| File name: | 新版360文件粉碎机.exe |
| Full analysis: | https://app.any.run/tasks/75efeeaa-56f5-4798-9d24-3eb2d147780d |
| Verdict: | Suspicious activity |
| Analysis date: | November 11, 2019, 06:48:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B53756F0669013A61E969F57BA30AFB4 |
| SHA1: | E8B026B9A480C6A4862B030D44D5293E40DB4455 |
| SHA256: | 80F1266FEC447C9304E9B3CE871354471F0127B28025913839CCB845D36796A8 |
| SSDEEP: | 98304:ZLUEkNpIzy+f2Zq5Ktrt3SYjskbBYRbhC:xWNpIzwIcdBvYRbI |
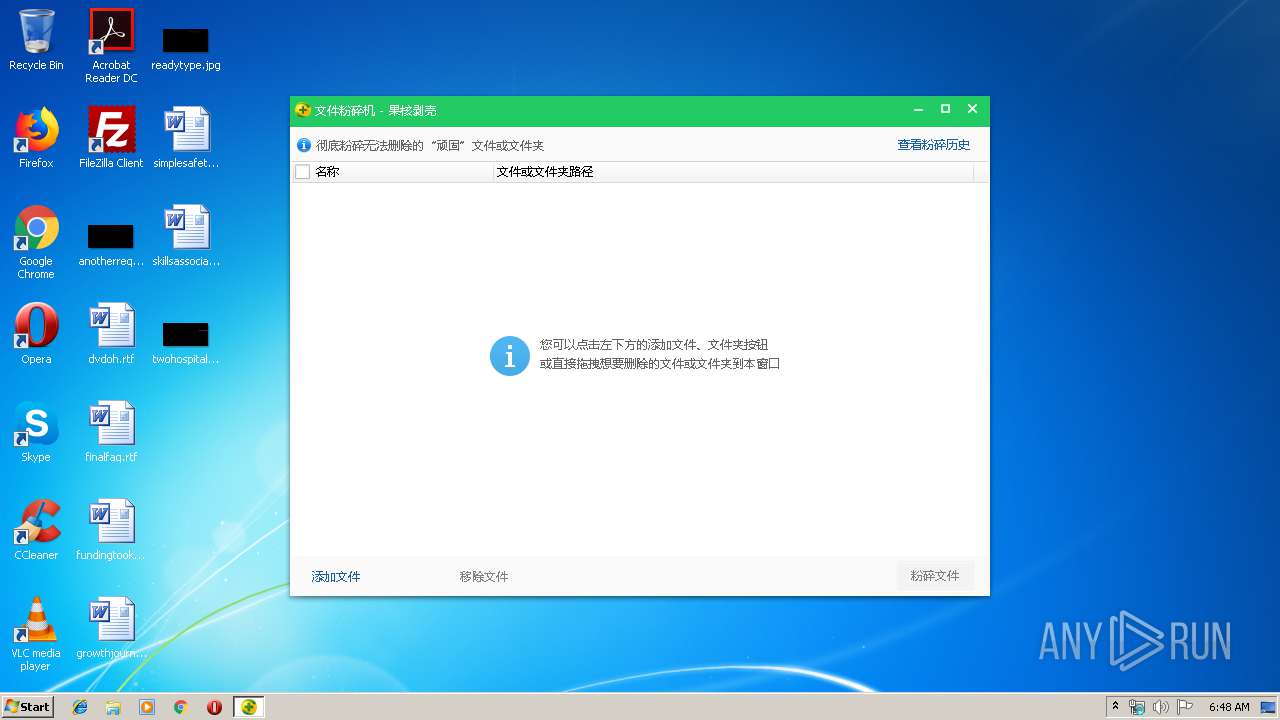
MALICIOUS
Loads dropped or rewritten executable
- FileSmasher.exe (PID: 2728)
Application was dropped or rewritten from another process
- FileSmasher.exe (PID: 2728)
SUSPICIOUS
Executable content was dropped or overwritten
- 新版360文件粉碎机.exe (PID: 3468)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:23 08:32:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 285696 |
| InitializedDataSize: | 191488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x376e7 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.9.8.10907 |
| ProductVersionNumber: | 5.9.8.10907 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 5.9.8.10907 |
| ProductVersion: | 5.9 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Aug-2018 06:32:27 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileVersion: | 5.9.8.10907 |
| ProductVersion: | 5.9 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 23-Aug-2018 06:32:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00045BFC | 0x00045C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6547 |
.rdata | 0x00047000 | 0x00011B18 | 0x00011C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.73914 |
.data | 0x00059000 | 0x0000A540 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65236 |
.rsrc | 0x00064000 | 0x00013F98 | 0x00014000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.5087 |
.reloc | 0x00078000 | 0x000055F4 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.48017 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3159 | 1217 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.7219 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.75392 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
107 | 2.67103 | 90 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
129 | 3.66614 | 476 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
131 | 7.16841 | 16478 | Latin 1 / Western European | Chinese - PRC | RT_BITMAP |
132 | 3.59875 | 758 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
304 | 3.80658 | 336 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
563 | 2.52313 | 82 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
626 | 6.14053 | 436 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2728 | "C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\Utils\FileSmasher.exe" | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\Utils\FileSmasher.exe | — | 新版360文件粉碎机.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: MEDIUM Description: 360安全卫士 文件粉碎机 Exit code: 0 Version: 7, 5, 0, 1056 Modules
| |||||||||||||||
| 3468 | "C:\Users\admin\Downloads\新版360文件粉碎机.exe" | C:\Users\admin\Downloads\新版360文件粉碎机.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.9.8.10907 Modules
| |||||||||||||||
Total events
387
Read events
380
Write events
7
Delete events
0
Modification events
| (PID) Process: | (3468) 新版360文件粉碎机.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3468) 新版360文件粉碎机.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2728) FileSmasher.exe | Key: | HKEY_CURRENT_USER\Software\360Safe |
| Operation: | write | Name: | DefaultSkin |
Value: config\defaultskin | |||
Executable files
8
Suspicious files
3
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | 新版360文件粉碎机.exe | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\Config\config.xml | xml | |
MD5:871E0B0B02E22486FA1BC9D174716195 | SHA256:4D8CE759AFA09EF93FBE42B3F27028572497F4B3A6DE86AAA83D92EEC0E3ECCC | |||
| 3468 | 新版360文件粉碎机.exe | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\360Util.dll | executable | |
MD5:18DAAD9865E7C9294F0444855C886B7A | SHA256:DF85A134EB6FDDA593D1F650D420FFFCDC1A1BF4512FB25FC2E2FB5C5A249A83 | |||
| 3468 | 新版360文件粉碎机.exe | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\360Base.dll | executable | |
MD5:3513CCCDBF86F168A8D5DFAF8FFB8042 | SHA256:AFDF610A735ED617C8275EAA52C46A4D465FE092E174C13073501CB8BADA51AF | |||
| 3468 | 新版360文件粉碎机.exe | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\safemon\wdefence.dll | executable | |
MD5:835212E2D46361902835E35582133CF1 | SHA256:A7BB626C295E968E58297FADA6BF7FAD94436D8C5F8594DD84A5D323B62C2D50 | |||
| 3468 | 新版360文件粉碎机.exe | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\MiniUI.dll | executable | |
MD5:481ECDB043CE58B0EF60B1EABB30F9F3 | SHA256:BF6DC8A724B457564E9E26FA40FD60C428F17ADD456E0BBAA6AB8602FBE7108C | |||
| 3468 | 新版360文件粉碎机.exe | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\Config\FileSmash.xml | xml | |
MD5:0883459193B125EE891BA999BB5A5287 | SHA256:34EF082F3FD626C27B07559FA71C890220B18824A400DBE923F6D1C9E0C28395 | |||
| 3468 | 新版360文件粉碎机.exe | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\360Common.dll | executable | |
MD5:926030598E6B41BC256CD3D0AC9B6CB2 | SHA256:23DAF2E9A6F67C9AD7010D50C3DE72B0EE8411D8EA0B0F10BB32A1C03D786891 | |||
| 3468 | 新版360文件粉碎机.exe | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\Config\newui\compatible\defaultskin\defaultskin_jr.ui | compressed | |
MD5:5D98F391D1226A93467C1B22E22F09A0 | SHA256:E8B15EEECEA611D90620263DCF144ACD92589FD656923E8A3CDEEAD6962188FF | |||
| 3468 | 新版360文件粉碎机.exe | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\Config\defaultskin\defaultskin.ui | compressed | |
MD5:1EA59A9ECC0CF9EF04684060C4795130 | SHA256:80AB0B023867F517B21286B49B3C0C3546C115F086ACD6BB1CB0AE65EEABEDF2 | |||
| 3468 | 新版360文件粉碎机.exe | C:\Users\admin\AppData\Local\Temp\HZ$D.752.3890\Config\newui\themes\default\default_theme.ui | compressed | |
MD5:E59250A5809B25D8C8BD1AC8A70BEAEE | SHA256:C14BA499796DC38C3AFF7F724996613CA11A3C843F2F7F07274483B478482C33 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report