| File name: | main.exe |
| Full analysis: | https://app.any.run/tasks/7dd9a29e-12c2-4bb1-8476-6225b4d3e266 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 16:29:05 |
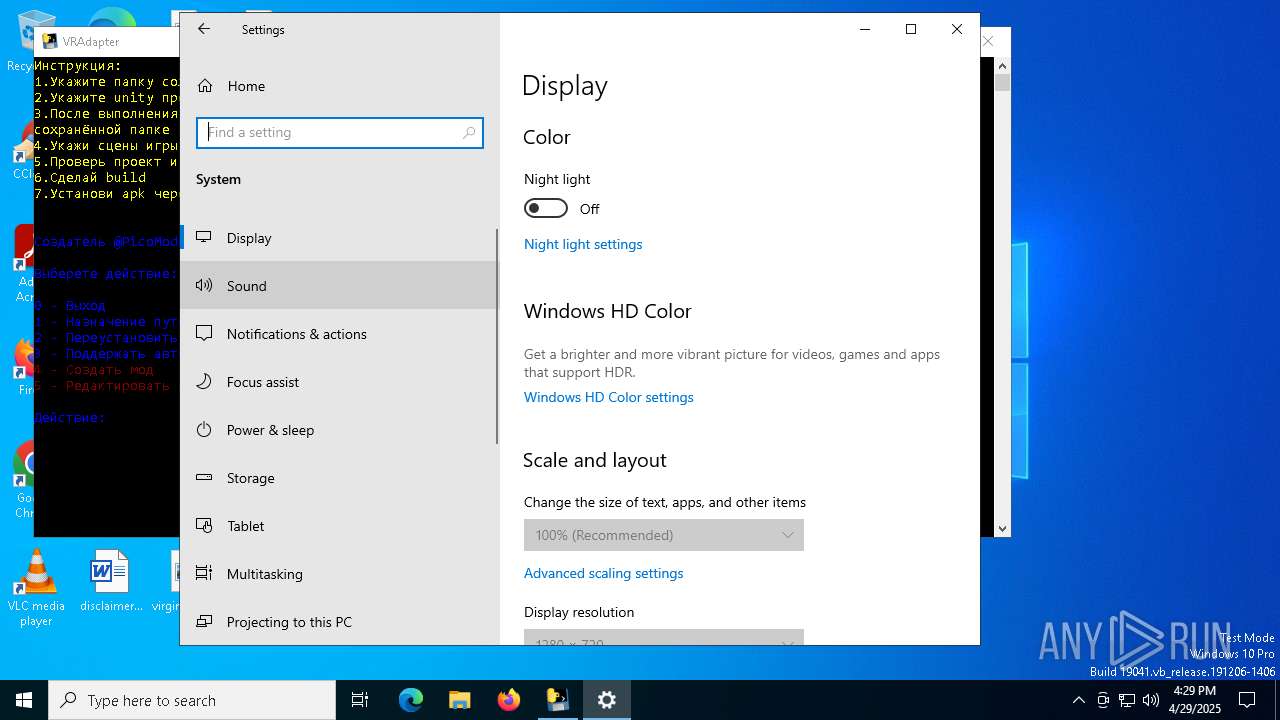
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | E3D7507120E70CA226518213E268C9E9 |
| SHA1: | 112AB89FBE73E387AEE79490D606F053D7459E8C |
| SHA256: | 812A5D2D7B187E4EA0E5AC85CE6EF7775437D7C8A21C777C7EF2952EF960470E |
| SSDEEP: | 98304:Zxb2n6WhZwlB4N+wcTAScUCYD4tHfktEzafhOsE+XZ0cGOxKbIeoH2vE/7UJDZ2f:RrFTyYIwnGpG6IR |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- main.exe (PID: 4880)
Process drops python dynamic module
- main.exe (PID: 4880)
Process drops legitimate windows executable
- main.exe (PID: 4880)
Executable content was dropped or overwritten
- main.exe (PID: 4880)
Application launched itself
- main.exe (PID: 4880)
Loads Python modules
- main.exe (PID: 7192)
Starts CMD.EXE for commands execution
- main.exe (PID: 7192)
INFO
Checks supported languages
- main.exe (PID: 4880)
- main.exe (PID: 7192)
Reads the computer name
- main.exe (PID: 4880)
Create files in a temporary directory
- main.exe (PID: 4880)
The sample compiled with english language support
- main.exe (PID: 4880)
PyInstaller has been detected (YARA)
- main.exe (PID: 4880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:22 12:19:52+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 178688 |
| InitializedDataSize: | 153600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc380 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
139
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4880 | "C:\Users\admin\AppData\Local\Temp\main.exe" | C:\Users\admin\AppData\Local\Temp\main.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7192 | "C:\Users\admin\AppData\Local\Temp\main.exe" | C:\Users\admin\AppData\Local\Temp\main.exe | — | main.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
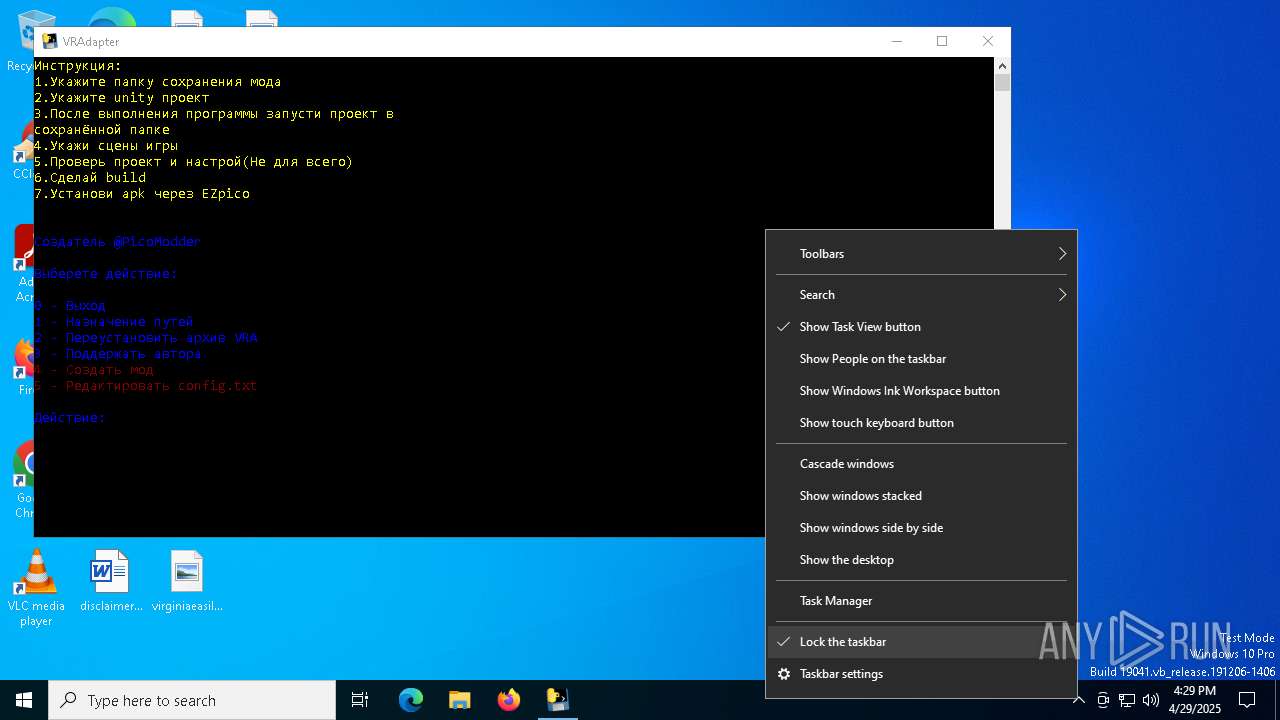
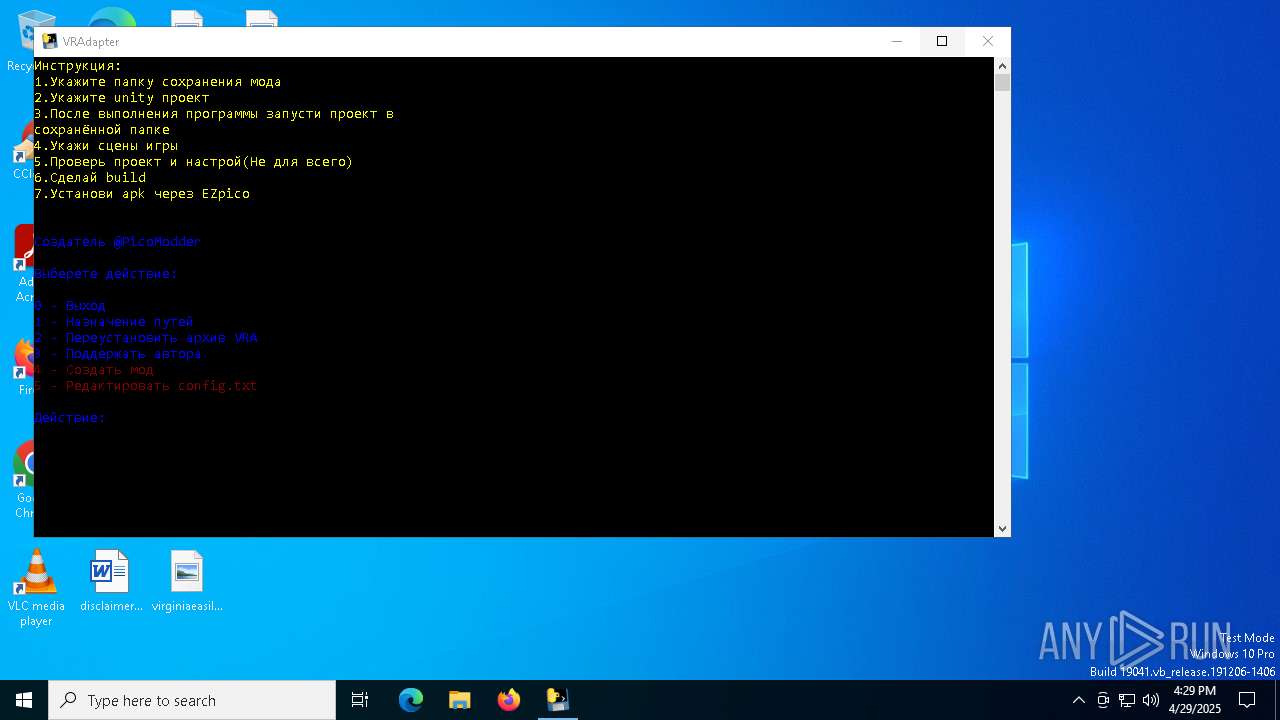
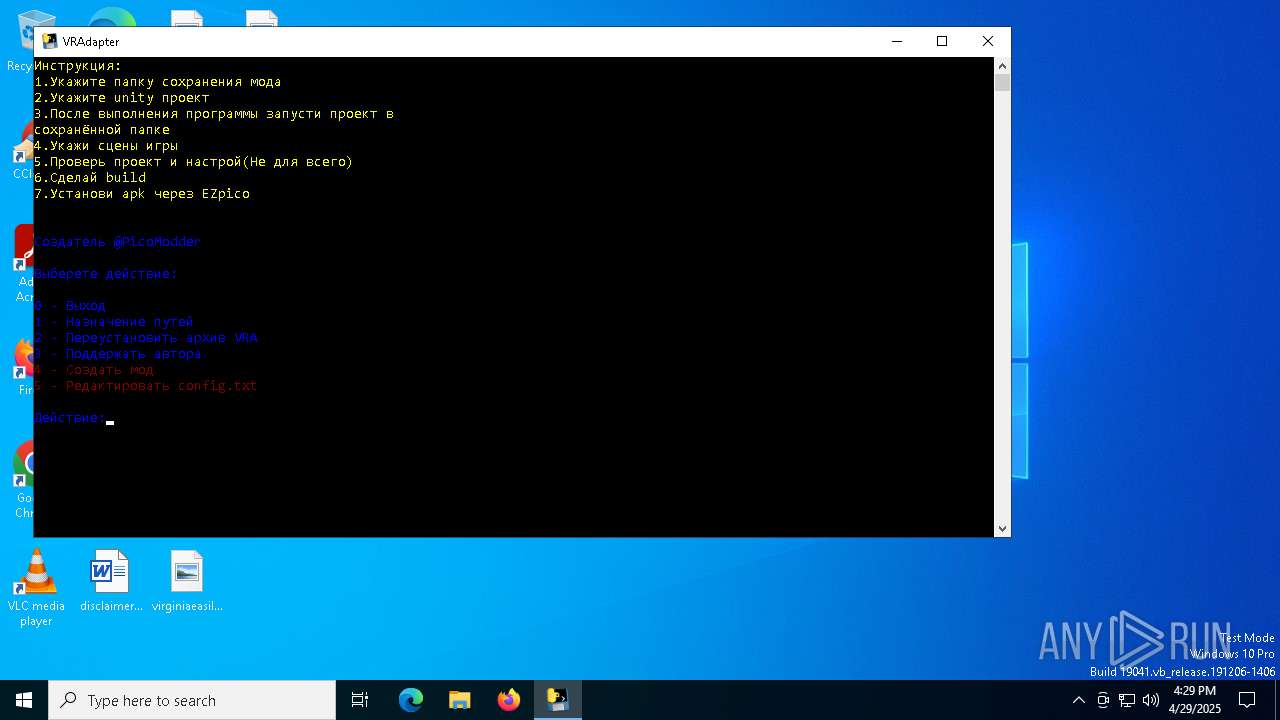
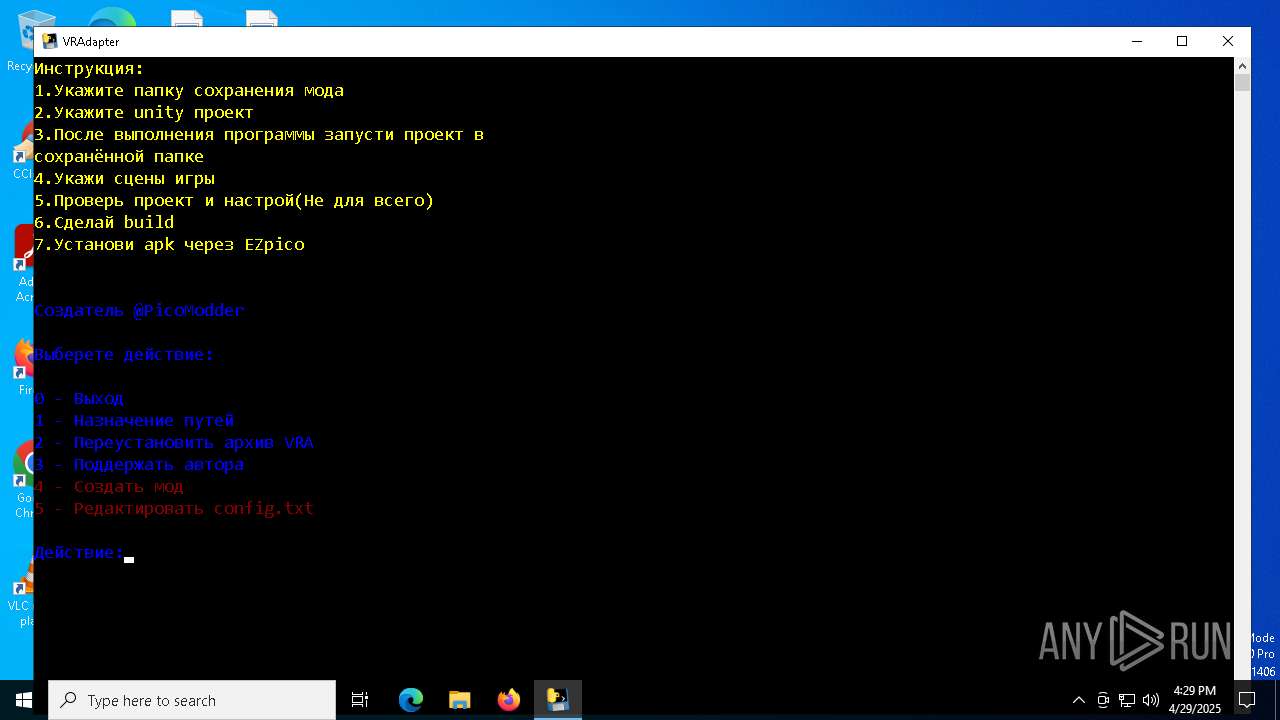
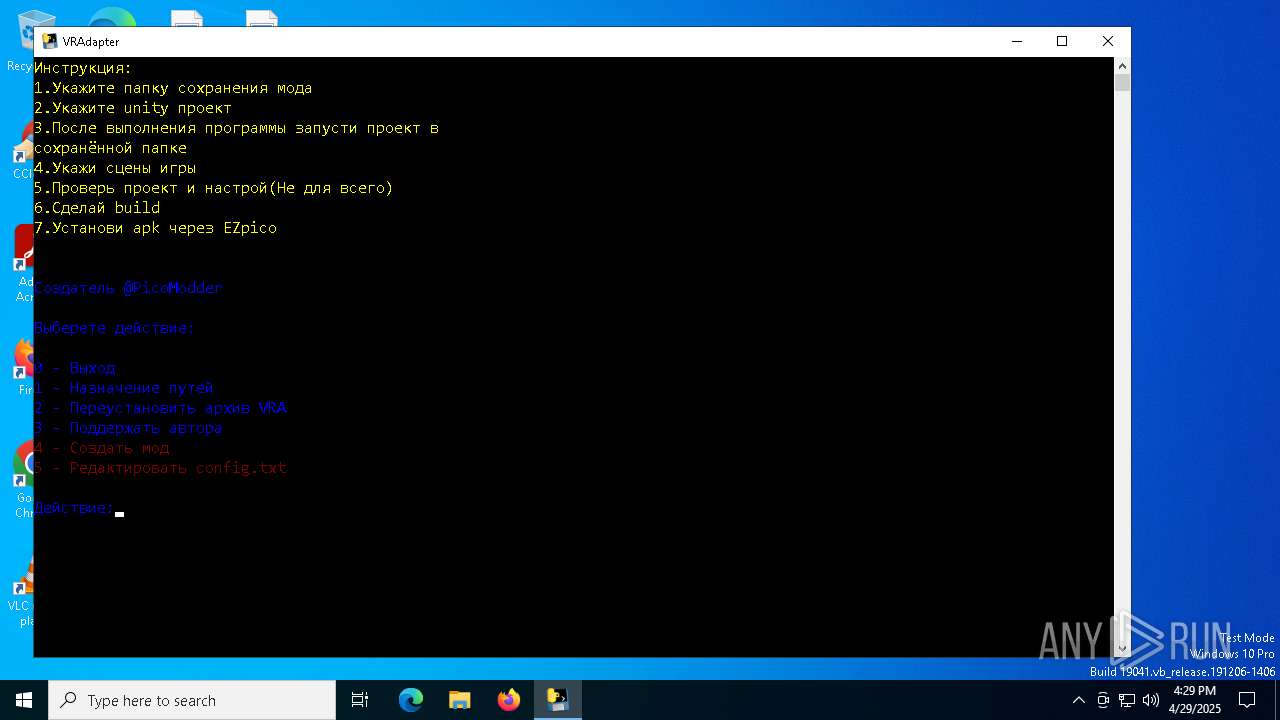
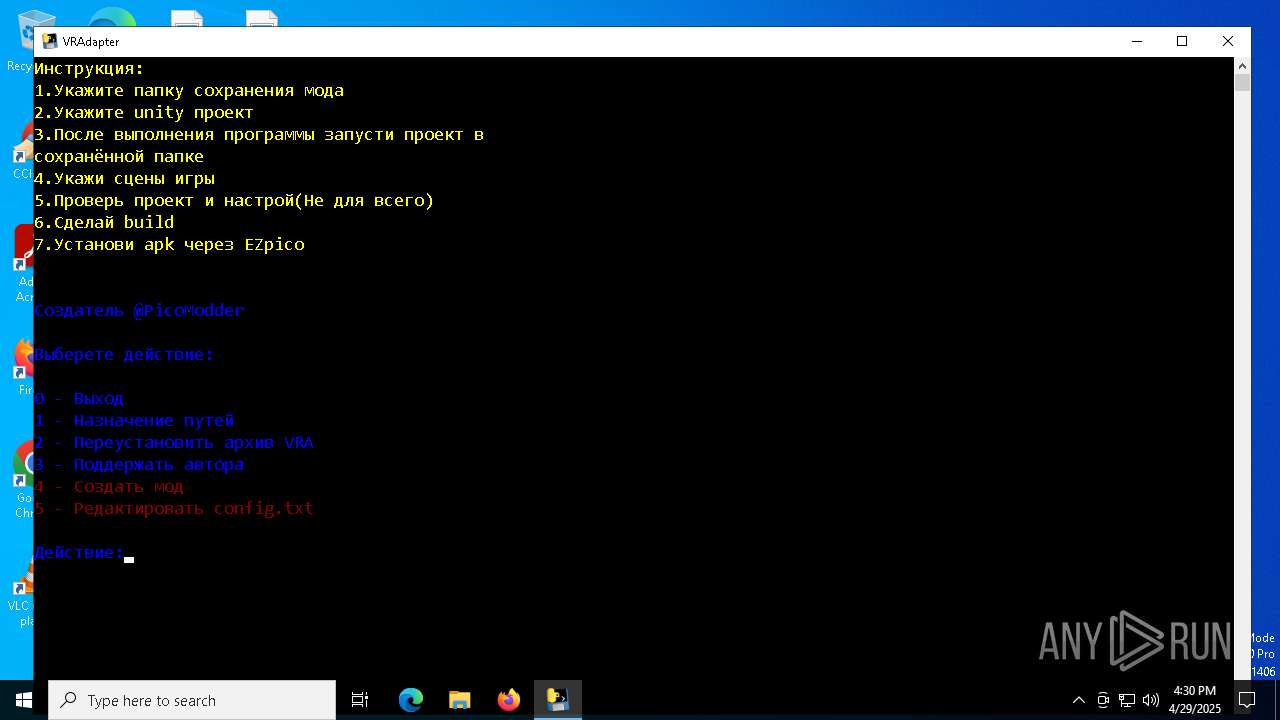
| 7212 | C:\WINDOWS\system32\cmd.exe /c title VRAdapter | C:\Windows\System32\cmd.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7232 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
224
Read events
224
Write events
0
Delete events
0
Modification events
Executable files
53
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4880 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI48802\_ssl.pyd | executable | |
MD5:1C0E3E447F719FBE2601D0683EA566FC | SHA256:63AE2FEFBFBBBC6EA39CDE0A622579D46FF55134BC8C1380289A2976B61F603E | |||
| 4880 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI48802\_ctypes.pyd | executable | |
MD5:A55E57D7594303C89B5F7A1D1D6F2B67 | SHA256:F63C6C7E71C342084D8F1A108786CA6975A52CEFEF8BE32CC2589E6E2FE060C8 | |||
| 4880 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI48802\_hashlib.pyd | executable | |
MD5:32D76C9ABD65A5D2671AEEDE189BC290 | SHA256:838D5C8B7C3212C8429BAF612623ABBBC20A9023EEC41E34E5461B76A285B86C | |||
| 4880 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI48802\_bz2.pyd | executable | |
MD5:CB8C06C8FA9E61E4AC5F22EEBF7F1D00 | SHA256:FC3B481684B926350057E263622A2A5335B149A0498A8D65C4F37E39DD90B640 | |||
| 4880 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI48802\_socket.pyd | executable | |
MD5:FE896371430BD9551717EF12A3E7E818 | SHA256:35246B04C6C7001CA448554246445A845CE116814A29B18B617EA38752E4659B | |||
| 4880 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI48802\_lzma.pyd | executable | |
MD5:1BA022D42024A655CF289544AE461FB8 | SHA256:D080EABD015A3569813A220FD4EA74DFF34ED2A8519A10473EB37E22B1118A06 | |||
| 4880 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI48802\_decimal.pyd | executable | |
MD5:F3377F3DE29579140E2BBAEEFD334D4F | SHA256:B715D1C18E9A9C1531F21C02003B4C6726742D1A2441A1893BC3D79D7BB50E91 | |||
| 4880 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI48802\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:33BBECE432F8DA57F17BF2E396EBAA58 | SHA256:7CF0944901F7F7E0D0B9AD62753FC2FE380461B1CCE8CDC7E9C9867C980E3B0E | |||
| 4880 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI48802\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:EFAD0EE0136532E8E8402770A64C71F9 | SHA256:3D2C55902385381869DB850B526261DDEB4628B83E690A32B67D2E0936B2C6ED | |||
| 4880 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI48802\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:E8B9D74BFD1F6D1CC1D99B24F44DA796 | SHA256:B1B3FD40AB437A43C8DB4994CCFFC7F88000CC8BB6E34A2BCBFF8E2464930C59 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
25
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.27:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.27:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4156 | SystemSettings.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4156 | SystemSettings.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7172 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7172 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.27:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.27:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cxcs.microsoft.net |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |