| File name: | 1.exe |
| Full analysis: | https://app.any.run/tasks/ec968bcc-d65b-4f8e-9527-442df1d379dc |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
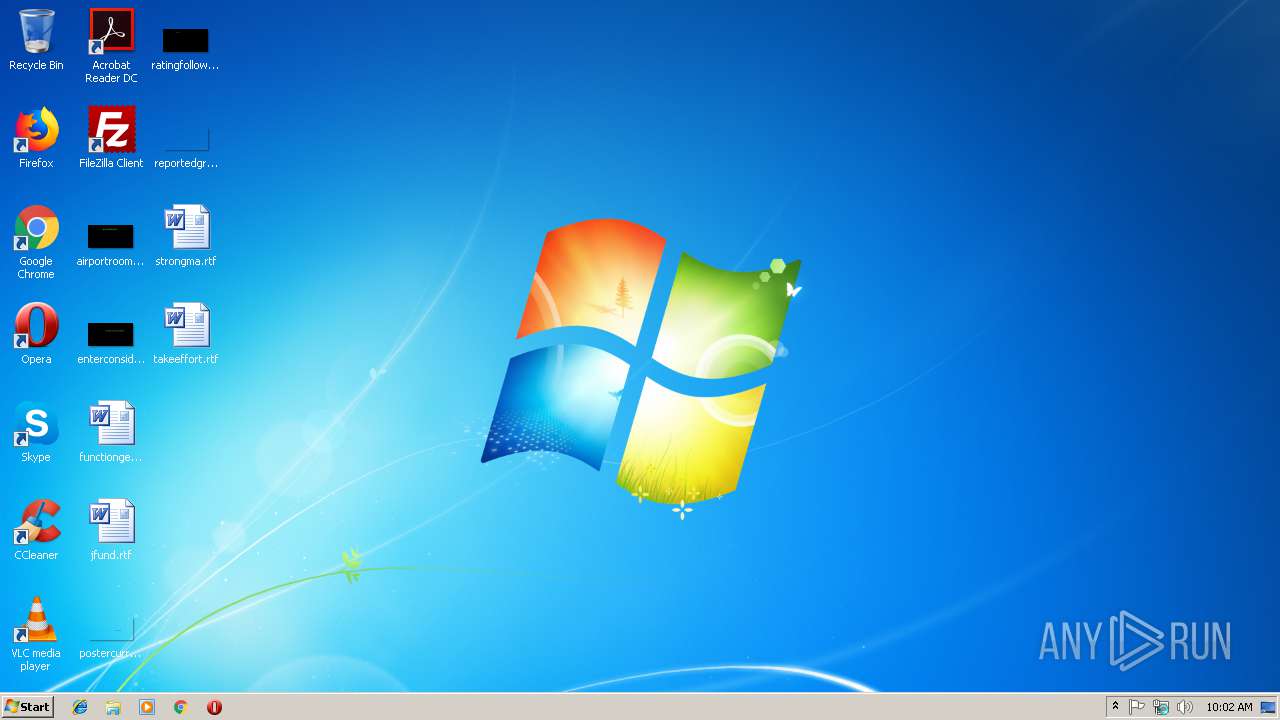
| Analysis date: | February 19, 2019, 10:02:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D6FA60094F8C7417722016E0D1E4C474 |
| SHA1: | FBDB54ED582BA35FDFA38EAEA0031DB0DC31C91B |
| SHA256: | 812F5627BBFA5311FC96D5894CEA16788C4F81D644729EBAEA432A45D65AB8FA |
| SSDEEP: | 3072:3KtH7Fxw0GQi8SHa0jNwriVcJLLmgM3U:aB3wq70pwrimxLi |
MALICIOUS
GandCrab keys found
- 1.exe (PID: 3096)
Writes file to Word startup folder
- 1.exe (PID: 3096)
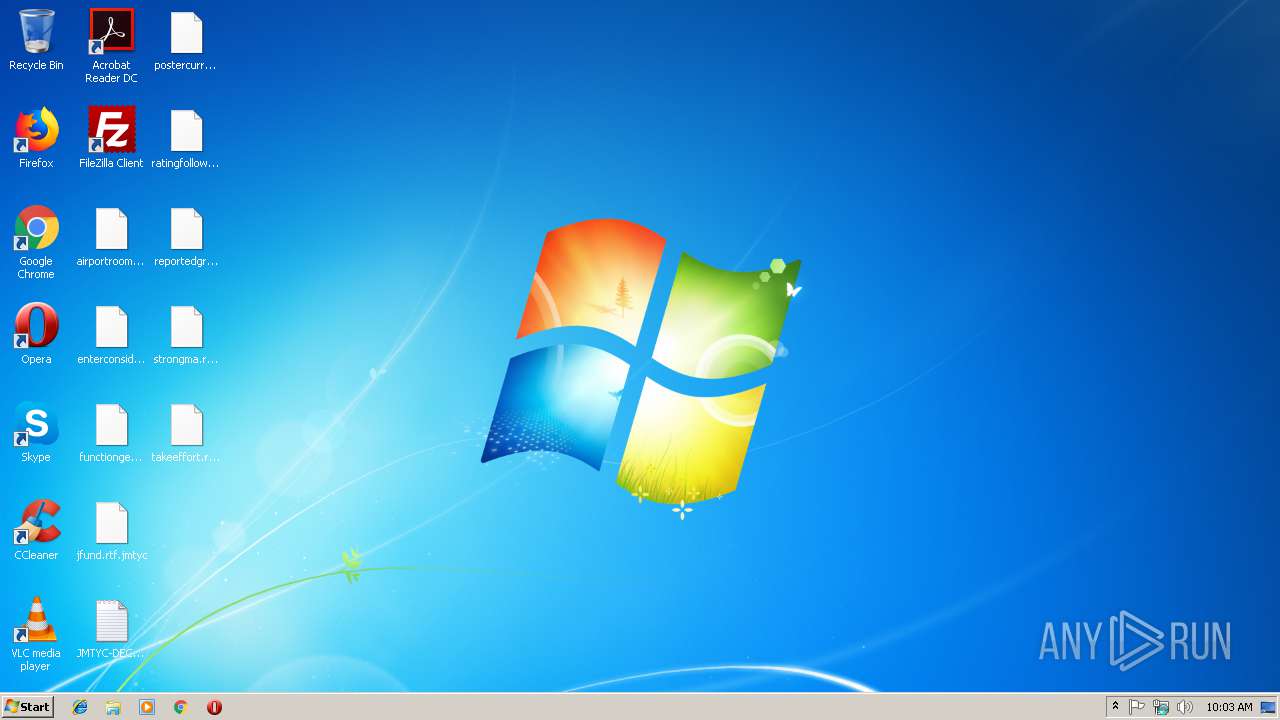
Renames files like Ransomware
- 1.exe (PID: 3096)
Deletes shadow copies
- 1.exe (PID: 3096)
Actions looks like stealing of personal data
- 1.exe (PID: 3096)
Connects to CnC server
- 1.exe (PID: 3096)
Dropped file may contain instructions of ransomware
- 1.exe (PID: 3096)
Changes settings of System certificates
- 1.exe (PID: 3096)
SUSPICIOUS
Reads the cookies of Mozilla Firefox
- 1.exe (PID: 3096)
Creates files like Ransomware instruction
- 1.exe (PID: 3096)
Creates files in the program directory
- 1.exe (PID: 3096)
Adds / modifies Windows certificates
- 1.exe (PID: 3096)
Creates files in the user directory
- 1.exe (PID: 3096)
INFO
Dropped object may contain TOR URL's
- 1.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:29 20:05:06+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 70144 |
| InitializedDataSize: | 30720 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x58ef |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jan-2019 19:05:06 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 29-Jan-2019 19:05:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00011112 | 0x00011200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61303 |
.rdata | 0x00013000 | 0x00001648 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94434 |
.data | 0x00015000 | 0x000056BC | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.67031 |
.reloc | 0x0001B000 | 0x00000628 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.59251 |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
RPCRT4.dll |
USER32.dll |
WININET.dll |
ole32.dll |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1616 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3096 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3752 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | 1.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
130
Read events
96
Write events
34
Delete events
0
Modification events
| (PID) Process: | (3096) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E006A006D007400790063000000 | |||
| (PID) Process: | (3096) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A40000525341310008000001000100514F949045EE9AAFA5F572AC75CFDA033C6AC437001AA54F8033F1AAA60DF9B0C677B79AF2630C682B0A7825C61EA0FBE38D886F10A8EB0B269BCD474AAC91B87DA1FDA9FD13BAD250A2FEF2C75ACF6AB29ED26F4B7E70DDD04036C4A634B3915AAD283FA2DB13710BB275B98F94B55D03ABE0649C8ABD09262CCE8798B10BD4D2ACCF32114422C0528DCDAC09F2A29FD3DF0B16D5273C137C5EAAEF3DF02859320CC5B45168C6EAC88A1B29FBFB09E503F61F677A34D26BC5CCB527CA6E86DA588E85CBB23B001FBDA1C60855C844E64BE772FB24A125BF21351816676A46174BB2CC693E748A1E615C0791D0AE33B8851F0BAD6D996A2787664D869FA4A8E3 | |||
| (PID) Process: | (3096) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 9404000019213073836DF5B0BAC6EFF2A4D00A1113AE2904BA71AE4F73CE4F96571B09A5DF5F7EEDA13FD5B8D3C2C211CFC0DC095438C2DED9E0B6BFB5F58E3D613E2B04A8915FB645E01EC69B9864D39FC68591E5DD9AFA959179F6AD05DA9C9D353087802CFBED0A8FEF6D1733D258E125A6157321BCD4A74AAB169EF0CA8D168F01E261A370BD55D1B18F99CD7CED63FEDF19CCBFDAE0BE04E0B3C2F7B68F3C24545EB9C12279FC83DDE39E8FF4E1129F3912C3947F865322761DC69E46279CDE2E53EDAD8DF89BAF50B1DCC3CEFD63C12A9E10DF492488F26D7F48E1ED3046CBAACFA1887994ED05DBC69D1D105A64C9CDBEB354C7B7CB0C34D7C90B17EDA504C92E30BAFE67A485027CC1C98D82187D08FADE8F6DFFBCEF3B5C1C5F5F29EEF2EFEAE4706179272A3270818949B4D59068932EF94A332C96ADCEA9B4537B72991D8DF1A409ADDD1EF66860E6136D12EDF5C14C1168815E25FEF58E44430AEA1D68431B9F9F72A502C1BD61C60ACAD63C16E5C24E7B62C49C988C9D579B7C98D307185439BDF7FF897644CFF9FF1658BFC4CE80D42A0D6BB58FAE3968CF223BC4076D718C6454B8659A2744B074A52DDC235FAD704E8C16EDB565D0CBD1E1186DB5BD05C02B0B7116E12E877C06AFC88FC1453A75E6B610443AAA4F03E3E658A382791DA87C7A70CA5BD3818CD694DD7C52C3894092BF969A47C8D4E098A31CF030716DA1C36FCFA939624BFC7F55AB68D7EEEDD8E966403D2E8A9C1517876C0E0784A43C9263B37C058C39F0C9AAC8BEB6CAC20D71652AF4E6A3D43815690B26DA42E4DF7D4811EFB67566C3EA8DAD1F546E9164D4E430BA17542DB4864EDEAF182D88A5189C8A63DC3A57E4BF3C537E616DCDA5DB83A4FC1DD5E0FCB85EA0984AC5A89B3A394FC86BA2C52D39652BBC99F0B534A265E61A2F94E3BDA71B048CB9BAC3811F2FE4BE8E5B8E1B55376A841F194073339B169235DDE33F414095FE4FCA674E31A0BF20AE22B7B4E88D6FB71154893C9D7D4966FF7D3911244DB9A82D6FEBDA66705EFC319921200E14A049E6190001EA959E98ADBF665FE8461D2919D003CA16B65CB2455C44FA2CB9BD23FE09E1FE19EC297DE23CC89BC5C506A8809AB24EB54436224388D2616F04E725B7D781D2455C0DCD922C2629ED3FEC99A59CBD1A26075E1B69AF95564F8898AA05972C3575514E4E97478F0E6657C102075EECB7BA1EE1E1227B87AA2A1C2B3310391068871844B3D741506A8A24506C37271E8C7C8AF74AADA0899350F662F8F4C182171ADC4A3B02440306313DB3E80681CCF02CAC6E35D309B1F79C1B61180FAE64EDF10C44B94DB7789029B0E9E1C8EB3EC1FBA1757D5CBA387D96CF9AE3D86CE0A13AF4CBA96ED79E029553EF9D7F3EDD173A4409252308AEFC9CF457D9F0E2E176B6D34BB9AA8B7AAD6A9804464D3584CC4E5BFF7D0960442F4B8E96D422CC22E680FCBDD069E759113E16846A023697DD8AE043A7D311D3571CA4AA5BD870D0BB3BC04A50F29B9A41E932542E4939F2C059C041888C15CB2FE5E271B07A9816243A50C30EB732210ECC35C547E9F364BAEE8E61E5E057C8D923DC1E3FB6C2BF0DDCF920A899B707624CBC00A557B777FA426BE42DC3029C4E9374650A5070D8724100E5A168ADAAE3580BA32B17117BD38D30600559ADA30574271D9FDE0C008D4AAD7738C6EC55D388A1277A0D06076FB8B031E86302D5254A5BC1ACBACD6FBF26F86DD230F16B9398177800C5D7C43869AB03DBA140B345251BAC9BFFA1BE831CFB847324B6AA995E2B60E246264AC487AD768F99A5946518833A9EAE4DBAFE38DEE148E8B52CF18A681697870F9EFD4BA812341DB04AFBD223CED0E4205C0B30C8E78E4EBC41BFEC88603F9CCA9938C43D998A617778B96AA71CCBB5E13683A49018D678A9C2C3BDCC18DD29A4B01A8E069EE0F5BE0738C8629D8E18B184F00FAFA2D65EF4270AA1AEF67F4DACFCB47EB27A94907771FAAA2AE1F22AF28453CD426F1D21900D24140E040C871C2E791C46409BAE756ABC6E1CA07EC7DD9F01C0B8CAAAEEF5C676093936168707781D2267ACE127A68EDCC5107734C5243690205992E67708B32F1469943F24BEF4412A0C99E03D46B7A532F908F59F2FDE32D2FD3CB04099B52CEE336F353664B1ACD83BB8DC3A7A1800C93DEA416F7F162314A92121C6E814F6C14249FC8A68224FC0EAA4141D41FDFF97E9AACE099F0F703C140E7BC47421C856AF462BFFF62285EF4AB06EA90425701AB241B314219F122896157C1F30C608CCD6EA95624AD0B9BDB44853B7F4570B28C33BD999363A3591BECD6A65B290E1BBB37F28983ECA8E2E112A73E6BFB45AED50F0A78F3A8FBAC083 | |||
| (PID) Process: | (3096) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3096) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3096) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\1_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3096) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\1_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3096) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\1_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3096) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\1_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3096) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\1_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
431
Text files
319
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | 1.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 3096 | 1.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.jmtyc | — | |
MD5:— | SHA256:— | |||
| 3096 | 1.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 3096 | 1.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3096 | 1.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3096 | 1.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3096 | 1.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3096 | 1.exe | C:\JMTYC-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3096 | 1.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3096 | 1.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\JMTYC-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3096 | 1.exe | GET | 301 | 185.52.2.154:80 | http://www.kakaocorp.link/ | NL | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3096 | 1.exe | 185.52.2.154:80 | www.kakaocorp.link | RouteLabel V.O.F. | NL | suspicious |
3096 | 1.exe | 185.52.2.154:443 | www.kakaocorp.link | RouteLabel V.O.F. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3096 | 1.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
3096 | 1.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
3096 | 1.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab v.5 SSL Connection |
2 ETPRO signatures available at the full report