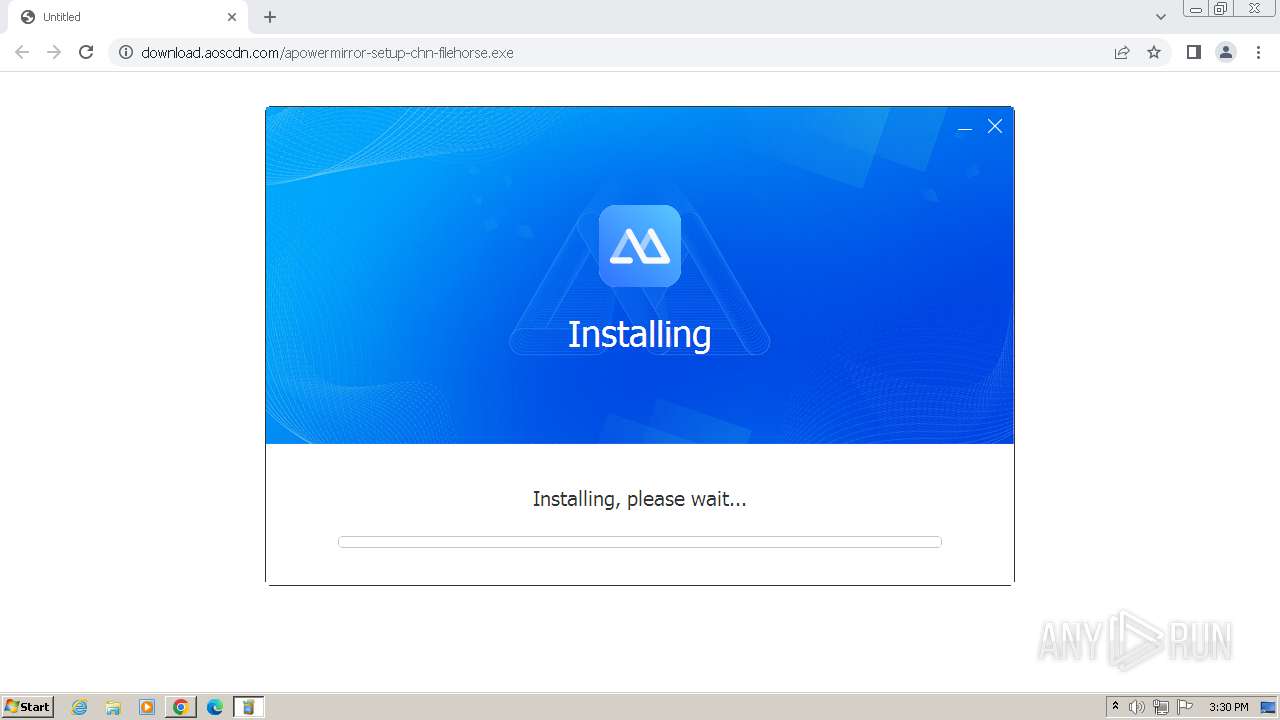
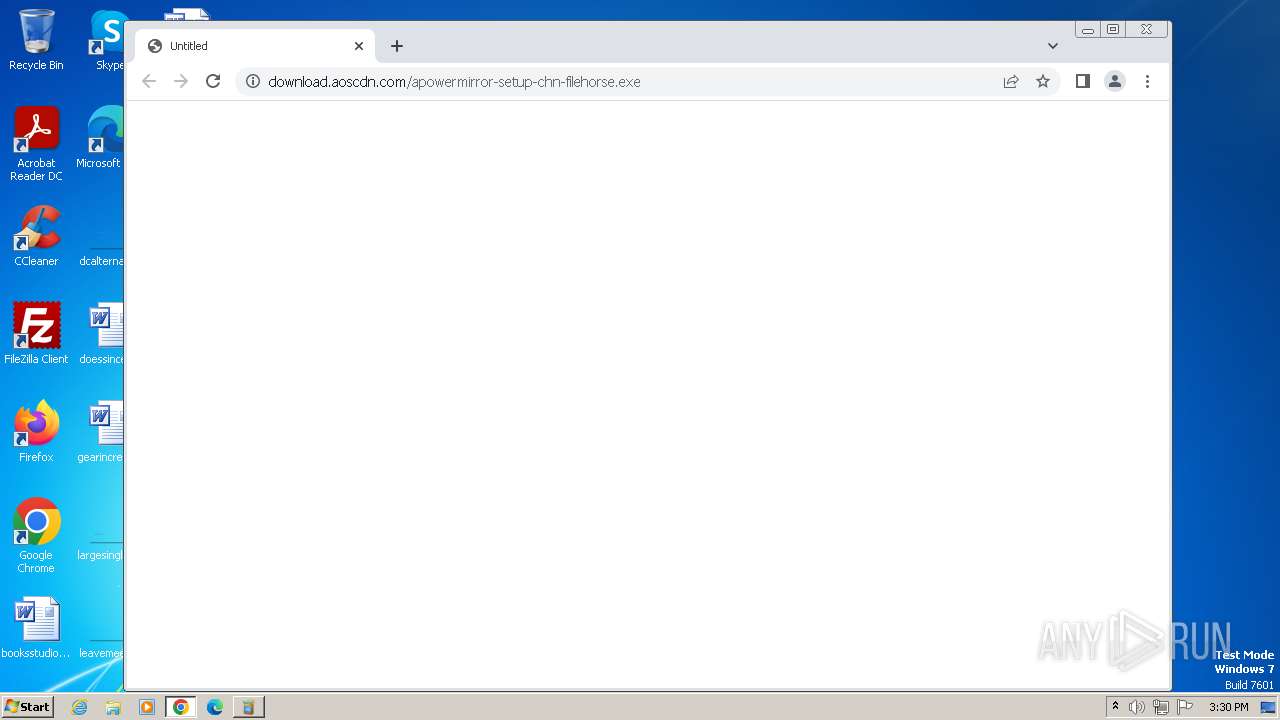
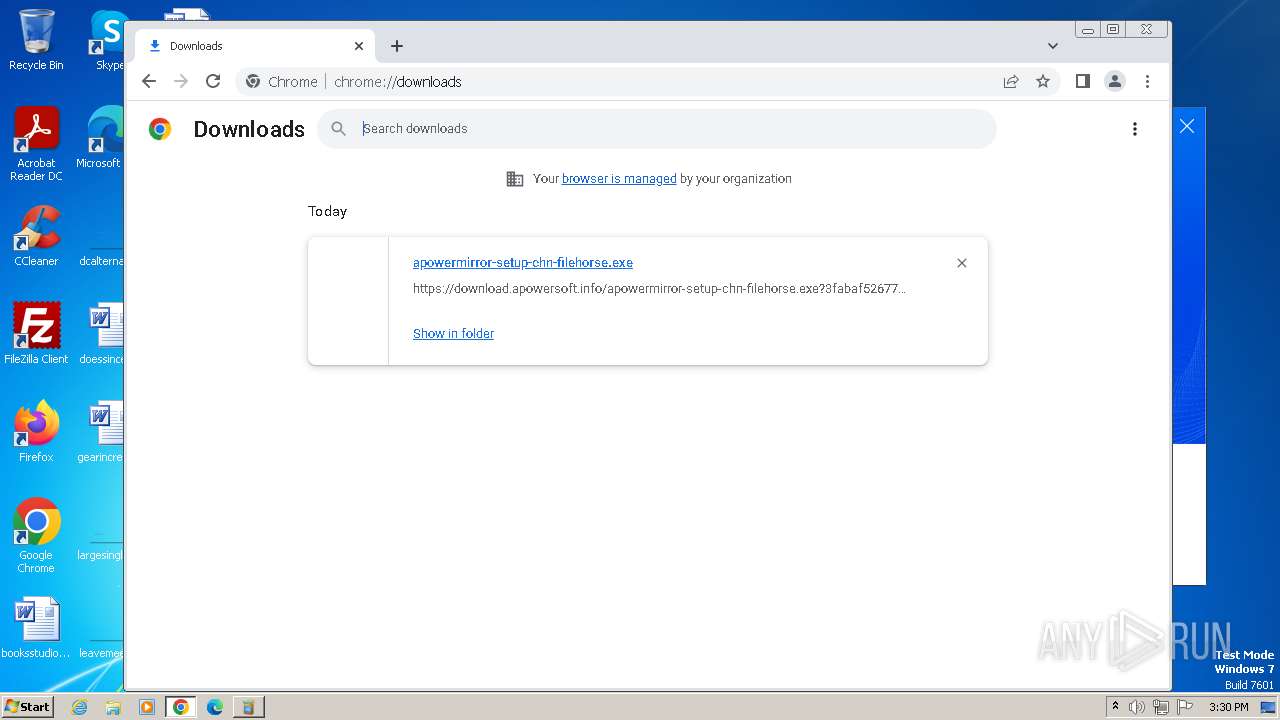
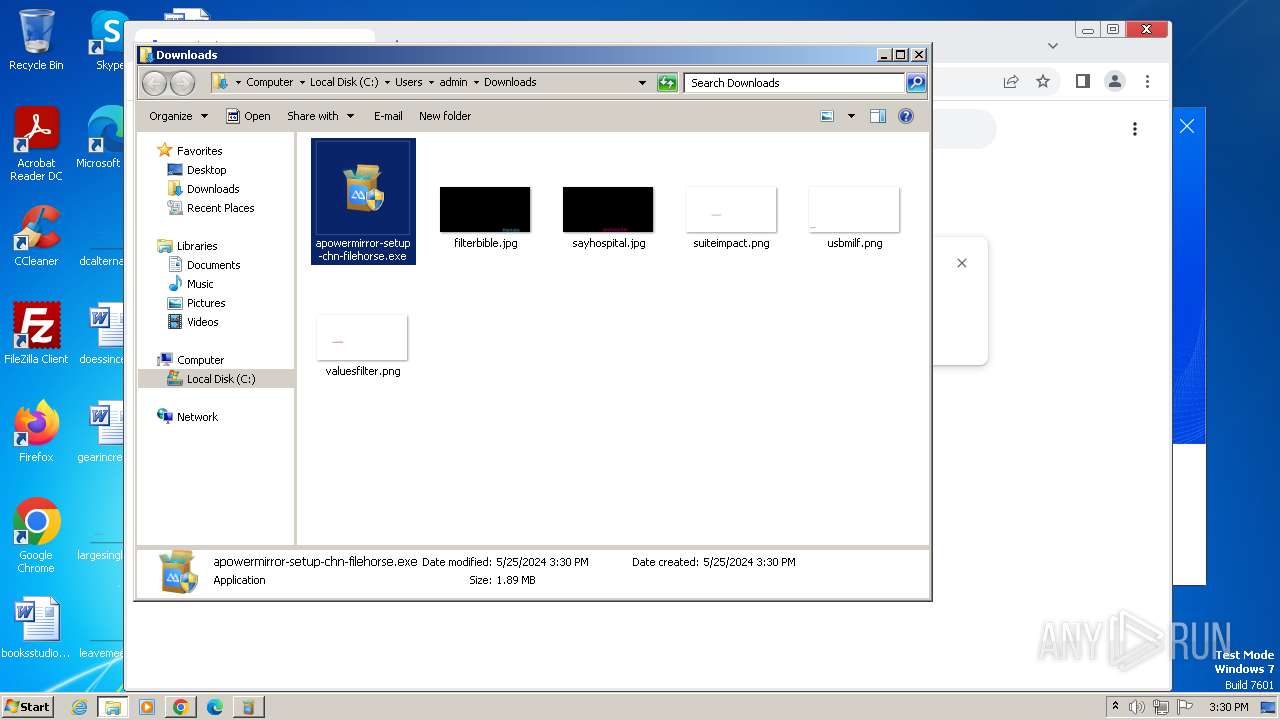
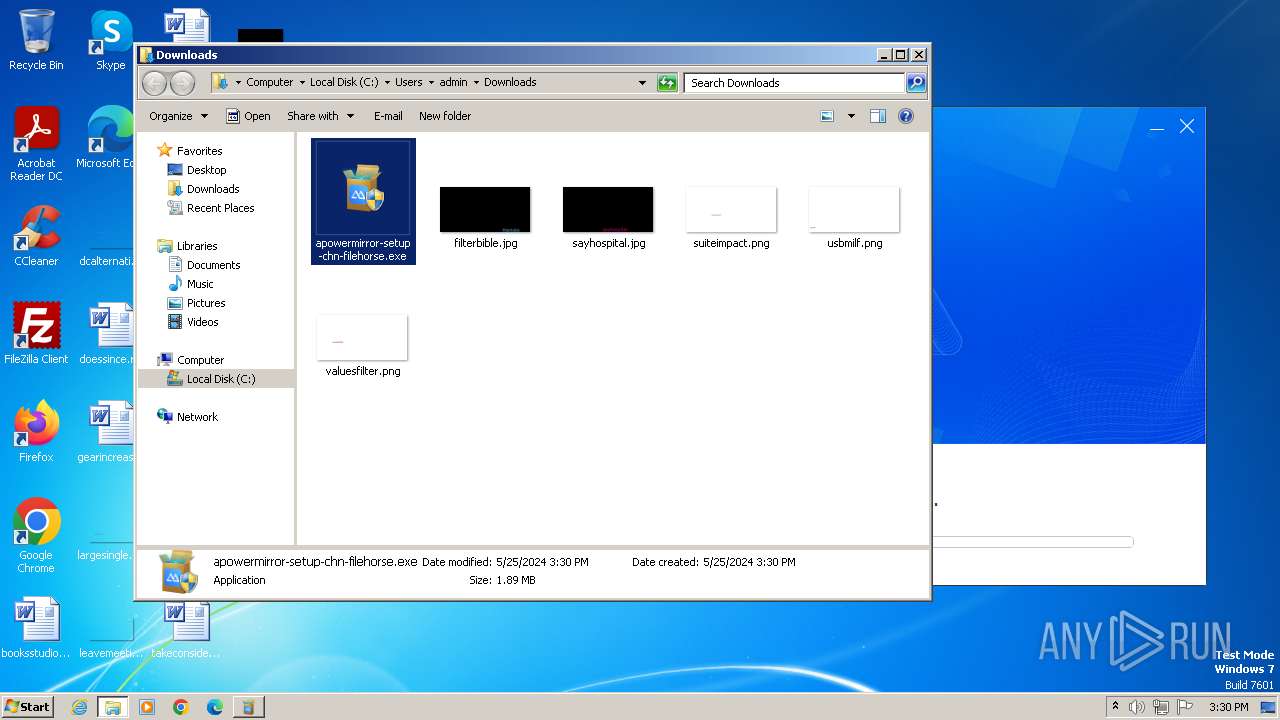
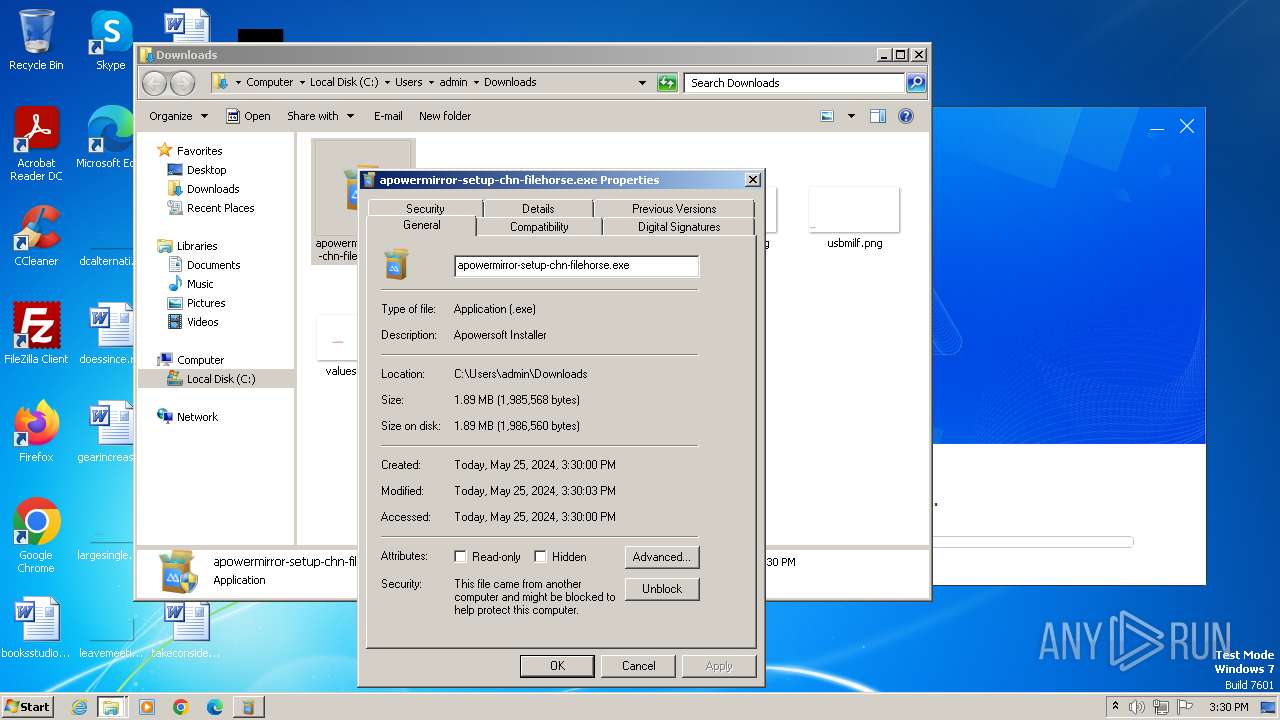
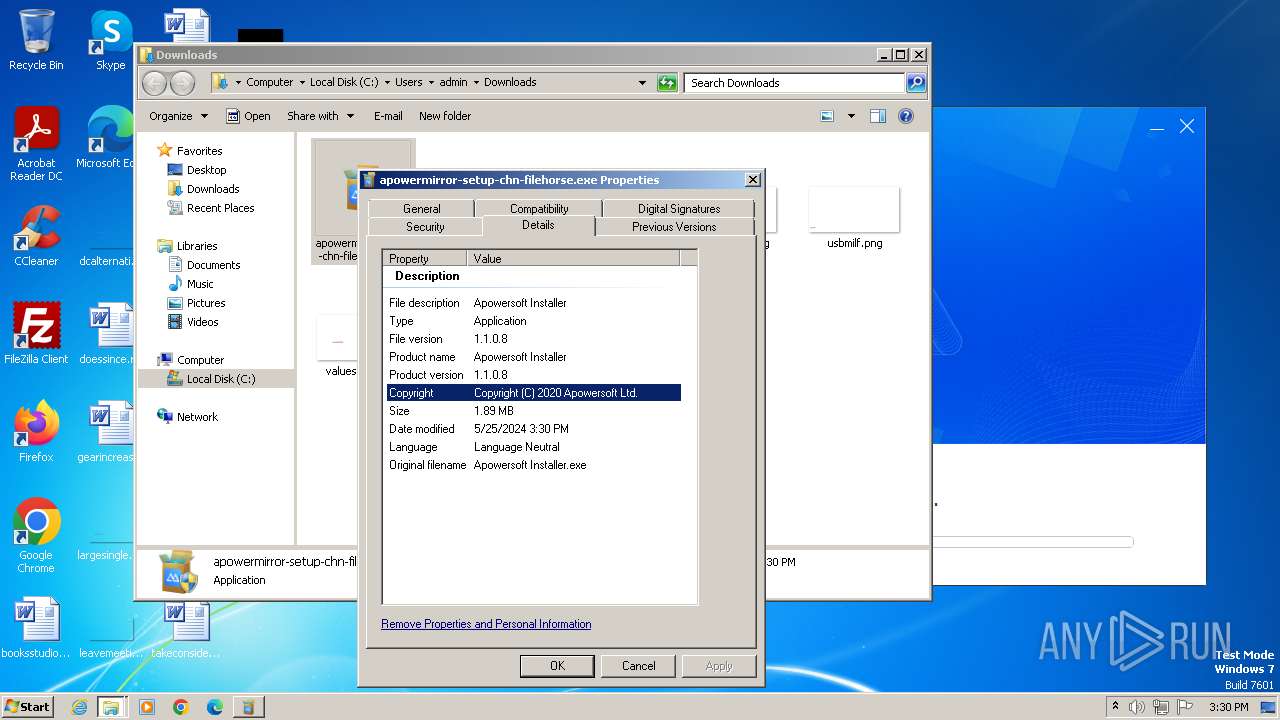
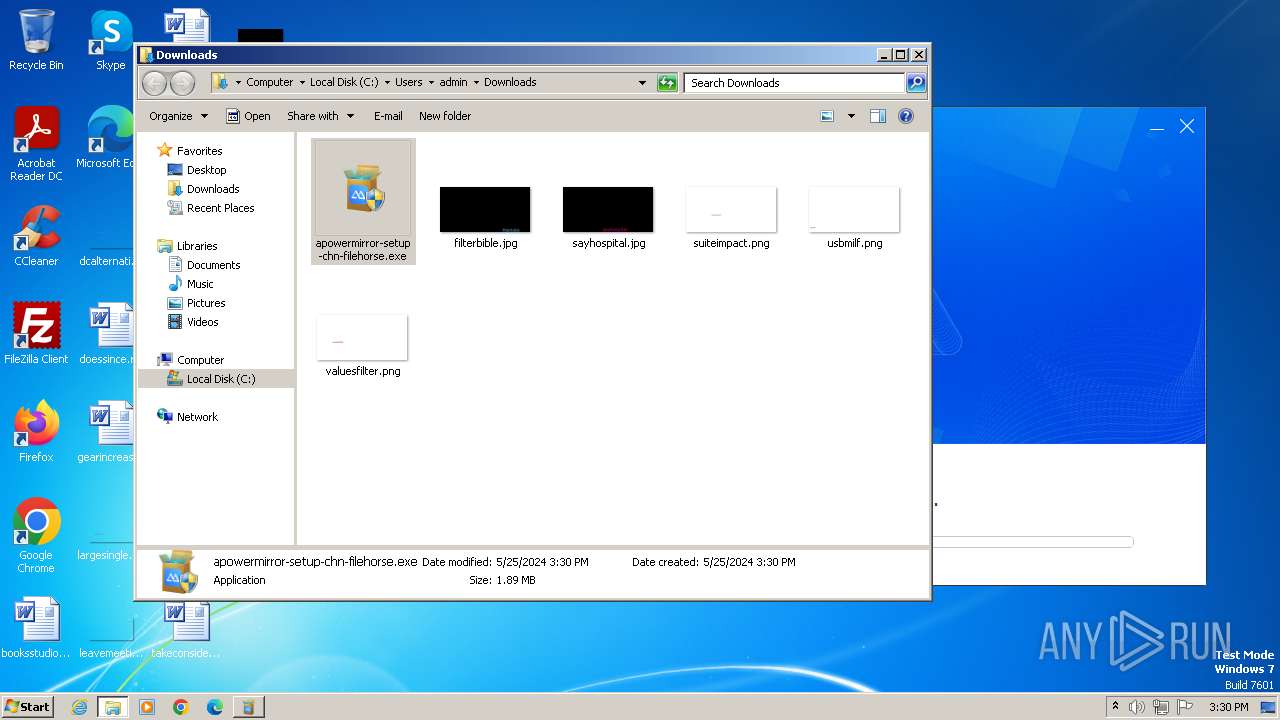
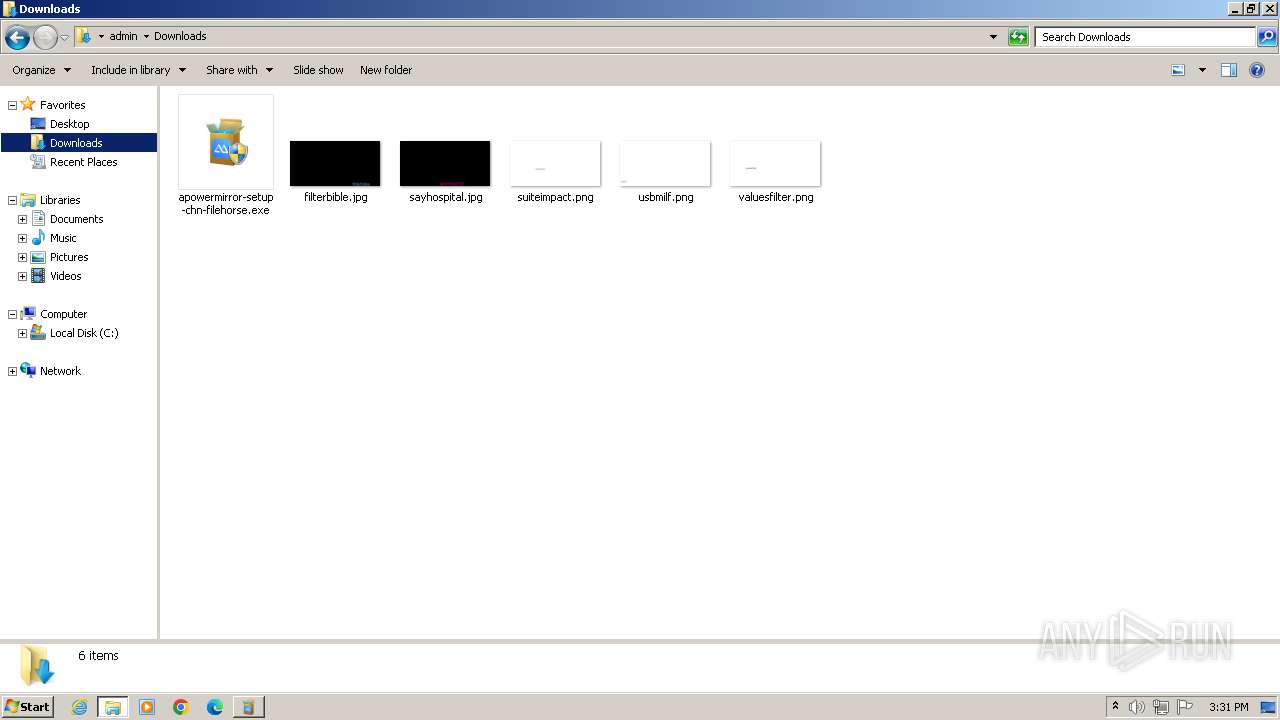
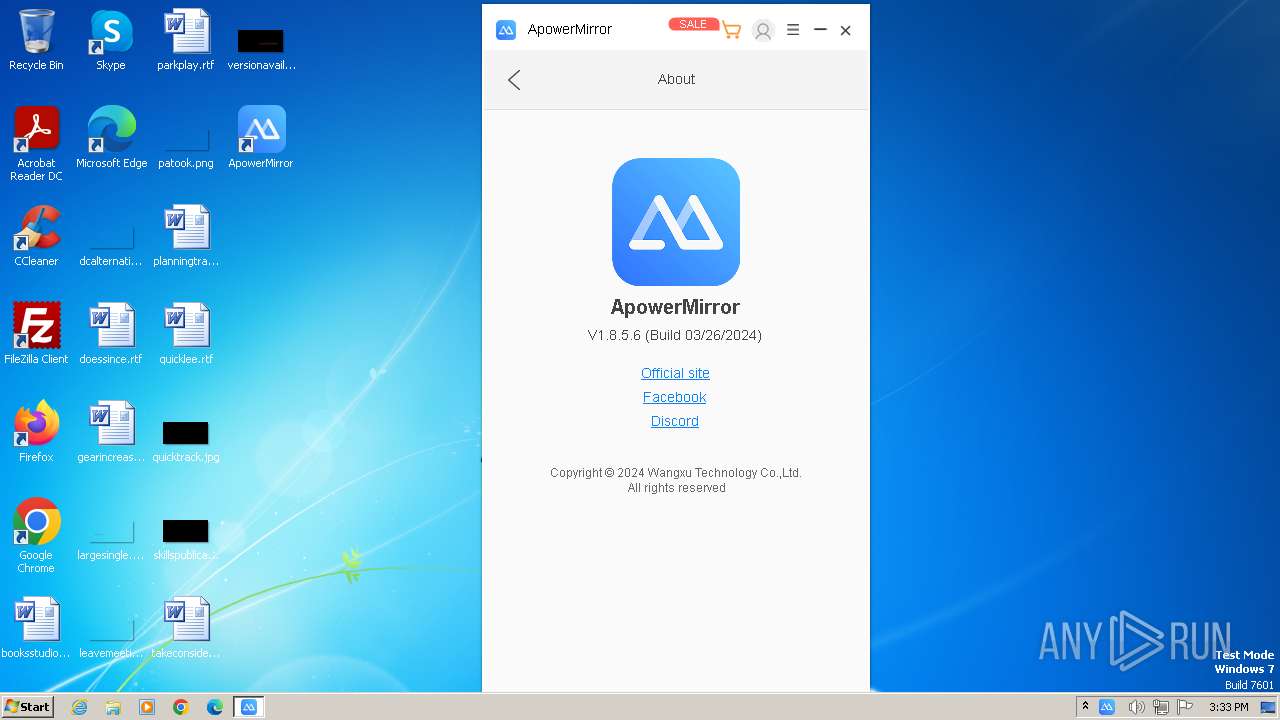
| URL: | https://download.aoscdn.com/apowermirror-setup-chn-filehorse.exe |
| Full analysis: | https://app.any.run/tasks/663a56ec-1adf-4ca6-8184-f9b9051fd097 |
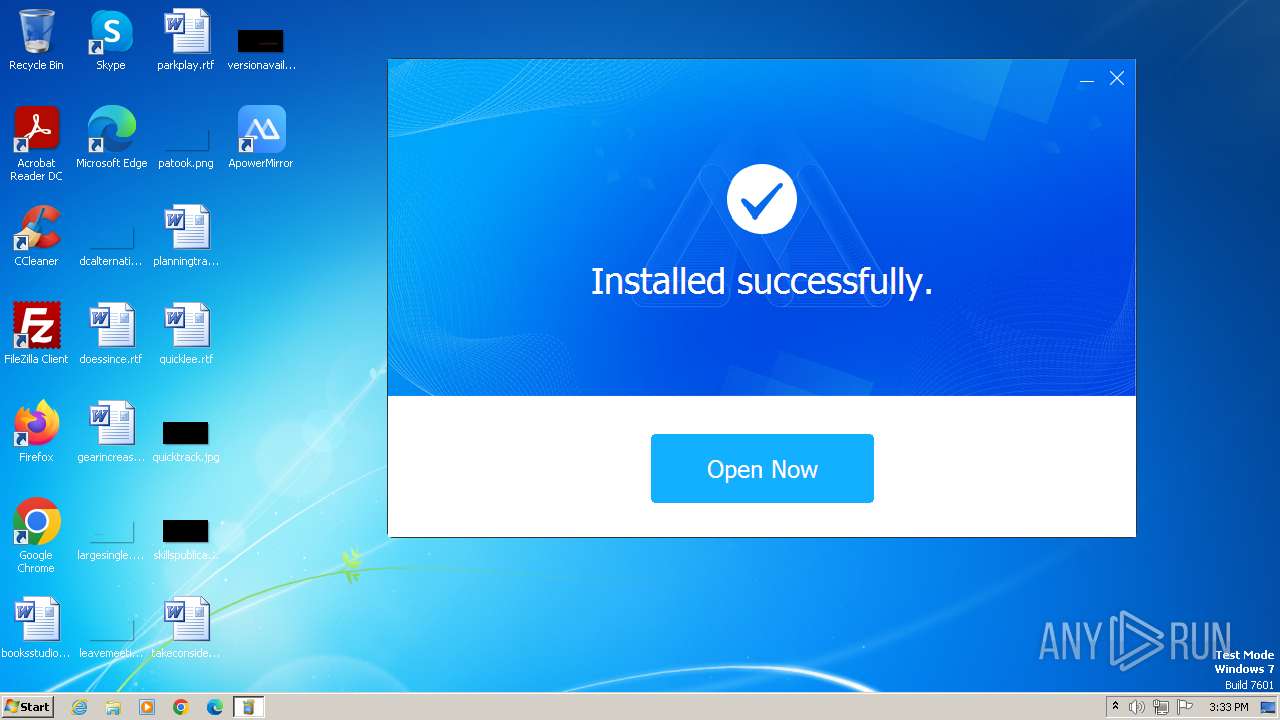
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2024, 14:29:46 |
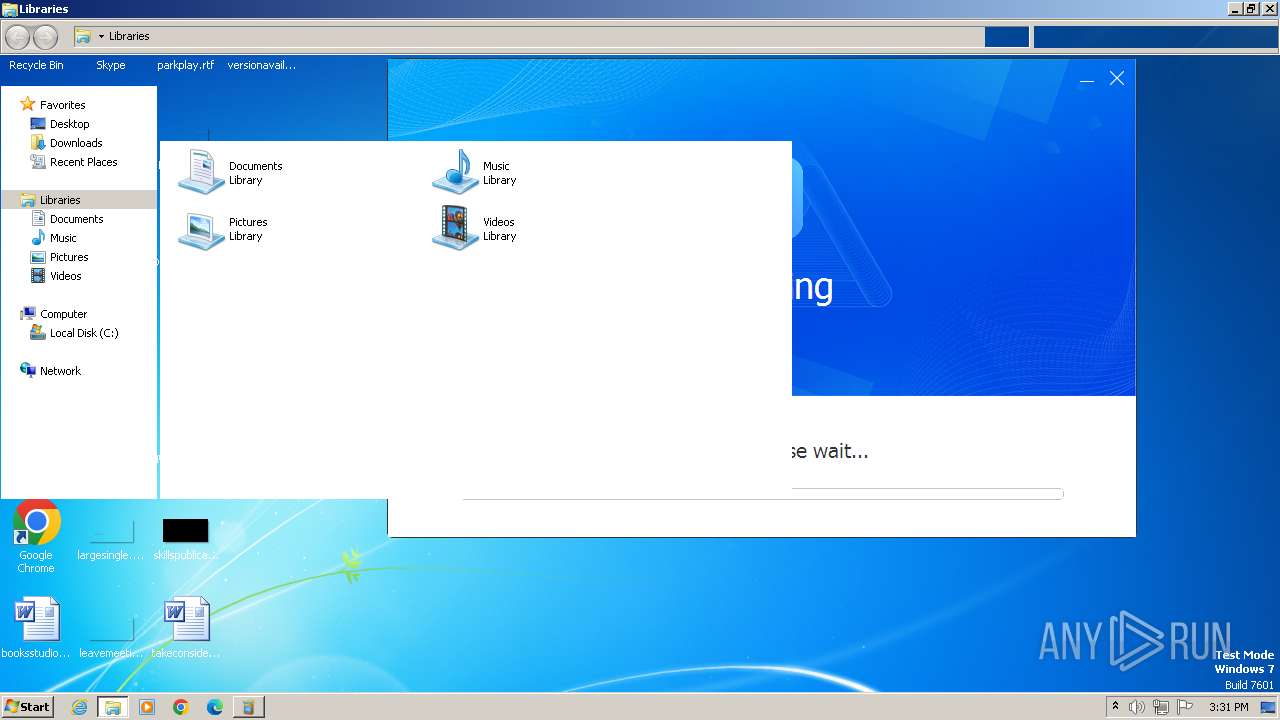
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EC3A524AD9A135EBA452372C2228DAB8 |
| SHA1: | 02E5A2A55A93745FCA008C2C792048774672158D |
| SHA256: | 80D1B09AD474B499C9662608A755CA4CEB9A6B163F23BF4FB60E8187D028A9D9 |
| SSDEEP: | 3:N8SEl32fCxXXsV7zANeAC:2SKGCqwNeAC |
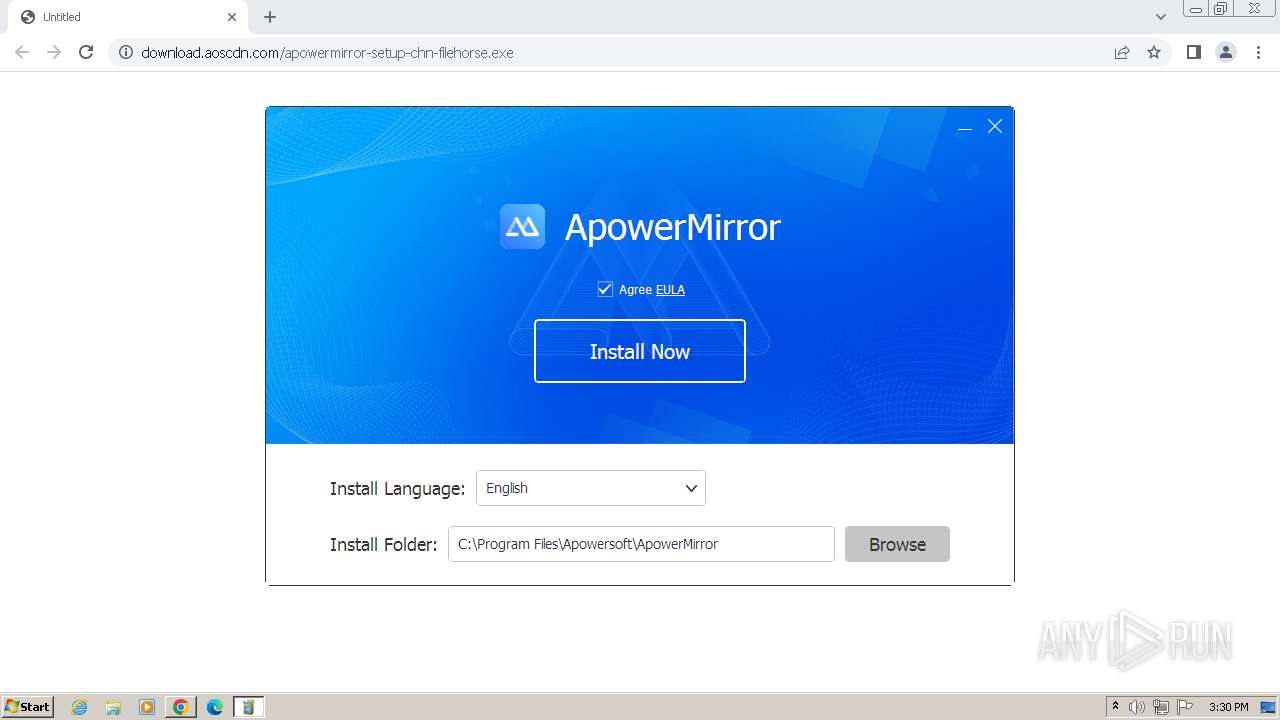
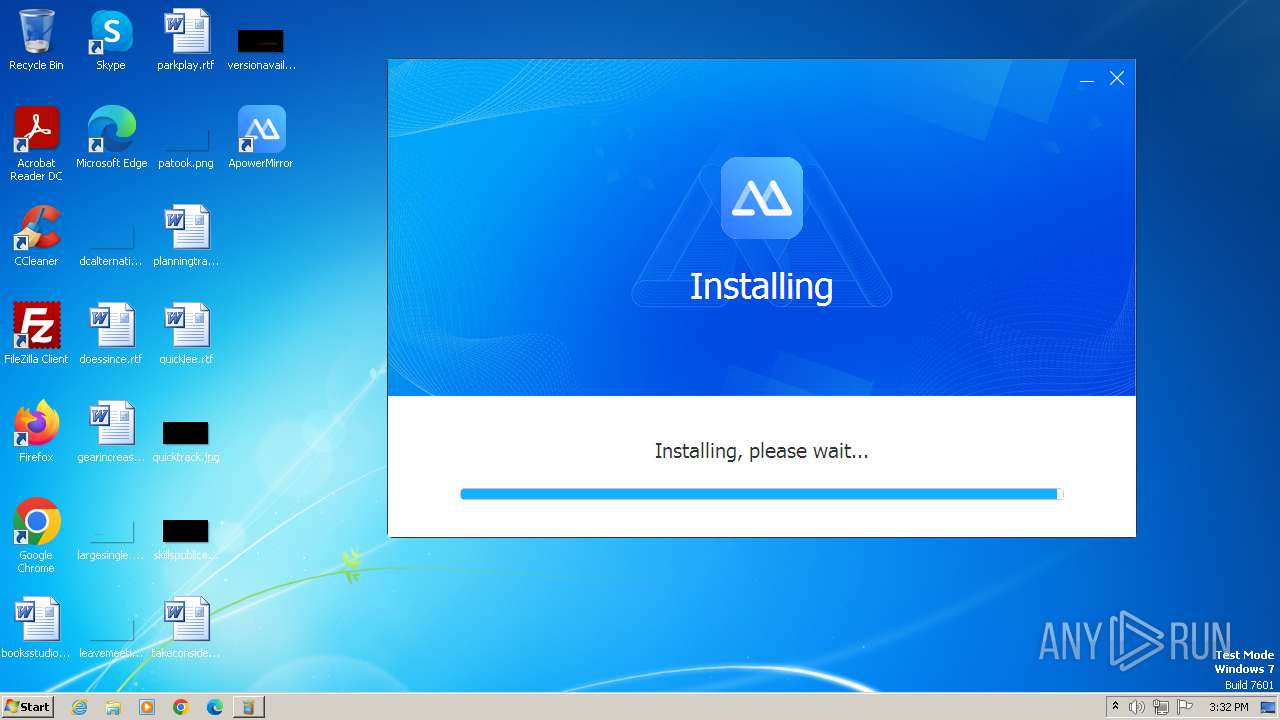
MALICIOUS
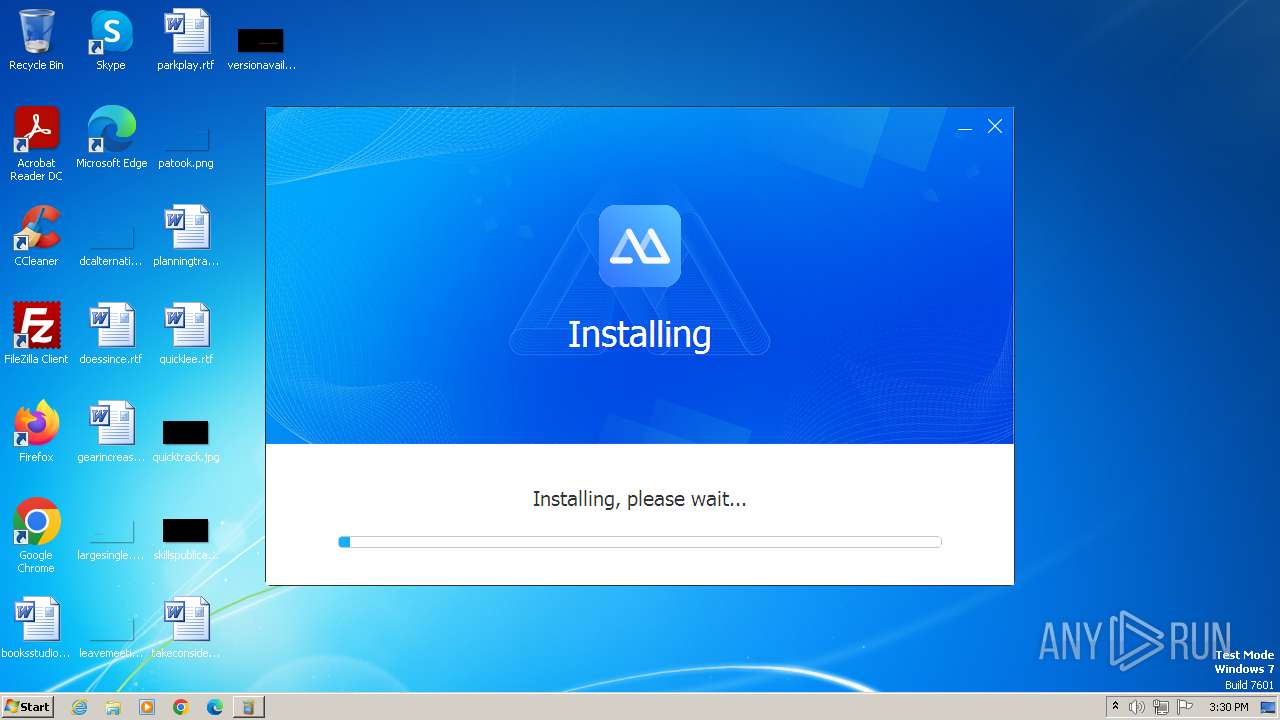
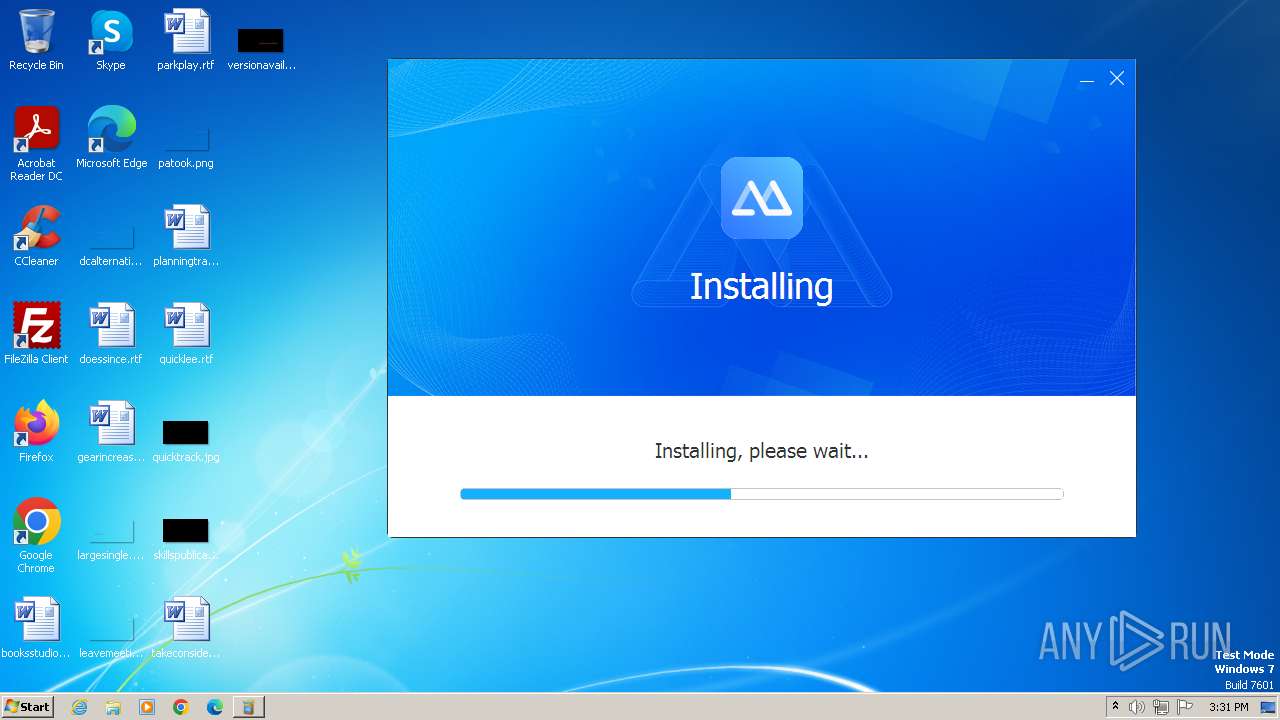
Drops the executable file immediately after the start
- installer.exe (PID: 1296)
- installer.tmp (PID: 2420)
- msiexec.exe (PID: 2644)
Creates a writable file in the system directory
- msiexec.exe (PID: 2644)
SUSPICIOUS
Reads the Internet Settings
- apowermirror-setup-chn-filehorse.exe (PID: 2704)
- msiexec.exe (PID: 4044)
- ApowerMirror.exe (PID: 1284)
Reads security settings of Internet Explorer
- apowermirror-setup-chn-filehorse.exe (PID: 2704)
- ApowerMirror.exe (PID: 1284)
Reads the Windows owner or organization settings
- installer.tmp (PID: 2420)
- msiexec.exe (PID: 2644)
Executable content was dropped or overwritten
- installer.tmp (PID: 2420)
- installer.exe (PID: 1296)
Get information on the list of running processes
- cmd.exe (PID: 2504)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 284)
- cmd.exe (PID: 1856)
Starts CMD.EXE for commands execution
- installer.tmp (PID: 2420)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 284)
Executing commands from a ".bat" file
- installer.tmp (PID: 2420)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2344)
- installer.tmp (PID: 2420)
Application launched itself
- cmd.exe (PID: 2764)
- cmd.exe (PID: 284)
The process drops C-runtime libraries
- installer.tmp (PID: 2420)
Drops 7-zip archiver for unpacking
- installer.tmp (PID: 2420)
Process drops legitimate windows executable
- installer.tmp (PID: 2420)
- msiexec.exe (PID: 2644)
Searches for installed software
- installer.tmp (PID: 2420)
Checks Windows Trust Settings
- msiexec.exe (PID: 2644)
Checks for Java to be installed
- msiexec.exe (PID: 4044)
Executes as Windows Service
- mDNSResponder.exe (PID: 4008)
Changes Internet Explorer settings (feature browser emulation)
- installer.tmp (PID: 2420)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- installer.tmp (PID: 2420)
Uses NETSH.EXE to add a firewall rule or allowed programs
- installer.tmp (PID: 2420)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 2644)
Reads Microsoft Outlook installation path
- ApowerMirror.exe (PID: 1284)
Reads Internet Explorer settings
- ApowerMirror.exe (PID: 1284)
Reads settings of System Certificates
- ApowerMirror.exe (PID: 1284)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 2348)
- apowermirror-setup-chn-filehorse.exe (PID: 2704)
- installer.tmp (PID: 2420)
- msiexec.exe (PID: 2644)
- msiexec.exe (PID: 4044)
- msiexec.exe (PID: 1580)
- mDNSResponder.exe (PID: 4008)
- ApowerMirror.exe (PID: 1284)
Application launched itself
- chrome.exe (PID: 3968)
- chrome.exe (PID: 916)
- msiexec.exe (PID: 2644)
- msedge.exe (PID: 2752)
- msedge.exe (PID: 3684)
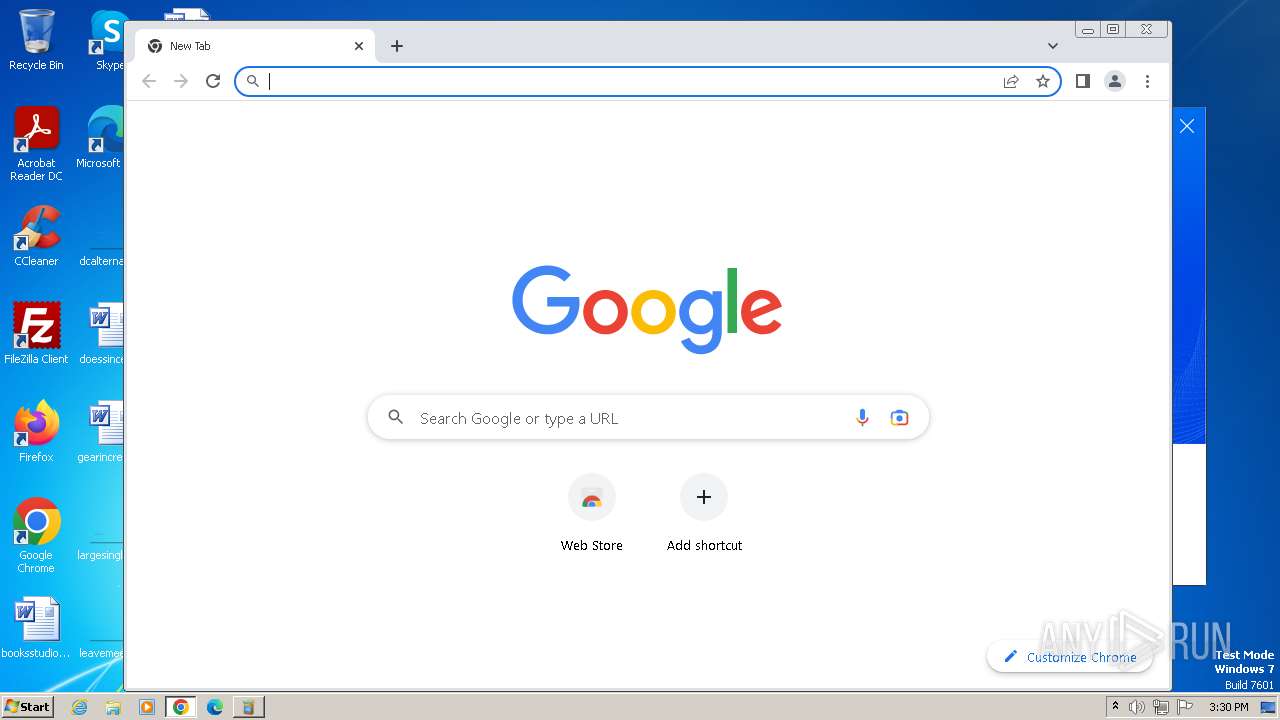
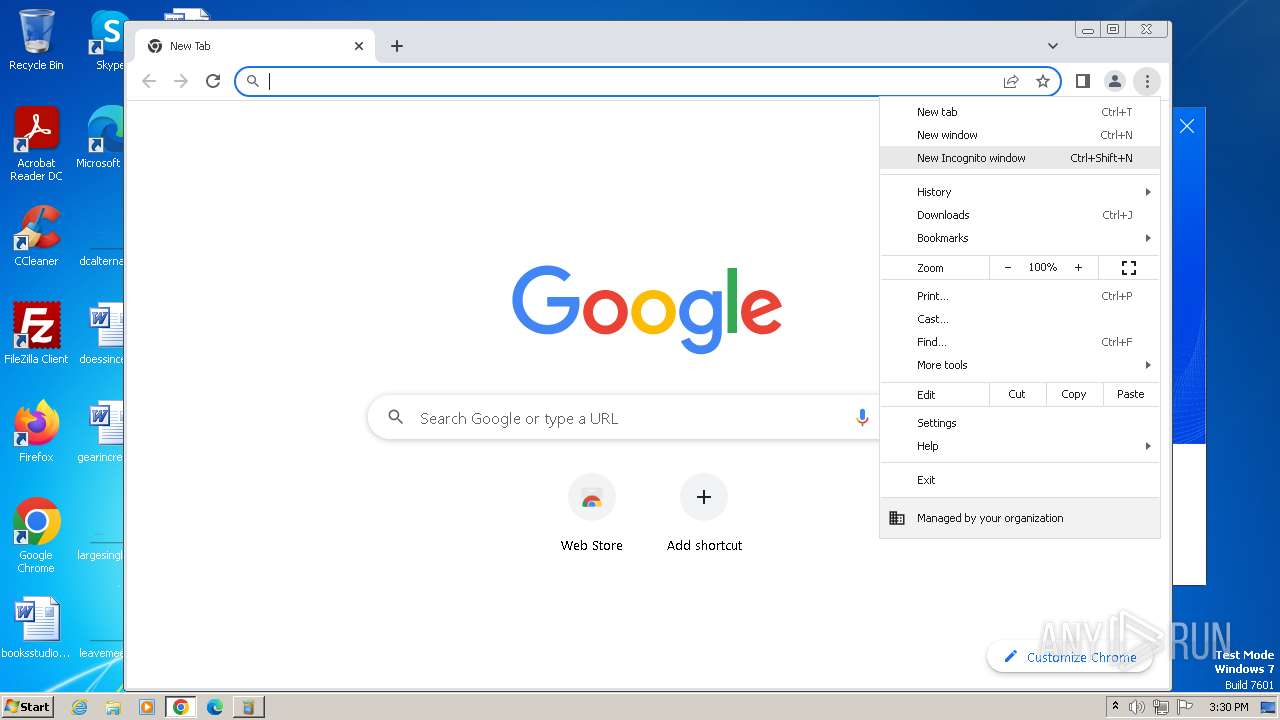
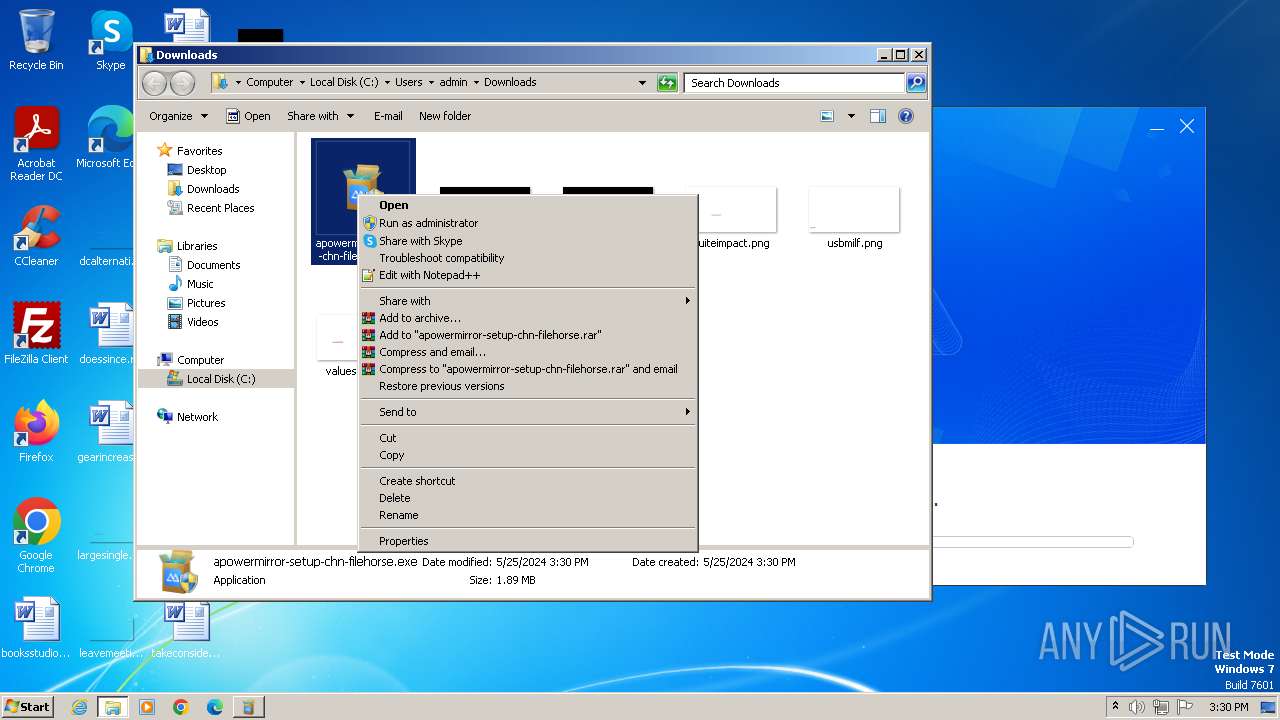
Manual execution by a user
- wmpnscfg.exe (PID: 2348)
- chrome.exe (PID: 916)
- msedge.exe (PID: 3684)
- ApowerMirror.exe (PID: 1284)
- explorer.exe (PID: 992)
Checks supported languages
- wmpnscfg.exe (PID: 2348)
- apowermirror-setup-chn-filehorse.exe (PID: 2704)
- installer.exe (PID: 1296)
- installer.tmp (PID: 2420)
- msiexec.exe (PID: 2644)
- msiexec.exe (PID: 4044)
- msiexec.exe (PID: 1580)
- mDNSResponder.exe (PID: 4008)
- ApowerMirror.exe (PID: 1284)
- adb.exe (PID: 784)
The process uses the downloaded file
- chrome.exe (PID: 2528)
- chrome.exe (PID: 3968)
Executable content was dropped or overwritten
- chrome.exe (PID: 3968)
- msiexec.exe (PID: 2644)
Create files in a temporary directory
- apowermirror-setup-chn-filehorse.exe (PID: 2704)
- installer.tmp (PID: 2420)
- msiexec.exe (PID: 2644)
- installer.exe (PID: 1296)
Reads the machine GUID from the registry
- apowermirror-setup-chn-filehorse.exe (PID: 2704)
- msiexec.exe (PID: 2644)
- msiexec.exe (PID: 4044)
- msiexec.exe (PID: 1580)
- ApowerMirror.exe (PID: 1284)
Creates files in the program directory
- apowermirror-setup-chn-filehorse.exe (PID: 2704)
- installer.tmp (PID: 2420)
- ApowerMirror.exe (PID: 1284)
Drops the executable file immediately after the start
- chrome.exe (PID: 3968)
Creates files or folders in the user directory
- installer.tmp (PID: 2420)
- ApowerMirror.exe (PID: 1284)
Checks proxy server information
- msiexec.exe (PID: 4044)
- ApowerMirror.exe (PID: 1284)
Reads the software policy settings
- msiexec.exe (PID: 2644)
- ApowerMirror.exe (PID: 1284)
Creates a software uninstall entry
- msiexec.exe (PID: 2644)
- installer.tmp (PID: 2420)
Reads Environment values
- ApowerMirror.exe (PID: 1284)
Process checks computer location settings
- ApowerMirror.exe (PID: 1284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
124
Monitored processes
73
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Windows\system32\cmd.exe" /C ""C:\Users\admin\AppData\Local\Temp\is-TF0VI.tmp\KillProcessWithName.bat" "ApowerMirror.exe"" | C:\Windows\System32\cmd.exe | — | installer.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 304 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="ApowerMirror" dir=in action=allow program="C:\Program Files\Apowersoft\ApowerMirror\ApowerMirror.exe" enable=yes | C:\Windows\System32\netsh.exe | — | installer.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 616 | find "ApowerMirror.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 736 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6c76f598,0x6c76f5a8,0x6c76f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 748 | "C:\Windows\system32\taskkill.exe" /f /t /im "ApowersoftAndroidDaemon.exe" | C:\Windows\System32\taskkill.exe | — | installer.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 784 | adb -L tcp:5037 fork-server server | C:\Program Files\Apowersoft\ApowerMirror\adb.exe | — | ApowerMirror.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1348 --field-trial-handle=1148,i,1835017371122547400,15868339868222336286,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 904 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3256 --field-trial-handle=1248,i,2457720651860269316,6655143058799619765,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
82 905
Read events
82 256
Write events
610
Delete events
39
Modification events
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
236
Suspicious files
189
Text files
900
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1034ed.TMP | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10350c.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old | text | |
MD5:6344721DA60A3CF7027C43288C8991C6 | SHA256:DA3AD5C3641E42979DFB9D4178EDE8533F887C3ACF9C49BE9737D83CEDA55473 | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF103664.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF104681.TMP | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF103683.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
124
DNS requests
68
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2704 | apowermirror-setup-chn-filehorse.exe | GET | 200 | 47.244.67.195:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=8287a29015fb0005117c3061d4580267&session_id=1716647404&app=ApowerMirror&appid=113&apptype=chn-filehorse&installer_version=1.1.0.8&is_old_user=-1&last_step_duration=0&os_available_memory=2457620000&os_culture=0409&os_dpi=100&os_fullname=Microsoft%20Windows%207%20Professional%20&os_lang=en-US&os_resolution=1280x720&os_total_memory=3145208000&os_version=6.1.7601&step=1 | unknown | — | — | unknown |
2704 | apowermirror-setup-chn-filehorse.exe | GET | 200 | 47.244.67.195:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=8287a29015fb0005117c3061d4580267&session_id=1716647404&app=ApowerMirror&app_install_path=C%3A%5CProgram%20Files%5CApowersoft%5CApowerMirror&app_lang=English&appid=113&apptype=chn-filehorse&last_step_duration=2&step=2 | unknown | — | — | unknown |
2704 | apowermirror-setup-chn-filehorse.exe | GET | 302 | 47.243.121.132:80 | http://download.aoscdn.com/down.php?softid=apowermirrorinstall-chn-filehorse | unknown | — | — | unknown |
2704 | apowermirror-setup-chn-filehorse.exe | GET | 404 | 163.181.92.226:80 | http://cdn.aoscdn.com/img/contact-group/installer-113-qq.jpg?19868 | unknown | — | — | unknown |
2704 | apowermirror-setup-chn-filehorse.exe | GET | 200 | 47.90.119.19:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=8287a29015fb0005117c3061d4580267&session_id=1716647404&app=ApowerMirror&appid=113&ga_error=&ga_ok=0&ga_response=&gaid=&step=2 | unknown | — | — | unknown |
2420 | installer.tmp | GET | 200 | 47.90.119.19:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/win-setup/track?APIVersion=0.6.0&__topic__=install&appid=113&apptype=saas | unknown | — | — | unknown |
2704 | apowermirror-setup-chn-filehorse.exe | GET | 200 | 47.90.119.19:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=8287a29015fb0005117c3061d4580267&session_id=1716647404&app=ApowerMirror&appid=113&installed=1&installed_ts=1716647567&step=2 | unknown | — | — | unknown |
2704 | apowermirror-setup-chn-filehorse.exe | GET | 200 | 47.90.119.19:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=8287a29015fb0005117c3061d4580267&session_id=1716647404&app=ApowerMirror&app_size=134106080&app_version=1.8.5.6&appid=113&apptype=chn-filehorse&download_duration=78&download_retry=0&install_duration=82&install_retry=0&last_step_duration=166&step=3&success=1 | unknown | — | — | unknown |
1284 | ApowerMirror.exe | POST | 200 | 47.90.119.19:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/113 | unknown | — | — | unknown |
2892 | msedge.exe | GET | 302 | 47.243.121.132:80 | http://r.aoscdn.com/jumper?type=install&product_id=113&language=en&unique_id=8287a29015fb0005117c3061d4580267&apptype=chn-filehorse&appver=1.8.5.6&first_install_ts=1716647567&ts=1716647567&wxga=&ct=0&mt=0&h=&hash=ae770cbead2da2b7dbbf0770e6f2c238 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
820 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3968 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
820 | chrome.exe | 47.243.121.132:443 | download.aoscdn.com | Alibaba US Technology Co., Ltd. | HK | unknown |
820 | chrome.exe | 104.26.5.201:443 | download.apowersoft.info | CLOUDFLARENET | US | unknown |
820 | chrome.exe | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
3968 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
820 | chrome.exe | 216.58.206.46:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.aoscdn.com |
| unknown |
accounts.google.com |
| shared |
download.apowersoft.info |
| unknown |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
wx-user-behavior.cn-hongkong.log.aliyuncs.com |
| unknown |
cdn.aoscdn.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| unknown |
config.edge.skype.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
1088 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
2892 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
2892 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
— | — | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
— | — | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |