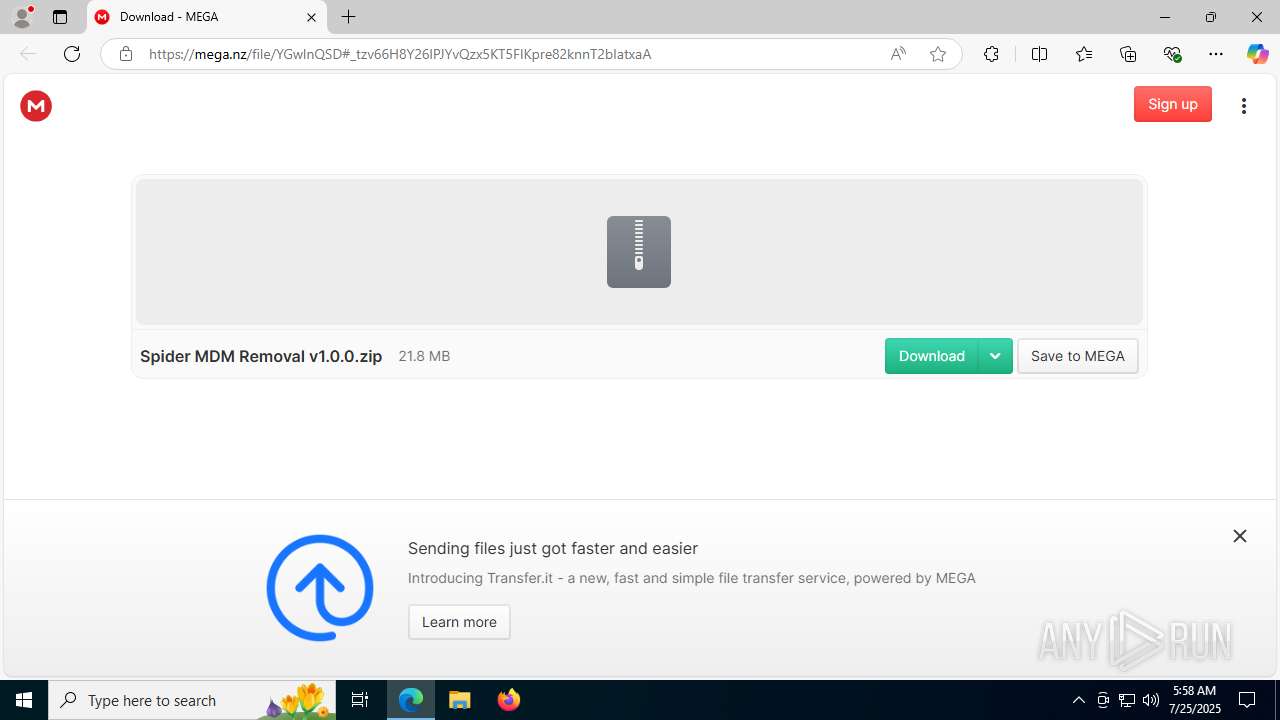
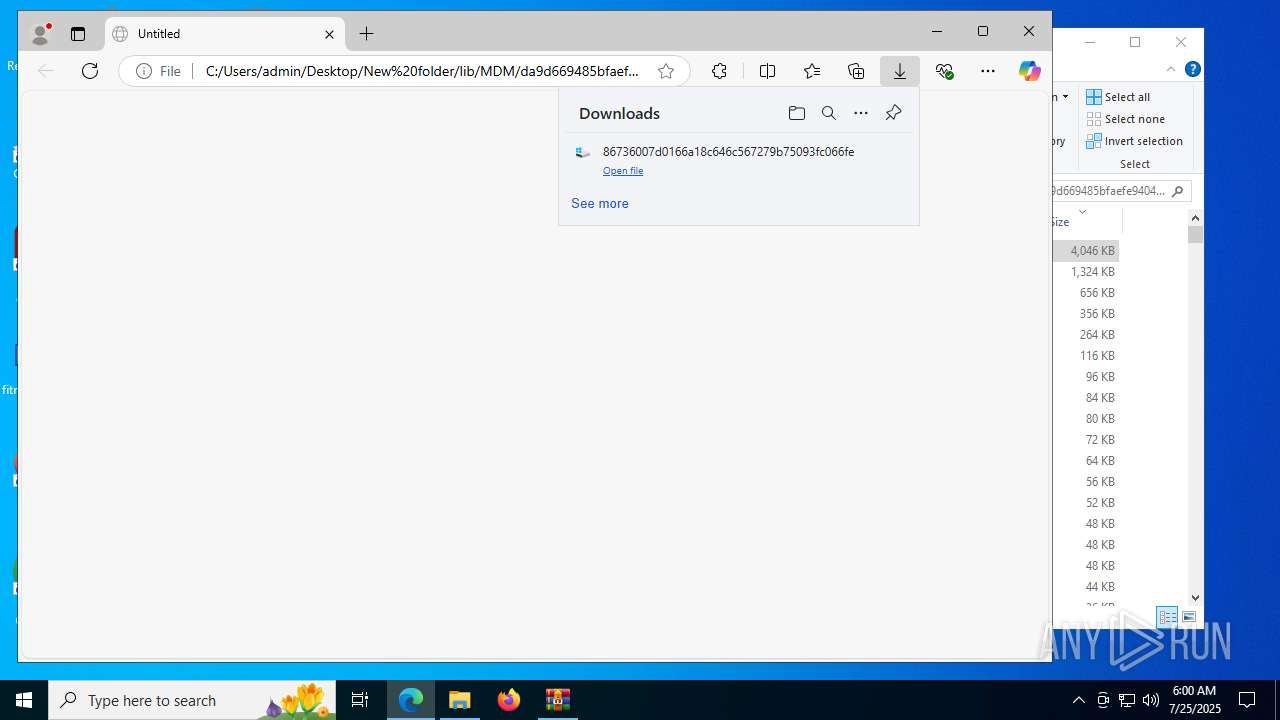
| URL: | https://mega.nz/file/YGwlnQSD#_tzv66H8Y26lPJYvQzx5KT5FIKpre82knnT2bIatxaA |
| Full analysis: | https://app.any.run/tasks/ebac84bb-73ac-461d-8575-e27493ccadd5 |
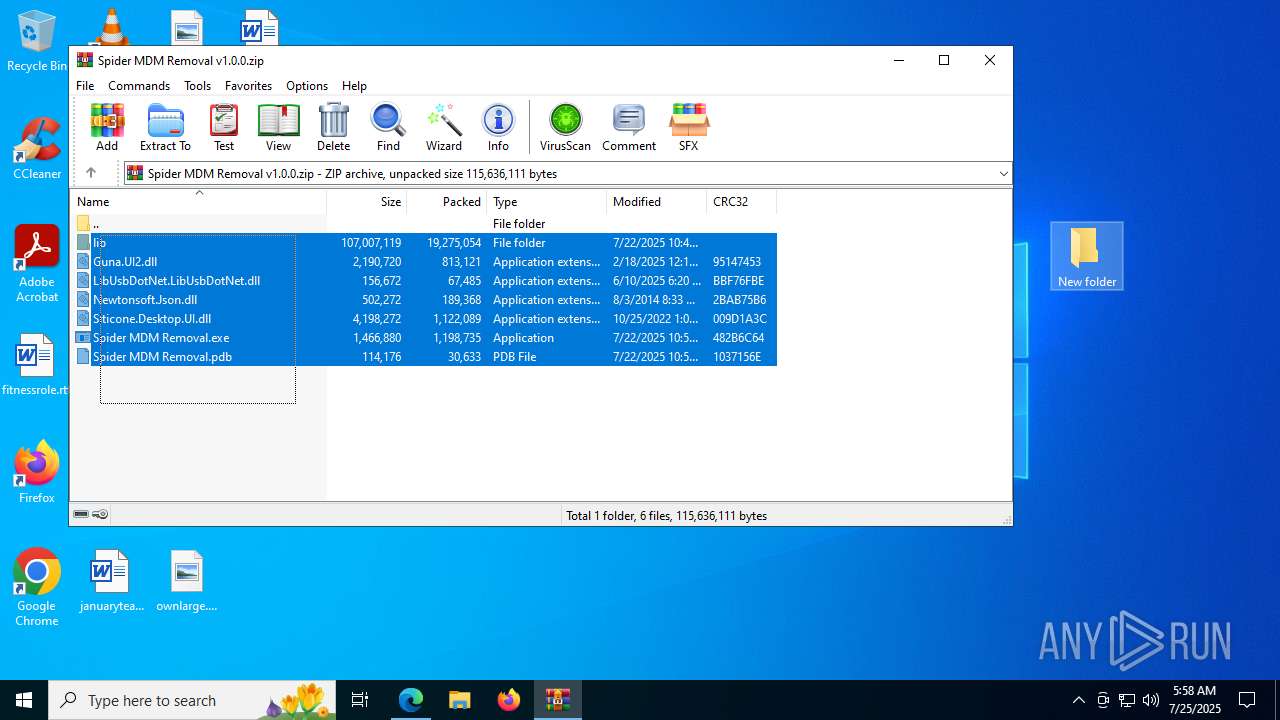
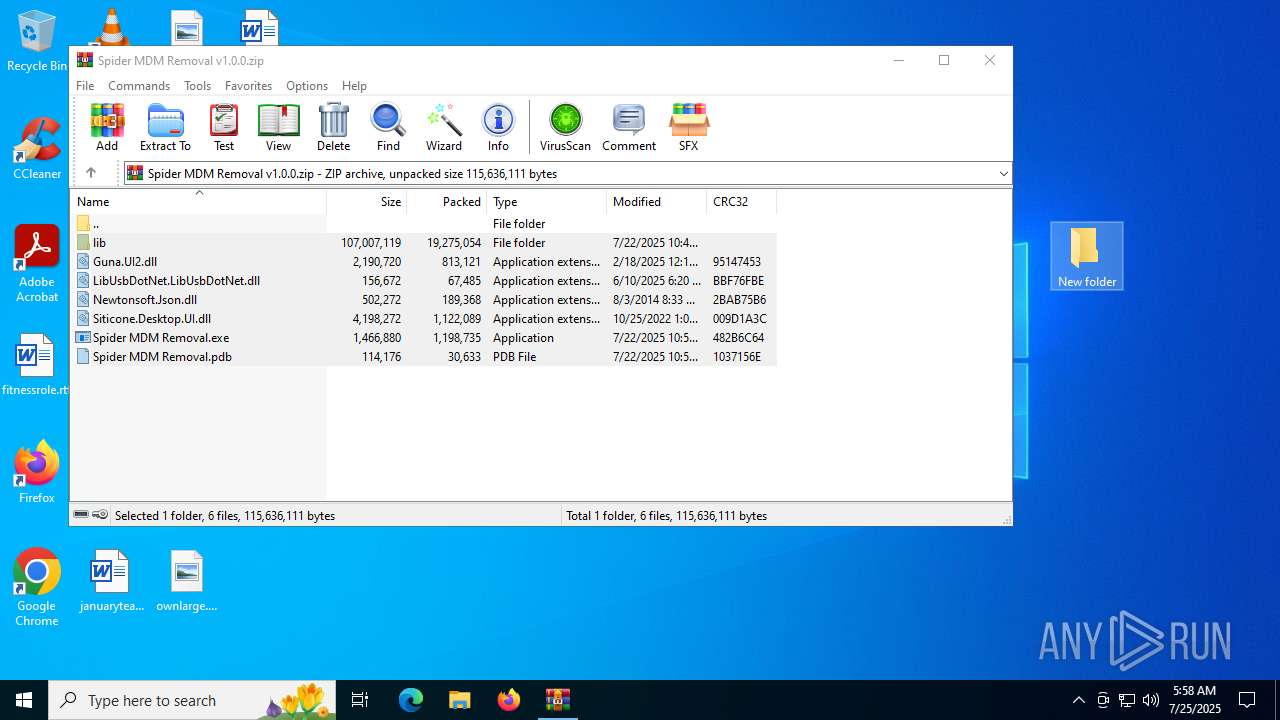
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2025, 05:58:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 5C5237B084A2DE52EC32013B7FB87CC1 |
| SHA1: | 003DFF0F317E43A7F25A1B4F3DF4FBB557DD9206 |
| SHA256: | 811A6782FA159A9FBD79BA76DB6FD1EF0ADF262DEDFE87E3F7C0D38CBC28F1E4 |
| SSDEEP: | 3:N8X/iAx2Q6RYDnQ7TLLxXMCn:2F2vOILx8Cn |
MALICIOUS
No malicious indicators.SUSPICIOUS
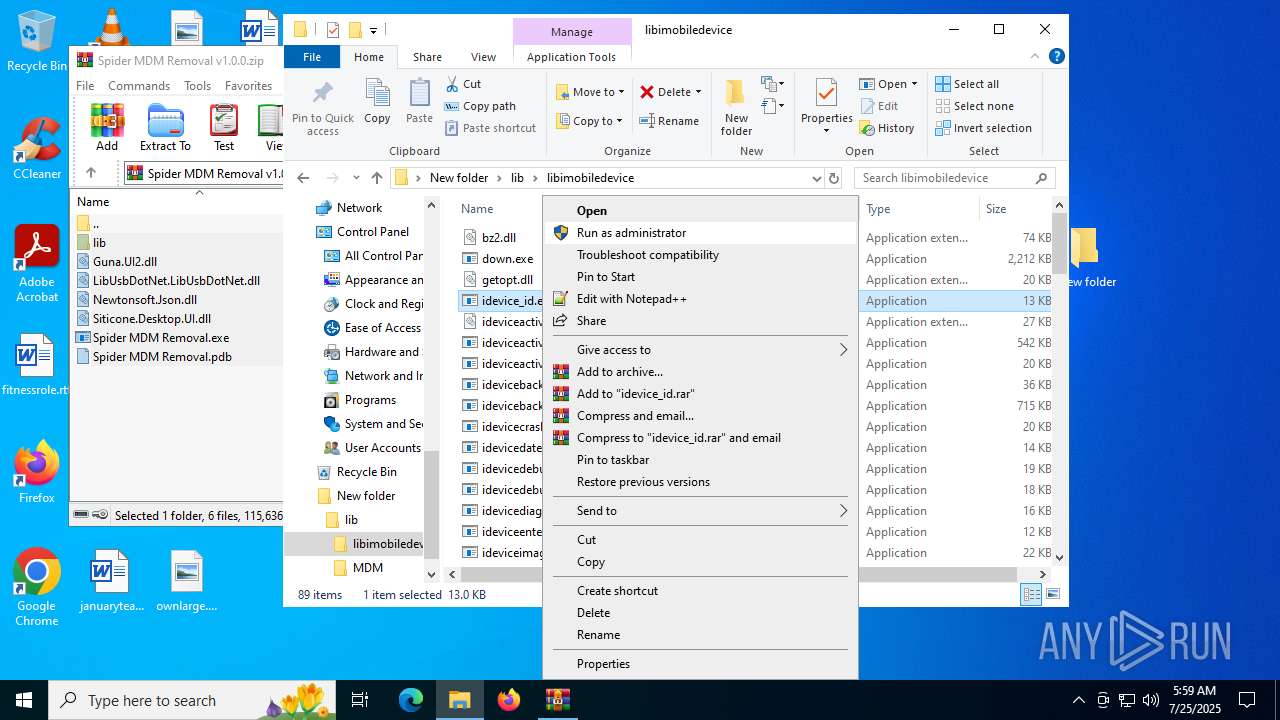
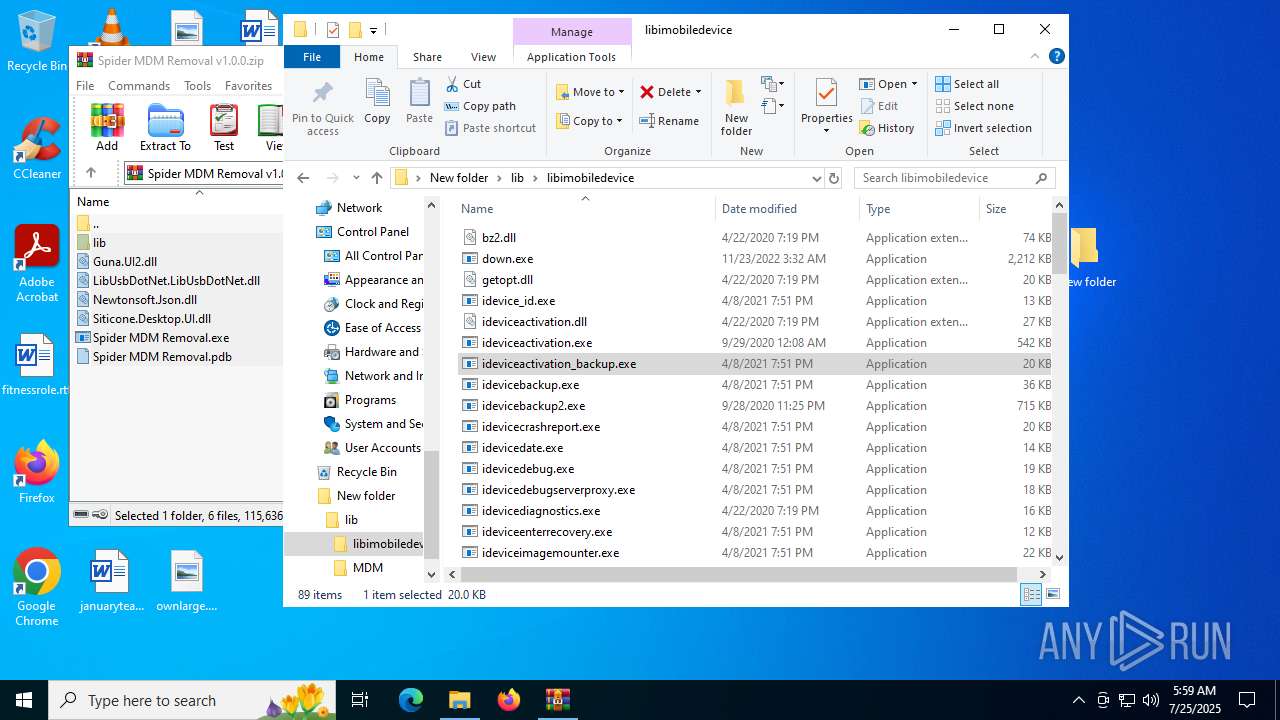
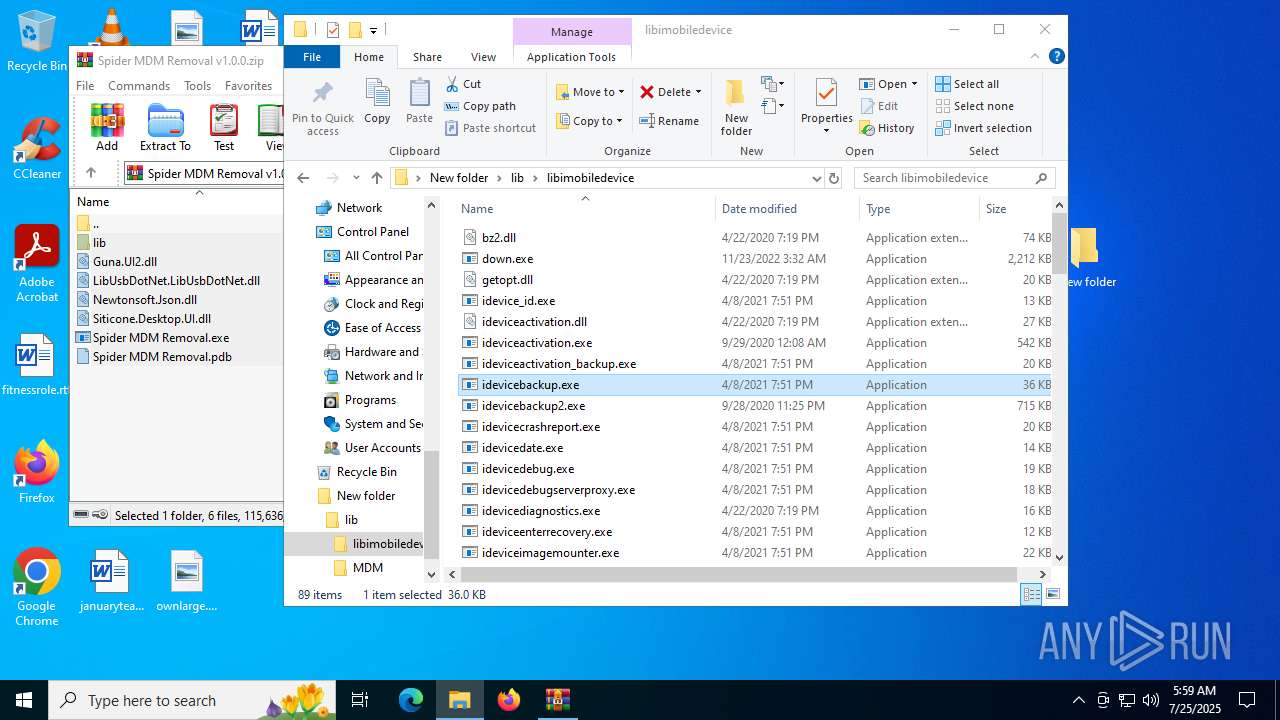
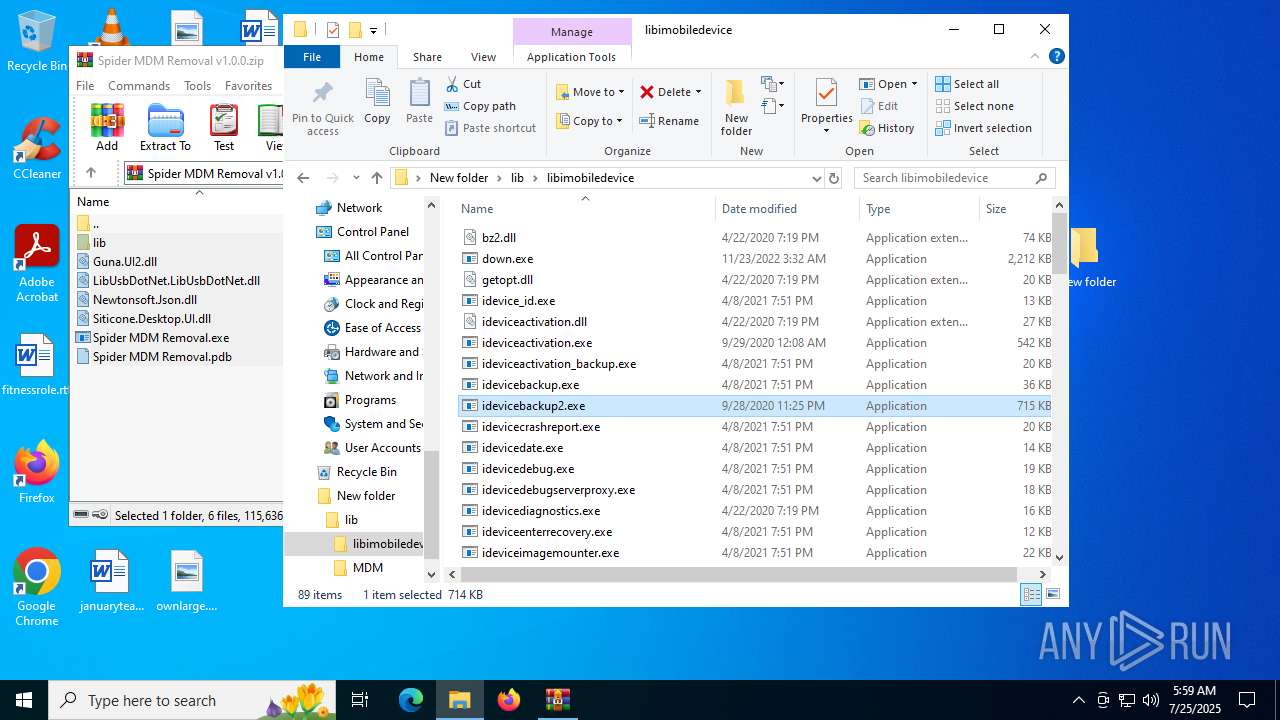
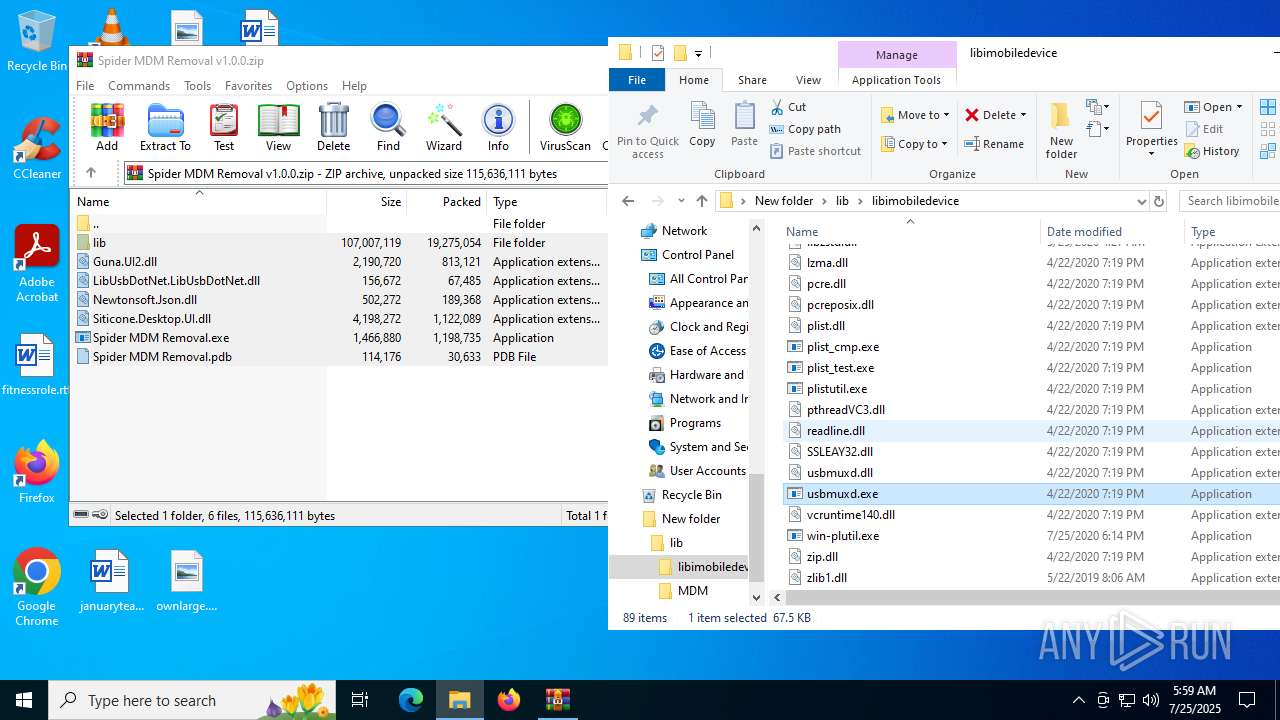
Process drops legitimate windows executable
- WinRAR.exe (PID: 1380)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 7896)
INFO
Checks supported languages
- identity_helper.exe (PID: 7912)
- ShellExperienceHost.exe (PID: 7896)
- identity_helper.exe (PID: 8120)
- down.exe (PID: 888)
- down.exe (PID: 5372)
- idevice_id.exe (PID: 7624)
