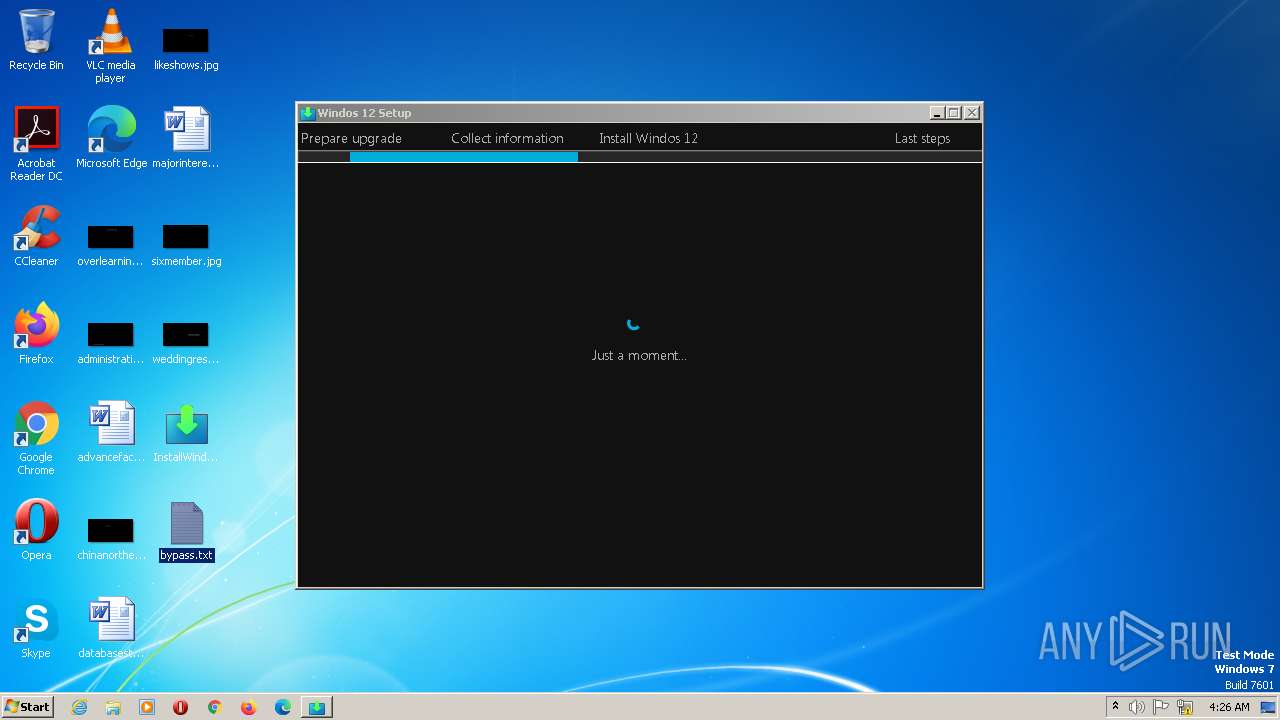
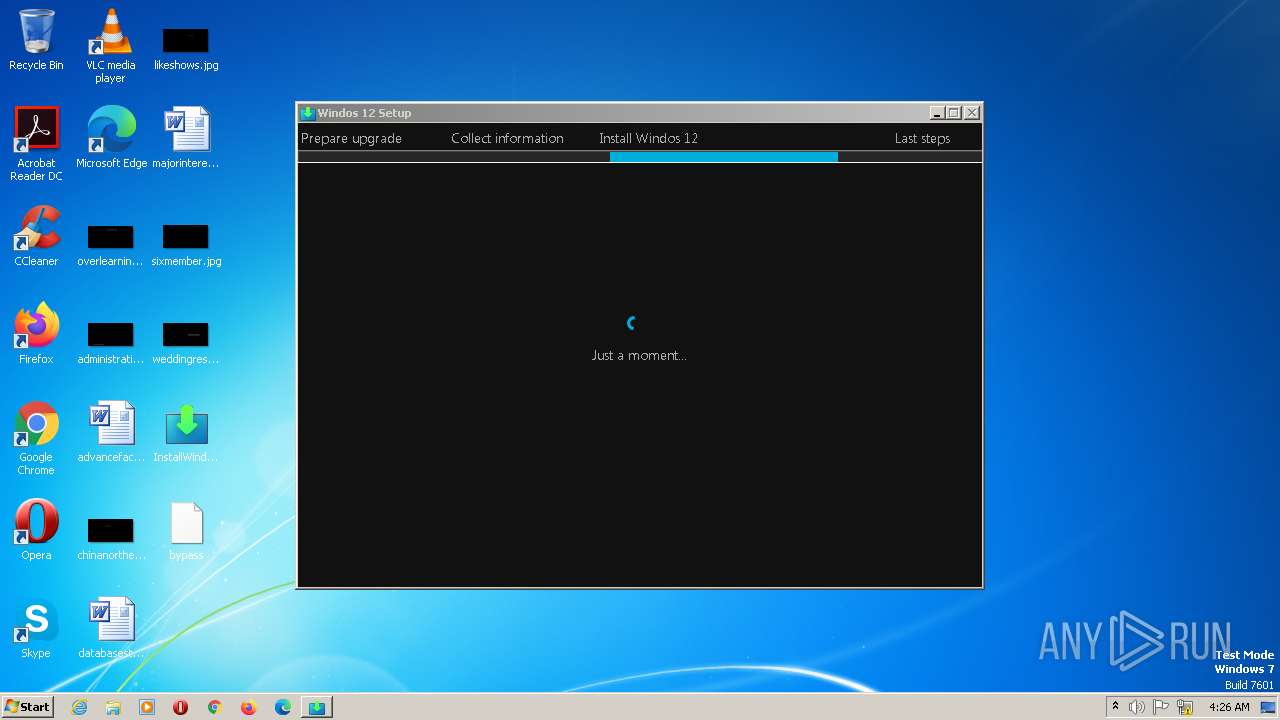
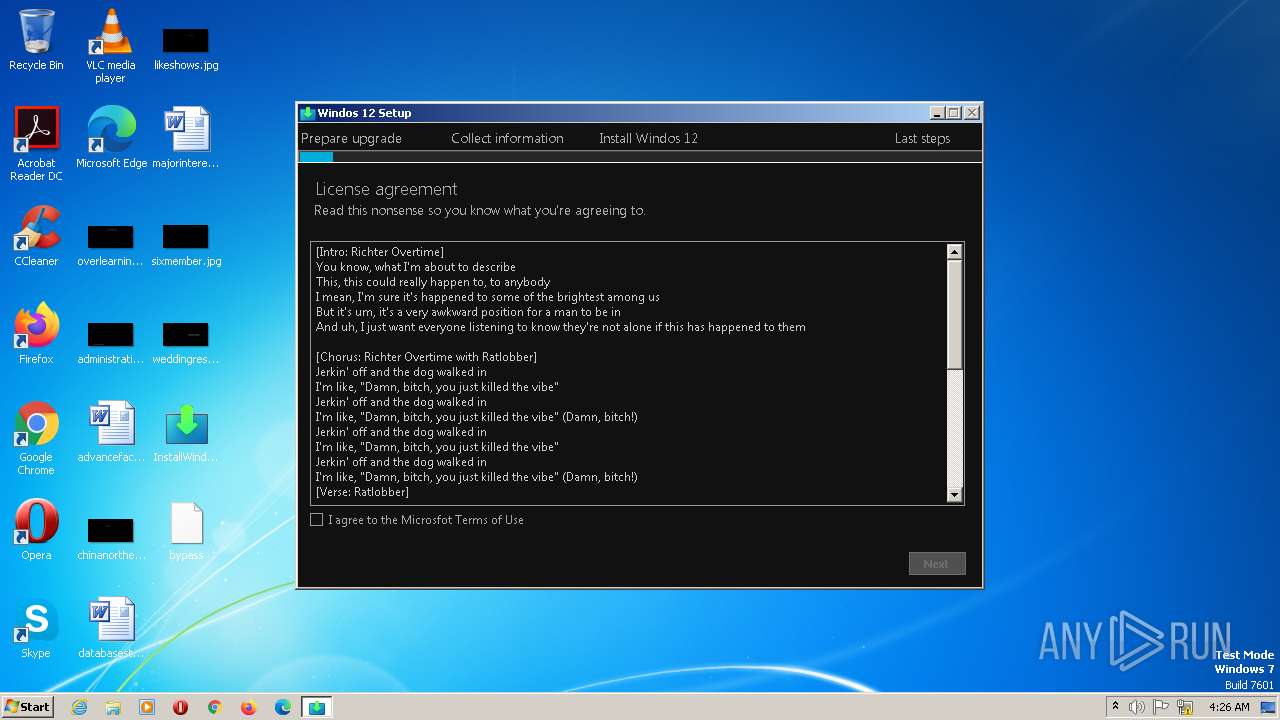
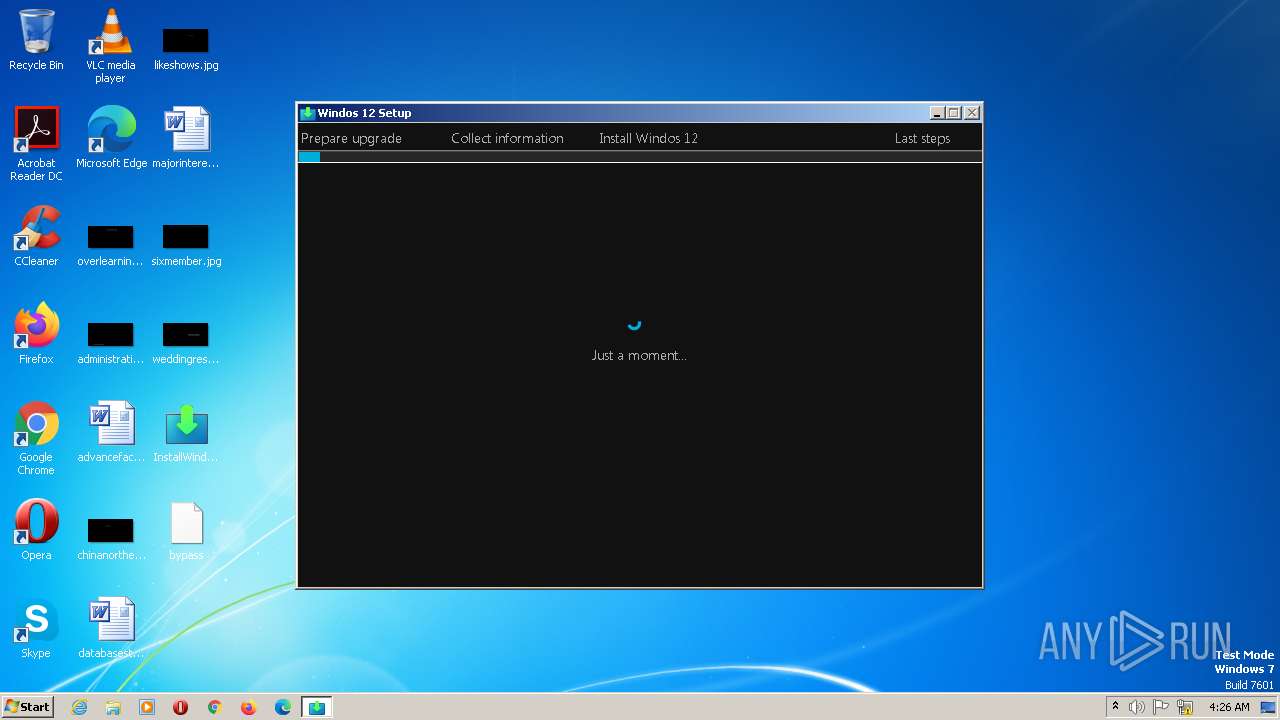
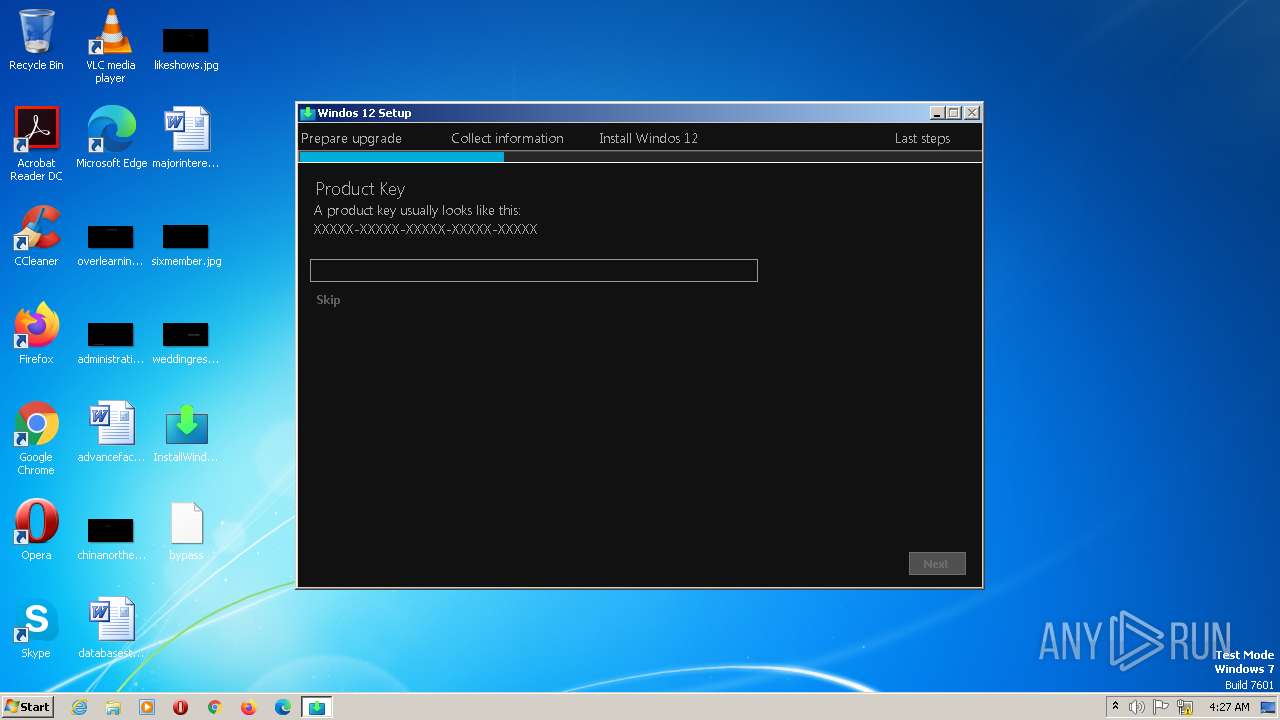
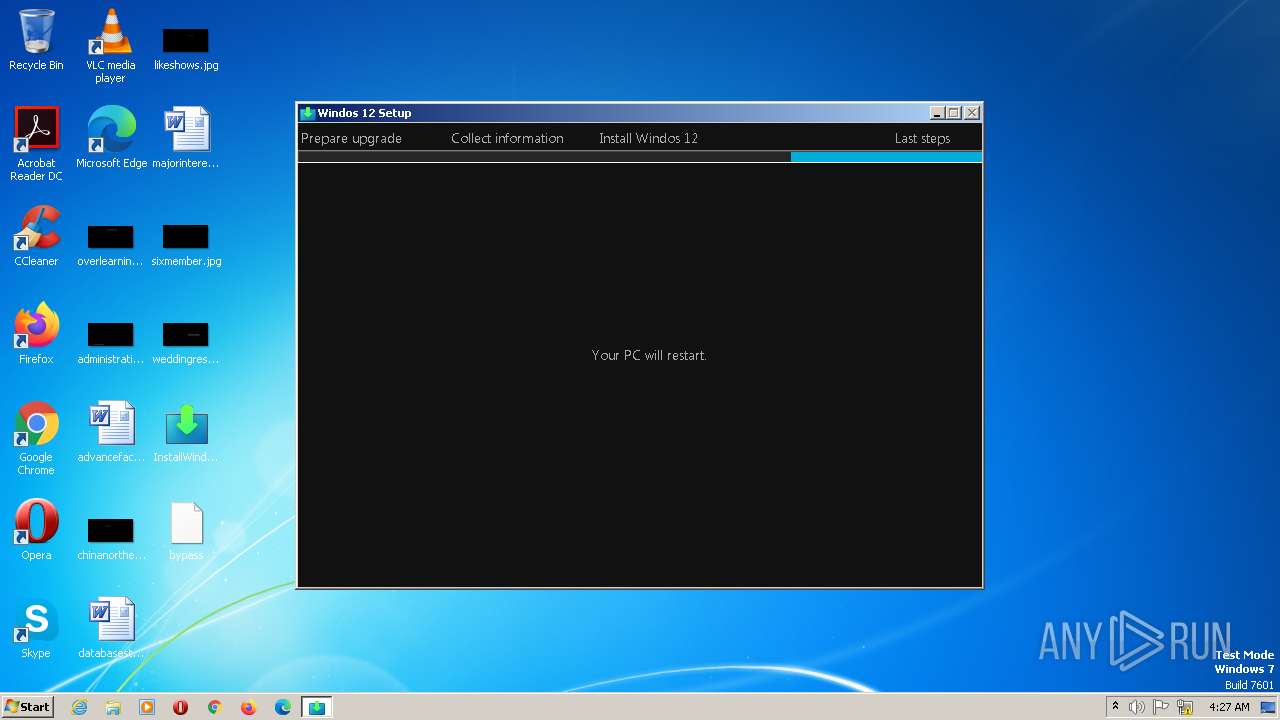
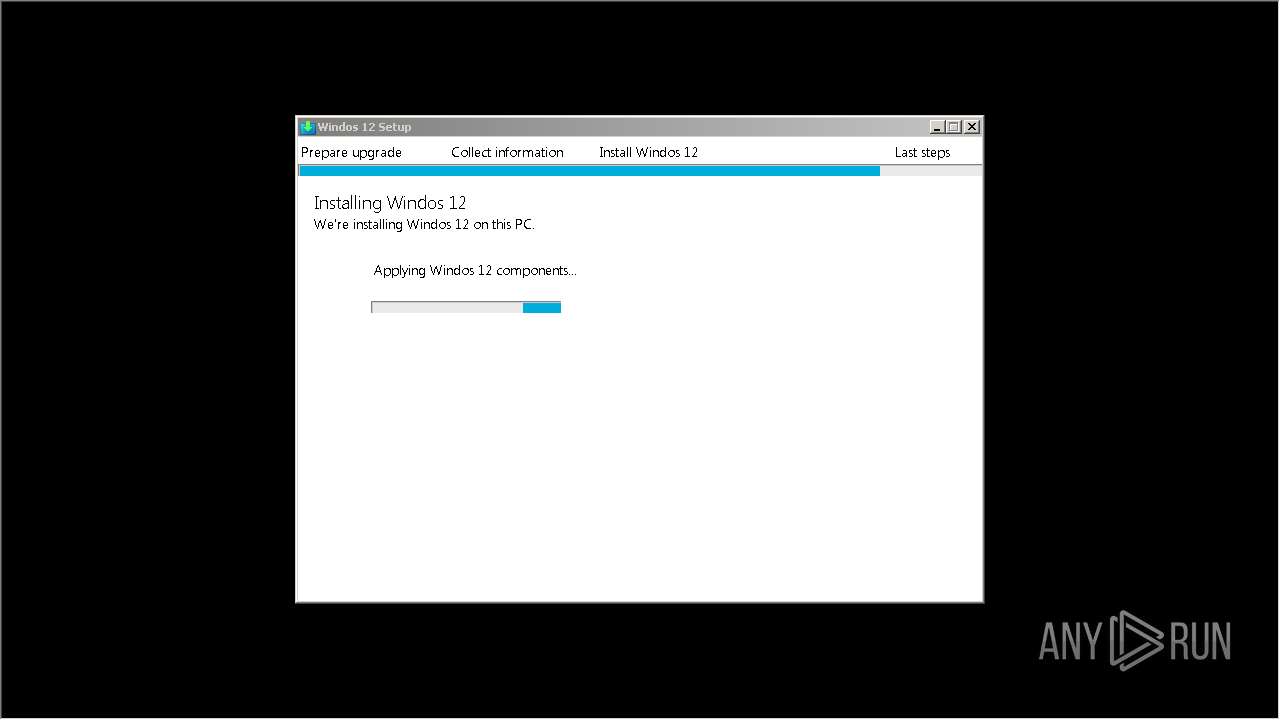
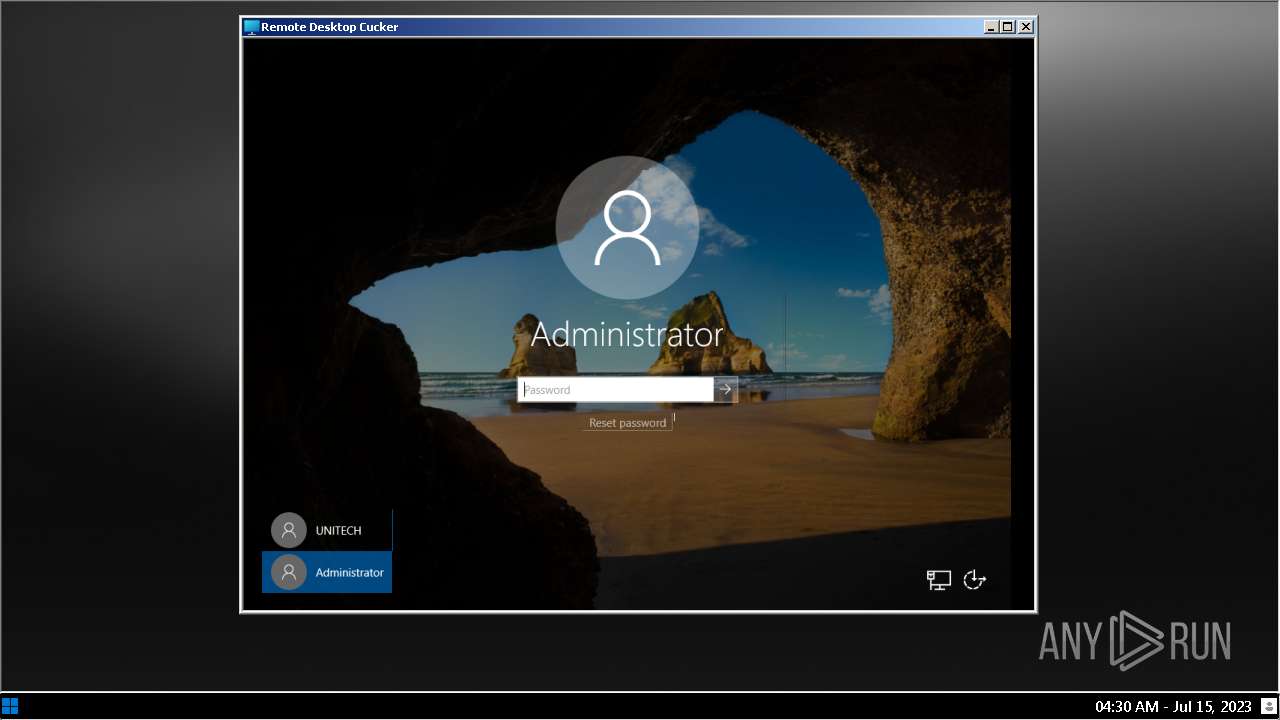
| File name: | InstallWindos12.exe |
| Full analysis: | https://app.any.run/tasks/6f240b15-e3e4-4326-a619-cdc25bffe3af |
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2023, 04:25:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 664DA061808BAE528082E03320482DD4 |
| SHA1: | 855EAE850A9733E951973B3F23B9CA23E7A1CF81 |
| SHA256: | 80C8B06CDFE7FBF8054AC7FBAD1264115E0E7913EC19C04C25E6AAB2CC1948F1 |
| SSDEEP: | 196608:VYNSCFRn9zx3C9InOKYcK9InOKzcpwemh4:uzCITY7ITzI5m |
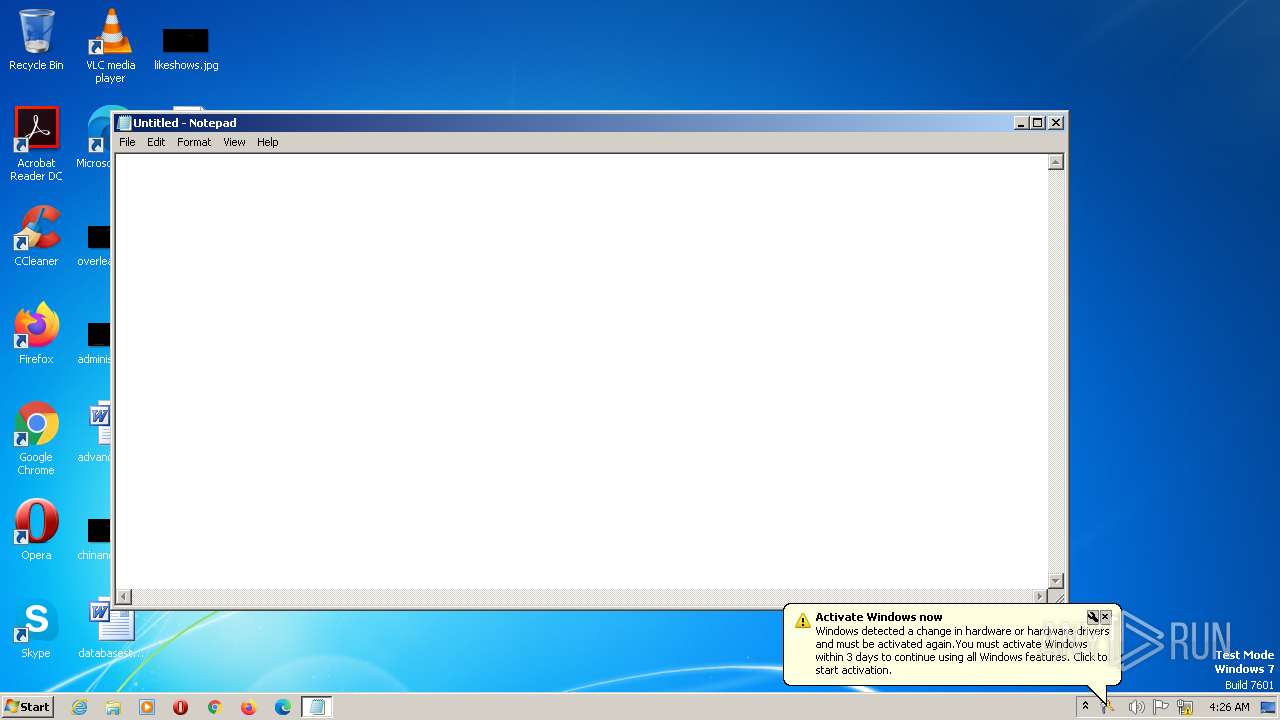
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- notepad.exe (PID: 2904)
- InstallWindos12.exe (PID: 2980)
Connects to unusual port
- InstallWindos12.exe (PID: 2980)
Reads Microsoft Outlook installation path
- InstallWindos12.exe (PID: 2980)
Reads Internet Explorer settings
- InstallWindos12.exe (PID: 2980)
Checks Windows Trust Settings
- InstallWindos12.exe (PID: 2980)
Reads security settings of Internet Explorer
- InstallWindos12.exe (PID: 2980)
Reads settings of System Certificates
- InstallWindos12.exe (PID: 2980)
INFO
The process checks LSA protection
- notepad.exe (PID: 2904)
- InstallWindos12.exe (PID: 2980)
- slui.exe (PID: 2316)
Reads the machine GUID from the registry
- InstallWindos12.exe (PID: 2980)
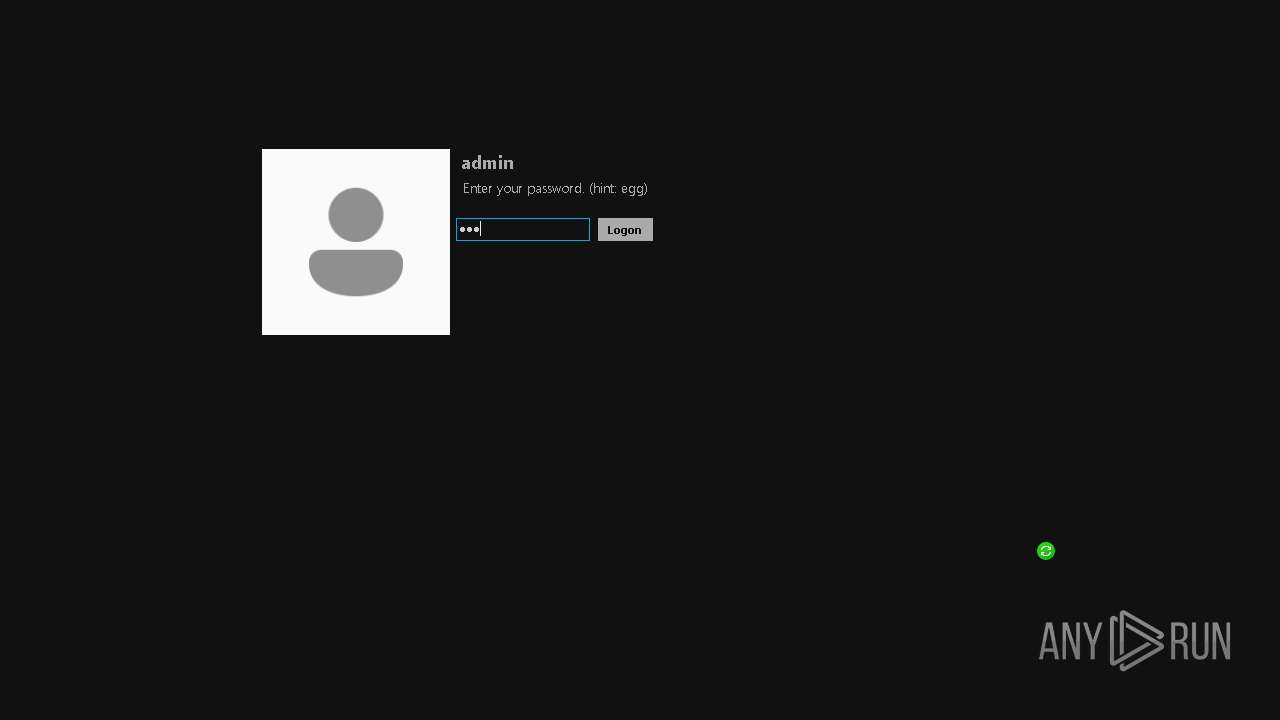
Manual execution by a user
- InstallWindos12.exe (PID: 2980)
Reads the computer name
- InstallWindos12.exe (PID: 2980)
Checks proxy server information
- InstallWindos12.exe (PID: 2980)
Checks supported languages
- InstallWindos12.exe (PID: 2980)
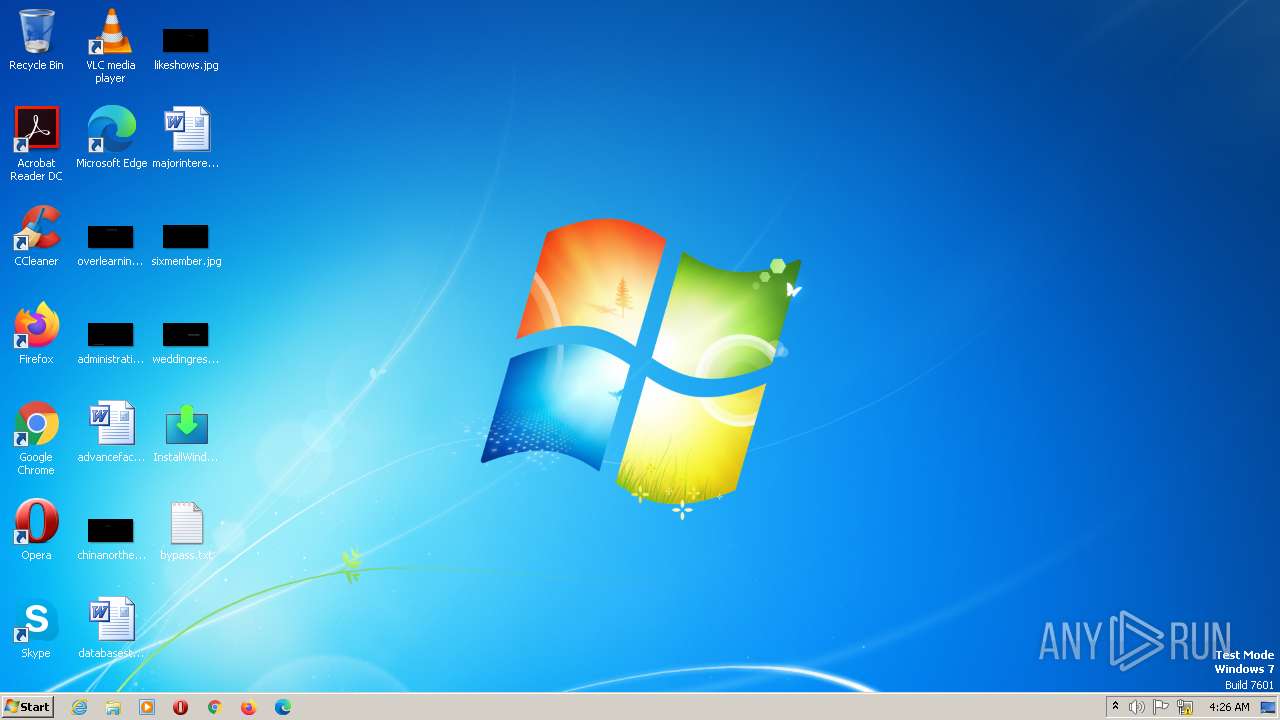
Creates files or folders in the user directory
- InstallWindos12.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (34.7) |
|---|---|---|
| .odttf | | | Obfuscated subsetted Font (24.6) |
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win64 Executable (generic) (13) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
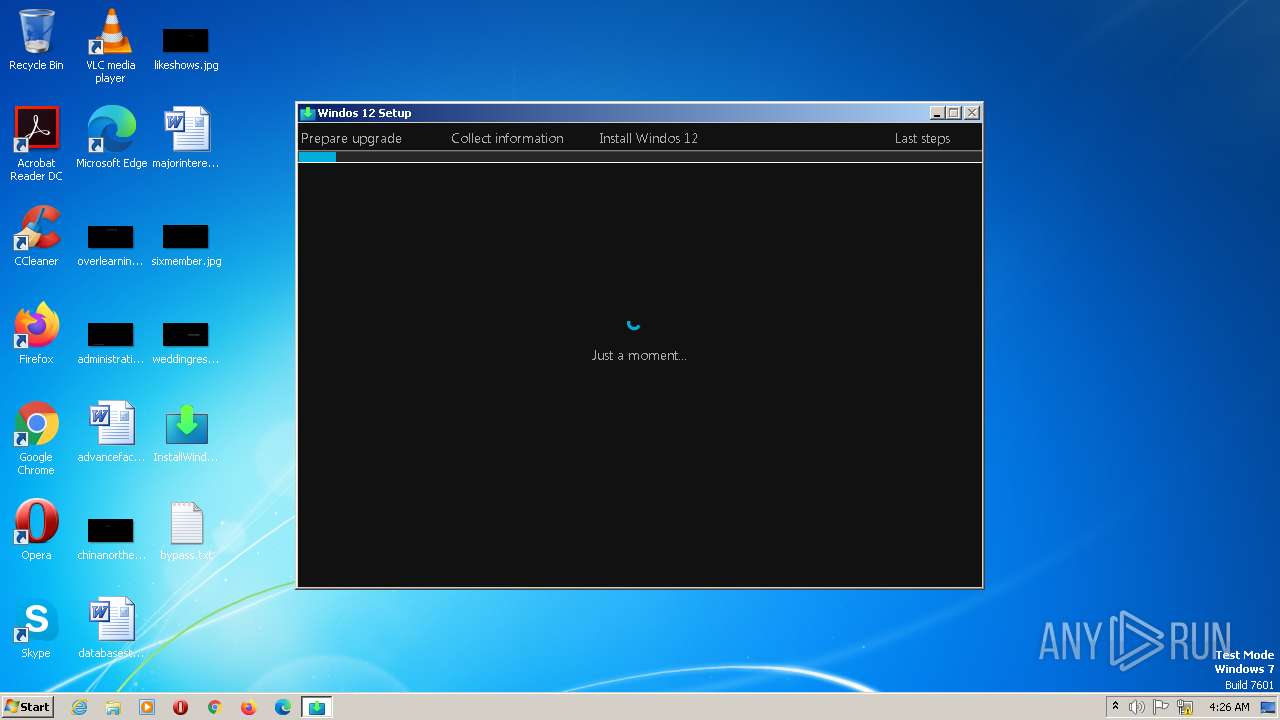
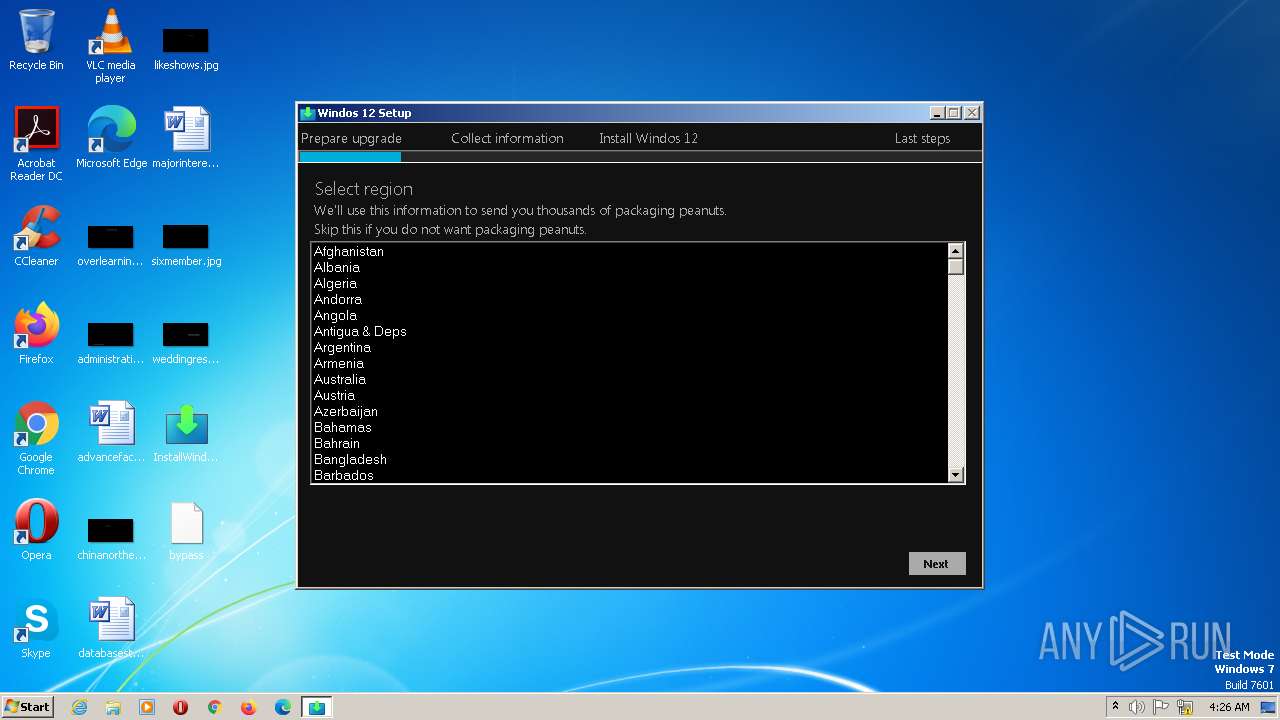
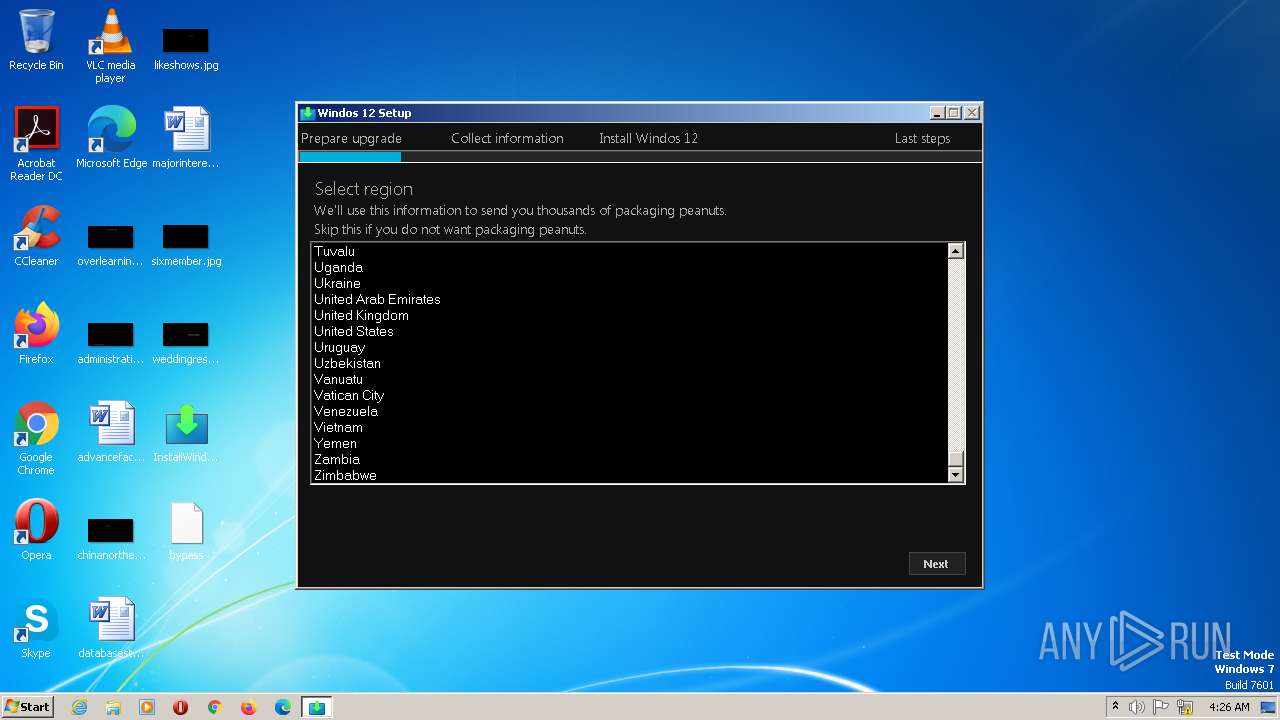
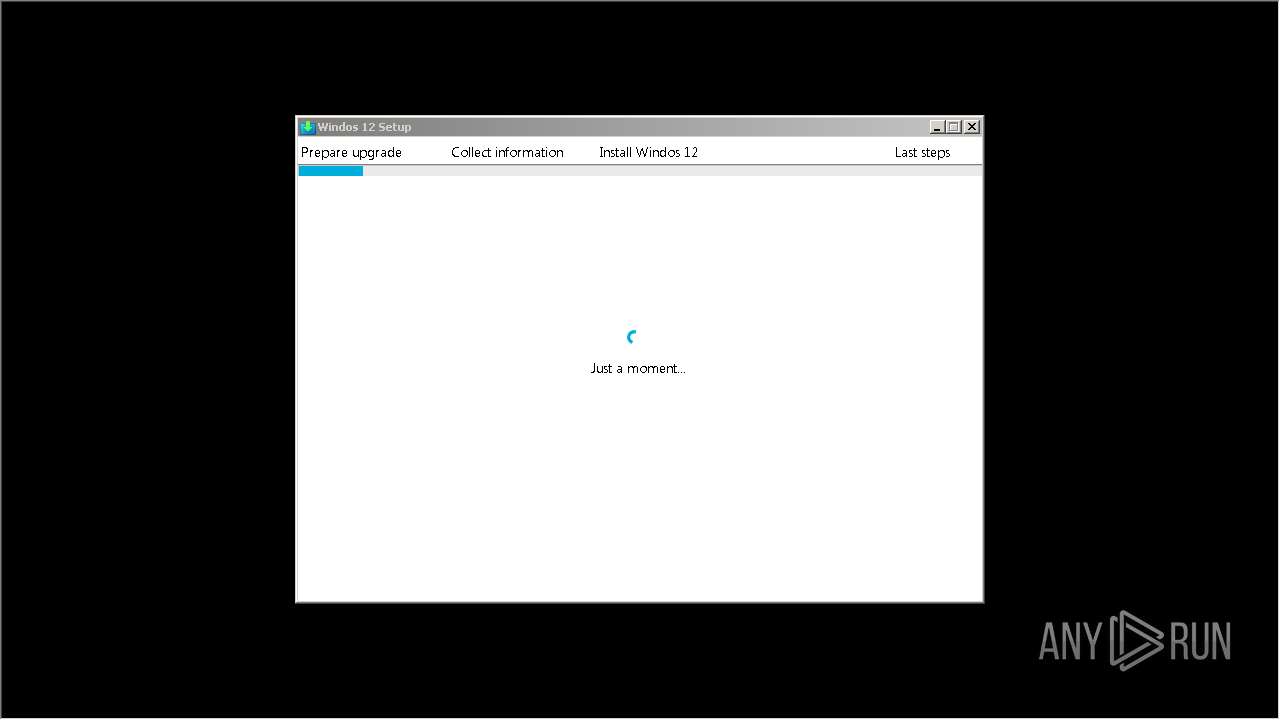
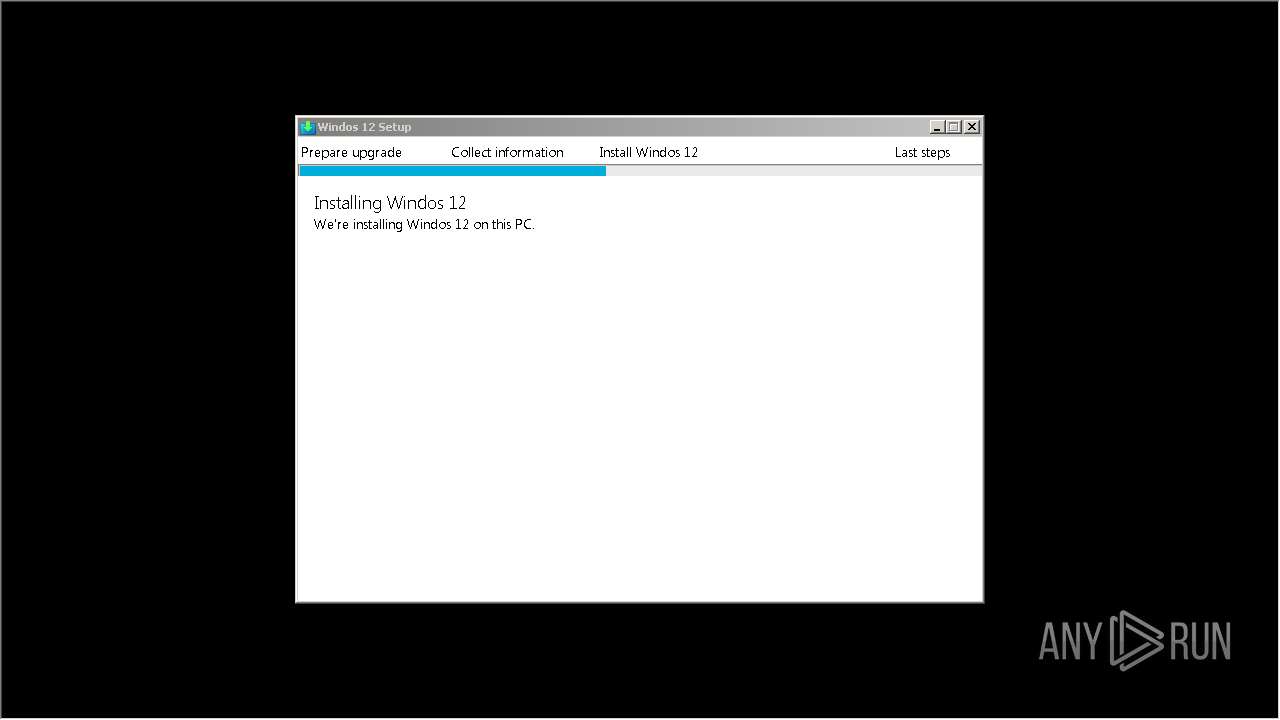
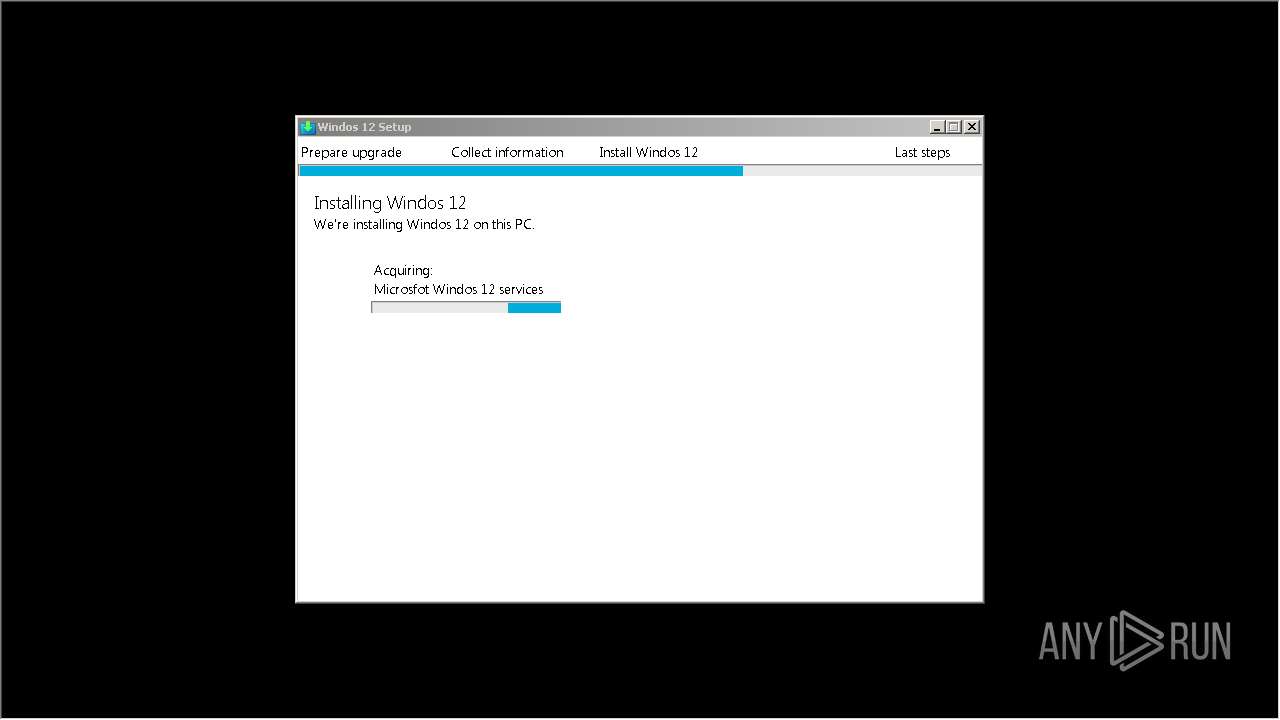
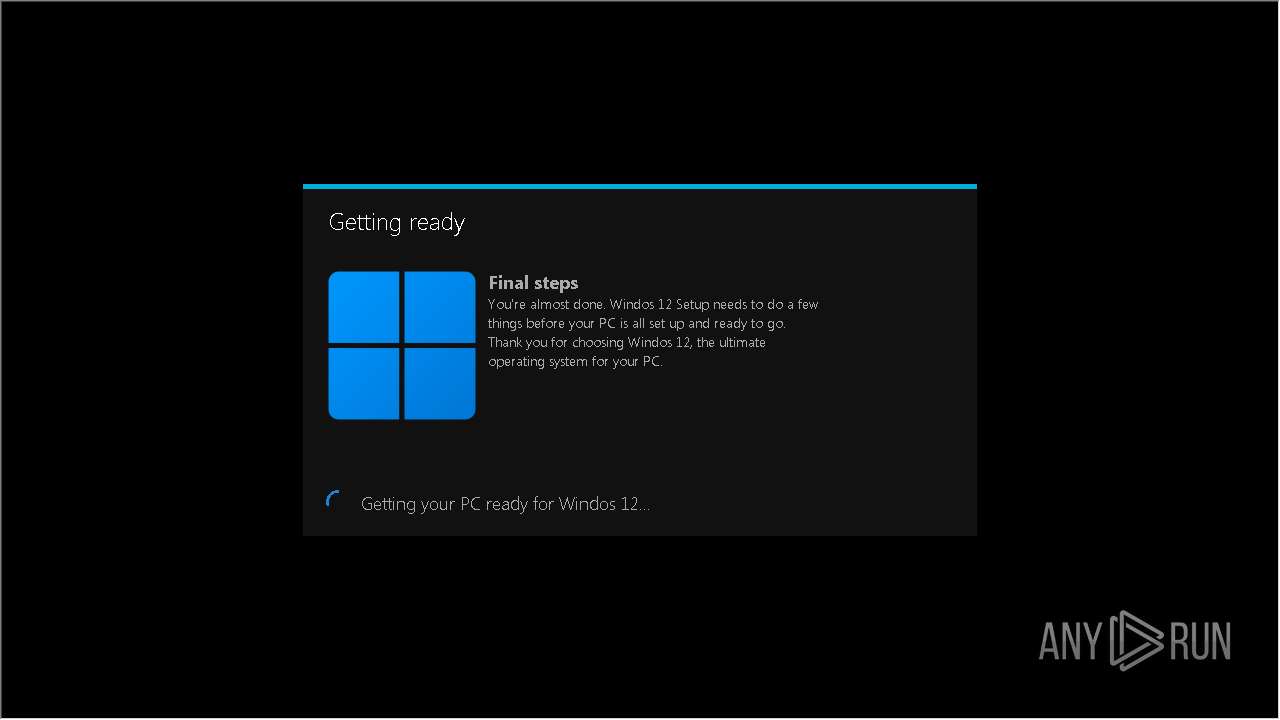
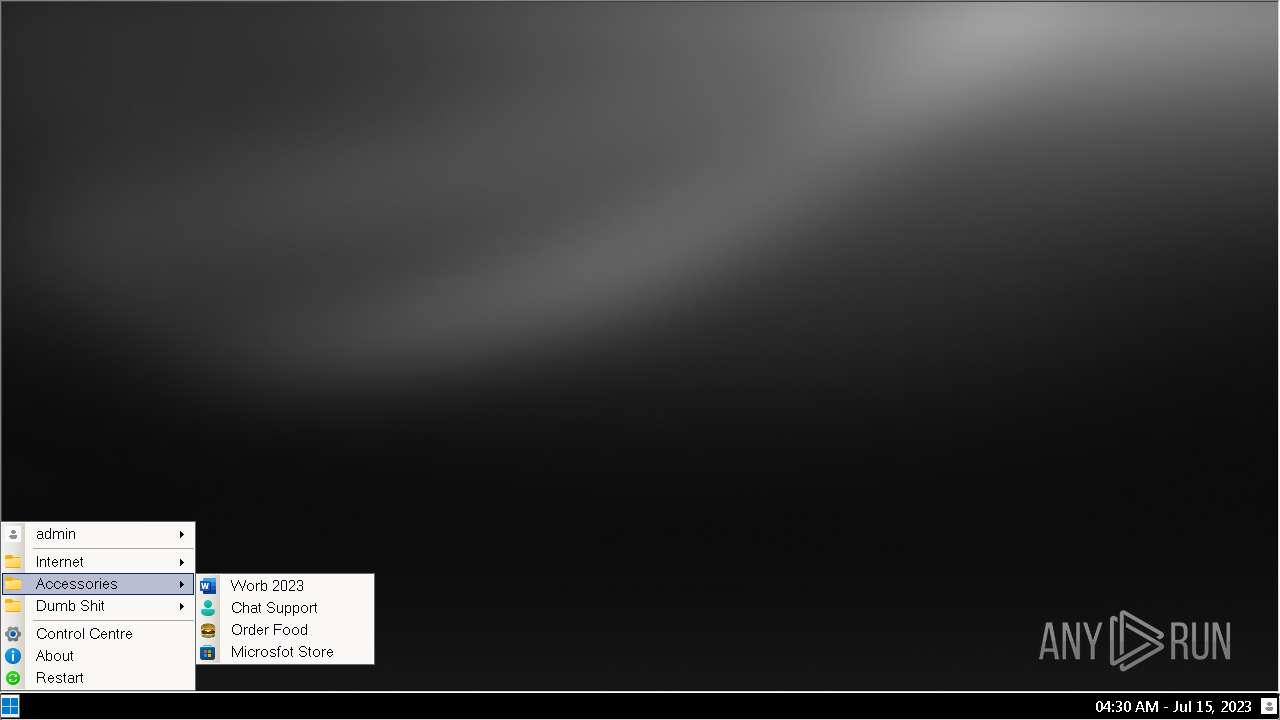
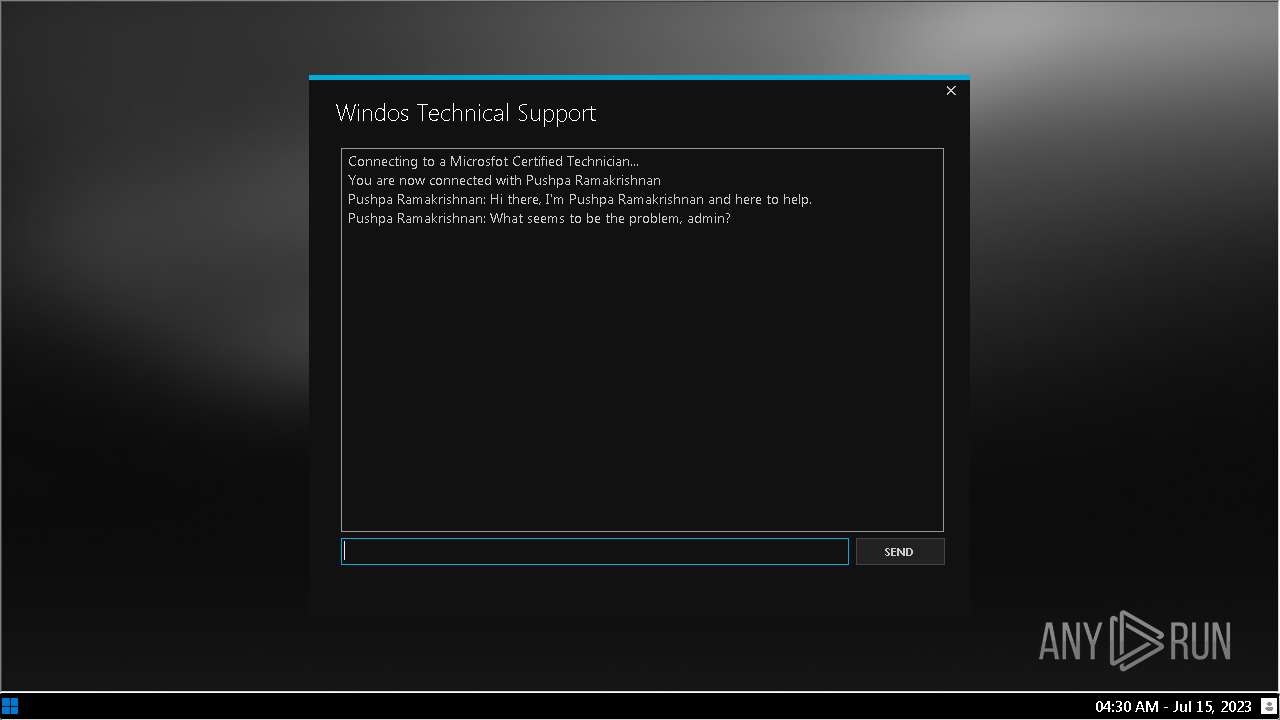
| ProductName: | Windos 12 Insider Preview |
| OriginalFileName: | Windos12Installer.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © Microsfot 2023 |
| InternalName: | Windos12Installer.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Microsfot Windos 12 |
| CompanyName: | Microsfot Corporation |
| Comments: | Windos installation |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x7ea1ae |
| UninitializedDataSize: | - |
| InitializedDataSize: | 80896 |
| CodeSize: | 8290816 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:04:11 21:04:53+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Apr-2023 21:04:53 |
| Debug artifacts: |
|
| Comments: | Windos installation |
| CompanyName: | Microsfot Corporation |
| FileDescription: | Microsfot Windos 12 |
| FileVersion: | 1.0.0.0 |
| InternalName: | Windos12Installer.exe |
| LegalCopyright: | Copyright © Microsfot 2023 |
| LegalTrademarks: | - |
| OriginalFilename: | Windos12Installer.exe |
| ProductName: | Windos 12 Insider Preview |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 11-Apr-2023 21:04:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x007E81B4 | 0x007E8200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.17069 |
.rsrc | 0x007EC000 | 0x00013846 | 0x00013A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.57365 |
.reloc | 0x00800000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.78181 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.73652 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.86479 | 6760 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.81058 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.97677 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.00105 | 1720 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 5.37261 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.94105 | 118 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
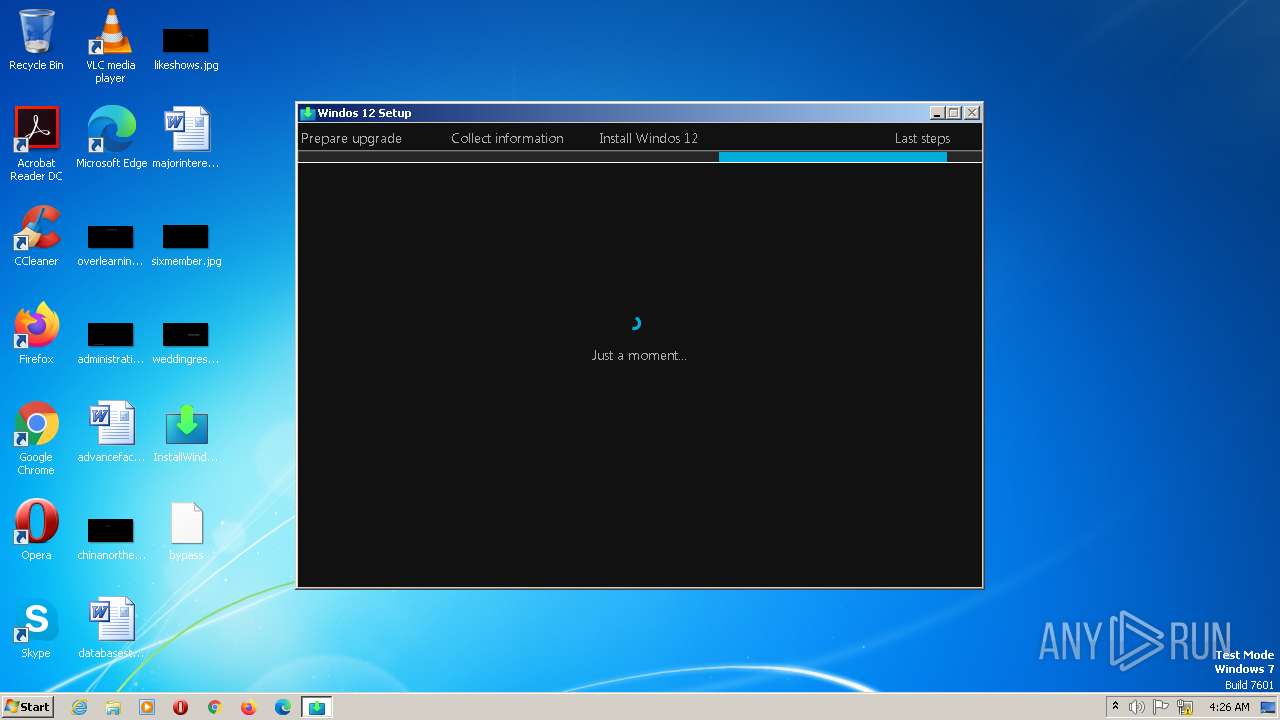
Total processes
48
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2316 | C:\Windows\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
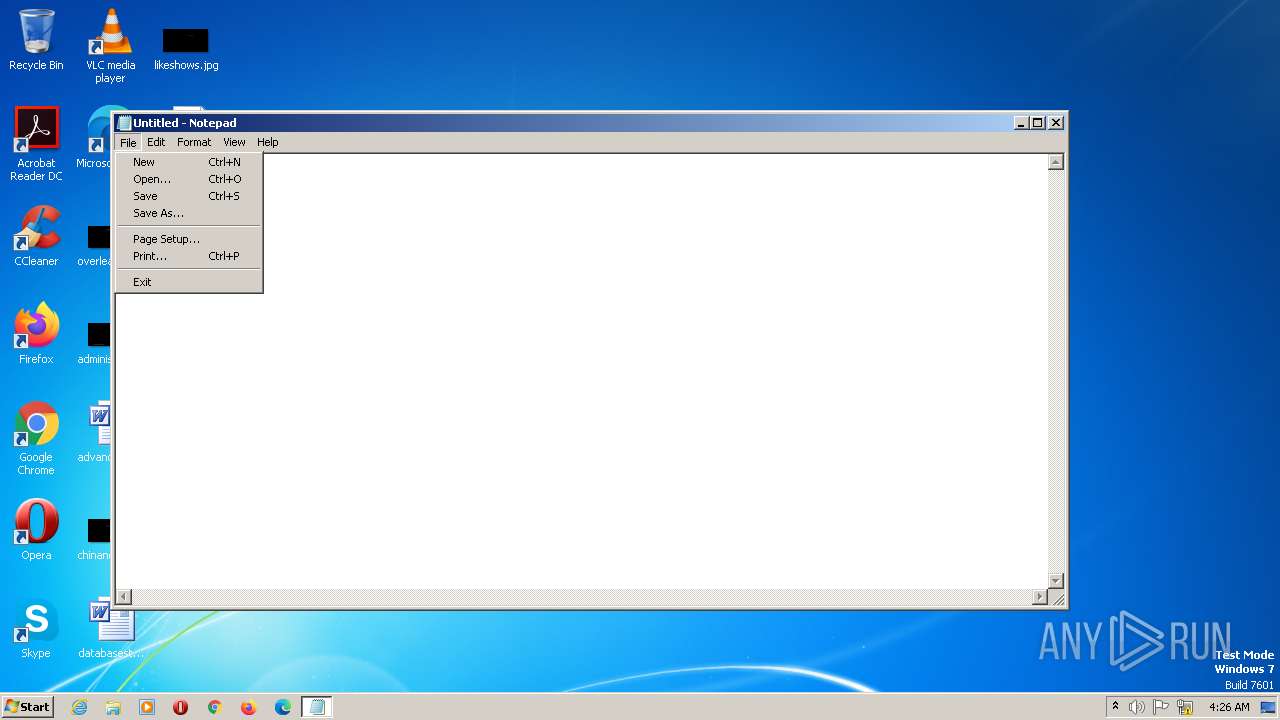
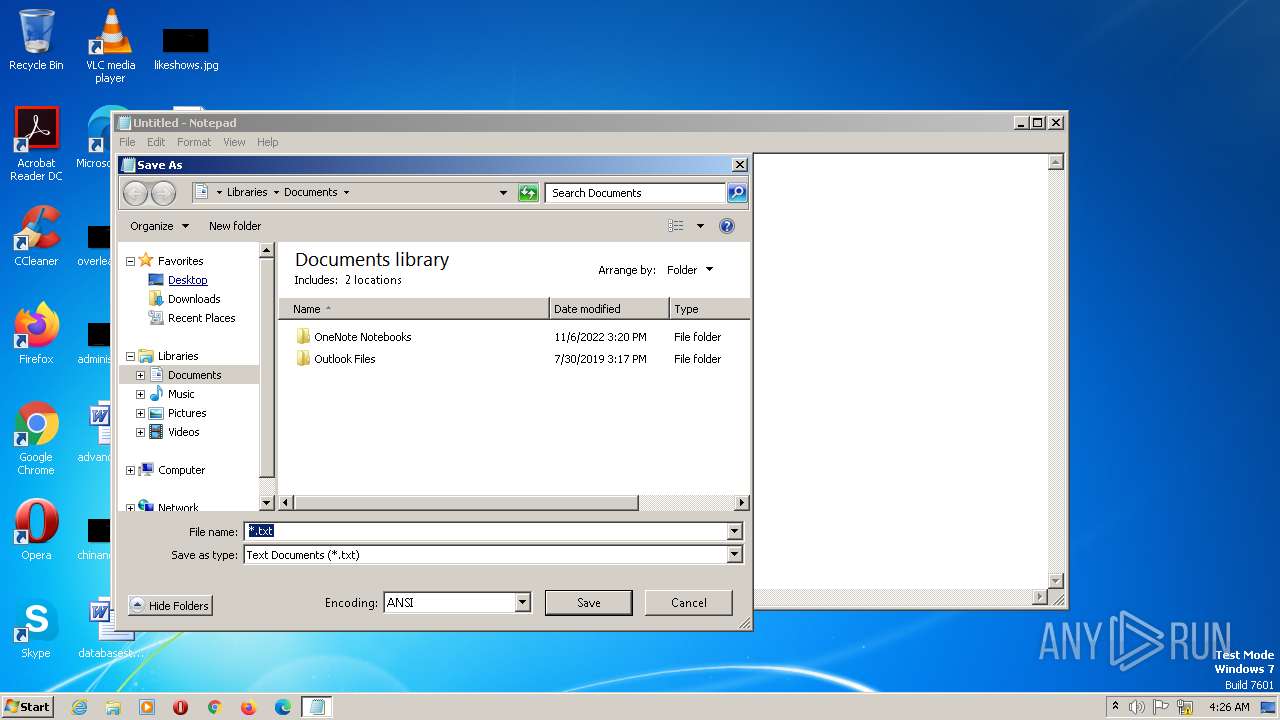
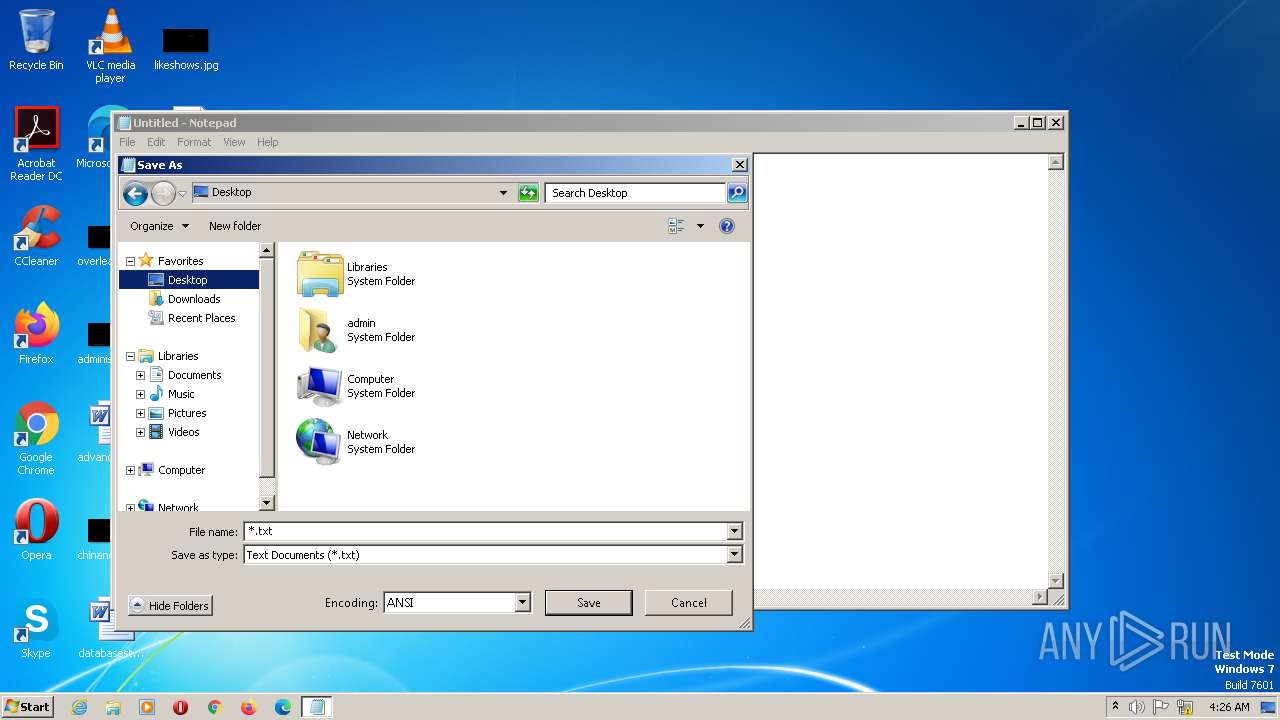
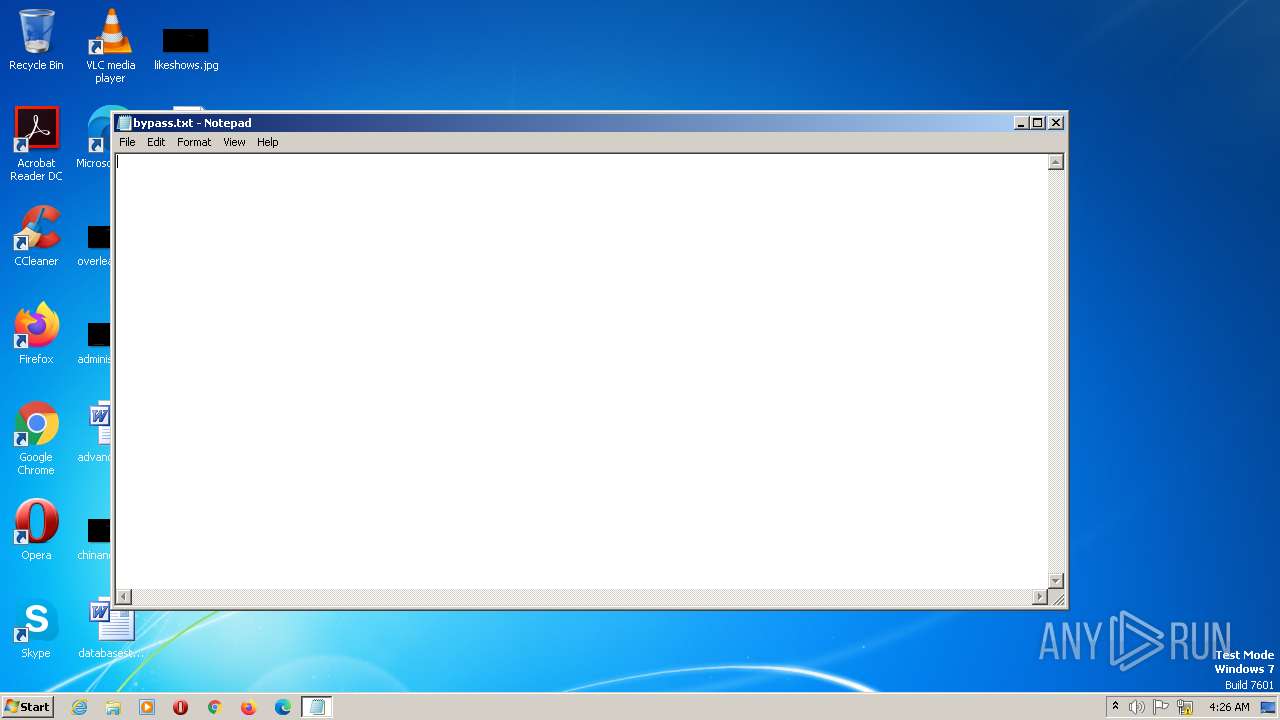
| 2904 | "C:\Windows\System32\notepad.exe" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\Desktop\InstallWindos12.exe" | C:\Users\admin\Desktop\InstallWindos12.exe | explorer.exe | ||||||||||||
User: admin Company: Microsfot Corporation Integrity Level: MEDIUM Description: Microsfot Windos 12 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
2 963
Read events
2 882
Write events
79
Delete events
2
Modification events
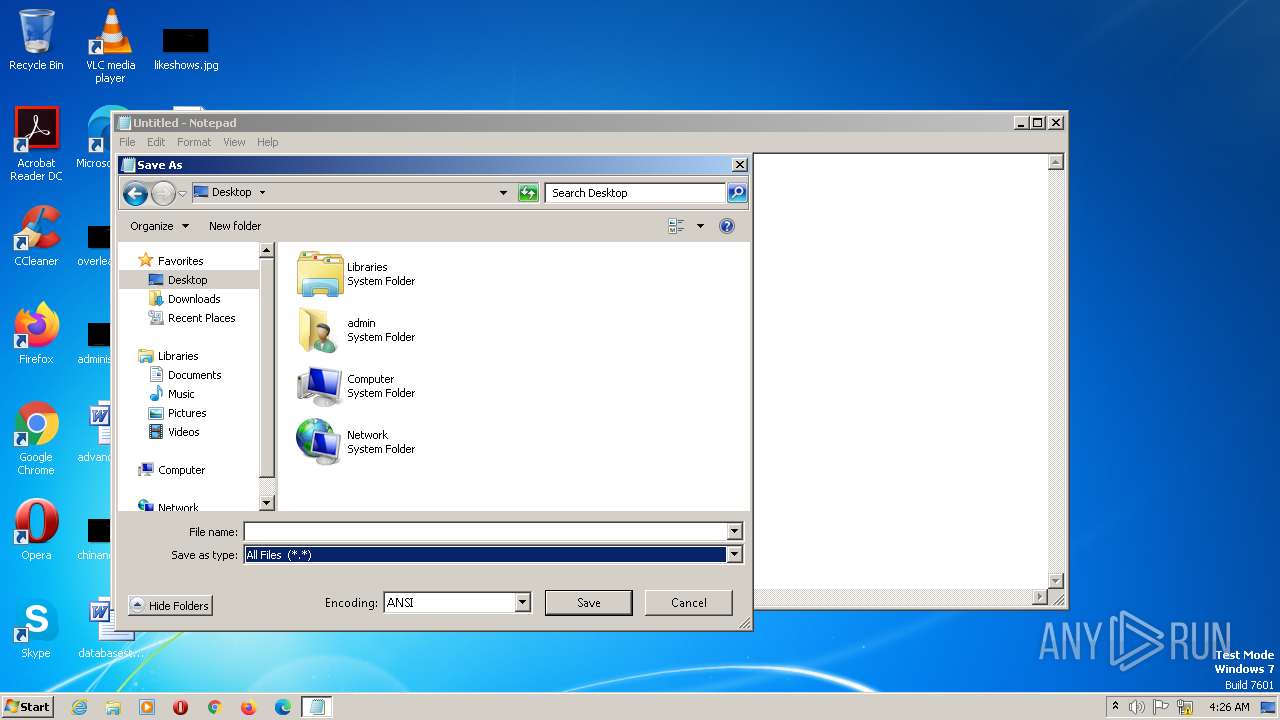
| (PID) Process: | (2904) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2904) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 000000000600000002000000010000000800000007000000050000000300000004000000FFFFFFFF | |||
| (PID) Process: | (2904) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\2 |
| Operation: | write | Name: | MRUListEx |
Value: 03000000000000000200000001000000FFFFFFFF | |||
| (PID) Process: | (2904) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000000000006000000010000000800000007000000050000000300000004000000FFFFFFFF | |||
| (PID) Process: | (2904) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\37\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2904) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\37\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2904) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\37\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2904) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\155\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2904) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (2904) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
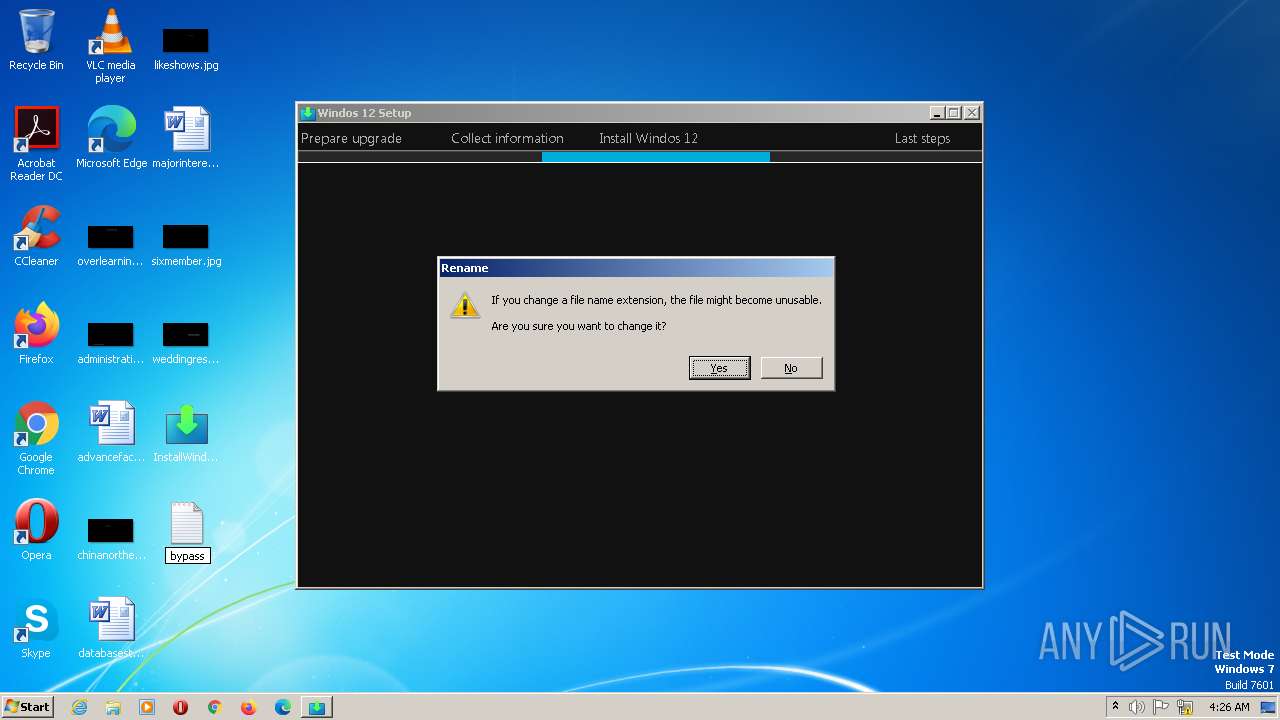
| 2904 | notepad.exe | C:\Users\admin\Desktop\bypass.txt | — | |
MD5:— | SHA256:— | |||
| 2980 | InstallWindos12.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\K1X771N9.txt | text | |
MD5:14EA2A43B15F257CC3FB5762A378F4EF | SHA256:FB377C029C53466B109438EA8CC9153C14C5BFF6F1E71591D3A1289E4692B020 | |||
| 2980 | InstallWindos12.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2U1WPAC\recaptcha__en[1].js | text | |
MD5:0412C030048DB82D958EADBB899B0B6F | SHA256:237F4A5B7B8E81B7AD01C54CBB6205368AA9D55E1D6FD1EF38454FACDC01353C | |||
| 2980 | InstallWindos12.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\GWSXVINH.txt | text | |
MD5:41CDDE57B5EC9A112BA634ADD2406784 | SHA256:C826963CDA63D8FDC74AD87B3E069C2BE522455F3997E9E965928B02101B20B0 | |||
| 2980 | InstallWindos12.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\api[1].js | text | |
MD5:2E3E4D05EBA04C032758843C3ACA80C4 | SHA256:1C5F2FC4A7D1DDD45D3F965B175B70973260F079BBE0FBC6EB5FEEE59D41A70E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
7
DNS requests
4
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
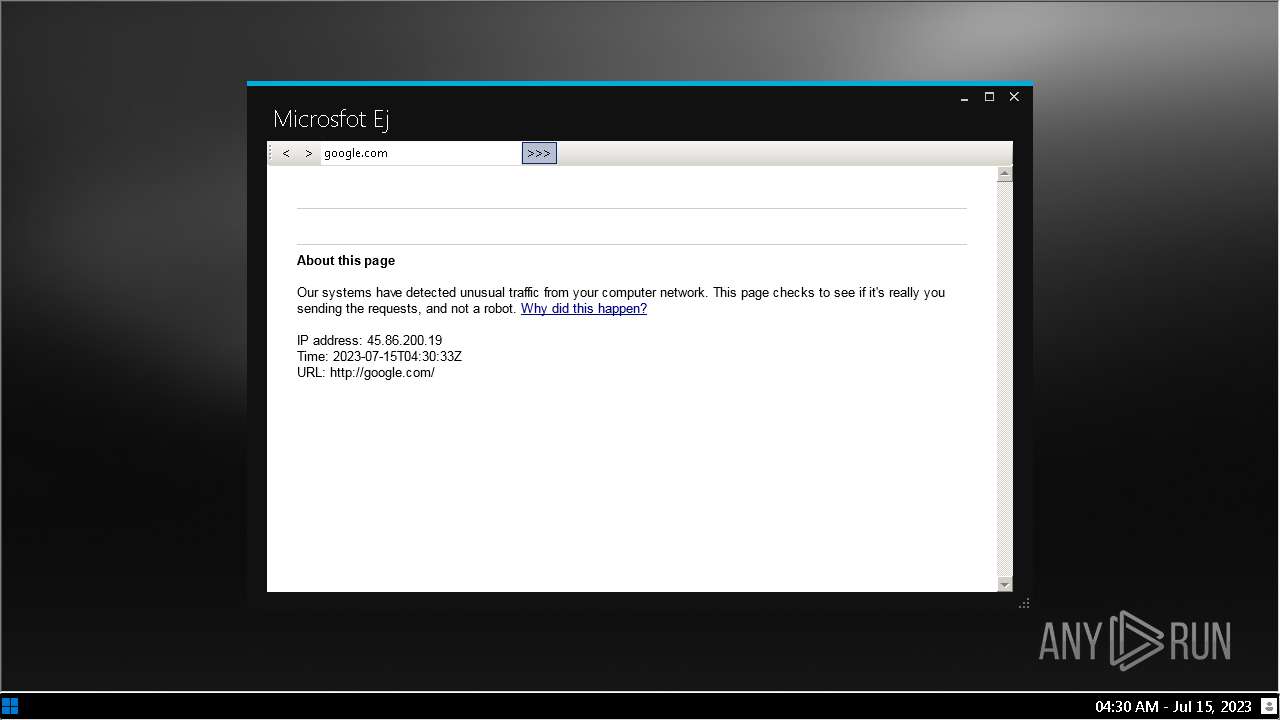
2980 | InstallWindos12.exe | GET | 302 | 142.250.186.110:80 | http://google.com/ | US | html | 356 b | malicious |
2980 | InstallWindos12.exe | GET | 429 | 142.250.186.100:80 | http://www.google.com/sorry/index?continue=http://google.com/&q=EgQtVsgkGOnByKUGIjAuVRVIDO3QXWvLA-4W3-a_HnF-sfbGKcure2B-hN-ipcvTixr5gSDPhD71xofkcqoyAXJaAUM | US | html | 3.00 Kb | malicious |
2980 | InstallWindos12.exe | GET | 429 | 142.250.186.100:80 | http://www.google.com/sorry/index?continue=http://google.com/&q=EgQtVsgkGOrByKUGIjC1KIkPKn0Ljc88FohCxdy-teDjl0mpiZ6wtR_9FSXHSh1XY4NdUx9PvUto0yXtJG8yAXJaAUM | US | html | 3.00 Kb | malicious |
2980 | InstallWindos12.exe | GET | 302 | 142.250.186.110:80 | http://google.com/ | US | html | 356 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
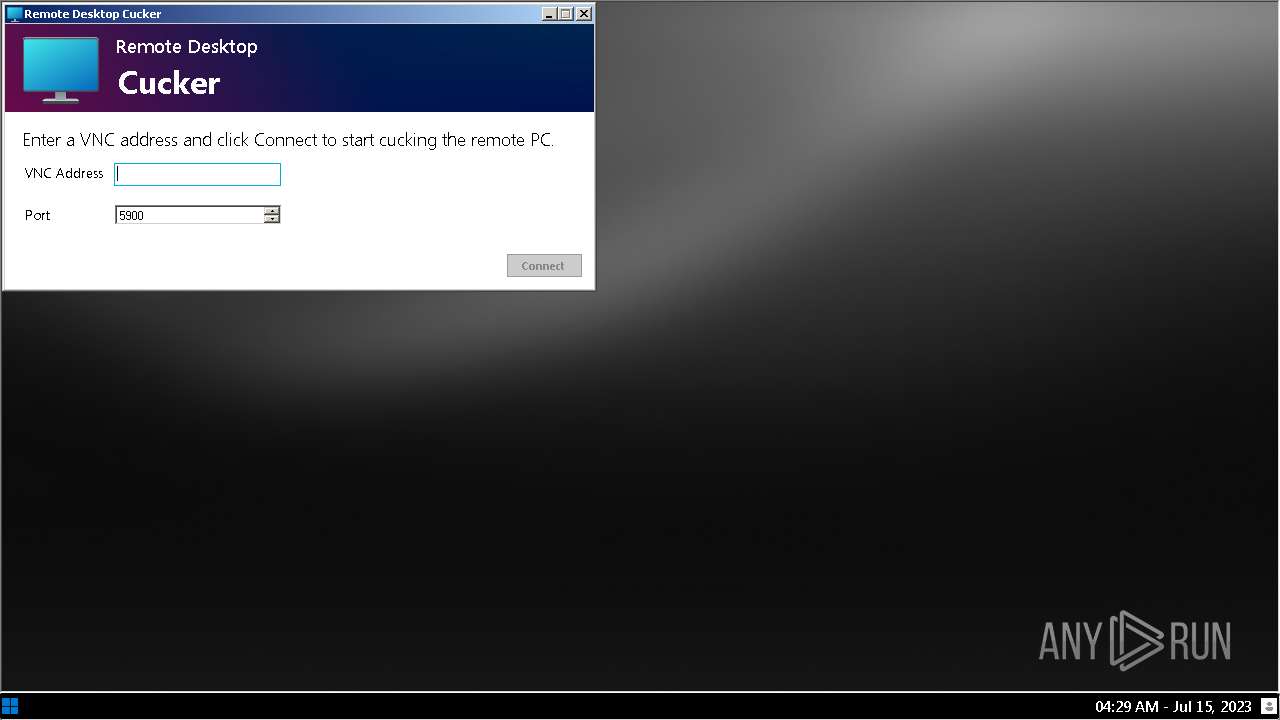
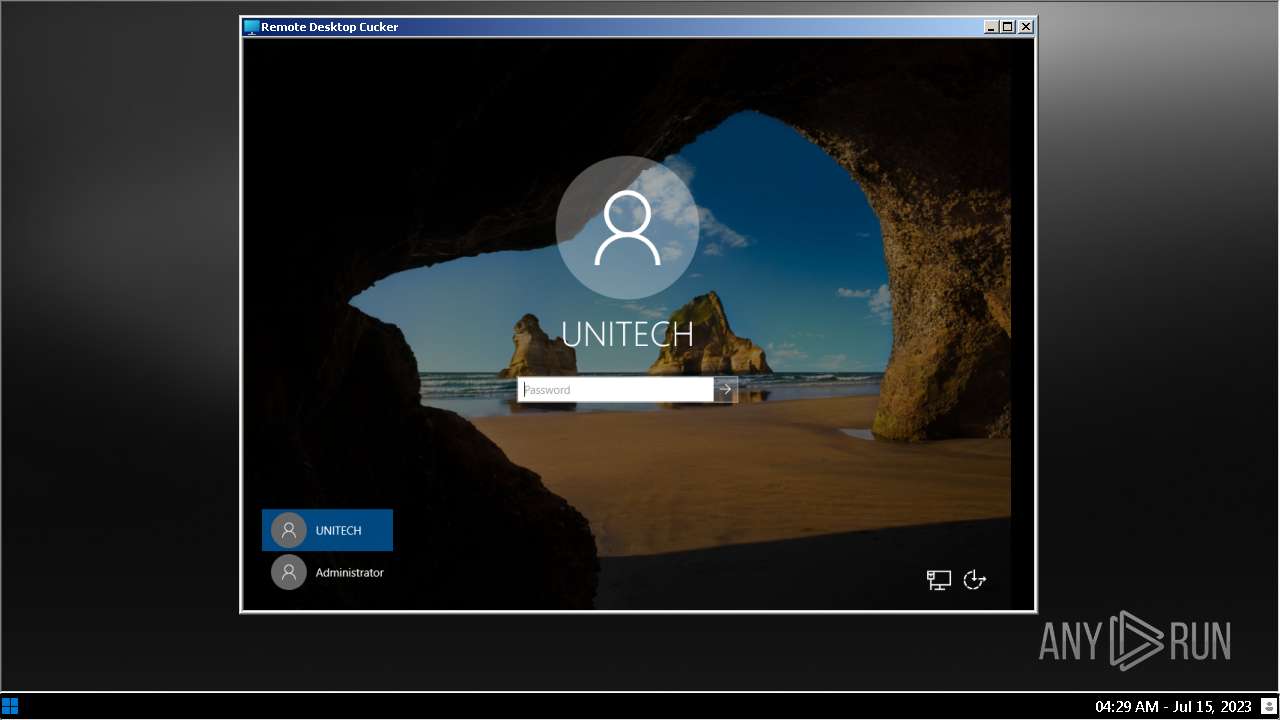
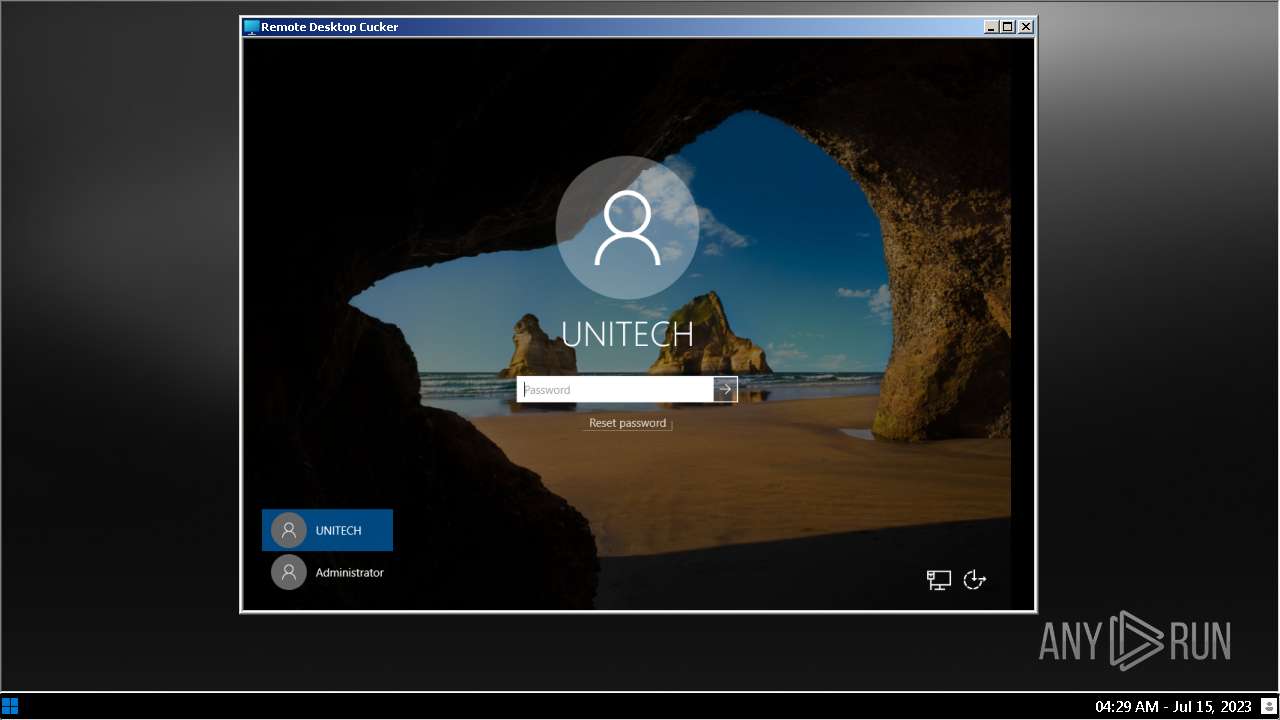
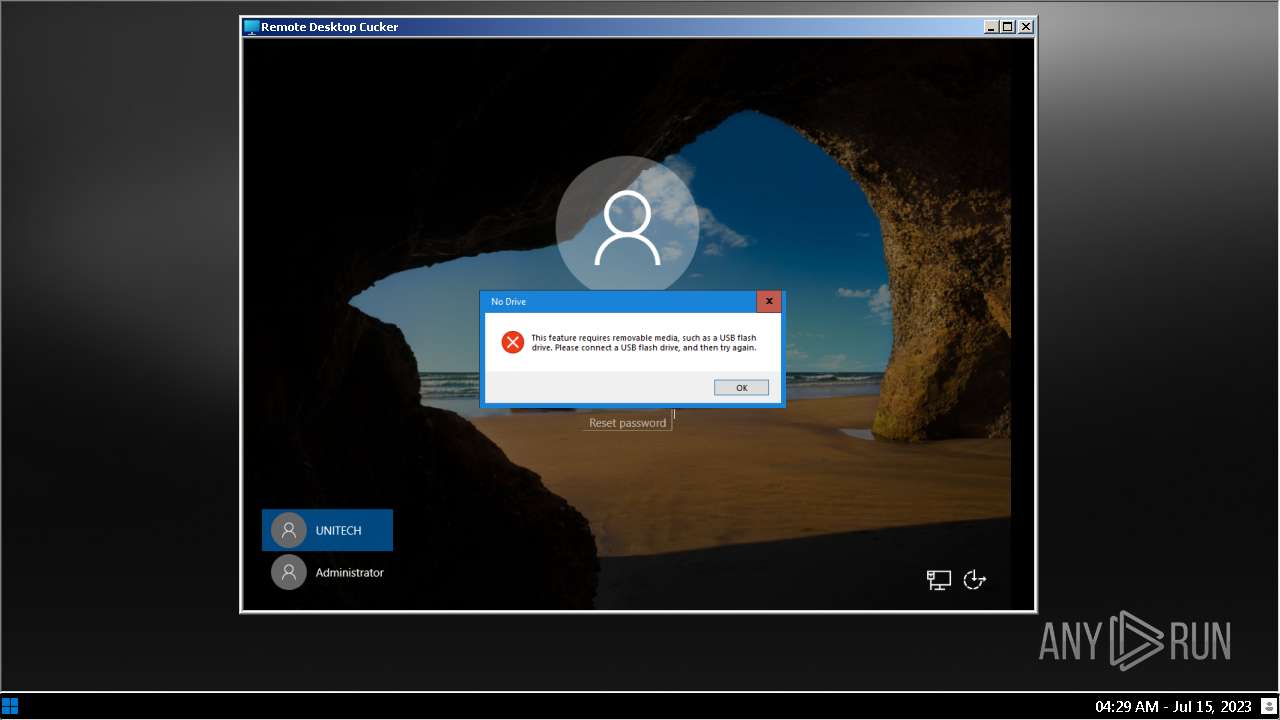
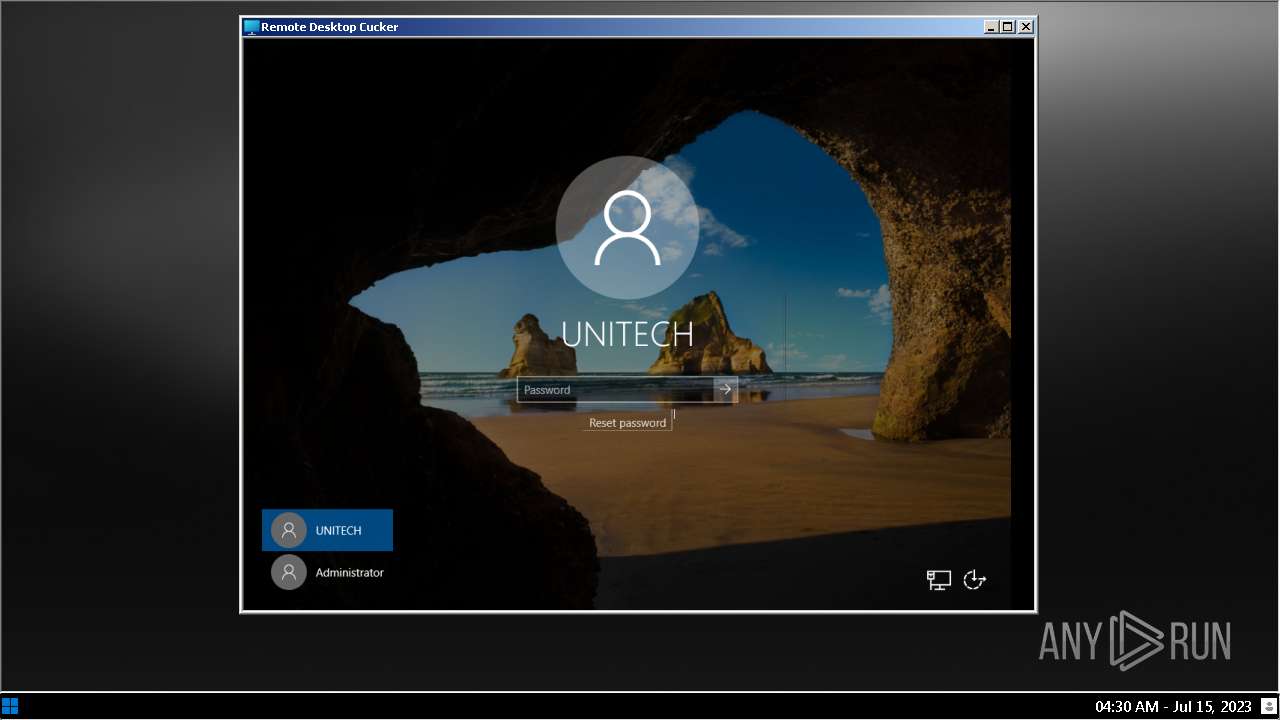
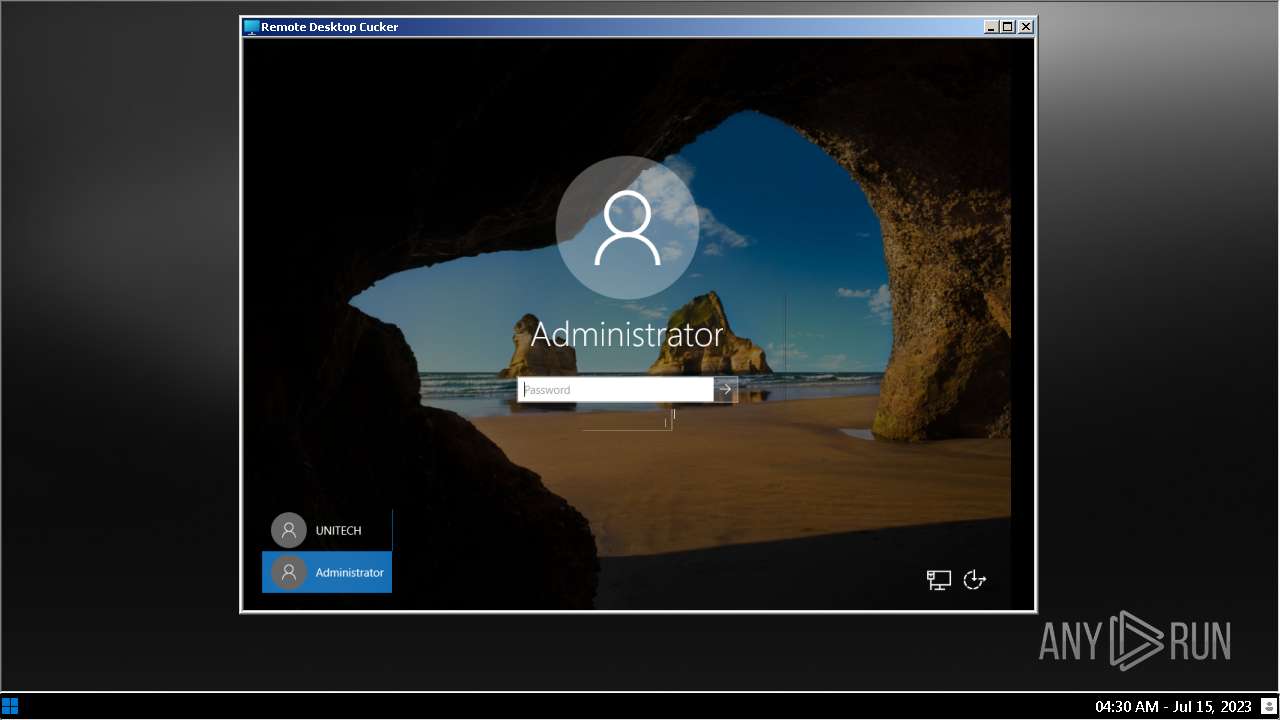
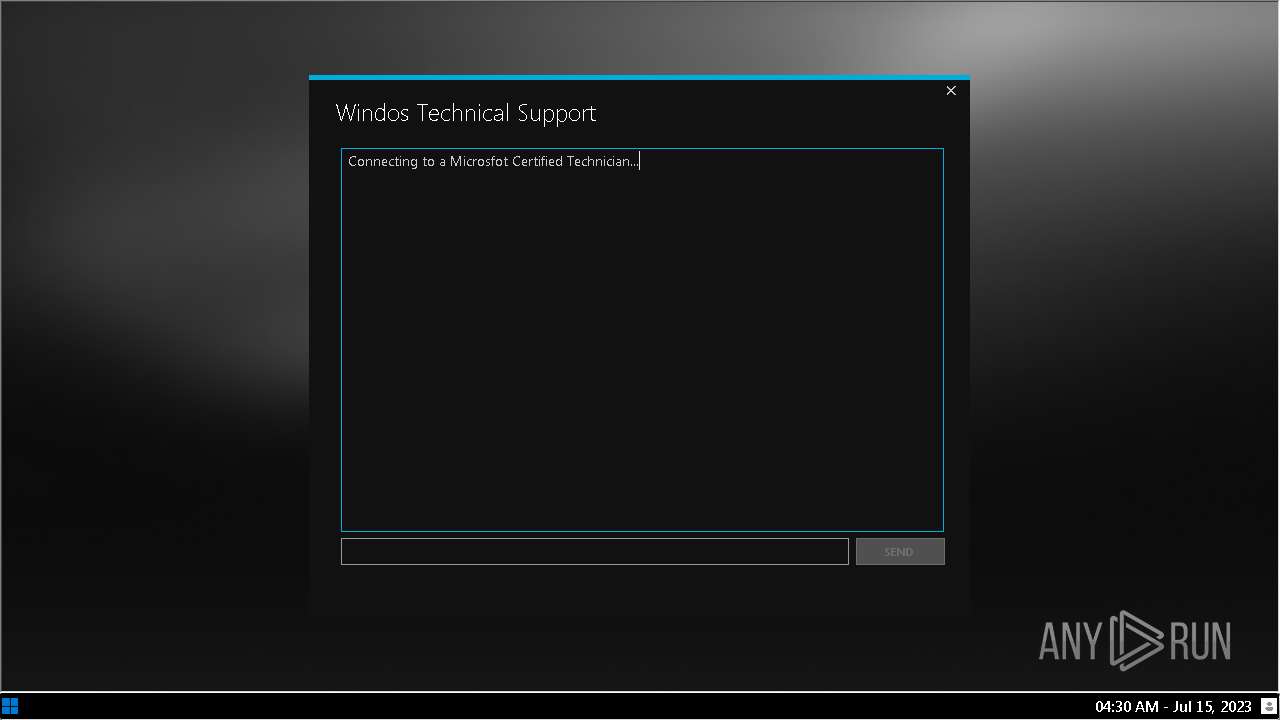
2980 | InstallWindos12.exe | 92.204.40.107:5900 | — | Host Europe GmbH | FR | suspicious |
2980 | InstallWindos12.exe | 23.148.232.35:443 | microsfot.epicgamer.org | — | — | suspicious |
2980 | InstallWindos12.exe | 142.250.185.99:443 | www.gstatic.com | GOOGLE | US | whitelisted |
2980 | InstallWindos12.exe | 142.250.186.100:443 | www.google.com | GOOGLE | US | whitelisted |
2980 | InstallWindos12.exe | 142.250.186.110:80 | google.com | GOOGLE | US | whitelisted |
2980 | InstallWindos12.exe | 142.250.186.100:80 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsfot.epicgamer.org |
| suspicious |
google.com |
| malicious |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
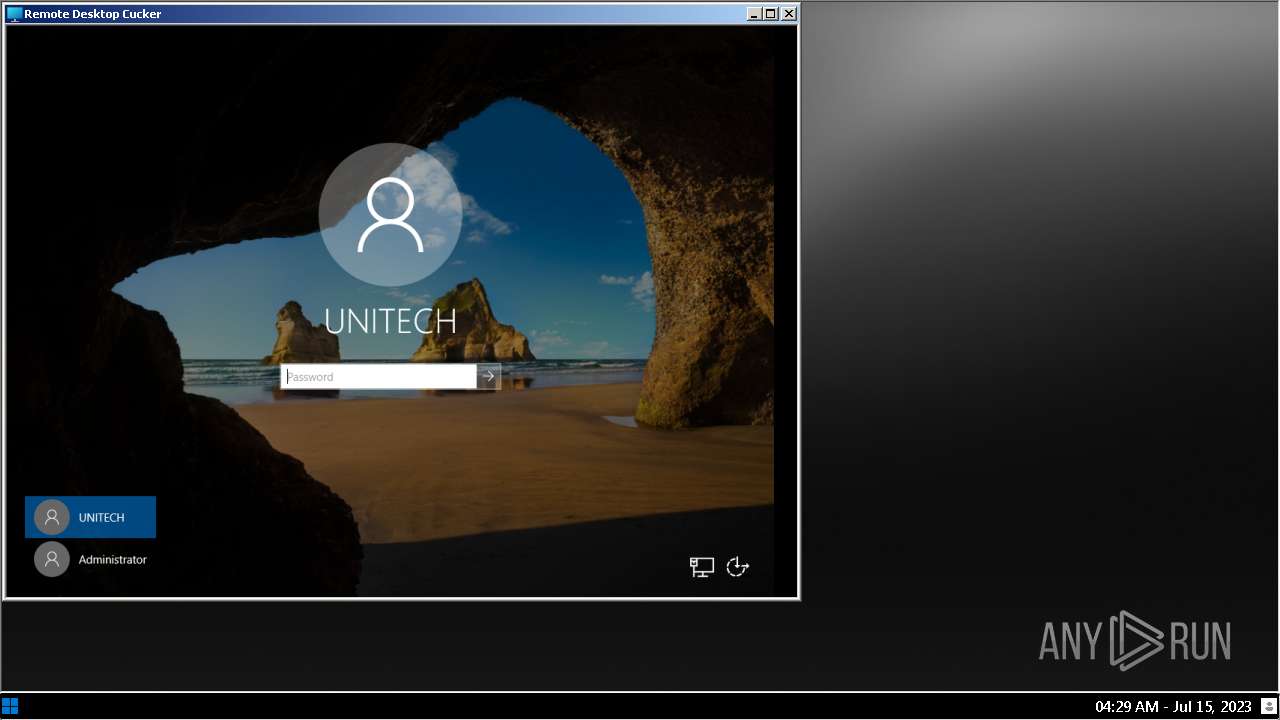
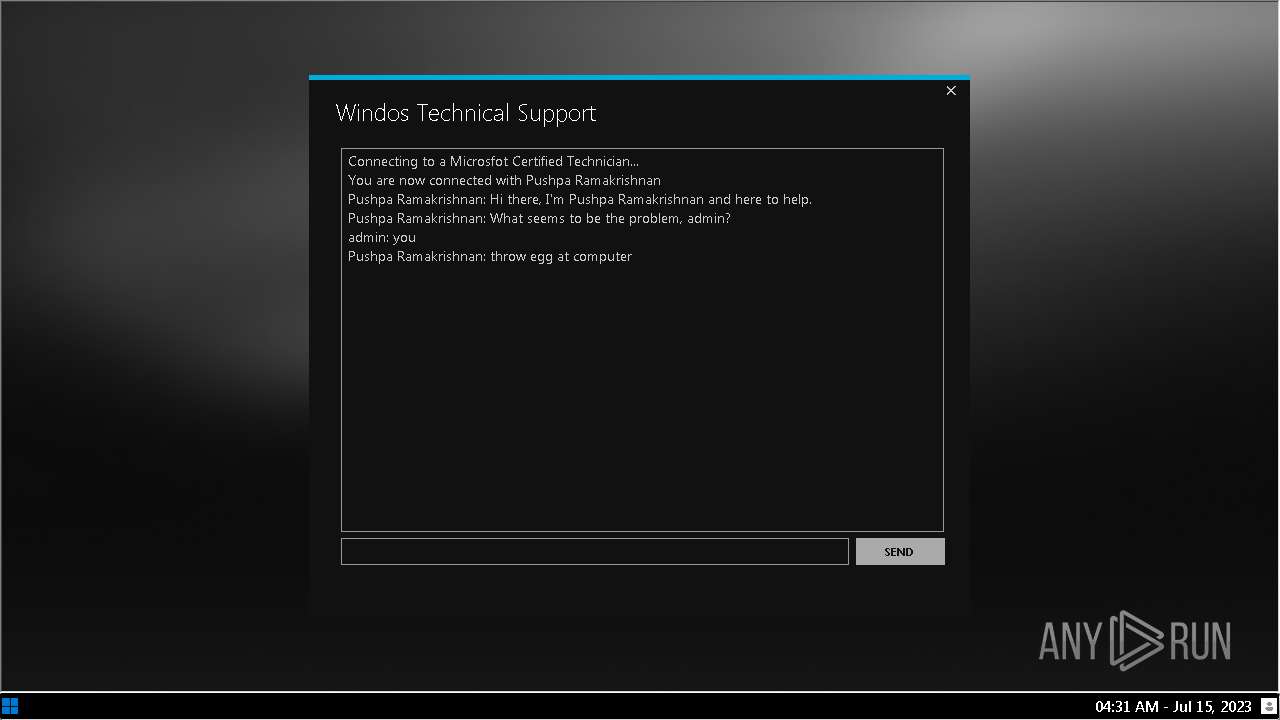
2980 | InstallWindos12.exe | Potential Corporate Privacy Violation | SUSPICIOUS [ANY.RUN] VNC negotiation was detected (ProtocolVersion message) |
324 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.epicgamer .org Domain |
4 ETPRO signatures available at the full report