| File name: | Password_Filter.exe |
| Full analysis: | https://app.any.run/tasks/ab3ae626-b8d2-4d93-81d9-13d13d123efa |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 18:52:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 3231534FC76347221060A6EE13D02122 |
| SHA1: | AF4014DF57055EE1750113420BDECD6ECEB65030 |
| SHA256: | 814D2C8CA490384F58334AEAC7F0A1BD62CDFB1BA5E696C1AE147C5A357AA5E1 |
| SSDEEP: | 98304:aiMu3wXmTjJ5q9Jt4gy9ImjXE3cPtEBO7oVog1TmUHJP+3yBt9O:9Bw4J5q9D4ImjXEMGBO7oh16UHhUot9 |
MALICIOUS
Loads dropped or rewritten executable
- Password_Filter.exe (PID: 3964)
SUSPICIOUS
Executable content was dropped or overwritten
- Password_Filter.exe (PID: 3076)
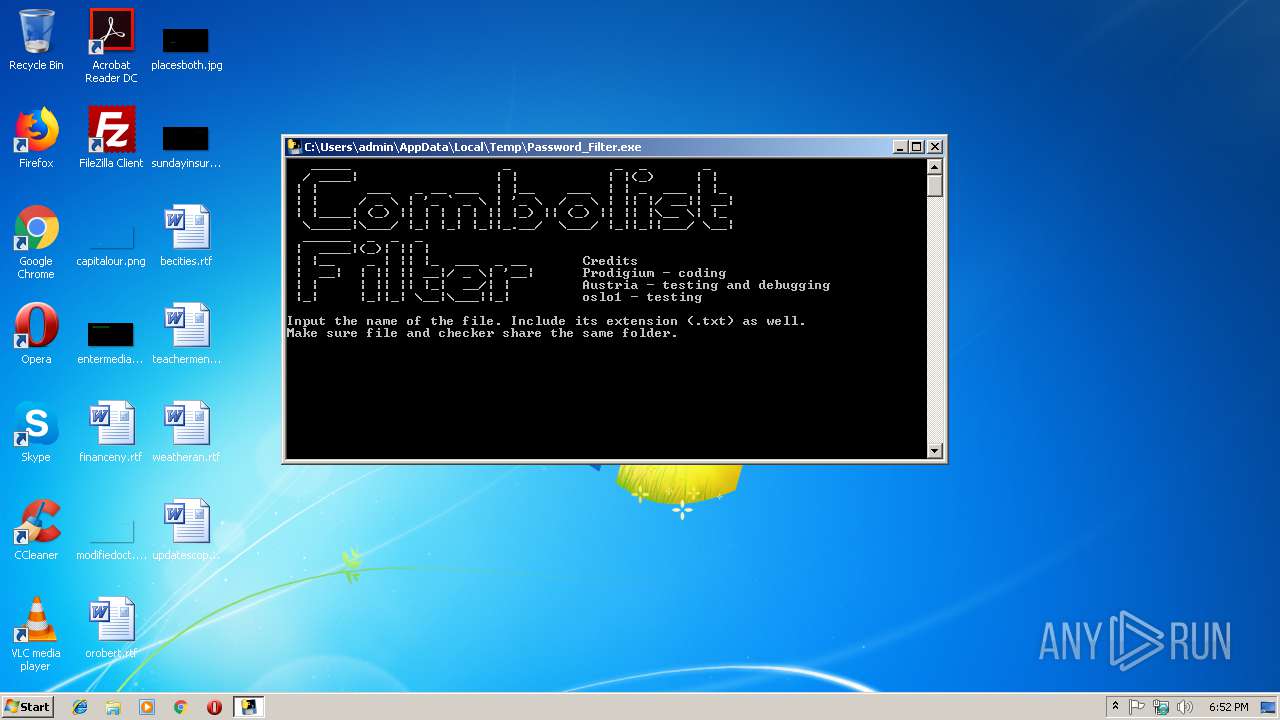
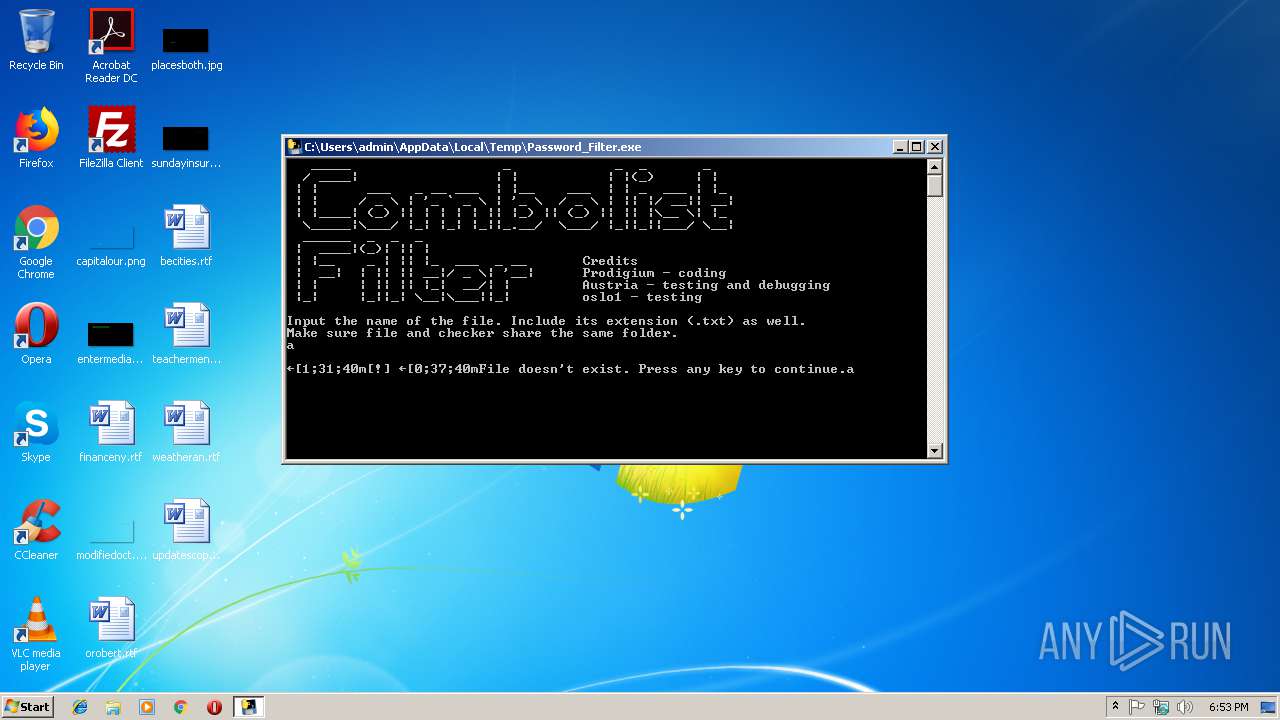
Starts CMD.EXE for commands execution
- Password_Filter.exe (PID: 3964)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 16:42:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x779a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 04-Sep-2018 14:42:13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Sep-2018 14:42:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F224 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65269 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10091 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.89006 |
.rsrc | 0x0003D000 | 0x0000EA38 | 0x0000EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.29706 |
.reloc | 0x0004C000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65088 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.58652 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.05629 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
37
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2176 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Password_Filter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2468 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Password_Filter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2948 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Password_Filter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3076 | "C:\Users\admin\AppData\Local\Temp\Password_Filter.exe" | C:\Users\admin\AppData\Local\Temp\Password_Filter.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3404 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Password_Filter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3540 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Password_Filter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3960 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Password_Filter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3964 | "C:\Users\admin\AppData\Local\Temp\Password_Filter.exe" | C:\Users\admin\AppData\Local\Temp\Password_Filter.exe | — | Password_Filter.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
36
Read events
36
Write events
0
Delete events
0
Modification events
Executable files
12
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3076 | Password_Filter.exe | C:\Users\admin\AppData\Local\Temp\_MEI30762\base_library.zip | compressed | |
MD5:— | SHA256:— | |||
| 3076 | Password_Filter.exe | C:\Users\admin\AppData\Local\Temp\_MEI30762\_lzma.pyd | executable | |
MD5:2A8FFABBEC5E95F8A0BA388265FE57F3 | SHA256:1FE26E0940EADB05BAC03BBC553FD9011FDB0C067B8082B896C1D425D17F7542 | |||
| 3076 | Password_Filter.exe | C:\Users\admin\AppData\Local\Temp\_MEI30762\_ssl.pyd | executable | |
MD5:36E29BB673D0DD63EDAC4AB90C307C4E | SHA256:9280FE6A4FD3324754548BC19CFAB60AAE8A824E7C7B7BA41592BF1587B29A4B | |||
| 3076 | Password_Filter.exe | C:\Users\admin\AppData\Local\Temp\_MEI30762\teststrings.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 3076 | Password_Filter.exe | C:\Users\admin\AppData\Local\Temp\_MEI30762\libssl-1_1.dll | executable | |
MD5:A11C90DEFA3969B20B8730450447636C | SHA256:5B24D33EF69546A929B021738018C55EE6CEA62B3DDD8D69A78DCAD4DC5C6255 | |||
| 3076 | Password_Filter.exe | C:\Users\admin\AppData\Local\Temp\_MEI30762\_hashlib.pyd | executable | |
MD5:12ABEE03CDA22A296D320789FECFDD22 | SHA256:78B2DC72E12EB23B933E9ECF0E750416FF045D1FDF270330650F1EA05C0A4A19 | |||
| 3076 | Password_Filter.exe | C:\Users\admin\AppData\Local\Temp\_MEI30762\_bz2.pyd | executable | |
MD5:8CFF8F580A47047643F1311F32A3252E | SHA256:F424B87C901D99B9C4C1CED6BD04A458816CD48ECAD771E743F0D23BC1DDDEAF | |||
| 3076 | Password_Filter.exe | C:\Users\admin\AppData\Local\Temp\_MEI30762\select.pyd | executable | |
MD5:47EE76E87AB88AD190BD8B78029A4E8D | SHA256:8B4D0B17FDC351528ABFCCB8F0E56B7D10F9565FC1ECDC098E6A961C1EEDBEEF | |||
| 3076 | Password_Filter.exe | C:\Users\admin\AppData\Local\Temp\_MEI30762\_socket.pyd | executable | |
MD5:0281B1C65F282411916FB936DF7F7ECD | SHA256:89032E74EB1454BD3BEB212A7ED0AF0EF5D1589F06C793E8E49734DE69F2625A | |||
| 3076 | Password_Filter.exe | C:\Users\admin\AppData\Local\Temp\_MEI30762\pyexpat.pyd | executable | |
MD5:120E3801A03698BD7E5149C7AA356797 | SHA256:150CD7AD573EEE27CECCF284C41355C95C01DC503DD2B05D99A0D3D12394B608 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report