- ideviceactivation.exe (PID: 2432)
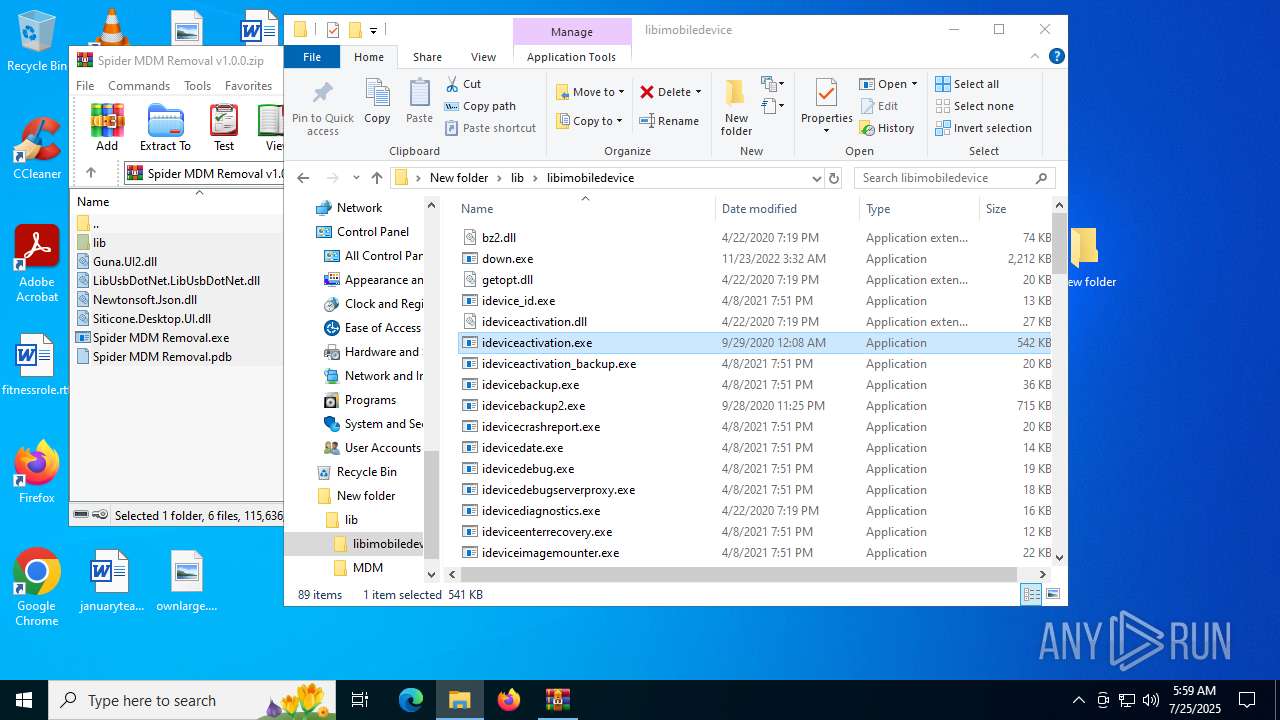
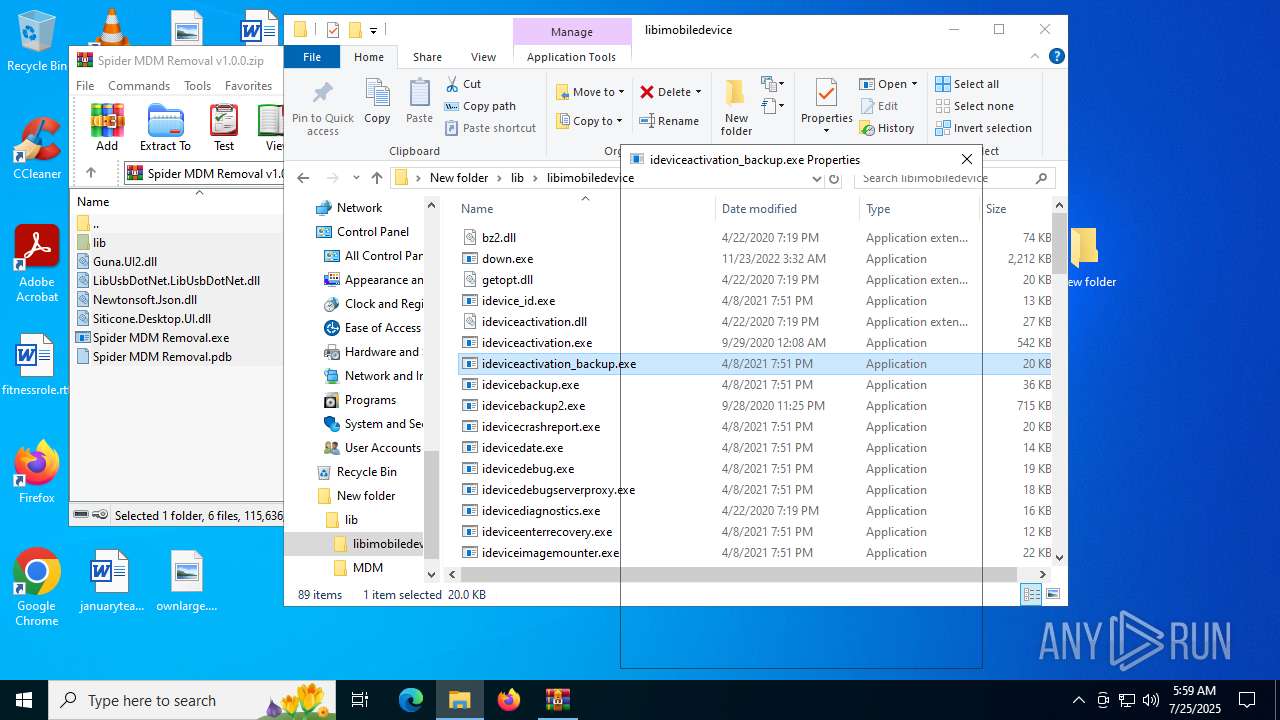
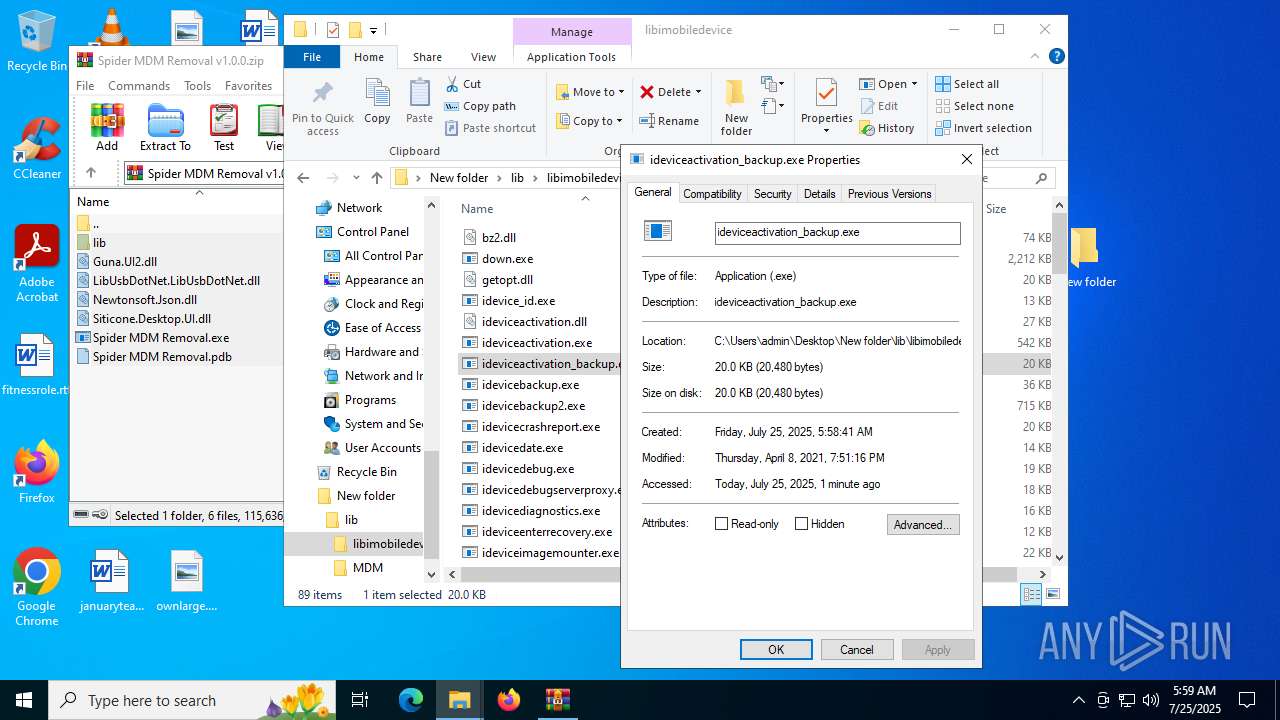
- ideviceactivation_backup.exe (PID: 7888)
- idevicebackup2.exe (PID: 6980)
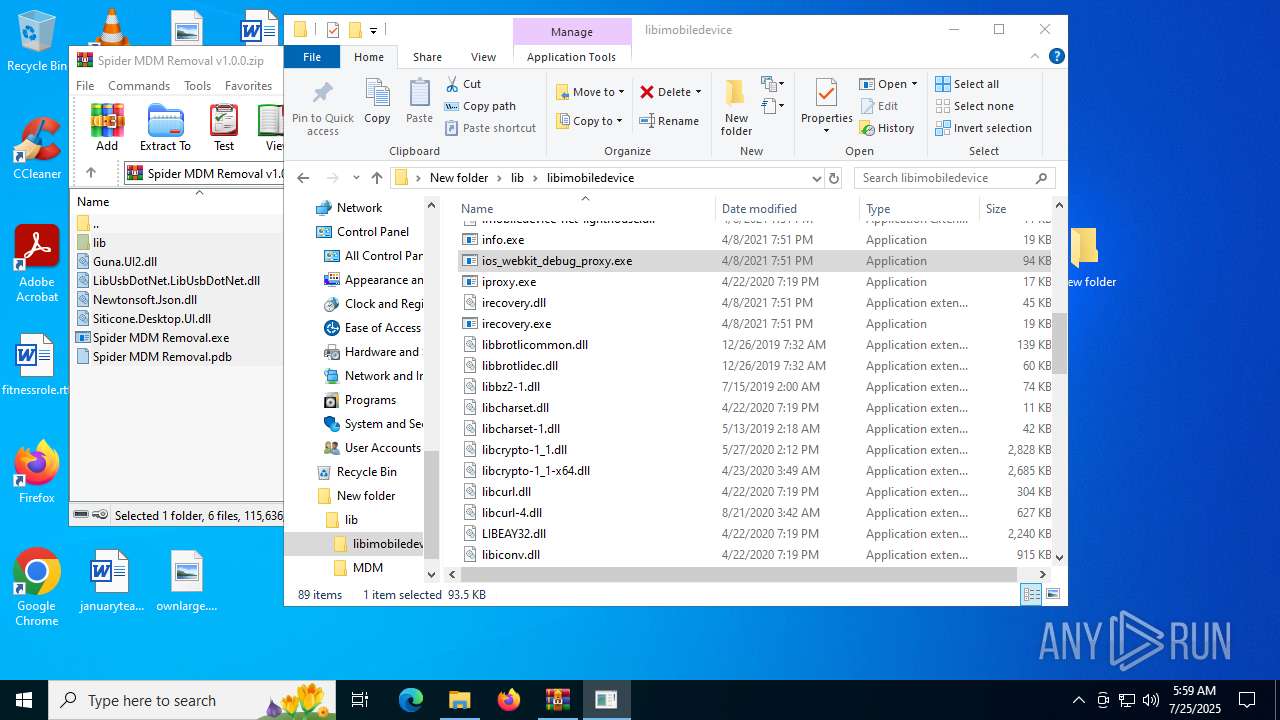
- ios_webkit_debug_proxy.exe (PID: 828)
- irecovery.exe (PID: 1128)
- iproxy.exe (PID: 1668)
- info.exe (PID: 1156)
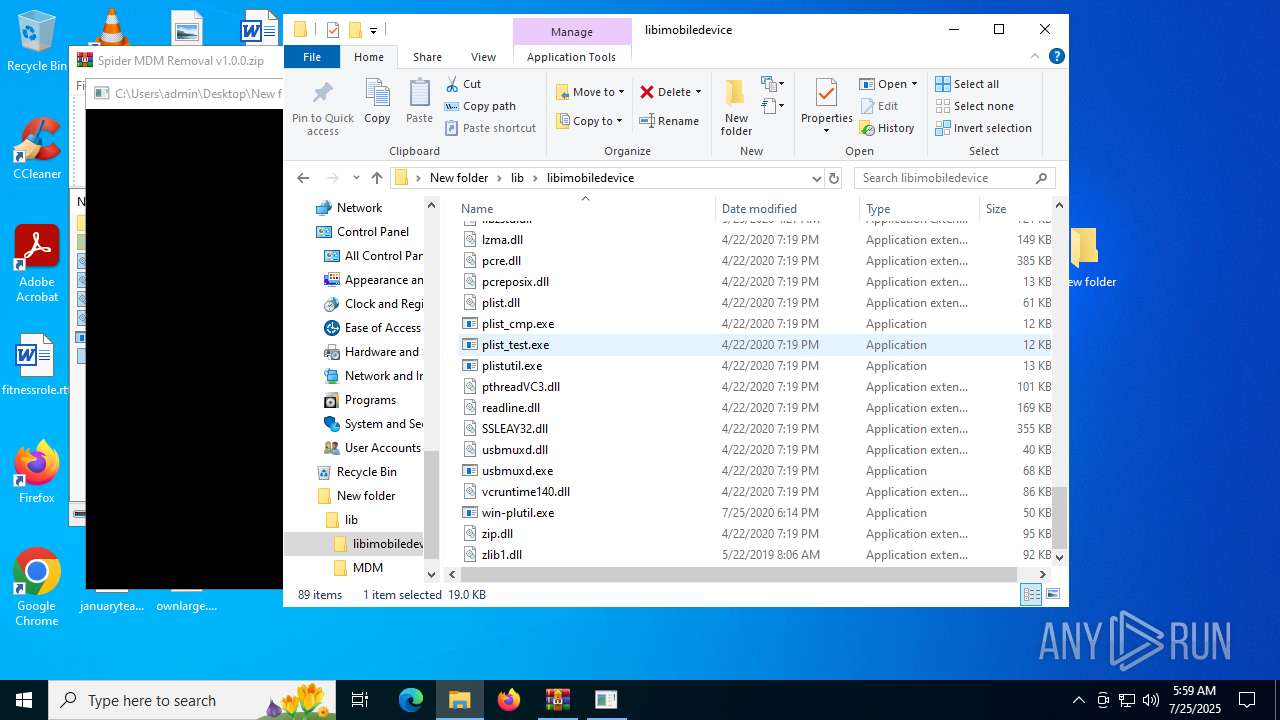
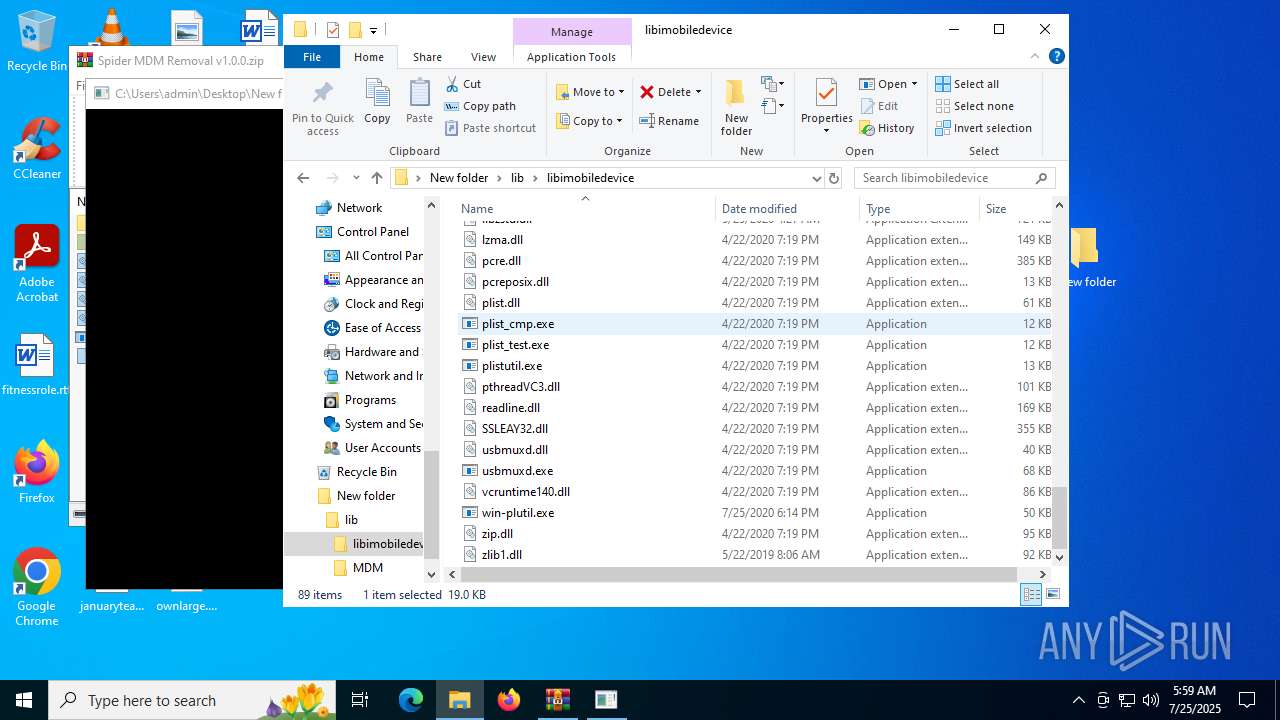
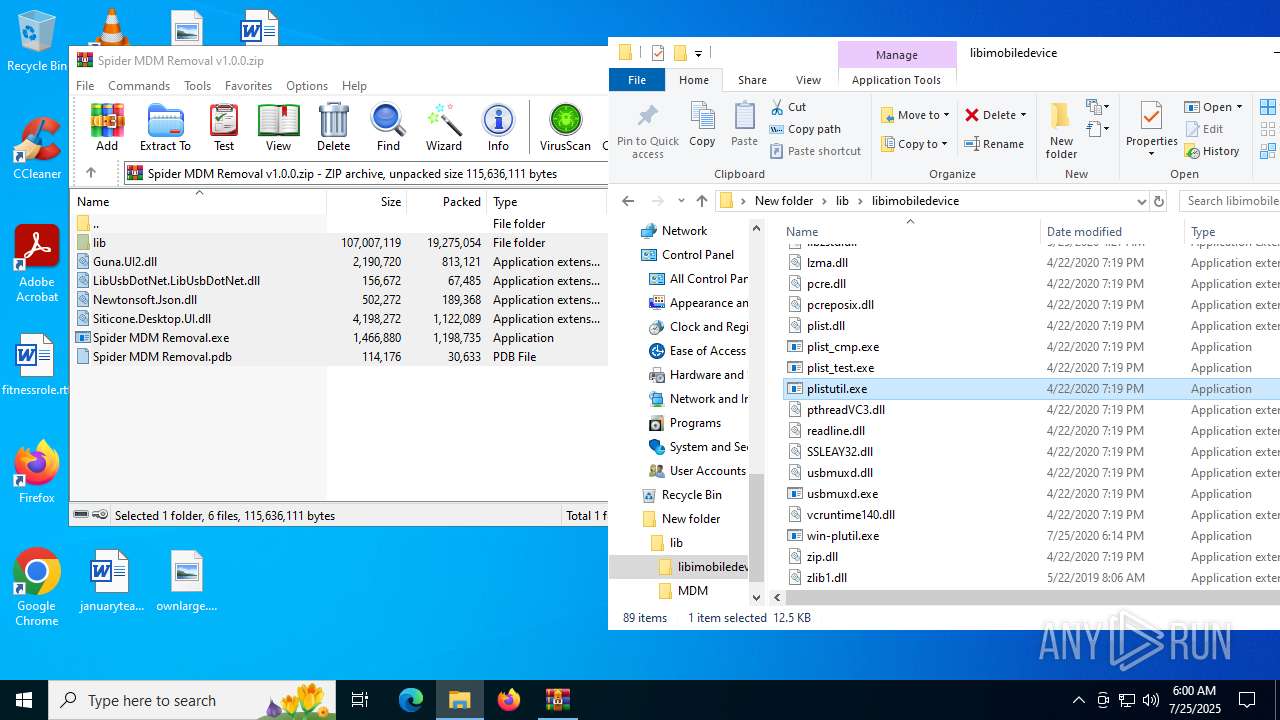
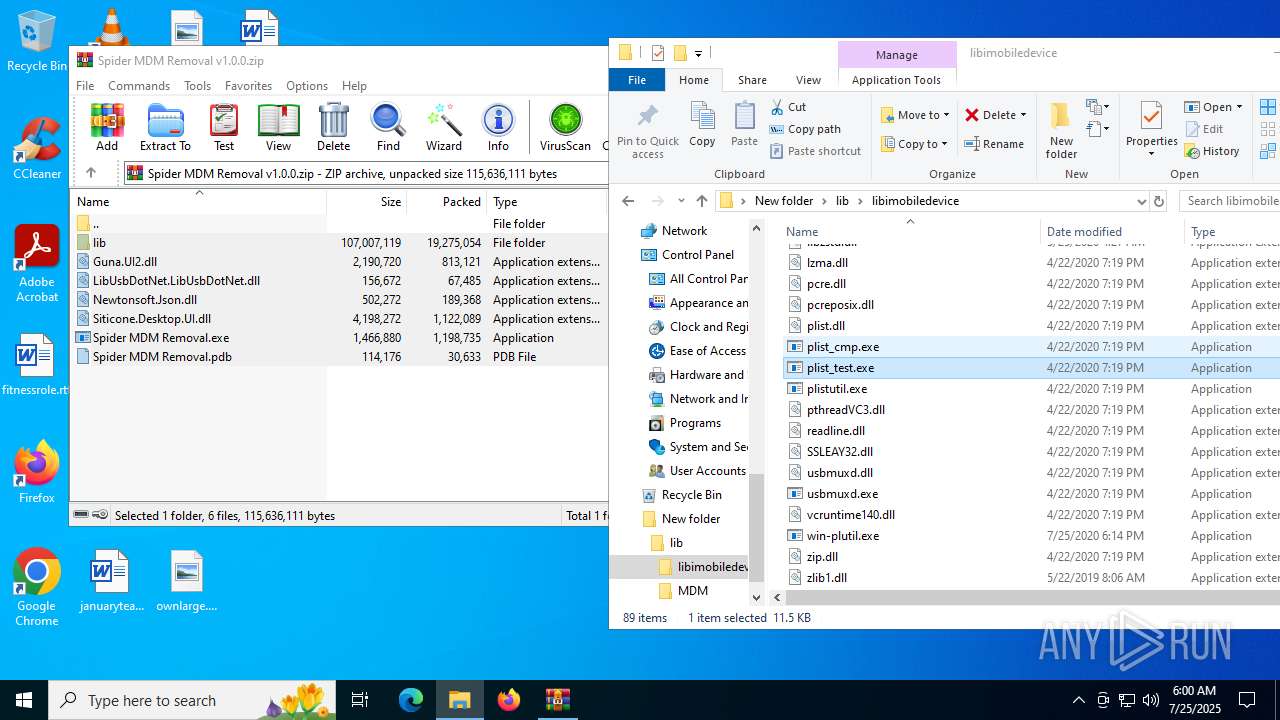
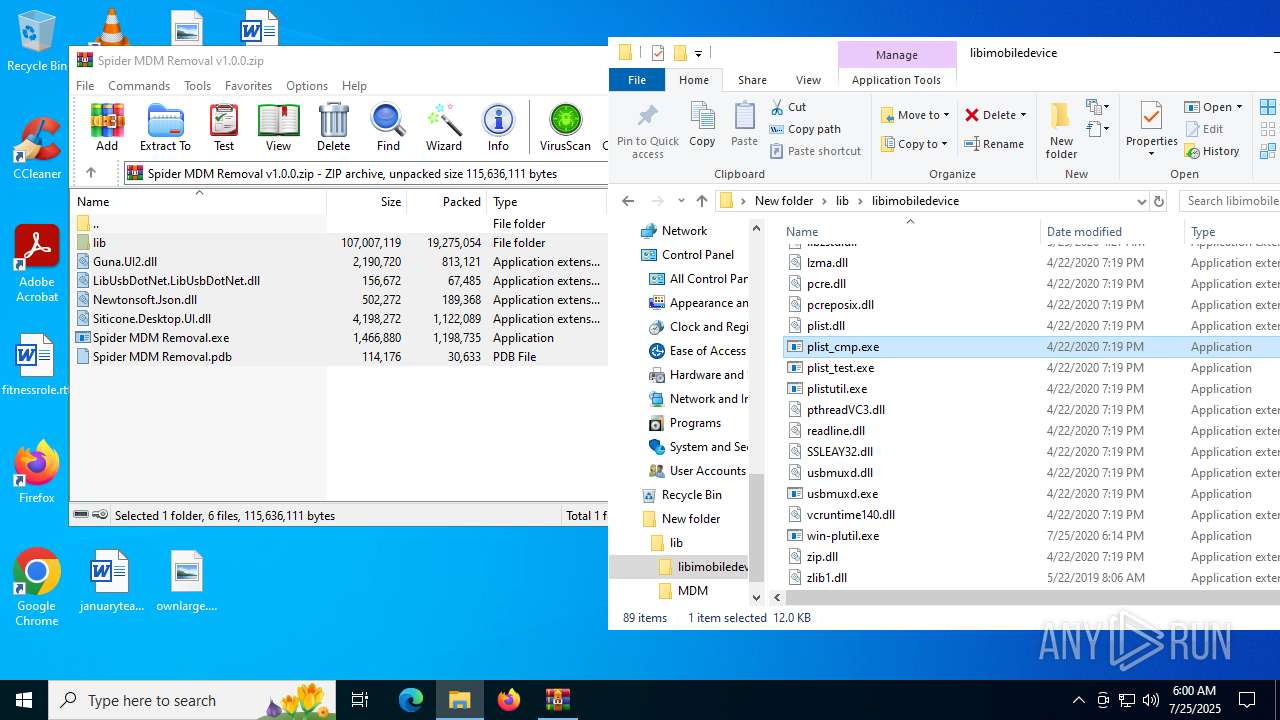
- plist_cmp.exe (PID: 7256)
- win-plutil.exe (PID: 2096)
- usbmuxd.exe (PID: 6808)
- idevicebackup.exe (PID: 3288)
- plistutil.exe (PID: 4124)
- plist_test.exe (PID: 7224)
- plist_cmp.exe (PID: 3628)
- identity_helper.exe (PID: 6148)
Application launched itself
- msedge.exe (PID: 2848)
- msedge.exe (PID: 4768)
- msedge.exe (PID: 3392)
Reads Environment values
- identity_helper.exe (PID: 7912)
- identity_helper.exe (PID: 8120)
- identity_helper.exe (PID: 6148)
Reads the computer name
- identity_helper.exe (PID: 7912)
- ShellExperienceHost.exe (PID: 7896)
- identity_helper.exe (PID: 8120)
- ios_webkit_debug_proxy.exe (PID: 828)
- win-plutil.exe (PID: 2096)
- identity_helper.exe (PID: 6148)
The sample compiled with english language support
- WinRAR.exe (PID: 1380)
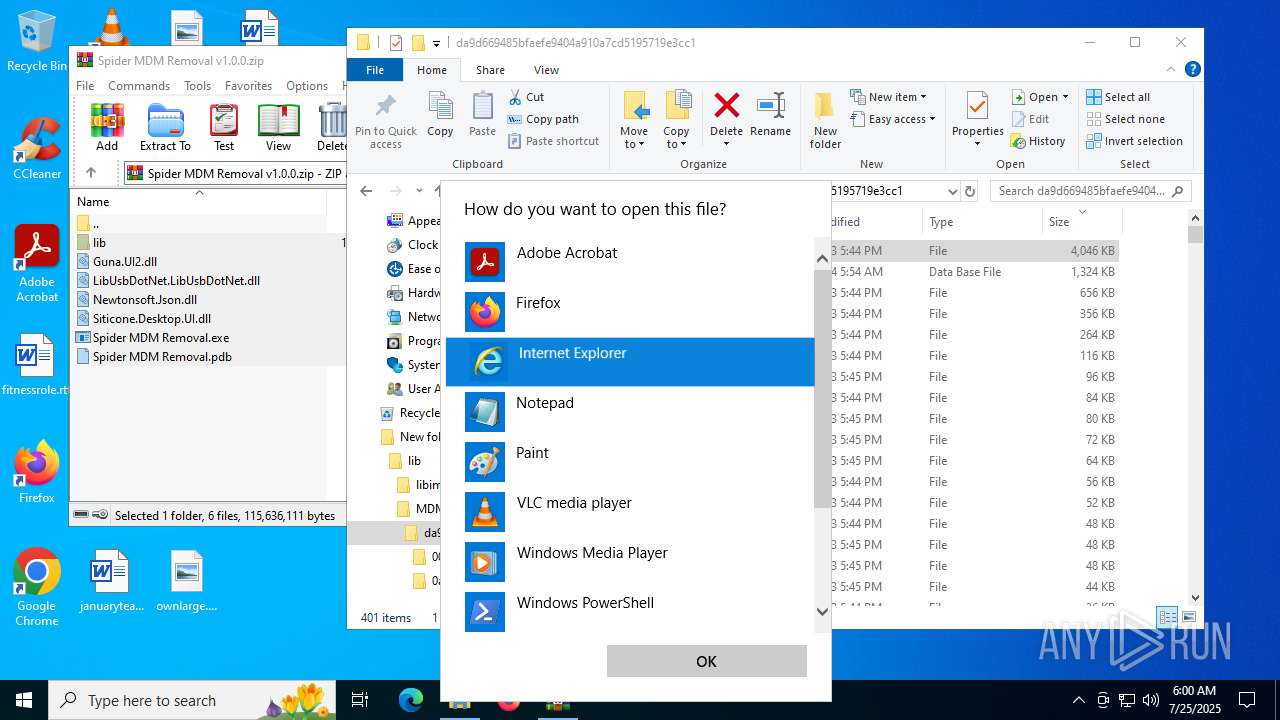
Reads Microsoft Office registry keys
- msedge.exe (PID: 2848)
- OpenWith.exe (PID: 2716)
- OpenWith.exe (PID: 1388)
- OpenWith.exe (PID: 8180)
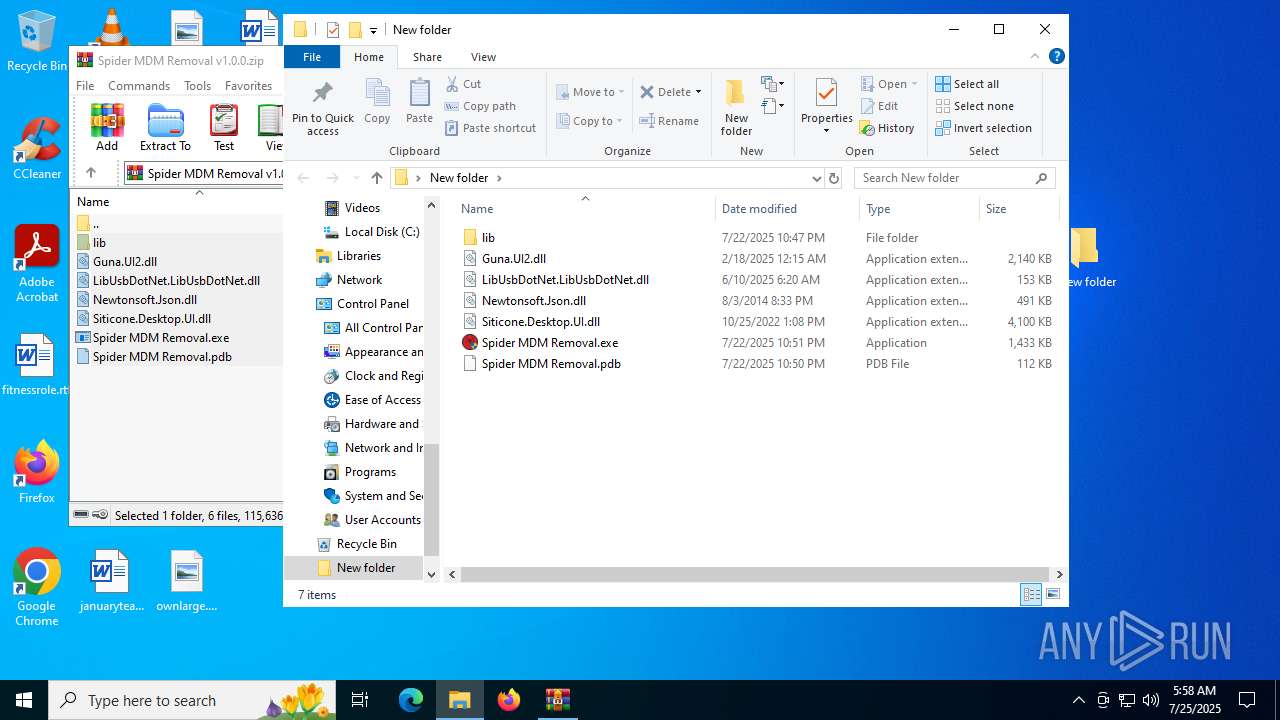
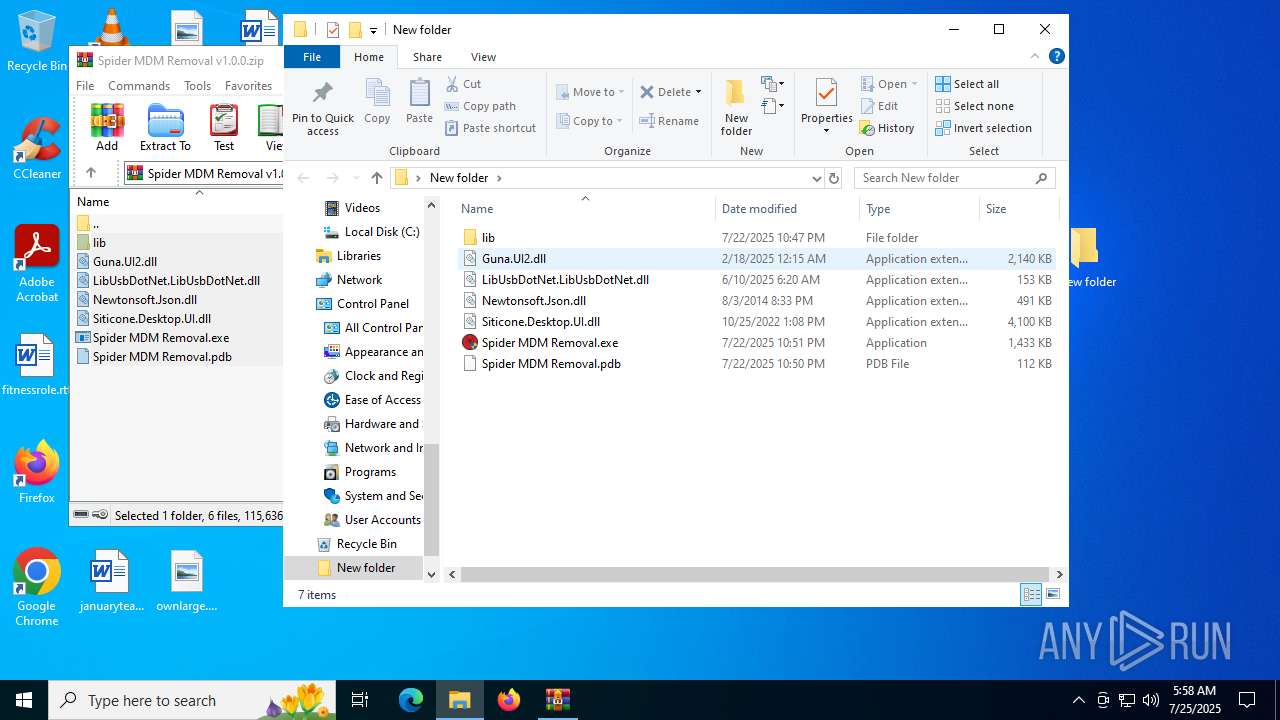
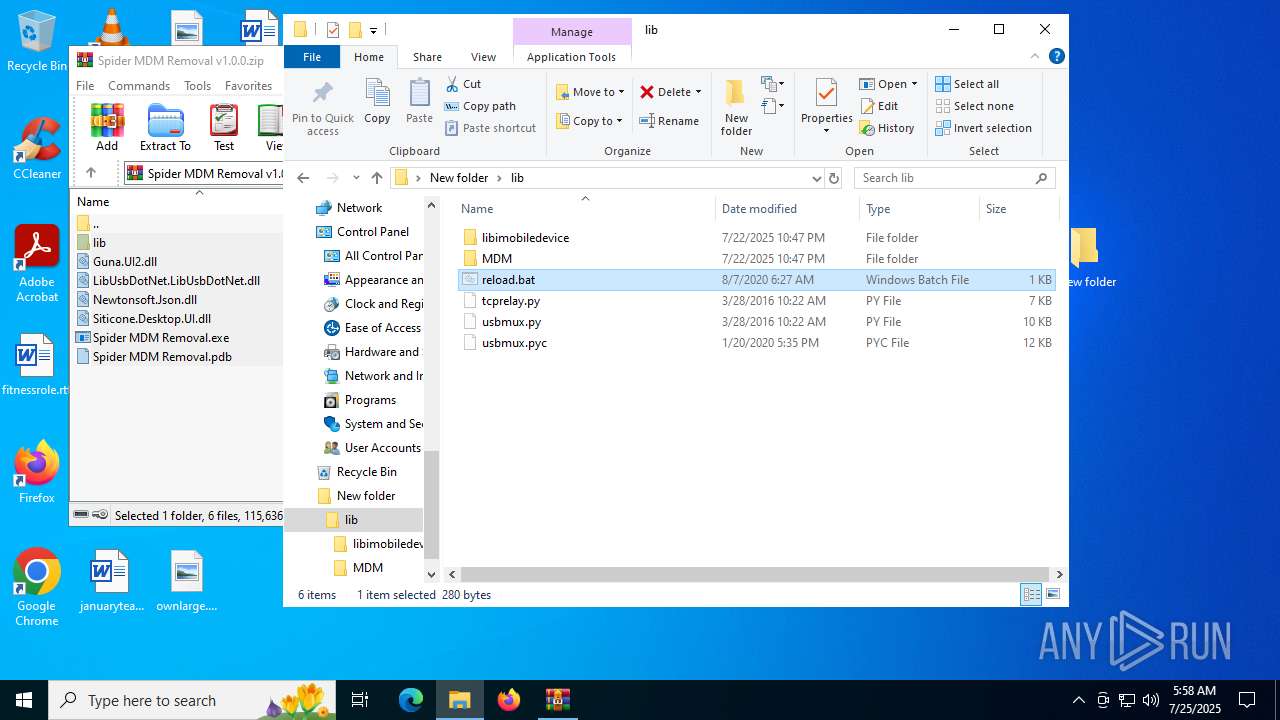
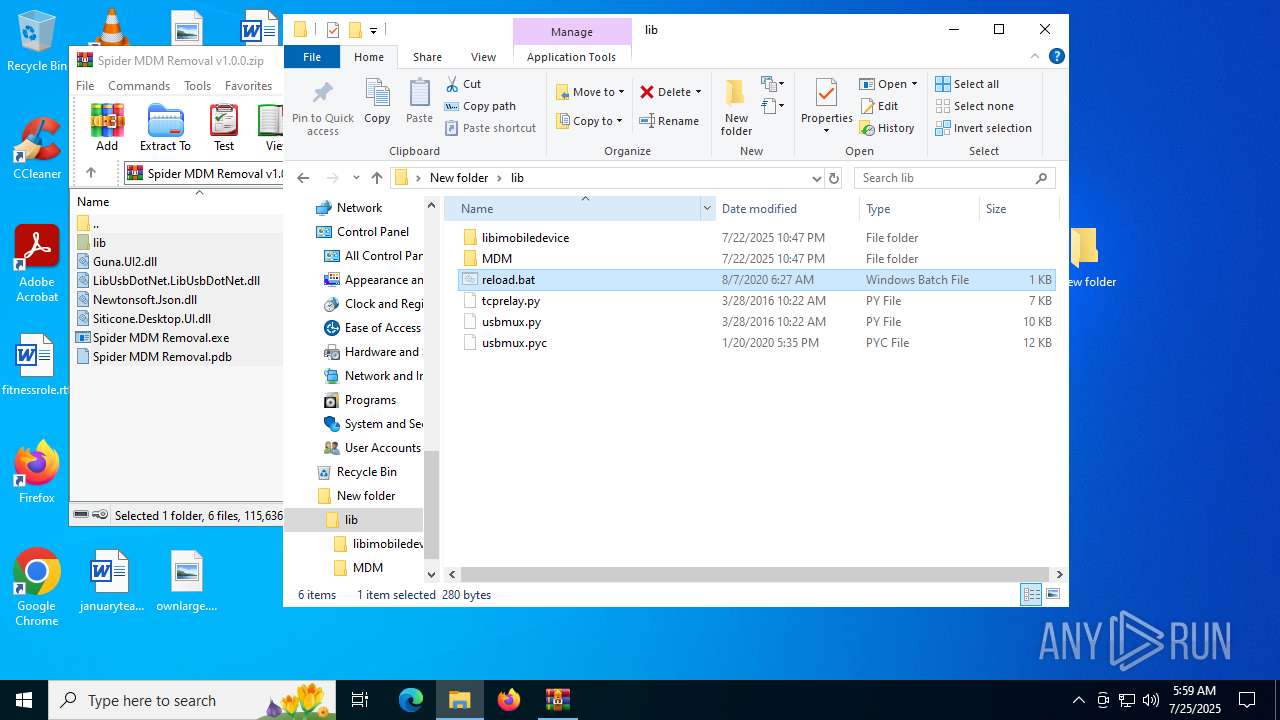
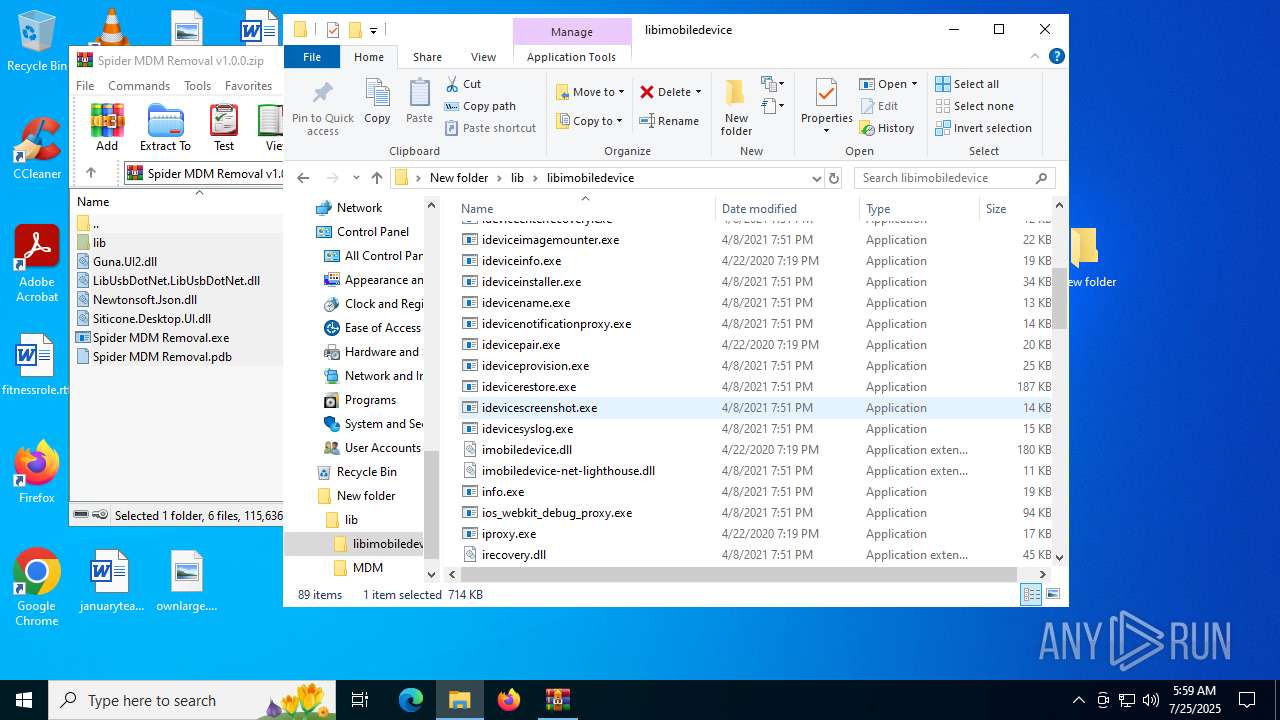
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1380)
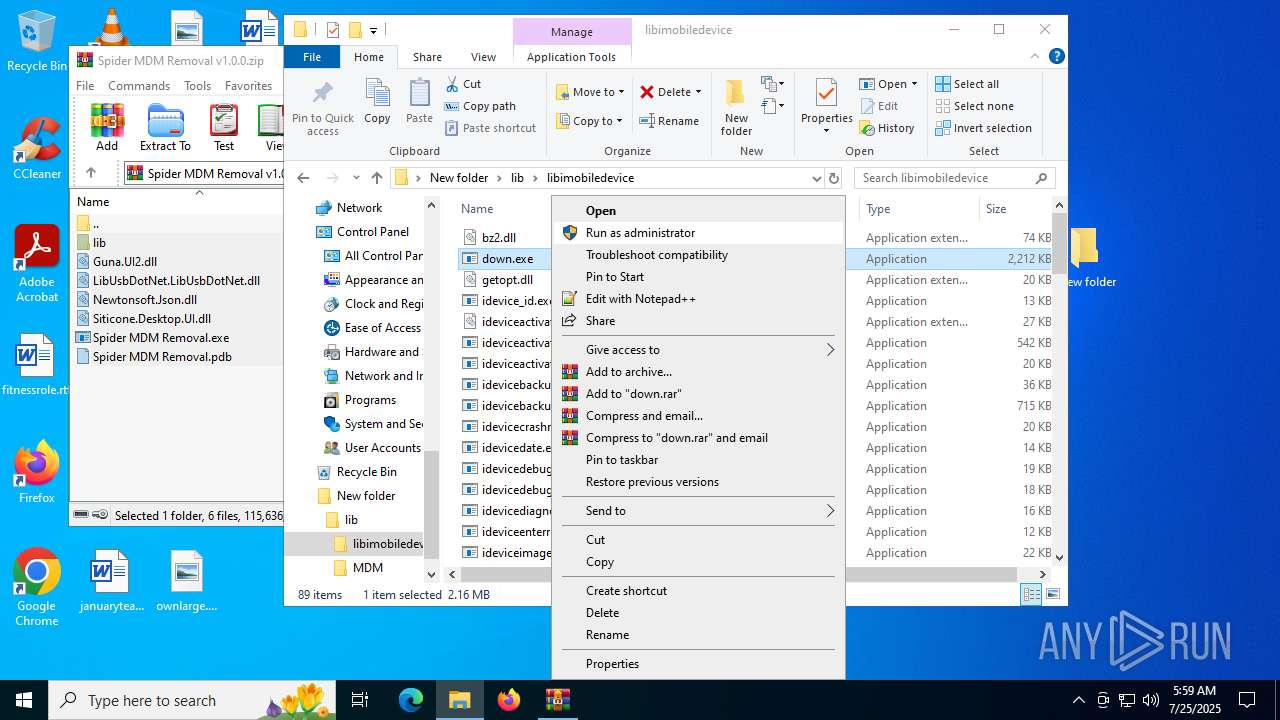
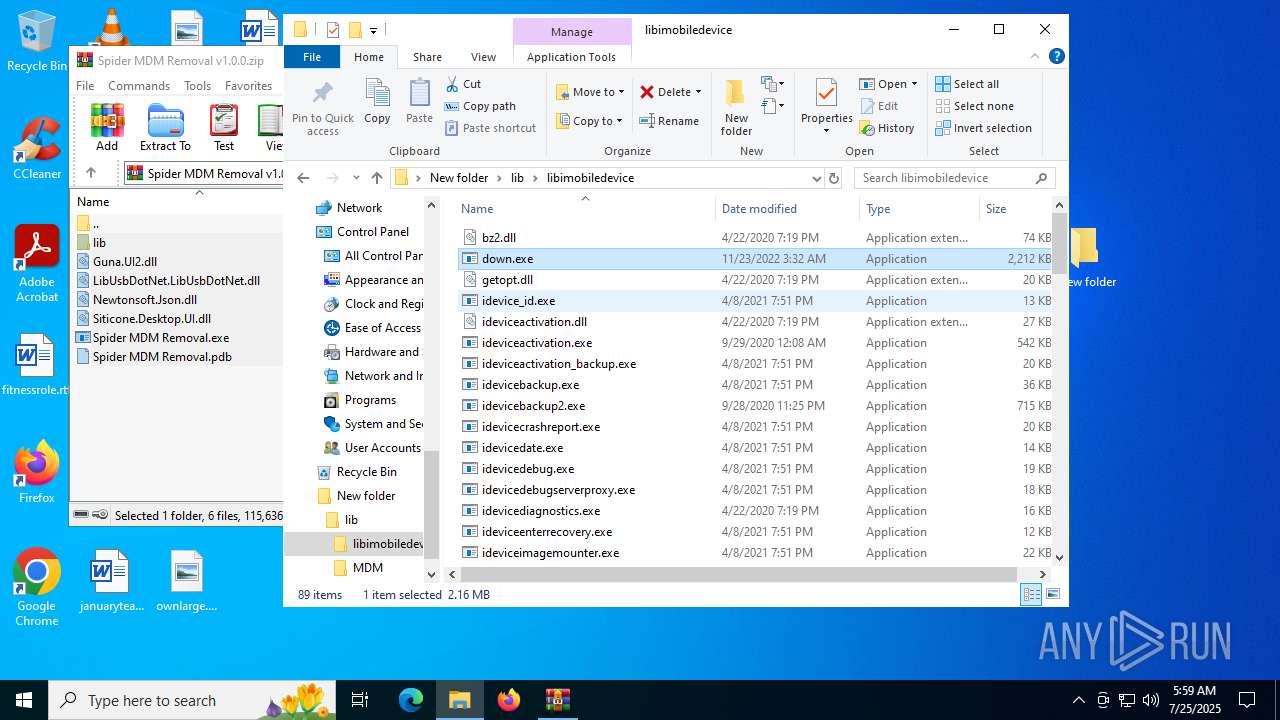
Manual execution by a user
- cmd.exe (PID: 8168)
- cmd.exe (PID: 7872)
- down.exe (PID: 888)
- down.exe (PID: 5372)
- idevice_id.exe (PID: 7624)
- idevicebackup.exe (PID: 3288)
- idevicebackup2.exe (PID: 6980)
- ideviceactivation.exe (PID: 2432)
- irecovery.exe (PID: 1128)
- info.exe (PID: 1156)
- plist_cmp.exe (PID: 7256)
- iproxy.exe (PID: 1668)
- ios_webkit_debug_proxy.exe (PID: 828)
- win-plutil.exe (PID: 2096)
- plistutil.exe (PID: 4124)
- usbmuxd.exe (PID: 6808)
- plist_test.exe (PID: 7224)
- plist_cmp.exe (PID: 3628)
- ideviceactivation_backup.exe (PID: 7888)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 8180)
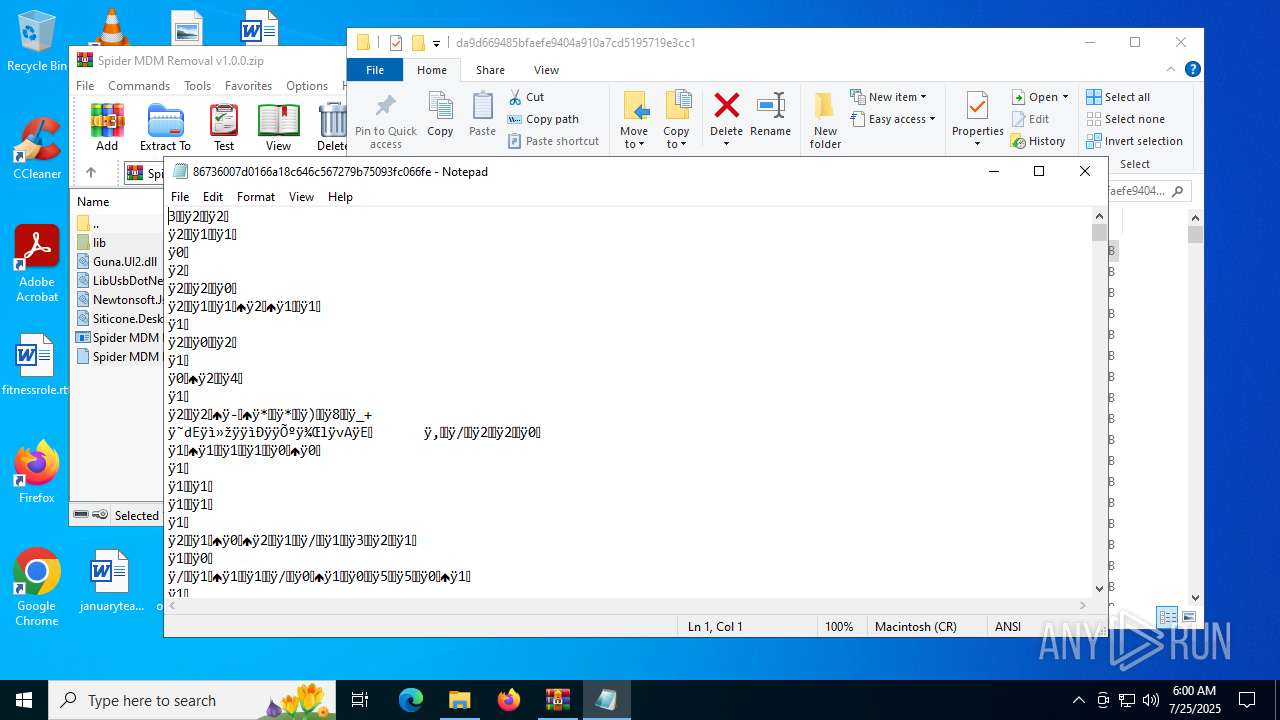
- notepad.exe (PID: 4648)
- OpenWith.exe (PID: 1388)
Checks proxy server information
- slui.exe (PID: 6220)
Reads the software policy settings
- slui.exe (PID: 6220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
250
Monitored processes
101
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2748,i,7422958519459060108,10043459671129300828,262144 --variations-seed-version --mojo-platform-channel-handle=2768 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
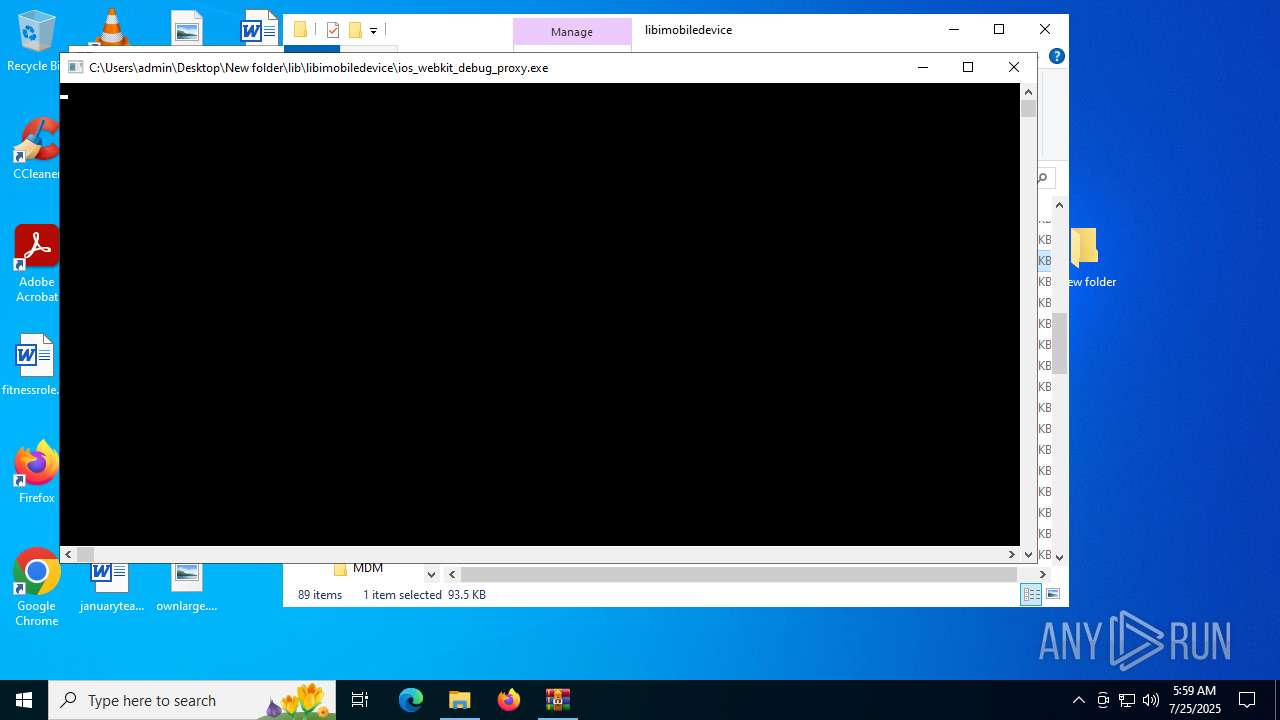
| 828 | "C:\Users\admin\Desktop\New folder\lib\libimobiledevice\ios_webkit_debug_proxy.exe" | C:\Users\admin\Desktop\New folder\lib\libimobiledevice\ios_webkit_debug_proxy.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 888 | "C:\Users\admin\Desktop\New folder\lib\libimobiledevice\down.exe" | C:\Users\admin\Desktop\New folder\lib\libimobiledevice\down.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4736,i,5187024185310493396,3846021984940770331,262144 --variations-seed-version --mojo-platform-channel-handle=5368 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1128 | "C:\Users\admin\Desktop\New folder\lib\libimobiledevice\irecovery.exe" | C:\Users\admin\Desktop\New folder\lib\libimobiledevice\irecovery.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | irecovery.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | "C:\Users\admin\Desktop\New folder\lib\libimobiledevice\info.exe" | C:\Users\admin\Desktop\New folder\lib\libimobiledevice\info.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
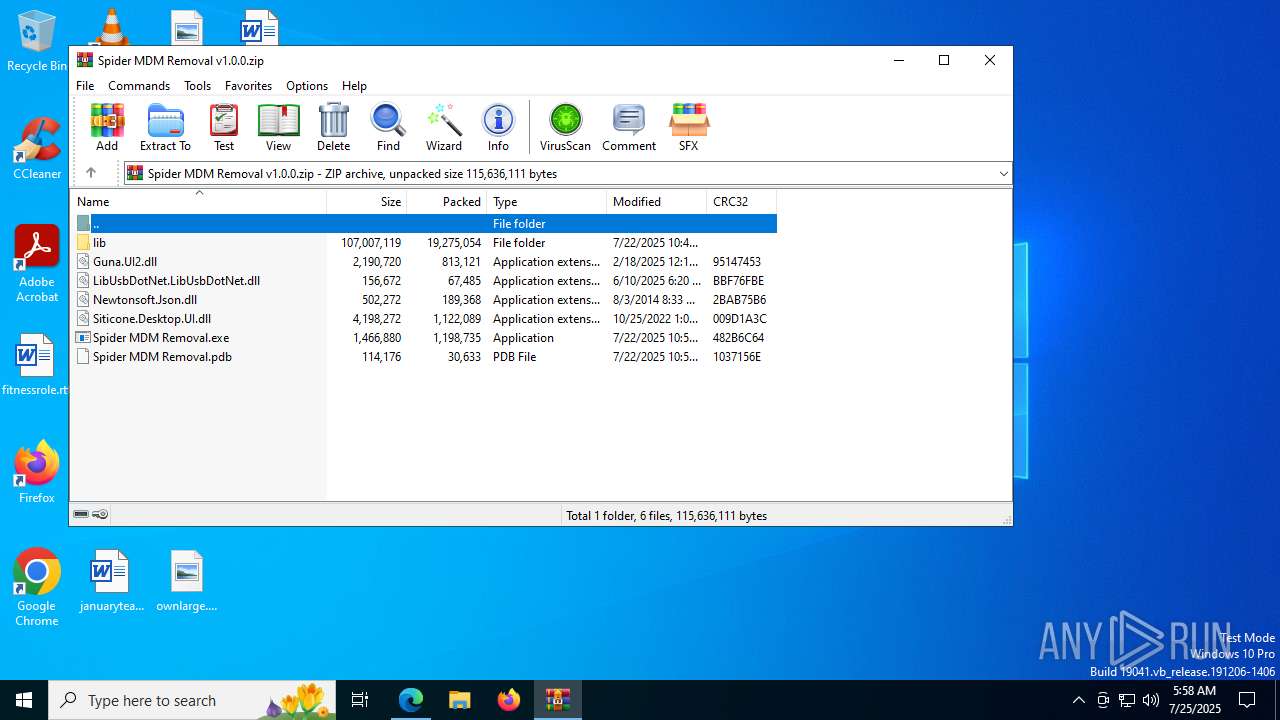
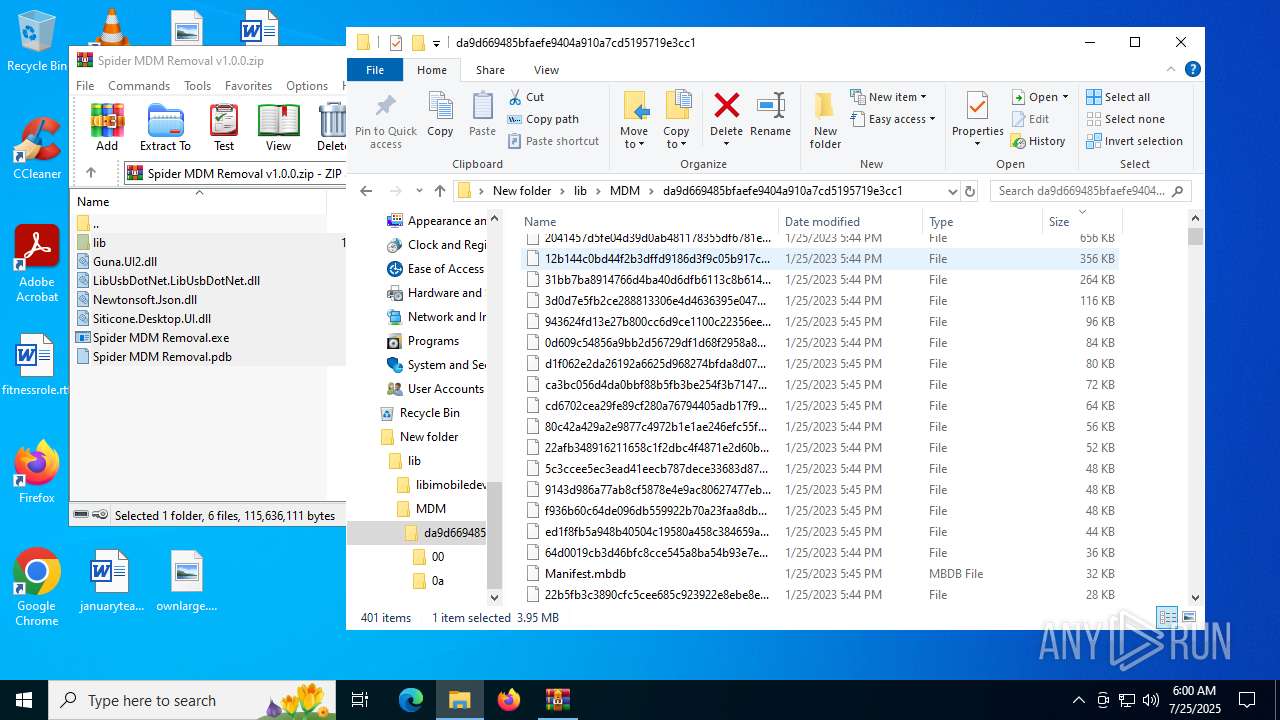
| 1380 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Spider MDM Removal v1.0.0.zip" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1388 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1580 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 152
Read events
19 091
Write events
61
Delete events
0
Modification events
| (PID) Process: | (2848) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2848) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2848) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2848) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2848) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3A2BC1E950992F00 | |||
| (PID) Process: | (2848) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459532 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B878F325-EE64-4090-8A49-1688A721ACAA} | |||
| (PID) Process: | (2848) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459532 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B772715F-9129-4988-A637-B66279DE75D5} | |||
| (PID) Process: | (2848) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459532 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {121B21D6-0B23-4EA5-B6B9-F93B941CDDE1} | |||
| (PID) Process: | (2848) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459532 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {265ADF60-9261-4940-8E5D-6268AAABFF4F} | |||
| (PID) Process: | (2848) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459532 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2379ECFB-C1E6-4A44-8E4B-E239849C0A0A} | |||
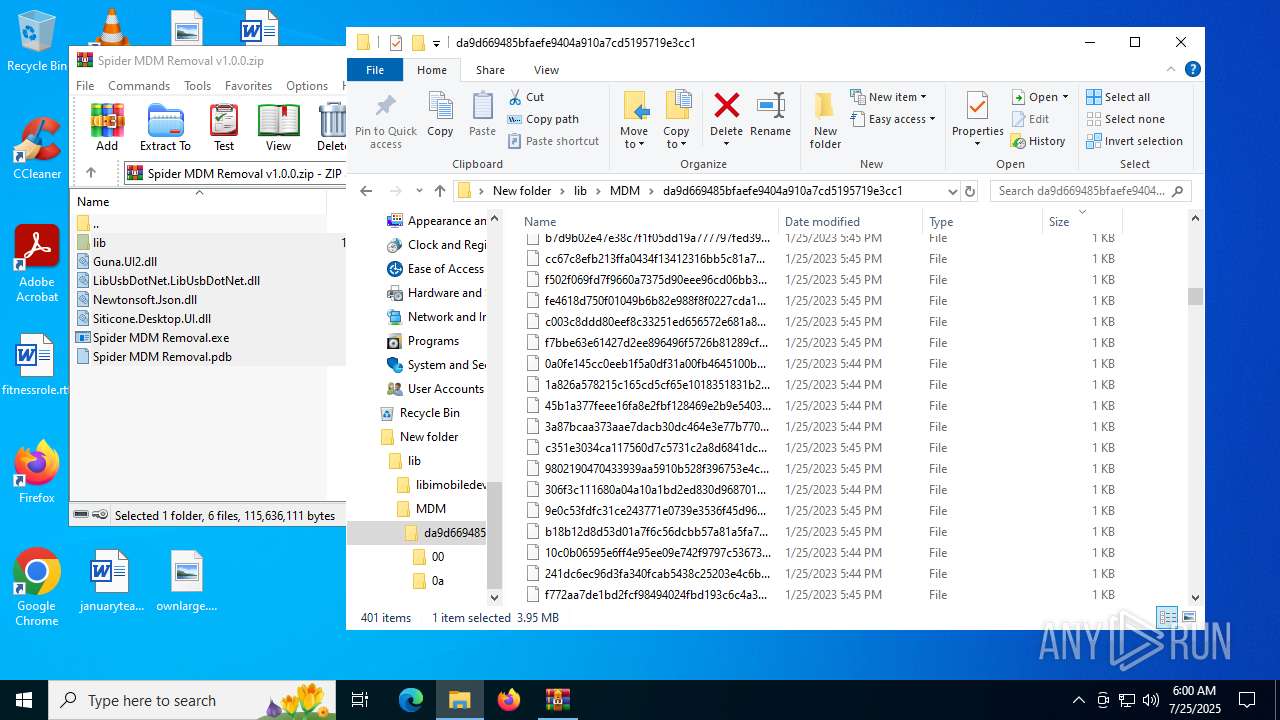
Executable files
94
Suspicious files
668
Text files
220
Unknown types
127
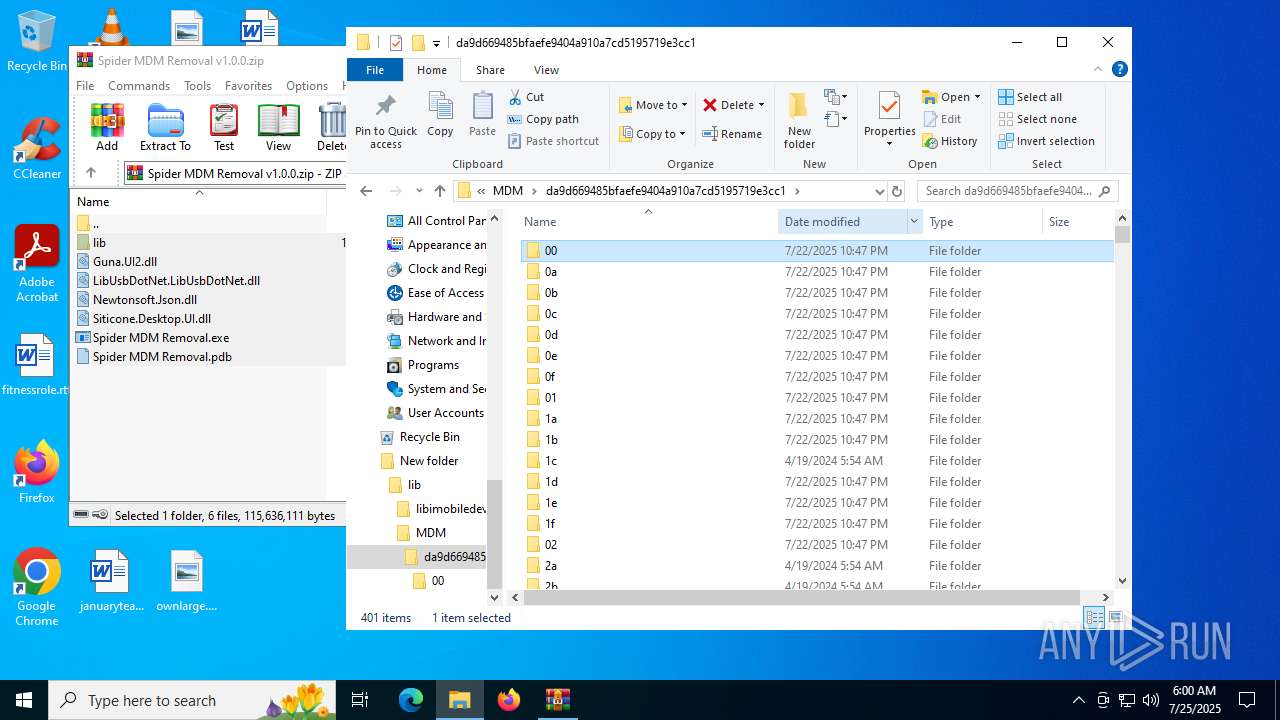
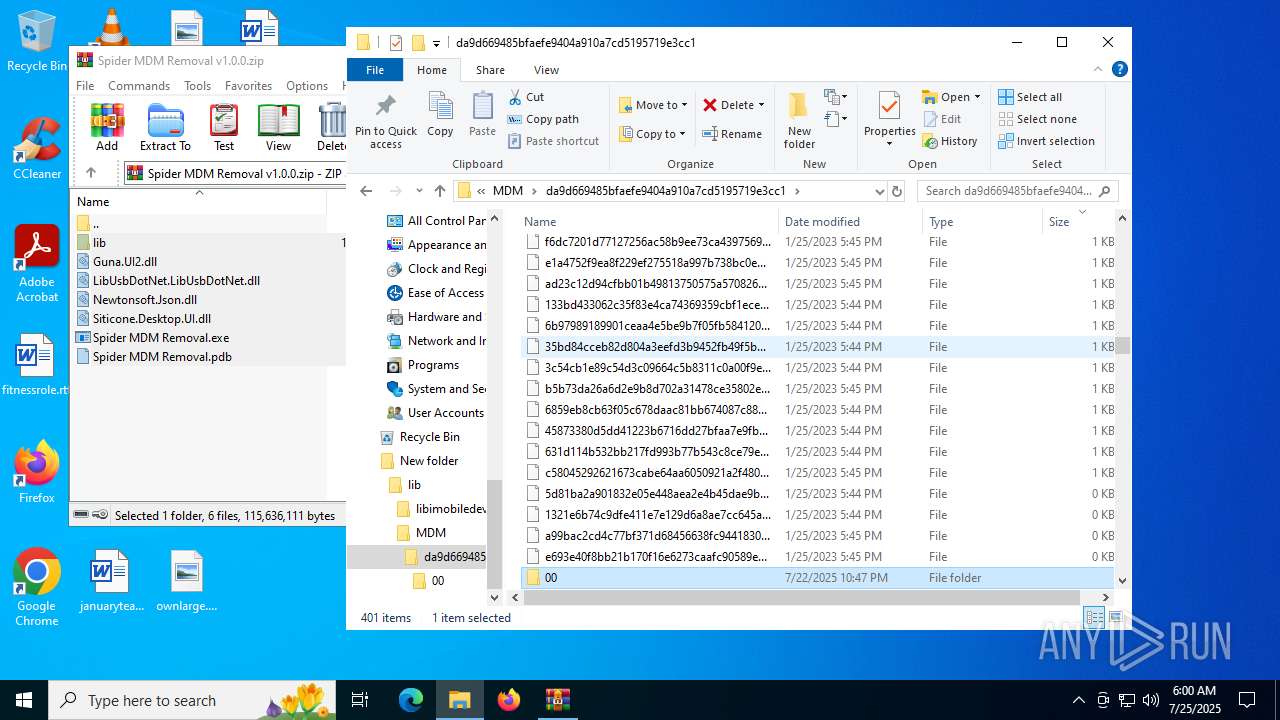
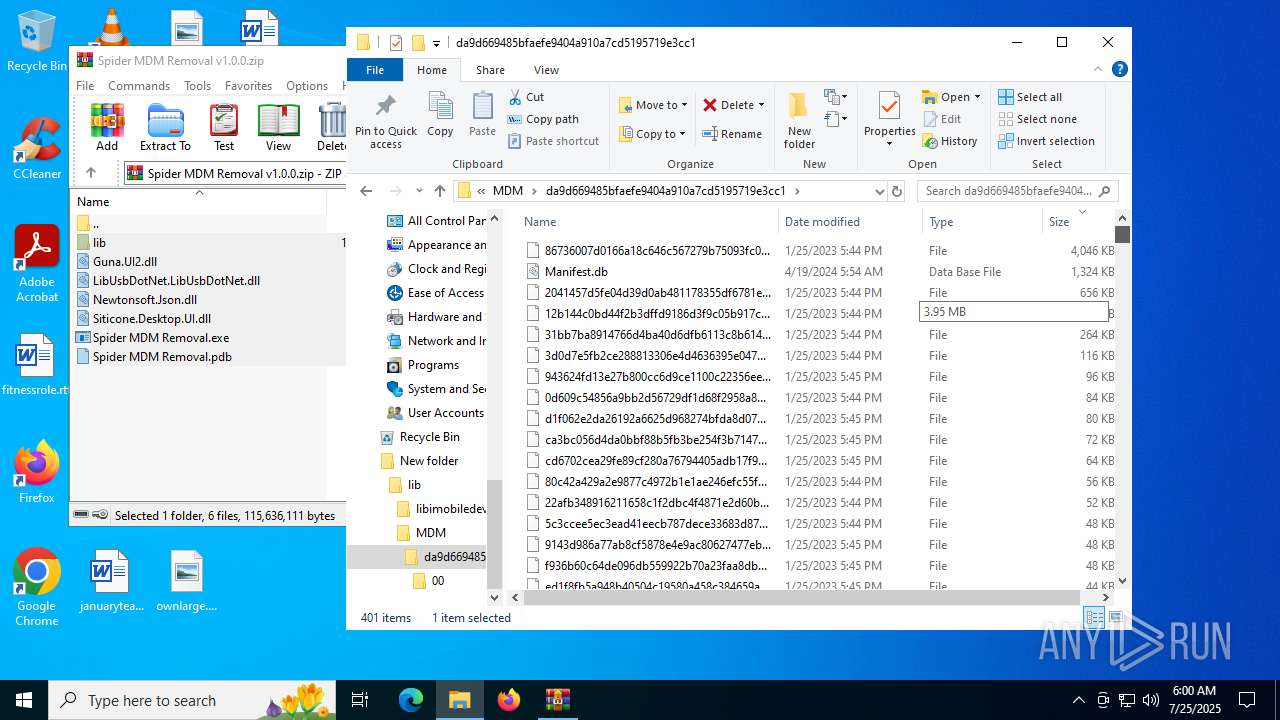
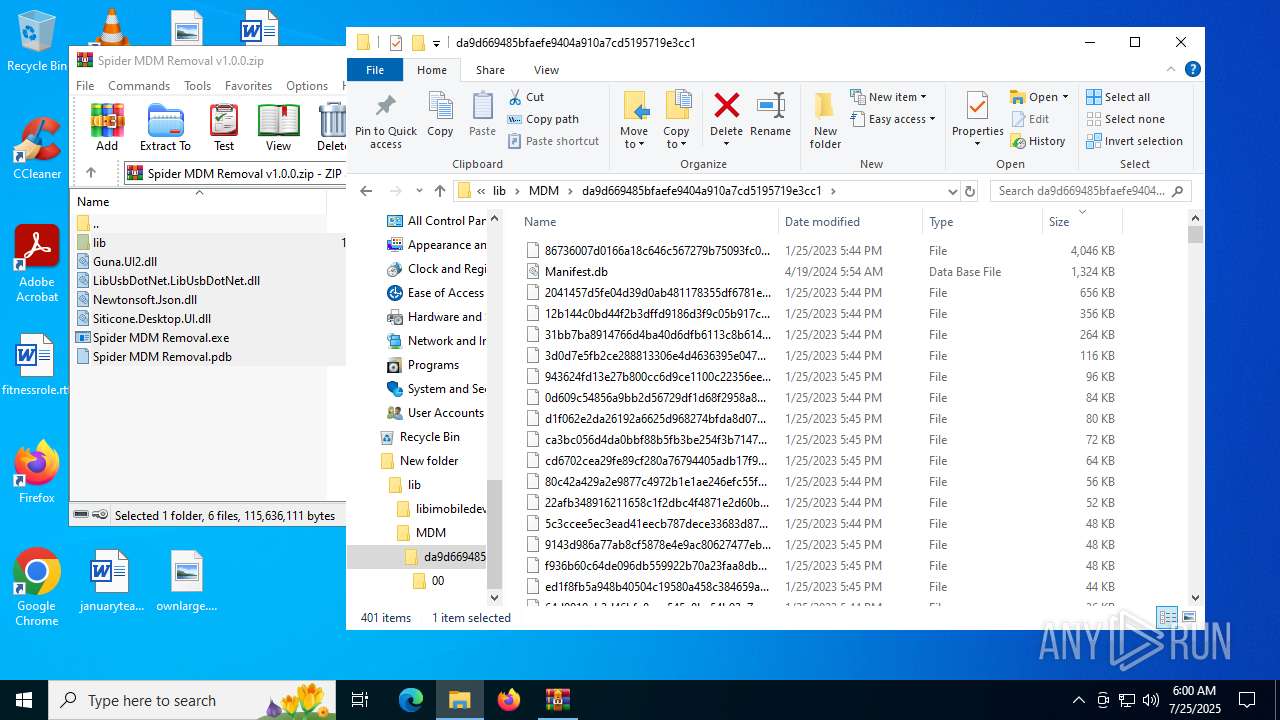
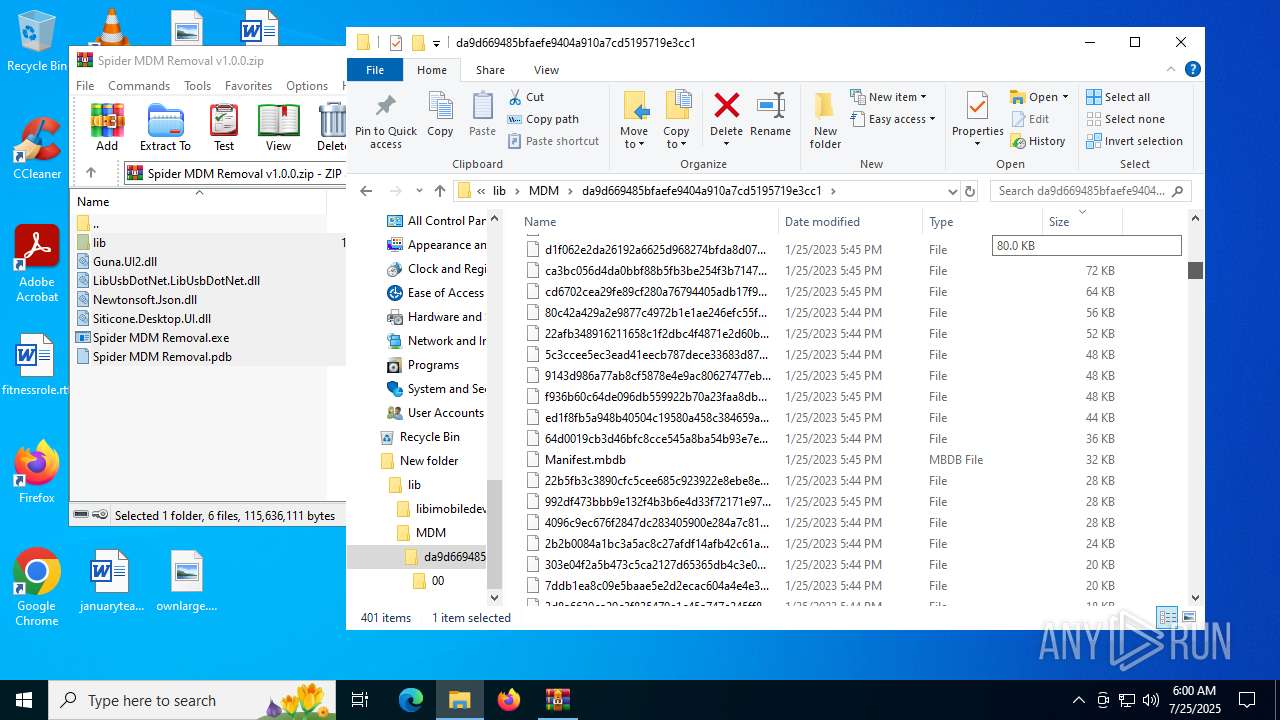
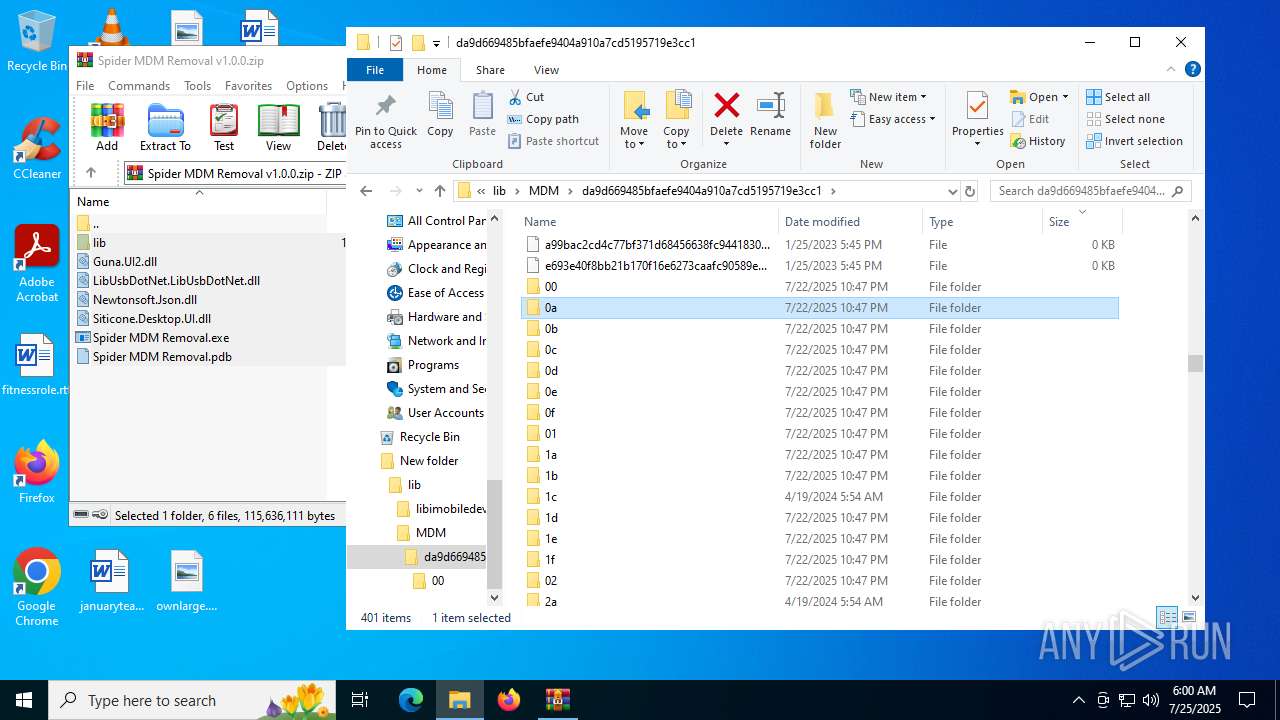
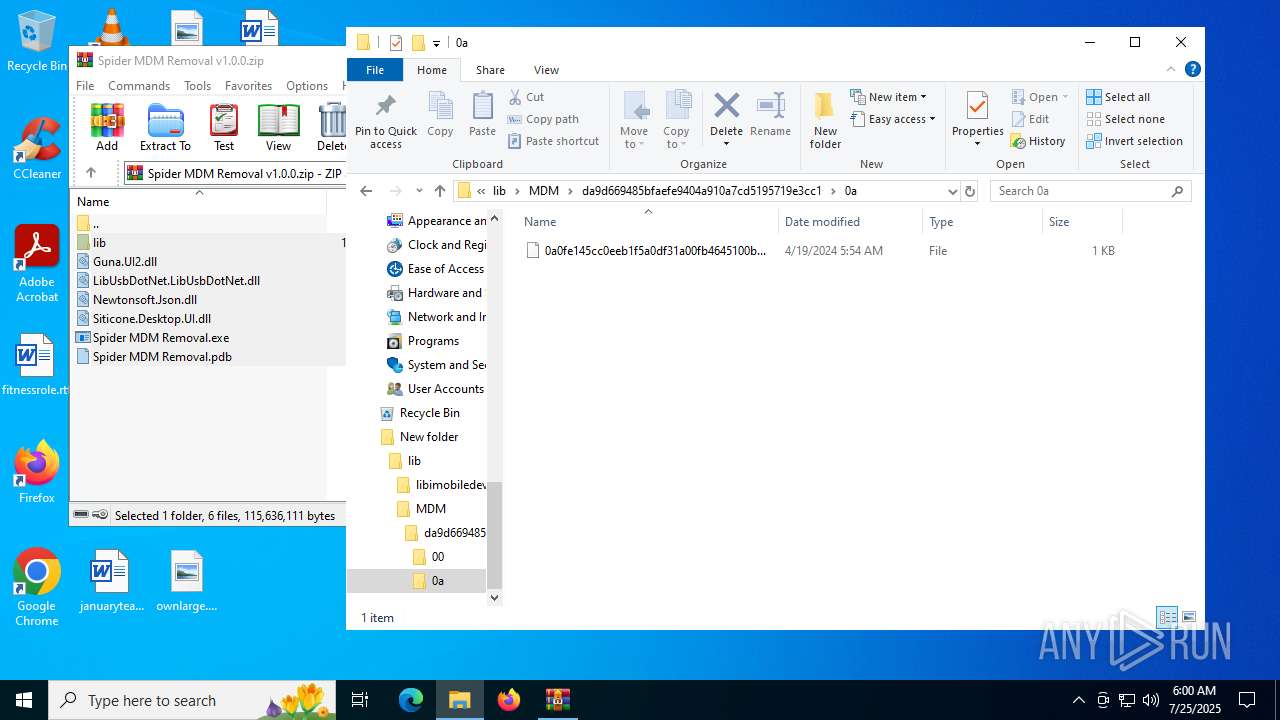
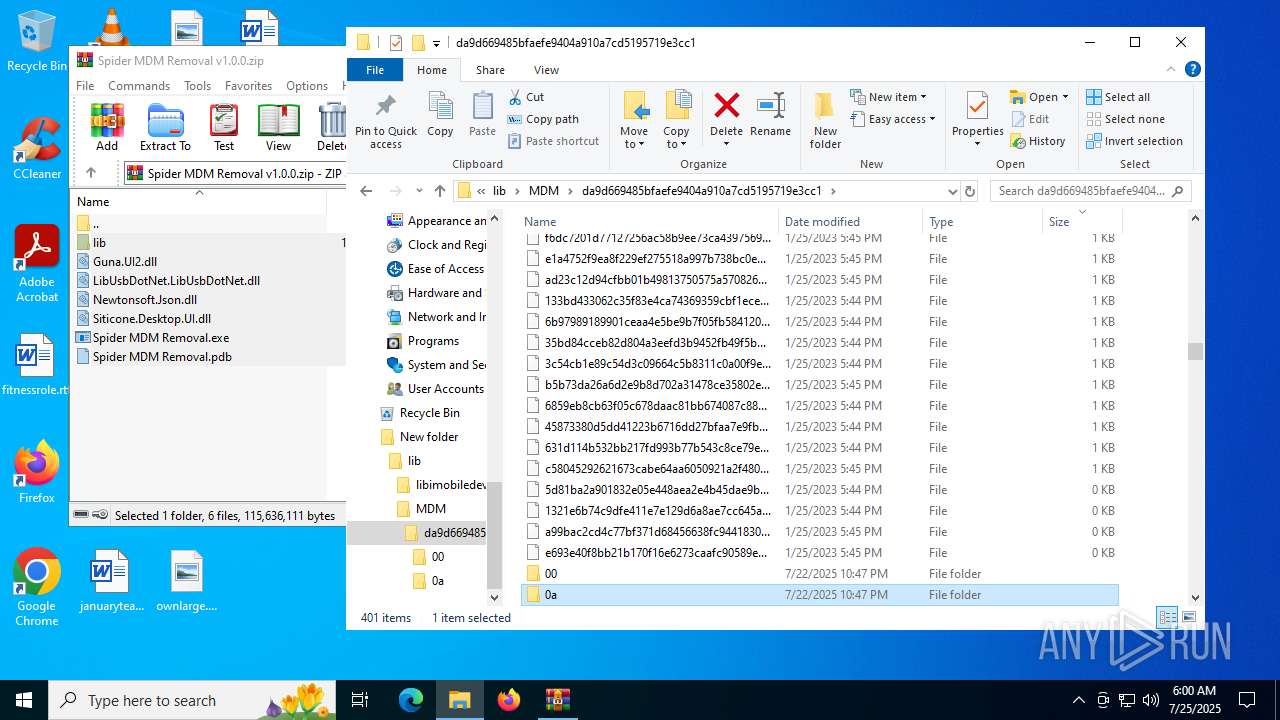
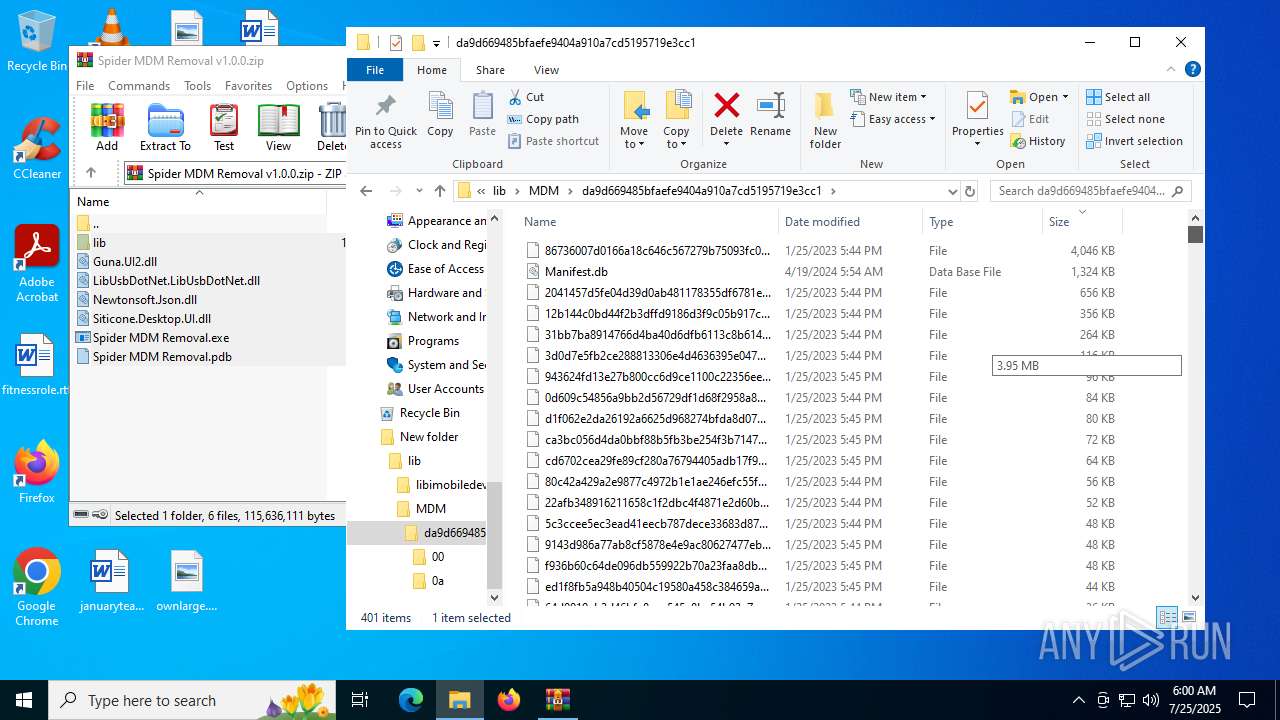
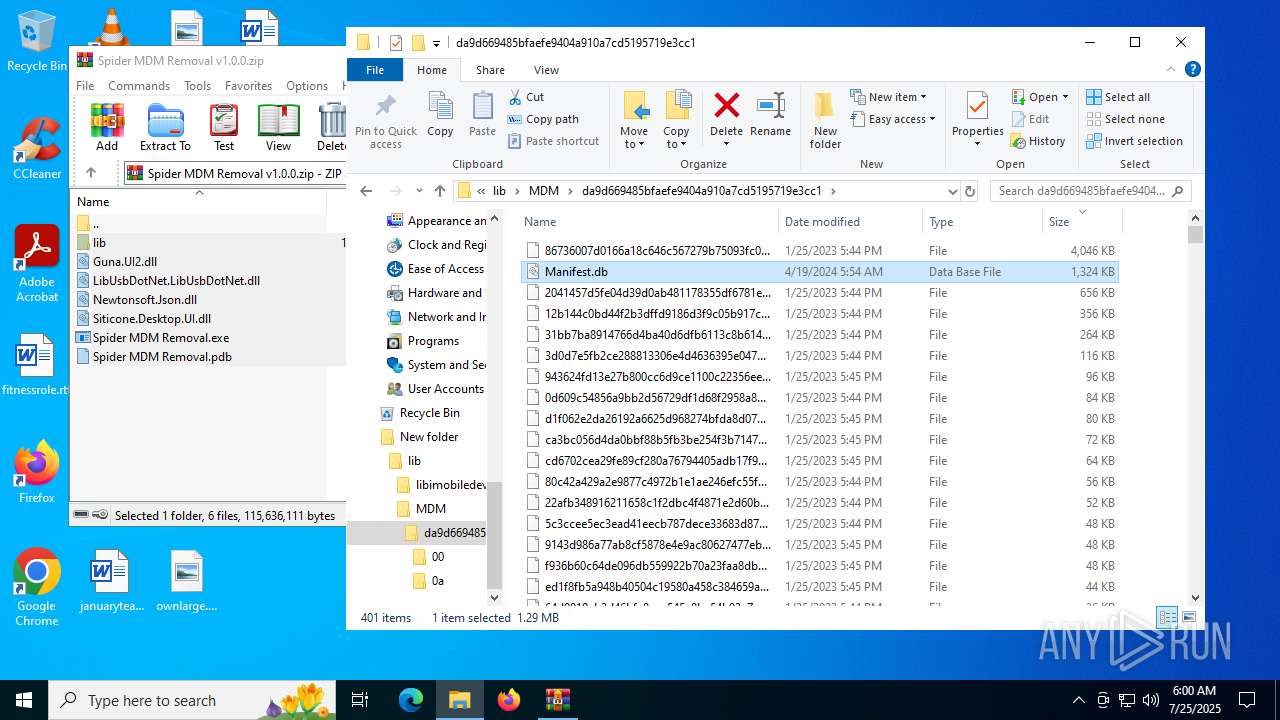
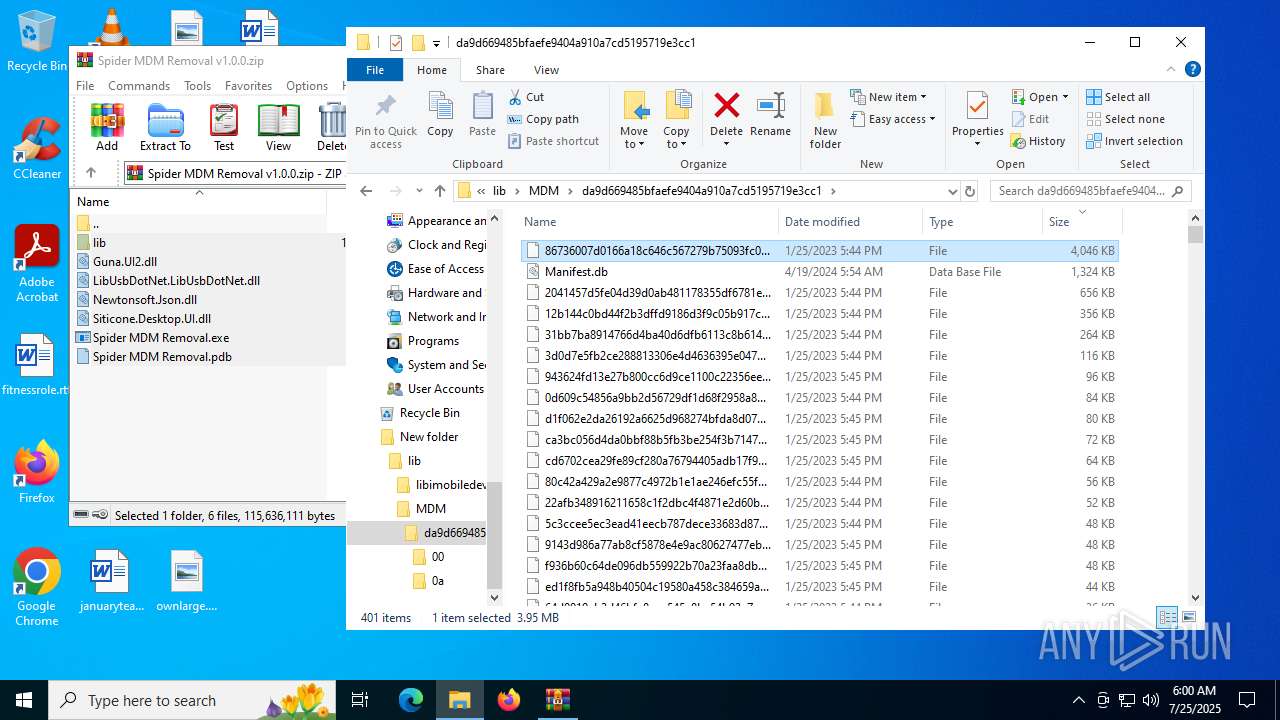
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18daab.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18daab.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18daab.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18dabb.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18daab.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
96
DNS requests
86
Threats
39
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5460 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:kk3Iy3VmBYyl84-70QCai2el1AD6AoRtrf55NuCFLTo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6936 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8176 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8176 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753768819&P2=404&P3=2&P4=H688hl9pMbC93BgPeoltbHKyQaJH8M7HRnbxI2sjFBf9s2mP2rzCyXfyrqRagkgt3KVEwq9T%2beW1waakVXNdZg%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753768819&P2=404&P3=2&P4=H688hl9pMbC93BgPeoltbHKyQaJH8M7HRnbxI2sjFBf9s2mP2rzCyXfyrqRagkgt3KVEwq9T%2beW1waakVXNdZg%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753768819&P2=404&P3=2&P4=H688hl9pMbC93BgPeoltbHKyQaJH8M7HRnbxI2sjFBf9s2mP2rzCyXfyrqRagkgt3KVEwq9T%2beW1waakVXNdZg%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3836 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5460 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5460 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5460 | msedge.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
5460 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5460 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mega.nz |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
eu.static.mega.co.nz |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
g.api.mega.co.nz |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5460 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
5460 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
5460 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
5460 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
5460 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
5460 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
5460 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
5460 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
5460 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
5460 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |