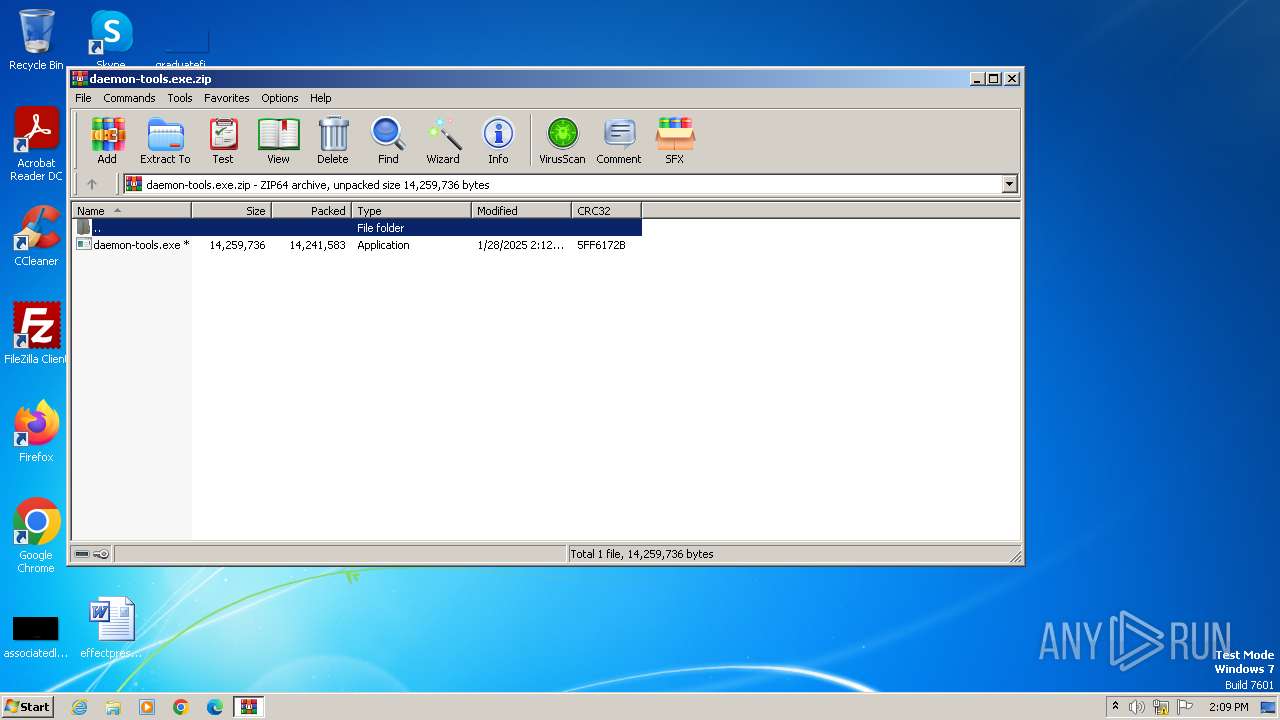
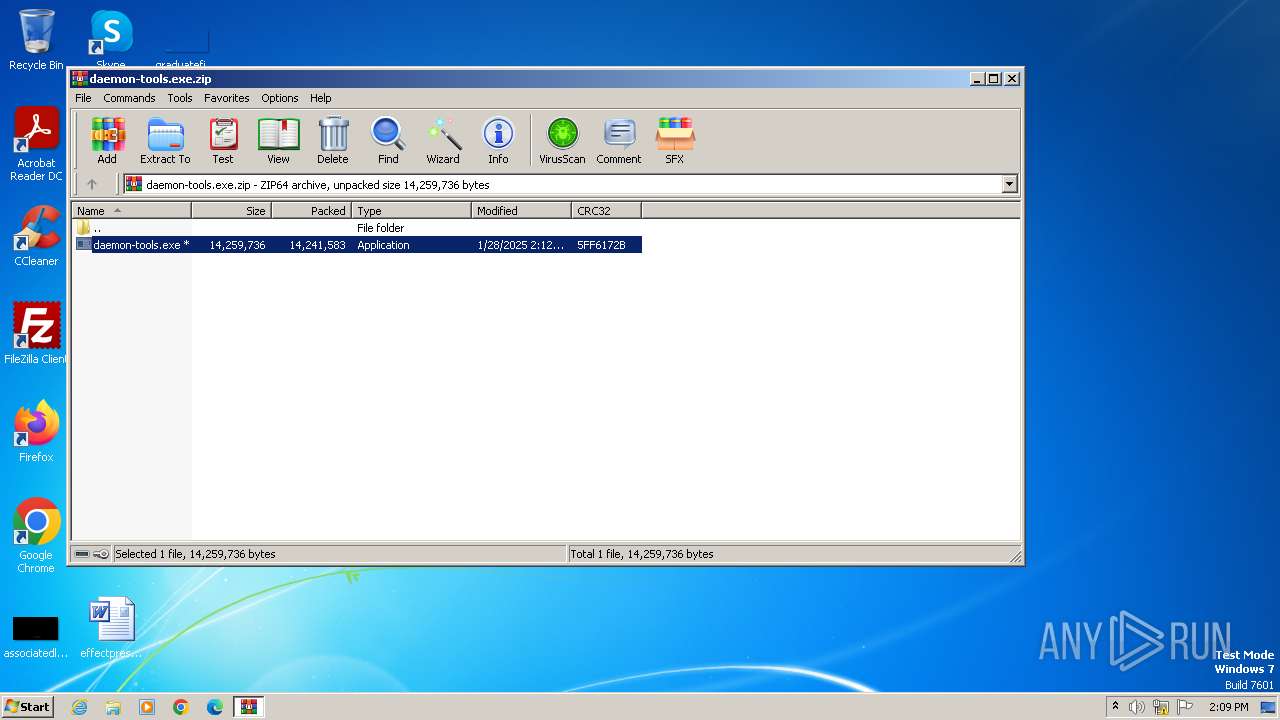
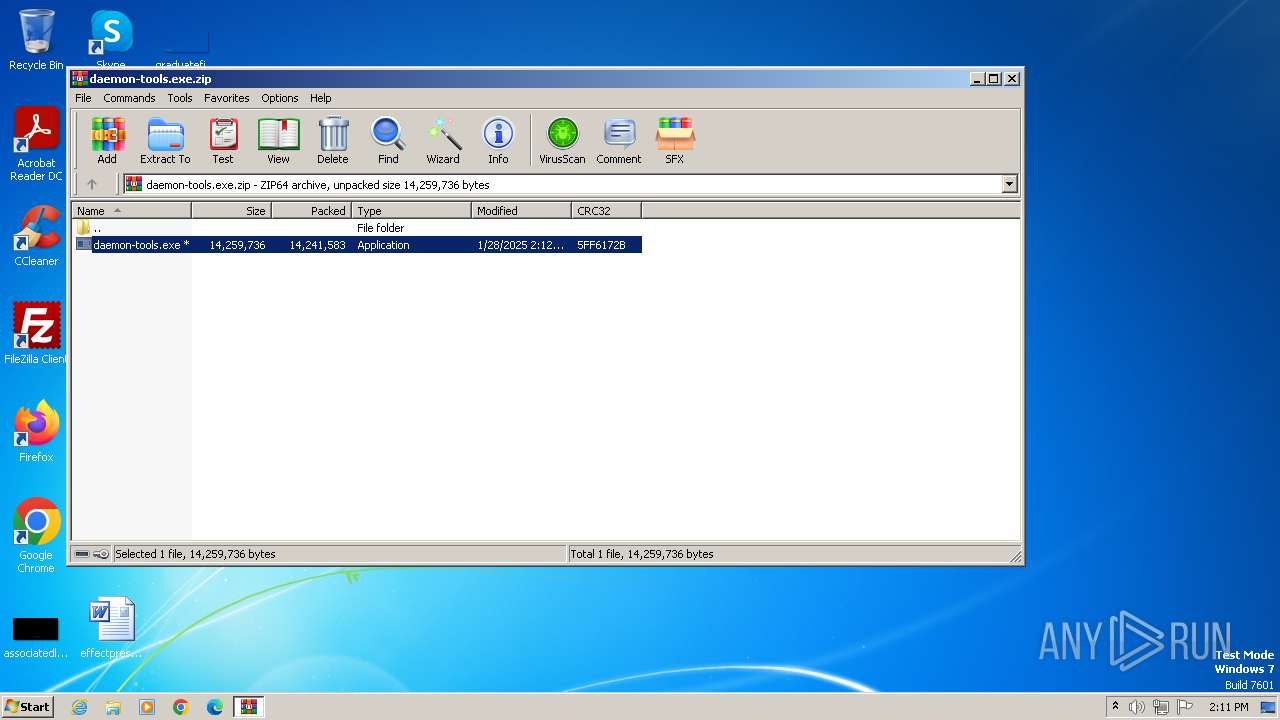
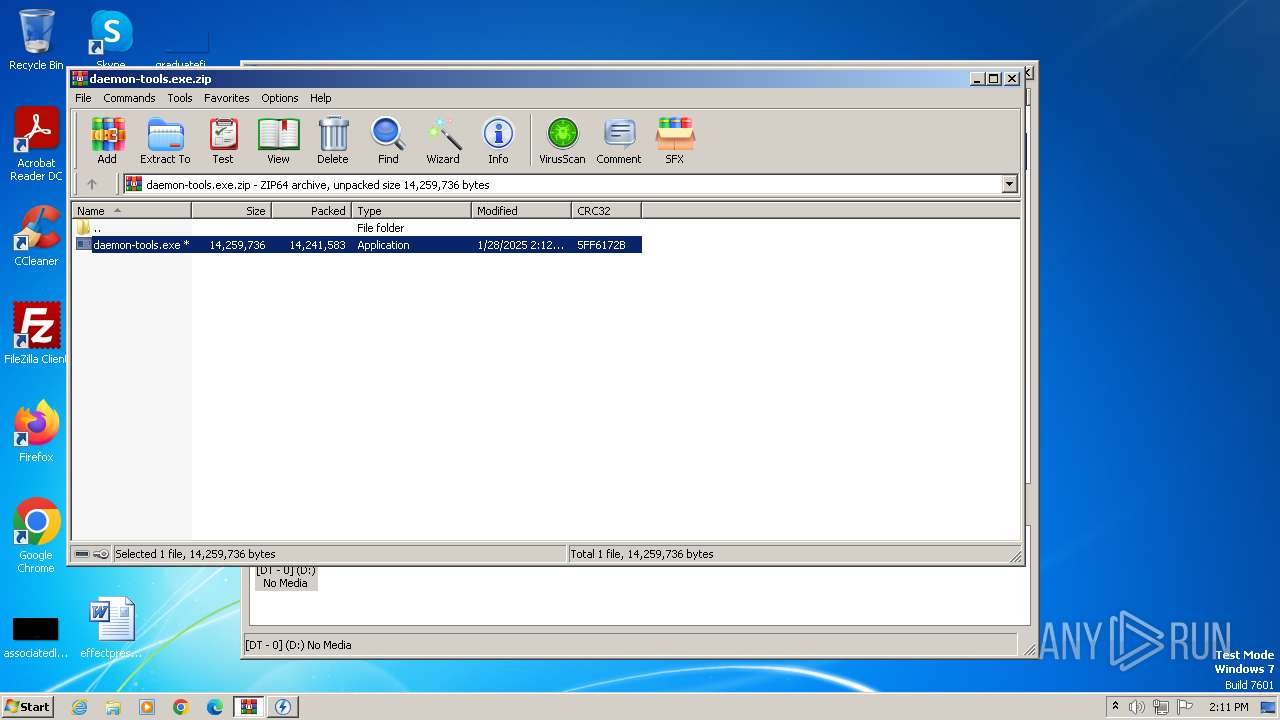
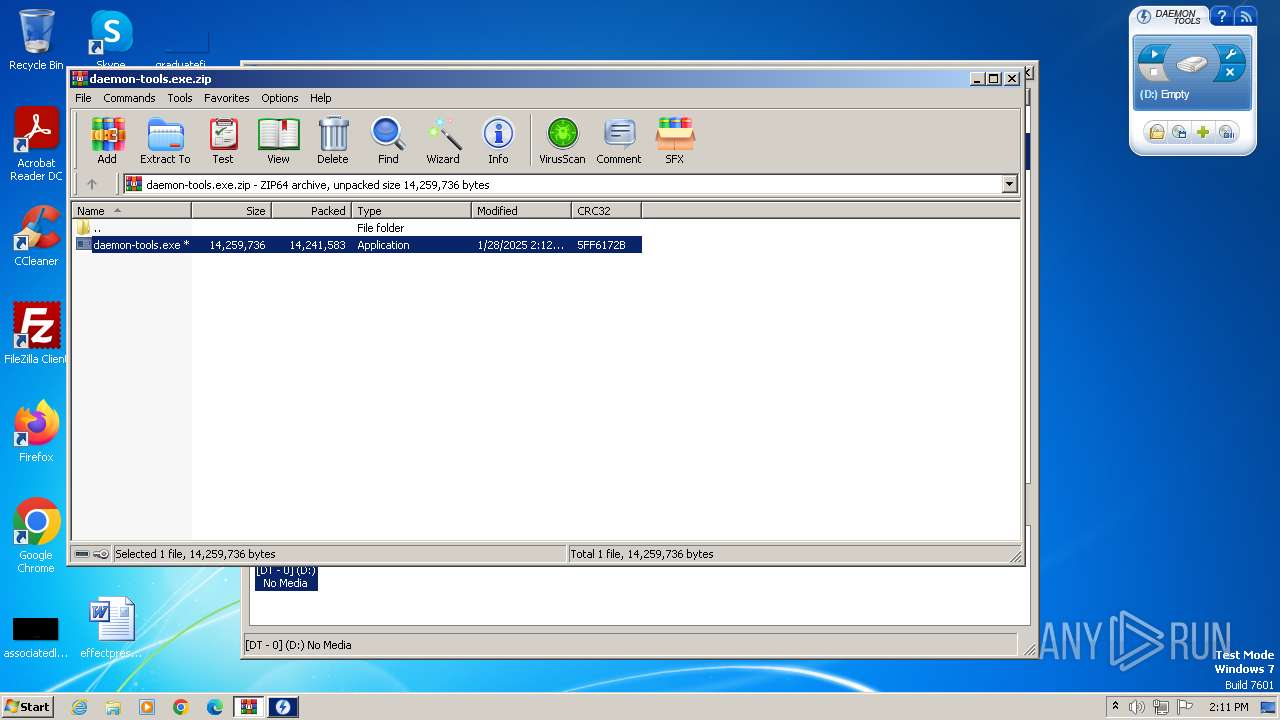
| File name: | daemon-tools.exe.zip |
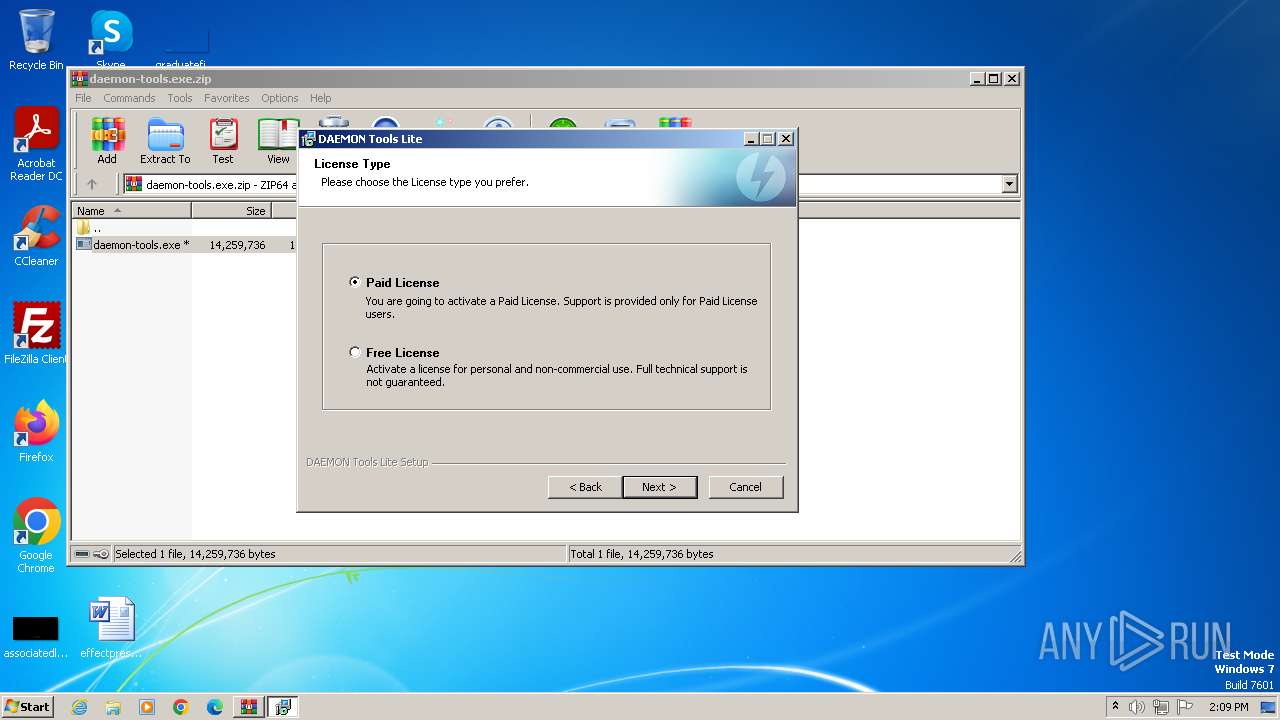
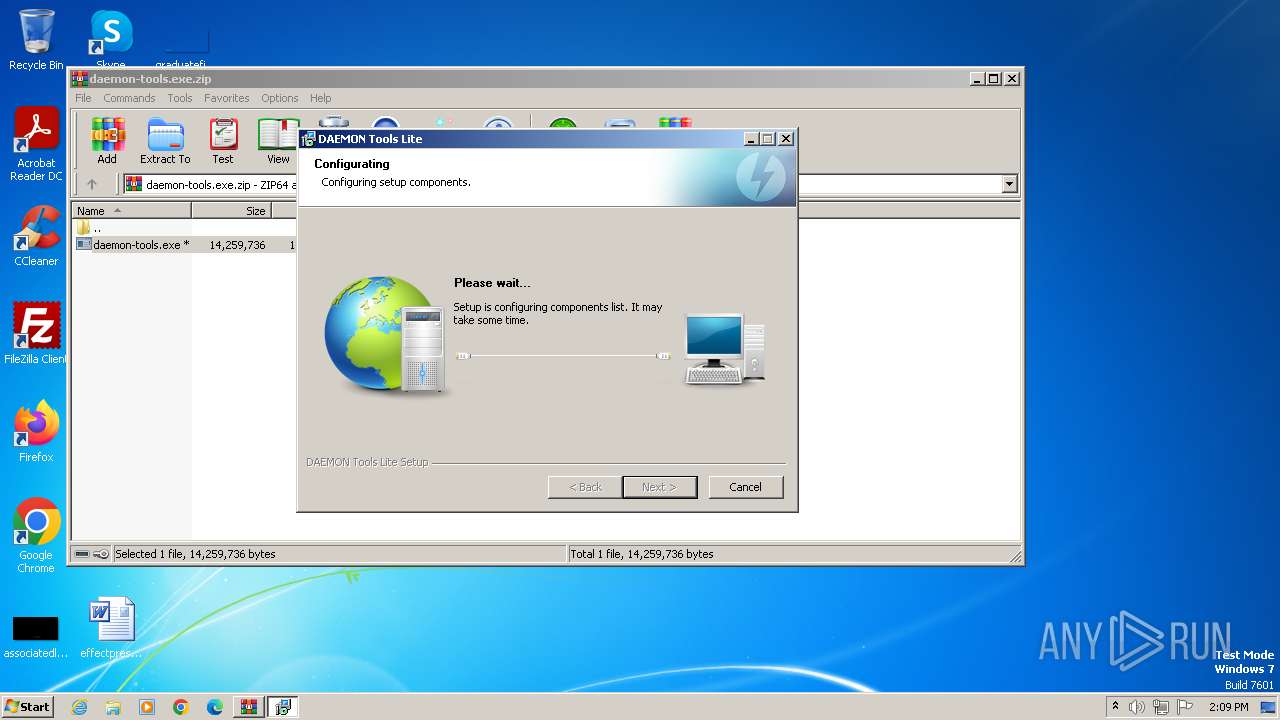
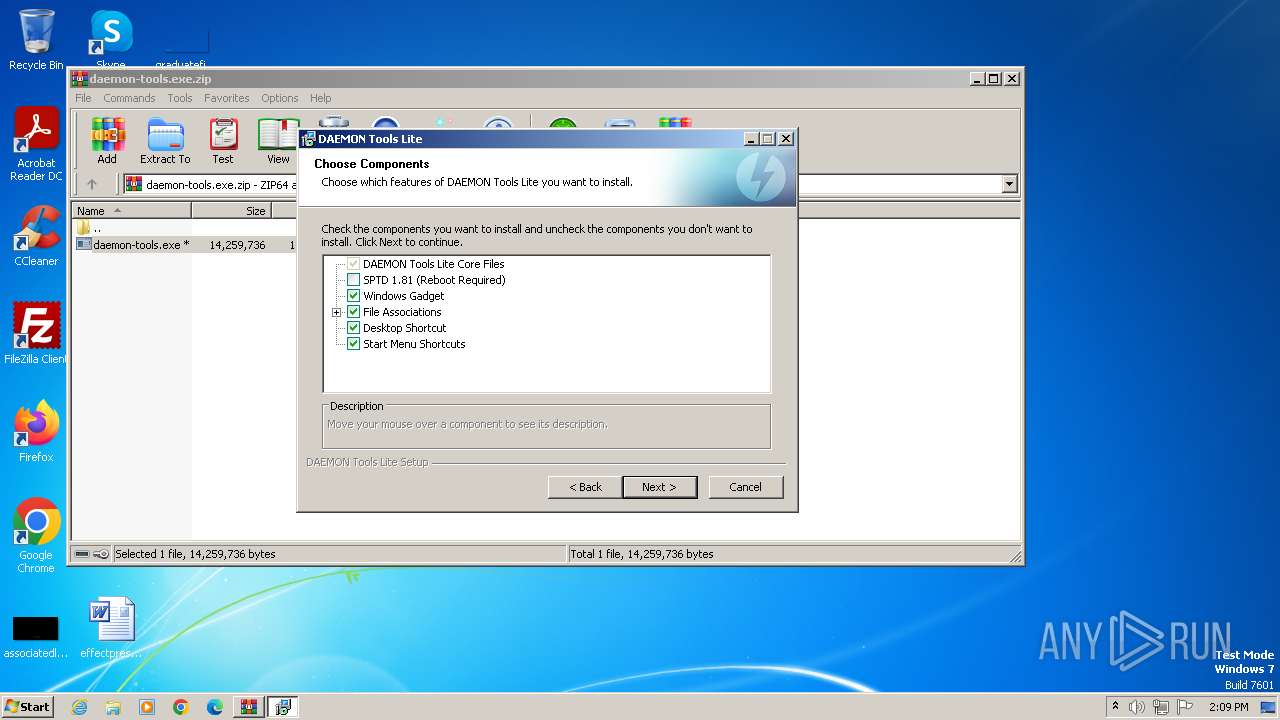
| Full analysis: | https://app.any.run/tasks/a8a0d216-5c56-41a0-a80d-33232a7a00ea |
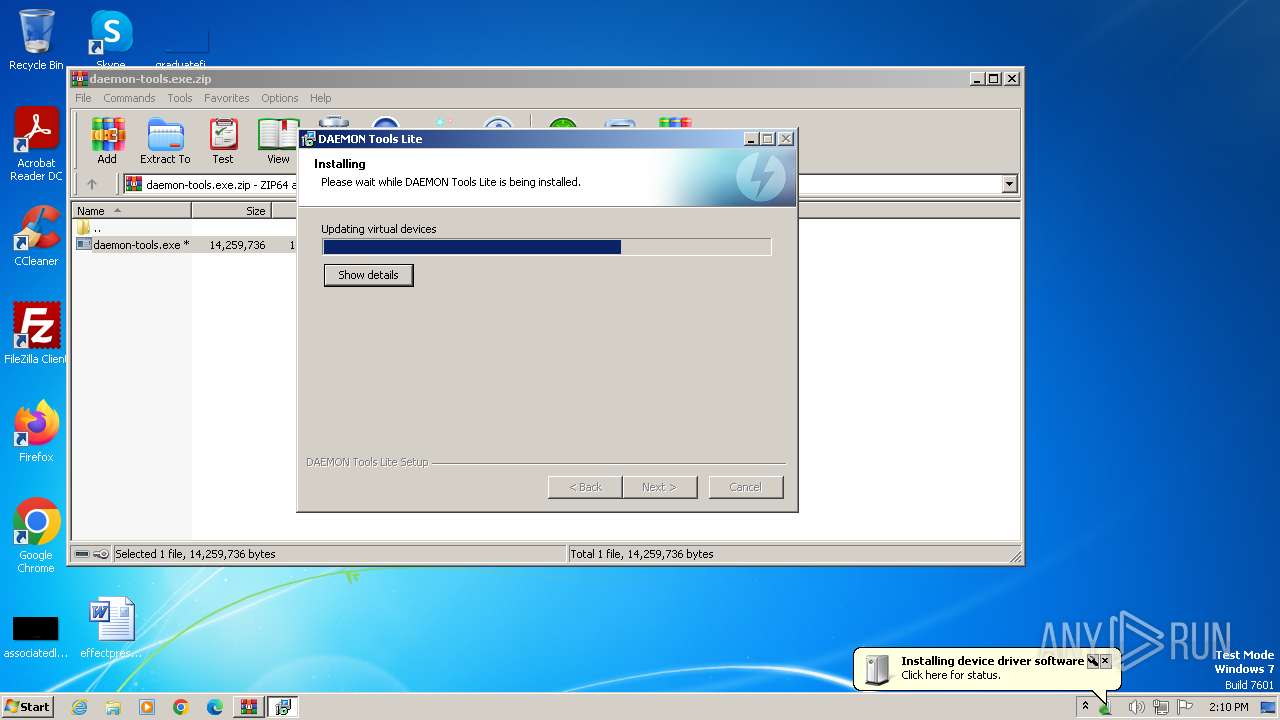
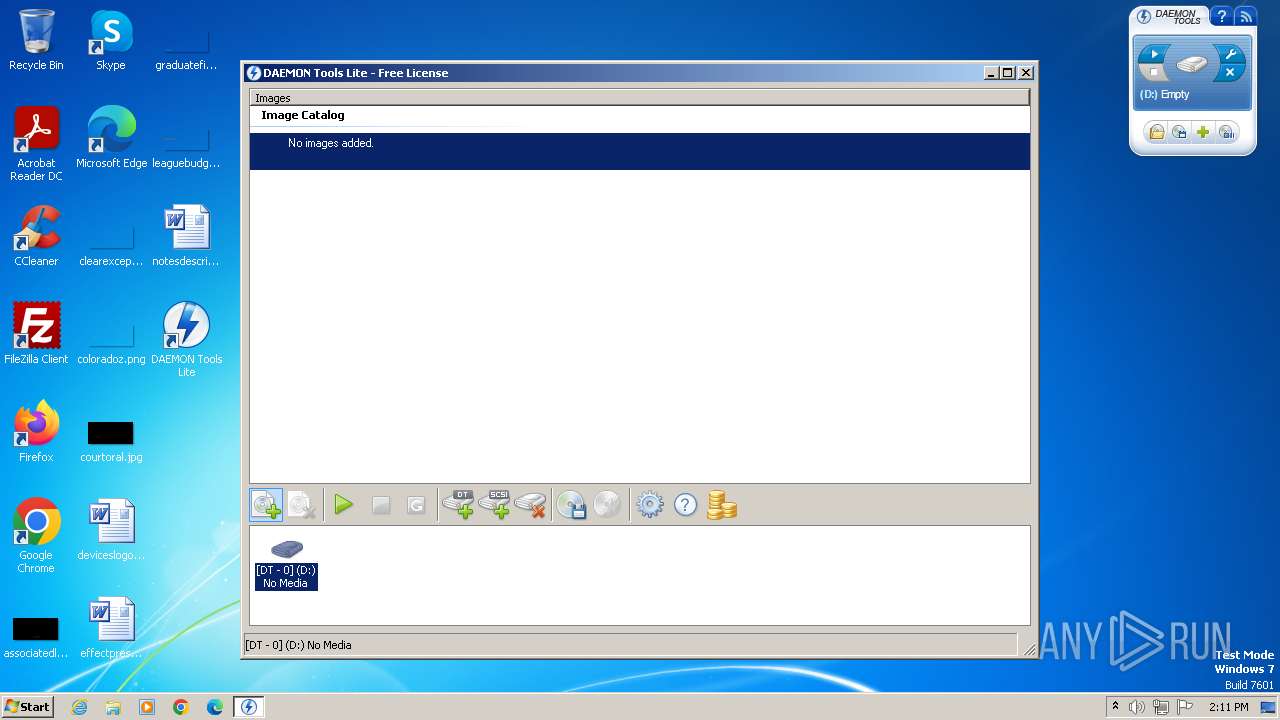
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2025, 14:08:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 8753ECB898B6C62C53D7AE0B36A60141 |
| SHA1: | 8BD51B2E80B759FDB3D8F50367B1BF078A1896DF |
| SHA256: | 81063CD1ADF29484EC7CB453657099F3DCAA025A25D9B84F4DE7CB957DBF06C8 |
| SSDEEP: | 196608:0TzGAGo2TDYOk83yuD2BCAieYunJz0Y76LwY:0TrGoopk83yuqBCveYunJdW9 |
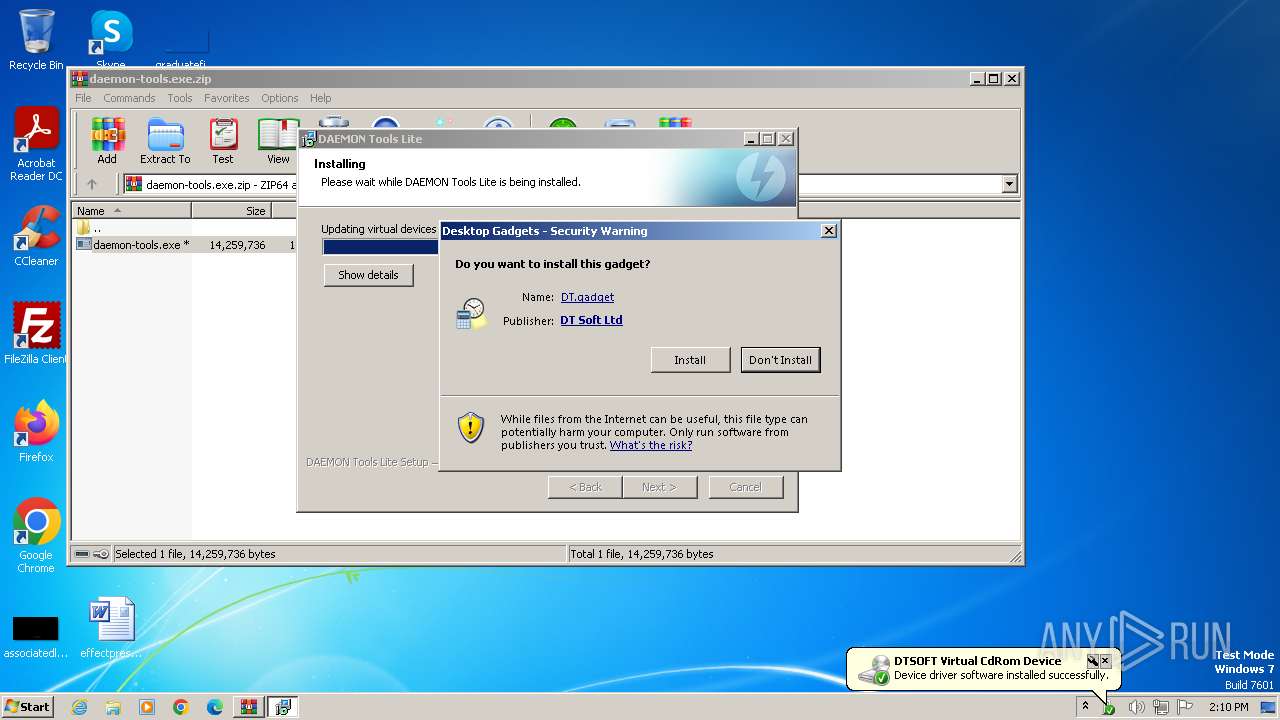
MALICIOUS
Executing a file with an untrusted certificate
- DTSetupHelper.exe (PID: 2776)
- daemon-tools.exe (PID: 1804)
- daemon-tools.exe (PID: 2184)
- SetupHelper.exe (PID: 3680)
- SetupHelper.exe (PID: 3788)
- DTShellHlp.exe (PID: 2012)
- DTLite.exe (PID: 3352)
Changes the autorun value in the registry
- daemon-tools.exe (PID: 2184)
- sidebar.exe (PID: 3660)
Registers / Runs the DLL via REGSVR32.EXE
- daemon-tools.exe (PID: 2184)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1580)
- daemon-tools.exe (PID: 2184)
- SetupHelper.exe (PID: 3680)
- sidebar.exe (PID: 3660)
Malware-specific behavior (creating "System.dll" in Temp)
- daemon-tools.exe (PID: 2184)
Searches for installed software
- daemon-tools.exe (PID: 2184)
The process creates files with name similar to system file names
- daemon-tools.exe (PID: 2184)
Executable content was dropped or overwritten
- daemon-tools.exe (PID: 2184)
