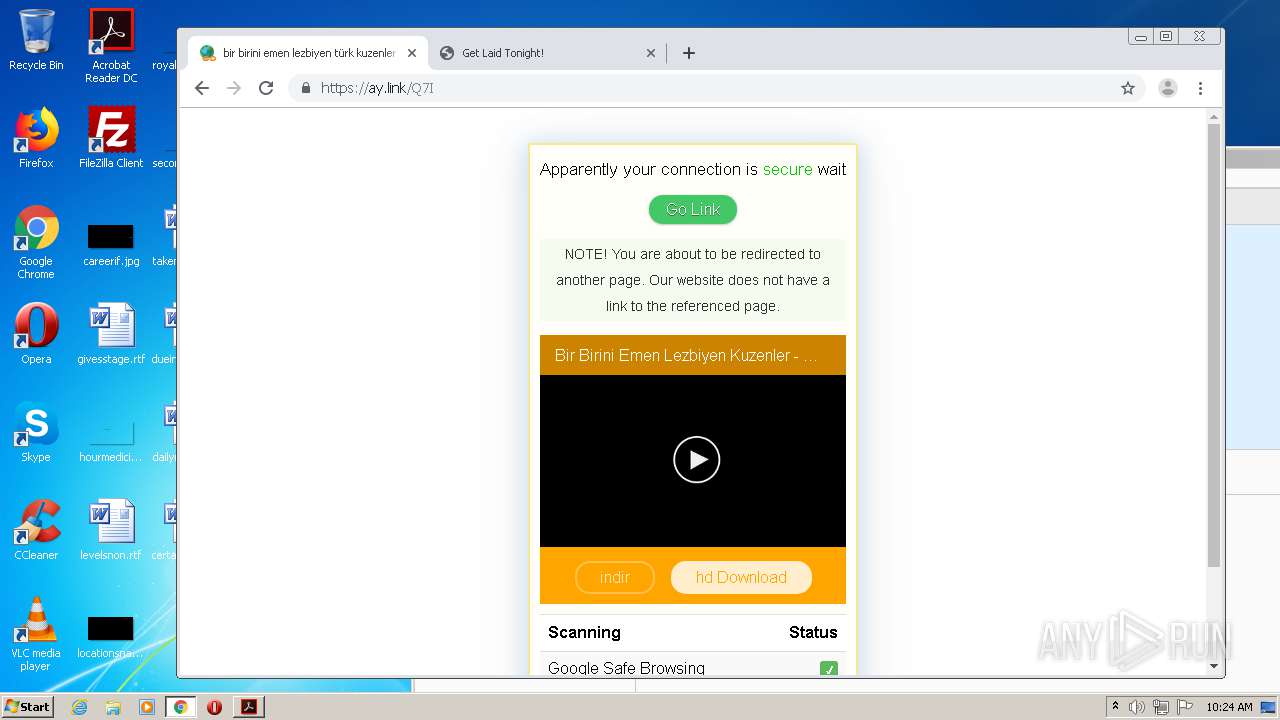
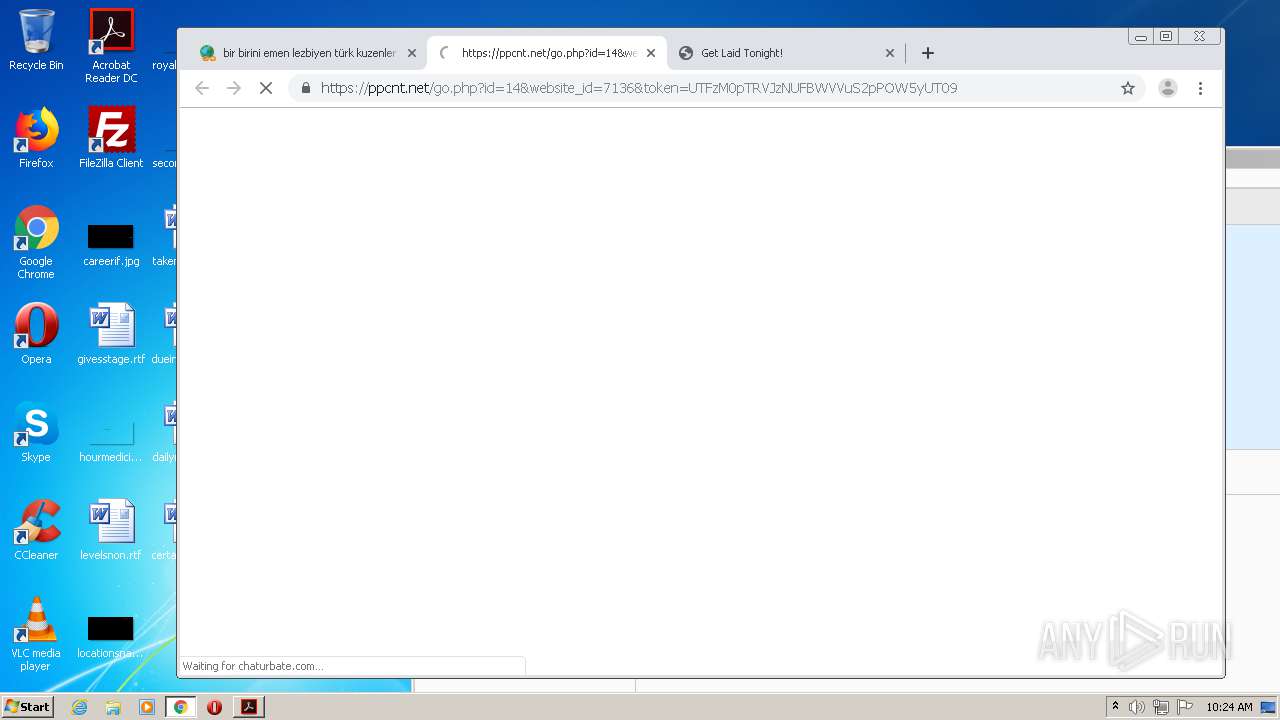
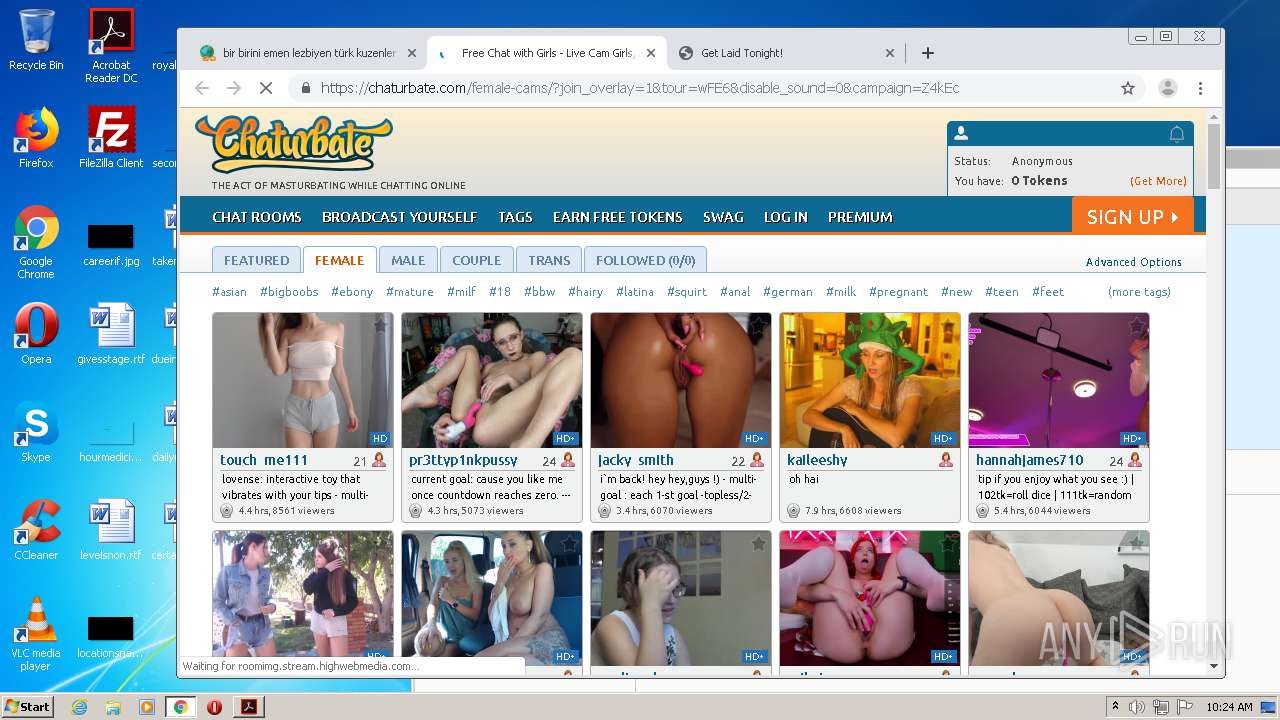
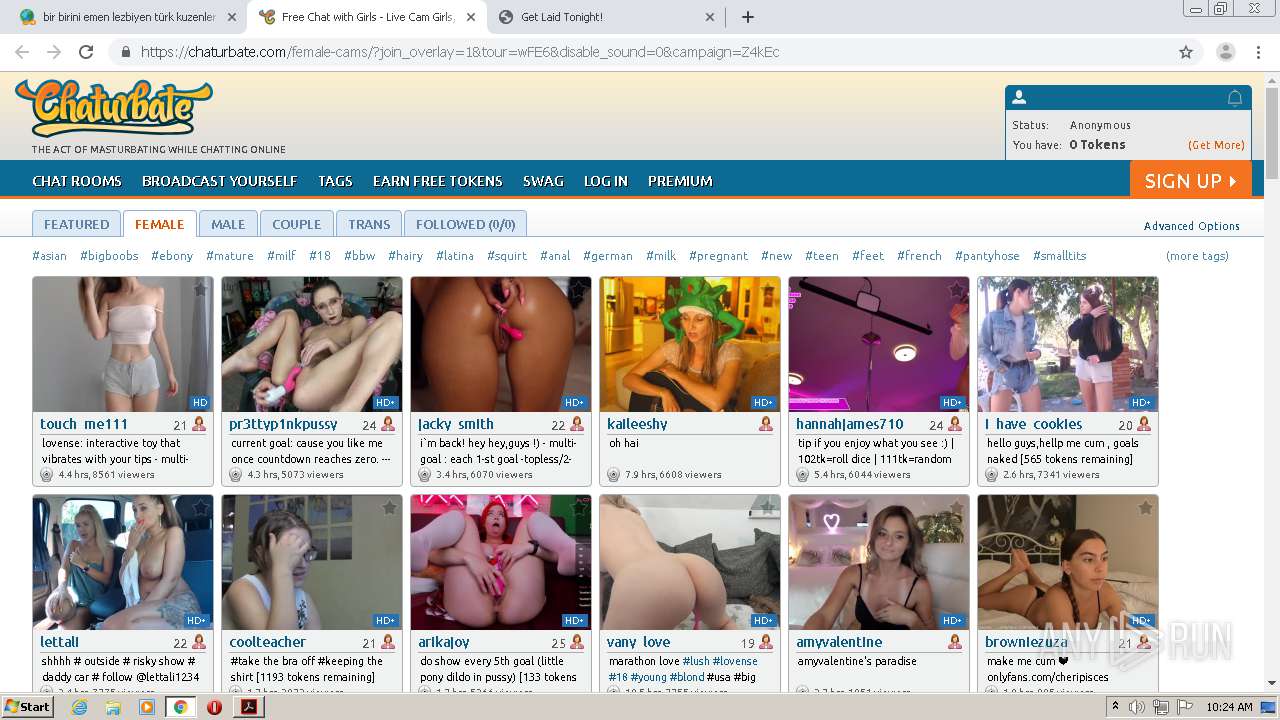
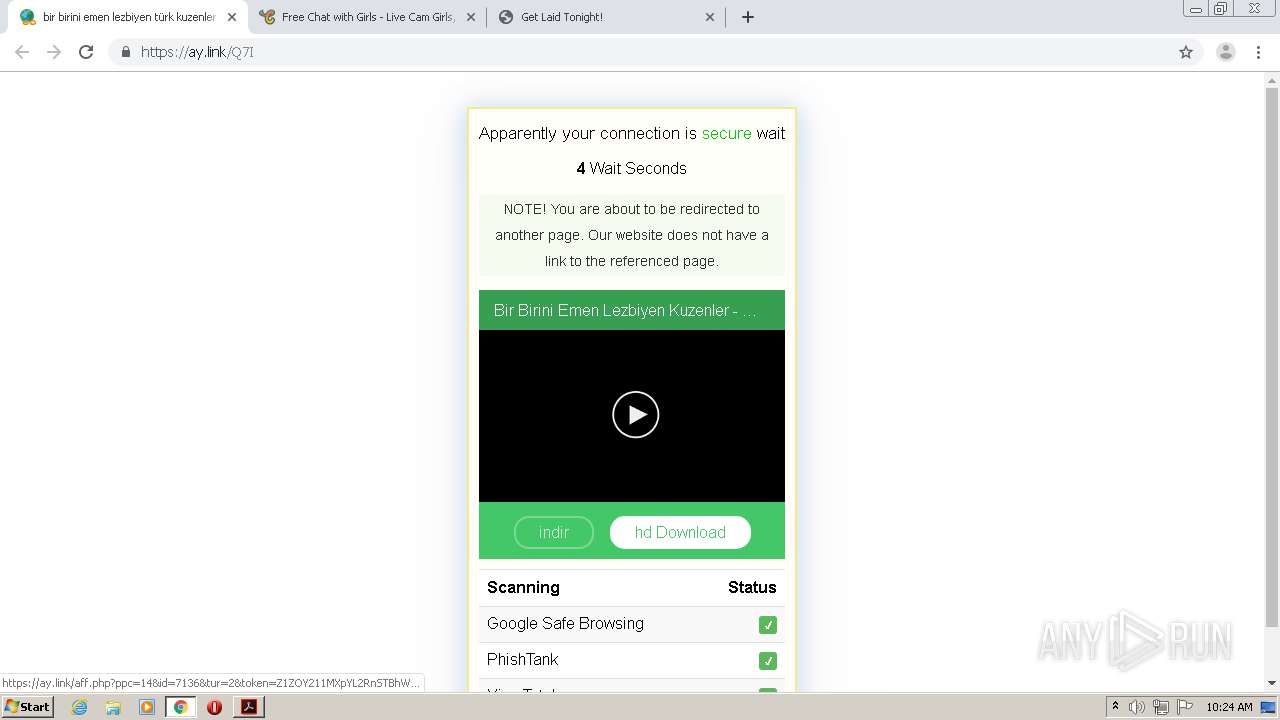
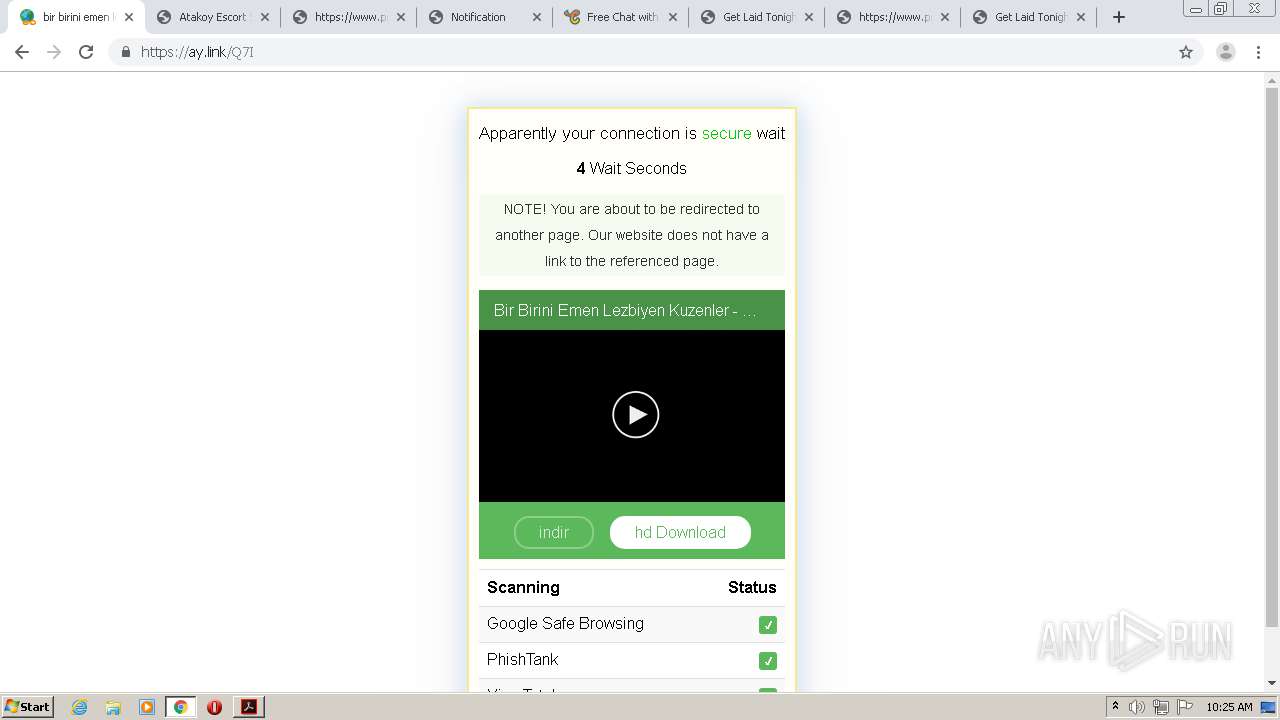
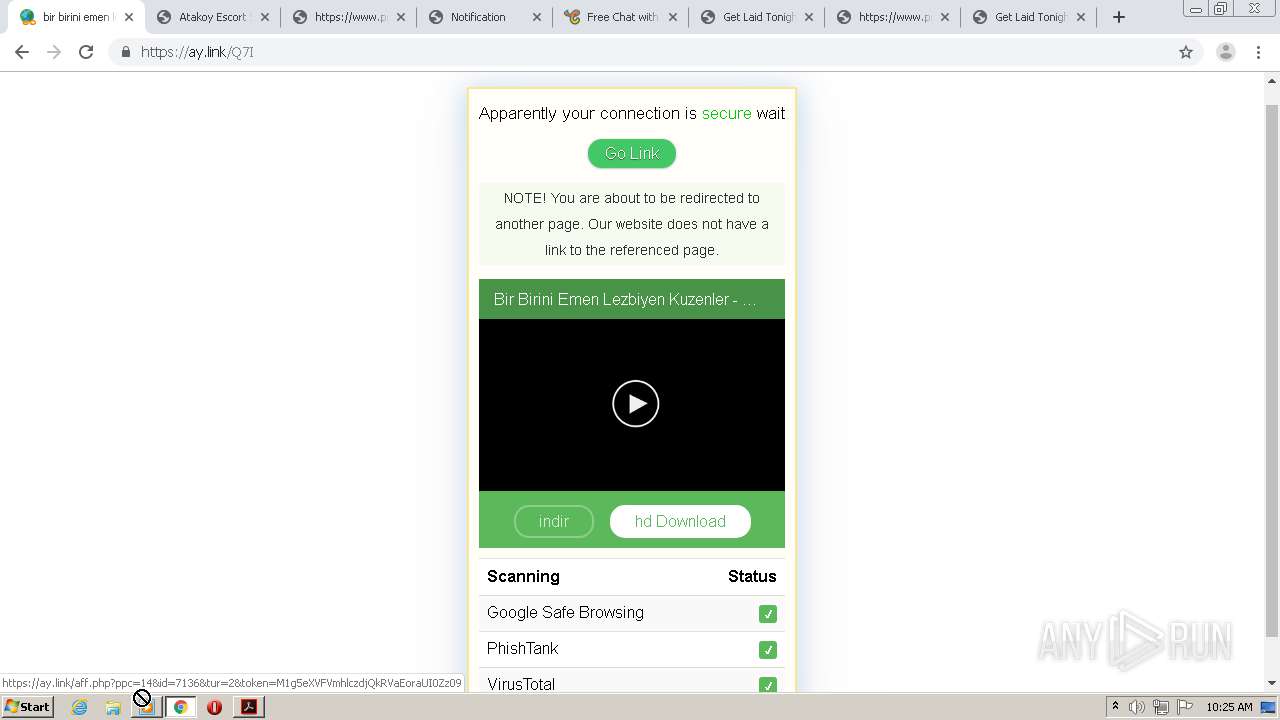
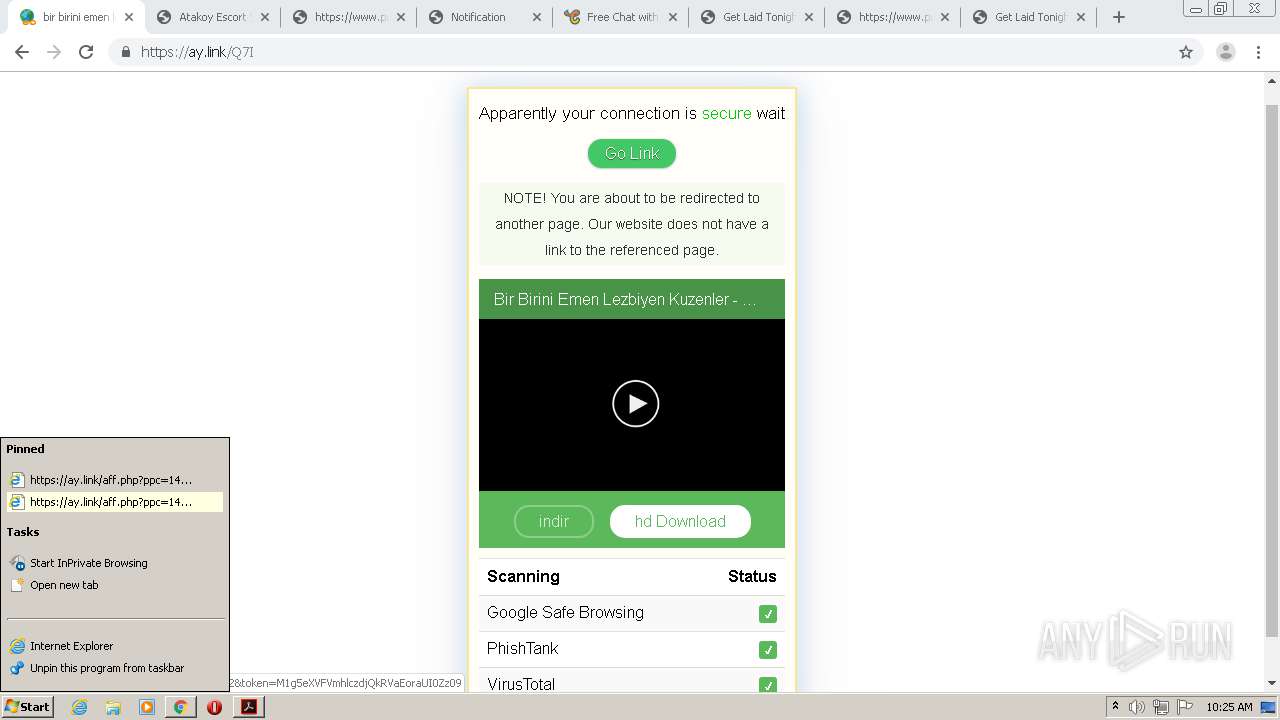
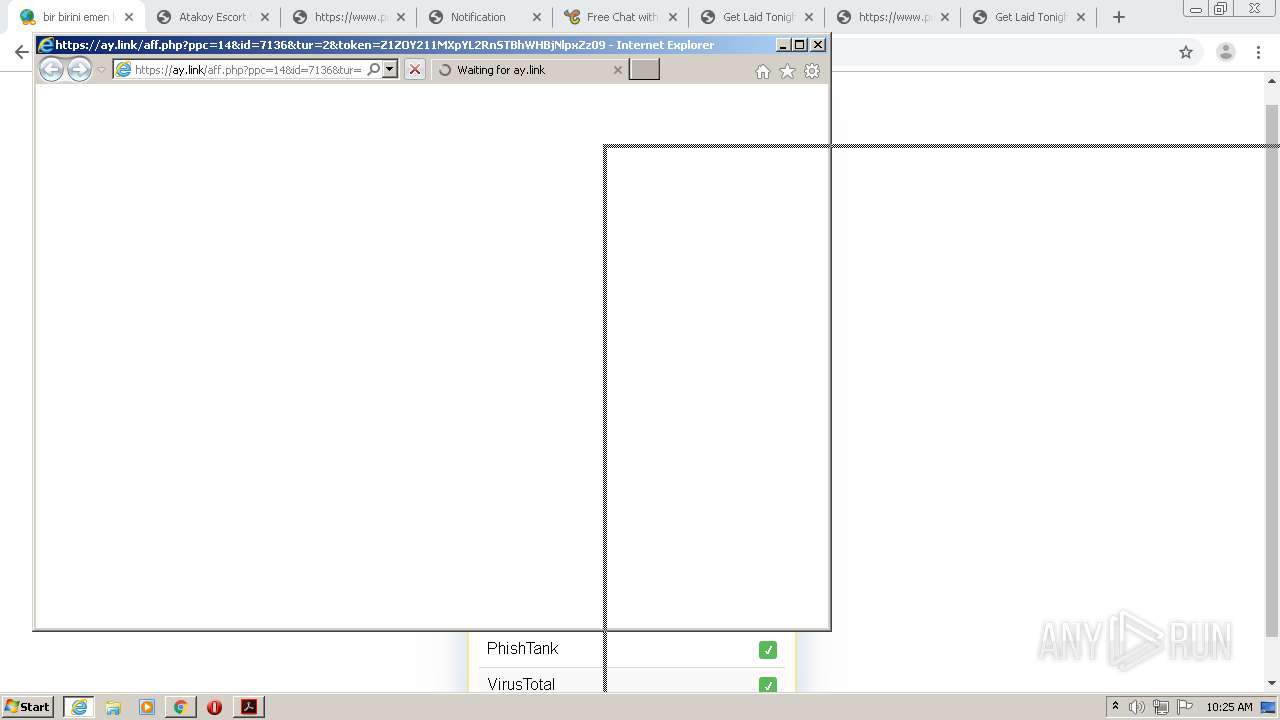
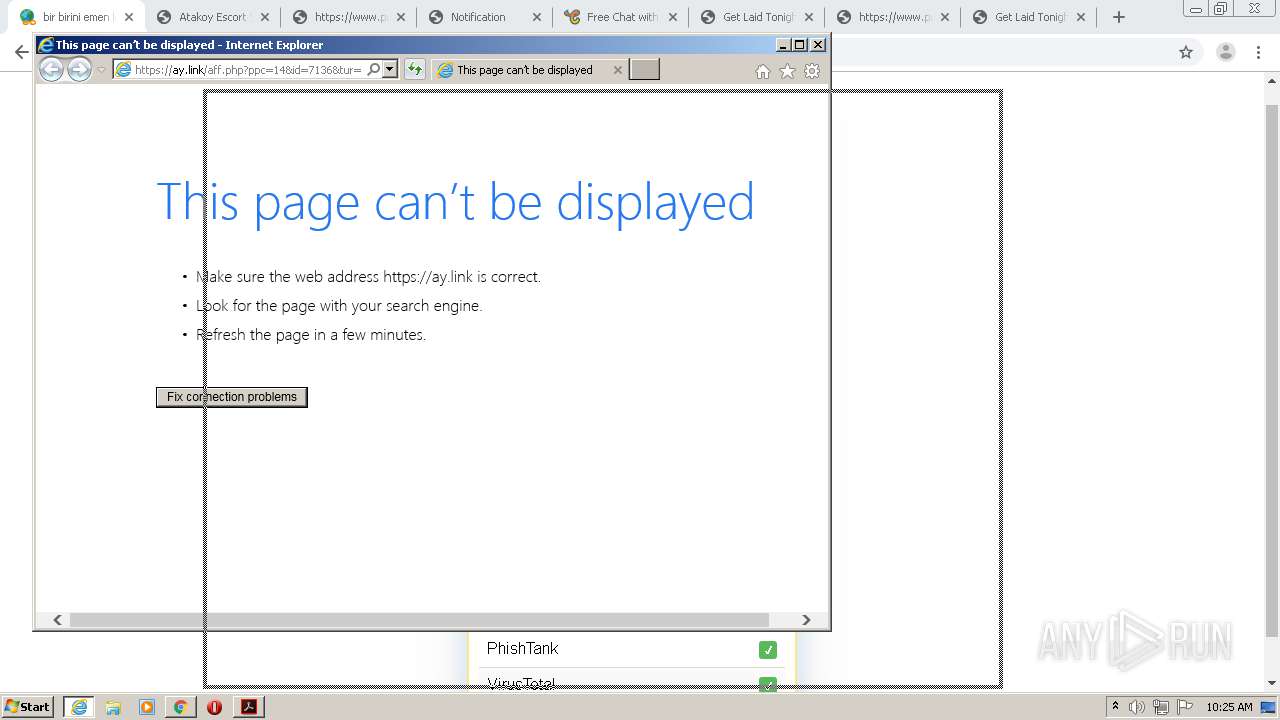
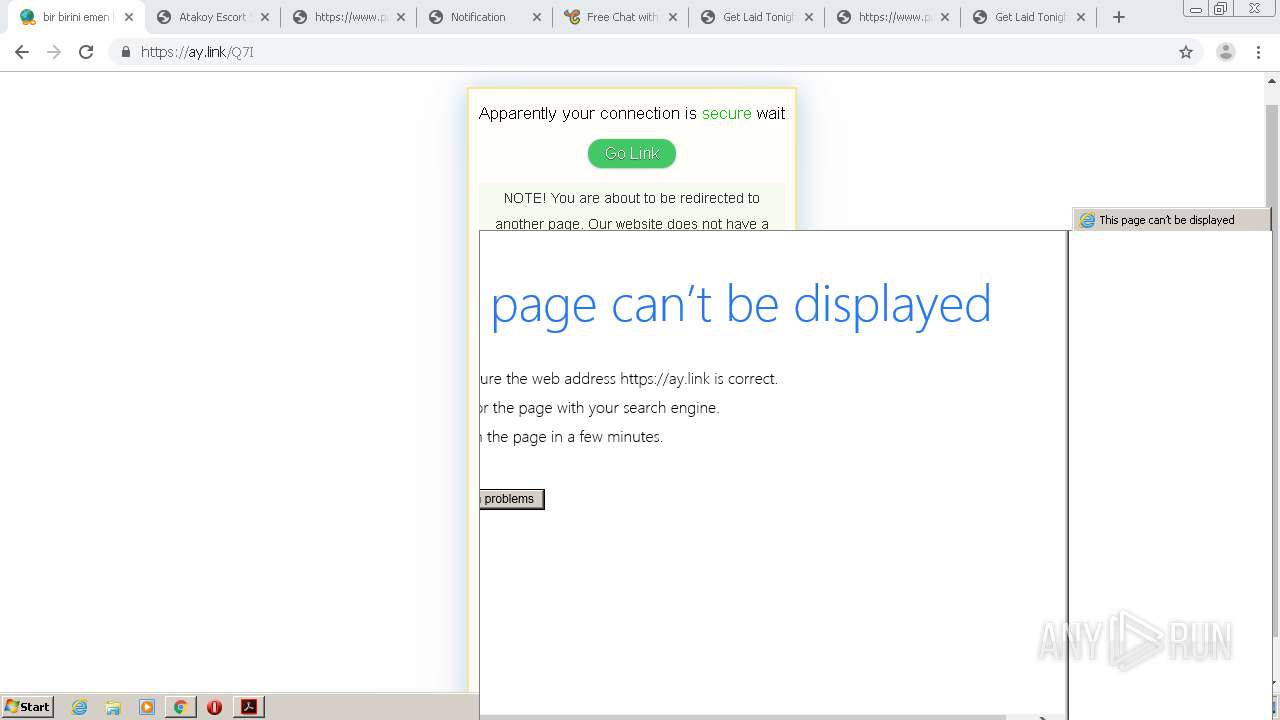
| 548 | "C:\Program Files\Internet Explorer\iexplore.exe" https://ay.link/aff.php?ppc=14&id=7136&tur=2&token=Z1ZOY211MXpYL2RnSTBhWHBjNlpxZz09 | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,3074282237262450378,3351141411722303329,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10961316341765009019 --mojo-platform-channel-handle=3900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,3074282237262450378,3351141411722303329,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15534757211720496514 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,3074282237262450378,3351141411722303329,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7161970437940081173 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,3074282237262450378,3351141411722303329,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11526418705530890761 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | explorer.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
Total events
1 968
Read events
1 707
Write events
255
Delete events
6
Modification events
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2888-13244116984561125 |
Value: 259 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
244
Text files
389
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f829a07f-9e0d-4759-88bc-9764f0d9e088.tmp | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF150c3e.TMP | text | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF150d96.TMP | — | |
MD5:— | SHA256:— | |||
| 2888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF150ba2.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
122
TCP/UDP connections
251
DNS requests
117
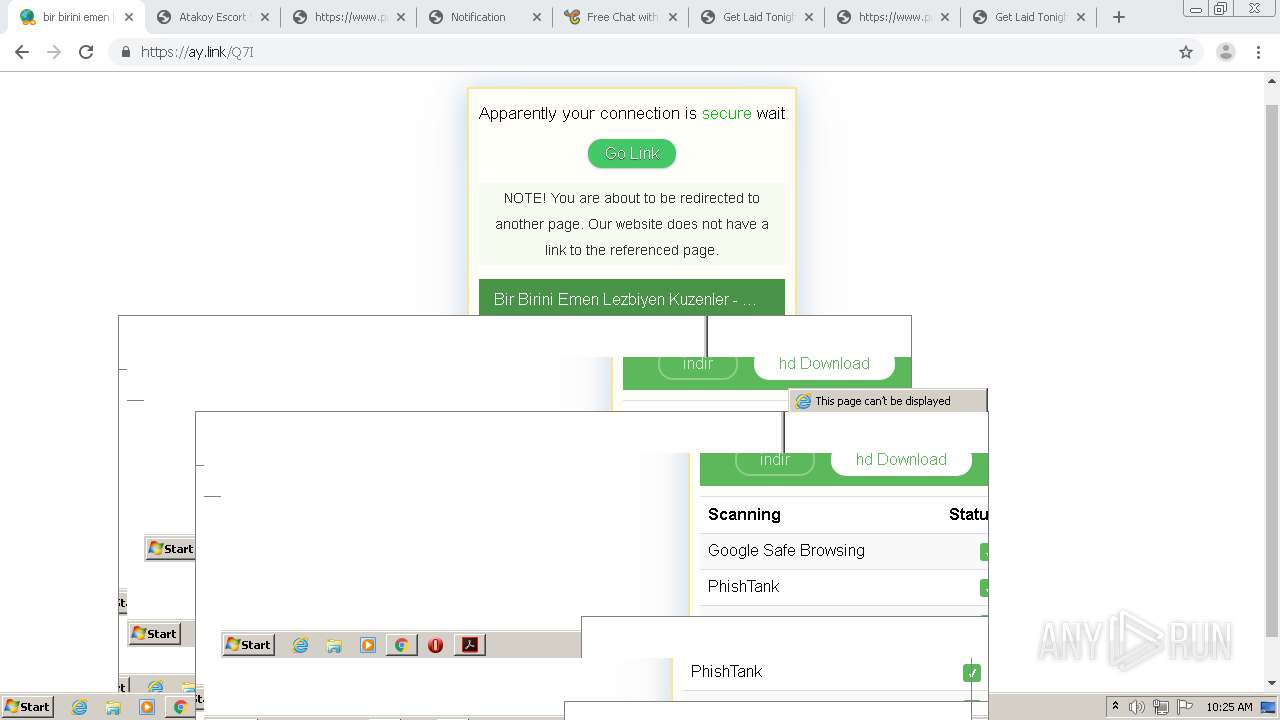
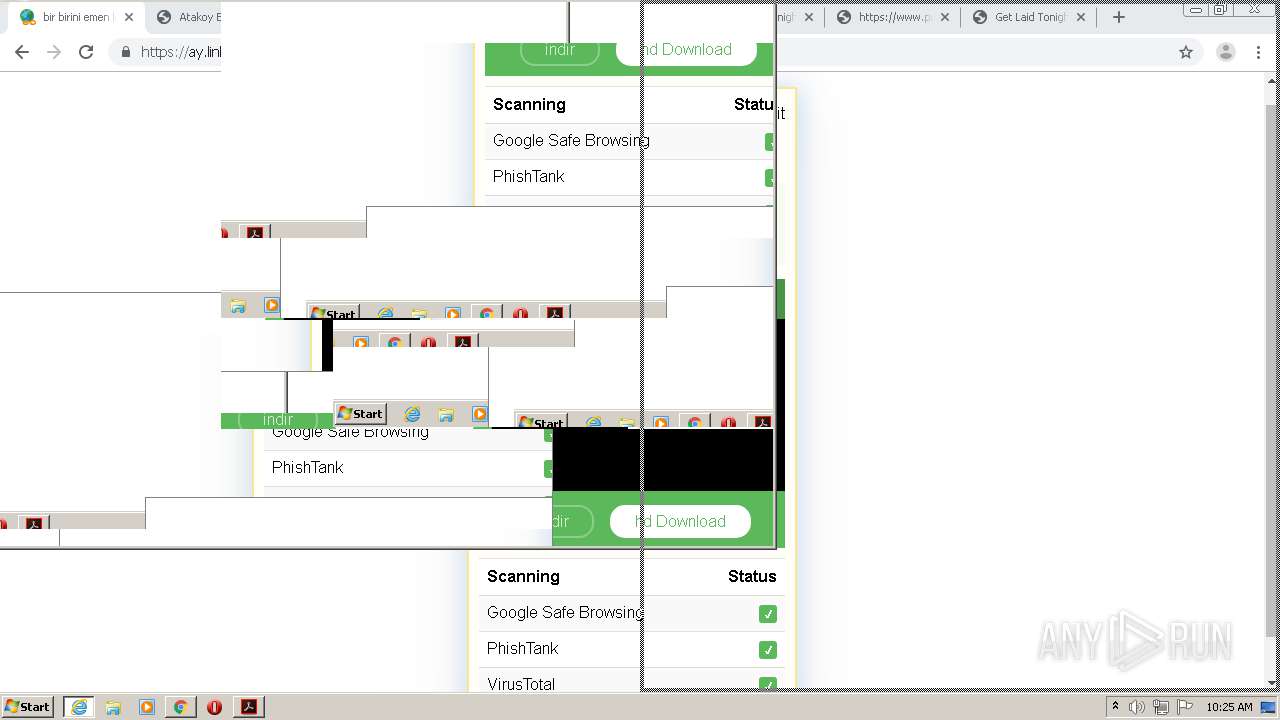
Threats
72
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
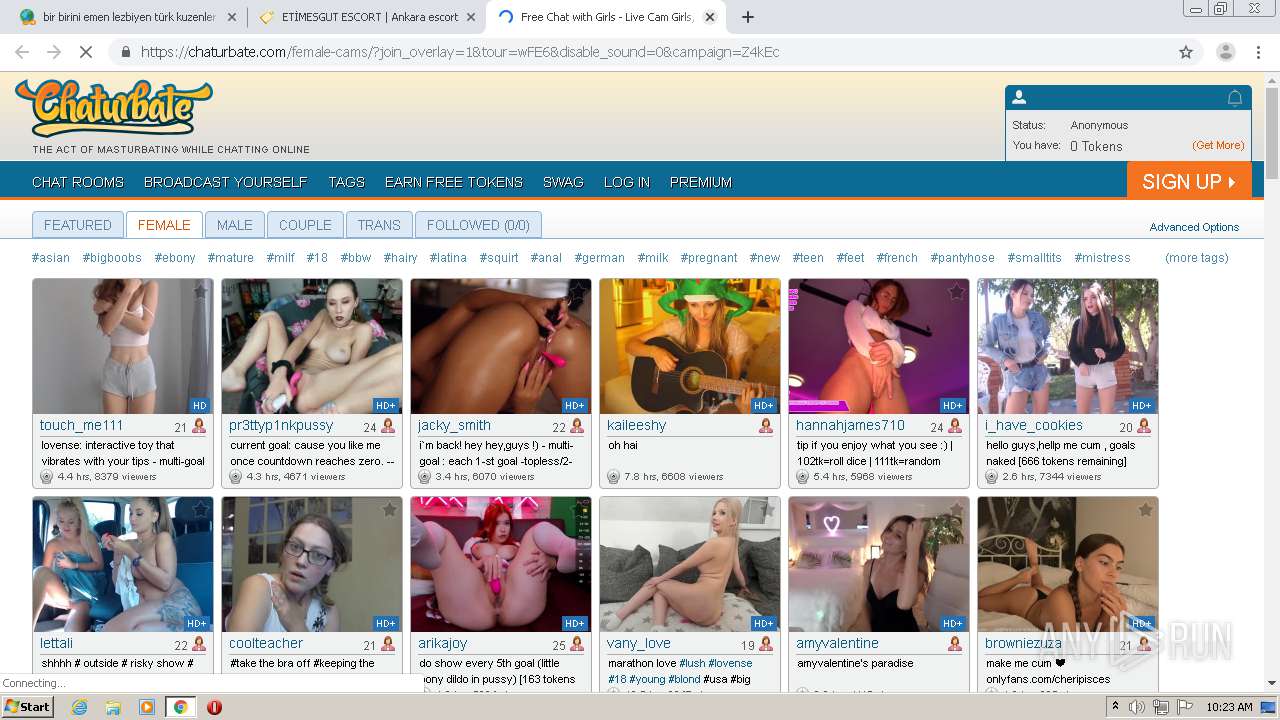
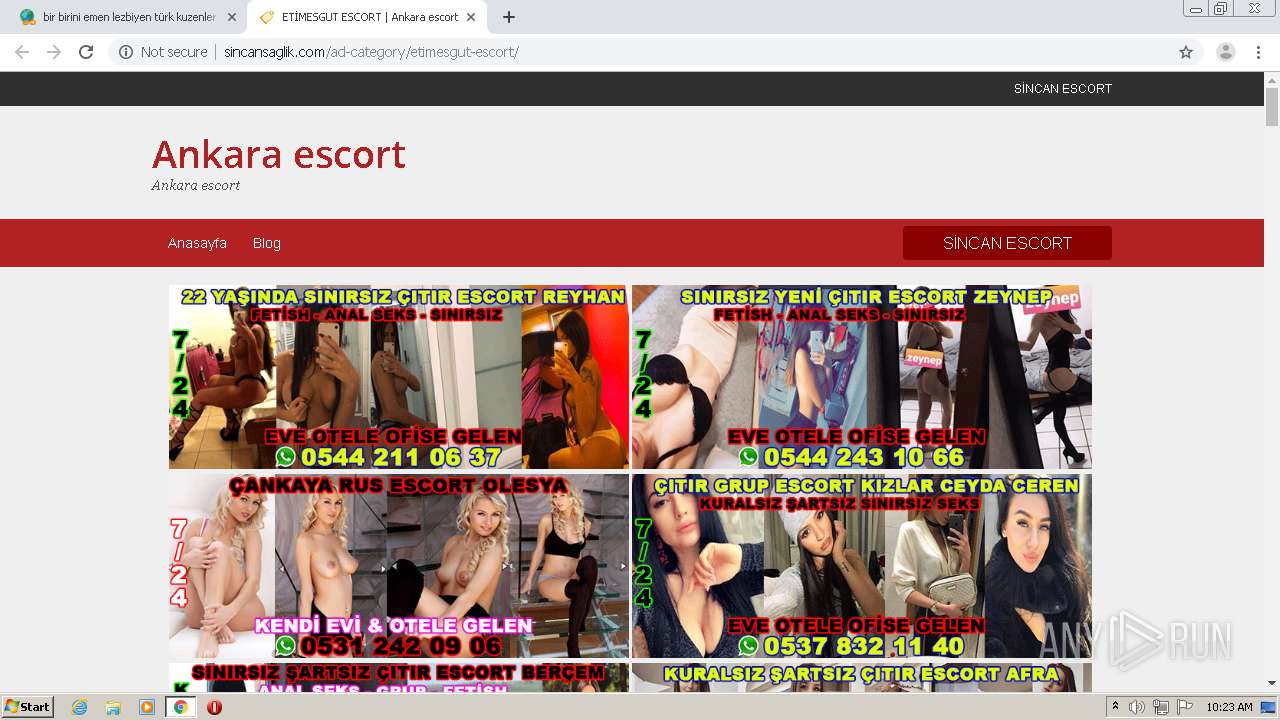
2860 | chrome.exe | GET | 200 | 172.67.175.55:80 | http://cdn.sincansaglik.com/wp-content/uploads/2019/08/Sohbet-Sever-Gecelik-S%C4%B1hh%C4%B1ye-Escort-Cemre-250x250.jpeg | US | image | 5.79 Kb | suspicious |
2860 | chrome.exe | GET | 200 | 173.194.187.72:80 | http://r3---sn-4g5e6nsk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=89.187.165.47&mm=28&mn=sn-4g5e6nsk&ms=nvh&mt=1599639795&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 834 Kb | whitelisted |
2860 | chrome.exe | GET | 200 | 104.18.44.66:80 | http://meteilan108.xyz/wp-content/uploads/2020/09/goldreyhan.gif | US | image | 128 Kb | suspicious |
2860 | chrome.exe | GET | 200 | 104.18.44.66:80 | http://meteilan108.xyz/wp-content/uploads/2020/09/ceydaceren.gif | US | image | 152 Kb | suspicious |
2860 | chrome.exe | GET | 200 | 104.18.44.66:80 | http://meteilan108.xyz/wp-content/uploads/2020/09/goldzeynep.gif | US | image | 133 Kb | suspicious |
2860 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
2860 | chrome.exe | GET | 200 | 172.67.175.55:80 | http://cdn.sincansaglik.com/wp-content/uploads/2019/12/Swinger-Gen%C3%A7-Sevgililer-Demetevler-Escort-G%C3%BCne%C5%9F.jpg | US | image | 12.8 Kb | suspicious |
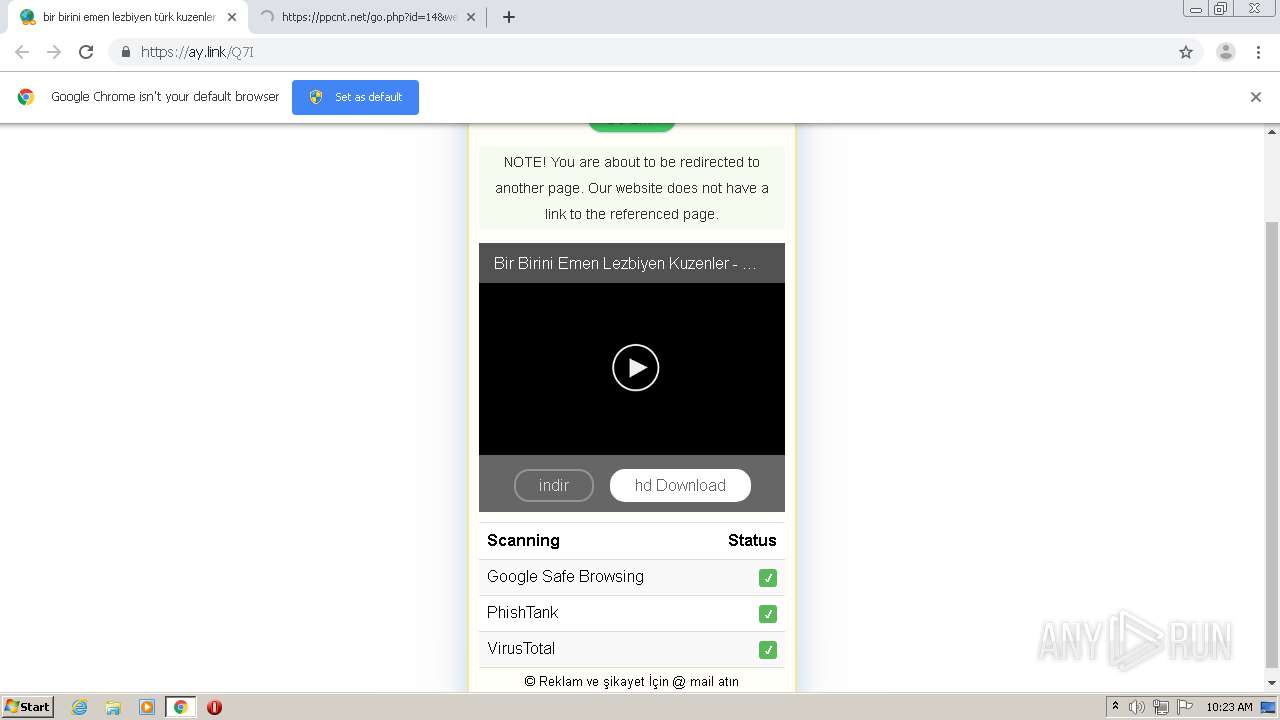
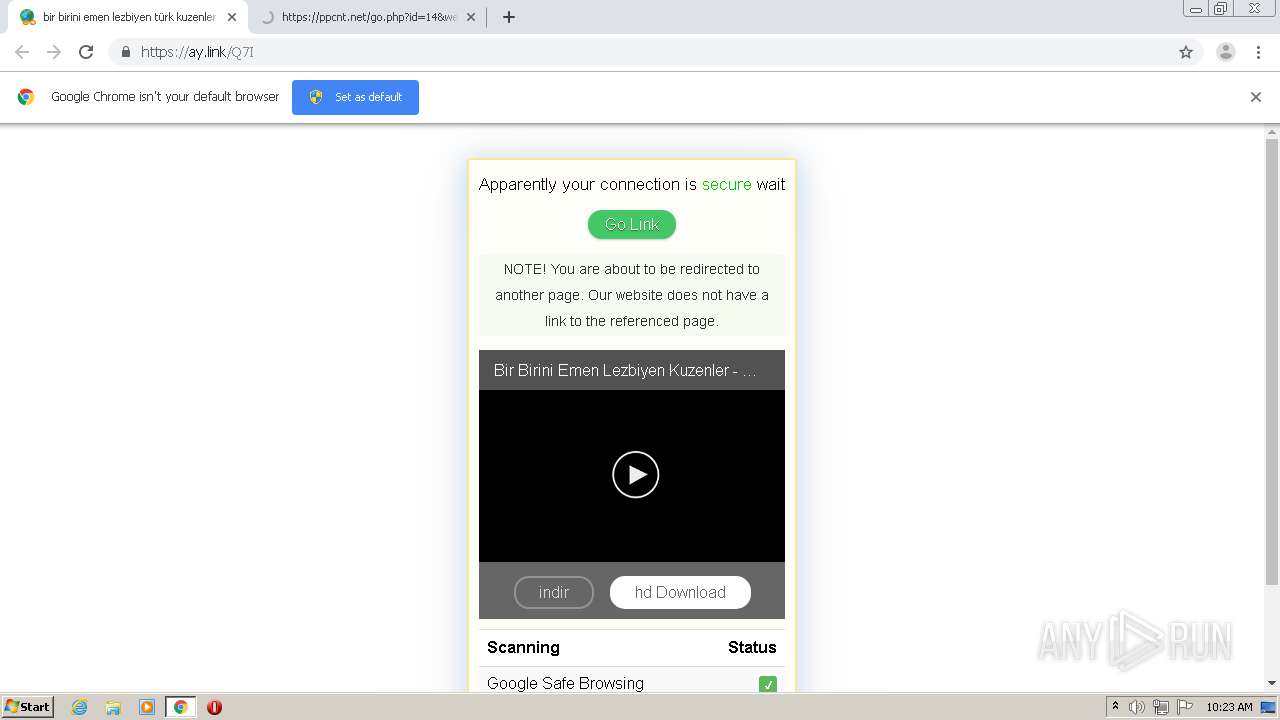
