| File name: | install.exe |
| Full analysis: | https://app.any.run/tasks/c234705a-bcdf-4817-afaf-1c85b6f9084b |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2026, 04:34:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | EE9444339E5A87D0E7843263B46BF6A8 |
| SHA1: | 440630FCC0992BFEF57689CBF735C13E73D85C15 |
| SHA256: | 8107BBD08F5C2AEB1EEEAC0700A3C110BB205FBEA841323C14794F8EBABCA723 |
| SSDEEP: | 98304:6zyeS/wbHxntMTGwdvk1aXdND9XLDbenkuA83wpYp2twAQoIrGJZYorg4jOsQgFh:Dq9oL881mwLuzNK496U |
MALICIOUS
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7204)
Disables Windows Defender
- install.exe (PID: 7468)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7204)
UAC/LUA settings modification
- install.exe (PID: 7468)
Run PowerShell with an invisible window
- powershell.exe (PID: 7204)
- powershell.exe (PID: 6384)
- powershell.exe (PID: 7564)
Adds process to the Windows Defender exclusion list
- install.exe (PID: 7468)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7204)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7204)
Changes settings for real-time protection
- powershell.exe (PID: 7204)
Changes Windows Defender settings
- install.exe (PID: 7468)
Changes powershell execution policy (Bypass)
- install.exe (PID: 7468)
Starts SC.EXE for service management
- cmd.exe (PID: 4944)
Uses TASKKILL.EXE to kill antiviruses
- cmd.exe (PID: 2156)
- cmd.exe (PID: 4968)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 2156)
- taskkill.exe (PID: 3692)
- cmd.exe (PID: 4968)
- taskkill.exe (PID: 684)
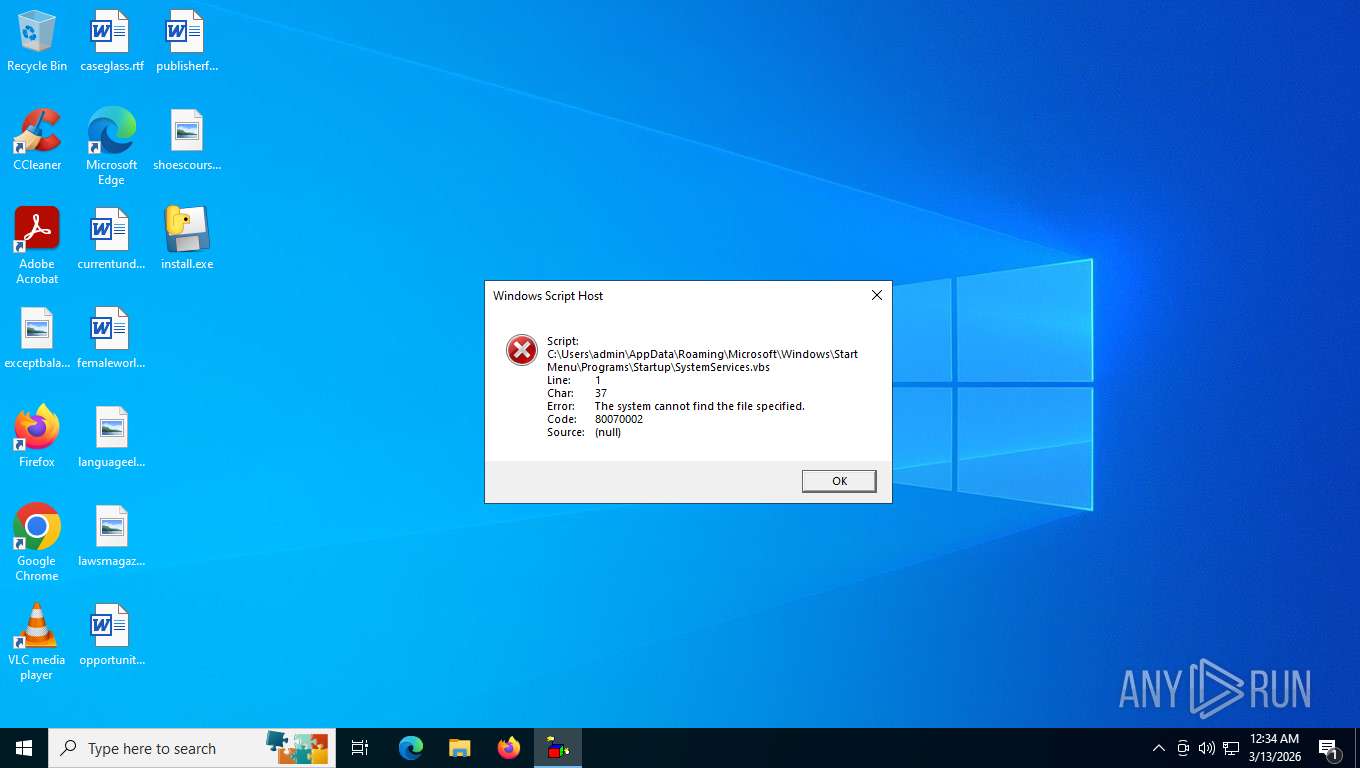
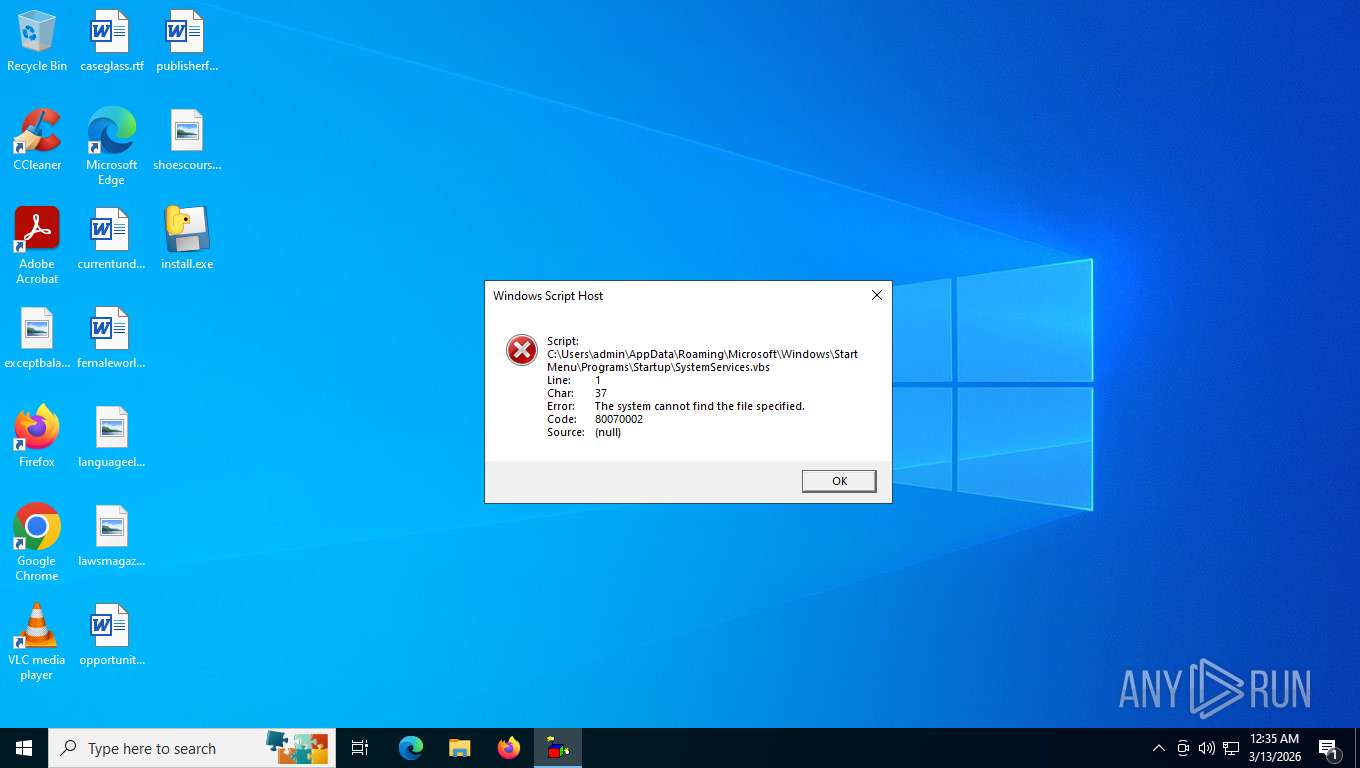
Create files in the Startup directory
- install.exe (PID: 7468)
Changes the autorun value in the registry
- install.exe (PID: 7468)
SUSPICIOUS
Application launched itself
- install.exe (PID: 4624)
- install.exe (PID: 4396)
- install.exe (PID: 6200)
Loads Python modules
- install.exe (PID: 4396)
- install.exe (PID: 7468)
Executable content was dropped or overwritten
- install.exe (PID: 4624)
- install.exe (PID: 6200)
Reads the date of Windows installation
- install.exe (PID: 4396)
Process drops python dynamic module
- install.exe (PID: 4624)
- install.exe (PID: 6200)
The process drops C-runtime libraries
- install.exe (PID: 4624)
- install.exe (PID: 6200)
The process bypasses the loading of PowerShell profile settings
- install.exe (PID: 7468)
Starts POWERSHELL.EXE for commands execution
- install.exe (PID: 7468)
Script adds exclusion path to Windows Defender
- install.exe (PID: 7468)
Bypass execution policy to execute commands
- powershell.exe (PID: 7204)
- powershell.exe (PID: 6384)
- powershell.exe (PID: 7564)
Script disables Windows Defender's real-time protection
- install.exe (PID: 7468)
Script disables Windows Defender's behavior monitoring
- install.exe (PID: 7468)
Stops a currently running service
- sc.exe (PID: 3612)
- sc.exe (PID: 7356)
- sc.exe (PID: 5200)
- sc.exe (PID: 5772)
Script adds exclusion process to Windows Defender
- install.exe (PID: 7468)
The process hide an interactive prompt from the user
- install.exe (PID: 7468)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 7204)
Service autostart disabling
- cmd.exe (PID: 5584)
- cmd.exe (PID: 5888)
- sc.exe (PID: 8140)
- cmd.exe (PID: 5712)
- cmd.exe (PID: 1280)
- sc.exe (PID: 6084)
- sc.exe (PID: 3580)
- sc.exe (PID: 7476)
Starts CMD.EXE for commands execution
- install.exe (PID: 7468)
Starts SC.EXE for service management
- cmd.exe (PID: 5888)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 5712)
- cmd.exe (PID: 1280)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 5584)
Windows service management via SC.EXE
- sc.exe (PID: 8140)
- sc.exe (PID: 7476)
- sc.exe (PID: 6084)
- sc.exe (PID: 3580)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2368)
- cmd.exe (PID: 6628)
- cmd.exe (PID: 5700)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 7628)
Uses WMIC.EXE to obtain data on processes
- cmd.exe (PID: 3508)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 2664)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6384)
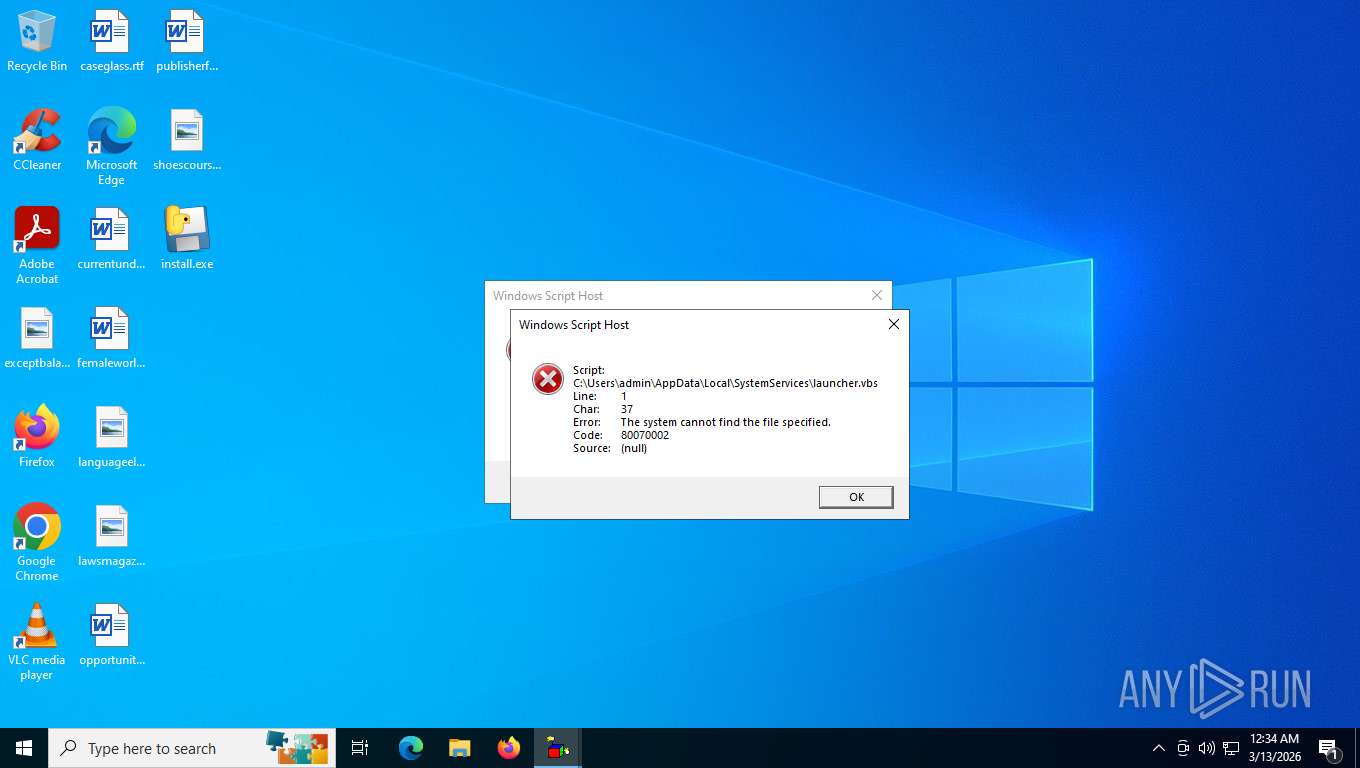
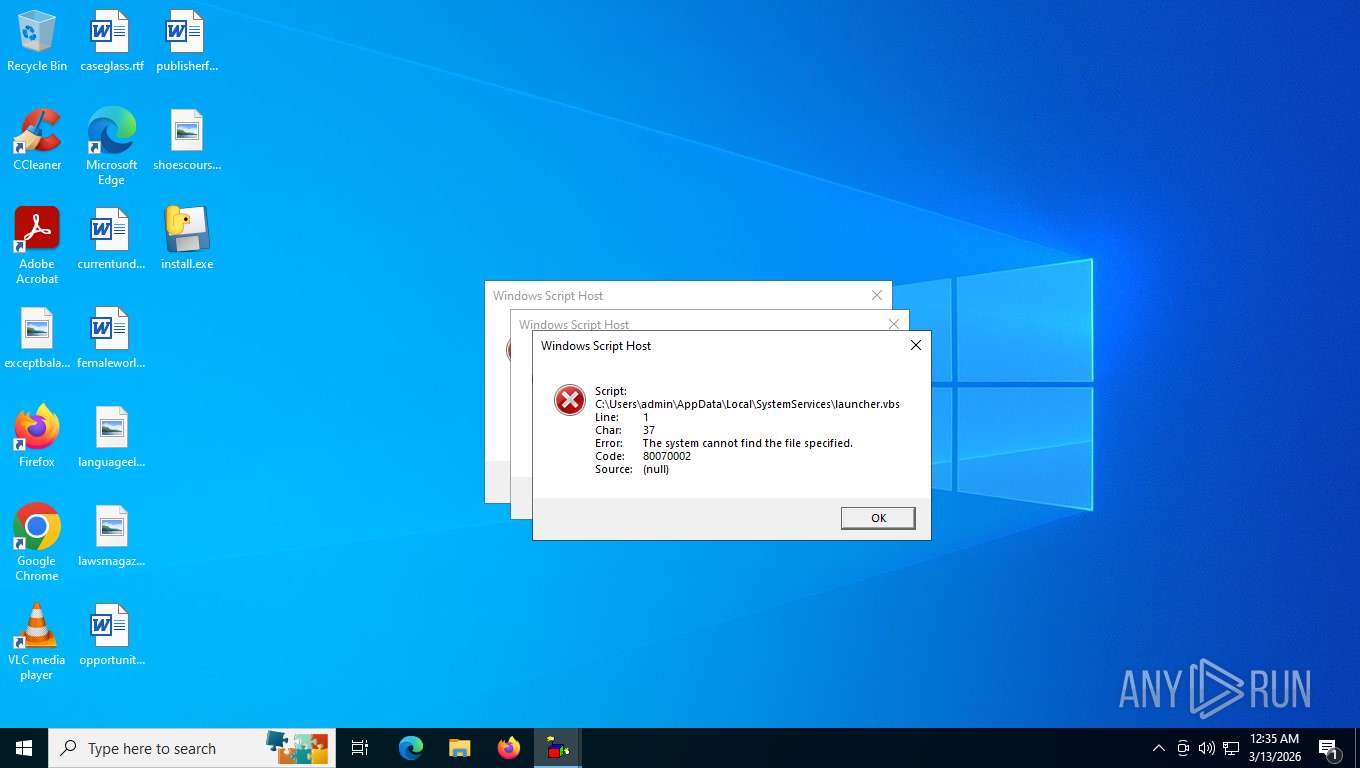
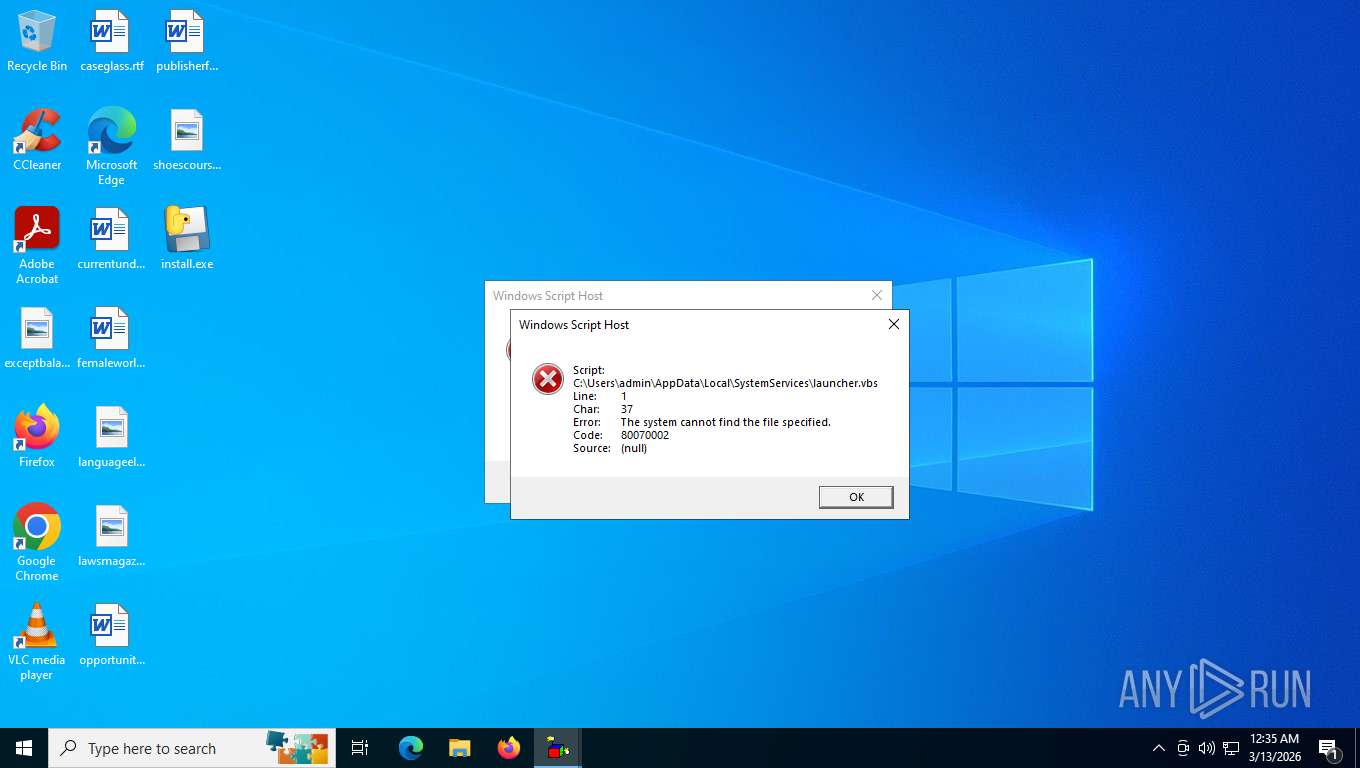
The process executes VB scripts
- wscript.exe (PID: 3380)
- wscript.exe (PID: 7776)
- wscript.exe (PID: 7664)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7664)
- wscript.exe (PID: 7776)
- wscript.exe (PID: 3380)
INFO
Reads the computer name
- install.exe (PID: 4624)
- install.exe (PID: 4396)
- install.exe (PID: 6200)
Checks supported languages
- install.exe (PID: 4624)
- install.exe (PID: 4396)
- install.exe (PID: 6200)
- install.exe (PID: 7468)
Create files in a temporary directory
- install.exe (PID: 4624)
- install.exe (PID: 6200)
- install.exe (PID: 7468)
Process checks computer location settings
- install.exe (PID: 4396)
The sample compiled with english language support
- install.exe (PID: 4624)
- install.exe (PID: 6200)
Reads security settings of Internet Explorer
- install.exe (PID: 4396)
- WMIC.exe (PID: 3580)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7564)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 6384)
Disables trace logs
- powershell.exe (PID: 6384)
Launching a file from the Startup directory
- install.exe (PID: 7468)
Reads Internet Explorer settings
