| File name: | eshow.exe |
| Full analysis: | https://app.any.run/tasks/9ad2be0b-a458-413f-8ecf-2c8b0012802e |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2022, 10:02:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 394328CF1B1963613B86B5F1291CEF28 |
| SHA1: | 052707E51CC6A9F11D92EFBA31A73C942E5196EB |
| SHA256: | 8107D24ED0DDE8B274AA155F39BE168D87E73F0E1CC0859C469AC1FD59925041 |
| SSDEEP: | 98304:jDK+XCYcnpYbkDbuKx6vOd9xDUu3jGqONAtSQL:jDlXmnWHOd9x4zNAtSQ |
MALICIOUS
Changes the autorun value in the registry
- eshow.exe (PID: 2980)
Drops executable file immediately after starts
- eshow.exe (PID: 2980)
Application was dropped or rewritten from another process
- donglemonitor.exe (PID: 3444)
SUSPICIOUS
Checks supported languages
- eshow.exe (PID: 2980)
- donglemonitor.exe (PID: 3444)
Reads the computer name
- eshow.exe (PID: 2980)
- donglemonitor.exe (PID: 3444)
Drops a file that was compiled in debug mode
- eshow.exe (PID: 2980)
Executable content was dropped or overwritten
- eshow.exe (PID: 2980)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (4.9) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (3.4) |
| .exe | | | Generic Win/DOS Executable (1.5) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| SpecialBuild: | 2016.11.03 |
|---|---|
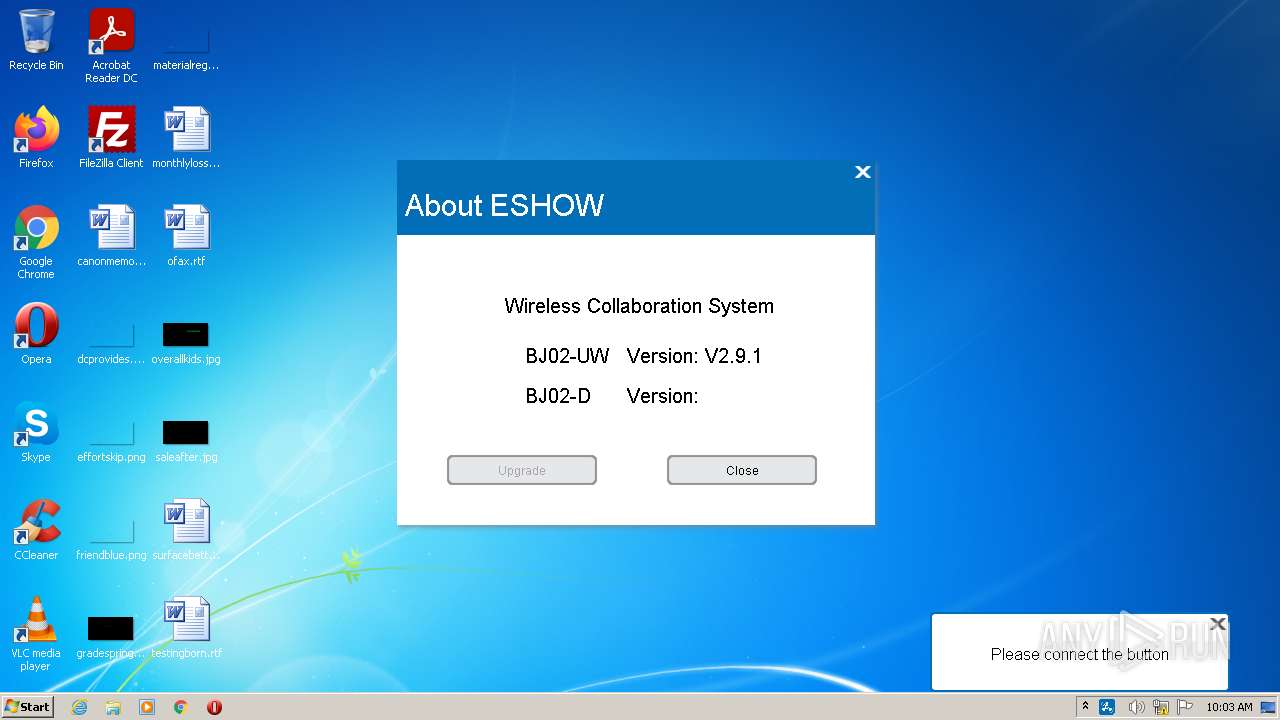
| ProductVersion: | 2.9.1.1 |
| ProductName: | ESHOW |
| PrivateBuild: | 2016.11.03 |
| OriginalFileName: | ESHOW.exe |
| LegalCopyright: | Copyright © 2016 |
| InternalName: | ESHOW.exe |
| FileVersion: | 2.9.1.1 |
| FileDescription: | ESHOW |
| Comments: | 一键联 - 无线联.享系统 |
| CharacterSet: | Unicode |
| LanguageCode: | Chinese (Simplified) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.1.0.0 |
| FileVersionNumber: | 2.1.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x1fe11a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2140160 |
| CodeSize: | 3552256 |
| LinkerVersion: | 14.23 |
| PEType: | PE32 |
| TimeStamp: | 2019:11:04 07:31:10+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Nov-2019 06:31:10 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | 一键联 - 无线联.享系统 |
| FileDescription: | ESHOW |
| FileVersion: | 2.9.1.1 |
| InternalName: | ESHOW.exe |
| LegalCopyright: | Copyright © 2016 |
| OriginalFilename: | ESHOW.exe |
| PrivateBuild: | 2016.11.03 |
| ProductName: | ESHOW |
| ProductVersion: | 2.9.1.1 |
| SpecialBuild: | 2016.11.03 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000148 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 04-Nov-2019 06:31:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x003530BF | 0x00353200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67555 |
.text.un\xfc\xd5 | 0x00355000 | 0x0000D5FC | 0x0000D600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.32916 |
.rodata | 0x004A3000 | 0x00000210 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.83982 |
.rdata | 0x00366000 | 0x00096F5C | 0x00097000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.66907 |
.data | 0x003FD000 | 0x00094288 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.73309 |
.eh_fram\xa4\x04\x01 | 0x00492000 | 0x000104A4 | 0x00010600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.91179 |
.rsrc | 0x004A4000 | 0x0009EE90 | 0x0009F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.70503 |
.reloc | 0x00543000 | 0x0002F900 | 0x0002FA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59955 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11344 | 917 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.62411 | 270376 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 2.75901 | 84 | UNKNOWN | Chinese - PRC | RT_STRING |
9 | 5.33724 | 138 | UNKNOWN | Chinese - PRC | RT_STRING |
10 | 5.30131 | 398 | UNKNOWN | Chinese - PRC | RT_STRING |
11 | 4.8344 | 308 | UNKNOWN | Chinese - PRC | RT_STRING |
103 | 3.7554 | 342 | UNKNOWN | Chinese - PRC | RT_DIALOG |
107 | 1.67095 | 20 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
108 | 1.83321 | 20 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
109 | 1.79879 | 16 | UNKNOWN | Chinese - PRC | RT_ACCELERATOR |
Imports
ADVAPI32.dll |
AVRT.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
HID.DLL |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2980 | "C:\Users\admin\AppData\Local\Temp\eshow.exe" | C:\Users\admin\AppData\Local\Temp\eshow.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ESHOW Exit code: 0 Version: 2.9.1.1 Modules
| |||||||||||||||
| 3444 | "C:\Users\admin\AppData\Local\ESHOW\donglemonitor.exe" | C:\Users\admin\AppData\Local\ESHOW\donglemonitor.exe | — | eshow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: donglemonitor Exit code: 0 Version: 1.0.2.3 Modules
| |||||||||||||||
Total events
103
Read events
101
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2980) eshow.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: eshow.exe | |||
| (PID) Process: | (2980) eshow.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ESHOW_Sev |
Value: C:\Users\admin\AppData\Local\ESHOW\donglemonitor.exe | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | eshow.exe | C:\Users\admin\AppData\Local\ESHOW\donglemonitor.exe | executable | |
MD5:1BA6FA16372EE867A2D8A3B0B846AD15 | SHA256:AFE842FDC0A8D0CA7F5C585B0D6179344AC5B34C5F184AF2EDB195A3E85F28D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
eshow.exe | 10:03:05:0531 ===DUPLICATIONMANAGER Constructor===
|
eshow.exe | 10:03:05:0531 =======time caps:1========
|
eshow.exe | 10:03:05:0531 =======Win8_Less========
|
eshow.exe | 10:03:05:0556 priPID 9 subPID 1 |
eshow.exe | 10:03:05:0561 ===WM_INITDIALOG===
|
eshow.exe | 10:03:05:0568 =======InstallDeviceMonitor flag 0========
|
eshow.exe | C:\Users\admin\AppData\Local\ESHOW\donglemonitor.exe |
eshow.exe | 10:03:05:0617 get config.ini ViewScale : [WM_VIEWSCALE_16X9]
|
eshow.exe | 10:03:05:0617 Aero Glass is not open
|
eshow.exe | 10:03:05:0623 -----0 0 1280 720--
|