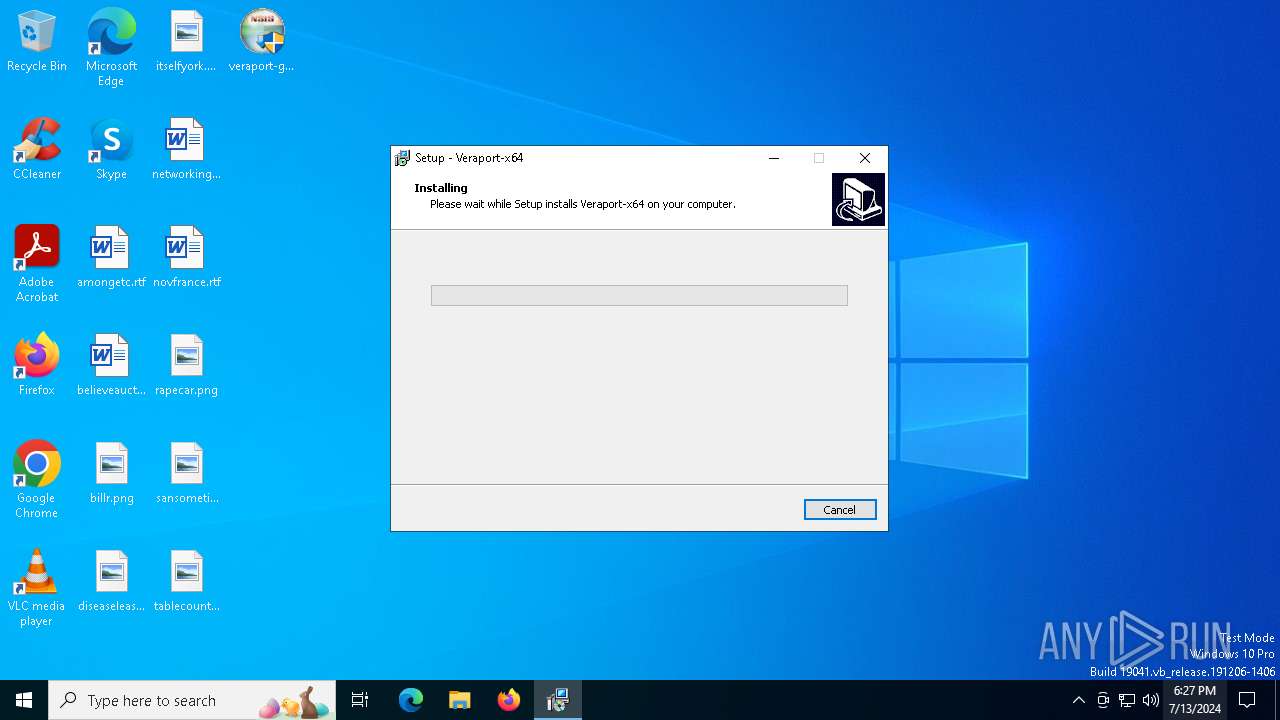
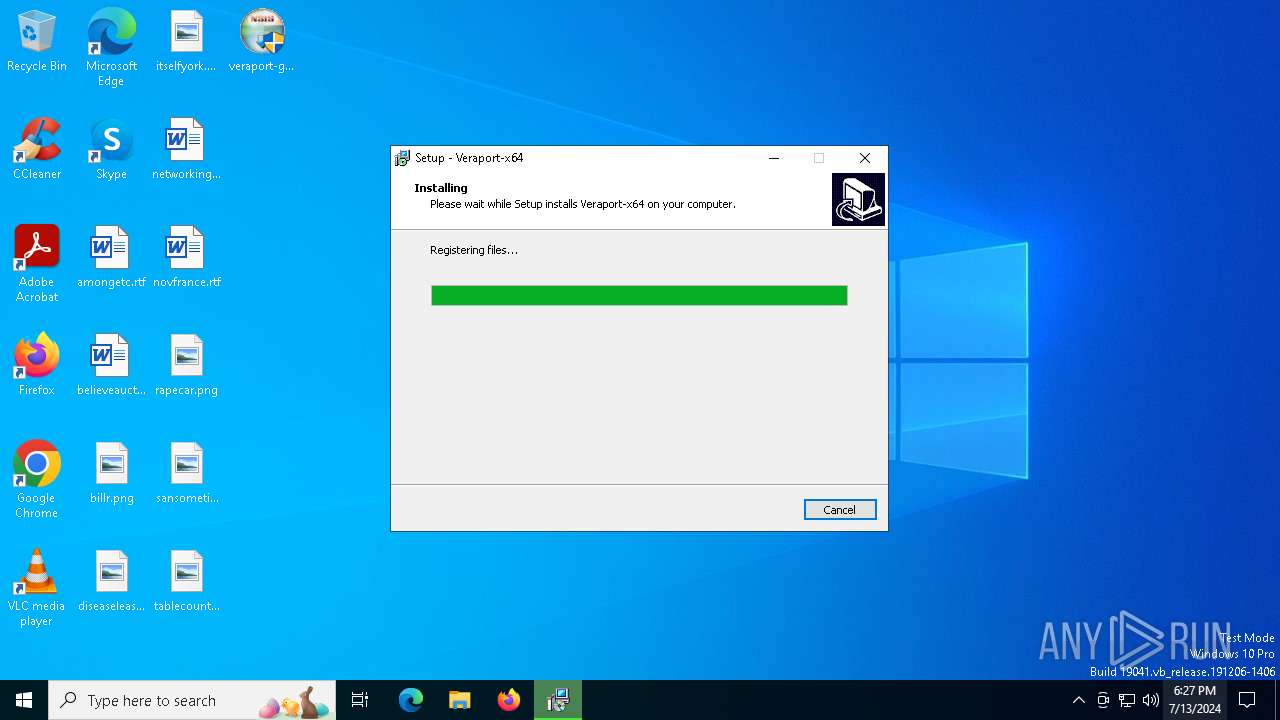
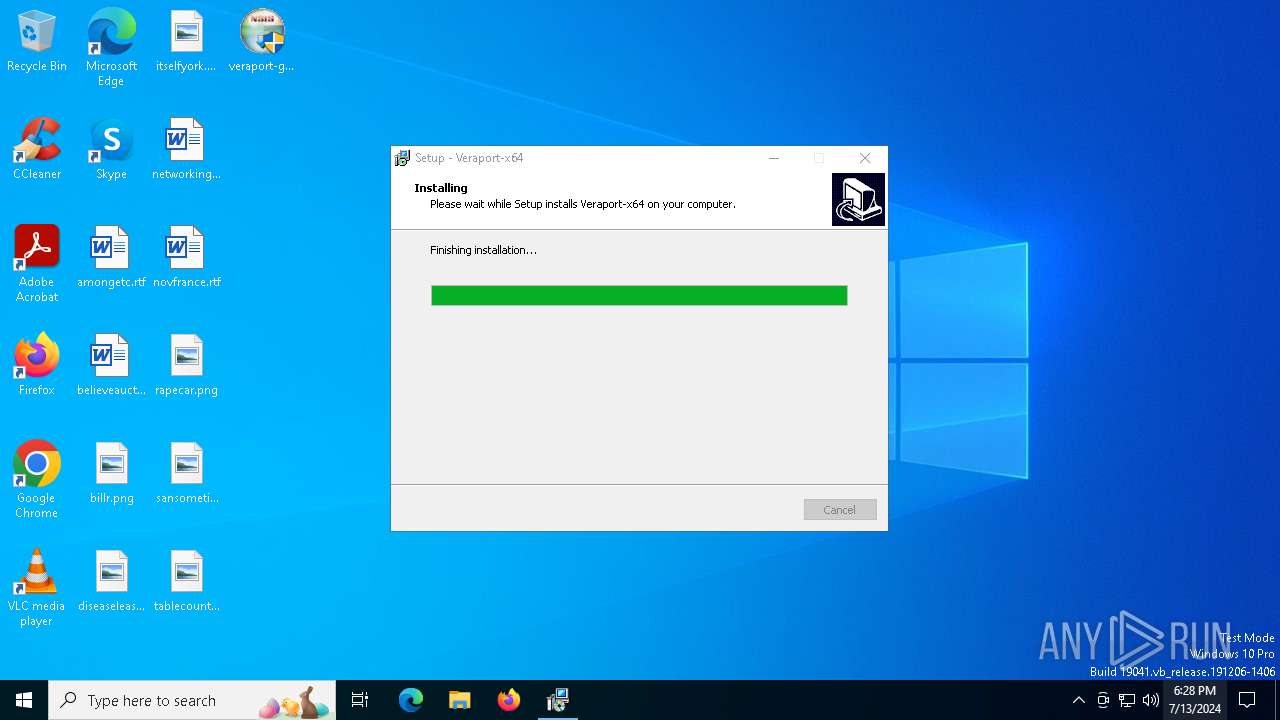
| File name: | veraport-g3s-x64-sha2.exe |
| Full analysis: | https://app.any.run/tasks/e1bc8bdf-08e8-4c60-9fe5-73b477b9f571 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2024, 18:27:25 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4C79B446929F81A9B4FD98D87339DEF5 |
| SHA1: | BCE74EC44452CAAD64631AB5CE0C5FB67415ECE4 |
| SHA256: | 816BF68BA072B6FDF2CE538DC0BB4E8EB580B0A4D46C2F51C2D35485C1BDDE9F |
| SSDEEP: | 393216:oGFSgG4IdxMXjXYjQtDE8q/wzFA5tJaw80zOiT:o+1e8jXYjV/cS5iw80tT |
MALICIOUS
Drops the executable file immediately after the start
- veraport-g3s-x64-sha2.exe (PID: 1324)
- veraport-g3-x64.exe (PID: 2120)
- wizcertutil.exe (PID: 420)
- veraport-g3-x64.tmp (PID: 2868)
- wpmsvcsetup.exe (PID: 884)
- wpmsvcsetup.tmp (PID: 5324)
Registers / Runs the DLL via REGSVR32.EXE
- veraport-g3-x64.tmp (PID: 2868)
Changes the autorun value in the registry
- veraport-g3-x64.tmp (PID: 2868)
Steals credentials from Web Browsers
- wizcertutil.exe (PID: 420)
Actions looks like stealing of personal data
- wizcertutil.exe (PID: 420)
- certutil.exe (PID: 4124)
- certutil.exe (PID: 1296)
- certutil.exe (PID: 3868)
- certutil.exe (PID: 4104)
- certutil.exe (PID: 4724)
- certutil.exe (PID: 5000)
- certutil.exe (PID: 3828)
- certutil.exe (PID: 3624)
- certutil.exe (PID: 5736)
- certutil.exe (PID: 4928)
- certutil.exe (PID: 5988)
- certutil.exe (PID: 4556)
- certutil.exe (PID: 244)
- certutil.exe (PID: 2476)
SUSPICIOUS
Starts SC.EXE for service management
- veraport-g3-x64.tmp (PID: 2868)
Reads the BIOS version
- veraport20unloader.exe (PID: 3560)
- veraport20unloader.exe (PID: 4800)
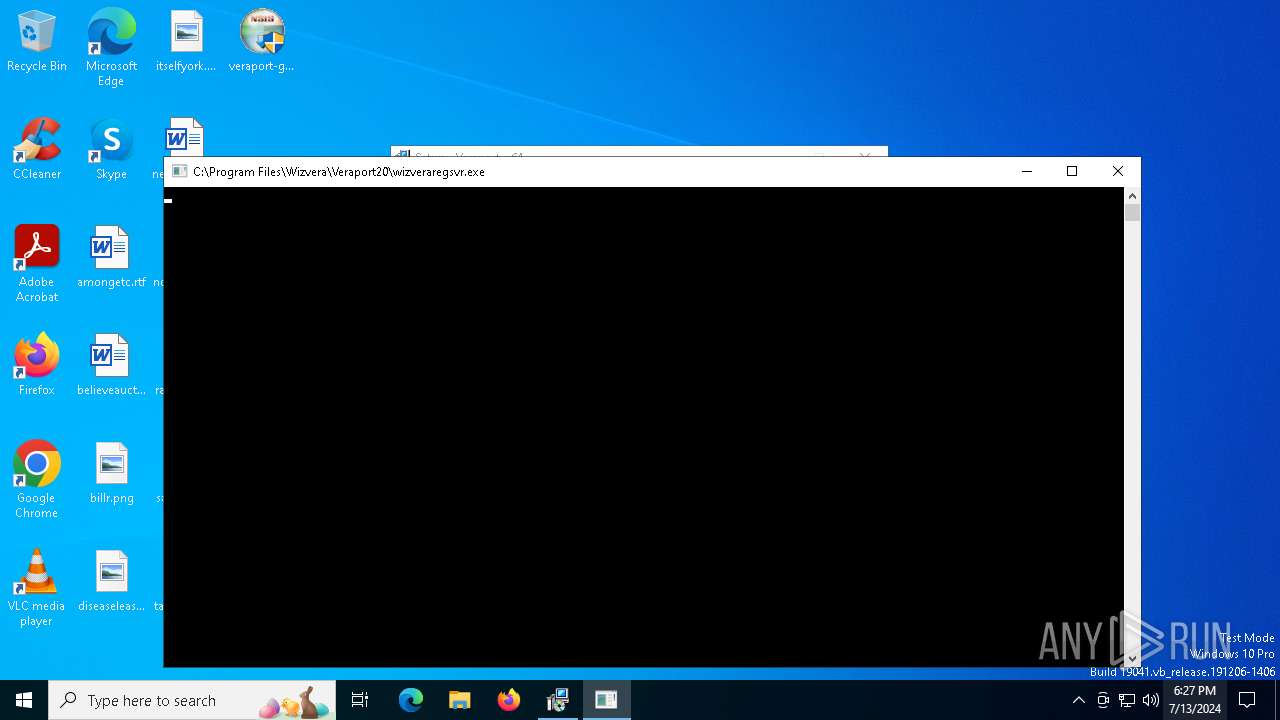
- wizveraregsvr.exe (PID: 4680)
- WizSvcUtil.exe (PID: 1832)
- wpmsvc.exe (PID: 4628)
- veraport-x64.exe (PID: 3088)
- wpmsvc.exe (PID: 4524)
Executable content was dropped or overwritten
- veraport-g3s-x64-sha2.exe (PID: 1324)
- veraport-g3-x64.exe (PID: 2120)
- veraport-g3-x64.tmp (PID: 2868)
- wpmsvcsetup.exe (PID: 884)
- wpmsvcsetup.tmp (PID: 5324)
Reads the date of Windows installation
- veraport20unloader.exe (PID: 3560)
- veraport20unloader.exe (PID: 4800)
Reads security settings of Internet Explorer
- veraport20unloader.exe (PID: 3560)
- veraport20unloader.exe (PID: 4800)
- veraport-x64.exe (PID: 3088)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3228)
- wizveraregsvr.exe (PID: 4680)
Uses TASKKILL.EXE to kill process
- veraport20unloader.exe (PID: 4800)
The process drops C-runtime libraries
- veraport-g3-x64.tmp (PID: 2868)
Adds/modifies Windows certificates
- wizcertutil.exe (PID: 420)
- wpmsvc.exe (PID: 4524)
Process drops legitimate windows executable
- veraport-g3-x64.tmp (PID: 2868)
- wpmsvcsetup.tmp (PID: 5324)
Reads the Windows owner or organization settings
- veraport-g3-x64.tmp (PID: 2868)
- wpmsvcsetup.tmp (PID: 5324)
Executes as Windows Service
- wpmsvc.exe (PID: 4524)
Checks Windows Trust Settings
- wpmsvc.exe (PID: 4524)
- veraport-x64.exe (PID: 3088)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- veraport-g3-x64.tmp (PID: 2868)
Uses NETSH.EXE to add a firewall rule or allowed programs
- veraport-g3-x64.tmp (PID: 2868)
INFO
Checks supported languages
- veraport-g3-x64.exe (PID: 2120)
- veraport-g3s-x64-sha2.exe (PID: 1324)
- veraport20unloader.exe (PID: 3560)
- veraport20unloader.exe (PID: 4800)
- wizveraregsvr.exe (PID: 4680)
- certutil.exe (PID: 1296)
- certutil.exe (PID: 4124)
- wizcertutil.exe (PID: 420)
- certutil.exe (PID: 4104)
- certutil.exe (PID: 4724)
- certutil.exe (PID: 5000)
- certutil.exe (PID: 3868)
- certutil.exe (PID: 4928)
- certutil.exe (PID: 2476)
- veraport-g3-x64.tmp (PID: 2868)
- certutil.exe (PID: 3624)
- certutil.exe (PID: 3828)
- certutil.exe (PID: 244)
- certutil.exe (PID: 5736)
- certutil.exe (PID: 5988)
- certutil.exe (PID: 4556)
- wpmsvcsetup.exe (PID: 884)
- wpmsvcsetup.tmp (PID: 5324)
- WizSvcUtil.exe (PID: 1832)
- wpmsvc.exe (PID: 4628)
- veraport-x64.exe (PID: 3088)
- wpmsvc.exe (PID: 4524)
Process checks whether UAC notifications are on
- veraport20unloader.exe (PID: 3560)
- veraport20unloader.exe (PID: 4800)
- wizveraregsvr.exe (PID: 4680)
- WizSvcUtil.exe (PID: 1832)
- wpmsvc.exe (PID: 4628)
- wpmsvc.exe (PID: 4524)
- veraport-x64.exe (PID: 3088)
Reads the computer name
- veraport20unloader.exe (PID: 3560)
- veraport-g3-x64.tmp (PID: 2868)
- veraport20unloader.exe (PID: 4800)
- wizveraregsvr.exe (PID: 4680)
- certutil.exe (PID: 1296)
- certutil.exe (PID: 4124)
- certutil.exe (PID: 3868)
- certutil.exe (PID: 4104)
- certutil.exe (PID: 4724)
- certutil.exe (PID: 5000)
- certutil.exe (PID: 3828)
- certutil.exe (PID: 2476)
- certutil.exe (PID: 4928)
- certutil.exe (PID: 244)
- certutil.exe (PID: 5736)
- certutil.exe (PID: 5988)
- certutil.exe (PID: 3624)
- certutil.exe (PID: 4556)
- wpmsvcsetup.tmp (PID: 5324)
- wpmsvc.exe (PID: 4628)
- wpmsvc.exe (PID: 4524)
- veraport-x64.exe (PID: 3088)
Create files in a temporary directory
- veraport-g3s-x64-sha2.exe (PID: 1324)
- veraport-g3-x64.exe (PID: 2120)
- veraport-g3-x64.tmp (PID: 2868)
- wpmsvcsetup.exe (PID: 884)
- wpmsvcsetup.tmp (PID: 5324)
Process checks computer location settings
- veraport20unloader.exe (PID: 3560)
- veraport20unloader.exe (PID: 4800)
Creates a software uninstall entry
- veraport-g3-x64.tmp (PID: 2868)
- wpmsvcsetup.tmp (PID: 5324)
Creates files in the program directory
- veraport-g3-x64.tmp (PID: 2868)
- wizcertutil.exe (PID: 420)
- wpmsvcsetup.tmp (PID: 5324)
Reads the machine GUID from the registry
- wizcertutil.exe (PID: 420)
- wpmsvc.exe (PID: 4524)
- veraport-x64.exe (PID: 3088)
Creates files or folders in the user directory
- certutil.exe (PID: 3868)
- certutil.exe (PID: 4104)
- certutil.exe (PID: 3828)
- certutil.exe (PID: 4928)
- certutil.exe (PID: 5736)
- certutil.exe (PID: 4556)
Reads the software policy settings
- wpmsvc.exe (PID: 4524)
- veraport-x64.exe (PID: 3088)
Themida protector has been detected
- wpmsvc.exe (PID: 4524)
- veraport-x64.exe (PID: 3088)
Checks proxy server information
- veraport-x64.exe (PID: 3088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 03:20:13+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x312a |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.8.6.7 |
| ProductVersionNumber: | 3.8.6.7 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | WIZVERA Co,. Ltd |
| FileDescription: | Veraport G3 silent wrapper x64 |
| FileVersion: | 3.8.6.7 |
| LegalCopyright: | WIZVERA Co,. Ltd |
| ProductVersion: | 3.8.6.7 |
Total processes
194
Monitored processes
70
Malicious processes
16
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 244 | "c:\users\admin\appdata\local\temp\is-b0p37.tmp\.\nss_new\certutil.exe" -L -d sql:.\ | C:\Users\admin\AppData\Local\Temp\is-B0P37.tmp\nss_new\certutil.exe | wizcertutil.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 420 | "C:\Users\admin\AppData\Local\Temp\is-B0P37.tmp\wizcertutil.exe" /force /gencert /target veraport | C:\Users\admin\AppData\Local\Temp\is-B0P37.tmp\wizcertutil.exe | veraport-g3-x64.tmp | ||||||||||||
User: admin Company: Wizvera Integrity Level: HIGH Description: Certificate Util Exit code: 0 Version: 1.2.0.1 Modules
| |||||||||||||||
| 608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "C:\WINDOWS\system32\netsh.exe" advfirewall firewall delete rule name="Wizvera-Veraport-G3(x64)" | C:\Windows\System32\netsh.exe | — | veraport-g3-x64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 884 | "C:\Users\admin\AppData\Local\Temp\is-B0P37.tmp\wpmsvcsetup.exe" /VERYSILENT | C:\Users\admin\AppData\Local\Temp\is-B0P37.tmp\wpmsvcsetup.exe | veraport-g3-x64.tmp | ||||||||||||
User: admin Company: WIZVERA Integrity Level: HIGH Description: Exit code: 0 Version: Modules
| |||||||||||||||
| 1048 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CheckNetIsolation.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | "c:\users\admin\appdata\local\temp\is-b0p37.tmp\.\nss_new\certutil.exe" -L -d .\ | C:\Users\admin\AppData\Local\Temp\is-B0P37.tmp\nss_new\certutil.exe | wizcertutil.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 255 Modules
| |||||||||||||||
Total events
21 553
Read events
21 427
Write events
96
Delete events
30
Modification events
| (PID) Process: | (3560) veraport20unloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3560) veraport20unloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3560) veraport20unloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3560) veraport20unloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4800) veraport20unloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4800) veraport20unloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4800) veraport20unloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4800) veraport20unloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2868) veraport-g3-x64.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Wizvera\Veraport20 |
| Operation: | write | Name: | Version |
Value: 3,8,6,9 | |||
| (PID) Process: | (2868) veraport-g3-x64.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Wizvera\Veraport20 |
| Operation: | write | Name: | Install |
Value: C:\Program Files\Wizvera\Veraport20 | |||
Executable files
62
Suspicious files
26
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2868 | veraport-g3-x64.tmp | C:\Program Files\Wizvera\Veraport20\unins000.exe | executable | |
MD5:34B4DB985D127B4D8115B12846163275 | SHA256:397F36BC5D09D70FF2AFDCAD887694C496CC2CFA1754D15F724A9E91E49CC555 | |||
| 1324 | veraport-g3s-x64-sha2.exe | C:\Users\admin\AppData\Local\Temp\veraport-g3-x64.exe | executable | |
MD5:A6AF6BD24D734676E7A743A89F33E8F8 | SHA256:AE591F5D7F084C56B2CF6F3E6DCBA6E23BE254E581E109BE063BD737FE03A82D | |||
| 2868 | veraport-g3-x64.tmp | C:\Program Files\Wizvera\Veraport20\is-FR2IB.tmp | executable | |
MD5:34B4DB985D127B4D8115B12846163275 | SHA256:397F36BC5D09D70FF2AFDCAD887694C496CC2CFA1754D15F724A9E91E49CC555 | |||
| 2868 | veraport-g3-x64.tmp | C:\Users\admin\AppData\Local\Temp\is-B0P37.tmp\veraport20unloader.exe | executable | |
MD5:D0F24C3902D7B2D7B1B66068B778224A | SHA256:2C3DD7C3CDE5B860BC4F1DB474DEFEA508BB94DBE3495EF372E3D525B0B12840 | |||
| 2868 | veraport-g3-x64.tmp | C:\Program Files\Wizvera\Veraport20\veraport20.dll | executable | |
MD5:B967B594C844405B0B812F138CAA0387 | SHA256:F382F0065A661338E5F08F9E5071268E7074D43FA454C84ED9D12653F290B39A | |||
| 2868 | veraport-g3-x64.tmp | C:\Program Files\Wizvera\Veraport20\is-N5IF3.tmp | executable | |
MD5:B967B594C844405B0B812F138CAA0387 | SHA256:F382F0065A661338E5F08F9E5071268E7074D43FA454C84ED9D12653F290B39A | |||
| 2868 | veraport-g3-x64.tmp | C:\Users\admin\AppData\Local\Temp\is-B0P37.tmp\_isetup\_setup64.tmp | executable | |
MD5:C8871EFD8AF2CF4D9D42D1FF8FADBF89 | SHA256:E4FC574A01B272C2D0AED0EC813F6D75212E2A15A5F5C417129DD65D69768F40 | |||
| 2868 | veraport-g3-x64.tmp | C:\Users\admin\AppData\Local\Temp\is-B0P37.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 2120 | veraport-g3-x64.exe | C:\Users\admin\AppData\Local\Temp\is-S8GRF.tmp\veraport-g3-x64.tmp | executable | |
MD5:63B15124BE653DBE589C7981DA9D397C | SHA256:61674B90891CA099D5FEE62BF063A948A80863530AB6A31E7F9E06F0E5BC7599 | |||
| 2868 | veraport-g3-x64.tmp | C:\Program Files\Wizvera\Veraport20\npveraport20.dll | executable | |
MD5:69C1B4D6A90EB292C9239AECBBF85331 | SHA256:28ADCEC0FA02CE2DEAE1B11F520547C4C790EB75182E1792B371EC19F2BDEC2B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
31
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4392 | svchost.exe | GET | 200 | 2.16.164.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2220 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1828 | RUXIMICS.exe | GET | 200 | 2.16.164.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1828 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.189.173.10:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1828 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.23.209.189:443 | www.bing.com | Akamai International B.V. | GB | unknown |
2220 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4392 | svchost.exe | 2.16.164.107:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
1828 | RUXIMICS.exe | 2.16.164.107:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
2220 | MoUsoCoreWorker.exe | 2.16.164.107:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
1828 | RUXIMICS.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |