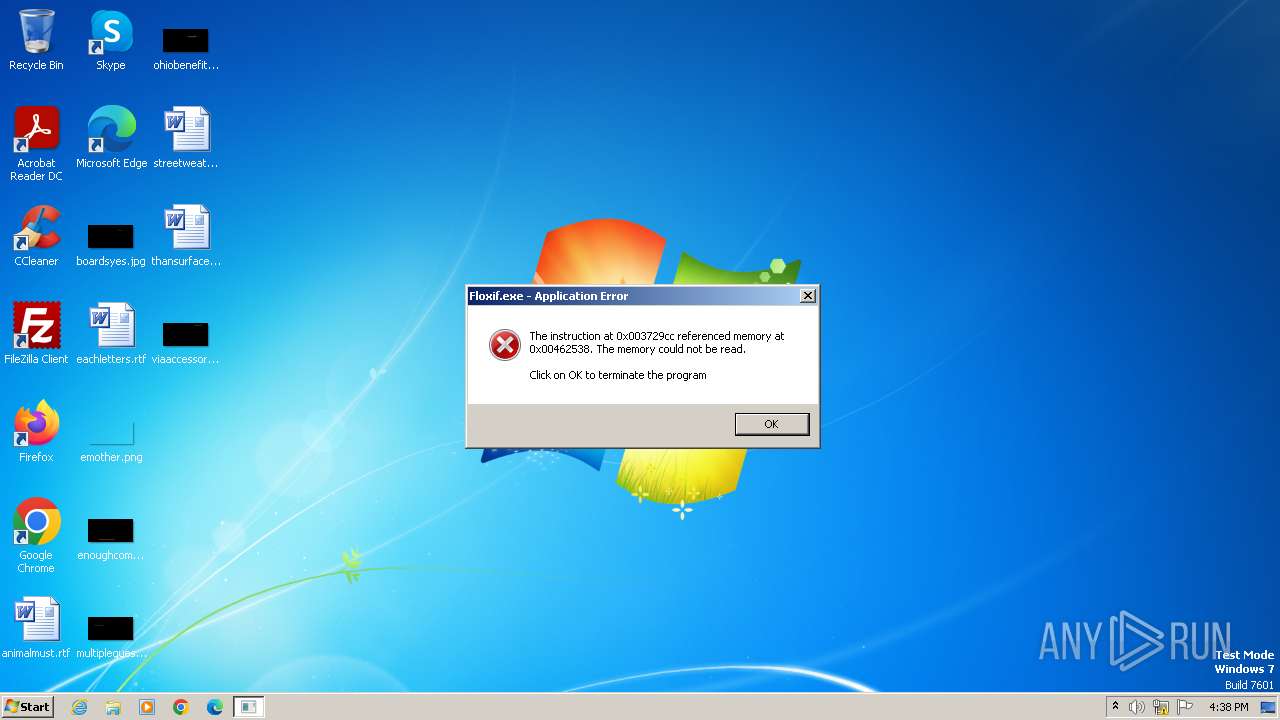
| File name: | Floxif.exe |
| Full analysis: | https://app.any.run/tasks/a61cf066-74e2-4815-a2ba-385cb6367787 |
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2025, 16:38:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 00ADD4A97311B2B8B6264674335CAAB6 |
| SHA1: | 3688DE985909CC9F9FA6E0A4F2E43D986FE6D0EC |
| SHA256: | 812AF0EC9E1DFD8F48B47FD148BAFE6EECB42D0A304BC0E4539750DD23820A7F |
| SSDEEP: | 12288:l86GkvJFajbhjTpHjq0dfpT1Oc02XEfGdnGwVUNUnEnAE3F:l8lT9PdpwO0fkGwVUSnEnAoF |
MALICIOUS
Executing a file with an untrusted certificate
- Floxif.exe (PID: 1332)
SUSPICIOUS
Executable content was dropped or overwritten
- Floxif.exe (PID: 1332)
Process drops legitimate windows executable
- Floxif.exe (PID: 1332)
Reads the Internet Settings
- Floxif.exe (PID: 1332)
Reads security settings of Internet Explorer
- Floxif.exe (PID: 1332)
INFO
The sample compiled with chinese language support
- Floxif.exe (PID: 1332)
Checks supported languages
- Floxif.exe (PID: 1332)
- wmpnscfg.exe (PID: 448)
The sample compiled with english language support
- Floxif.exe (PID: 1332)
Failed to create an executable file in Windows directory
- Floxif.exe (PID: 1332)
Reads the computer name
- Floxif.exe (PID: 1332)
- wmpnscfg.exe (PID: 448)
UPX packer has been detected
- Floxif.exe (PID: 1332)
Create files in a temporary directory
- Floxif.exe (PID: 1332)
Checks proxy server information
- Floxif.exe (PID: 1332)
Reads the machine GUID from the registry
- Floxif.exe (PID: 1332)
Manual execution by a user
- wmpnscfg.exe (PID: 448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:07:09 05:33:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 334336 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3ad73 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.7.0.329 |
| ProductVersionNumber: | 6.7.0.329 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Pre-release, Private build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | Sogou.com Inc. |
| FileDescription: | 搜狗下载器 |
| FileVersion: | 6.7.0.0329 |
| InternalName: | SogouPY |
| LegalCopyright: | © 2013 Sogou.com Inc. All rights reserved. |
| OriginalFileName: | SGDownload.exe |
| ProductName: | 搜狗下载器 |
| ProductVersion: | 6.7.0.0329 |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1108 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Temp\Floxif.exe" | C:\Users\admin\AppData\Local\Temp\Floxif.exe | explorer.exe | ||||||||||||
User: admin Company: Sogou.com Inc. Integrity Level: MEDIUM Description: 搜狗下载器 Exit code: 3221225477 Version: 6.7.0.0329 Modules
| |||||||||||||||
Total events
434
Read events
408
Write events
20
Delete events
6
Modification events
| (PID) Process: | (1332) Floxif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
| (PID) Process: | (1332) Floxif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionTime |
Value: 38B143ECD970DB01 | |||
| (PID) Process: | (1332) Floxif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecision |
Value: 0 | |||
| (PID) Process: | (1332) Floxif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadNetworkName |
Value: Network 3 | |||
| (PID) Process: | (1332) Floxif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | delete value | Name: | WpadDetectedUrl |
Value: | |||
| (PID) Process: | (1332) Floxif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\52-54-00-36-3e-ff |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
| (PID) Process: | (1332) Floxif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\52-54-00-36-3e-ff |
| Operation: | write | Name: | WpadDecisionTime |
Value: 38B143ECD970DB01 | |||
| (PID) Process: | (1332) Floxif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\52-54-00-36-3e-ff |
| Operation: | write | Name: | WpadDecision |
Value: 0 | |||
| (PID) Process: | (1332) Floxif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\52-54-00-36-3e-ff |
| Operation: | delete value | Name: | WpadDetectedUrl |
Value: | |||
| (PID) Process: | (1332) Floxif.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1332 | Floxif.exe | C:\Users\admin\AppData\Local\Temp\conres.dll | executable | |
MD5:CCF7E487353602C57E2E743D047ACA36 | SHA256:EAF76E5F1A438478ECF7B678744DA34E9D9E5038B128F0C595672EE1DBBFD914 | |||
| 1332 | Floxif.exe | C:\Users\admin\AppData\Local\Temp\conres.dll.000 | text | |
MD5:BD8E44AD8A3AFA94FE2C0150D6C0AEEC | SHA256:288E0E4D32DB79AA610ED2A688ACDA5D38D851372A0BEB0D659151FFBFFECDB5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1332 | Floxif.exe | GET | 404 | 49.13.77.253:80 | http://www.zxslb.com/logo.gif | unknown | — | — | unknown |
1332 | Floxif.exe | GET | 404 | 96.126.123.244:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
1332 | Floxif.exe | GET | 404 | 49.13.77.253:80 | http://www.zxslb.com/logo.gif | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1332 | Floxif.exe | 49.13.77.253:80 | www.zxslb.com | Hetzner Online GmbH | DE | unknown |
1332 | Floxif.exe | 96.126.123.244:80 | www.aieov.com | Linode, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.zxslb.com |
| unknown |
www.aieov.com |
| malicious |