2860 | chrome.exe | GET | 200 | 172.67.175.55:80 | http://sincansaglik.com/ad-category/etimesgut-escort/ | US | html | 12.8 Kb | suspicious |
2860 | chrome.exe | GET | 200 | 104.18.44.66:80 | http://meteilan108.xyz/wp-content/uploads/2020/07/goldsbercem.gif | US | image | 139 Kb | suspicious |
2860 | chrome.exe | GET | 200 | 172.67.175.55:80 | http://cdn.sincansaglik.com/wp-includes/css/dashicons.min.css | US | text | 27.9 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
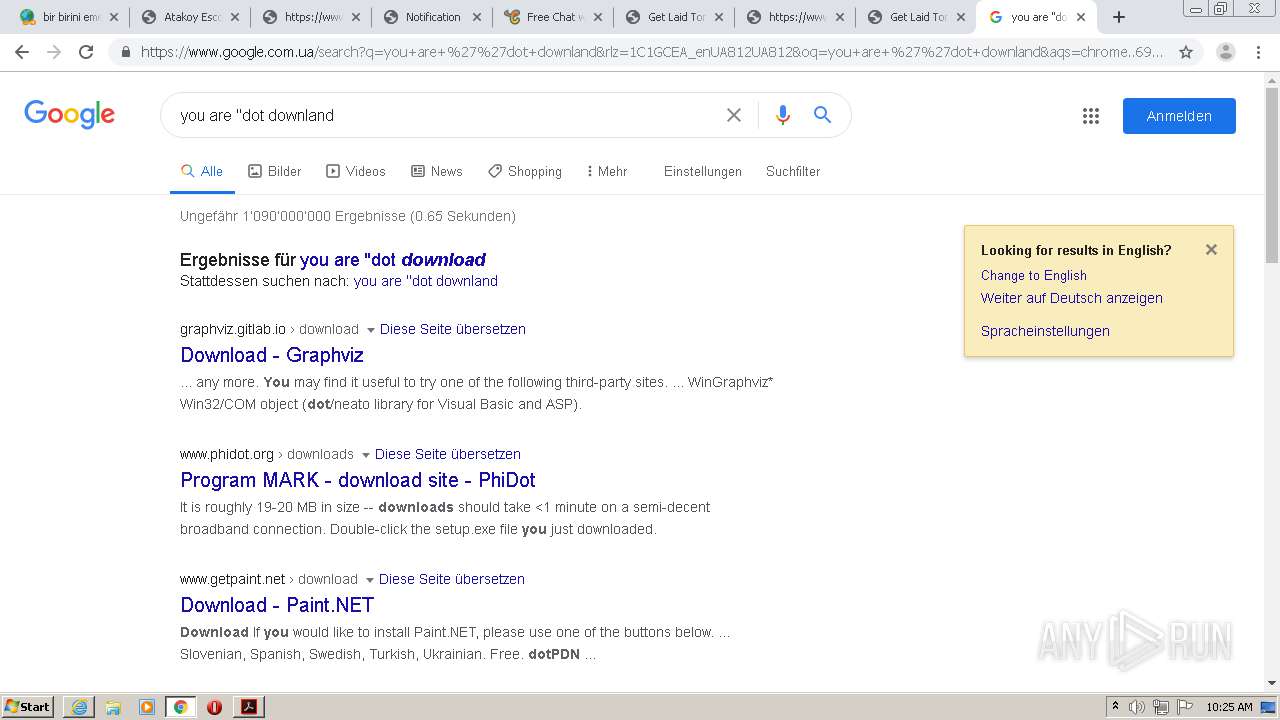
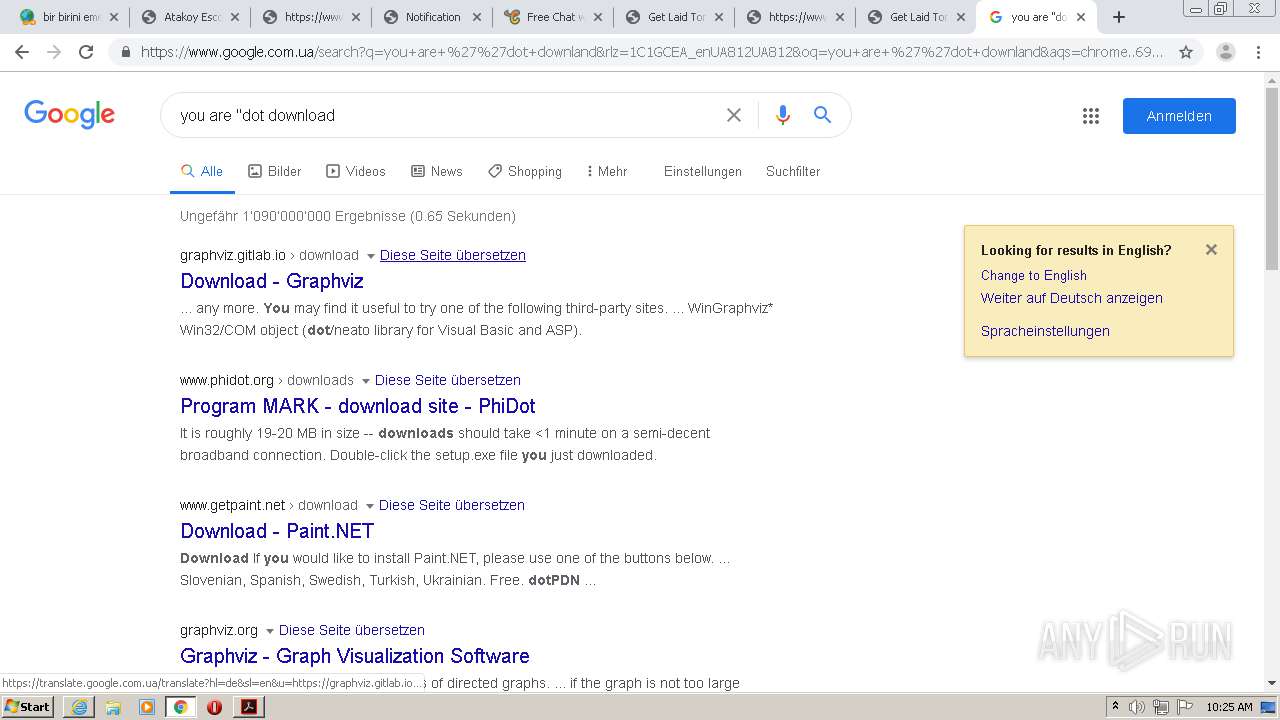
2860 | chrome.exe | 172.217.23.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2860 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 104.244.42.69:443 | t.co | Twitter Inc. | US | suspicious |
2860 | chrome.exe | 172.217.23.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
2860 | chrome.exe | 104.28.29.38:443 | cdn.adreda.com | Cloudflare Inc | US | shared |
2860 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 104.244.42.133:443 | t.co | Twitter Inc. | US | suspicious |
2860 | chrome.exe | 195.181.175.49:443 | 1109786562.rsc.cdn77.org | Datacamp Limited | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t.co |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
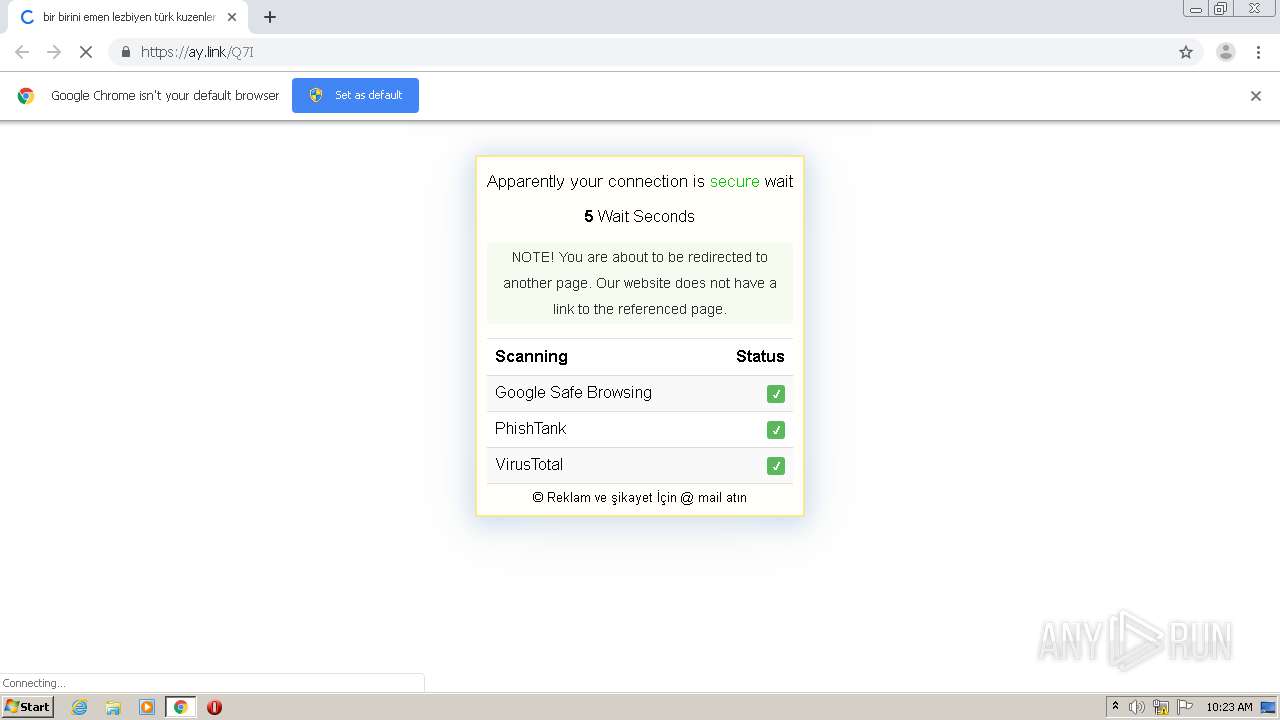
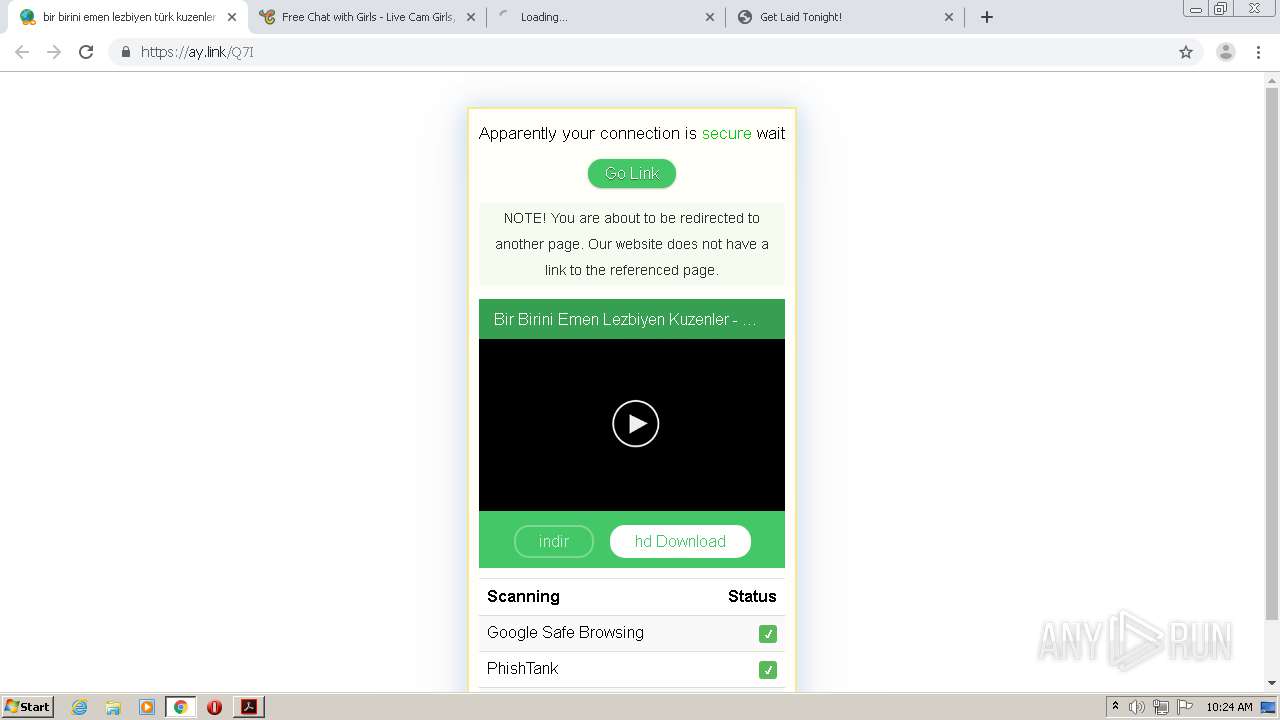
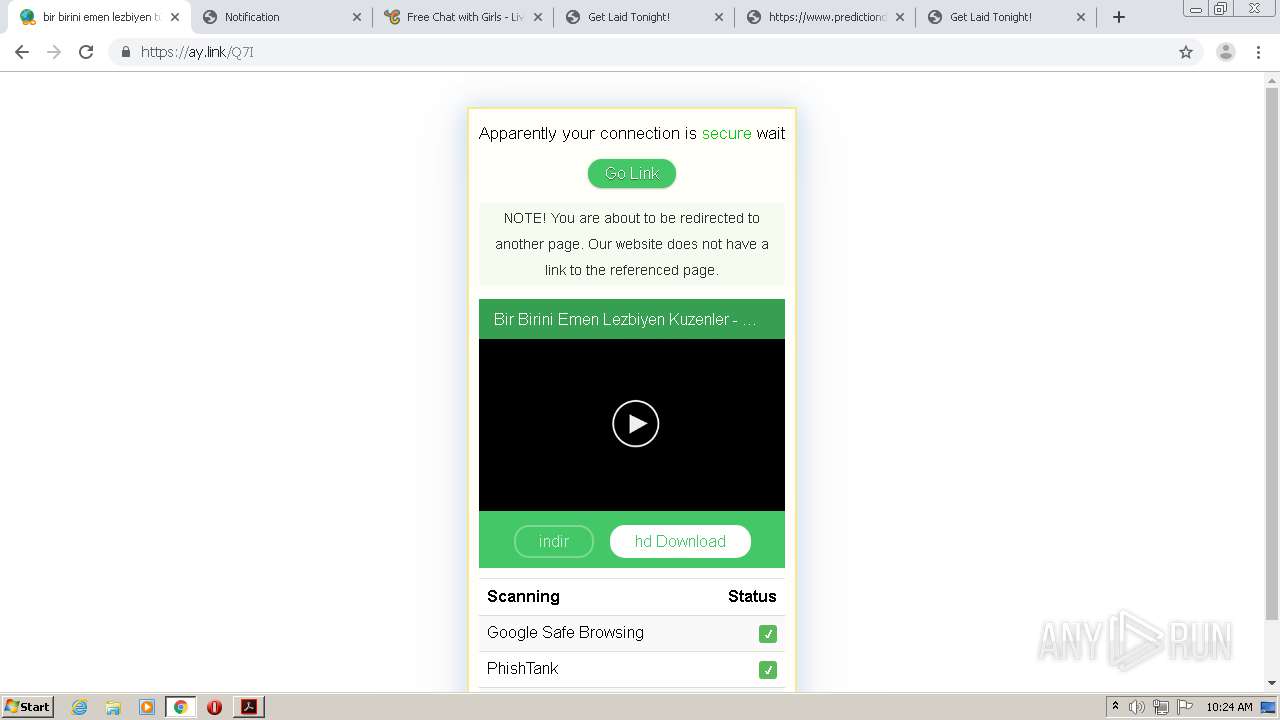
ay.link |
| suspicious |
clients2.google.com |
| whitelisted |
1109786562.rsc.cdn77.org |
| malicious |
cdn.adreda.com |
| unknown |
code.jquery.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2860 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2860 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2860 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2860 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2860 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2860 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2860 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2860 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2860 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2860 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |