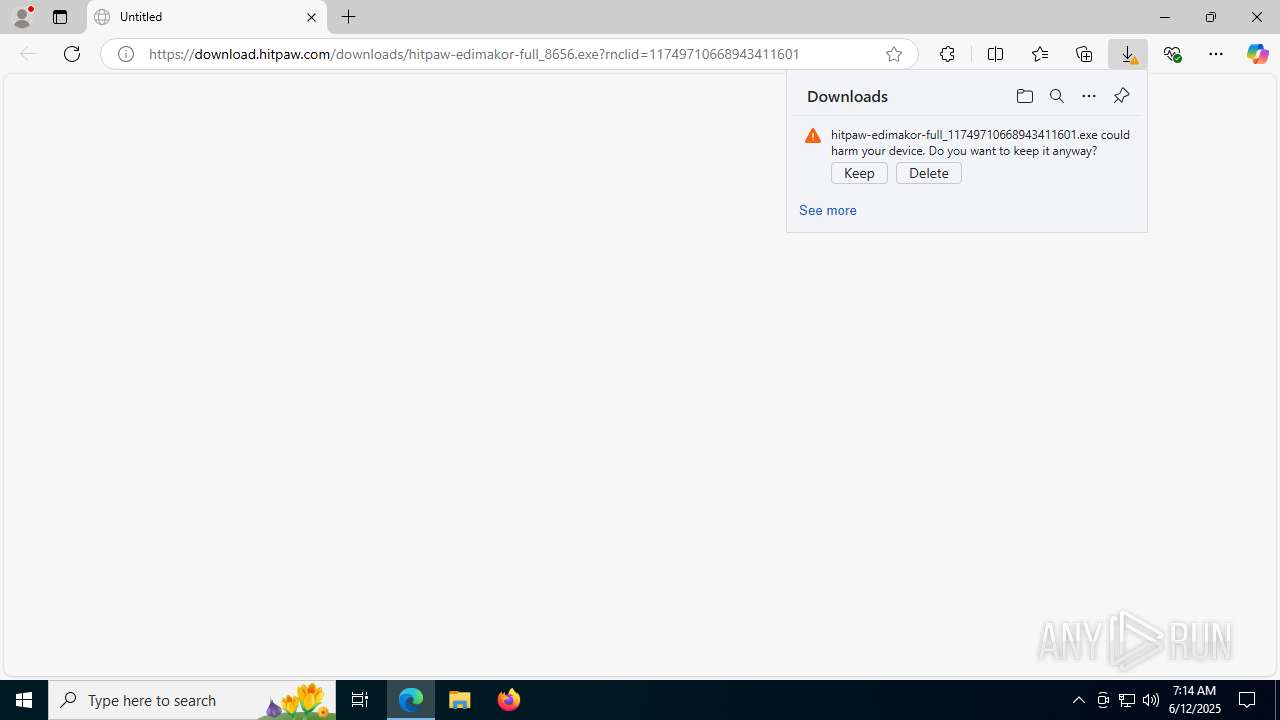
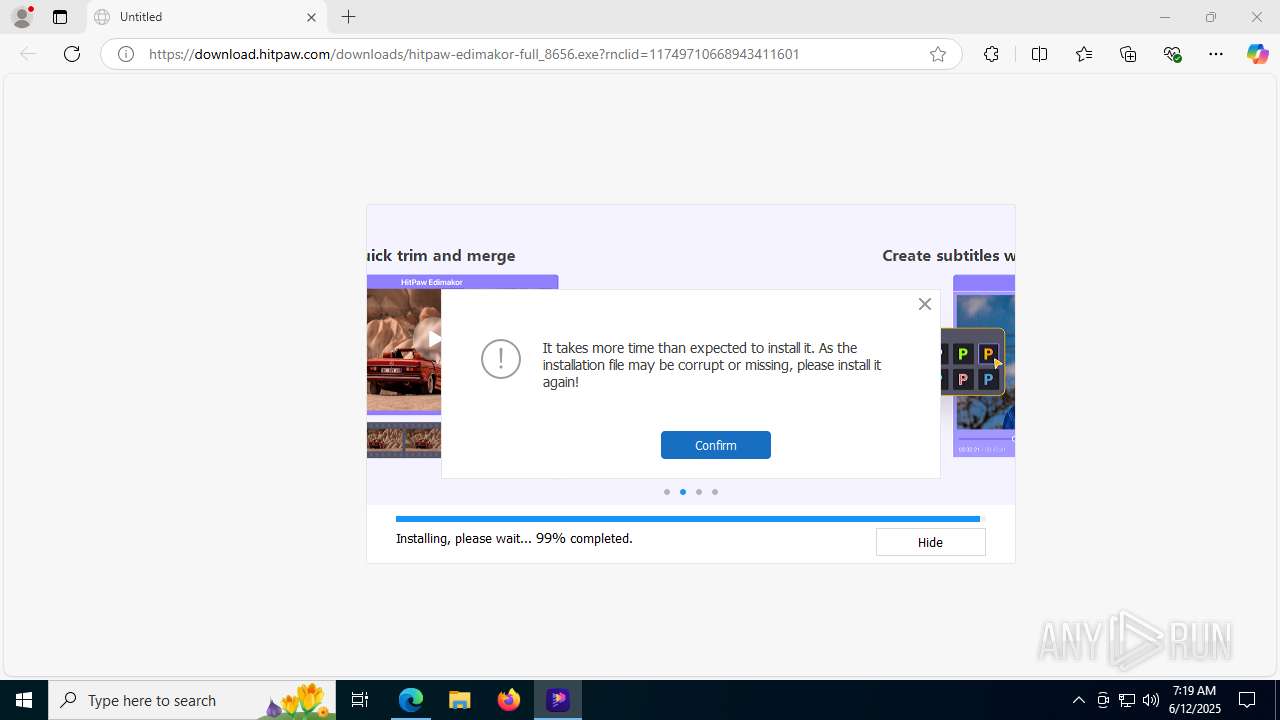
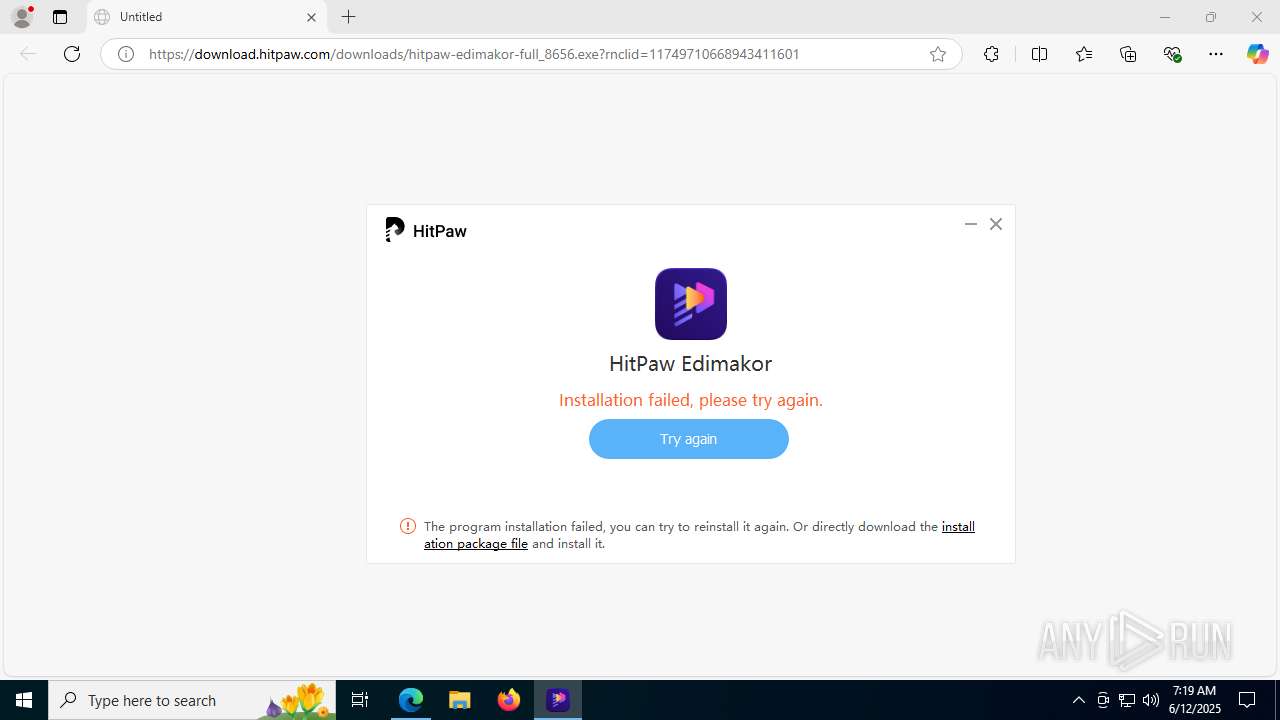
| URL: | https://download.hitpaw.com/downloads/hitpaw-edimakor-full_8656.exe?rnclid=11749710668943411601 |
| Full analysis: | https://app.any.run/tasks/edc83122-03b8-468d-ae9d-7593aaf2bab6 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2025, 07:14:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CD7036B09BE6BCC2DD55033BB28A86D4 |
| SHA1: | 9EFBDD08CA9B1075ADE756414B07AC3282B94ACC |
| SHA256: | 811638D1F3E5899914038245BFF5EB4E7CF9719F464253CE50B57E9C890931B0 |
| SSDEEP: | 3:N8SElpXKePUYD32gdjGJMnRcSS6WjU:2SKpaeMYD3Ry56v |
MALICIOUS
No malicious indicators.SUSPICIOUS
Potential Corporate Privacy Violation
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
Checks for external IP
- svchost.exe (PID: 2200)
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
Reads security settings of Internet Explorer
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
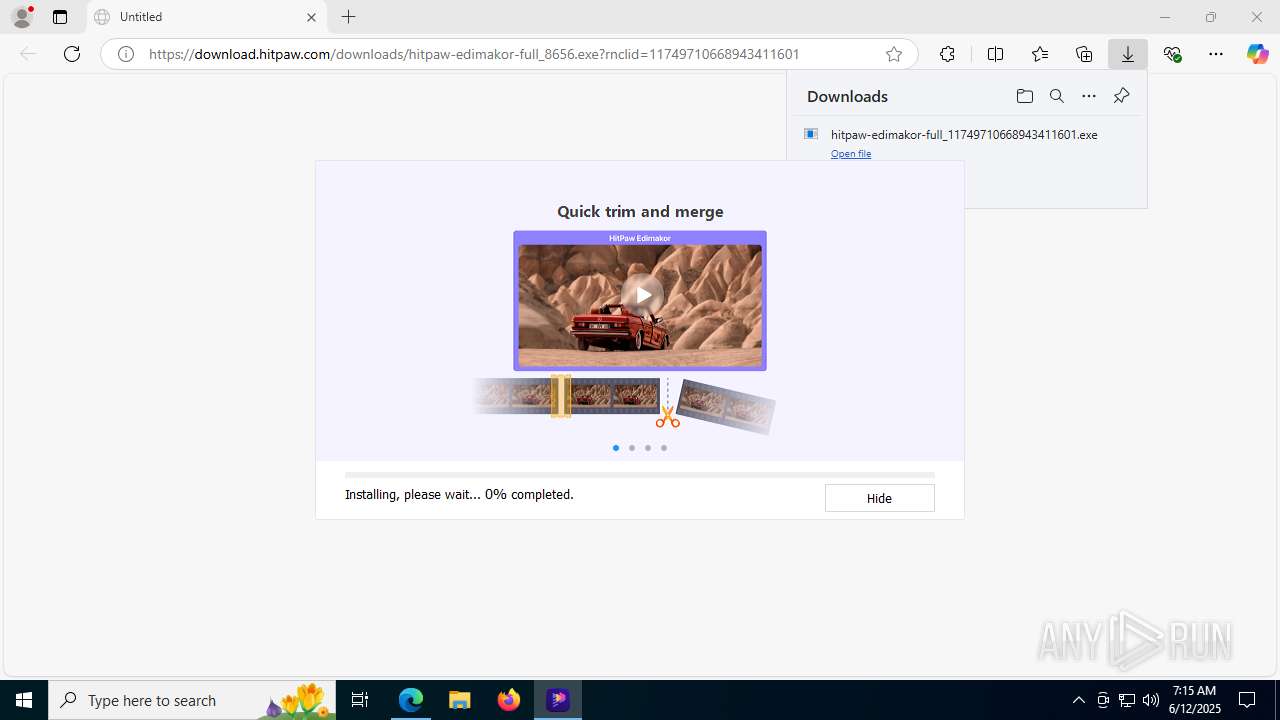
Uses TASKKILL.EXE to kill process
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
Starts CMD.EXE for commands execution
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
Process drops legitimate windows executable
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
Get information on the list of running processes
- cmd.exe (PID: 7520)
- cmd.exe (PID: 8172)
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
Drops 7-zip archiver for unpacking
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
Executable content was dropped or overwritten
- hitpawedimakor_hitpawem_4.0.1.exe (PID: 7856)
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
The process drops C-runtime libraries
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
INFO
Reads the computer name
- identity_helper.exe (PID: 7628)
Application launched itself
- msedge.exe (PID: 1604)
The sample compiled with english language support
- msedge.exe (PID: 1604)
- msedge.exe (PID: 4804)
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
Reads Environment values
- identity_helper.exe (PID: 7628)
Launching a file from the Downloads directory
- msedge.exe (PID: 1604)
Checks supported languages
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
- identity_helper.exe (PID: 7628)
Executable content was dropped or overwritten
- msedge.exe (PID: 4804)
- msedge.exe (PID: 1604)
Checks proxy server information
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
Creates files or folders in the user directory
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
Reads the machine GUID from the registry
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
Reads the software policy settings
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
Creates files in the program directory
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
Create files in a temporary directory
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
The sample compiled with chinese language support
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
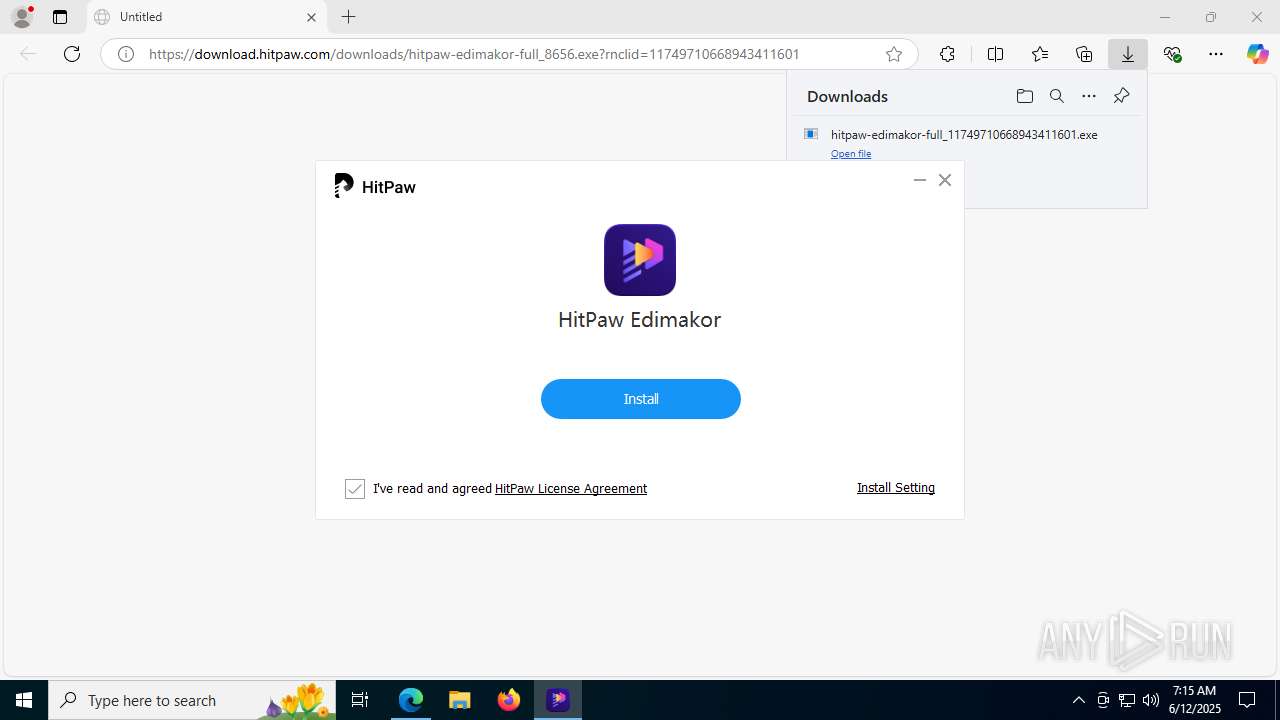
Compiled with Borland Delphi (YARA)
- hitpawedimakor_hitpawem_4.0.1.exe (PID: 7856)
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
UPX packer has been detected
- hitpaw-edimakor-full_11749710668943411601.exe (PID: 8052)
Detects InnoSetup installer (YARA)
- hitpawedimakor_hitpawem_4.0.1.exe (PID: 7856)
- hitpawedimakor_hitpawem_4.0.1.tmp (PID: 1752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
220
Monitored processes
70
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4228,i,211290741060477728,13778949608199543612,262144 --variations-seed-version --mojo-platform-channel-handle=4280 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4920,i,211290741060477728,13778949608199543612,262144 --variations-seed-version --mojo-platform-channel-handle=5220 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1100 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4972,i,211290741060477728,13778949608199543612,262144 --variations-seed-version --mojo-platform-channel-handle=4968 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1564 | "C:\WINDOWS\system32\taskkill.exe" /F /IM HitPawEdimakor.exe | C:\Windows\System32\taskkill.exe | — | hitpawedimakor_hitpawem_4.0.1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1604 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://download.hitpaw.com/downloads/hitpaw-edimakor-full_8656.exe?rnclid=11749710668943411601" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | "C:\Users\admin\AppData\Local\Temp\is-J9OK1.tmp\hitpawedimakor_hitpawem_4.0.1.tmp" /SL5="$40340,592525346,534528,C:\Users\admin\AppData\Local\Temp\hitpawedimakor_hitpawem\hitpawedimakor_hitpawem_4.0.1.exe" /VERYSILENT /SP- /NORESTART /DIR="C:\Program Files (x86)\HitPaw\HitPaw Edimakor\" /LANG=en /LOG="C:\Users\admin\AppData\Local\Temp\HitPaw Edimakor_Setup_20250612071540.log" /sptrack hitpaw-edimakor-full_11749710668943411601.exe | C:\Users\admin\AppData\Local\Temp\is-J9OK1.tmp\hitpawedimakor_hitpawem_4.0.1.tmp | hitpawedimakor_hitpawem_4.0.1.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=6036,i,211290741060477728,13778949608199543612,262144 --variations-seed-version --mojo-platform-channel-handle=5992 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1964 | "C:\WINDOWS\system32\dxdiag.exe" /whql:off /t C:\Users\admin\AppData\Local\cache\HitPaw Edimakor\sysinfo.txt | C:\Windows\System32\dxdiag.exe | — | hitpawedimakor_hitpawem_4.0.1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft DirectX Diagnostic Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 424
Read events
17 271
Write events
132
Delete events
21
Modification events
| (PID) Process: | (1604) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1604) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1604) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1604) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1604) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0AF077F8F0952F00 | |||
| (PID) Process: | (1604) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262940 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {11353598-28E8-4719-9CA5-C68EB94FF4A5} | |||
| (PID) Process: | (1604) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262940 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D8D7D17E-8470-4C44-88C7-3DCB00ABA9B0} | |||
| (PID) Process: | (1604) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 76C687F8F0952F00 | |||
| (PID) Process: | (1604) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (1604) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
1 042
Suspicious files
338
Text files
2 908
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176419.TMP | — | |
MD5:— | SHA256:— | |||
| 1604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176428.TMP | — | |
MD5:— | SHA256:— | |||
| 1604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176428.TMP | — | |
MD5:— | SHA256:— | |||
| 1604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176419.TMP | — | |
MD5:— | SHA256:— | |||
| 1604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176438.TMP | — | |
MD5:— | SHA256:— | |||
| 1604 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
119
DNS requests
70
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8052 | hitpaw-edimakor-full_11749710668943411601.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAhflMAthXvozBT%2FU%2B2iPio%3D | unknown | — | — | whitelisted |
3768 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8052 | hitpaw-edimakor-full_11749710668943411601.exe | GET | 301 | 104.18.24.249:80 | http://www.tenorshare.com/downloads/service/softwarelog.txt | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8052 | hitpaw-edimakor-full_11749710668943411601.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/csv | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6756 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8052 | hitpaw-edimakor-full_11749710668943411601.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA2Z%2Fk0pRoOk7pRvaISe4Lo%3D | unknown | — | — | whitelisted |
8052 | hitpaw-edimakor-full_11749710668943411601.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTjzY2p9Pa8oibmj%2BNSMWsz63kmWgQUuhbZbU2FL3MpdpovdYxqII%2BeyG8CEAuuZrxaun%2BVh8b56QTjMwQ%3D | unknown | — | — | whitelisted |
6756 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3956 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4804 | msedge.exe | 150.171.30.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4804 | msedge.exe | 92.122.215.2:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4804 | msedge.exe | 172.217.18.3:443 | update.googleapis.com | GOOGLE | US | whitelisted |
4804 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4804 | msedge.exe | 104.18.24.102:443 | download.hitpaw.com | CLOUDFLARENET | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
download.hitpaw.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8052 | hitpaw-edimakor-full_11749710668943411601.exe | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |
8052 | hitpaw-edimakor-full_11749710668943411601.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2200 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
8052 | hitpaw-edimakor-full_11749710668943411601.exe | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |