| File name: | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134 |
| Full analysis: | https://app.any.run/tasks/fc53e6d5-87c2-45c7-8c62-ac250c113383 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 14:28:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4301A568B394F99A59D48462F07F77C5 |
| SHA1: | 6785DF87500B8BF43CC5690E3643BA2FEB69707F |
| SHA256: | 81189195FBCE17284B30F36888945F04A332333F9BCD537D23ED7A49B1AF8134 |
| SSDEEP: | 98304:fFgjiEKlwM+V7zffvrioMD1HgUsctxkM0Tc54vqLg3WWunJoazTma5:fFb4V7L6D1TdCc2qLNWXa375 |
MALICIOUS
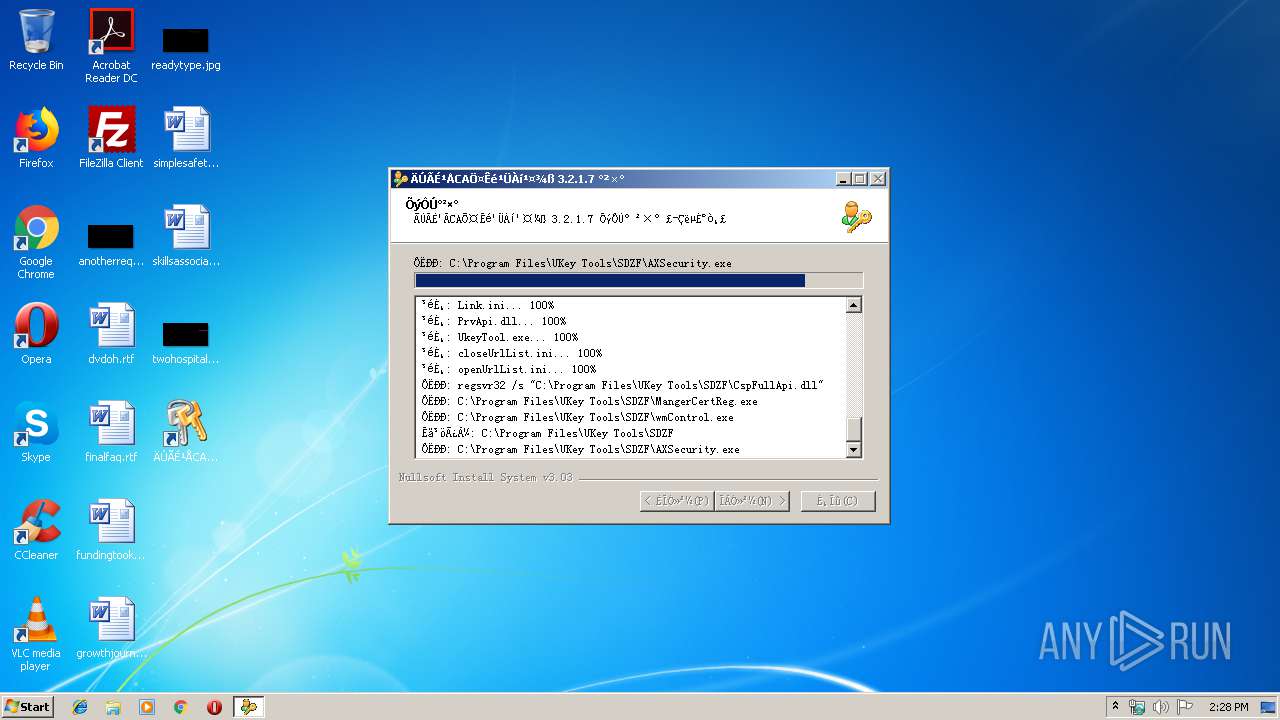
Loads dropped or rewritten executable
- 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe (PID: 1796)
- regsvr32.exe (PID: 3328)
- MangerCertReg.exe (PID: 3092)
- regsvr32.exe (PID: 3984)
Registers / Runs the DLL via REGSVR32.EXE
- 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe (PID: 1796)
- cmd.exe (PID: 3980)
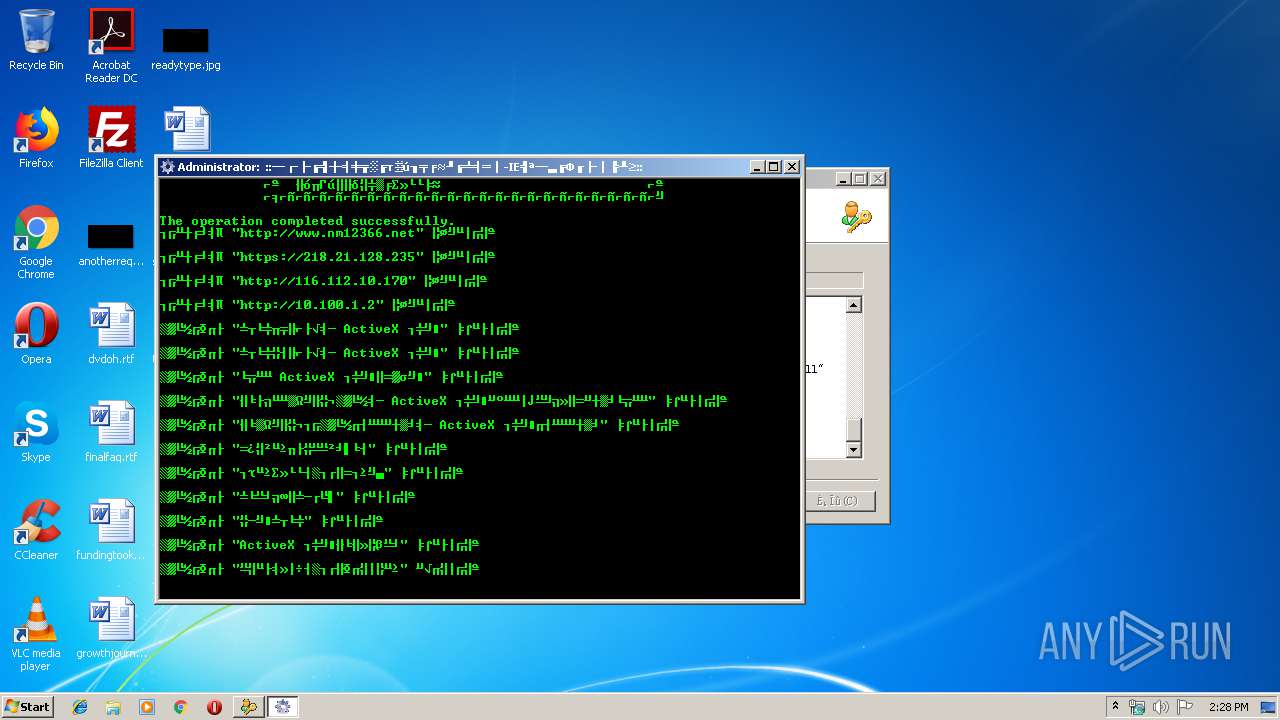
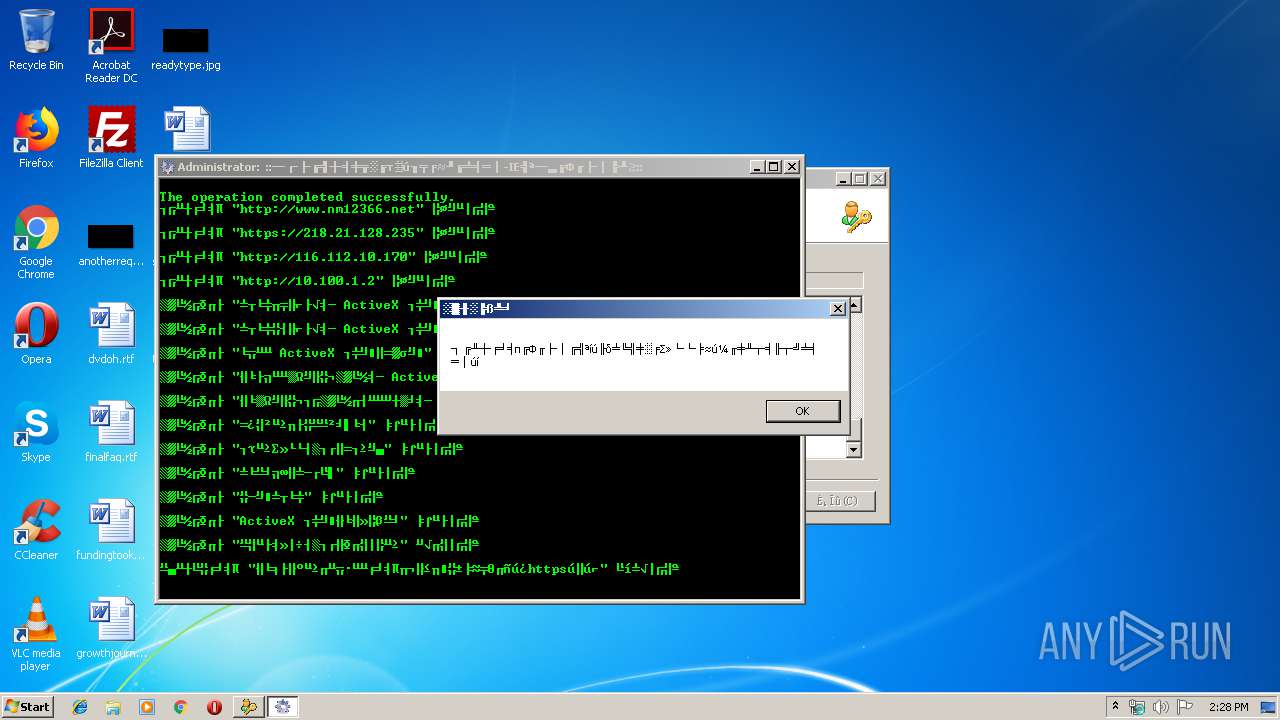
Changes settings of System certificates
- 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe (PID: 1796)
Application was dropped or rewritten from another process
- AXSecurity.exe (PID: 2716)
- MangerCertReg.exe (PID: 3092)
- Init_IE_Env.exe (PID: 2256)
- KeyMonitor.exe (PID: 1252)
- wmControl.exe (PID: 3844)
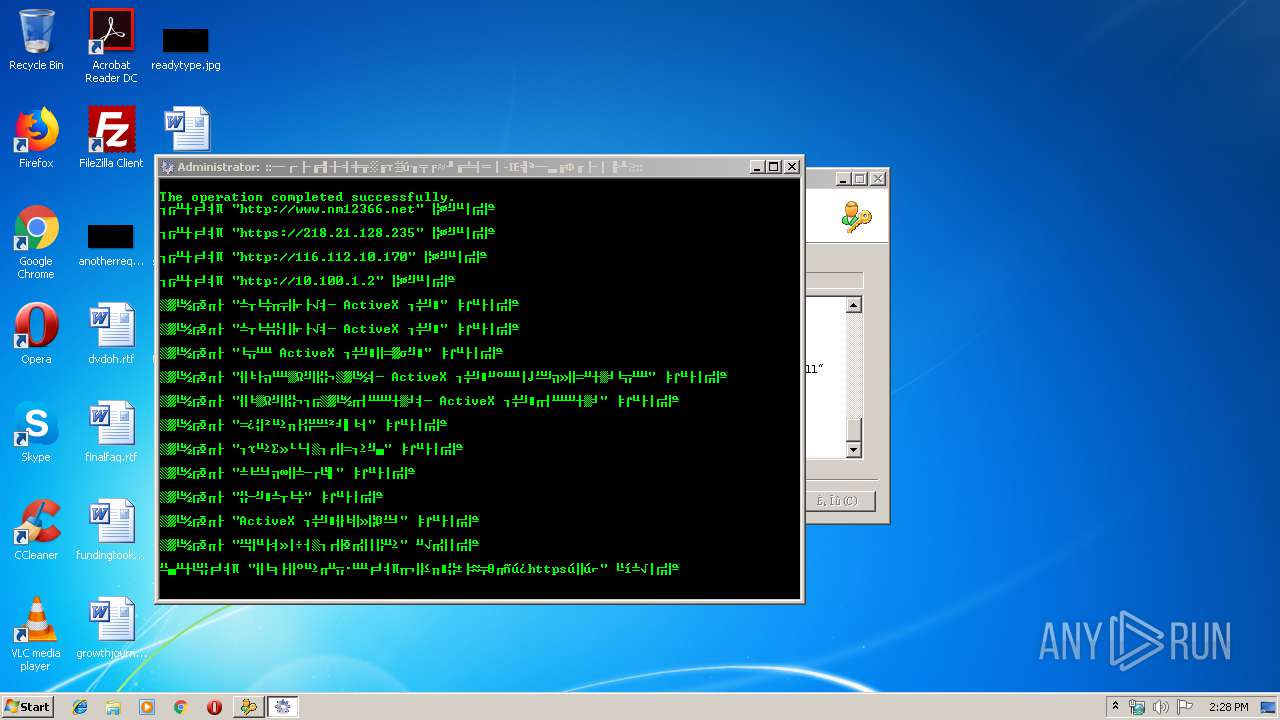
Changes internet zones settings
- reg.exe (PID: 4076)
- reg.exe (PID: 3736)
- reg.exe (PID: 3960)
- reg.exe (PID: 2308)
- reg.exe (PID: 1992)
- reg.exe (PID: 3276)
- reg.exe (PID: 1028)
- reg.exe (PID: 1036)
- reg.exe (PID: 3620)
- reg.exe (PID: 392)
- reg.exe (PID: 2392)
Changes the autorun value in the registry
- 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe (PID: 1796)
SUSPICIOUS
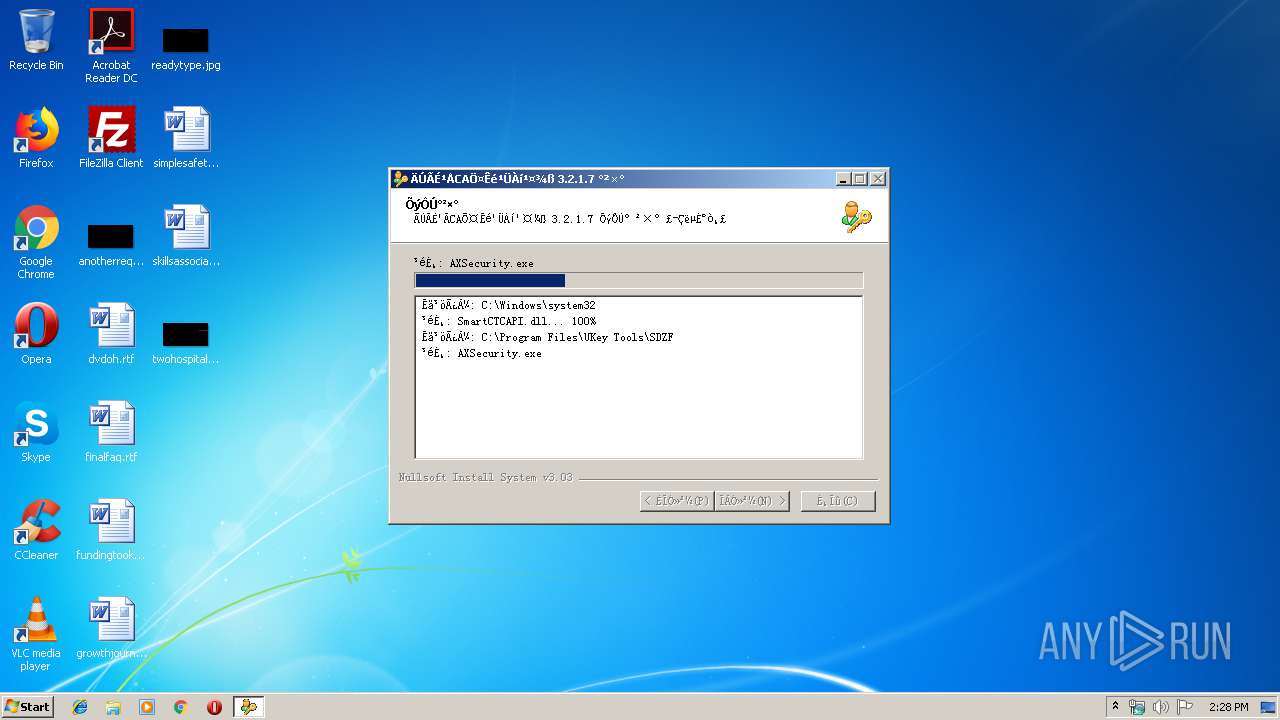
Creates files in the program directory
- 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe (PID: 1796)
- AXSecurity.exe (PID: 2716)
Executable content was dropped or overwritten
- 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe (PID: 1796)
- AXSecurity.exe (PID: 2716)
- cmd.exe (PID: 3980)
Creates files in the Windows directory
- 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe (PID: 1796)
- cmd.exe (PID: 3980)
Starts CMD.EXE for commands execution
- AXSecurity.exe (PID: 2716)
- Init_IE_Env.exe (PID: 2256)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2720)
Starts MSHTA.EXE for opening HTA or HTMLS files
- cmd.exe (PID: 2720)
Creates a software uninstall entry
- 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe (PID: 1796)
INFO
Dropped object may contain Bitcoin addresses
- 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe (PID: 1796)
Reads internet explorer settings
- mshta.exe (PID: 2088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:45+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x320c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
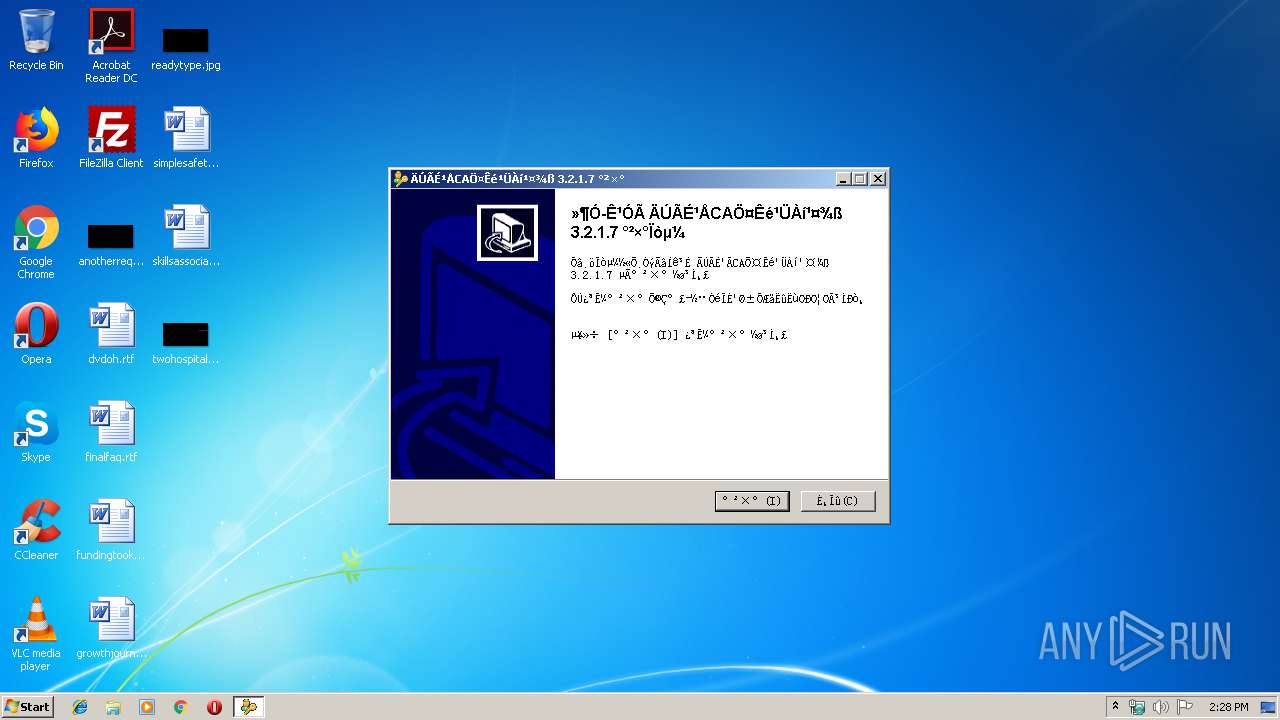
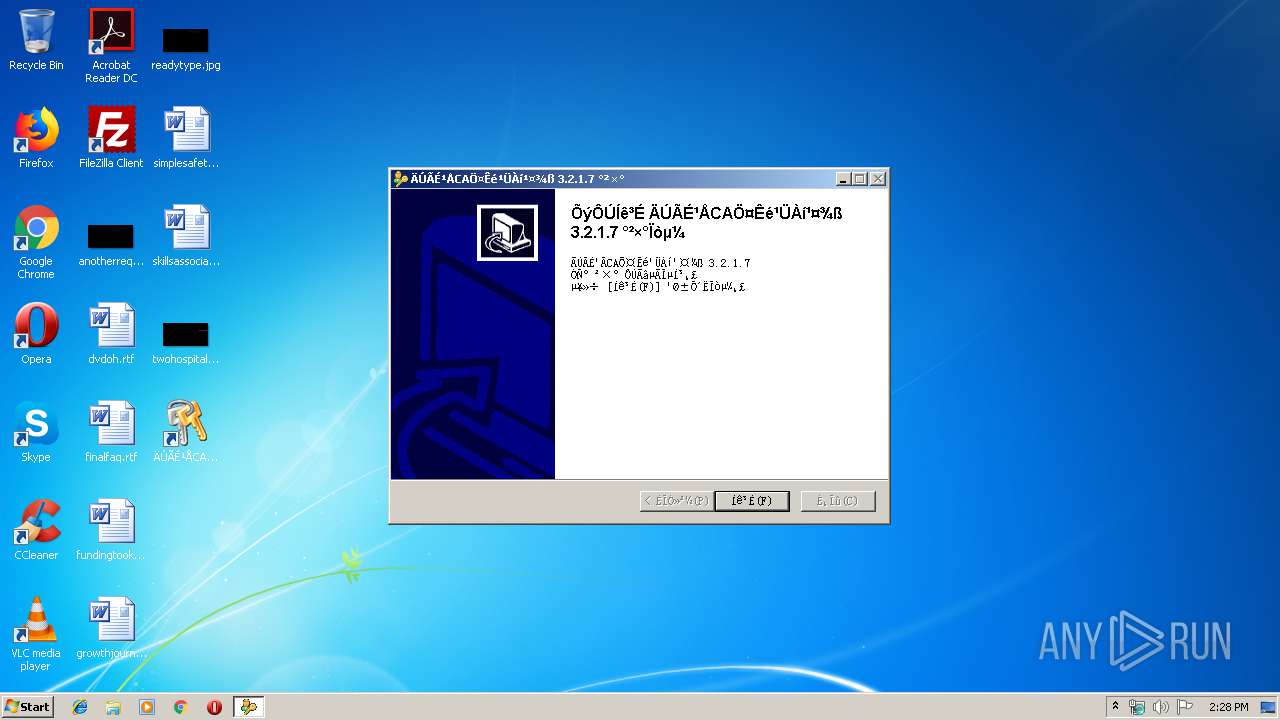
| FileVersionNumber: | 3.2.1.7 |
| ProductVersionNumber: | 3.2.1.7 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
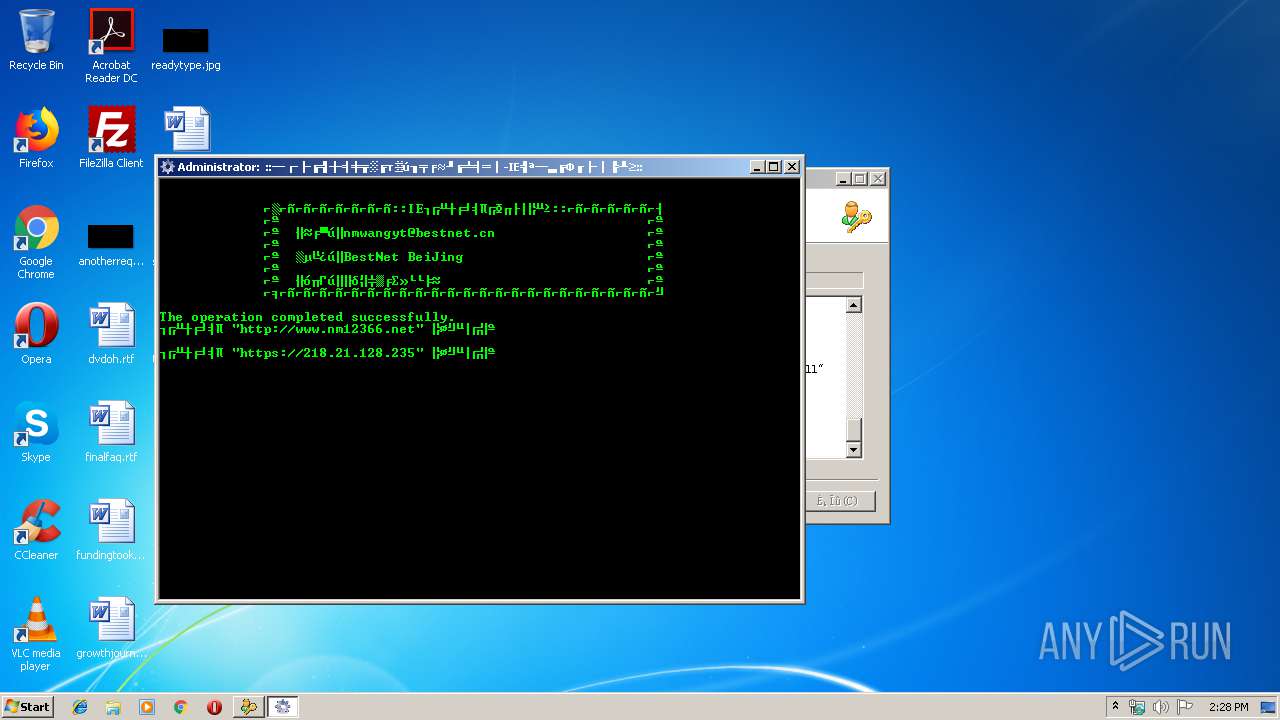
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| Comments: | For NMGCA |
| CompanyName: | 内蒙古CA证书管理工具 |
| FileDescription: | 内蒙古CA证书管理工具 |
| FileVersion: | 3.2.1.7 |
| LegalCopyright: | NMGCA |
| ProductName: | UKEY-MS |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:45 |
| Detected languages: |
|
| Comments: | For NMGCA |
| CompanyName: | 内蒙古CA证书管理工具 |
| FileDescription: | 内蒙古CA证书管理工具 |
| FileVersion: | 3.2.1.7 |
| LegalCopyright: | NMGCA |
| ProductName: | UKEY-MS |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000628F | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4422 |
.rdata | 0x00008000 | 0x00001354 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23627 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04938 |
.ndata | 0x00030000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x00001490 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.86939 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.5789 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68733 | 494 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
75
Monitored processes
36
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\New Windows" /v PopupMgr /t REG_SZ /d no /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2" /v 1004 /t REG_DWORD /d 0x00000000 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Ranges\Range101" /v :Range /t REG_SZ /d 218.21.128.235 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1028 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2" /v 1803 /t REG_DWORD /d 0x00000000 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2" /v 1609 /t REG_DWORD /d 0x00000000 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | "C:\Program Files\UKey Tools\SDZF\KeyMonitor.exe" | C:\Program Files\UKey Tools\SDZF\KeyMonitor.exe | — | MangerCertReg.exe | |||||||||||
User: admin Integrity Level: HIGH Description: key monitor build2017070501 Exit code: 0 Version: 3, 1, 1, 8 Modules
| |||||||||||||||
| 1412 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Ranges\Range103" /v http /t REG_DWORD /d 0x00000002 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\nm12366.net\www" /v http /t REG_DWORD /d 0x00000002 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1752 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Ranges\Range101" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1796 | "C:\Users\admin\AppData\Local\Temp\81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe" | C:\Users\admin\AppData\Local\Temp\81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | explorer.exe | ||||||||||||
User: admin Company: 内蒙古CA证书管理工具 Integrity Level: HIGH Description: 内蒙古CA证书管理工具 Exit code: 0 Version: 3.2.1.7 Modules
| |||||||||||||||
Total events
562
Read events
478
Write events
84
Delete events
0
Modification events
| (PID) Process: | (3328) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Defaults\Provider\Cute Cryptographic Provider v4.0.0.16 |
| Operation: | write | Name: | Image Path |
Value: C:\Program Files\UKey Tools\SDZF\CspFullApi.dll | |||
| (PID) Process: | (3328) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Defaults\Provider\Cute Cryptographic Provider v4.0.0.16 |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (3328) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Defaults\Provider\Cute Cryptographic Provider v4.0.0.16 |
| Operation: | write | Name: | SigInFile |
Value: 0 | |||
| (PID) Process: | (1796) 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\CA\Certificates\898E42061416FA4E8E8158CD90669FE1F980CB4E |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000898E42061416FA4E8E8158CD90669FE1F980CB4E2000000001000000A00200003082029C30820205A00302010202106EBA620E226F8833A41C6C62583CF174300D06092A864886F70D01010505003038310B300906035504061302434E3111300F060355040A1308416E58696E204341311630140603550403130D416E58696E20434120526F6F74301E170D3034303932333037343331385A170D3331303332323037343331385A3049310B300906035504061302434E310F300D060355040A13064E4D4720434131293027060355040313204E4D4720436572746966696361746520417574686F726974792043656E74657230819F300D06092A864886F70D010101050003818D0030818902818100C5120BECB938B945C417CDA389C3CFEDF71B734640846F70E2AB175DD1475A35A82716BEBE7F5EDDB0649046A78EA22D9BC30D1CFAA830F5D23967D62A6B1F6A81F34345231A4BABDD8D8E8BD97A51EAAD0A9A58249D91B076AD77EEA7145A7E99D0748B99A55CB8305EEB7D7FD9FB494C5E05510EAFFBE3952D5960ADE61B7F0203010001A38195308192301F0603551D230418301680147AD98AA7B94D04A1B7DB849A772F48AF4E12033B301D0603551D0E04160414587305F7344D366876A111C5DC9A92B84560B400300C0603551D130405300301010130420603551D1F043B30393037A035A0338631687474703A2F2F636F6E6E6563746F722E616E78696E63612E636F6D2F416E58696E526F6F7443726C2F63726C2E636C72300D06092A864886F70D0101050500038181001449F3F9BA7F8300274380F07AD4354A5052D24E3EC31D525D06AEED5E254A104AE4C92874E181BC0054ED6BF12B1AF6E5A98BC1EE21BAABDC34A7662FA71F53D18EB1641F6C209B9EA0F9E8DC5D025D9834DDF582FE3B6A8D977BDAA56F89DDEACB3687305A4C1326818914411C73A8A191B38A2B72333F356B097BF6A42784 | |||
| (PID) Process: | (1796) 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\CA\Certificates\0F486C0B9814304C17704B042746E17D11FF7061 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000000F486C0B9814304C17704B042746E17D11FF70612000000001000000B6030000308203B23082031BA00302010202101FE3CEA7A85562CFFFFD9EF7B48D6D42300D06092A864886F70D01010505003067310B300906035504061302434E3111300F060355040A1308416E58696E20434131183016060355040B130F7777772E616E78696E63612E636F6D312B302906035504031322416E58696E20436572746966696361746520417574686F7269747920436F2E4C7464301E170D3136303430313032323833345A170D3333303531323032323833345A3049310B300906035504061302434E310F300D060355040A13064E4D4720434131293027060355040313204E4D4720436572746966696361746520417574686F726974792043656E74657230819F300D06092A864886F70D010101050003818D0030818902818100AA0995AA659AB30C614D5C8933793E16C5D7E4F5A6EF58AAF18A77E92DAC8DBAC9DC045541909FFF94C9AF884D60EFDCCFB7B4FF1020FB0AA4F9AAA61F81421698390A1C32F15222FA5CAEA29C874B3063776B6DF7A6D659A69BEDDF9F51171B6837F584A5D4ECF28D7D647D0047892478BC7BC2B88967C11D7D7FBA5EF1E2BF0203010001A382017B30820177301F0603551D23041830168014D18D7DA5B979AE02120E6455D93017BA35958C60301D0603551D0E04160414BD926BBAC44F24038C9F82AFB9A47ED9E9546B86300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106308201120603551D1F04820109308201053044A042A040A43E303C310B300906035504061302434E310C300A060355040A13034A49543110300E060355040B13074144443243524C310D300B0603550403130463726C313037A035A0338631687474703A2F2F636F6E6E6563746F722E616E78696E63612E636F6D2F616E78696E72736163726C2F63726C312E63726C308183A08180A07E867C6C6461703A2F2F736D326C6461702E616E78696E63612E636F6D3A3339302F434E3D63726C312C4F553D4144443243524C2C4F3D4A49542C433D434E3F63657274696669636174655265766F636174696F6E4C6973743F626173653F6F626A656374636C6173733D63524C446973747269627574696F6E506F696E74300D06092A864886F70D010105050003818100BCD8D98395E742A94771707B68DD9919152EE8C0D26E673B22218910552D6539698F1A2DC5B1549F382DDD467AD39F103E7F21D20936285FA86646ACA24E25074AECF8035D4590557B5CC50005B8078C9F81FB714BF53FEBB30E0B9A910C354EC142116D7CA906AAA5E01DF5125E675B9FD7C102D4A5210D27FB4DA85C50C5AE | |||
| (PID) Process: | (1796) 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\CA\Certificates\30DEF716B6C10F58744D70130C06CF842CC94E83 |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000030DEF716B6C10F58744D70130C06CF842CC94E832000000001000000C6020000308202C230820267A003020102021073E70A73831702BB84AF24A9B007B1FE300C06082A811CCF5501837505003037310B300906035504061302434E3111300F060355040A0C08416E58696E2043413115301306035504030C0C416E58696E20534D32204341301E170D3136303332353036303235345A170D3333303632343036303235345A3033310B300906035504061302434E310F300D060355040A13064E4D47204341311330110603550403130A4E4D4720534D322043413059301306072A8648CE3D020106082A811CCF5501822D034200040D207F8AD9DB2D2F0388254299B4FC0E3FF414A656C71A3A24EB8DCE94664E64D4643618B29EBDD6016F3EFB1ED123873258D064576A03434B5773C9DD7876C0A382015530820151301F0603551D23041830168014BB7FF95E3869F8596709AA77E1C6830418E90115301D0603551D0E04160414E8AFFFC65C99A75163775ACEEEA6DB763DCBCF10300F0603551D130101FF040530030101FF300E0603551D0F0101FF0404030201063081ED0603551D1F0481E53081E23032A030A02EA42C302A310B300906035504061302434E310C300A060355040B130343524C310D300B0603550403130463726C313032A030A02E862C687474703A2F2F636F6E6E6563746F722E616E78696E63612E636F6D2F736D3263726C2F63726C312E63726C3078A076A07486726C6461703A2F2F736D326C6461702E616E78696E63612E636F6D3A3339302F434E3D63726C312C4F553D43524C2C433D434E3F63657274696669636174655265766F636174696F6E4C6973743F626173653F6F626A656374636C6173733D63524C446973747269627574696F6E506F696E74300C06082A811CCF5501837505000347003044022006E3E32D3515FBF80FE0CDAF75F5E37186377B6CA3D923F1AAB7433F1B26B03902205AEF77104B16F6A64A658FCFC8EC54101CC5EDB1A64D92955FA50ACC502B7354 | |||
| (PID) Process: | (1796) 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\CA\Certificates\AB58A10404967D21D3912DFBD29C4304D8AF4DB2 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000AB58A10404967D21D3912DFBD29C4304D8AF4DB220000000010000008E0200003082028A3082022FA003020102021076756E291181250671EAC079853625DC300C06082A811CCF550183750500302E310B300906035504061302434E310E300C060355040A0C054E52434143310F300D06035504030C06524F4F544341301E170D3133303830393032303632325A170D3333303830343032303632325A3037310B300906035504061302434E3111300F060355040A0C08416E58696E2043413115301306035504030C0C416E58696E20534D322043413059301306072A8648CE3D020106082A811CCF5501822D034200040EA97A42C7E0812A20FC19C15C3CFEAE1989A4876A1F86672457E52F0E2C43B6267623C46FD1766B215369045CD2F5AFA2F45B07D02C71E9CA7682DDFA551991A38201223082011E301F0603551D230418301680144C32B197D9331BC4A605C1C6E58B625BF0977658300F0603551D130101FF040530030101FF3081BA0603551D1F0481B23081AF3041A03FA03DA43B3039310B300906035504061302434E310E300C060355040A0C054E52434143310C300A060355040B0C0341524C310C300A06035504030C0361726C302AA028A0268624687474703A2F2F7777772E726F6F7463612E676F762E636E2F61726C2F61726C2E63726C303EA03CA03A86386C6461703A2F2F6C6461702E726F6F7463612E676F762E636E3A3338392F434E3D61726C2C4F553D41524C2C4F3D4E524341432C433D434E300E0603551D0F0101FF040403020106301D0603551D0E04160414BB7FF95E3869F8596709AA77E1C6830418E90115300C06082A811CCF55018375050003470030440220800B89F411ED47C08BB286D4DAD1D13B8EE0C7B864670ADA1205BBA336816C9802202B7F2A110CFCB0FD330BA1407C49C91901AA905891D6295B78C0F04BDEF4FA65 | |||
| (PID) Process: | (1796) 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\CA\Certificates\0605B626168A7A785D37B978B2D7210585D88FD9 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000000605B626168A7A785D37B978B2D7210585D88FD92000000001000000B7010000308201B330820157A003020102020869E2FEC0170AC67B300C06082A811CCF550183750500302E310B300906035504061302434E310E300C060355040A0C054E52434143310F300D06035504030C06524F4F544341301E170D3132303731343033313135395A170D3432303730373033313135395A302E310B300906035504061302434E310E300C060355040A0C054E52434143310F300D06035504030C06524F4F5443413059301306072A8648CE3D020106082A811CCF5501822D0342000430F09C6BAA6681C721B137F652705E2FDAEDA789F0FA2B64D4ACEB99B9EAA34E655309309562BEE0E22BB45740AA745357B43DBF586D92FE364EC22EB73775DBA35D305B301F0603551D230418301680144C32B197D9331BC4A605C1C6E58B625BF0977658300C0603551D13040530030101FF300B0603551D0F040403020106301D0603551D0E041604144C32B197D9331BC4A605C1C6E58B625BF0977658300C06082A811CCF550183750500034800304502201B56D22DE397A77A01F07EDBE775BE08A38F9763E49E6584ABF94C86D9F6E479022100DA1C3816C5616D9C2AC18C7D7AFD6DC4CE7EFF53F563A39C48A43A22561B0BC2 | |||
| (PID) Process: | (1796) 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\AB58A10404967D21D3912DFBD29C4304D8AF4DB2 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000AB58A10404967D21D3912DFBD29C4304D8AF4DB220000000010000008E0200003082028A3082022FA003020102021076756E291181250671EAC079853625DC300C06082A811CCF550183750500302E310B300906035504061302434E310E300C060355040A0C054E52434143310F300D06035504030C06524F4F544341301E170D3133303830393032303632325A170D3333303830343032303632325A3037310B300906035504061302434E3111300F060355040A0C08416E58696E2043413115301306035504030C0C416E58696E20534D322043413059301306072A8648CE3D020106082A811CCF5501822D034200040EA97A42C7E0812A20FC19C15C3CFEAE1989A4876A1F86672457E52F0E2C43B6267623C46FD1766B215369045CD2F5AFA2F45B07D02C71E9CA7682DDFA551991A38201223082011E301F0603551D230418301680144C32B197D9331BC4A605C1C6E58B625BF0977658300F0603551D130101FF040530030101FF3081BA0603551D1F0481B23081AF3041A03FA03DA43B3039310B300906035504061302434E310E300C060355040A0C054E52434143310C300A060355040B0C0341524C310C300A06035504030C0361726C302AA028A0268624687474703A2F2F7777772E726F6F7463612E676F762E636E2F61726C2F61726C2E63726C303EA03CA03A86386C6461703A2F2F6C6461702E726F6F7463612E676F762E636E3A3338392F434E3D61726C2C4F553D41524C2C4F3D4E524341432C433D434E300E0603551D0F0101FF040403020106301D0603551D0E04160414BB7FF95E3869F8596709AA77E1C6830418E90115300C06082A811CCF55018375050003470030440220800B89F411ED47C08BB286D4DAD1D13B8EE0C7B864670ADA1205BBA336816C9802202B7F2A110CFCB0FD330BA1407C49C91901AA905891D6295B78C0F04BDEF4FA65 | |||
| (PID) Process: | (1796) 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\68070B9B7A5ADE3C267EF0393CD6EA24DFA27FA9 |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000068070B9B7A5ADE3C267EF0393CD6EA24DFA27FA920000000010000001A040000308204163082037FA0030201020210668FD1A163061D16E5D22D6774BDED32300D06092A864886F70D01010505003067310B300906035504061302434E3111300F060355040A1308416E58696E20434131183016060355040B130F7777772E616E78696E63612E636F6D312B302906035504031322416E58696E20436572746966696361746520417574686F7269747920436F2E4C7464301E170D3136303332353036323830315A170D3333303632343036323830315A3067310B300906035504061302434E3111300F060355040A1308416E58696E20434131183016060355040B130F7777772E616E78696E63612E636F6D312B302906035504031322416E58696E20436572746966696361746520417574686F7269747920436F2E4C746430819F300D06092A864886F70D010101050003818D0030818902818100C1F987F0389906033B4CCF37443242332599D6CD34F7B3D33A4B5F0DEFEDAFB7FBD3145F6AE93AA66A1C2B09338507F41EC13D13D7E52688F9D4384D1185E72B2A6FEC6BE6711348137BF593202277ED929EF2ABC5E449E25959B03C16145E3B8163922FF158AE8BE03D9937640A2E798D625EB2F7319EF518969132FC9148F90203010001A38201C1308201BD308201580603551D1F0482014F3082014B3081B5A042A040A43E303C310B300906035504061302434E310C300A060355040A13034A49543110300E060355040B13074144443243524C310D300B0603550403130443524C31810201EEA26BA4693067310B300906035504061302434E3111300F060355040A1308416E58696E20434131183016060355040B130F7777772E616E78696E63612E636F6D312B302906035504031322416E58696E20436572746966696361746520417574686F7269747920436F2E4C7464308190A01DA01B8619687474703A2F2F3132372E302E302E312F63726C312E63726C810201EEA26BA4693067310B300906035504061302434E3111300F060355040A1308416E58696E20434131183016060355040B130F7777772E616E78696E63612E636F6D312B302906035504031322416E58696E20436572746966696361746520417574686F7269747920436F2E4C7464300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414D18D7DA5B979AE02120E6455D93017BA35958C60301F0603551D23041830168014D18D7DA5B979AE02120E6455D93017BA35958C60300D06092A864886F70D0101050500038181002BC40800D6CA8CB6285CAD67CAFABD1C3D3E60DC8A57CCB6625CBA07FF1B27439EC471AFF72F88A06862394C7E9293C6FCBCAF28023EC9AF4E6E7CDD14D25C3354AD71CC0BA66119C8C5ED963329E354568C994A23CB91258EBB386CD586F09656C3EA625E1046D7D173F83585B71AA2A452FB33E9776878A215975C241410DB | |||
Executable files
48
Suspicious files
2
Text files
45
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1796 | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | C:\Users\admin\AppData\Local\Temp\nshB2E0.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 1796 | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | C:\Program Files\UKey Tools\SDZF\AnXin SM2 CA.cer | der | |
MD5:— | SHA256:— | |||
| 1796 | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | C:\Windows\system32\SmartCTCAPI.dll | executable | |
MD5:— | SHA256:— | |||
| 1796 | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | C:\Program Files\UKey Tools\SDZF\AXSecurity.exe | executable | |
MD5:— | SHA256:— | |||
| 1796 | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | C:\Program Files\UKey Tools\SDZF\AnXin Certificate Authority Co.Ltd.cer | der | |
MD5:— | SHA256:— | |||
| 1796 | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | C:\Program Files\UKey Tools\SDZF\CertOperApi.dll | executable | |
MD5:— | SHA256:— | |||
| 1796 | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | C:\Users\admin\AppData\Local\Temp\nshB2E0.tmp\FindProcDLL.dll | executable | |
MD5:8614C450637267AFACAD1645E23BA24A | SHA256:0FA04F06A6DE18D316832086891E9C23AE606D7784D5D5676385839B21CA2758 | |||
| 1796 | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | C:\Users\admin\AppData\Local\Temp\nshB2E0.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 1796 | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | C:\Users\admin\AppData\Local\Temp\nshB2E0.tmp\KillProcDLL.dll | executable | |
MD5:99F345CF51B6C3C317D20A81ACB11012 | SHA256:C2689BA1F66066AFCE85CA6457ECD36370BE0FE351C58422E45EFD0948655C93 | |||
| 1796 | 81189195fbce17284b30f36888945f04a332333f9bcd537d23ed7a49b1af8134.exe | C:\Users\admin\AppData\Local\Temp\nshB2E0.tmp\InstallOptions.dll | executable | |
MD5:8D5A5529462A9BA1AC068EE0502578C7 | SHA256:E625DCD0188594B1289891B64DEBDDEB5159ACA182B83A12675427B320BF7790 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report