- drvinst.exe (PID: 1924)
- drvinst.exe (PID: 3068)
There is functionality for taking screenshot (YARA)
- daemon-tools.exe (PID: 2184)
- DTShellHlp.exe (PID: 2012)
- DTLite.exe (PID: 3352)
Creates a software uninstall entry
- daemon-tools.exe (PID: 2184)
Reads the Internet Settings
- daemon-tools.exe (PID: 2184)
- rundll32.exe (PID: 944)
- SetupHelper.exe (PID: 3680)
- sidebar.exe (PID: 3660)
- SetupHelper.exe (PID: 3788)
- DTLite.exe (PID: 3352)
- DTShellHlp.exe (PID: 2012)
Adds/modifies Windows certificates
- daemon-tools.exe (PID: 2184)
Drops a system driver (possible attempt to evade defenses)
- daemon-tools.exe (PID: 2184)
- drvinst.exe (PID: 1924)
- drvinst.exe (PID: 3068)
Creates files in the driver directory
- drvinst.exe (PID: 1924)
- drvinst.exe (PID: 3068)
Checks Windows Trust Settings
- drvinst.exe (PID: 1924)
- daemon-tools.exe (PID: 2184)
- drvinst.exe (PID: 3068)
- drvinst.exe (PID: 3452)
- sidebar.exe (PID: 3660)
Reads settings of System Certificates
- daemon-tools.exe (PID: 2184)
- sidebar.exe (PID: 3660)
- DTLite.exe (PID: 3352)
Executes as Windows Service
- VSSVC.exe (PID: 396)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2800)
Reads Microsoft Outlook installation path
- sidebar.exe (PID: 3660)
Reads Internet Explorer settings
- sidebar.exe (PID: 3660)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1580)
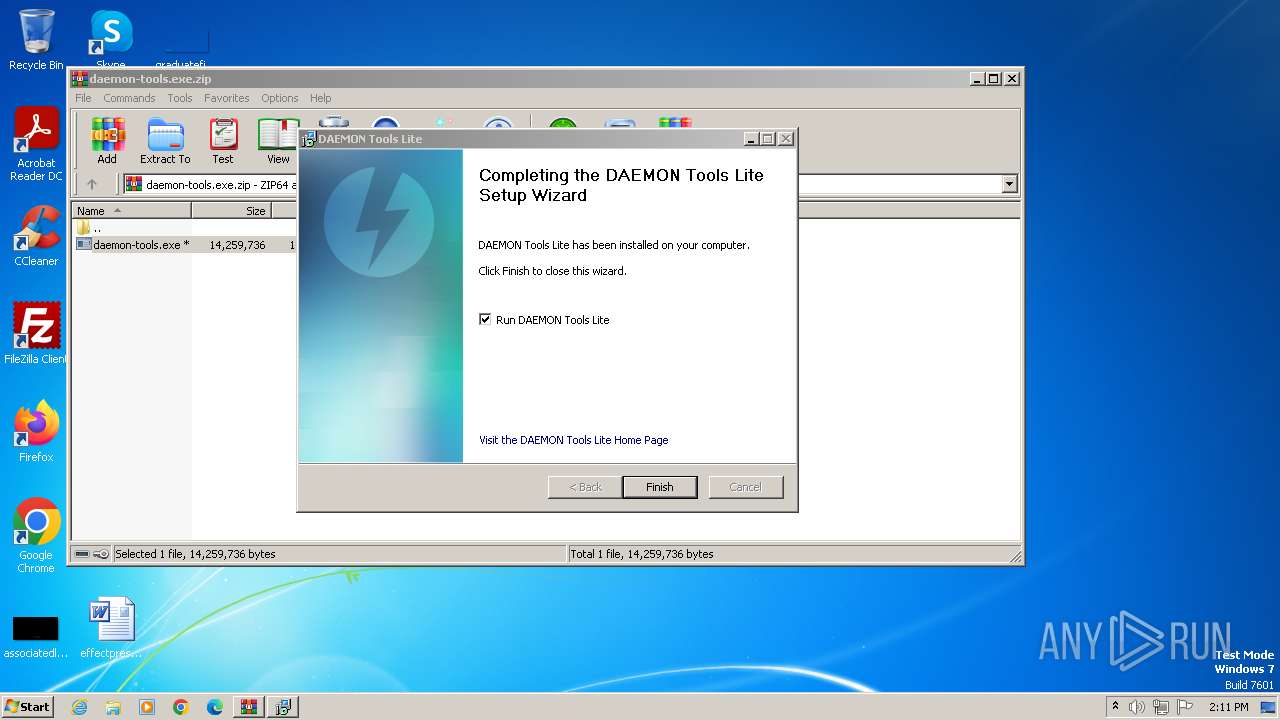
Creates files in the program directory
- daemon-tools.exe (PID: 2184)
Reads the computer name
- daemon-tools.exe (PID: 2184)
- wmpnscfg.exe (PID: 2912)
- drvinst.exe (PID: 1924)
- drvinst.exe (PID: 3068)
- drvinst.exe (PID: 3452)
- SetupHelper.exe (PID: 3680)
- sidebar.exe (PID: 3660)
- SetupHelper.exe (PID: 3788)
- DTLite.exe (PID: 3352)
- DTShellHlp.exe (PID: 2012)
Checks supported languages
- daemon-tools.exe (PID: 2184)
- DTSetupHelper.exe (PID: 2776)
- wmpnscfg.exe (PID: 2912)
- drvinst.exe (PID: 1924)
- drvinst.exe (PID: 3068)
- drvinst.exe (PID: 3452)
- SetupHelper.exe (PID: 3680)
- sidebar.exe (PID: 3660)
- SetupHelper.exe (PID: 3788)
- DTLite.exe (PID: 3352)
- DTShellHlp.exe (PID: 2012)
The sample compiled with english language support
- daemon-tools.exe (PID: 2184)
- drvinst.exe (PID: 1924)
- drvinst.exe (PID: 3068)
Manual execution by a user
- wmpnscfg.exe (PID: 2912)
Create files in a temporary directory
- daemon-tools.exe (PID: 2184)
Reads the machine GUID from the registry
- daemon-tools.exe (PID: 2184)
- drvinst.exe (PID: 1924)
- drvinst.exe (PID: 3068)
- drvinst.exe (PID: 3452)
- DTLite.exe (PID: 3352)
- sidebar.exe (PID: 3660)
Reads Windows Product ID
- daemon-tools.exe (PID: 2184)
Reads the software policy settings
- drvinst.exe (PID: 1924)
- daemon-tools.exe (PID: 2184)
- drvinst.exe (PID: 3068)
- drvinst.exe (PID: 3452)
- sidebar.exe (PID: 3660)
- DTLite.exe (PID: 3352)
Adds/modifies Windows certificates
- drvinst.exe (PID: 1924)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 944)
Process checks computer location settings
- drvinst.exe (PID: 3452)
Creates files or folders in the user directory
- sidebar.exe (PID: 3660)
Checks proxy server information
- sidebar.exe (PID: 3660)
Application launched itself
- msedge.exe (PID: 3780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | 0x0809 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:01:28 14:12:46 |
| ZipCRC: | 0x5ff6172b |
| ZipCompressedSize: | 14241583 |
| ZipUncompressedSize: | 14259736 |
| ZipFileName: | daemon-tools.exe |
Total processes
64
Monitored processes
21
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | rundll32.exe C:\Windows\system32\newdev.dll,pDiDeviceInstallNotification \\.\pipe\PNP_Device_Install_Pipe_1.{af4f893d-22da-4eb5-9a8d-e3adac4e9355} "(null)" | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1108 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
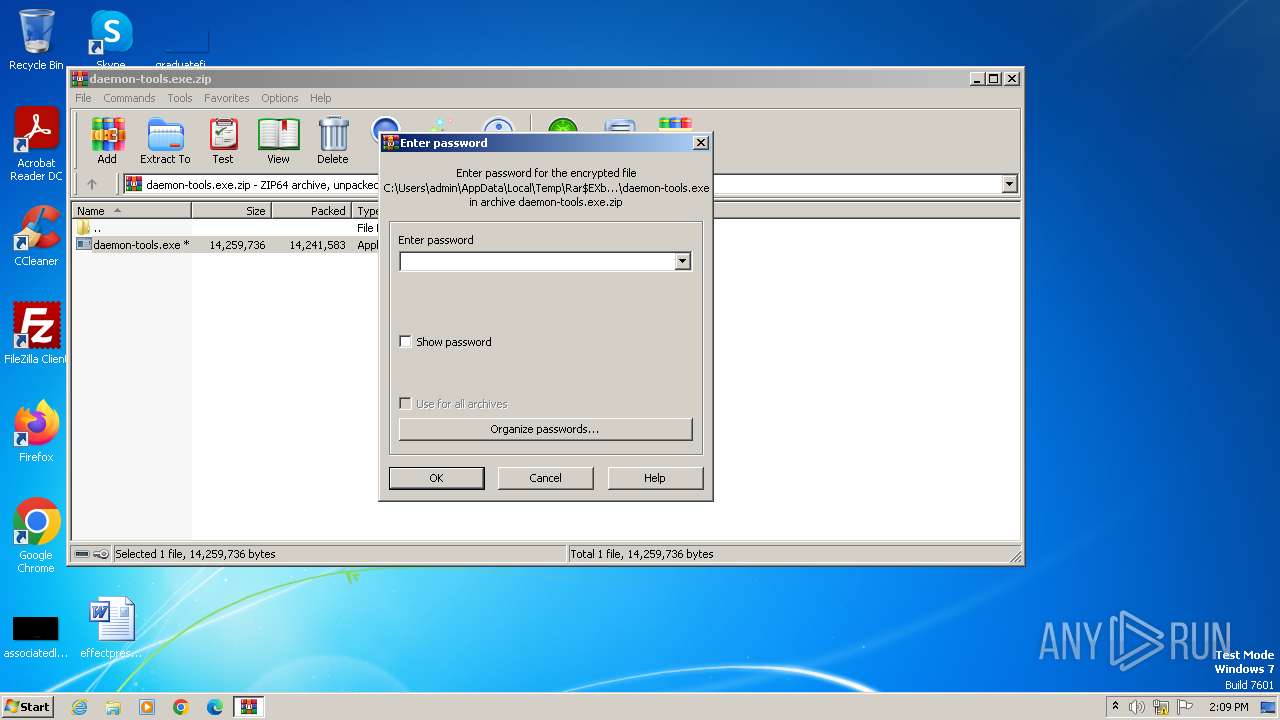
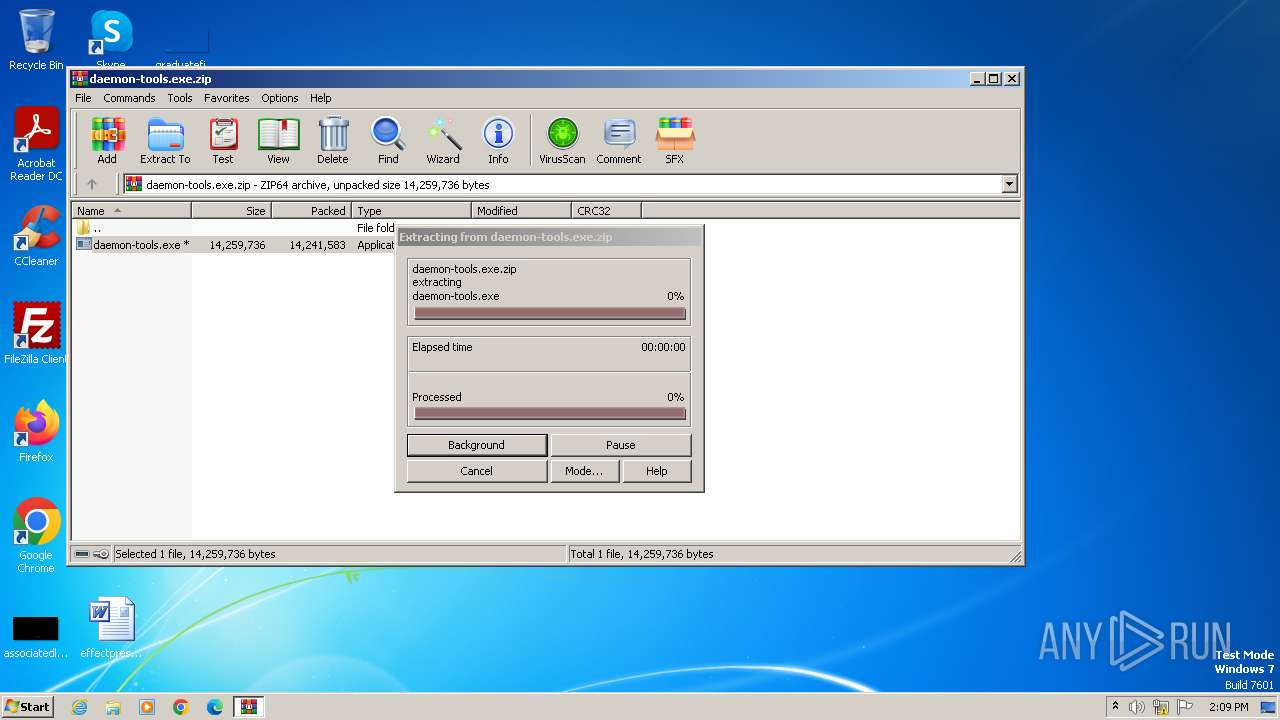
| 1580 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\daemon-tools.exe.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
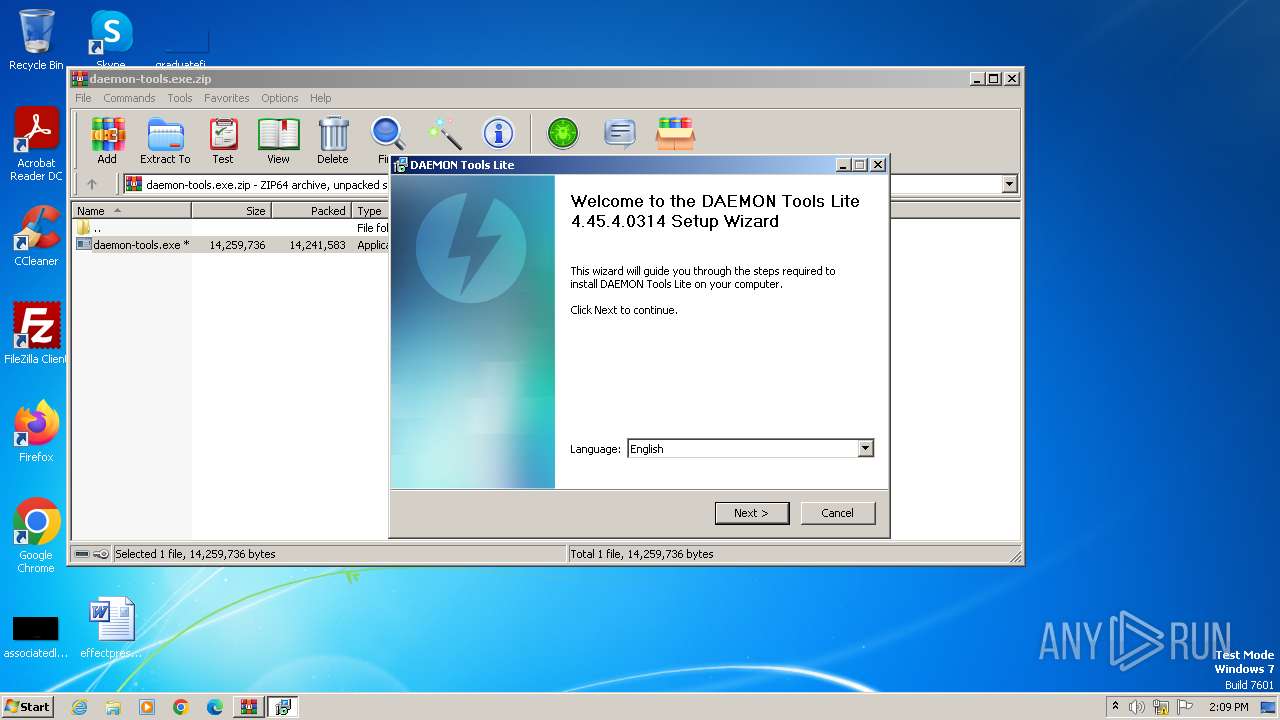
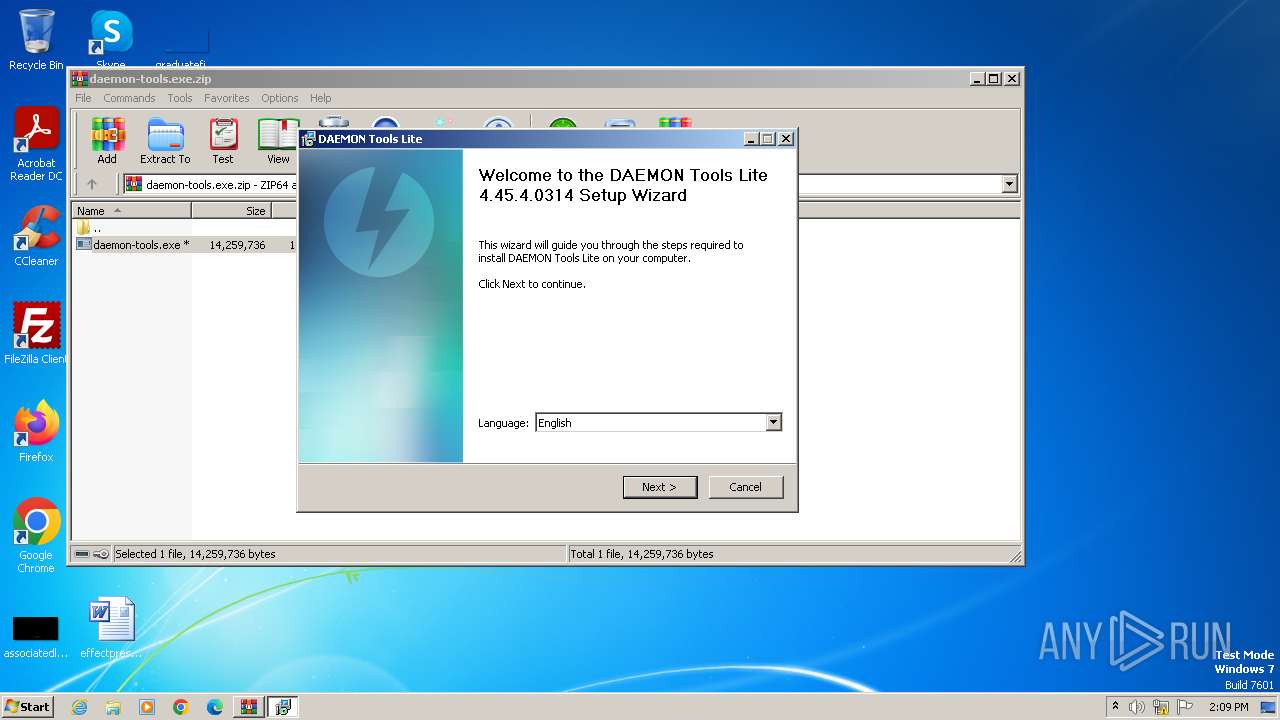
| 1804 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1580.16271\daemon-tools.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1580.16271\daemon-tools.exe | — | WinRAR.exe | |||||||||||
User: admin Company: DT Soft Ltd Integrity Level: MEDIUM Description: DAEMON Tools Lite Setup Exit code: 3221226540 Version: 4.45.4.0314.0 Modules
| |||||||||||||||
| 1924 | DrvInst.exe "4" "20" "C:\Users\admin\AppData\Local\Temp\{276e37b3-0c1e-0f48-1803-2238fe3e2c43}\dtsoftbus01.inf" "0" "6fa1095ab" "000004B0" "WinSta0\Default" "00000588" "208" "C:\Program Files\DAEMON Tools Lite" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2012 | "C:\Program Files\DAEMON Tools Lite\DTShellHlp.exe" | C:\Program Files\DAEMON Tools Lite\DTShellHlp.exe | — | sidebar.exe | |||||||||||
User: admin Company: DT Soft Ltd Integrity Level: MEDIUM Description: DAEMON Tools Shell Extensions Helper Version: 4.45.4.0314 Modules
| |||||||||||||||
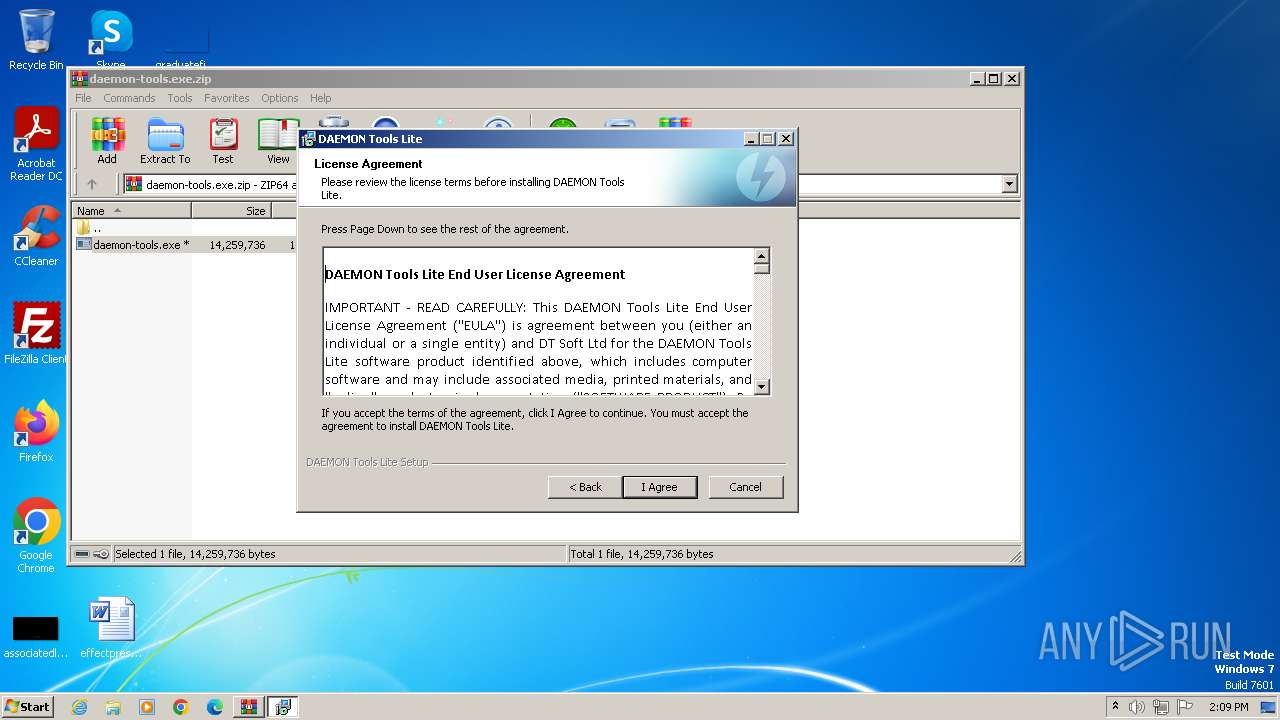
| 2184 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1580.16271\daemon-tools.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1580.16271\daemon-tools.exe | WinRAR.exe | ||||||||||||
User: admin Company: DT Soft Ltd Integrity Level: HIGH Description: DAEMON Tools Lite Setup Exit code: 0 Version: 4.45.4.0314.0 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1388 --field-trial-handle=1256,i,1846566556644883304,6687090904868363546,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2776 | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\DTSetupHelper.exe | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\DTSetupHelper.exe | — | daemon-tools.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
38 378
Read events
37 861
Write events
464
Delete events
53
Modification events
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\daemon-tools.exe.zip | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
116
Suspicious files
74
Text files
656
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | daemon-tools.exe | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\Lang\BGR.dll | executable | |
MD5:6A80832F5554B2D79E1B6F86FF1295A2 | SHA256:87835A1A901163EF44DB6A5BD739E1F338AC2B5C3AFA265DC850A49C4764A8FF | |||
| 2184 | daemon-tools.exe | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\Lang\AFK.dll | executable | |
MD5:8E2D9B28774FAEEF58D4ADB24BB0EC2C | SHA256:785B0E1DDE8C3E50561FE8B6CA1F78808336139A86E80F6FEBE6EBAC17A27E2F | |||
| 2184 | daemon-tools.exe | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\Lang\CAT.dll | executable | |
MD5:145899F9A5871819EEFF357081E7102A | SHA256:F3D1137F47ECAF0123C902D77428B2DFF46606AAE04C9AA6114BD2FED55337F5 | |||
| 2184 | daemon-tools.exe | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\Lang\ENU.dll | executable | |
MD5:97E00C2C357CF2BBD5ADD5828A813B89 | SHA256:7002D416FBF6869CB116EC15D959F5771EC9BE845E8F8992FD2EEFAAE70435AD | |||
| 1580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1580.16271\daemon-tools.exe | executable | |
MD5:2763B8AC8F1E3A56241600A70A2923A6 | SHA256:7BBA3EF65CFA242F70139DC8C339D351D3E60B7174D2687240613D94236DECD0 | |||
| 2184 | daemon-tools.exe | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\Lang\CHS.dll | executable | |
MD5:F68459BF7D4DD6426A7362032DC2CC5B | SHA256:7336F46103EFBC676D9B2C90FE611791F772EE83E8C7AC5692BFFD0E40DE10A2 | |||
| 2184 | daemon-tools.exe | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\Lang\ESN.dll | executable | |
MD5:4B69F6D2F45C444DAE6333FDED7DDDA4 | SHA256:2858C5D64BF3DCAE200B7385164235D4C02BF7C2EA5243A1C48B4AEA8DFA1C4D | |||
| 2184 | daemon-tools.exe | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\Lang\ARA.dll | executable | |
MD5:32F1B618BCE02707823B8A086AE90BBE | SHA256:206BFC015CB23F42BC092A09BD954EA635C67A95FC239BDBA527DC597481369F | |||
| 2184 | daemon-tools.exe | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\Lang\FRA.dll | executable | |
MD5:804ECD67B02E1B66FED80646DF3A0B63 | SHA256:3519B260054AD0F61EF0EA05C07A541BB573D1983B2CA55864DEB8190183A38F | |||
| 2184 | daemon-tools.exe | C:\Users\admin\AppData\Local\Temp\nsqD238.tmp\Lang\DAN.dll | executable | |
MD5:480CA59050881E81D03C1A2E1ACCDBDB | SHA256:A92A44C2C680A360AFFCC6D3468C6D01429EA84CCFB52B1FE1AB0327CD2FE651 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
21
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2184 | daemon-tools.exe | GET | 500 | 167.99.255.139:80 | http://dt.web-search-home.com/getsettings?query=QbxlDcV%2fBk6nHTXP6diD20bhCgRyJLx98tP2iw8RwcBiMWcrVApIDh1Uxiuivzy4AAIvUf2cPzy1qcrVXlNtLRrFs%2fO20X5gveYDPYDYiSyNpuJSEW0%2fIUDoSGShD%2fSwYBL6Kn2J2%2bmhEGQbPMEJewMgBVYpHvLX%2fxlkXRDP%2fMQ%3d | unknown | — | — | unknown |
2412 | msedge.exe | GET | 301 | 138.68.93.157:80 | http://dt-updates.com/license/greeting | unknown | — | — | unknown |
3352 | DTLite.exe | POST | 200 | 138.68.93.157:80 | http://dt-updates.com/license/activate | unknown | — | — | unknown |
3352 | DTLite.exe | POST | 301 | 188.42.46.250:80 | http://depot.mountspace.com/ | unknown | — | — | unknown |
3660 | sidebar.exe | GET | 200 | 108.138.2.173:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | — | — | whitelisted |
3660 | sidebar.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e000c2e47b2f79d2 | unknown | — | — | whitelisted |
3660 | sidebar.exe | GET | 301 | 18.157.65.230:80 | http://www.daemon-tools.cc/rss_news.xml | unknown | — | — | unknown |
3660 | sidebar.exe | GET | 200 | 18.66.145.213:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | unknown | — | — | whitelisted |
3660 | sidebar.exe | GET | 200 | 18.66.145.213:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | — | — | whitelisted |
3660 | sidebar.exe | GET | 200 | 18.173.208.27:80 | http://ocsp.r2m02.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRmbQtwnInkvkvr7BNFR%2BS2lTYPjAQUwDFSzVpQw4J8dHHOy%2Bmc%2BXrrguICEA53iX56lxh1lwK6RR6DH9Y%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
2184 | daemon-tools.exe | 167.99.255.139:80 | dt.web-search-home.com | DIGITALOCEAN-ASN | DE | unknown |
3352 | DTLite.exe | 188.42.46.250:80 | depot.mountspace.com | SERVERS-COM | LU | suspicious |
3352 | DTLite.exe | 18.157.65.230:443 | www.daemon-tools.cc | AMAZON-02 | DE | unknown |
4052 | msedge.exe | 52.182.143.212:443 | nw-umwatson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3352 | DTLite.exe | 138.68.93.157:80 | dt-updates.com | DIGITALOCEAN-ASN | DE | suspicious |
3780 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2412 | msedge.exe | 52.123.224.68:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dt.web-search-home.com |
| unknown |
depot.mountspace.com |
| unknown |
www.daemon-tools.cc |
| unknown |
nw-umwatson.events.data.microsoft.com |
| whitelisted |
dt-updates.com |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1108 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1108 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
Process | Message |
|---|---|
msedge.exe | [0128/141118.814:ERROR:process_info.cc(617)] range at 0x0, size 0x18 fully unreadable
|
msedge.exe | [0128/141118.798:ERROR:process_info.cc(617)] range at 0x0, size 0x18 fully unreadable
|
msedge.exe | [0128/141121.861:ERROR:filesystem_win.cc(130)] GetFileAttributes C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\attachments\ca4b8cf6-ba90-459d-9f3e-322c61677f9b: The system cannot find the file specified. (0x2)
|
msedge.exe | [0128/141121.861:ERROR:filesystem_win.cc(130)] GetFileAttributes C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\attachments\ca4b8cf6-ba90-459d-9f3e-322c61677f9b: The system cannot find the file specified. (0x2)
|
msedge.exe | [0128/141121.892:ERROR:filesystem_win.cc(130)] GetFileAttributes C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\attachments\ca4b8cf6-ba90-459d-9f3e-322c61677f9b: The system cannot find the file specified. (0x2)
|
msedge.exe | [0128/141121.892:ERROR:filesystem_win.cc(130)] GetFileAttributes C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\attachments\ca4b8cf6-ba90-459d-9f3e-322c61677f9b: The system cannot find the file specified. (0x2)
|
msedge.exe | [0128/141123.851:ERROR:process_info.cc(617)] range at 0x0, size 0x18 fully unreadable
|
msedge.exe | [0128/141123.857:ERROR:process_info.cc(617)] range at 0x0, size 0x18 fully unreadable
|
msedge.exe | [0128/141125.504:ERROR:filesystem_win.cc(130)] GetFileAttributes C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\attachments\ca4b8cf6-ba90-459d-9f3e-322c61677f9b: The system cannot find the file specified. (0x2)
|
msedge.exe | [0128/141125.503:ERROR:filesystem_win.cc(130)] GetFileAttributes C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\attachments\ca4b8cf6-ba90-459d-9f3e-322c61677f9b: The system cannot find the file specified. (0x2)
|