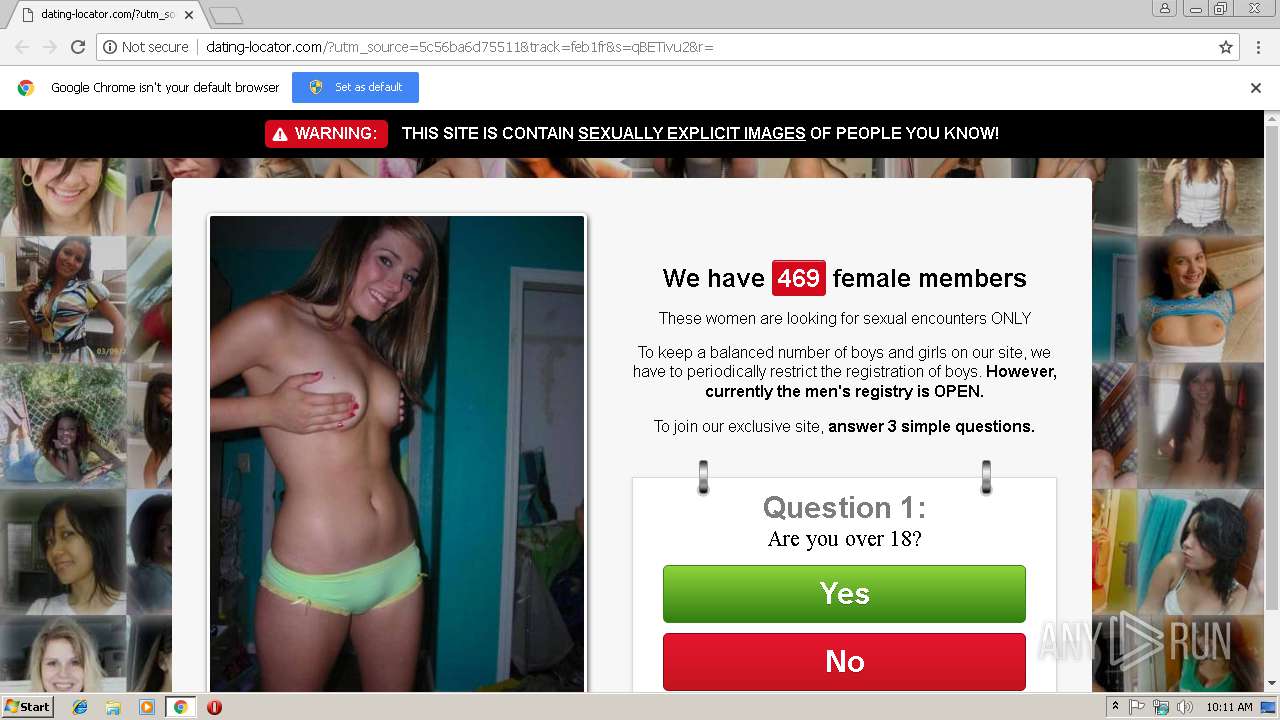
| URL: | http://cdggh.date-locator.com/?utm_source=5c56ba6d75511&track=feb1fr |
| Full analysis: | https://app.any.run/tasks/64f1a0c4-ab4e-4dd8-be07-6e82006d5a8a |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2019, 10:10:32 |
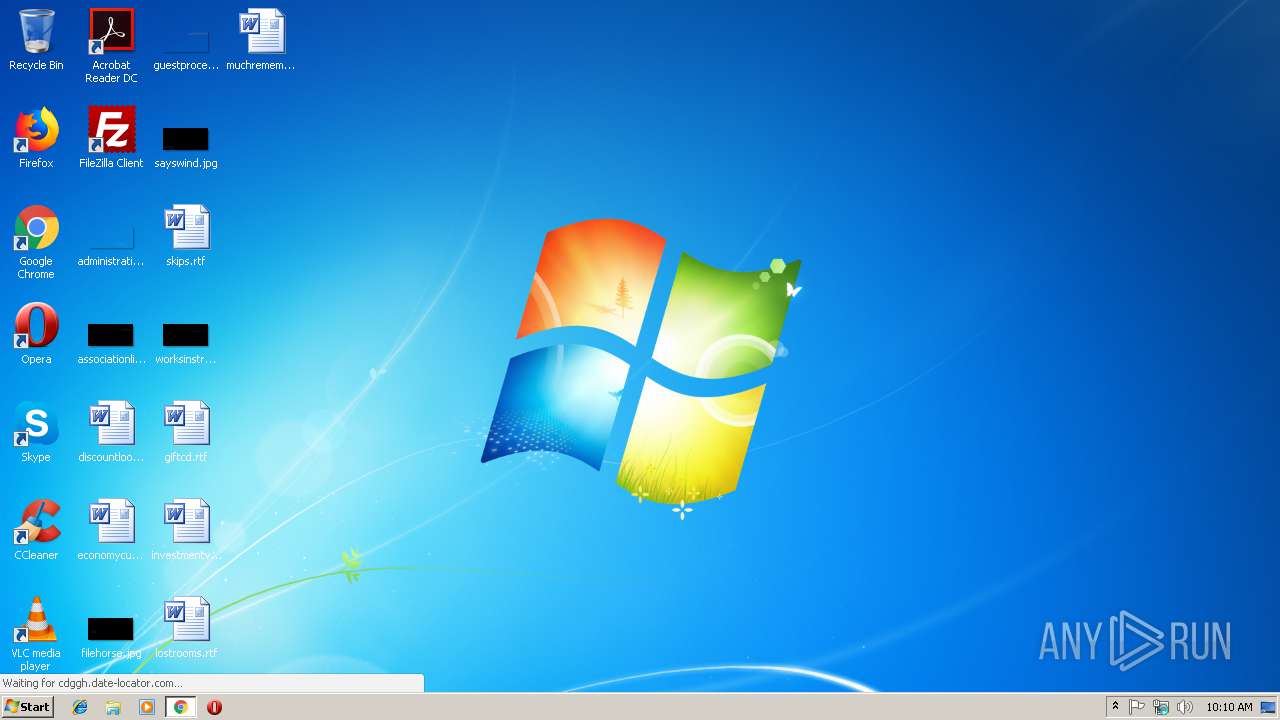
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2066ACDA9E8CF683CC580AB41DA7332B |
| SHA1: | 4AB33B15D271659CA22F868961ADD69DFFAA49DD |
| SHA256: | 815CD66F3DF334240FAC420F3C1D9DC0F0C5E13801E461F264808346AB8B5988 |
| SSDEEP: | 3:N1KdBCOLBEU2LdpCWVQm2ff:Ct52LiWVSf |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3020)
Reads settings of System Certificates
- chrome.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=936,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AA494380577D90A2CDEFA9D0D1E41C19 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=06F0A89E26151B7EC37DAD82D462C525 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=06F0A89E26151B7EC37DAD82D462C525 --renderer-client-id=4 --mojo-platform-channel-handle=1896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3024 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://cdggh.date-locator.com/?utm_source=5c56ba6d75511&track=feb1fr | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=A476A9D1919CDB71C85A5C94B7F0B3CD --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A476A9D1919CDB71C85A5C94B7F0B3CD --renderer-client-id=3 --mojo-platform-channel-handle=2052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=A90B2131359F5653122FE9C46D4C50F9 --mojo-platform-channel-handle=2312 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=936,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=F4CE9467278E7C74A1DE2CCE323CDAF2 --mojo-platform-channel-handle=3440 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x701500b0,0x701500c0,0x701500cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
490
Read events
446
Write events
41
Delete events
3
Modification events
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3020-13194353448083500 |
Value: 259 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3020-13194353448083500 |
Value: 259 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
10
Text files
49
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c6a484de-d67a-4c9d-b966-e6a0837a8f8f.tmp | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e41b6342-ea55-44ef-8806-976da6ac1b03.tmp | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF20e8ce.TMP | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF20e8ce.TMP | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e88f.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
12
DNS requests
6
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
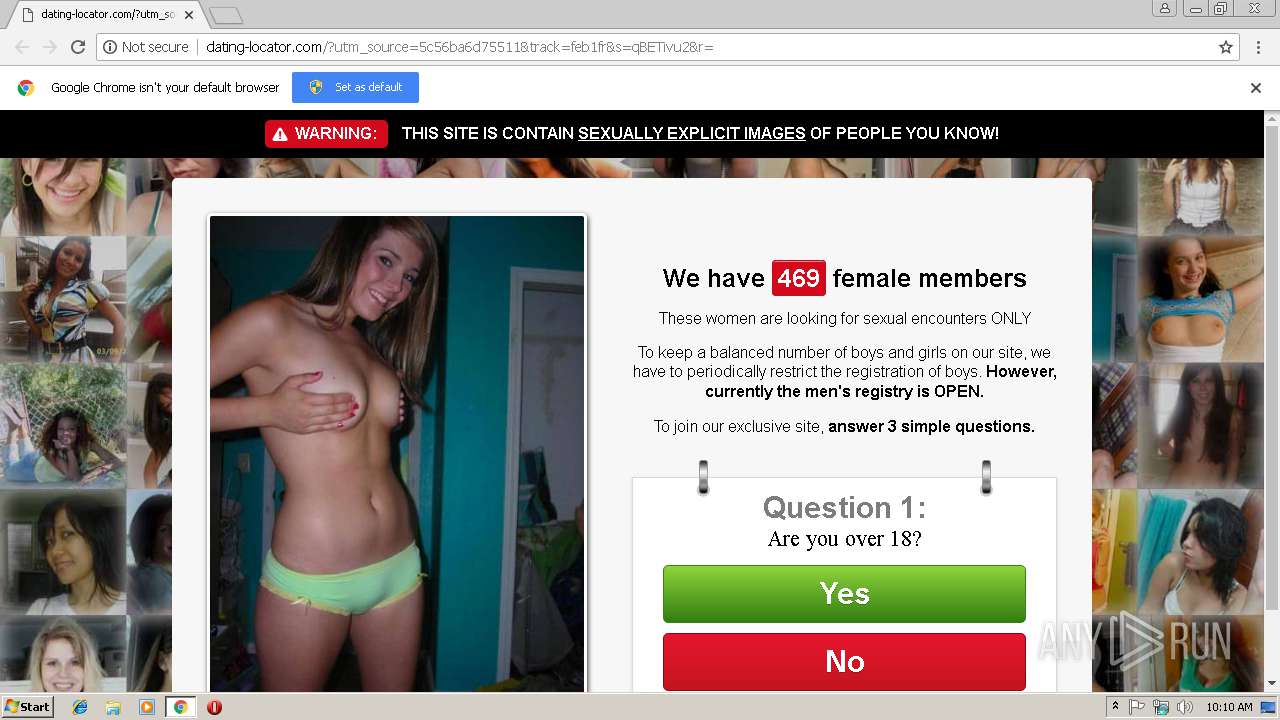
3020 | chrome.exe | GET | 200 | 31.184.255.77:80 | http://dating-locator.com/?utm_source=5c56ba6d75511&track=feb1fr&s=qBETivu2&r= | RU | html | 1.62 Kb | malicious |
3020 | chrome.exe | GET | 200 | 31.184.255.77:80 | http://dating-locator.com/bundle/24/assets/css/db049c46f3b2d509776f4b2993d2050a.css | RU | text | 1.34 Kb | malicious |
3020 | chrome.exe | GET | 200 | 95.213.251.197:80 | http://cdggh.date-locator.com/?utm_source=5c56ba6d75511&track=feb1fr | RU | html | 879 b | malicious |
3020 | chrome.exe | GET | 404 | 31.184.255.77:80 | http://dating-locator.com/favicon.ico | RU | html | 244 b | malicious |
3020 | chrome.exe | GET | 200 | 31.184.255.77:80 | http://dating-locator.com/bundle/24/assets/img/stop.png | RU | image | 11.0 Kb | malicious |
3020 | chrome.exe | GET | 200 | 95.213.251.197:80 | http://cdggh.date-locator.com/js/jquery-2.js | RU | text | 29.1 Kb | malicious |
3020 | chrome.exe | GET | 200 | 31.184.255.77:80 | http://dating-locator.com/bundle/24/assets/img/ring.png | RU | image | 709 b | malicious |
3020 | chrome.exe | GET | 200 | 31.184.255.77:80 | http://dating-locator.com/bundle/24/assets/img/body.jpg | RU | image | 156 Kb | malicious |
3020 | chrome.exe | GET | 200 | 31.184.255.77:80 | http://dating-locator.com/bundle/24/assets/img/warning_icon.png | RU | image | 272 b | malicious |
3020 | chrome.exe | GET | 200 | 31.184.255.77:80 | http://dating-locator.com/js/eclick.js | RU | text | 347 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3020 | chrome.exe | 95.213.251.197:80 | cdggh.date-locator.com | OOO Network of data-centers Selectel | RU | unknown |
3020 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3020 | chrome.exe | 216.58.207.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3020 | chrome.exe | 31.184.255.77:80 | cdggh.date-locator.com | — | RU | unknown |
3020 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdggh.date-locator.com |
| unknown |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
dating-locator.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3020 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] JS obfuscation (obfuscator.io) |
3020 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Redirection JScript Obfuscated (seen Banload) |