- powershell.exe (PID: 6384)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6384)
Creates files or folders in the user directory
- install.exe (PID: 7468)
Drops encrypted JS script (Microsoft Script Encoder)
- install.exe (PID: 7468)
There is functionality for taking screenshot (YARA)
- install.exe (PID: 6200)
PyInstaller has been detected (YARA)
- install.exe (PID: 6200)
Manual execution by a user
- wscript.exe (PID: 7776)
- wscript.exe (PID: 3380)
Launching a file from a Registry key
- install.exe (PID: 7468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2026:03:13 04:32:21+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 181760 |
| InitializedDataSize: | 159744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xdfa0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
199
Monitored processes
65
Malicious processes
5
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | taskkill /f /im MpCmdRun.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | C:\WINDOWS\system32\cmd.exe /c "sc config WdNisSvc start= disabled" | C:\Windows\System32\cmd.exe | — | install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2156 | C:\WINDOWS\system32\cmd.exe /c "taskkill /f /im MsMpEng.exe" | C:\Windows\System32\cmd.exe | — | install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | taskkill /f /im smartscreen.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2316 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2368 | C:\WINDOWS\system32\cmd.exe /c "taskkill /f /im smartscreen.exe" | C:\Windows\System32\cmd.exe | — | install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2452 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2528 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2664 | C:\WINDOWS\system32\cmd.exe /c "netsh advfirewall set allprofiles state off" | C:\Windows\System32\cmd.exe | — | install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2880 | taskkill /f /im SecurityHealthSystray.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 246
Read events
27 239
Write events
7
Delete events
0
Modification events
| (PID) Process: | (6576) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
| (PID) Process: | (7468) install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (7468) install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableRealtimeMonitoring |
Value: 1 | |||
| (PID) Process: | (7468) install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (7468) install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (7468) install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\System |
| Operation: | write | Name: | EnableSmartScreen |
Value: 0 | |||
| (PID) Process: | (7468) install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | SystemServices |
Value: wscript.exe "C:\Users\admin\AppData\Local\SystemServices\launcher.vbs" | |||
Executable files
110
Suspicious files
3
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4624 | install.exe | C:\Users\admin\AppData\Local\Temp\_MEI46242\_decimal.pyd | executable | |
MD5:90071379B9E53B2D1834D49F4FD804EC | SHA256:90045140E45EDCFE4F4859B3190184FAFF1249220011330A9D01319745766607 | |||
| 4624 | install.exe | C:\Users\admin\AppData\Local\Temp\_MEI46242\_hashlib.pyd | executable | |
MD5:9EC1021FA8A3C252E1F805AC7F172753 | SHA256:1430E4A2ED19EDA840668A292C39FF44488B598F53E903A61739A86B779ECBFE | |||
| 4624 | install.exe | C:\Users\admin\AppData\Local\Temp\_MEI46242\_ctypes.pyd | executable | |
MD5:AB19E3DD4731ED075589ABADCDE68991 | SHA256:697D05CAC7C167C00CCF22EA4FDBC7A8DB93AB9C6421061191558E42478068C5 | |||
| 4624 | install.exe | C:\Users\admin\AppData\Local\Temp\_MEI46242\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:E368A236F5676A3DA44E76870CD691C9 | SHA256:93C624B366BA16C643FC8933070A26F03B073AD0CF7F80173266D67536C61989 | |||
| 4624 | install.exe | C:\Users\admin\AppData\Local\Temp\_MEI46242\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:CC228FF8D86B608E73026B1E9960B2F8 | SHA256:4CADBC0C39DA7C6722206FDCEBD670ABE5B8D261E7B041DD94F9397A89D1990D | |||
| 4624 | install.exe | C:\Users\admin\AppData\Local\Temp\_MEI46242\api-ms-win-core-fibers-l1-1-0.dll | executable | |
MD5:B5E2760C5A46DBEB8AE18C75F335707E | SHA256:91D249D7BC0E38EF6BCB17158B1FDC6DD8888DC086615C9B8B750B87E52A5FB3 | |||
| 4624 | install.exe | C:\Users\admin\AppData\Local\Temp\_MEI46242\api-ms-win-core-fibers-l1-1-1.dll | executable | |
MD5:050A30A687E7A2FA6F086A0DB89AA131 | SHA256:FC9D86CEC621383EAB636EBC87DDD3F5C19A3CB2A33D97BE112C051D0B275429 | |||
| 4624 | install.exe | C:\Users\admin\AppData\Local\Temp\_MEI46242\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:344A09B4BE069F86356A89482C156647 | SHA256:8F105771B236DBCB859DE271F0A6822CE1CB79C36988DD42C9E3F6F55C5F7EB9 | |||
| 4624 | install.exe | C:\Users\admin\AppData\Local\Temp\_MEI46242\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:9F45A47EBFD9D0629F4935764243DD5A | SHA256:1CA895ABA4E7435563A6B43E85EBA67A0F8C74AA6A6A94D0FC48FA35535E2585 | |||
| 4624 | install.exe | C:\Users\admin\AppData\Local\Temp\_MEI46242\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:416AA8314222DB6CBB3760856BE13D46 | SHA256:39095F59C41D76EC81BB2723D646FDE4C148E7CC3402F4980D2ADE95CB9C84F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
23
DNS requests
10
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6076 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6076 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6576 | slui.exe | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | — | 512 b | whitelisted |
— | — | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | text | 512 b | whitelisted |
— | — | GET | — | 151.101.192.223:443 | https://www.python.org/ftp/python/3.12.4/python-3.12.4-amd64.exe | unknown | — | — | — |
6384 | powershell.exe | GET | 502 | 151.101.128.223:443 | https://www.python.org/ftp/python/3.12.4/python-3.12.4-amd64.exe | unknown | html | 247 b | unknown |
3312 | OfficeClickToRun.exe | POST | — | 20.44.10.123:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 52.168.117.169:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | text | 9 b | whitelisted |
— | — | POST | 200 | 104.208.16.92:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | — | — | whitelisted |
3312 | OfficeClickToRun.exe | POST | 200 | 20.44.10.123:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | — | 9 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7824 | slui.exe | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6076 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6076 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5208 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6576 | slui.exe | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6076 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2404 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.python.org |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Misc activity | ET INFO Request for EXE via Powershell |
6384 | powershell.exe | Misc activity | ET INFO Request for EXE via Powershell |
6384 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |